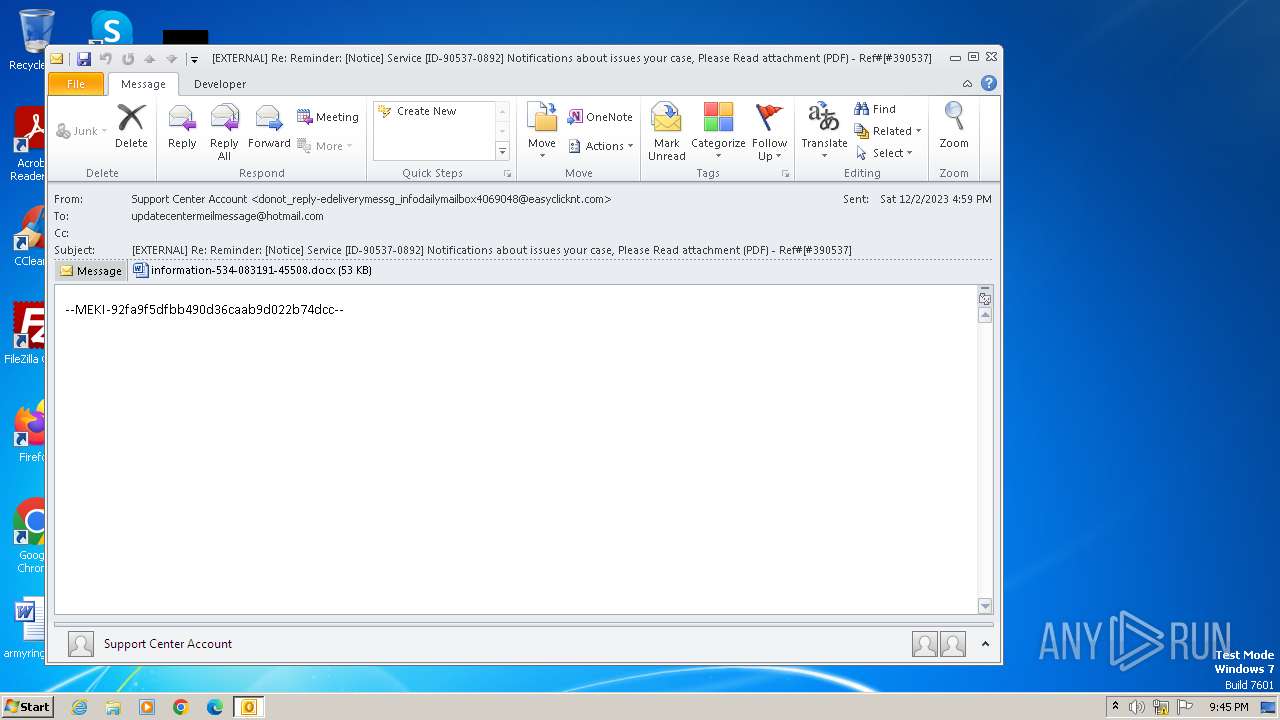
| File name: | [EXTERNAL] Re_ Reminder_ [Notice] Service [ID-90537-0892] Notifications about issues your case, Please Read attachment (PDF) - Ref#[#390537].eml |
| Full analysis: | https://app.any.run/tasks/e870537e-3ff9-4147-ae80-eb61bbca0135 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 21:45:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | 212CC327A668FE7CB78B2F628080EA93 |
| SHA1: | F22D537307951E5791E28144AC0271A8B09FE688 |
| SHA256: | AC54F579E2C724A7E2340DCCF8BF0D1081DB49472E55A388100D133E6173B192 |
| SSDEEP: | 1536:e45ZXSn/Q11OC/394q41adsVB+kZmQ8K43Ov8jLXeMqB/eQLkebJZr2g1O:egSn/e1O8Cq4IsVyQhdUjLXqde0Z3FO |
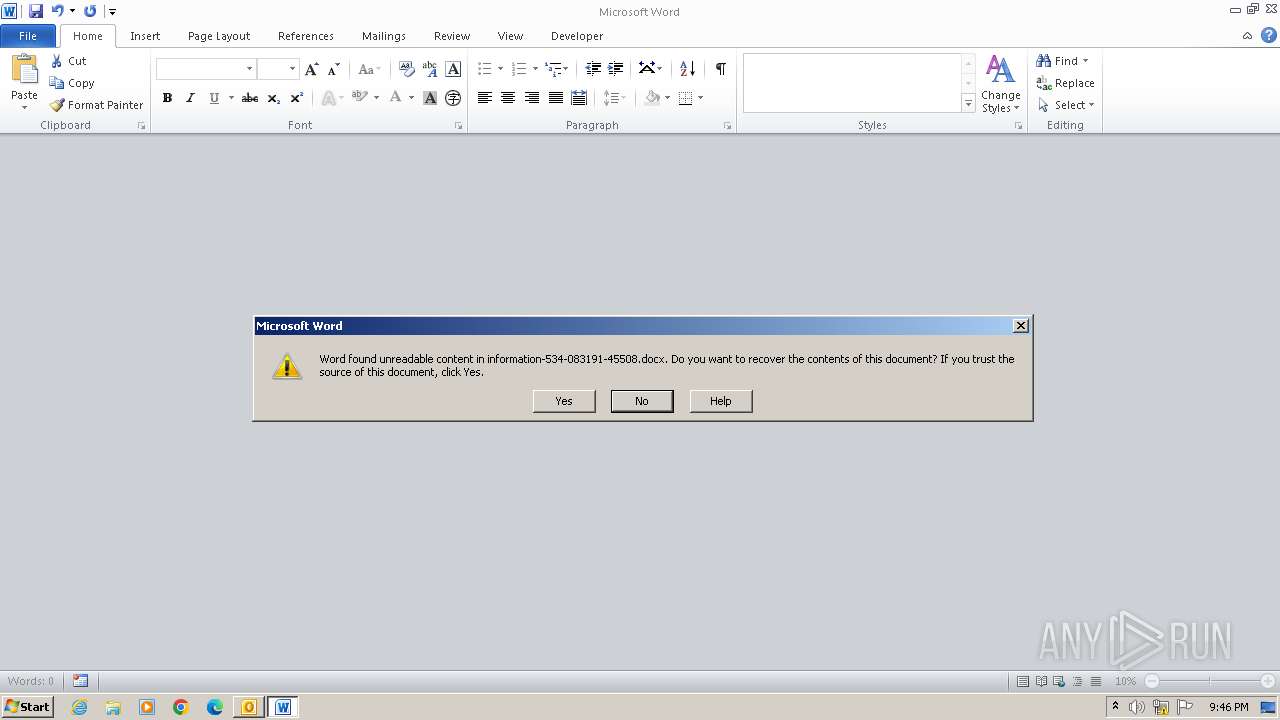
MALICIOUS
Connection from MS Office application
- WINWORD.EXE (PID: 2220)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 2220)
INFO
The process uses the downloaded file
- WINWORD.EXE (PID: 2220)
- OUTLOOK.EXE (PID: 3060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
43
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
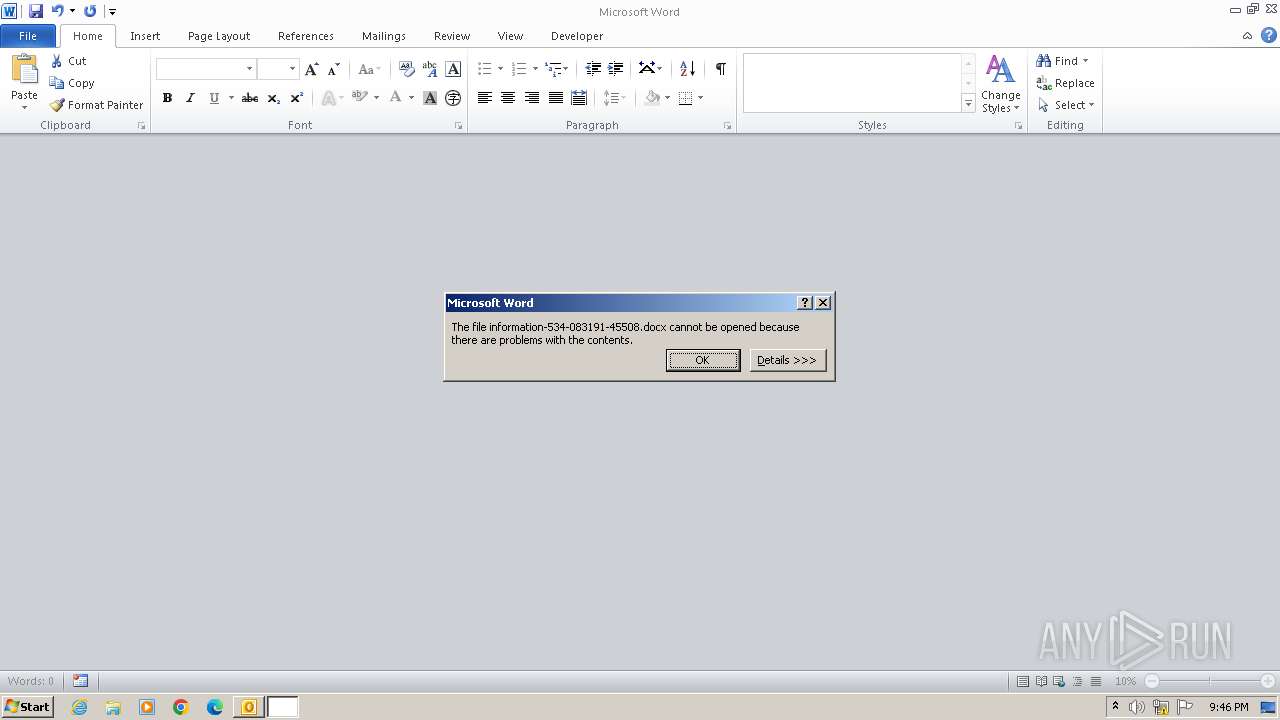
| 2220 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LSR1TET3\information-534-083191-45508.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3060 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\e870537e-3ff9-4147-ae80-eb61bbca0135.eml" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
9 347
Read events
8 325
Write events
808
Delete events
214
Modification events
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (3060) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
11
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3060 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6797.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3060 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2220 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9128.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2220 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:31BC672B989202B4A9E0338E93A2171C | SHA256:B8941361097D6346DB0CEED0D2869CACA34428317A96B8DF710263A6755808C6 | |||
| 3060 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LSR1TET3\information-534-083191-45508 (2).docx | binary | |
MD5:0E18966402039E169B43A1E1F42434C9 | SHA256:92BA96BC858E79E682CC84916D48503A271622C9E2BF5629520DA8CF5B1CC809 | |||
| 3060 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LSR1TET3\information-534-083191-45508.docx | binary | |
MD5:0E18966402039E169B43A1E1F42434C9 | SHA256:92BA96BC858E79E682CC84916D48503A271622C9E2BF5629520DA8CF5B1CC809 | |||
| 2220 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\msoC028.tmp | document | |
MD5:64E26212FA8F7C13FE3F80784F143D9A | SHA256:3A66B58EE972FD044F4A7DF73192757999EBCCFE8DE1F659E9395B15D1FCD525 | |||
| 3060 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LSR1TET3\information-534-083191-45508.docx:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 2220 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_AA11846C-CBDD-42D8-845F-1EC31FB767FB.0\msoC5E5.tmp | compressed | |
MD5:0C88AAC0E9ADCC8A4A46356FFDAC3CDC | SHA256:834D0E1085F7B7DC9EDA5395C1582F88BAEFEF68F28EBB99F5BEE34593BD90B1 | |||
| 3060 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LSR1TET3\information-534-083191-45508 (2).docx:Zone.Identifier:$DATA | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3060 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
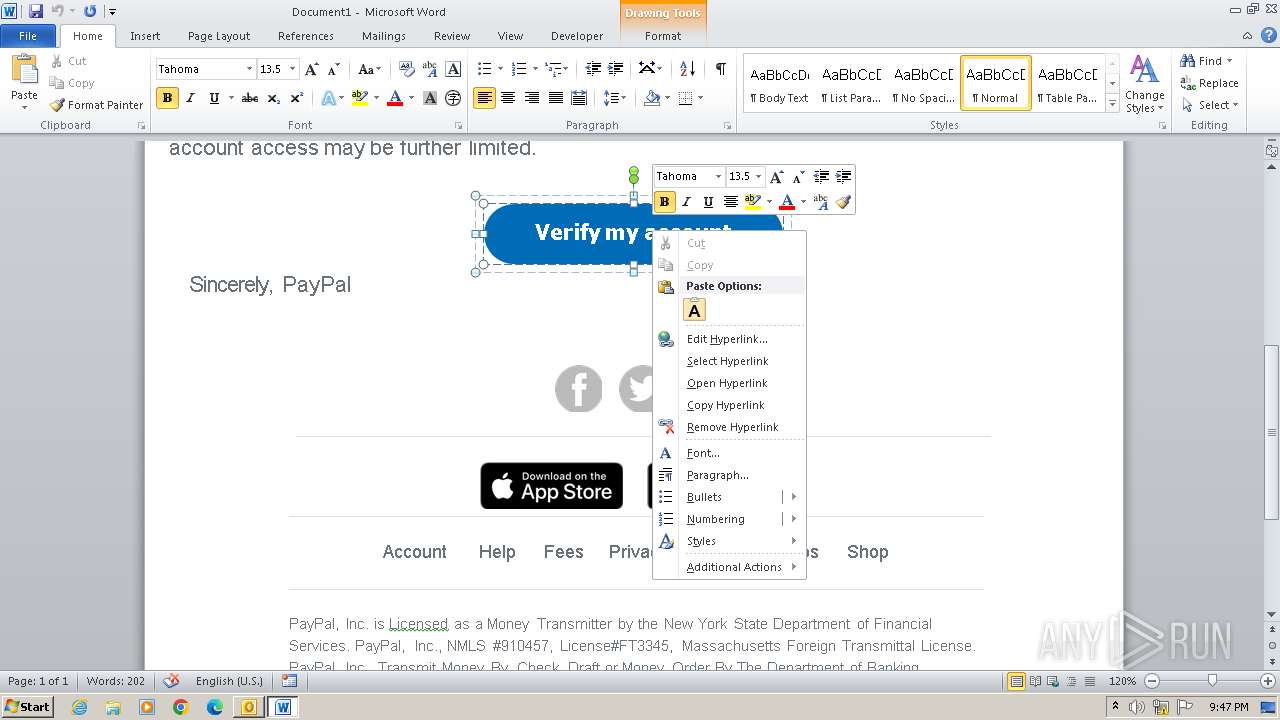
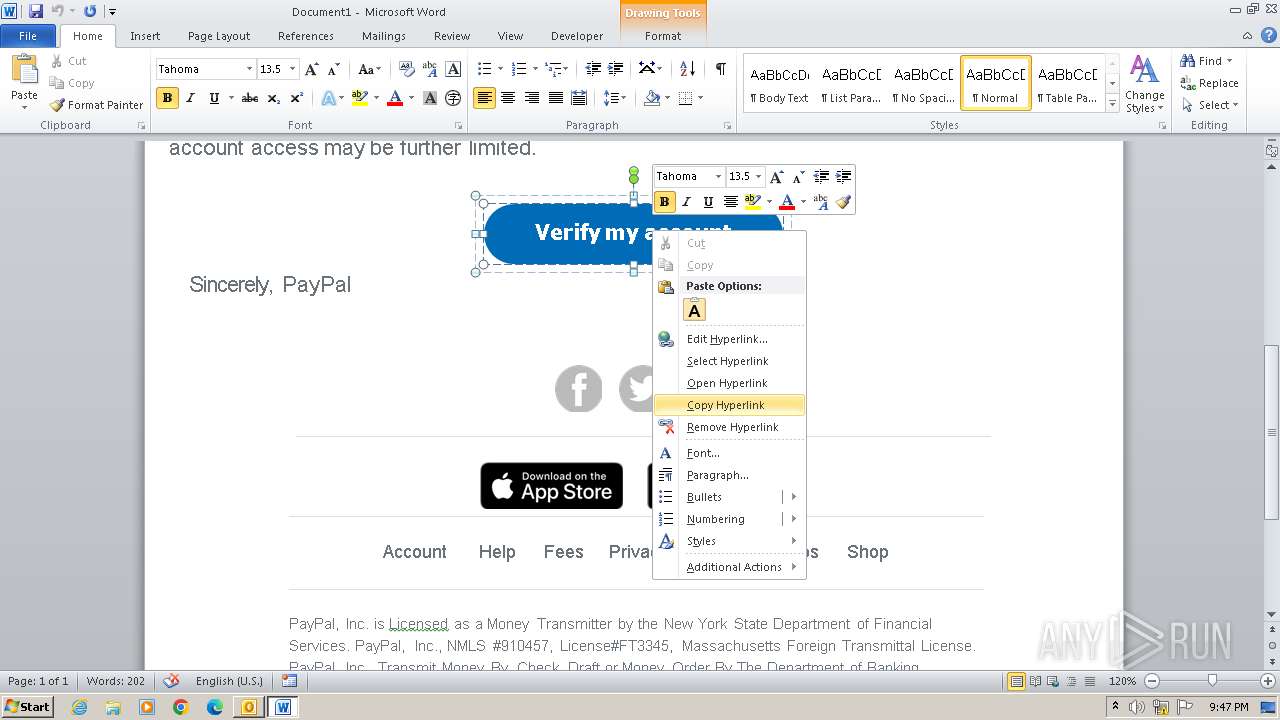
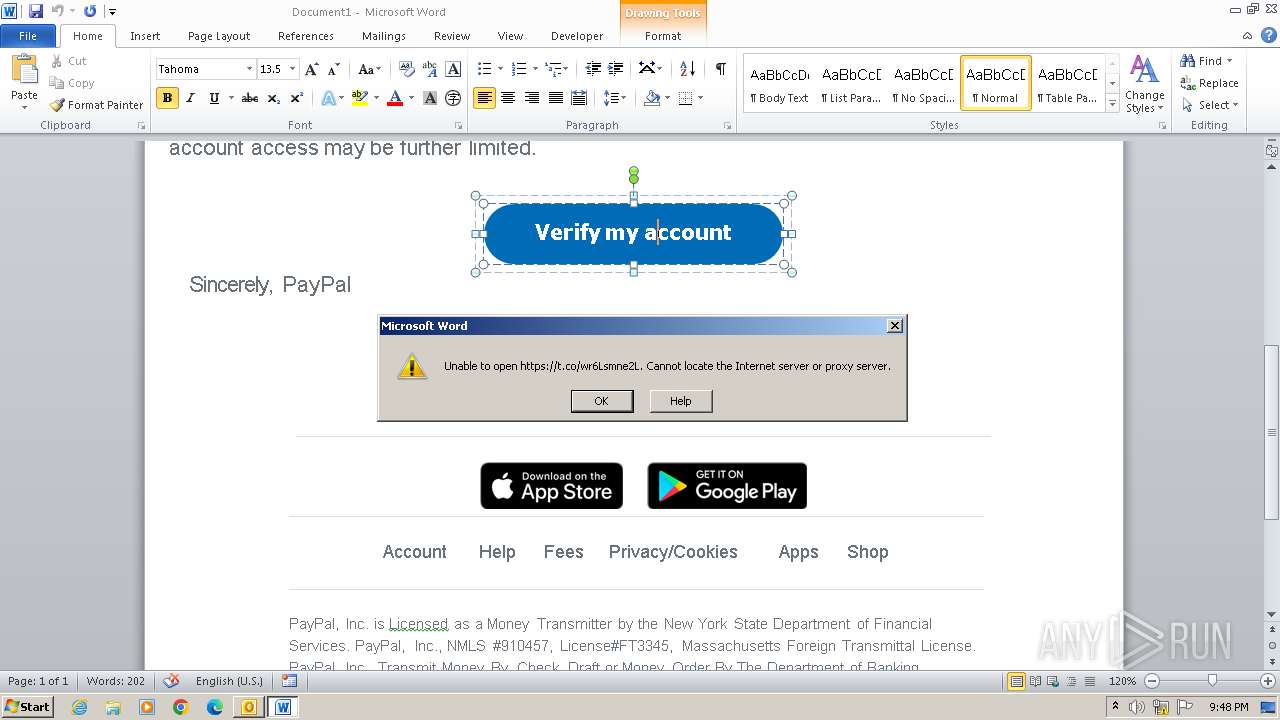
2220 | WINWORD.EXE | 104.244.42.5:443 | t.co | TWITTER | US | unknown |
2220 | WINWORD.EXE | 104.244.42.133:443 | t.co | TWITTER | US | unknown |
2220 | WINWORD.EXE | 104.244.42.69:443 | t.co | TWITTER | US | unknown |
2220 | WINWORD.EXE | 104.244.42.197:443 | t.co | TWITTER | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
t.co |
| shared |
dns.msftncsi.com |
| shared |