| File name: | autoruns.exe |
| Full analysis: | https://app.any.run/tasks/f9b1d83e-a943-482b-b783-6e08f02cae0d |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 19:59:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C8EDFCEAA2CDD1BC8BBE33C3FA18FBB5 |
| SHA1: | 13F082ECD6A3AC8A9BDB00D0115625D210B6AFC5 |
| SHA256: | AC5AAA2220DC5FF0DCB9786345E7888C725AE471FF730E6584E26524980EC14B |
| SSDEEP: | 49152:cqLkUum23pAgrYeogEWPpmQ4jPO69gd4QG7MaddUahD3n:cqLkUum2ZAMH4jPO69I4LM+ |
MALICIOUS
Loads the Task Scheduler COM API
- autoruns.exe (PID: 1056)
SUSPICIOUS
Reads the computer name
- autoruns.exe (PID: 1056)
Checks supported languages
- autoruns.exe (PID: 1056)
Reads default file associations for system extensions
- autoruns.exe (PID: 1056)
Reads Environment values
- autoruns.exe (PID: 1056)
INFO
Checks supported languages
- chrome.exe (PID: 3520)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 3800)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 396)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 3500)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 2404)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 1364)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 416)
- chrome.exe (PID: 1072)
Manual execution by user
- chrome.exe (PID: 3520)
Reads the computer name
- chrome.exe (PID: 3520)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 2412)
Reads settings of System Certificates
- autoruns.exe (PID: 1056)
- chrome.exe (PID: 2628)
Reads the hosts file
- chrome.exe (PID: 3520)
- chrome.exe (PID: 2628)
Application launched itself
- chrome.exe (PID: 3520)
Reads Microsoft Office registry keys
- autoruns.exe (PID: 1056)
Checks Windows Trust Settings
- autoruns.exe (PID: 1056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| ProductVersion: | 14.07 |
|---|---|
| ProductName: | Sysinternals autoruns |
| OriginalFileName: | autoruns.exe |
| LegalCopyright: | Copyright (C) 2002-2021 Mark Russinovich |
| InternalName: | Sysinternals Autoruns |
| FileVersion: | 14.07 |
| FileDescription: | Autostart program viewer |
| CompanyName: | Sysinternals - www.sysinternals.com |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 14.0.7.0 |
| FileVersionNumber: | 14.0.7.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0xd334e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1188864 |
| CodeSize: | 1307648 |
| LinkerVersion: | 14.29 |
| PEType: | PE32 |
| TimeStamp: | 2021:12:11 10:23:15+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2021 09:23:15 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Autostart program viewer |
| FileVersion: | 14.07 |
| InternalName: | Sysinternals Autoruns |
| LegalCopyright: | Copyright (C) 2002-2021 Mark Russinovich |
| OriginalFilename: | autoruns.exe |
| ProductName: | Sysinternals autoruns |
| ProductVersion: | 14.07 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 11-Dec-2021 09:23:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0013F3C6 | 0x0013F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50463 |
.rdata | 0x00141000 | 0x0004C332 | 0x0004C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.07326 |
.data | 0x0018E000 | 0x0000A5A8 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.29377 |
.detourc\x886 | 0x00199000 | 0x00003688 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.2491 |
.detourd$ | 0x0019D000 | 0x00000024 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.160329 |
.rsrc | 0x0019E000 | 0x000B5918 | 0x000B5A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.50782 |
.reloc | 0x00254000 | 0x0001259C | 0x00012600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.66525 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19312 | 2033 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.29011 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 5.13304 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.87852 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.74127 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 4.62992 | 38056 | UNKNOWN | English - United States | RT_ICON |
7 | 4.58855 | 67624 | UNKNOWN | English - United States | RT_ICON |
8 | 4.52782 | 152104 | UNKNOWN | English - United States | RT_ICON |
9 | 2.62625 | 138 | UNKNOWN | English - United States | RT_STRING |
10 | 1.95558 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
59
Monitored processes
25
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
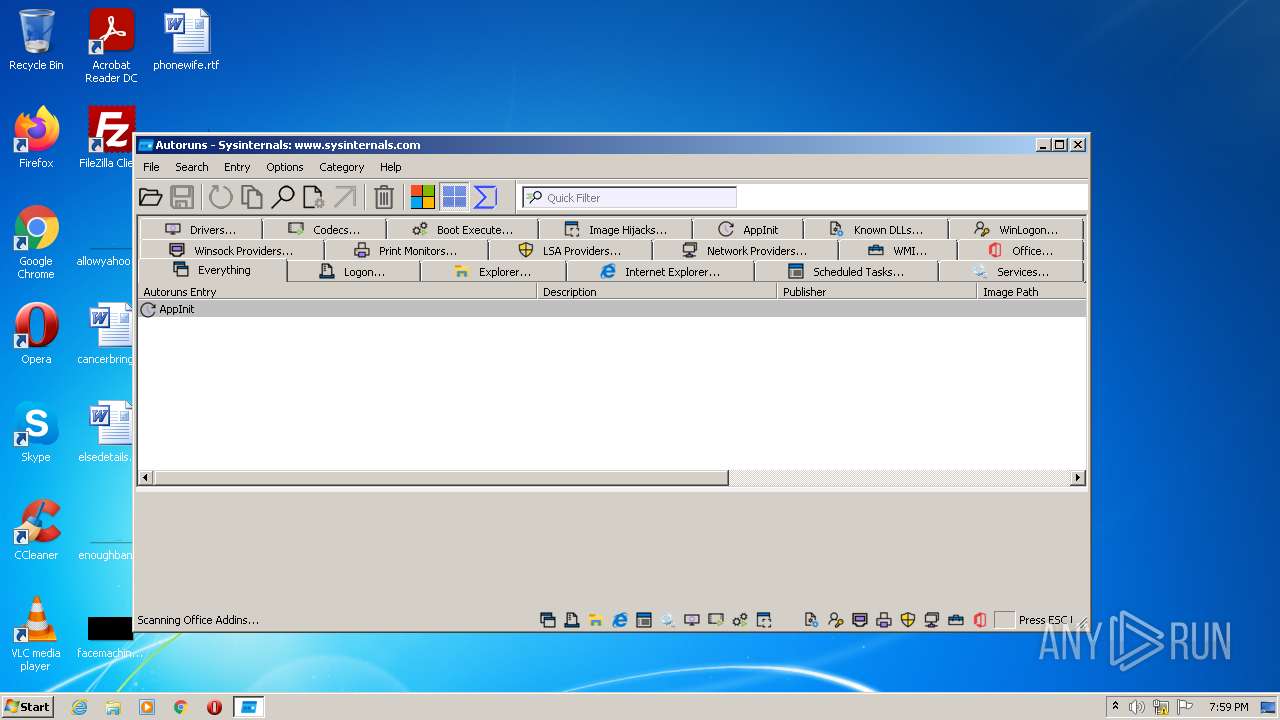
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,16345998946768637625,12054890115902344580,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2660 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,16345998946768637625,12054890115902344580,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4516 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1056 | "C:\Users\admin\AppData\Local\Temp\autoruns.exe" | C:\Users\admin\AppData\Local\Temp\autoruns.exe | Explorer.EXE | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Autostart program viewer Exit code: 0 Version: 14.07 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,16345998946768637625,12054890115902344580,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,16345998946768637625,12054890115902344580,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,16345998946768637625,12054890115902344580,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2468 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,16345998946768637625,12054890115902344580,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2408 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,16345998946768637625,12054890115902344580,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1076 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e7ed988,0x6e7ed998,0x6e7ed9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,16345998946768637625,12054890115902344580,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2460 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
61 505
Read events
61 373
Write events
132
Delete events
0
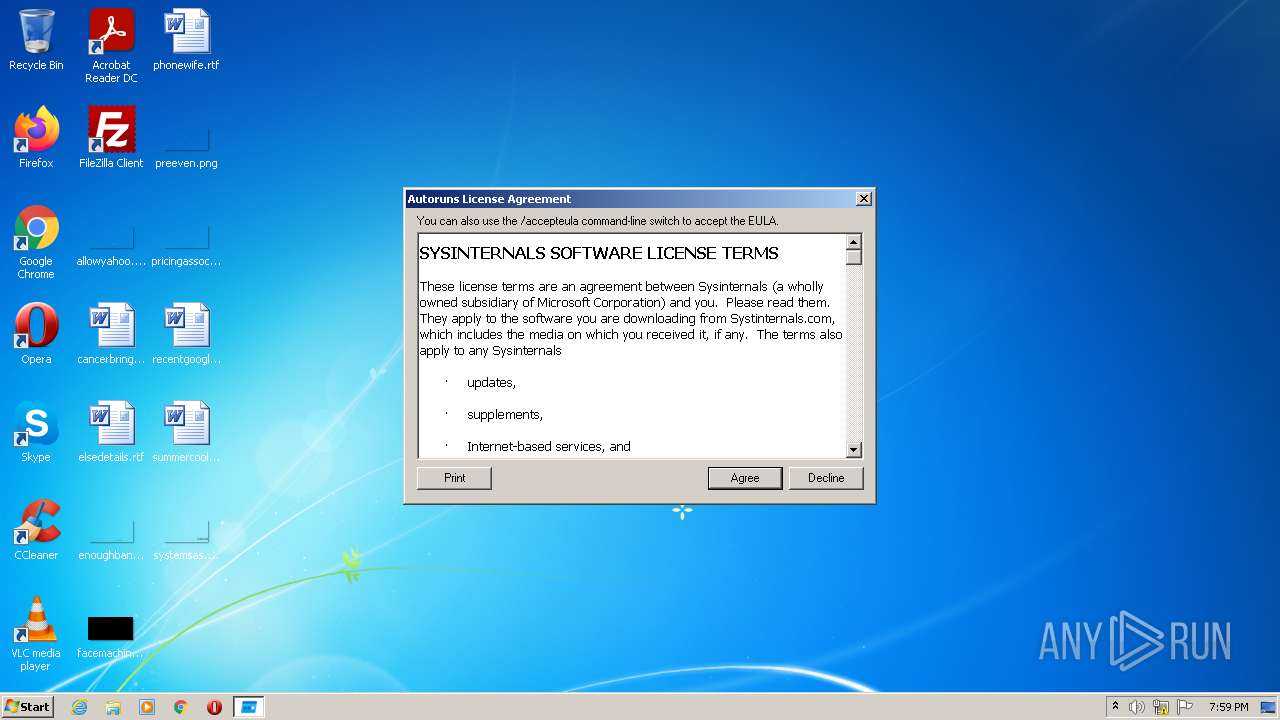
Modification events
| (PID) Process: | (1056) autoruns.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\Autoruns |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (1056) autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1056) autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wshtcpip.dll,-60100 |
Value: MSAFD Tcpip [TCP/IP] | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61E1D639-DC0.pma | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF119bfe.TMP | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF119d85.TMP | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF119e31.TMP | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF119ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
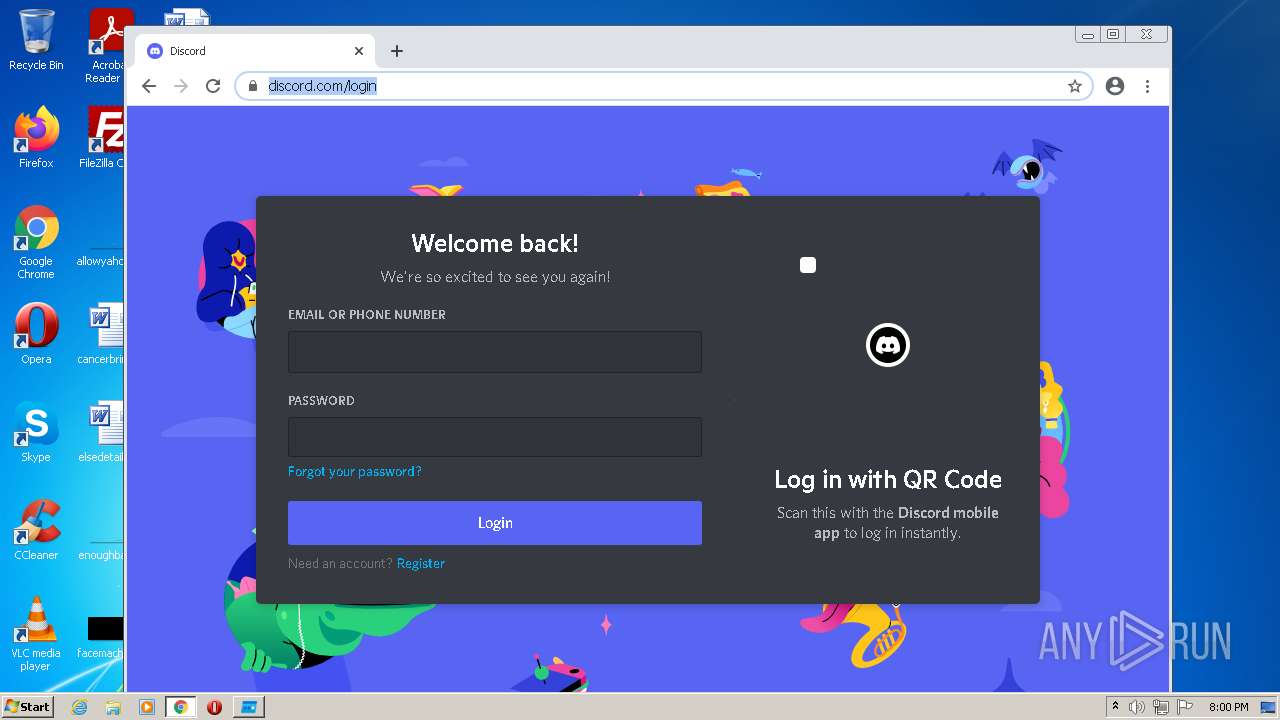
HTTP(S) requests
13
TCP/UDP connections
101
DNS requests
56
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 593 b | whitelisted |
1056 | autoruns.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | RU | der | 555 b | whitelisted |
1056 | autoruns.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | der | 564 b | whitelisted |
1056 | autoruns.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | RU | der | 530 b | whitelisted |
1056 | autoruns.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | RU | der | 767 b | whitelisted |
1056 | autoruns.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | RU | der | 824 b | whitelisted |
1056 | autoruns.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8cbd60462729d553 | US | compressed | 4.70 Kb | whitelisted |
1056 | autoruns.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/certs/Microsoft%20Development%20Root%20Certificate%20Authority%202014.crt | unknown | der | 1.51 Kb | whitelisted |
1056 | autoruns.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | RU | der | 519 b | whitelisted |
— | — | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | text | 37 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1056 | autoruns.exe | 178.18.231.171:80 | crl.microsoft.com | Peering Ltd | RU | suspicious |
1056 | autoruns.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
2628 | chrome.exe | 142.250.185.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 142.250.185.77:443 | accounts.google.com | Google Inc. | US | suspicious |
2628 | chrome.exe | 142.250.185.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 142.250.186.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 142.250.185.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 31.13.84.4:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2628 | chrome.exe | 104.20.185.68:443 | geolocation.onetrust.com | Cloudflare Inc | US | shared |
2628 | chrome.exe | 142.250.185.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
accounts.google.com |
| shared |
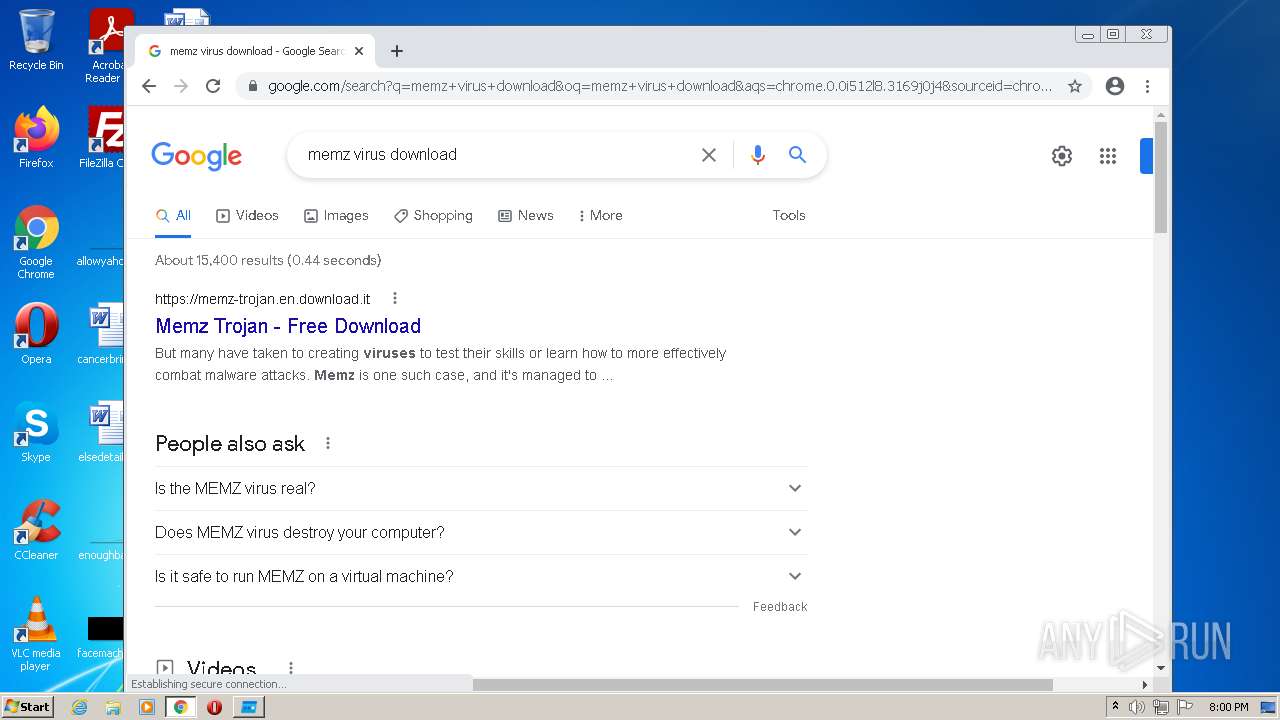
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |