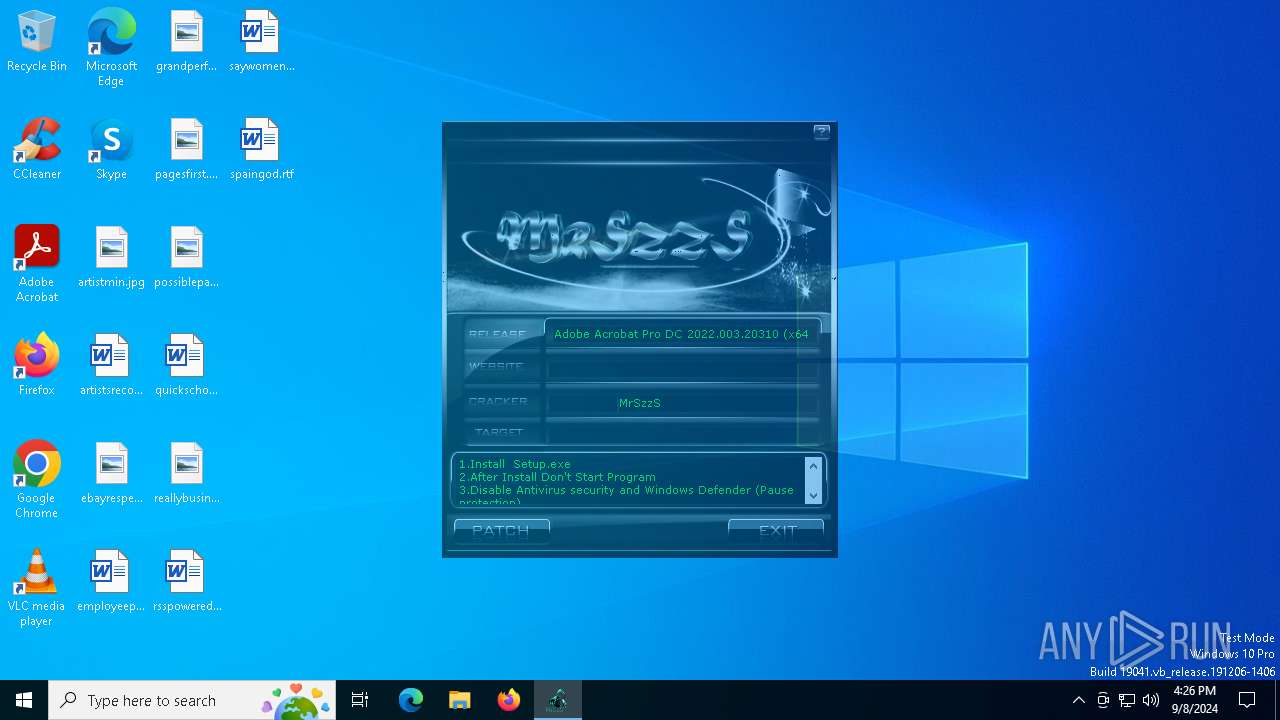
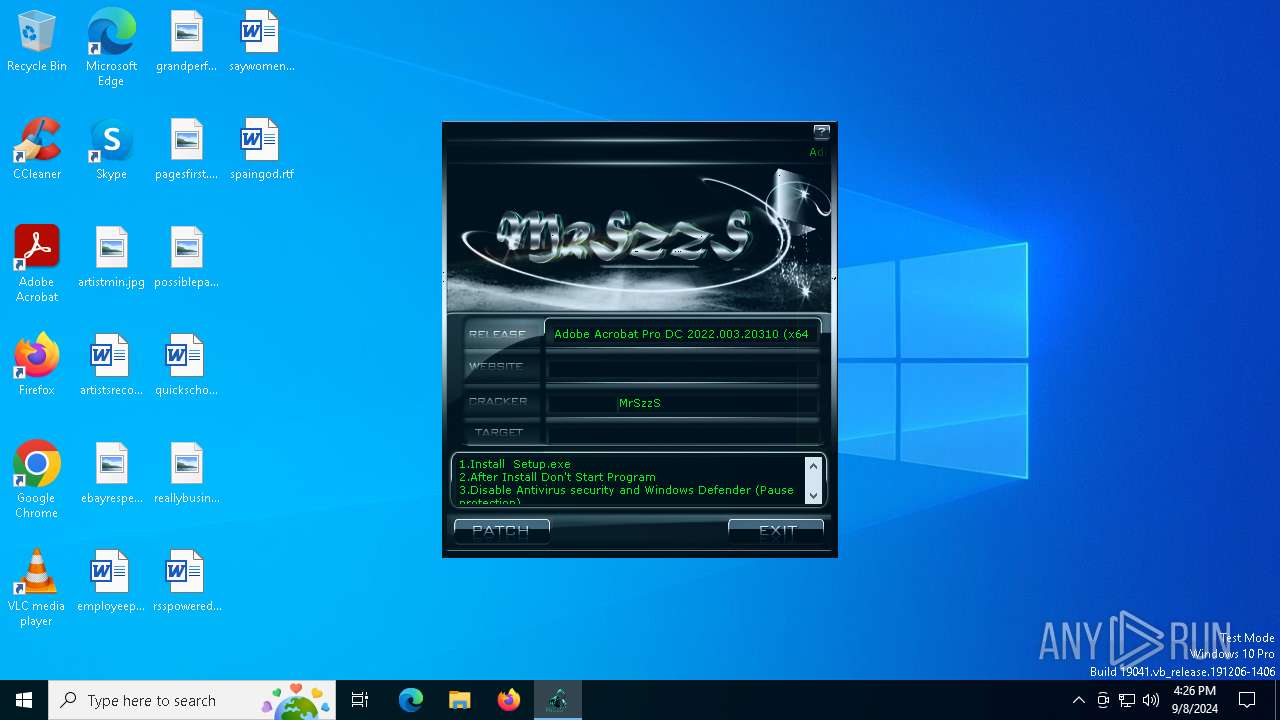
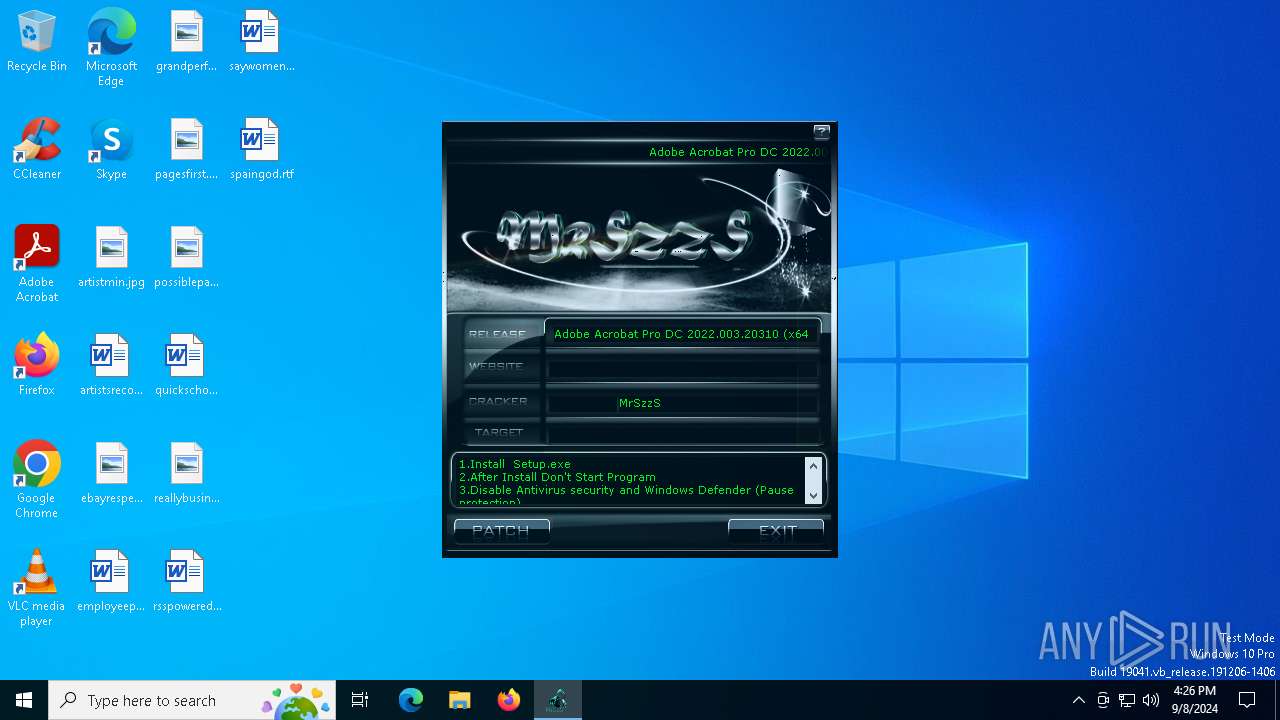
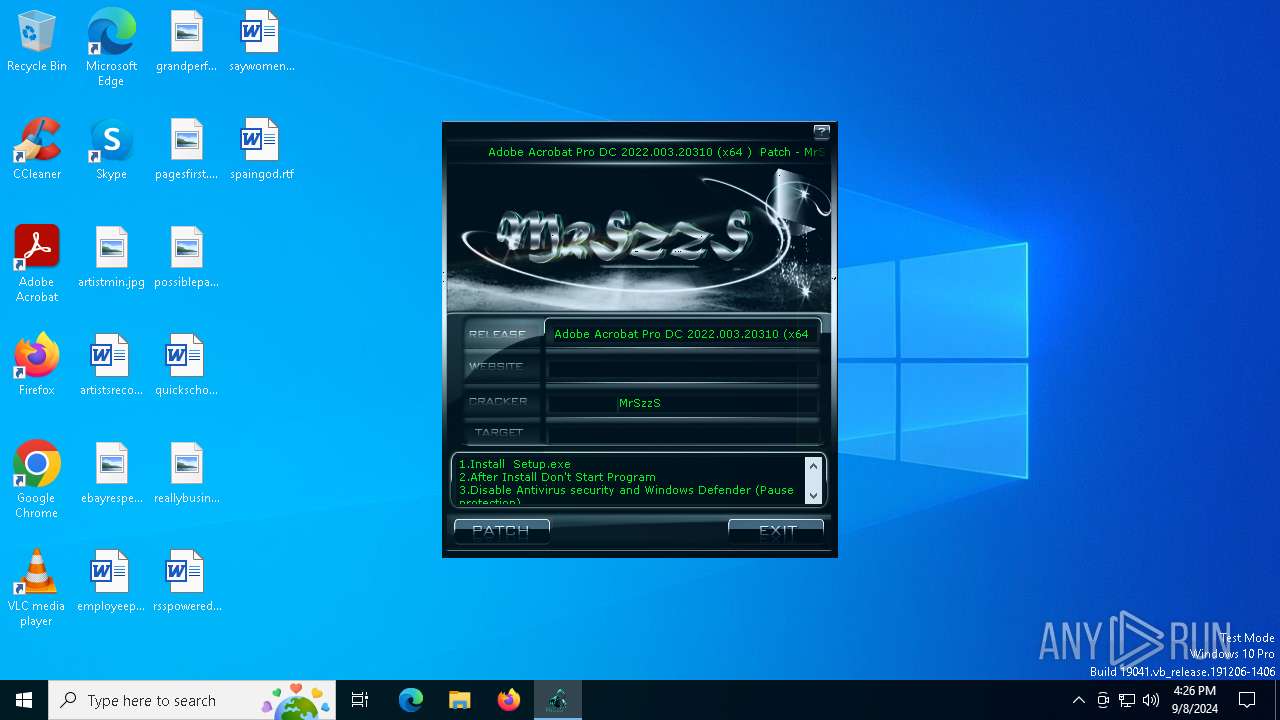
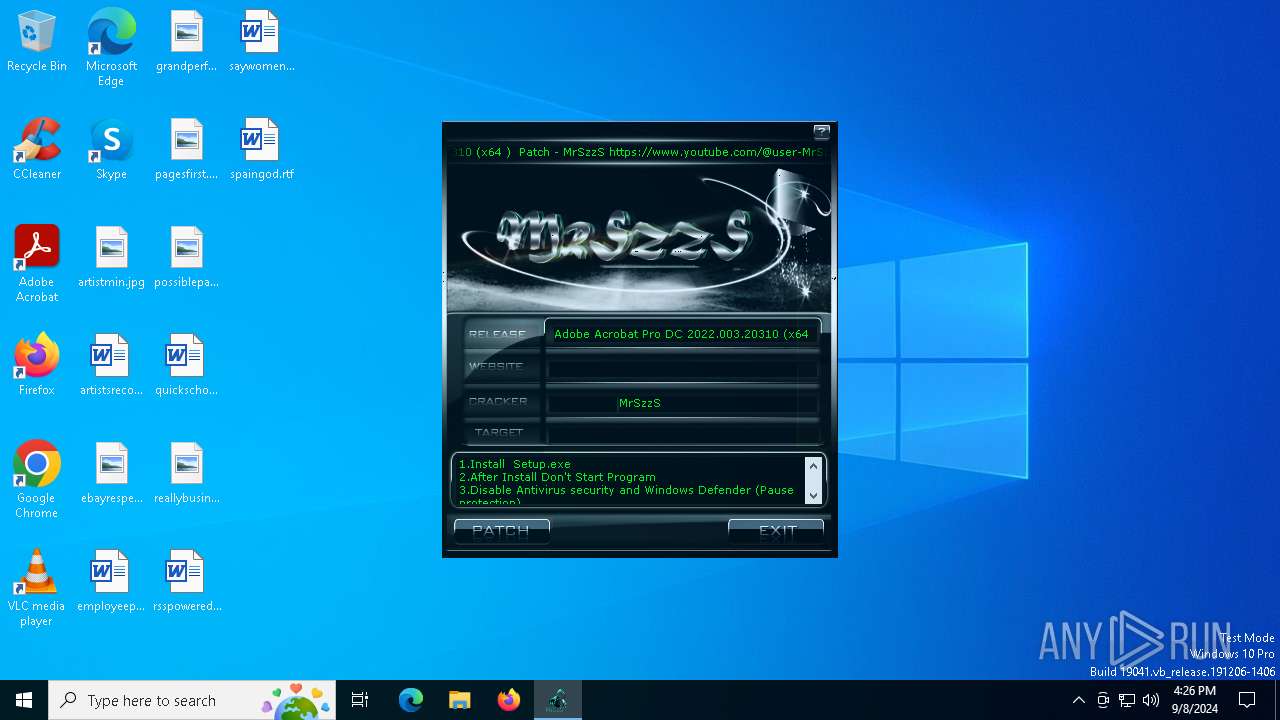
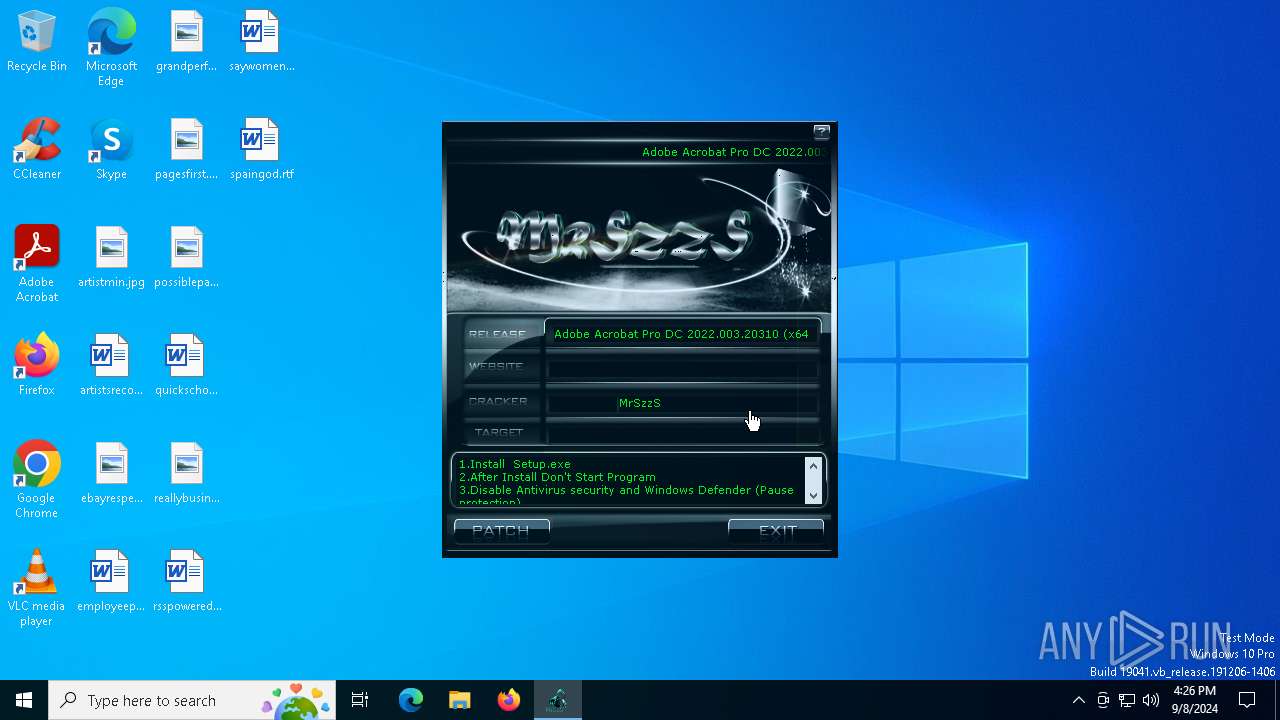
| File name: | (x64.)-patch.exe |
| Full analysis: | https://app.any.run/tasks/e0b9a52e-8dd5-4ef1-9c5c-f52d35d2e7bb |
| Verdict: | Malicious activity |
| Analysis date: | September 08, 2024, 16:26:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EEA0B5C1AF456596EDA11E4A60D76B21 |
| SHA1: | B31C67B73E1235C227B09AEE4BAEE52C2720E3C5 |
| SHA256: | AC473756CD24320B39624F525C6AC3027D53900116ED570480DA5BACDF5475BC |
| SSDEEP: | 24576:0DlYRgSoPg551sbm5RvNrnPv960aTreKaC1fnp:0uC9Pg5cmfNTH4v1zPp |
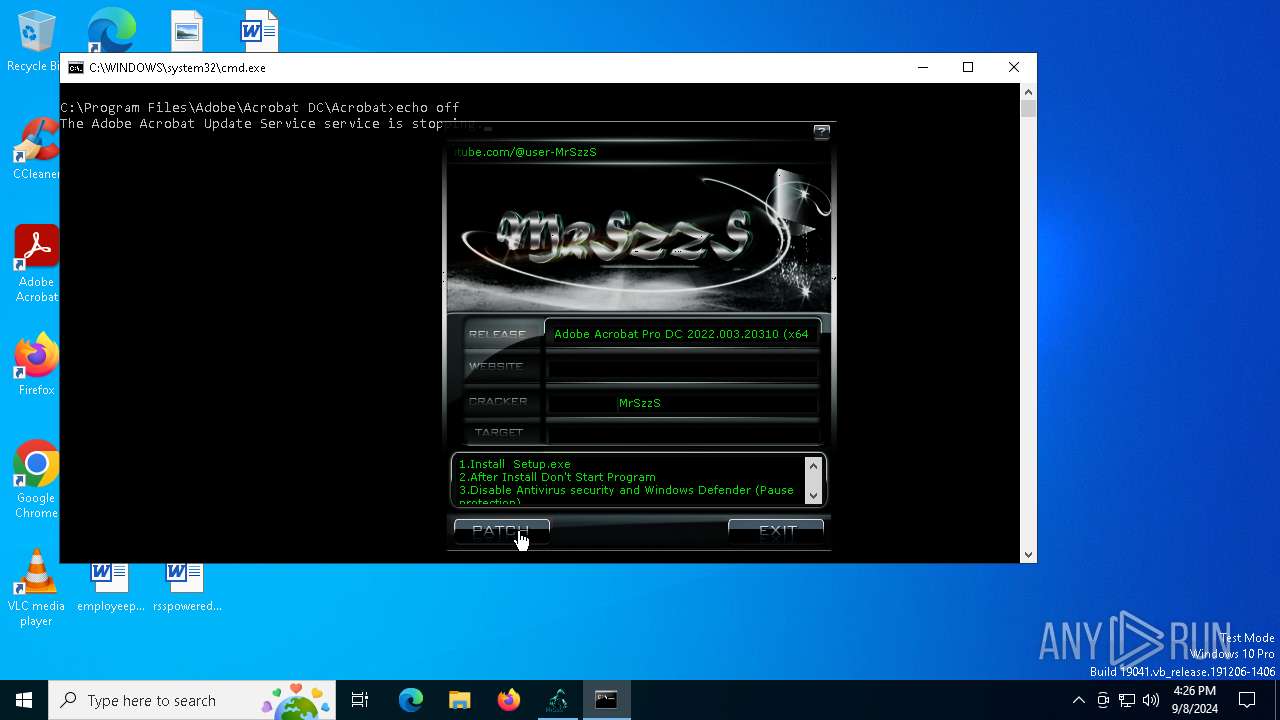
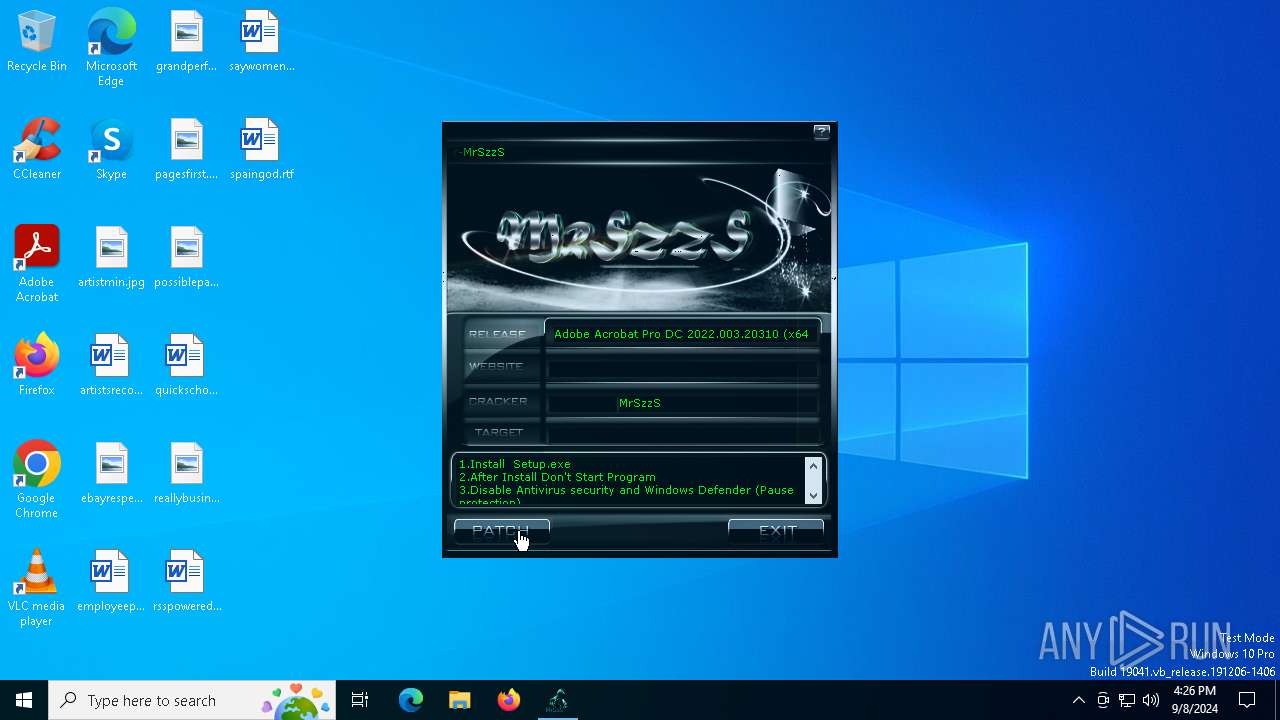
MALICIOUS
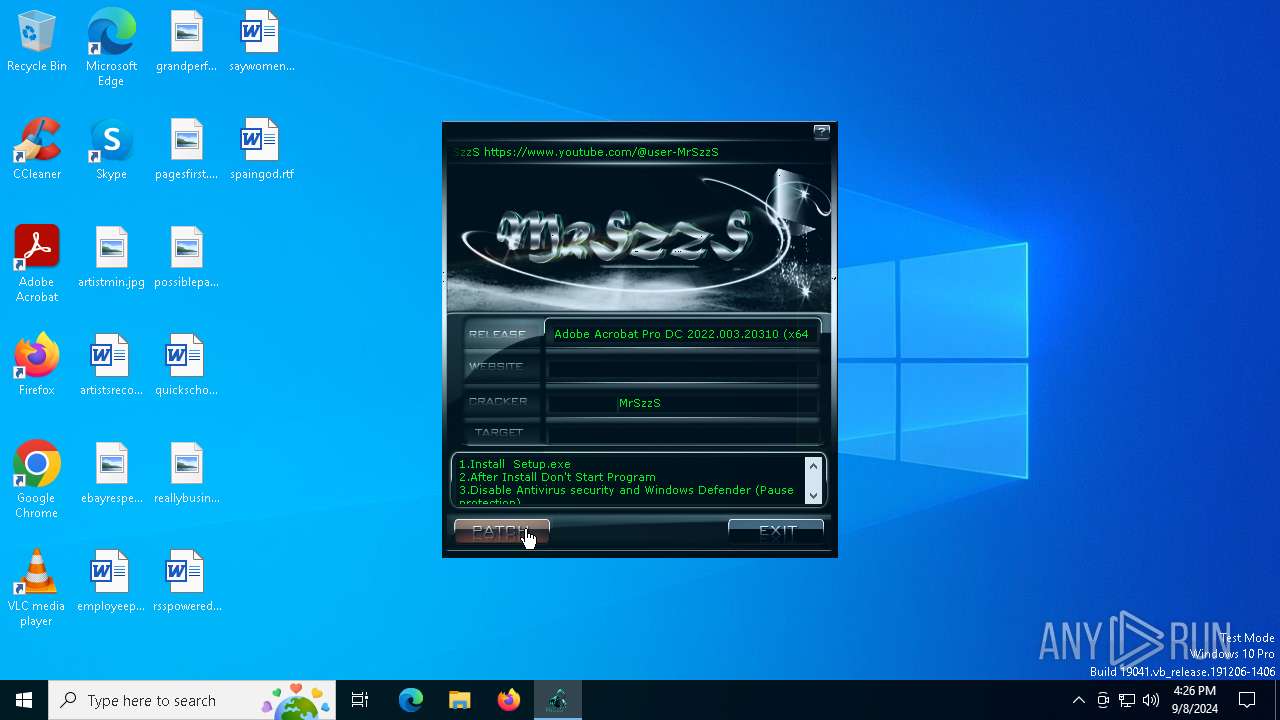
Starts NET.EXE for service management
- net.exe (PID: 3028)
- cmd.exe (PID: 6276)
Modifies hosts file to block updates
- cmd.exe (PID: 6276)
SUSPICIOUS
Executing commands from a ".bat" file
- (x64.)-patch.exe (PID: 1640)
Executable content was dropped or overwritten
- (x64.)-patch.exe (PID: 1640)
Starts CMD.EXE for commands execution
- (x64.)-patch.exe (PID: 1640)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 6276)
Starts SC.EXE for service management
- cmd.exe (PID: 6276)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6276)
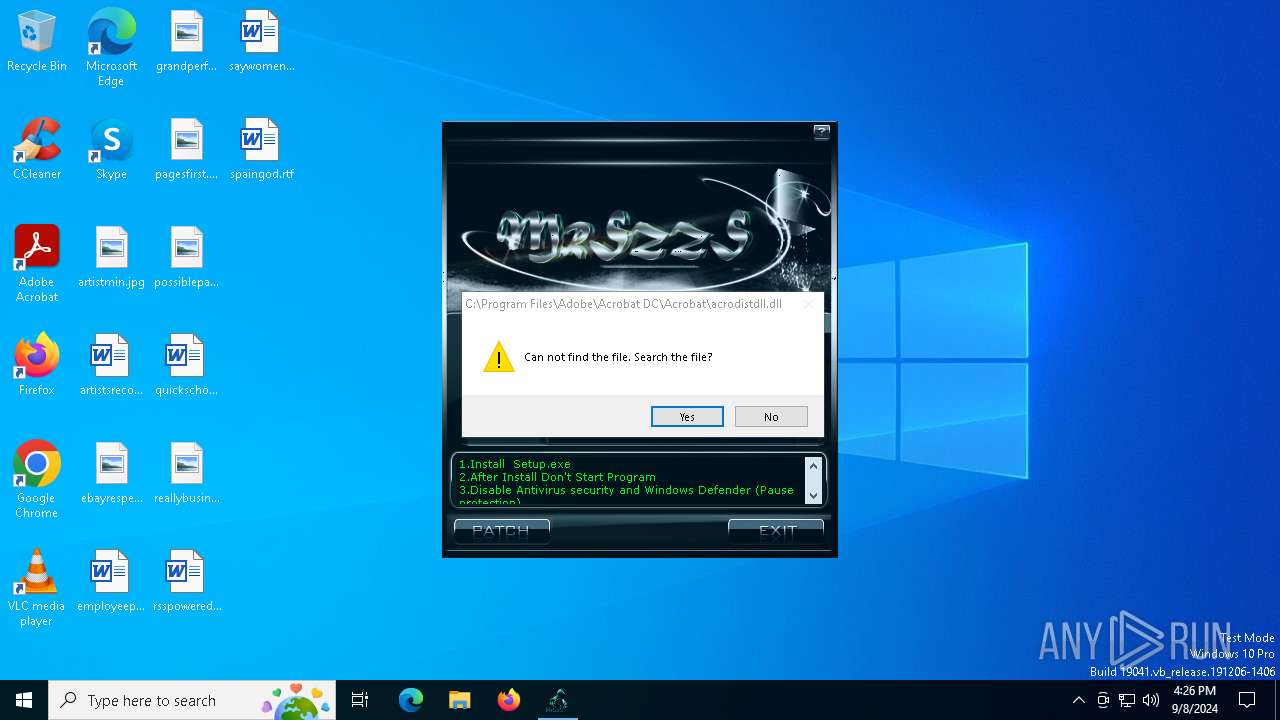
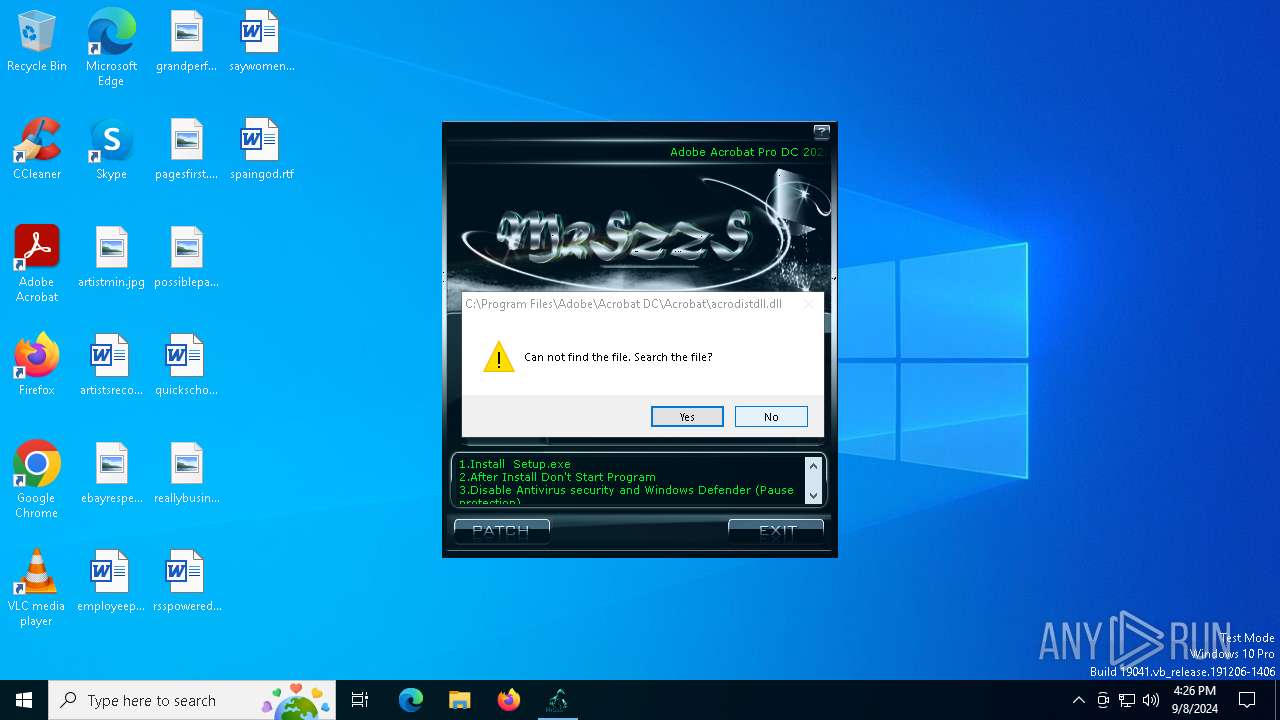
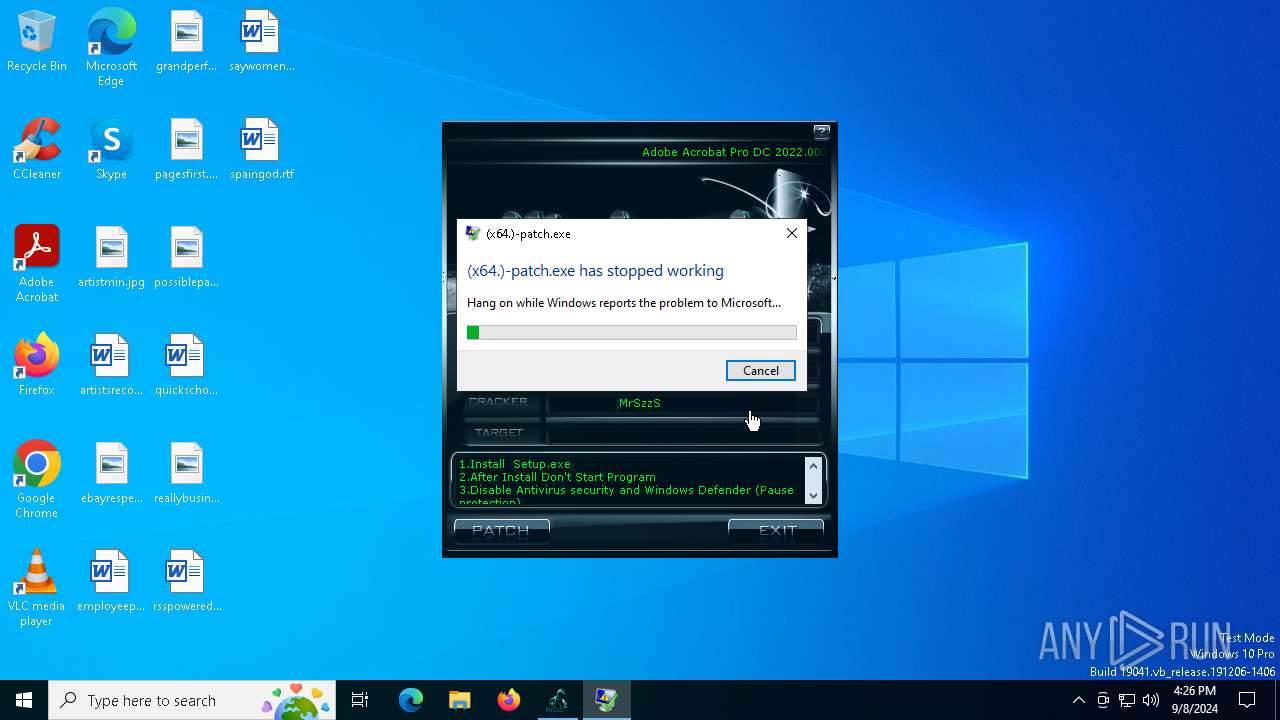
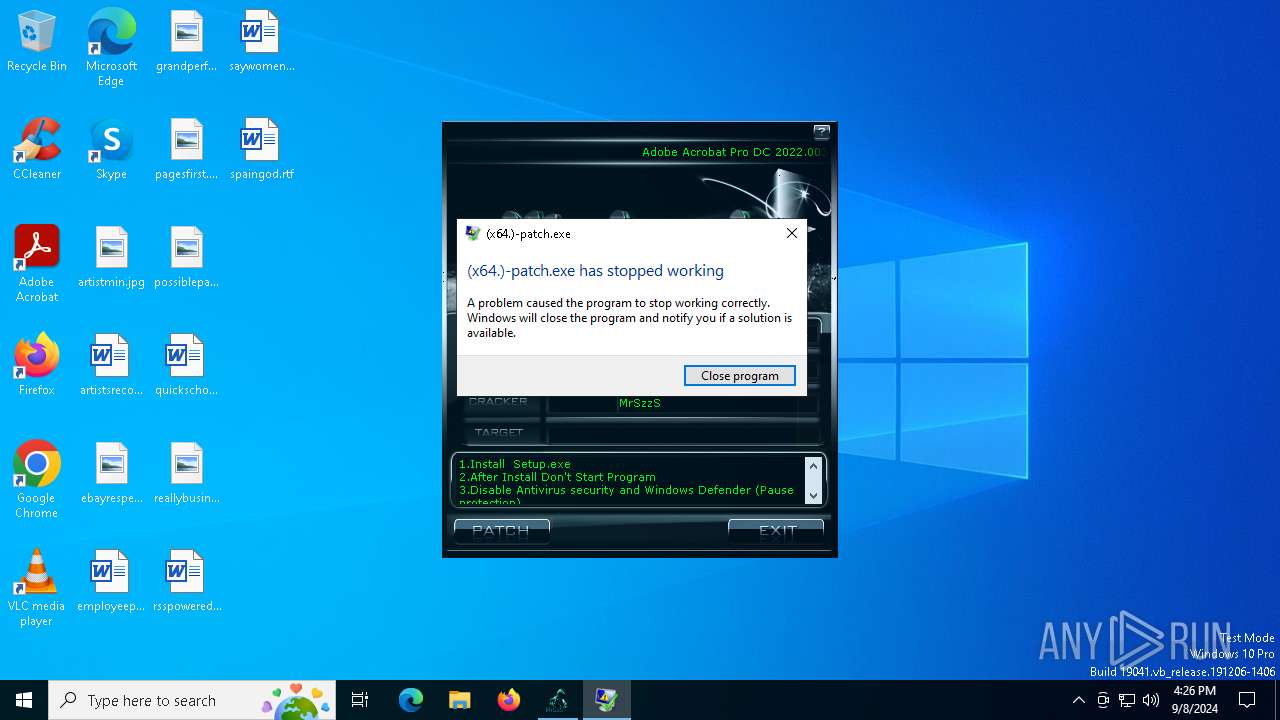
Executes application which crashes
- (x64.)-patch.exe (PID: 1640)
INFO
Checks supported languages
- (x64.)-patch.exe (PID: 1640)
Create files in a temporary directory
- (x64.)-patch.exe (PID: 1640)
Creates files in the program directory
- (x64.)-patch.exe (PID: 1640)
Reads the computer name
- (x64.)-patch.exe (PID: 1640)
Reads the software policy settings
- WerFault.exe (PID: 6544)
Creates files or folders in the user directory
- WerFault.exe (PID: 6544)
Checks proxy server information
- WerFault.exe (PID: 6544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 20:59:46+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 861184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
158
Monitored processes
34
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | FIND /C /I "lm-prd-da1.licenses.adobe.com" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | FIND /C /I "ereg.adobe.com" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1640 | "C:\Users\admin\AppData\Local\Temp\(x64.)-patch.exe" | C:\Users\admin\AppData\Local\Temp\(x64.)-patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\AppData\Local\Temp\(x64.)-patch.exe" | C:\Users\admin\AppData\Local\Temp\(x64.)-patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1944 | FIND /C /I "prod.adobegenuine.com" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1964 | FIND /C /I "practivate-da1.adobe.com" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | FIND /C /I "hlrcv.stage.adobe.com" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2036 | FIND /C /I "uds.licenses.adobe.com" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2112 | taskkill.exe /f /t /im acrotray.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2180 | FIND /C /I "helpexamples.com" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 417
Read events
4 409
Write events
5
Delete events
3
Modification events
| (PID) Process: | (6544) WerFault.exe | Key: | \REGISTRY\A\{7c7eef69-6224-8b6d-df7f-047a9d22cc97}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (6544) WerFault.exe | Key: | \REGISTRY\A\{7c7eef69-6224-8b6d-df7f-047a9d22cc97}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6544) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | ClockTimeSeconds |
Value: 48D0DD6600000000 | |||
| (PID) Process: | (6544) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | TickCount |
Value: E73D130000000000 | |||
Executable files
2
Suspicious files
6
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1640 | (x64.)-patch.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 6544 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_(x64.)-patch.exe_6e5930a023762b36b57155ddf4d1b75853c999a_a0bd0c63_a87d3342-c370-4187-a8ba-0fc86673a498\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1640 | (x64.)-patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:929A0868FB11866CFB6E025A2C0205C5 | SHA256:ED9F8AA8C3ACC5CA1813E8A7C965474FD8BCAD53E5F828C3FDFAC3F3424BCC0A | |||
| 6544 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:ABBF2E3501D8F7C976EAD6943AD044A9 | SHA256:B03AE264C6CA5CF6A9AFD18B653691FEB0CC6506DF37D135E00E3FA6E1115DF5 | |||
| 6544 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FB64A9EBEDF48D3895381D5B7D80743D | SHA256:EA21D495930AD76F267A33A0F593DBF0C7EA75E457FCAE49A29DAAD8BD920F42 | |||
| 6544 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:B206ED293AA7857836C0476407FC5231 | SHA256:A94A481FD4BF9F3460E13A6ACFF1118BDCF1244D3A4ACA8E7695A200C2FFFE91 | |||
| 6544 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER3C42.tmp.WERInternalMetadata.xml | xml | |
MD5:5EF1EEF40DC4301F18568532771B723D | SHA256:9CFD6C928D1303E7DD61DA9D96E398F07FC2A7574D0BECE2DA7188213C865842 | |||
| 6544 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER3C81.tmp.xml | xml | |
MD5:C2A1927F91552892AD69E77DE1961103 | SHA256:E9A10136E4FEB09AE27841C9583CF03AD64543E19A67EC12878D3084C907822B | |||
| 6544 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\(x64.)-patch.exe.1640.dmp | binary | |
MD5:550ED1D4EB69EB5898278A297BCD4827 | SHA256:31DA3E019670C1C7D8A182C464AC20AFD589DFDECA8B5E548A21DEB78E0FF7EB | |||
| 6276 | cmd.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:68ABFD64282A0F004DBA8A53532817CA | SHA256:F68083BE0FA9CD2333A1C34E35FAAD9B6F7949224E78CD6105C08977AEDAEFBA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
27
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6120 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1920 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1920 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | WerFault.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6120 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6120 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6164 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |