| URL: | https://myfamilydollar.com/ |
| Full analysis: | https://app.any.run/tasks/600b9545-5795-41b0-925f-05097238c05b |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 00:52:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7FAA13EB8B4F7093F5E70669360DC8BA |
| SHA1: | F078BAE67C25BAA1E5578AECBA793BE8EB4B07AE |
| SHA256: | AC5D2E26B2E86ADCB04F497294E2D228D8C96903E0D1D9FBA7A10D7AB648FEBE |
| SSDEEP: | 3:N8UP/et:2UPWt |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2728)
- chrome.exe (PID: 4008)
Application launched itself
- chrome.exe (PID: 2728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2508 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18248413086042957058 --mojo-platform-channel-handle=3224 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3933631374944316984 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2512 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14109245712090021583 --mojo-platform-channel-handle=2612 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2815263793540413597 --mojo-platform-channel-handle=884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6437352210358295736 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://myfamilydollar.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16399361562721568716 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3616 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17877520762385148580 --mojo-platform-channel-handle=2832 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8998888836596186740 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
594
Read events
518
Write events
72
Delete events
4
Modification events
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2728-13247628766203875 |
Value: 259 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2728-13247628766203875 |
Value: 259 | |||
Executable files
0
Suspicious files
21
Text files
64
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E34DE-AA8.pma | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\abe2642e-d8b0-4394-9d44-f0f10246d15e.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d4153.TMP | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d4182.TMP | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF2d41a1.TMP | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d4144.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
25
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
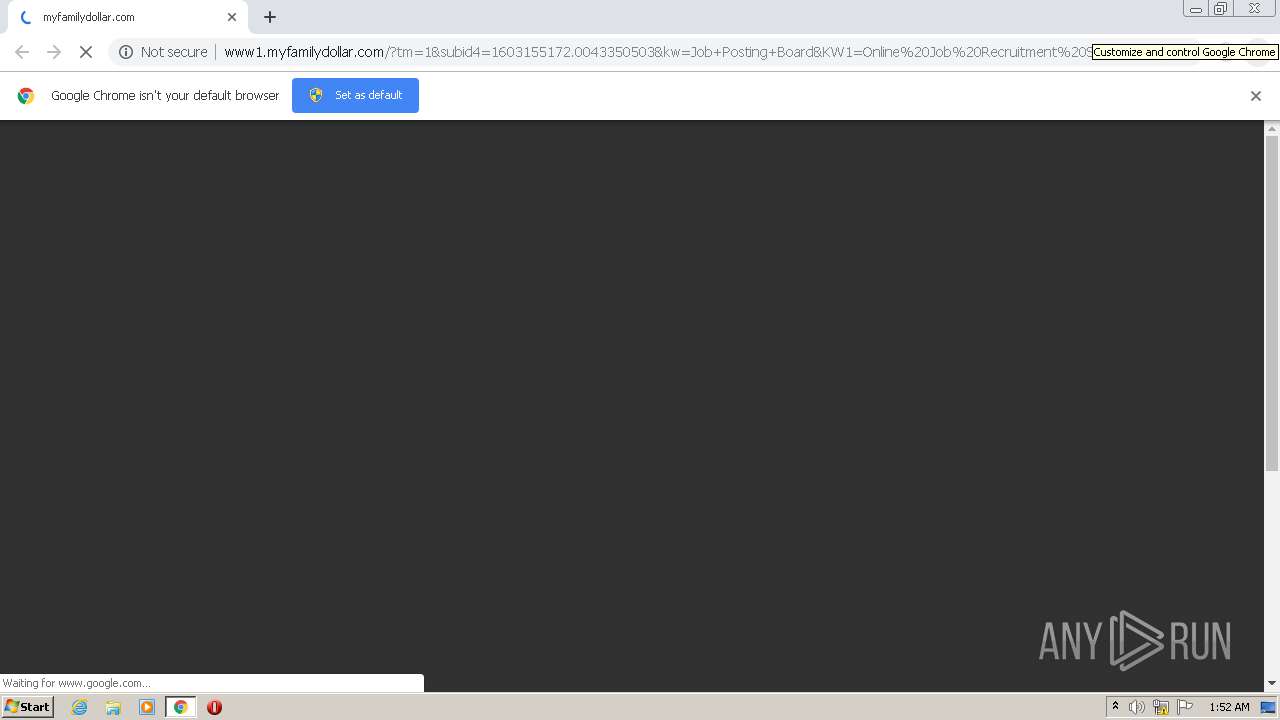
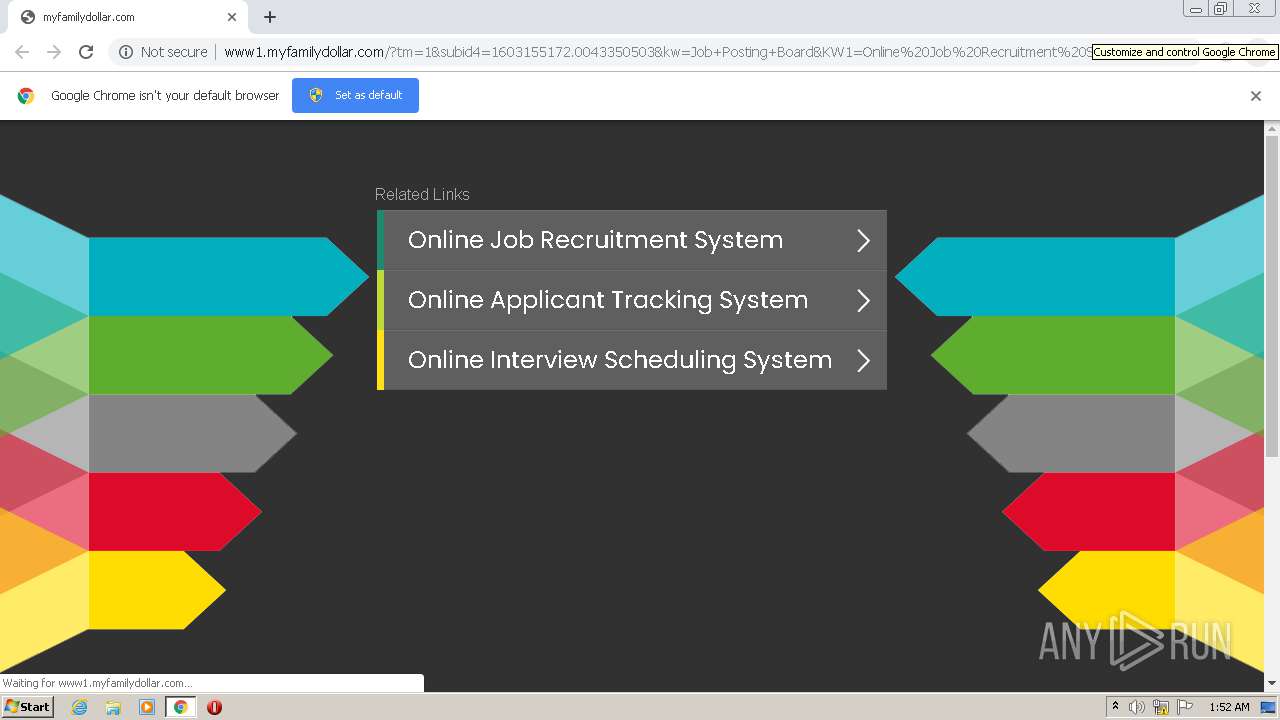
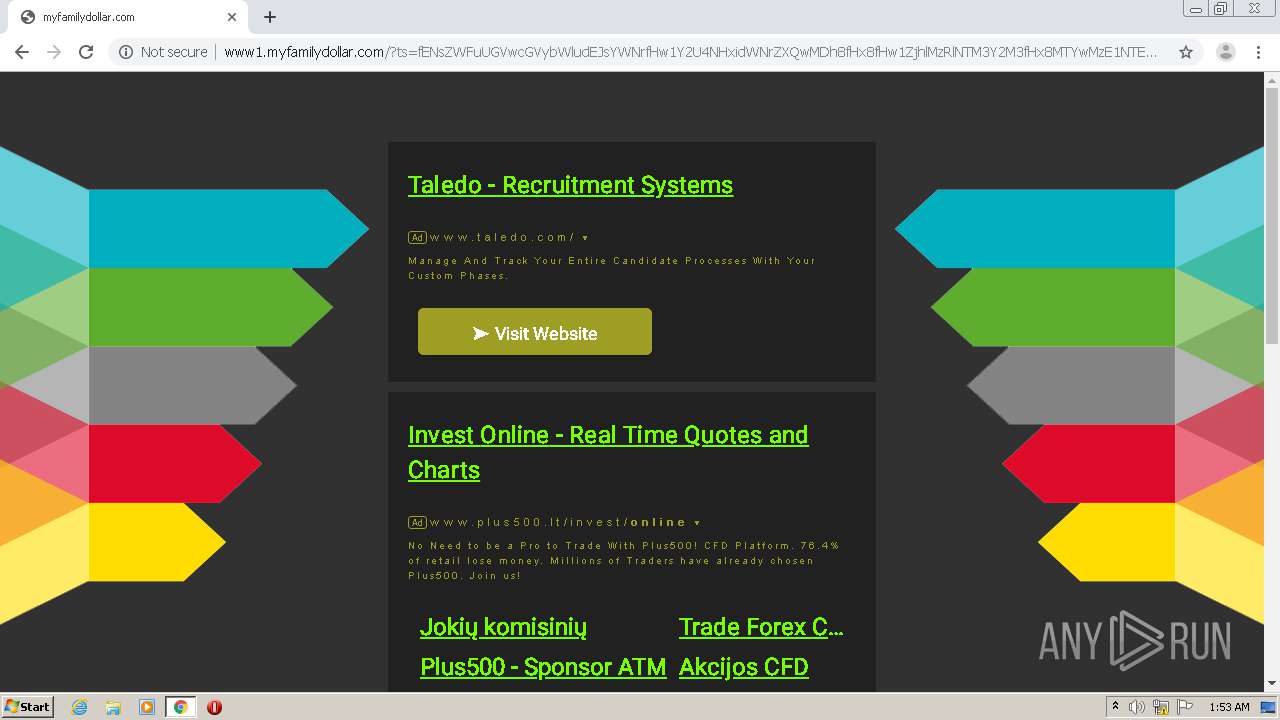
4008 | chrome.exe | GET | 200 | 13.248.148.254:80 | http://www1.myfamilydollar.com/?ts=fENsZWFuUGVwcGVybWludEJsYWNrfHw1Y2U4NHxidWNrZXQwMDh8fHx8fHw1ZjhlMzRlNTM3Y2M3fHx8MTYwMzE1NTE3My4yNDAzfDA1Y2Y4YTk1MjRmNTFiOTYxNmFlYTQ4YzFjZWViYWJiODg0ZWZjNTJ8fHx8fDF8fHwwfHx8fDF8fHx8fDB8MHx8fHx8fHwxfHx8MHwwfHwwfDB8MXwwfDB8VzEwPXx8MHxleUp6ZFdKcFpEUWlPaUl4TmpBek1UVTFNVGN5TGpBd05ETXpOVEExTURNaWZRPT18NTM0YTFmNTIyNGFkYmQ1YzA1ZTMxNDcxMjhkNjNiMDBkMTRkNWZlZg%3D%3D&query=Online%20Job%20Recruitment%20System&afdToken=3B1gljqXFvDUwA0l0fXXvhSKssRe9YcDrN9SSmhP3HMwKvH3TItKL-e7hS97L-58hGXvNRYAvait98s64sUWbYmz9kvpFbaUTskRo-uLUGzaNWLY&pcsa=false | US | html | 6.32 Kb | malicious |
4008 | chrome.exe | GET | 200 | 45.56.79.23:80 | http://myfamilydollar.com/mtm/async/eyJ1cmkiOiIvIiwiYXJncyI6IiIsInJlZmVyZXIiOiIiLCJob3N0X25hbWUiOiJteWZhbWlseWRvbGxhci5jb20ifQ:1kUftU:58U_wHyno0M8NWngSf4MHxx09z4/1 | US | text | 250 b | malicious |
4008 | chrome.exe | GET | 200 | 45.56.79.23:80 | http://myfamilydollar.com/ | US | html | 1.57 Kb | malicious |
4008 | chrome.exe | GET | 200 | 52.222.177.27:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/assets/style.css | US | text | 343 b | shared |
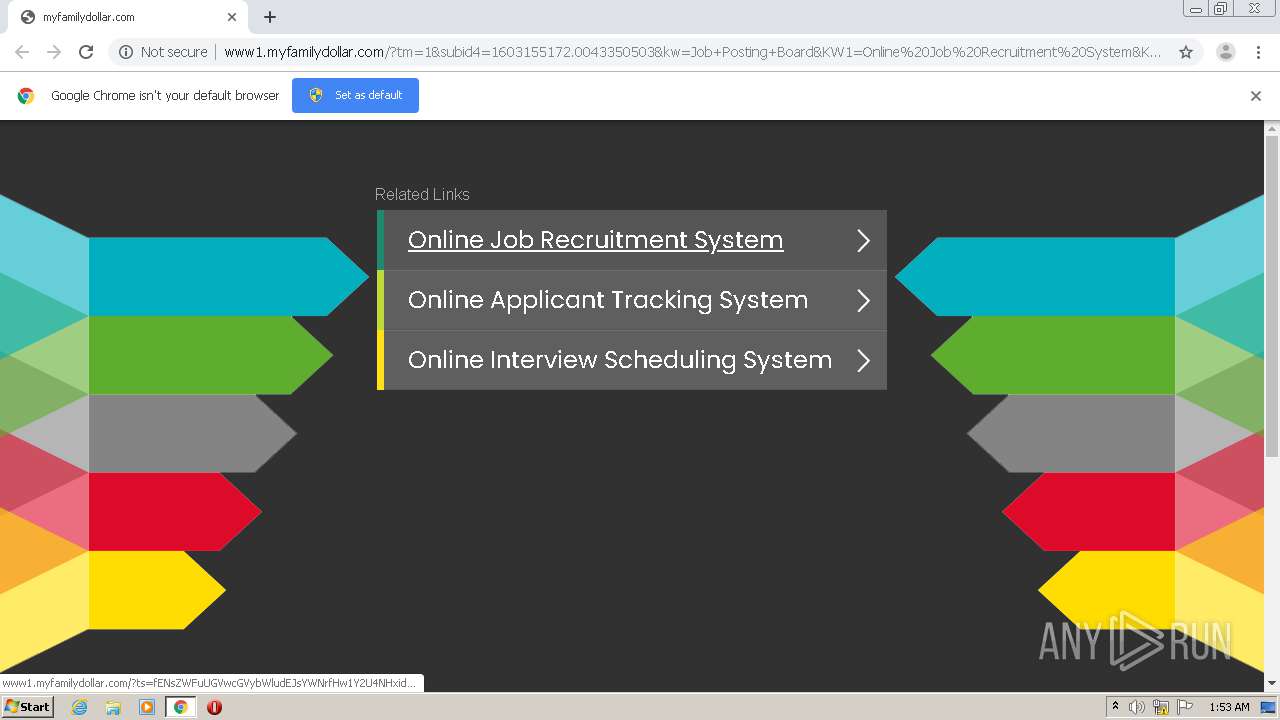
4008 | chrome.exe | GET | 200 | 13.248.148.254:80 | http://www1.myfamilydollar.com/?tm=1&subid4=1603155172.0043350503&kw=Job+Posting+Board&KW1=Online%20Job%20Recruitment%20System&KW2=Online%20Applicant%20Tracking%20System&KW3=Online%20Interview%20Scheduling%20System&searchbox=0&domainname=0&backfill=0 | US | html | 6.03 Kb | malicious |
4008 | chrome.exe | GET | 200 | 13.248.148.254:80 | http://www1.myfamilydollar.com/track.php?domain=myfamilydollar.com&toggle=browserjs&uid=MTYwMzE1NTE5OC42NDM4OjdjNTAwNzRjODViODc1ODBkODNmMzgxM2Y2ZWI5MjBiOTE1NWQ4YzJlZWZhMmNiNGExNDVhNDZkYjIzNjIxODc6NWY4ZTM0ZmU5ZDJiMQ%3D%3D | US | binary | 20 b | malicious |
4008 | chrome.exe | GET | 200 | 13.248.148.254:80 | http://www1.myfamilydollar.com/track.php?domain=myfamilydollar.com&caf=1&toggle=answercheck&answer=yes&uid=MTYwMzE1NTE5OC42NDM4OjdjNTAwNzRjODViODc1ODBkODNmMzgxM2Y2ZWI5MjBiOTE1NWQ4YzJlZWZhMmNiNGExNDVhNDZkYjIzNjIxODc6NWY4ZTM0ZmU5ZDJiMQ%3D%3D | US | binary | 20 b | malicious |
4008 | chrome.exe | GET | 200 | 45.56.79.23:80 | http://myfamilydollar.com/favicon.ico | US | image | 43 b | malicious |
4008 | chrome.exe | GET | 200 | 13.248.148.254:80 | http://www1.myfamilydollar.com/track.php?domain=myfamilydollar.com&toggle=browserjs&uid=MTYwMzE1NTE3My4yMzQyOjE0YzAzMTc0ZGIzMmMyNTJlZTNhOWVkZGZkZmM4YWIxNTRjNjVlMTc1OGVlODc4ZDg1MWUwZDIzYTA4MGZiNTY6NWY4ZTM0ZTUzOTJiYQ%3D%3D | US | binary | 20 b | malicious |
4008 | chrome.exe | GET | 200 | 13.248.148.254:80 | http://www1.myfamilydollar.com/track.php?domain=myfamilydollar.com&caf=1&toggle=answercheck&answer=yes&uid=MTYwMzE1NTE3My4yMzQyOjE0YzAzMTc0ZGIzMmMyNTJlZTNhOWVkZGZkZmM4YWIxNTRjNjVlMTc1OGVlODc4ZDg1MWUwZDIzYTA4MGZiNTY6NWY4ZTM0ZTUzOTJiYQ%3D%3D | US | binary | 20 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4008 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 45.56.79.23:443 | myfamilydollar.com | Linode, LLC | US | malicious |
4008 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 45.56.79.23:80 | myfamilydollar.com | Linode, LLC | US | malicious |
— | — | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 172.217.21.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 13.248.148.254:80 | www1.myfamilydollar.com | — | US | malicious |
4008 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 52.222.177.27:80 | d1lxhc4jvstzrp.cloudfront.net | Amazon.com, Inc. | US | unknown |
4008 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
myfamilydollar.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www1.myfamilydollar.com |
| malicious |
d1lxhc4jvstzrp.cloudfront.net |
| shared |
fonts.googleapis.com |
| whitelisted |
c.parkingcrew.net |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |