| File name: | terminal.exe |
| Full analysis: | https://app.any.run/tasks/851b7653-70c8-4940-b22f-e4ce78cd44c8 |
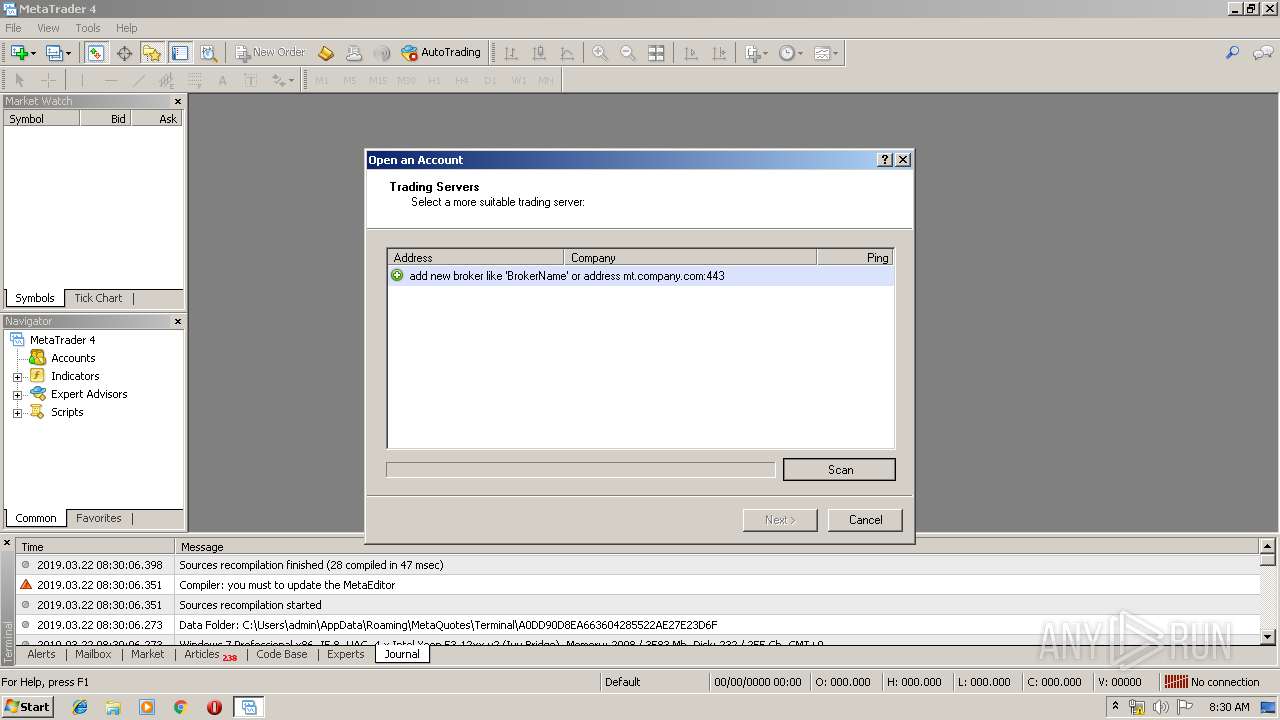
| Verdict: | Malicious activity |
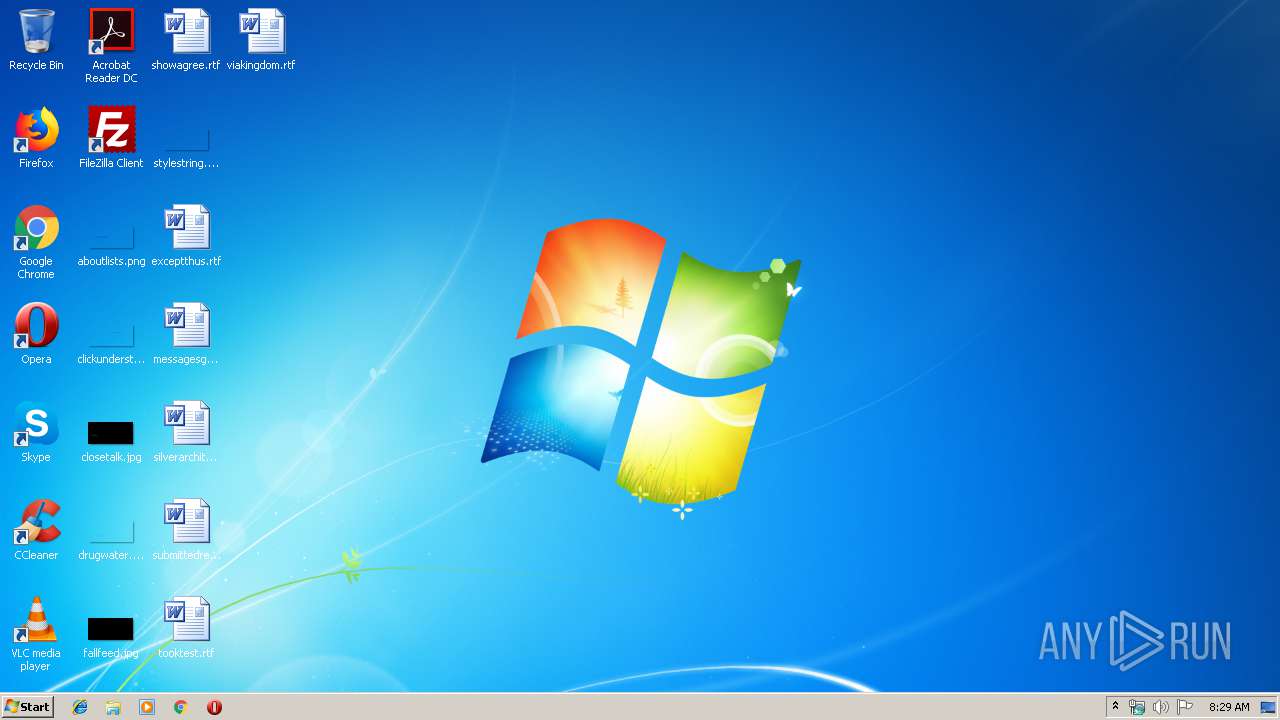
| Analysis date: | March 22, 2019, 08:29:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 25BCED5CD44321F40DBDC4A5F51ACF3E |
| SHA1: | C8BE86415E2D5FE41DCACCDE0338AA4848E0079E |
| SHA256: | AC5CC902DFFD7F29EE4F0751C87736567B9E71D459061DF3C6B83644BDD45E8B |
| SSDEEP: | 196608:1lCEwewwQ6qFlXL2AglxJFxHQkTQmJqJd9/bwGvVFlyZXp34dN8Yp:1lEwulXL27DJLfqr9rvVipXYp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- terminal.exe (PID: 2172)
Reads internet explorer settings
- terminal.exe (PID: 2172)
Changes IE settings (feature browser emulation)
- terminal.exe (PID: 2172)
Creates files in the user directory
- terminal.exe (PID: 2172)
INFO
Reads settings of System Certificates
- terminal.exe (PID: 2172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1970:06:10 22:54:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 6508032 |
| InitializedDataSize: | 12630016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1136fa0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.1170 |
| ProductVersionNumber: | 4.0.0.1170 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | https://www.metaquotes.net |
| CompanyName: | MetaQuotes Software Corp. |
| FileDescription: | MetaTrader |
| FileVersion: | 4.0.0.1170 |
| InternalName: | MetaTrader |
| LegalCopyright: | © 2000-2018, MetaQuotes Software Corp. |
| LegalTrademarks: | MetaTrader® |
| ProductName: | MetaTrader |
| ProductVersion: | 4.0.0.1170 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-1970 21:54:08 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | https://www.metaquotes.net |
| CompanyName: | MetaQuotes Software Corp. |
| FileDescription: | MetaTrader |
| FileVersion: | 4.0.0.1170 |
| InternalName: | MetaTrader |
| LegalCopyright: | © 2000-2018, MetaQuotes Software Corp. |
| LegalTrademarks: | MetaTrader® |
| ProductName: | MetaTrader |
| ProductVersion: | 4.0.0.1170 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 10-Jun-1970 21:54:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00634CEC | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.rdata | 0x00636000 | 0x000FA346 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.data | 0x00731000 | 0x000B252C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
_RDATA | 0x007E4000 | 0x000005E0 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.cod0 | 0x007E5000 | 0x005B1652 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.cod1 | 0x00D97000 | 0x00C1A650 | 0x00C1A800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.98141 |
.reloc | 0x019B2000 | 0x000005D4 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.42233 |
.rsrc | 0x019B3000 | 0x00A8265E | 0x00127200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.53193 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18261 | 2150 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.62163 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.79688 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.31633 | 7336 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.94507 | 3240 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 2.81563 | 872 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 0 | 52 | Latin 1 / Western European | UNKNOWN | RT_STRING |
8 | 5.26905 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 2.78683 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 3.65502 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
Total processes
30
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
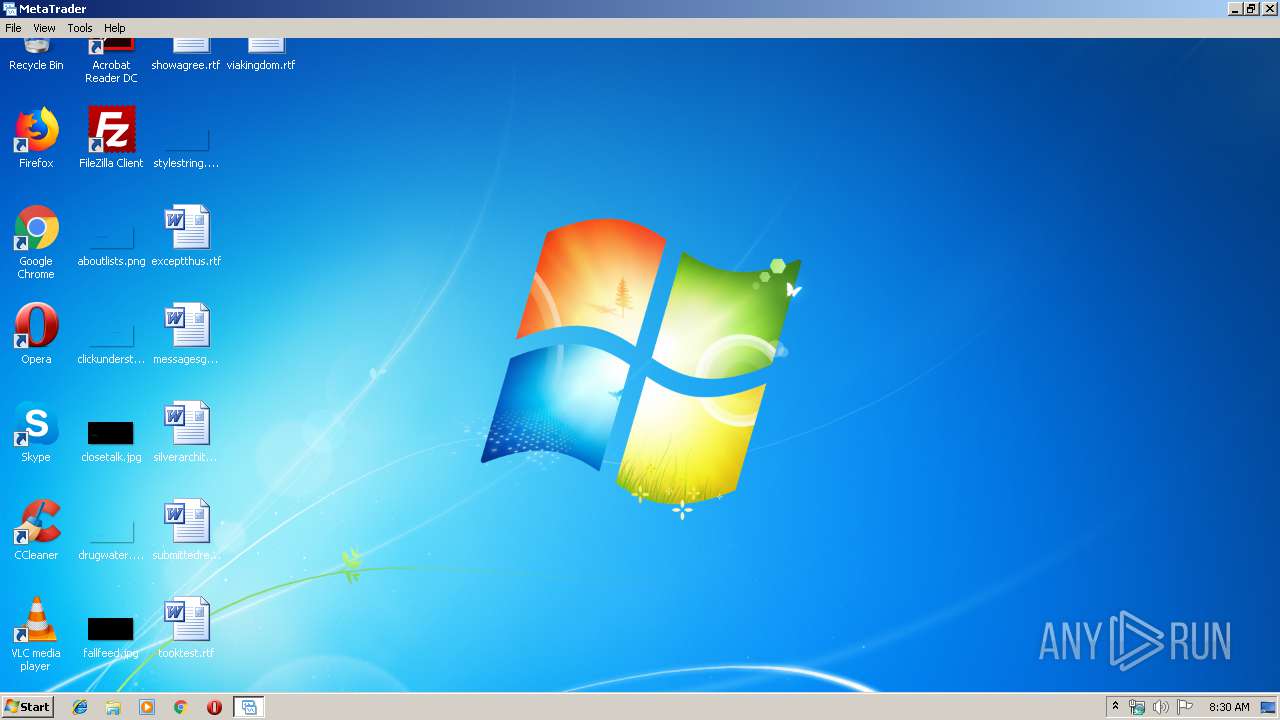
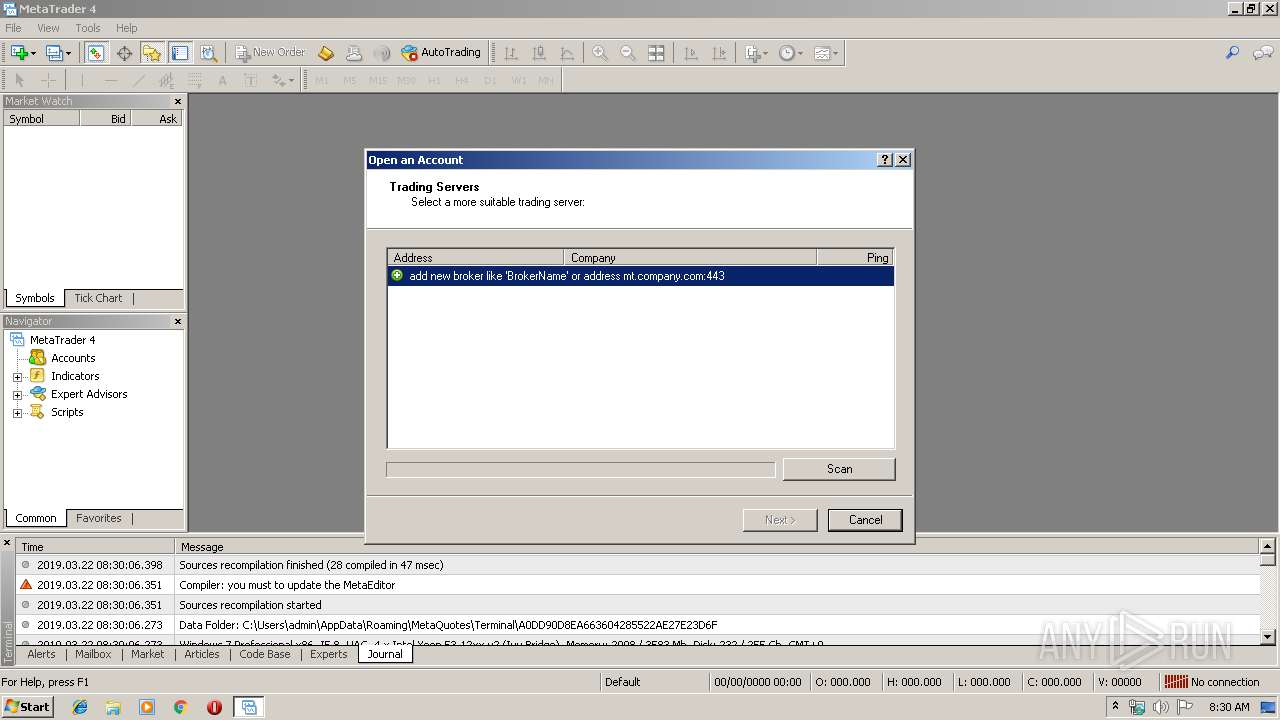
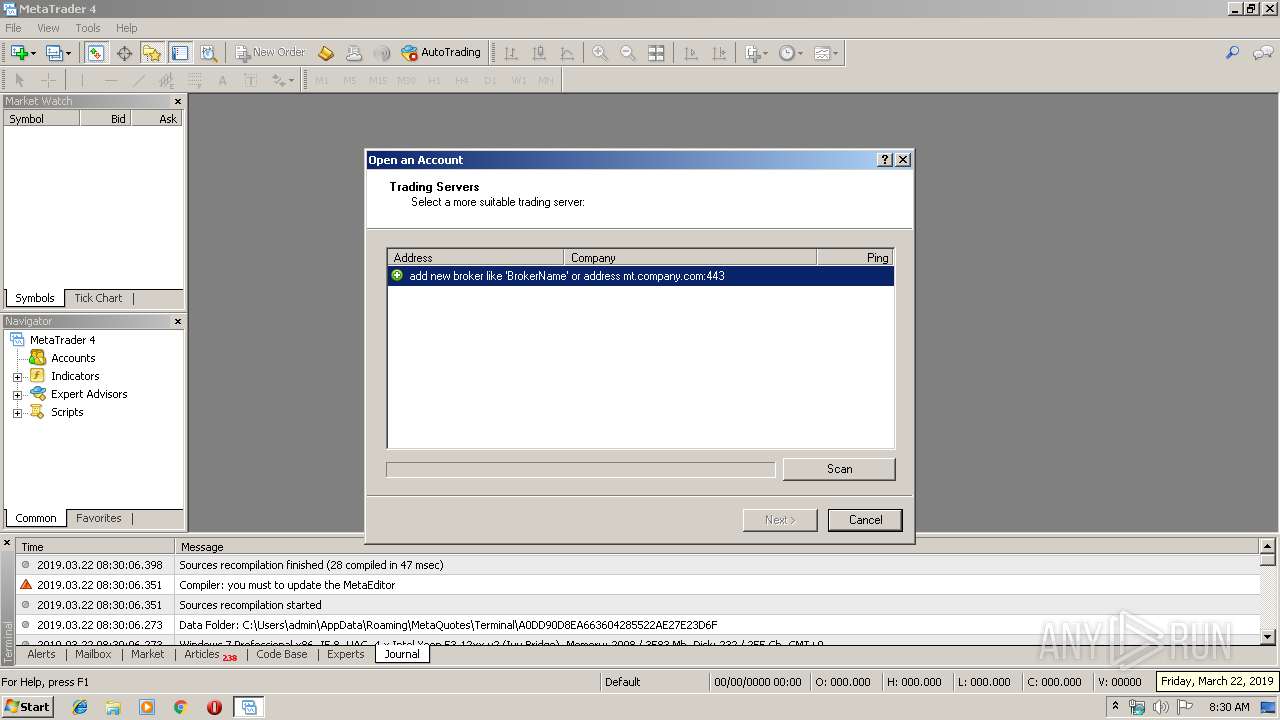
| 2172 | "C:\Users\admin\AppData\Local\Temp\terminal.exe" | C:\Users\admin\AppData\Local\Temp\terminal.exe | explorer.exe | ||||||||||||
User: admin Company: MetaQuotes Software Corp. Integrity Level: MEDIUM Description: MetaTrader Exit code: 0 Version: 4.0.0.1170 Modules
| |||||||||||||||
Total events
83
Read events
66
Write events
17
Delete events
0
Modification events
| (PID) Process: | (2172) terminal.exe | Key: | HKEY_CURRENT_USER\Software\MetaQuotes Software |
| Operation: | write | Name: | ID |
Value: 7C2125A2-5872-T-190322 | |||
| (PID) Process: | (2172) terminal.exe | Key: | HKEY_CURRENT_USER\Software\MetaQuotes Software |
| Operation: | write | Name: | Install.Time |
Value: 1553243406 | |||
| (PID) Process: | (2172) terminal.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | terminal.exe |
Value: 8000 | |||
| (PID) Process: | (2172) terminal.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2172) terminal.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2172) terminal.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
8
Text files
155
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\mql4.zip | — | |
MD5:— | SHA256:— | |||
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\config\terminal.ini | text | |
MD5:9F8A94E170DAAC4481BCED95A016FFDF | SHA256:0085F8B127E6D8E9D07DAB1B61602F3F64540AFCE1E2B20E9F041F2D6154BC95 | |||
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\MQL4\Include\Arrays\ArrayInt.mqh | text | |
MD5:B9A328A4E38A5152B93FE25C64C1DFBC | SHA256:7BB3A442630411746D43D4EC0DF18B1B2B3D56965CF29876228375E391997DEA | |||
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\templates\StrategyTester.htm | html | |
MD5:26B2D851BC754CE6F01893DF04C64090 | SHA256:E68AF34BA74F7AEFD077FE6147C6E2F40F91B90188E000656CAB533FFB419A04 | |||
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\MQL4\Include\Arrays\ArrayFloat.mqh | text | |
MD5:82EFD278D622ABF0AC3AFB98C1900D4B | SHA256:331E4B985BDFC45674F67A6EEADBA3848913359132DBCCE986052C7EF6A04F0D | |||
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\MQL4\Include\Arrays\ArrayDouble.mqh | text | |
MD5:1CA1A9D3122D67AC8FB7644C3016C554 | SHA256:C4F2C50FBB3BAF347C2C0C41E6F9729C4709273E0B46295F6A490B2E7BECB0F5 | |||
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\MQL4\Include\Arrays\ArrayLong.mqh | text | |
MD5:7FD0D8764BFD83E848593977B3F3ACC6 | SHA256:AD4F1F2315B49E1196209E1AB7EE6E47A952AB3CDE60E21C574ACF1D0FD75ED6 | |||
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\MQL4\Include\Arrays\TreeNode.mqh | text | |
MD5:648FC969B496E280B0BB86F007F902F0 | SHA256:67D7B2CCB7E9283CCA9DEB3603A24795D47F1396EA8734AB82D902B9C135DCDC | |||
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\MQL4\Include\Arrays\ArrayChar.mqh | text | |
MD5:A6D32CEDC7FD7E24D82F36039A1220AC | SHA256:595C4CB02C29CE99495ABB37E1BC93CB9384B05CE1A089A3ADE7E90090C27AF5 | |||
| 2172 | terminal.exe | C:\Users\admin\AppData\Roaming\MetaQuotes\Terminal\A0DD90D8EA663604285522AE27E23D6F\MQL4\Include\Arrays\ArrayObj.mqh | text | |
MD5:F8D64B176F2D22607BA4B0F86702EB66 | SHA256:A56CF708CAEFBB655A3275DAEAC312121AED8EA1C21811B079458433C70CCE28 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2172 | terminal.exe | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
2172 | terminal.exe | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | unknown | der | 969 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2172 | terminal.exe | 2.16.186.56:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2172 | terminal.exe | 78.140.180.43:443 | download.mql5.com | Webzilla B.V. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.mql5.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |