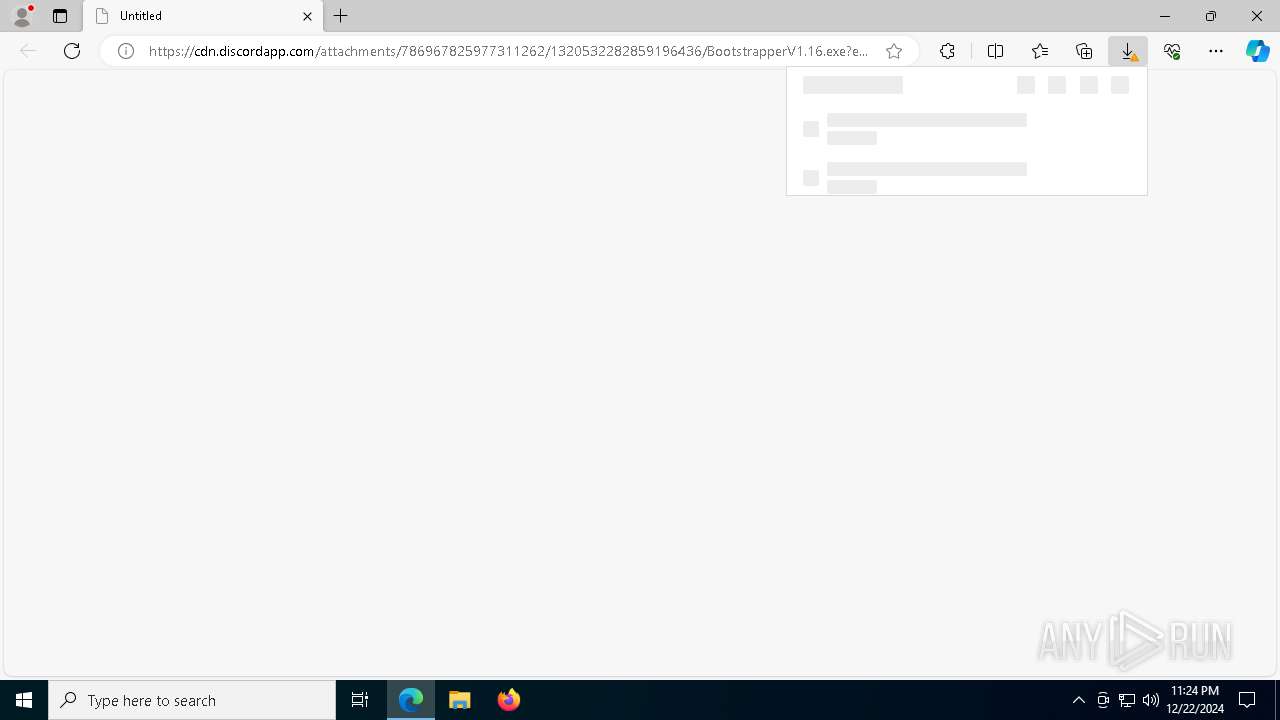
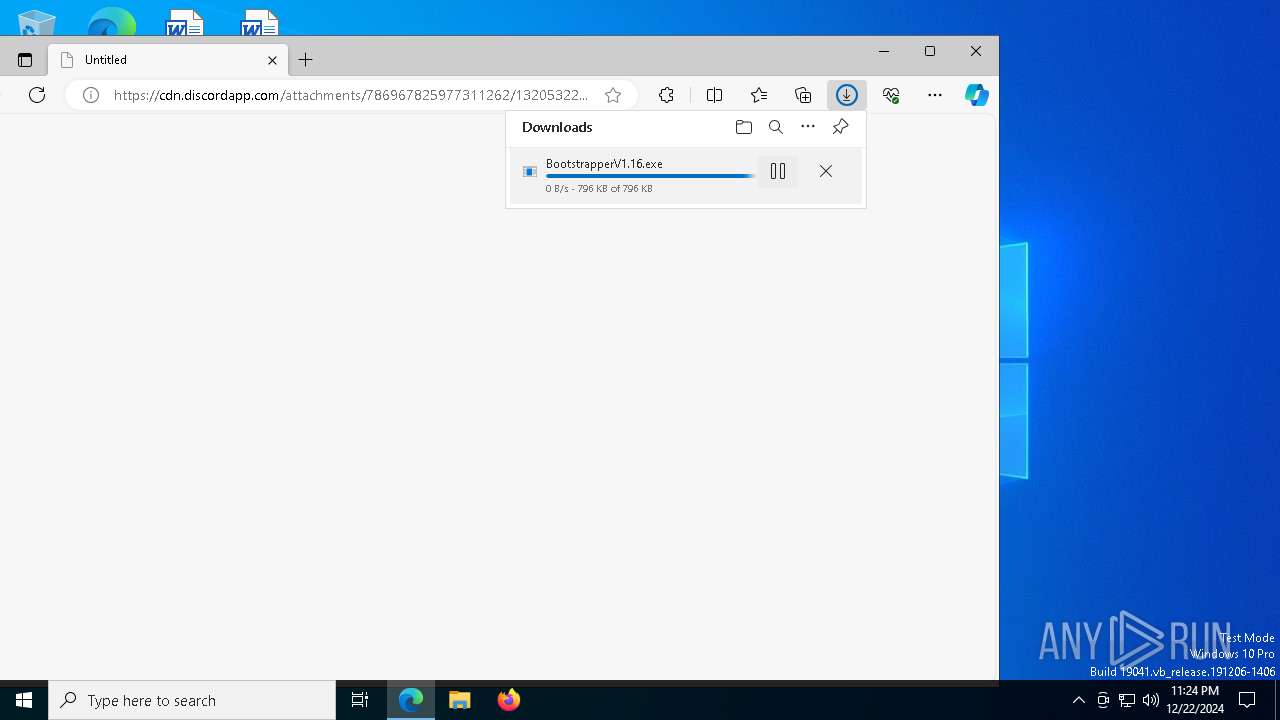
| URL: | https://cdn.discordapp.com/attachments/786967825977311262/1320532282859196436/BootstrapperV1.16.exe?ex=6769f106&is=67689f86&hm=955351810a47cef568990ffe2bdd3de6f64b5ef68457d7f9e472e9f3a68c748f& |
| Full analysis: | https://app.any.run/tasks/97a2ecb3-76f4-4d52-a253-632fce9f0391 |
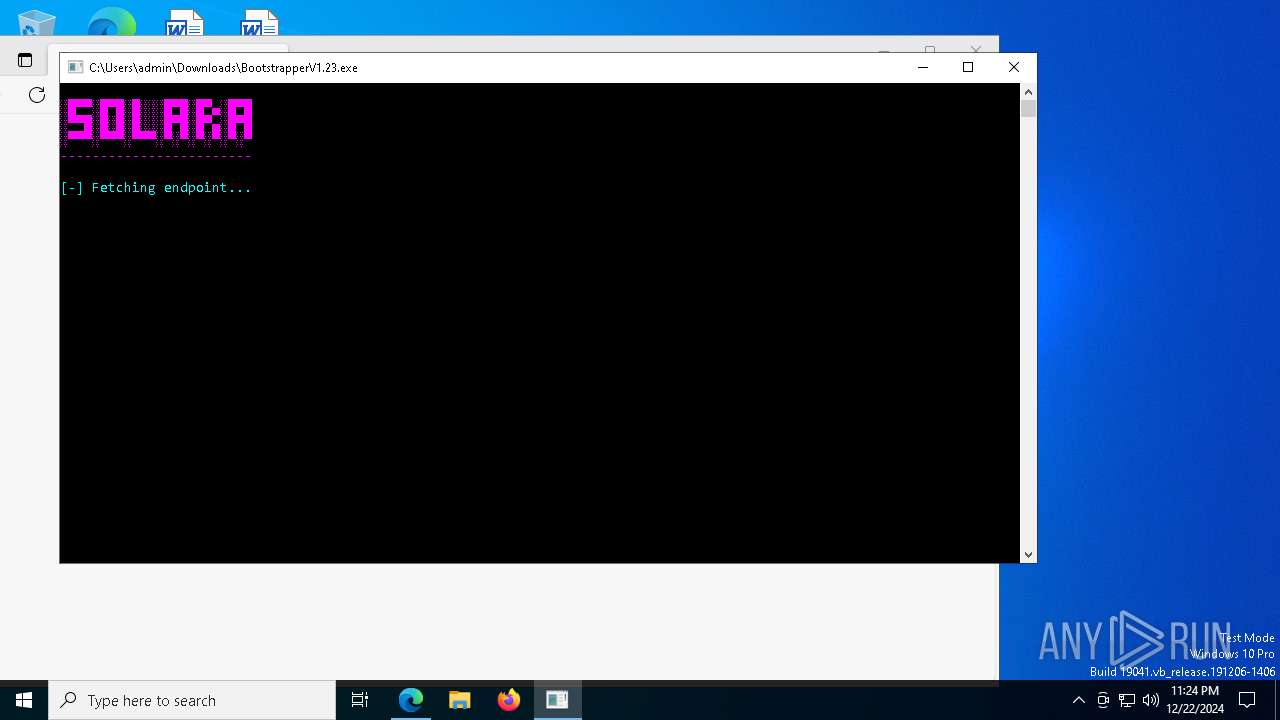
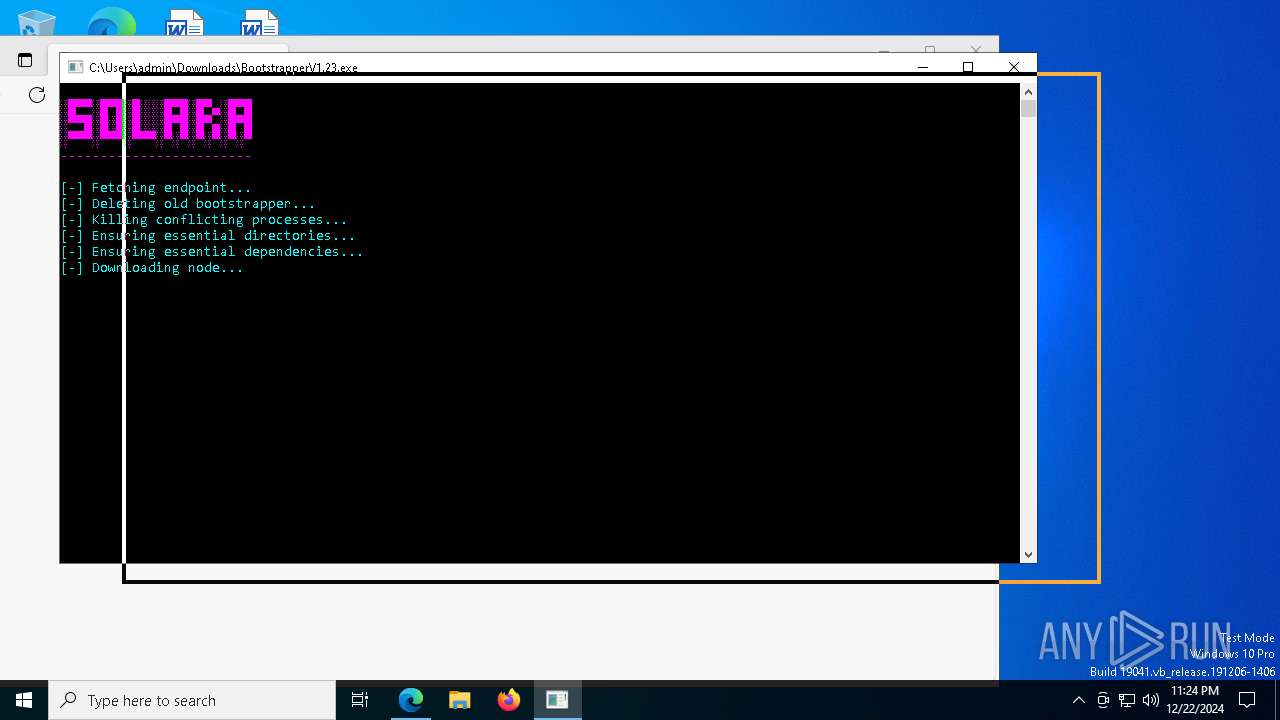
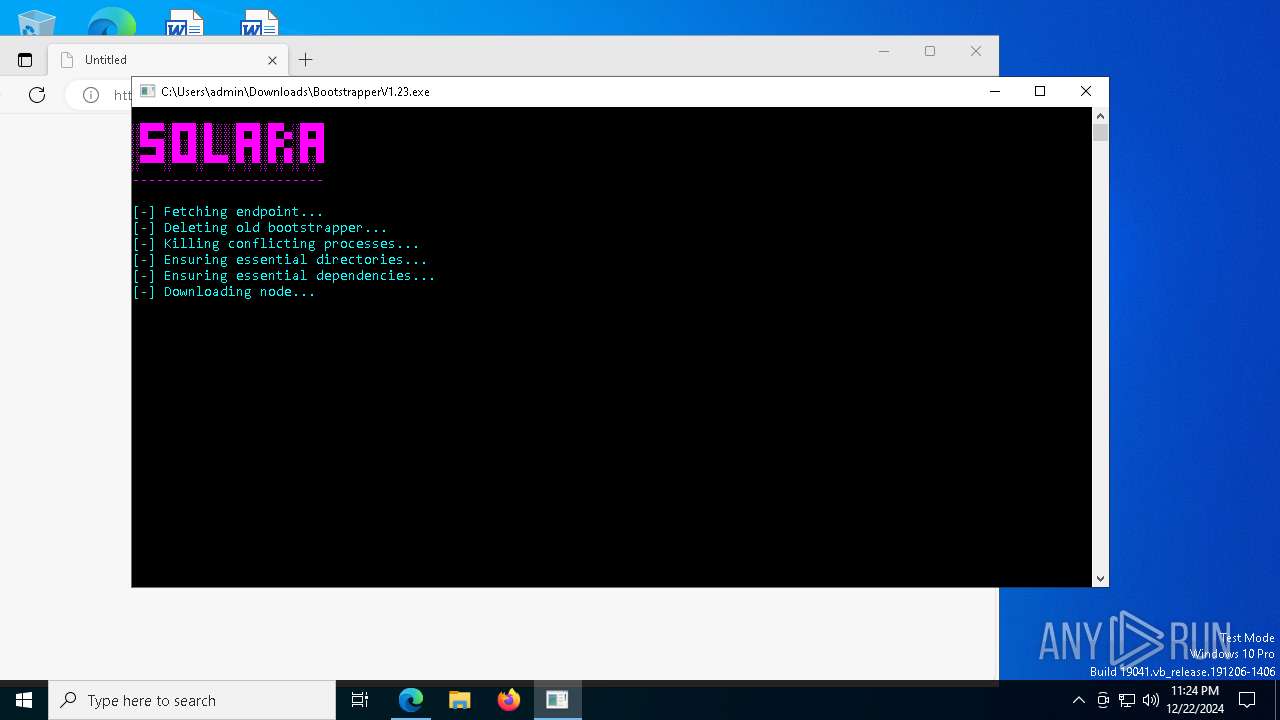
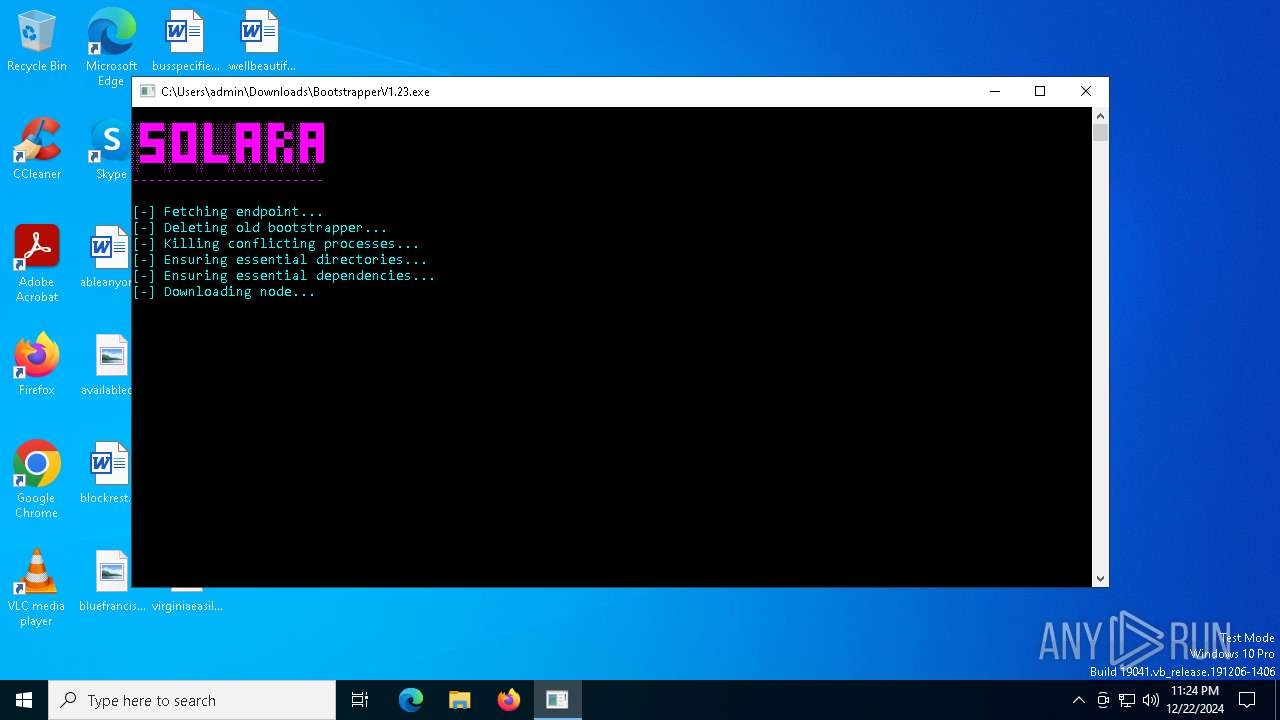
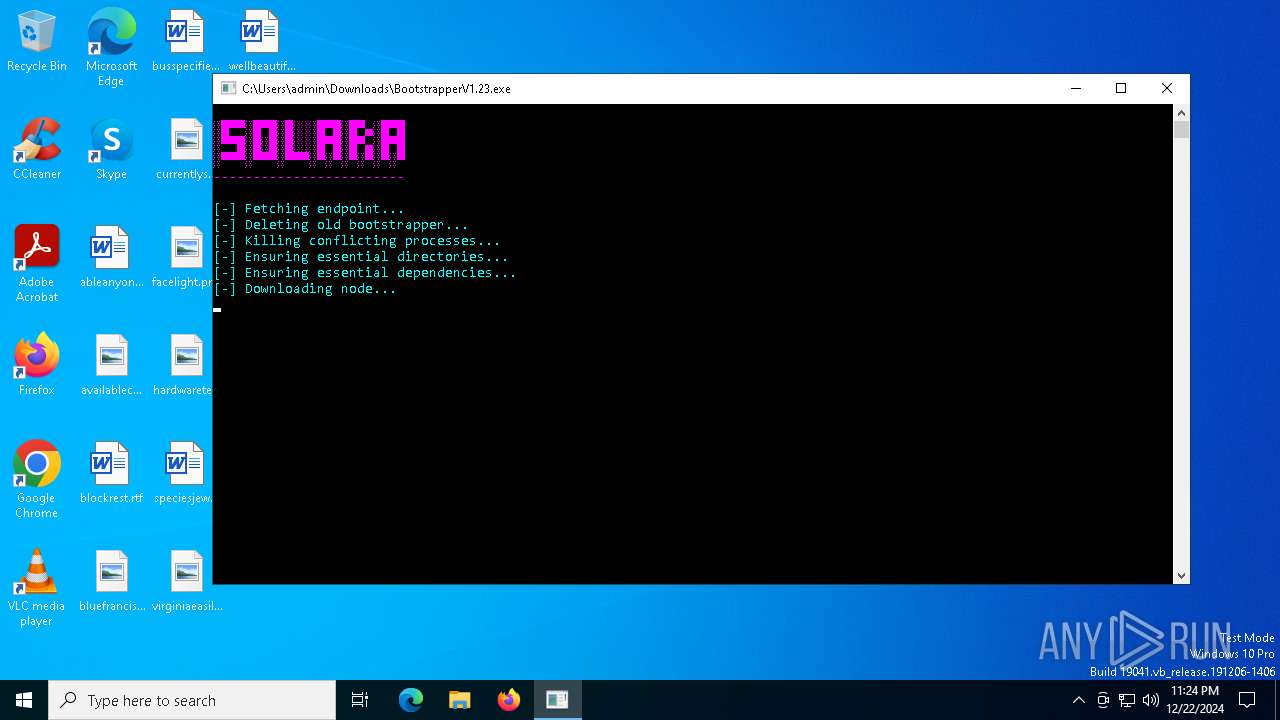
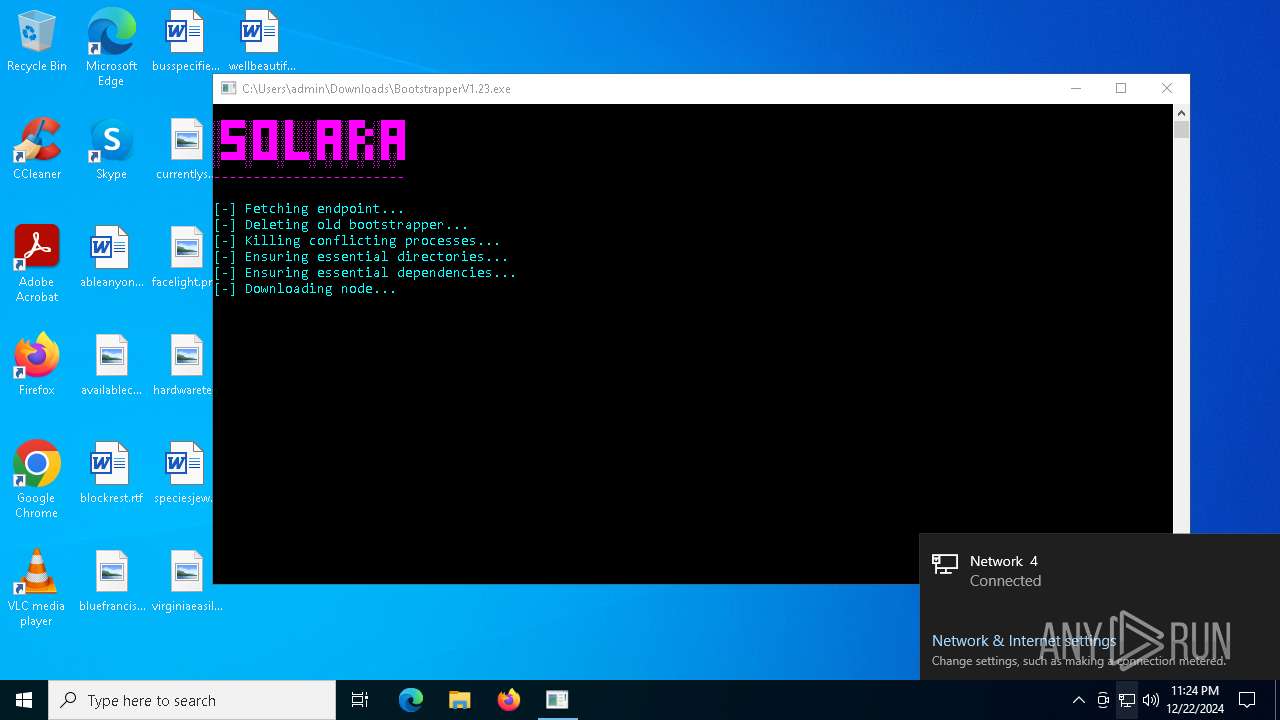
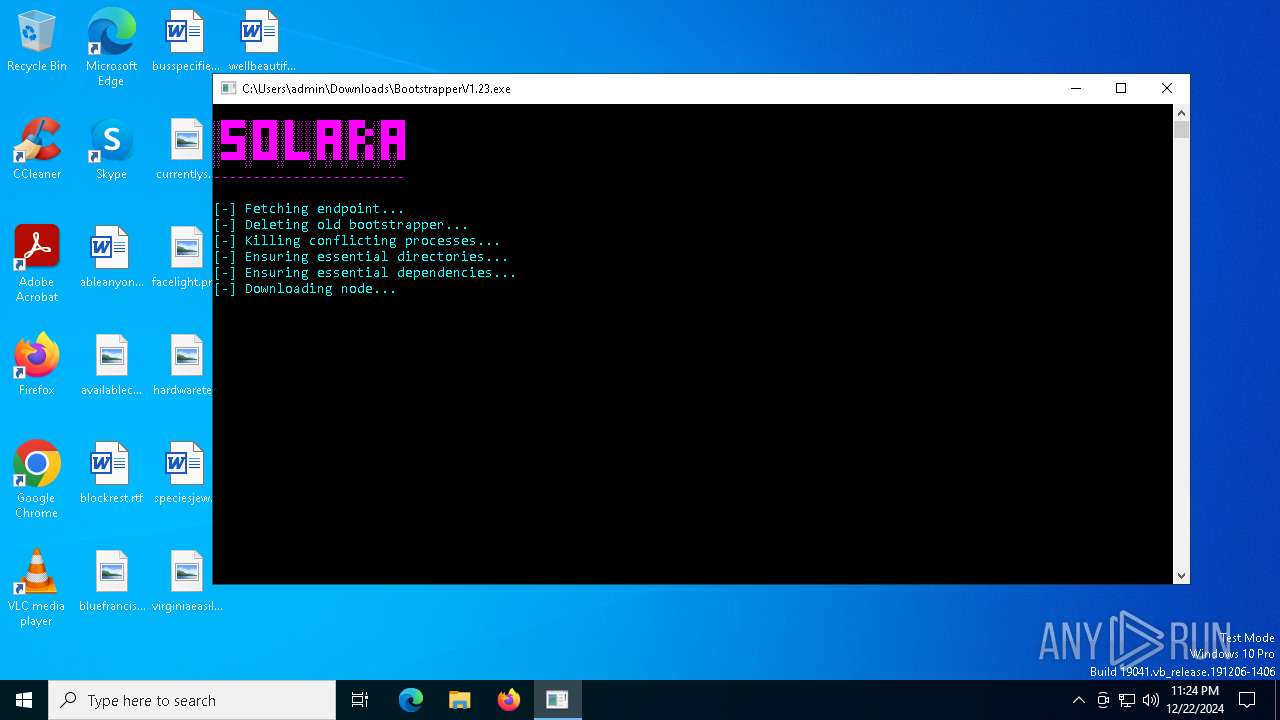
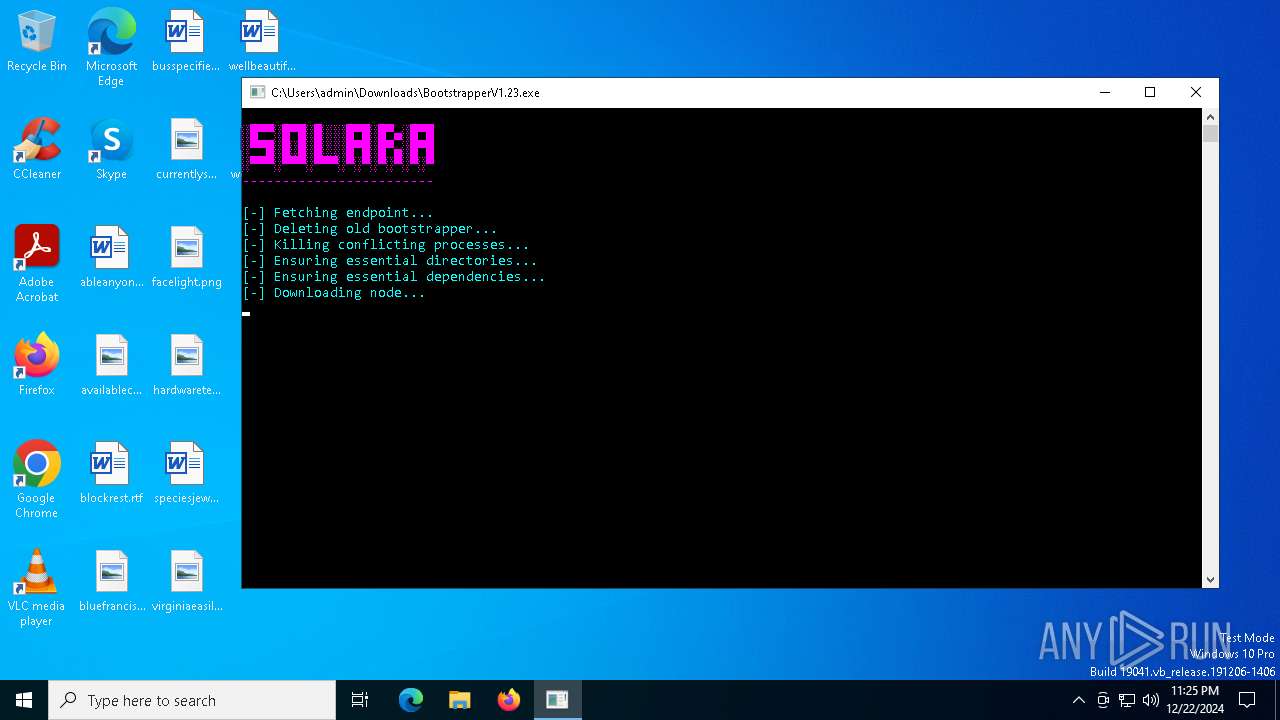
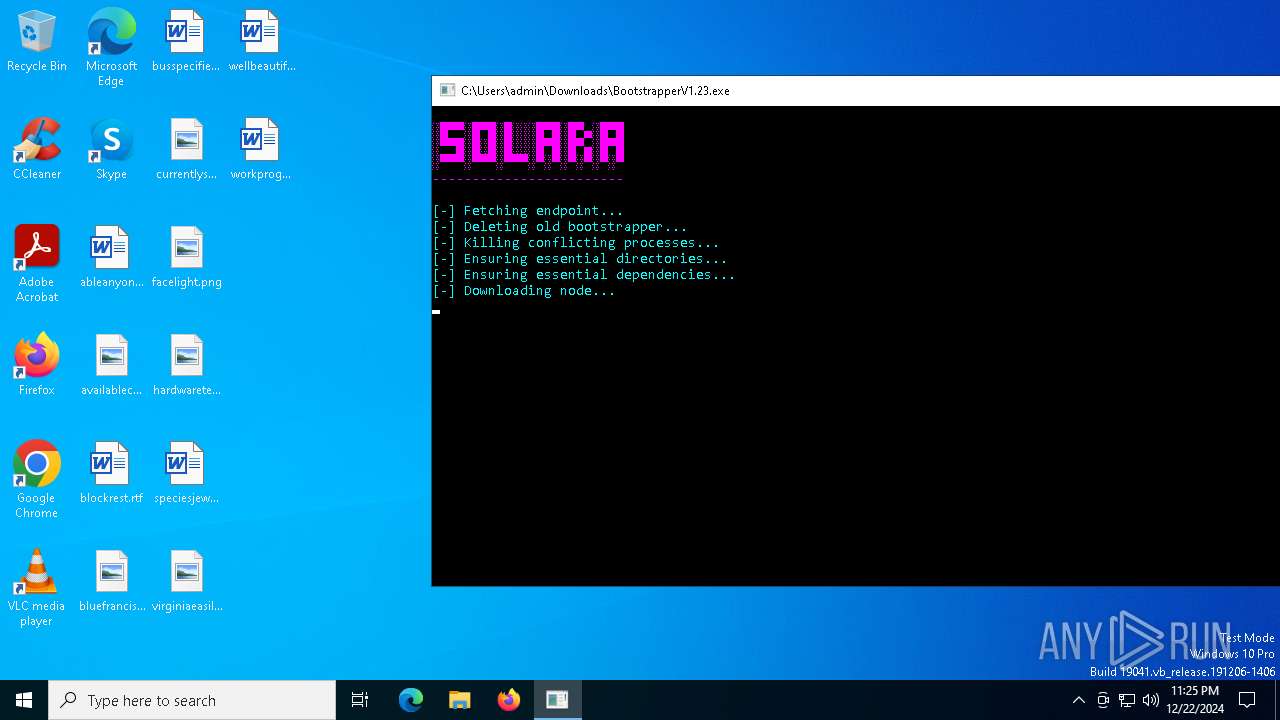
| Verdict: | Malicious activity |
| Analysis date: | December 22, 2024, 23:23:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0E36367792B4700A9423A160120EB5A6 |
| SHA1: | 30A6D950316495B70BCC42C64DD65635BED9D778 |
| SHA256: | AC57A62FD8D14D97F92AD49192B4BD5E3A4E325836A6375E855B96F85C0217EA |
| SSDEEP: | 3:N8cCWdy6//uFd5SOUw1vL3RpLUTL4/VMcINynMEv+Wcwm3QSw6E8D:2cry6XrM1LRl3/ScINynMMm3QWD |
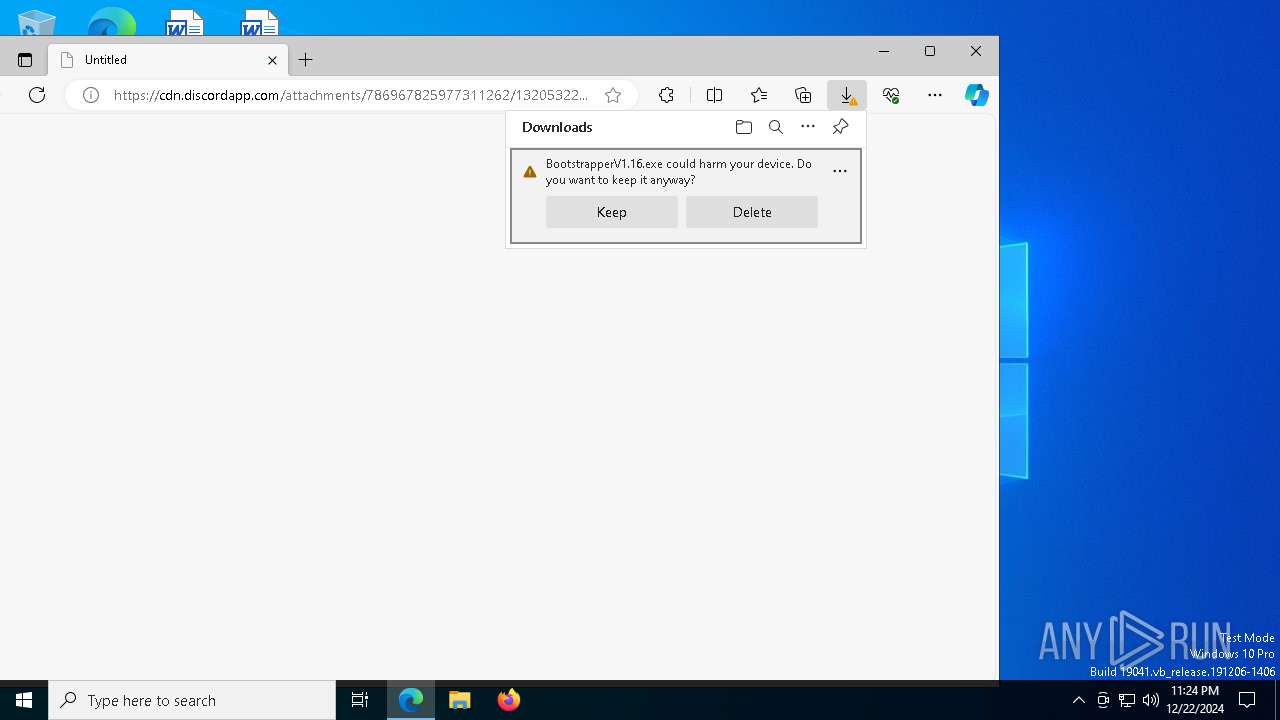
MALICIOUS
No malicious indicators.SUSPICIOUS
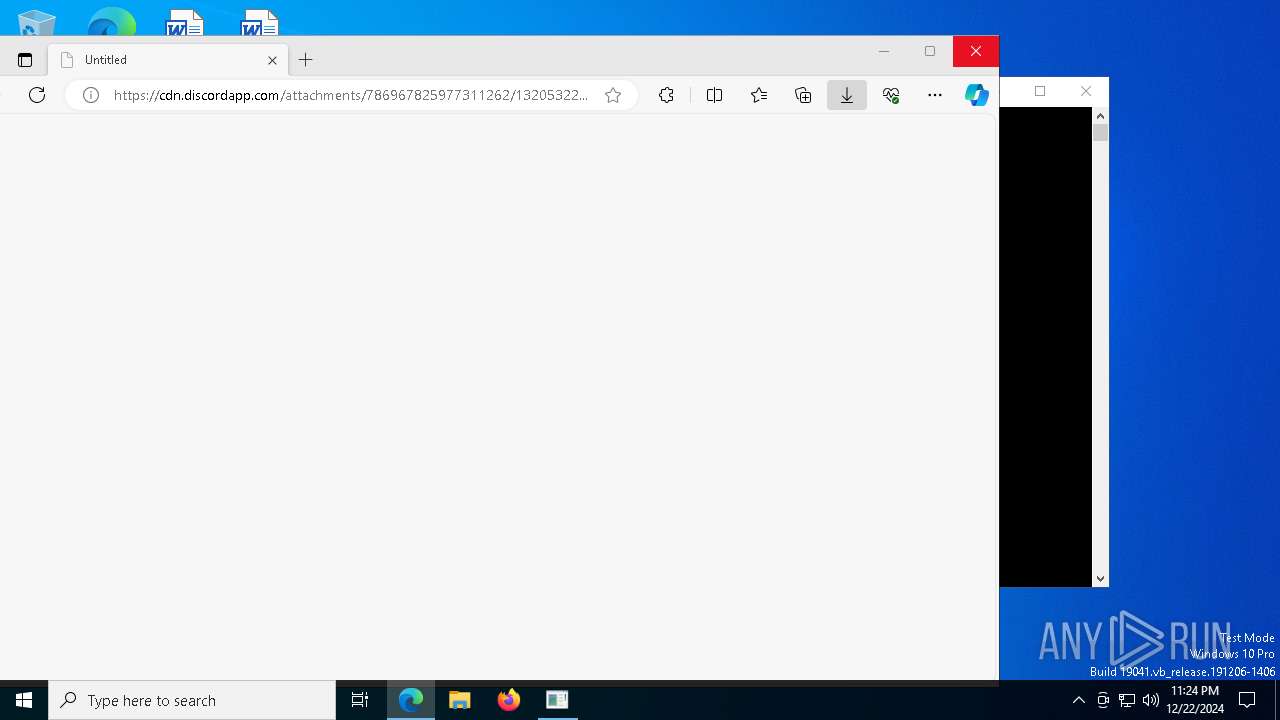
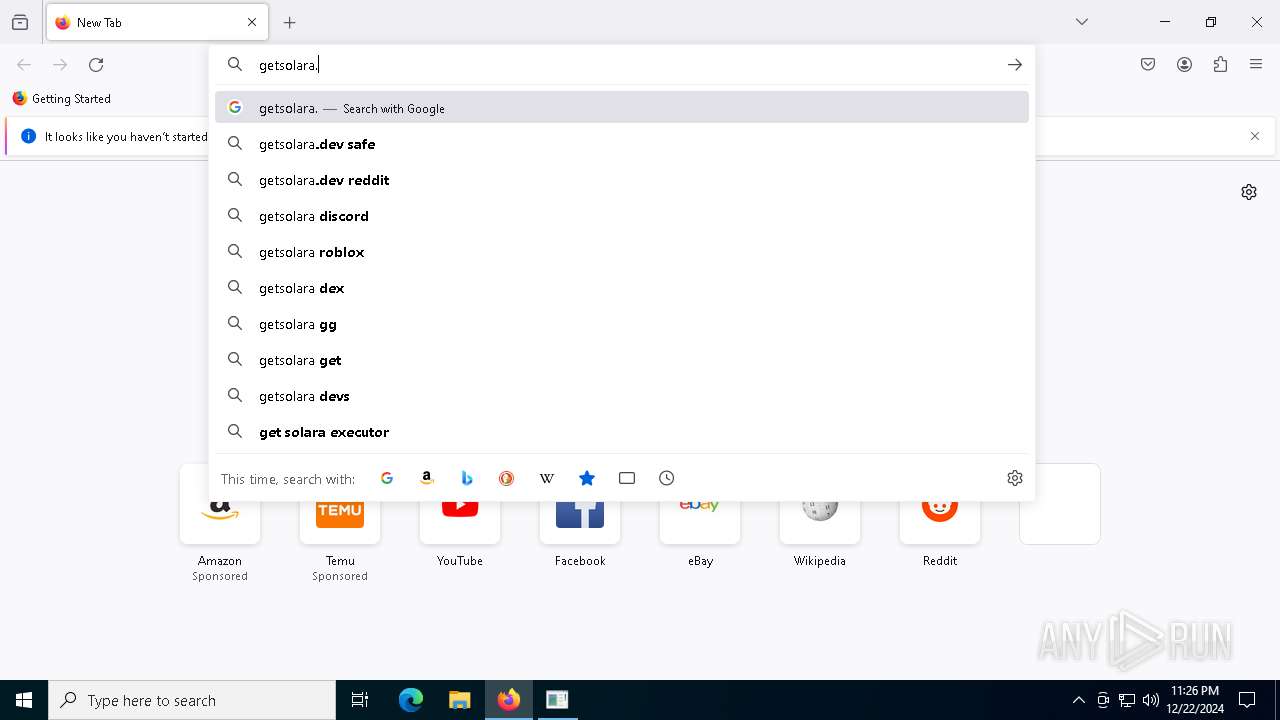
Discord domain found in command line (probably downloading payload)
- msedge.exe (PID: 2828)
Reads security settings of Internet Explorer
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
- msiexec.exe (PID: 7276)
- ShellExperienceHost.exe (PID: 7396)
- msiexec.exe (PID: 7036)
Executable content was dropped or overwritten
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
Starts CMD.EXE for commands execution
- BootstrapperV1.23.exe (PID: 5320)
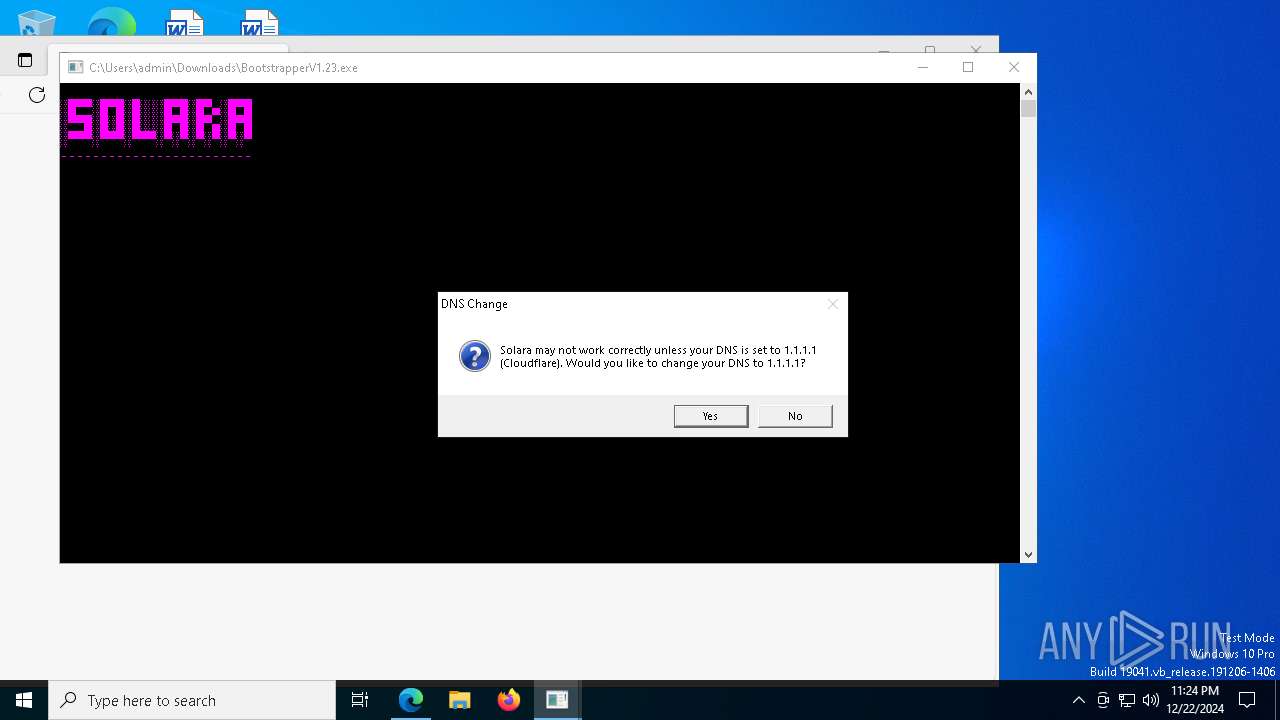
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 2928)
Uses WMIC.EXE to obtain information about the network interface controller
- cmd.exe (PID: 7996)
Reads the date of Windows installation
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 2728)
Checks Windows Trust Settings
- msiexec.exe (PID: 2728)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- wevtutil.exe (PID: 6932)
- msiexec.exe (PID: 7036)
Process drops legitimate windows executable
- BootstrapperV1.23.exe (PID: 5320)
The process drops C-runtime libraries
- BootstrapperV1.23.exe (PID: 5320)
Executes application which crashes
- Solara.exe (PID: 7756)
Checks for external IP
- svchost.exe (PID: 2192)
INFO
Application launched itself
- msedge.exe (PID: 2828)
- msiexec.exe (PID: 2728)
- msedge.exe (PID: 5076)
- firefox.exe (PID: 7304)
- firefox.exe (PID: 7040)
Checks supported languages
- identity_helper.exe (PID: 7696)
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
- msiexec.exe (PID: 7720)
- identity_helper.exe (PID: 6740)
- msiexec.exe (PID: 2728)
- msiexec.exe (PID: 7276)
- ShellExperienceHost.exe (PID: 7396)
- msiexec.exe (PID: 7036)
- Solara.exe (PID: 7756)
Reads the computer name
- identity_helper.exe (PID: 7696)
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
- msiexec.exe (PID: 7720)
- msiexec.exe (PID: 7276)
- identity_helper.exe (PID: 6740)
- msiexec.exe (PID: 2728)
- ShellExperienceHost.exe (PID: 7396)
- msiexec.exe (PID: 7036)
- Solara.exe (PID: 7756)
Reads Environment values
- identity_helper.exe (PID: 7696)
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
- identity_helper.exe (PID: 6740)
- Solara.exe (PID: 7756)
Executable content was dropped or overwritten
- msedge.exe (PID: 6524)
- msedge.exe (PID: 2828)
- msiexec.exe (PID: 2728)
- msedge.exe (PID: 7060)
- firefox.exe (PID: 7304)
The process uses the downloaded file
- msedge.exe (PID: 7860)
- msedge.exe (PID: 2828)
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
Attempting to use instant messaging service
- msedge.exe (PID: 6524)
Reads the machine GUID from the registry
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
- msiexec.exe (PID: 2728)
- Solara.exe (PID: 7756)
Disables trace logs
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
- Solara.exe (PID: 7756)
Checks proxy server information
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
- Solara.exe (PID: 7756)
- WerFault.exe (PID: 6300)
Reads the software policy settings
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
- msiexec.exe (PID: 2728)
- Solara.exe (PID: 7756)
- WerFault.exe (PID: 6300)
Process checks computer location settings
- BootstrapperV1.16.exe (PID: 1520)
- BootstrapperV1.23.exe (PID: 5320)
Create files in a temporary directory
- BootstrapperV1.23.exe (PID: 5320)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2008)
Creates files or folders in the user directory
- msiexec.exe (PID: 2728)
- WerFault.exe (PID: 6300)
Sends debugging messages
- ShellExperienceHost.exe (PID: 7396)
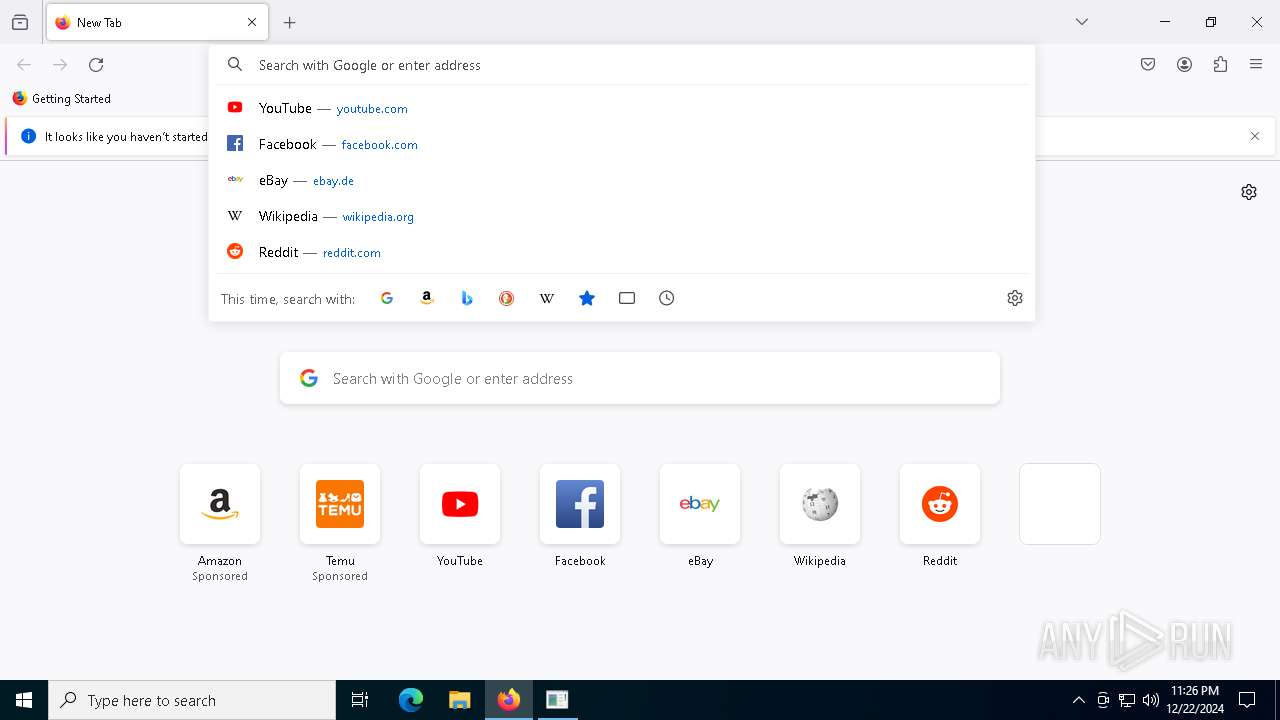
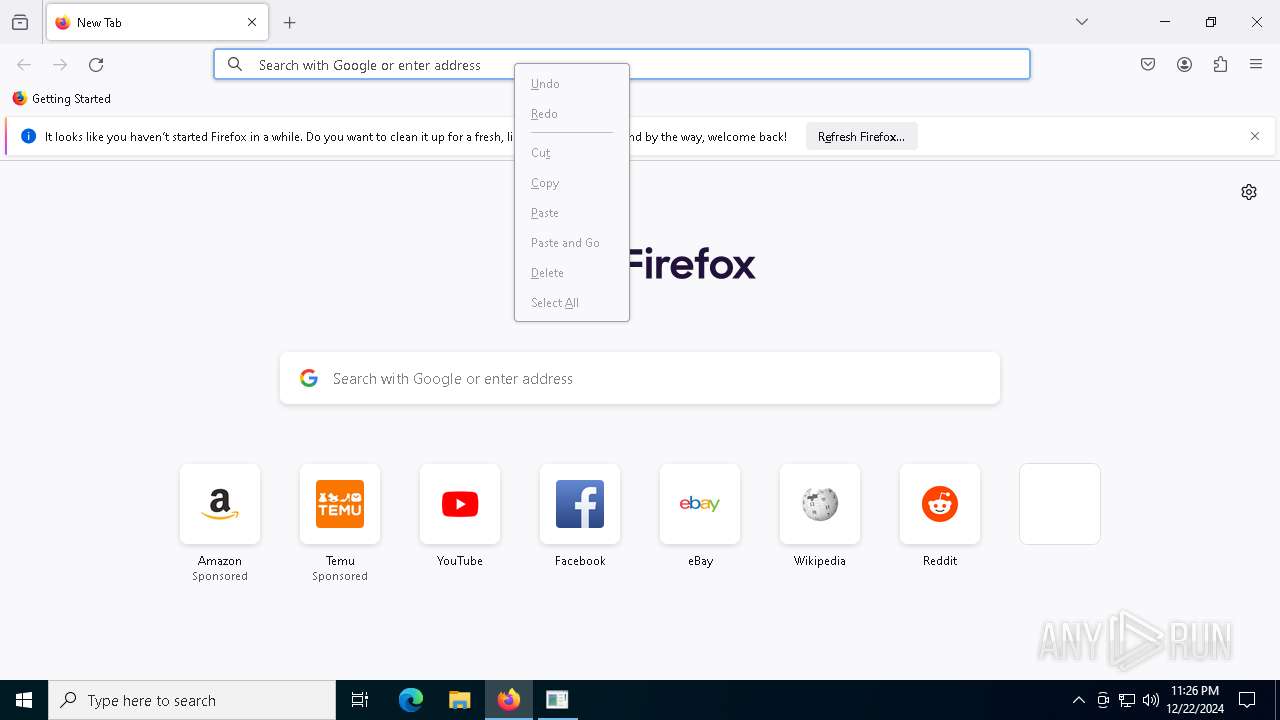
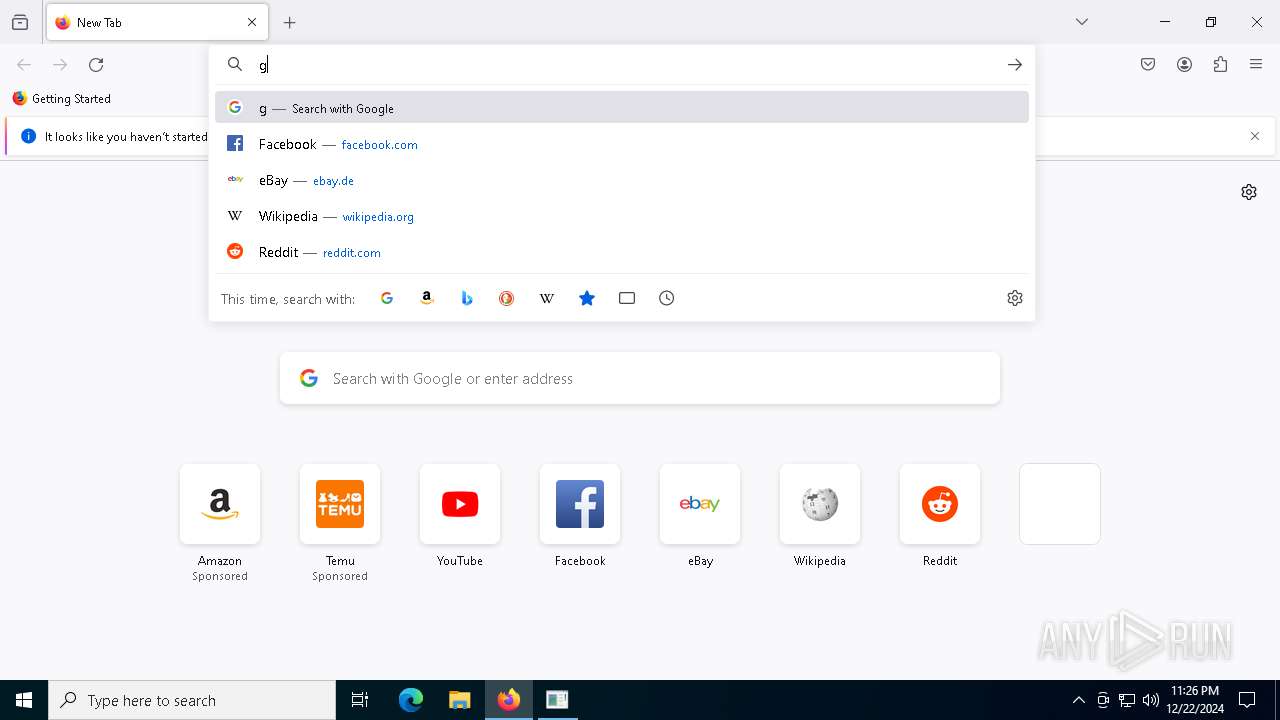
Manual execution by a user
- firefox.exe (PID: 7040)
The sample compiled with english language support
- msedge.exe (PID: 7060)
- BootstrapperV1.23.exe (PID: 5320)
Local mutex for internet shortcut management
- msiexec.exe (PID: 7036)
Creates a software uninstall entry
- msiexec.exe (PID: 2728)
Creates files in the program directory
- BootstrapperV1.23.exe (PID: 5320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
99
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1292 --field-trial-handle=2316,i,6811473988255901860,5289458170209738306,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
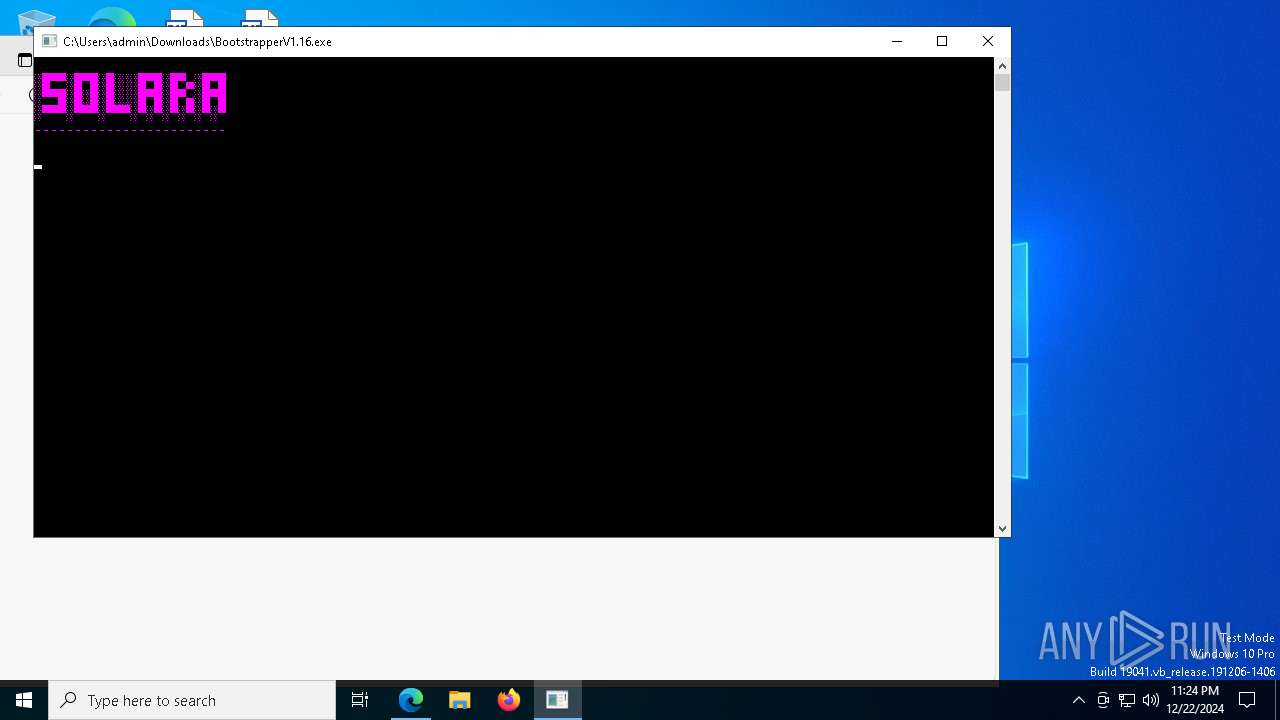
| 1520 | "C:\Users\admin\Downloads\BootstrapperV1.16.exe" | C:\Users\admin\Downloads\BootstrapperV1.16.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SolaraBootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1544 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi" /qn | C:\Windows\System32\msiexec.exe | — | BootstrapperV1.23.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1912 -parentBuildID 20240213221259 -prefsHandle 1840 -prefMapHandle 1832 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {bbce9ede-1cbc-49a1-831e-e6ed00f3041c} 7304 "\\.\pipe\gecko-crash-server-pipe.7304" 2197f9eb410 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4260 --field-trial-handle=2336,i,2365016279157984419,7311485225592234160,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5500 --field-trial-handle=2336,i,2365016279157984419,7311485225592234160,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | BootstrapperV1.16.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | wmic nicconfig where (IPEnabled=TRUE) call SetDNSServerSearchOrder ("1.1.1.1", "1.0.0.1") | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6196 -childID 8 -isForBrowser -prefsHandle 6376 -prefMapHandle 6380 -prefsLen 32019 -prefMapSize 244583 -jsInitHandle 1516 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f4a6b288-6b1f-4c65-968d-50b302f82428} 7304 "\\.\pipe\gecko-crash-server-pipe.7304" 219099c94d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
45 902
Read events
42 904
Write events
2 987
Delete events
11
Modification events
| (PID) Process: | (2828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2828) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AC3D6E757A882F00 | |||
| (PID) Process: | (2828) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CF3779757A882F00 | |||
| (PID) Process: | (2828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {045656CC-2F70-4163-B9BD-EEBE541438C4} | |||
| (PID) Process: | (2828) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F397C0757A882F00 | |||
| (PID) Process: | (2828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (7860) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000E70A8E9AC854DB01 | |||
Executable files
49
Suspicious files
2 372
Text files
894
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1356be.TMP | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1356ce.TMP | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1356ce.TMP | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1356fd.TMP | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1356ed.TMP | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
89
TCP/UDP connections
289
DNS requests
346
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6600 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1735351767&P2=404&P3=2&P4=ffzEwx85DDnV3a3iMiWr6d2rNqXCY92zLHGswbRJyTJ21%2fYfsZPcg6TbvytbwvzgVkVsnD2aoHXAIKihGXRWKA%3d%3d | unknown | — | — | whitelisted |
6600 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1735351767&P2=404&P3=2&P4=ffzEwx85DDnV3a3iMiWr6d2rNqXCY92zLHGswbRJyTJ21%2fYfsZPcg6TbvytbwvzgVkVsnD2aoHXAIKihGXRWKA%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6256 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2728 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | unknown | — | — | whitelisted |
2728 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAOO2y%2FG5AVzGnYPFRYUTIU%3D | unknown | — | — | whitelisted |
8108 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1356 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6524 | msedge.exe | 162.159.129.233:443 | cdn.discordapp.com | — | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
cdn.discordapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6524 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6524 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2192 | svchost.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
— | — | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
6524 | msedge.exe | Misc activity | ET INFO Observed Cloudflare DNS over HTTPS Domain (cloudflare-dns .com in TLS SNI) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |