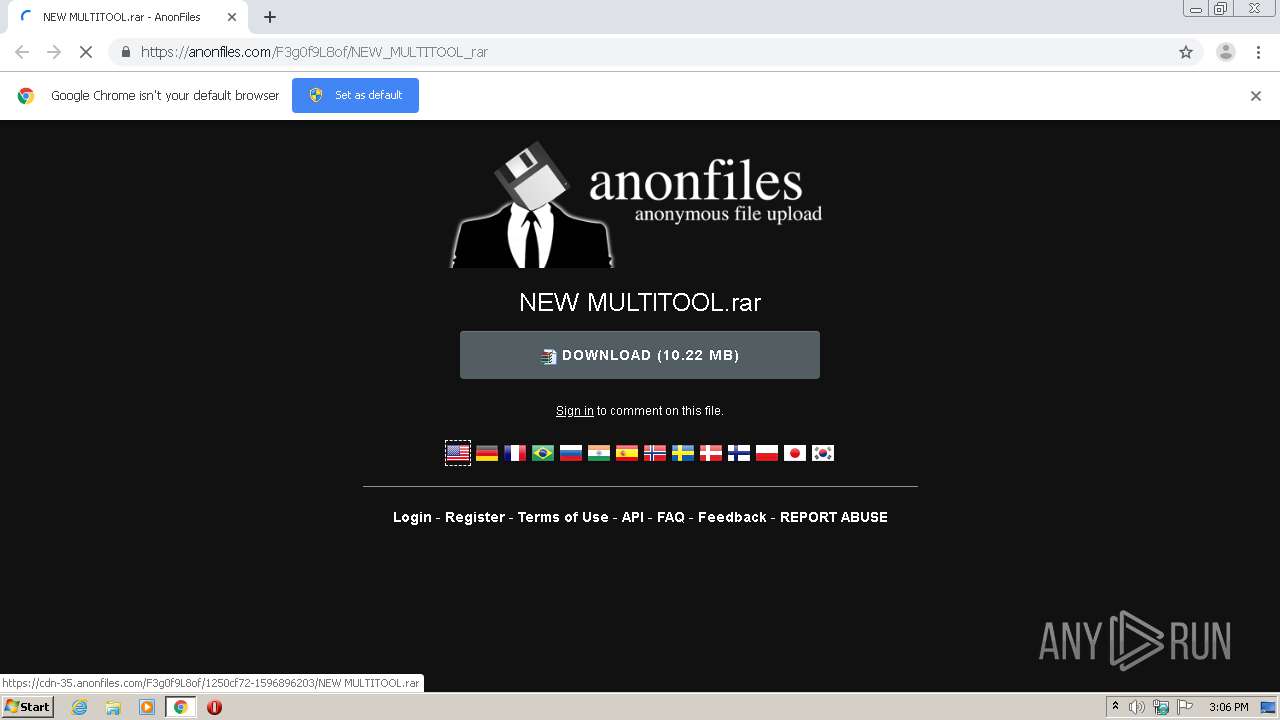
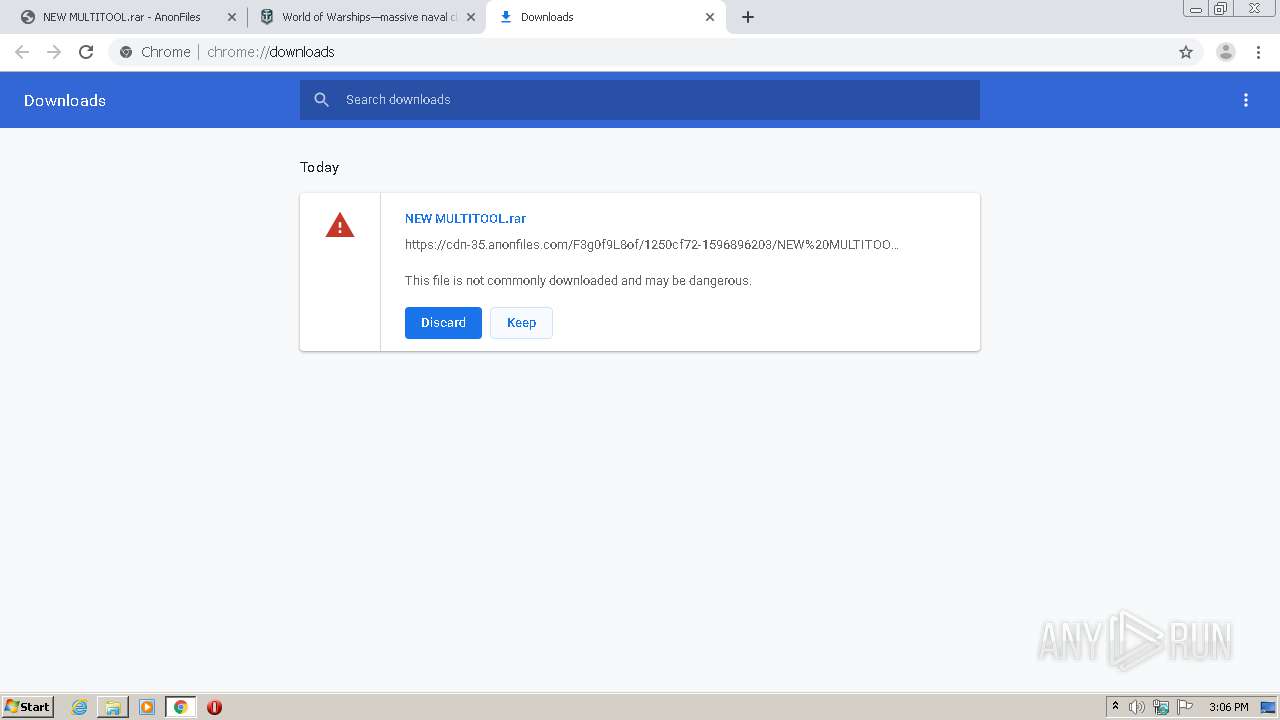
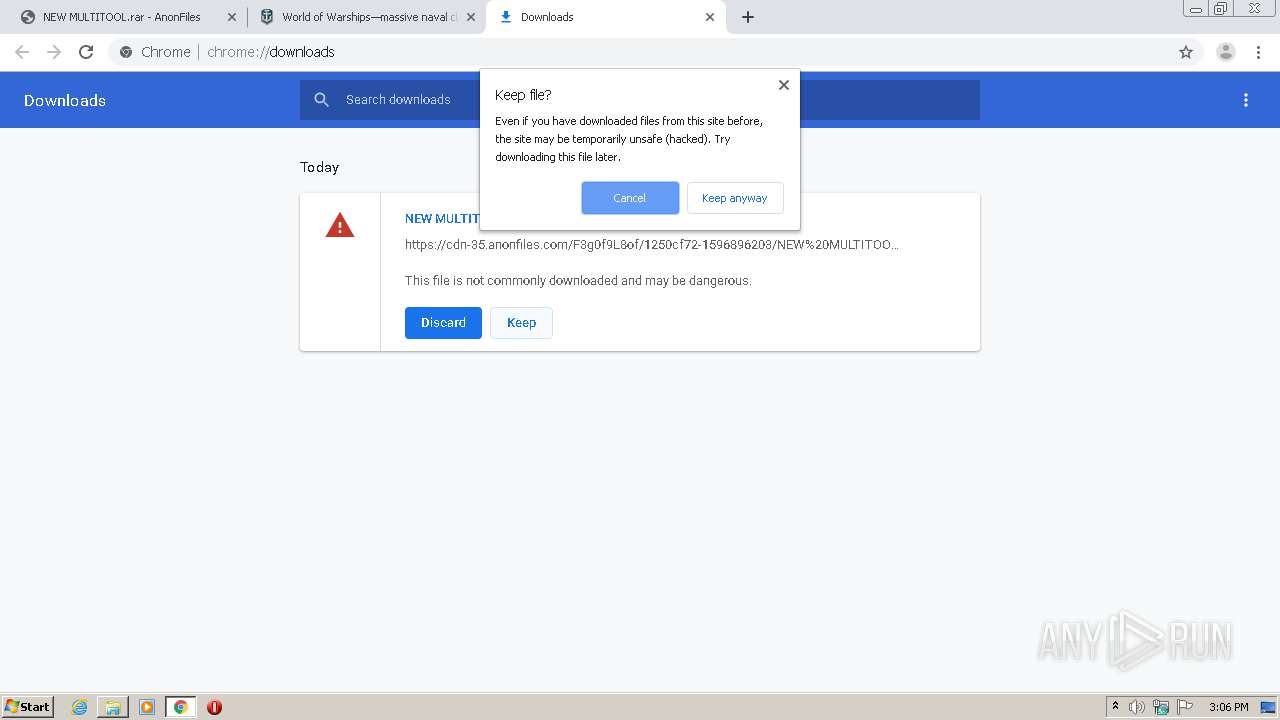
| URL: | https://anonfiles.com/F3g0f9L8of/NEW_MULTITOOL_rar |
| Full analysis: | https://app.any.run/tasks/1bb970e7-93e3-4a11-94f1-be6ceeb60edc |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 14:06:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4DD2A47B89DE75E3DC140FE2AE2A814F |
| SHA1: | FE3249B0C0FB997730B42FEC0E301D83ADC44521 |
| SHA256: | AC3F170FFFBFF452A152CF4FEDBEEB6289A14724232909A39228DDAE61BF503E |
| SSDEEP: | 3:N8M2ZHgpbxKVX:2M2GpI9 |
MALICIOUS
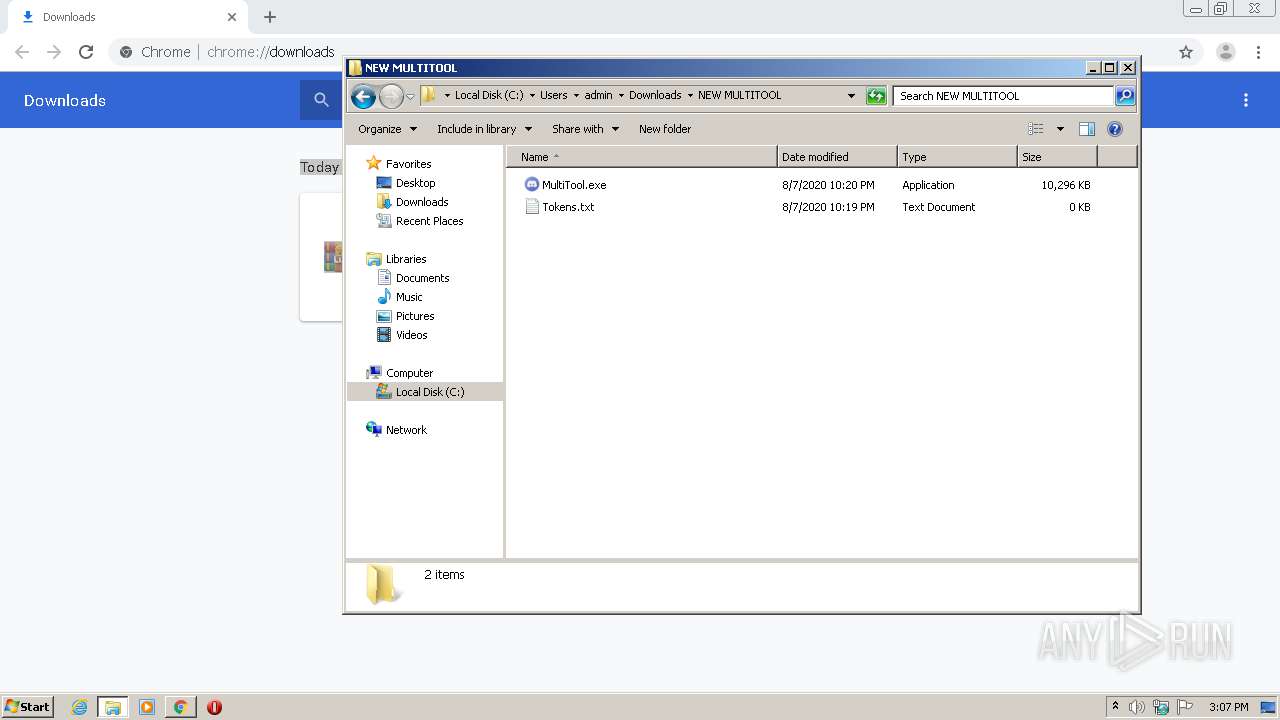
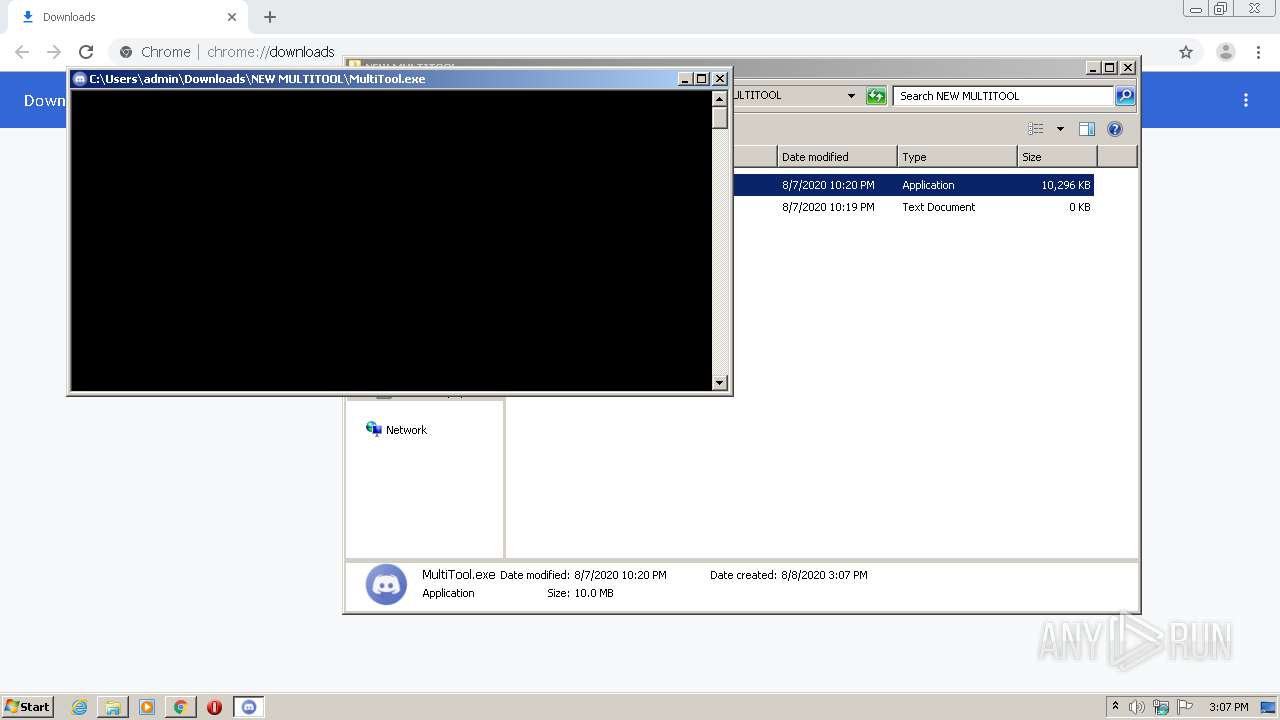
Application was dropped or rewritten from another process
- MultiTool.exe (PID: 968)
- MultiTool.exe (PID: 4092)
Loads dropped or rewritten executable
- MultiTool.exe (PID: 4092)
Actions looks like stealing of personal data
- MultiTool.exe (PID: 4092)
SUSPICIOUS
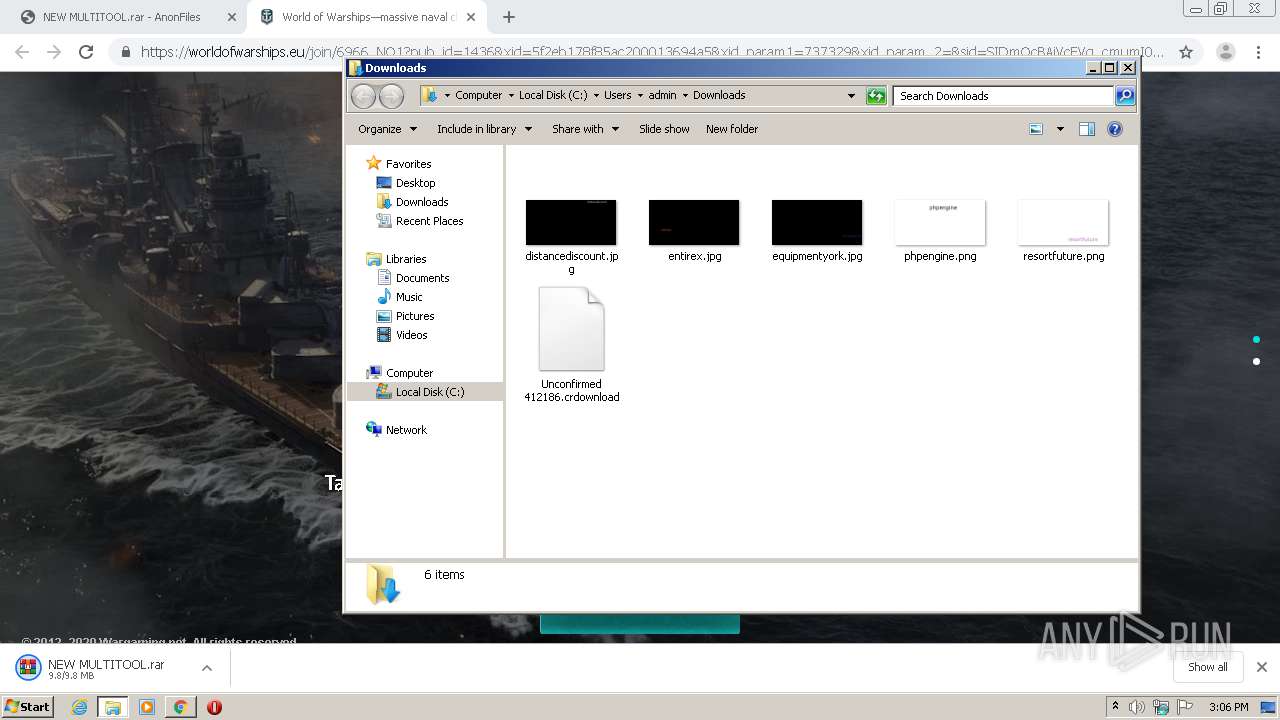
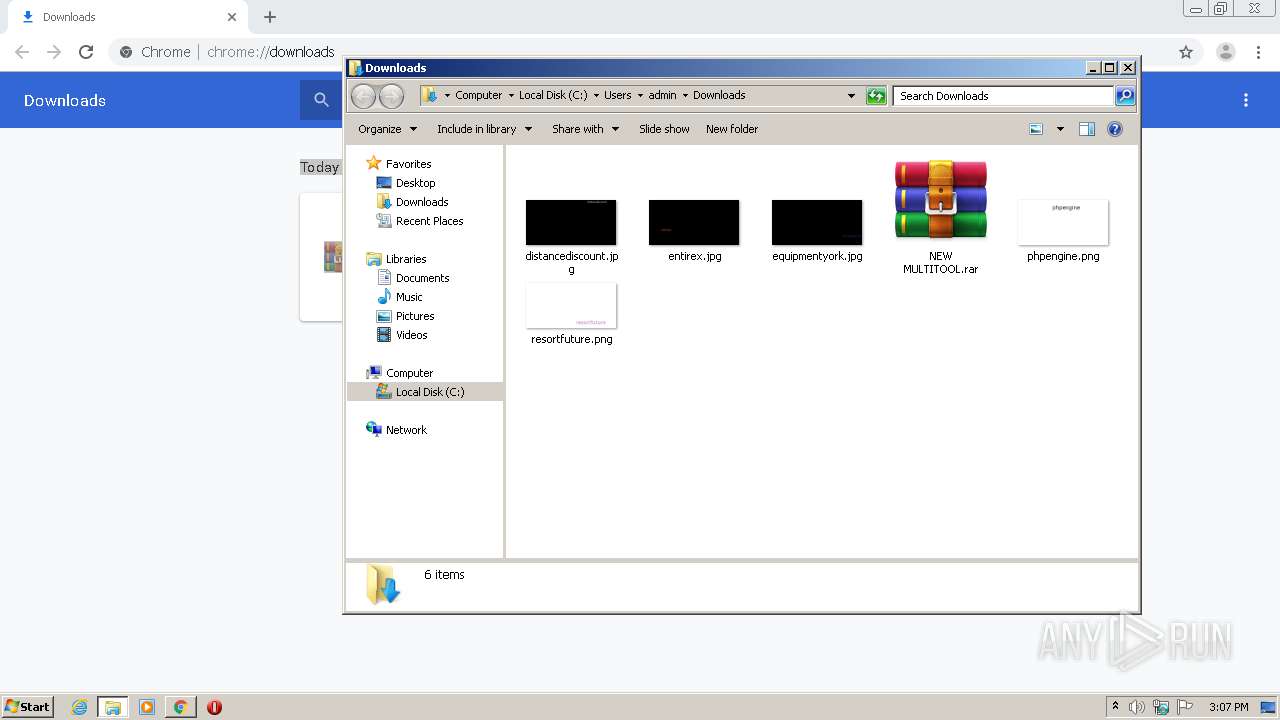
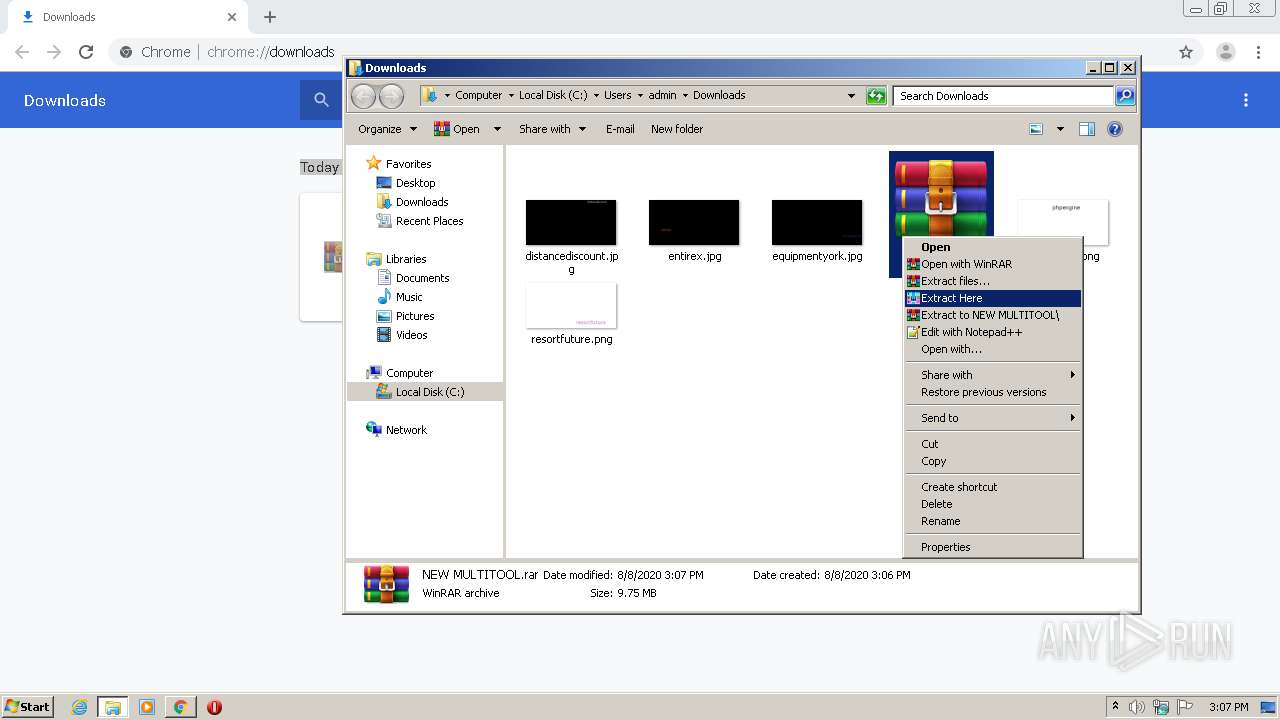
Executable content was dropped or overwritten
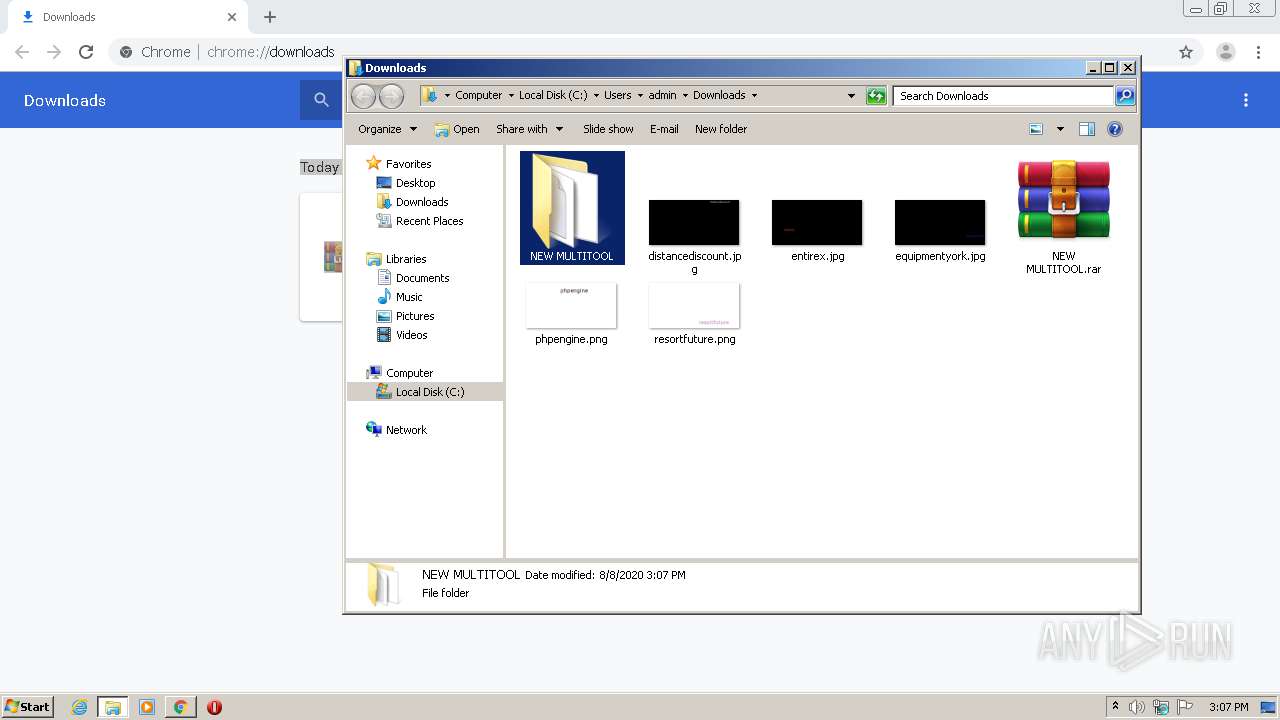
- WinRAR.exe (PID: 2852)
- MultiTool.exe (PID: 968)
Application launched itself
- MultiTool.exe (PID: 968)
Loads Python modules
- MultiTool.exe (PID: 4092)
Starts CMD.EXE for commands execution
- MultiTool.exe (PID: 4092)
INFO
Reads the hosts file
- chrome.exe (PID: 2688)
- chrome.exe (PID: 2268)
Reads Internet Cache Settings
- chrome.exe (PID: 2268)
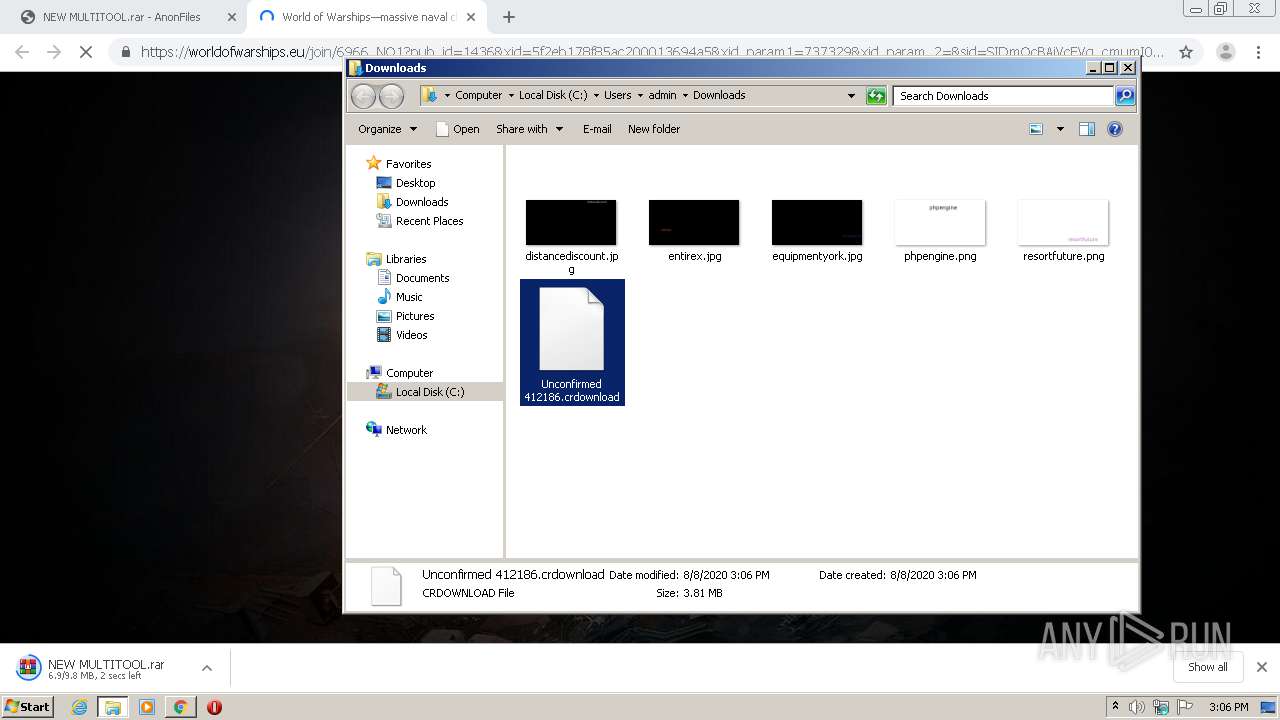
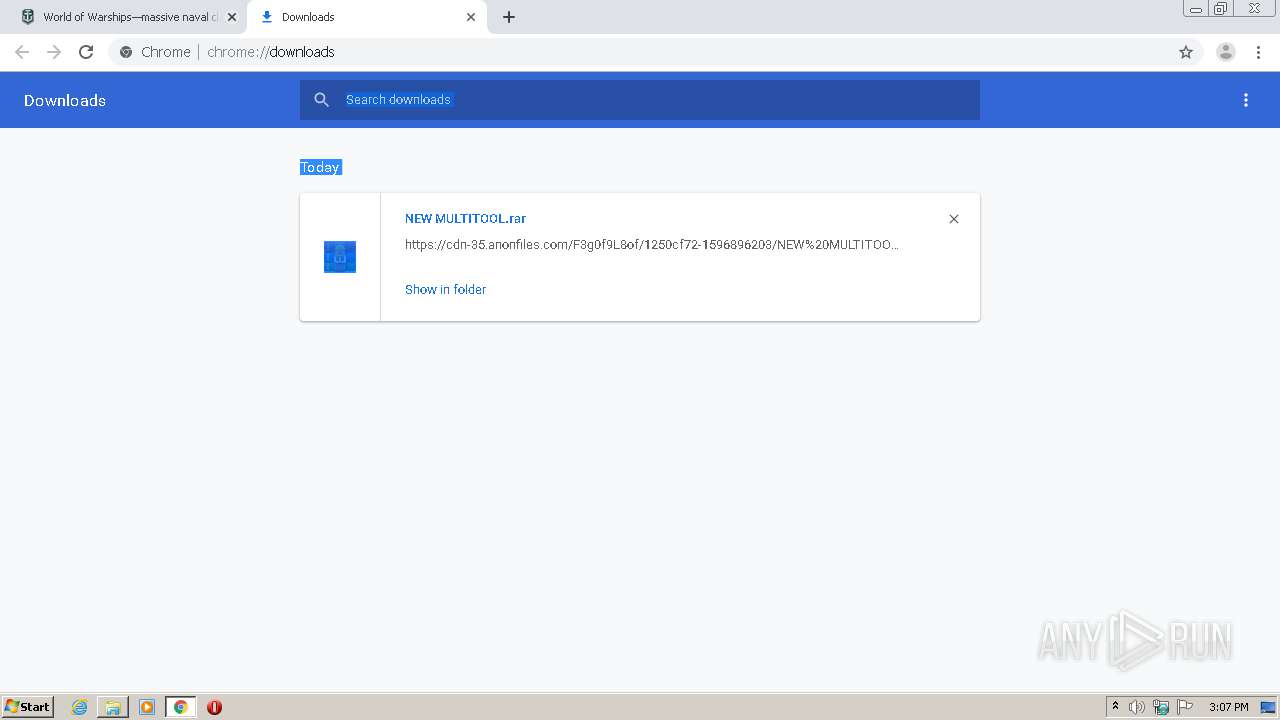
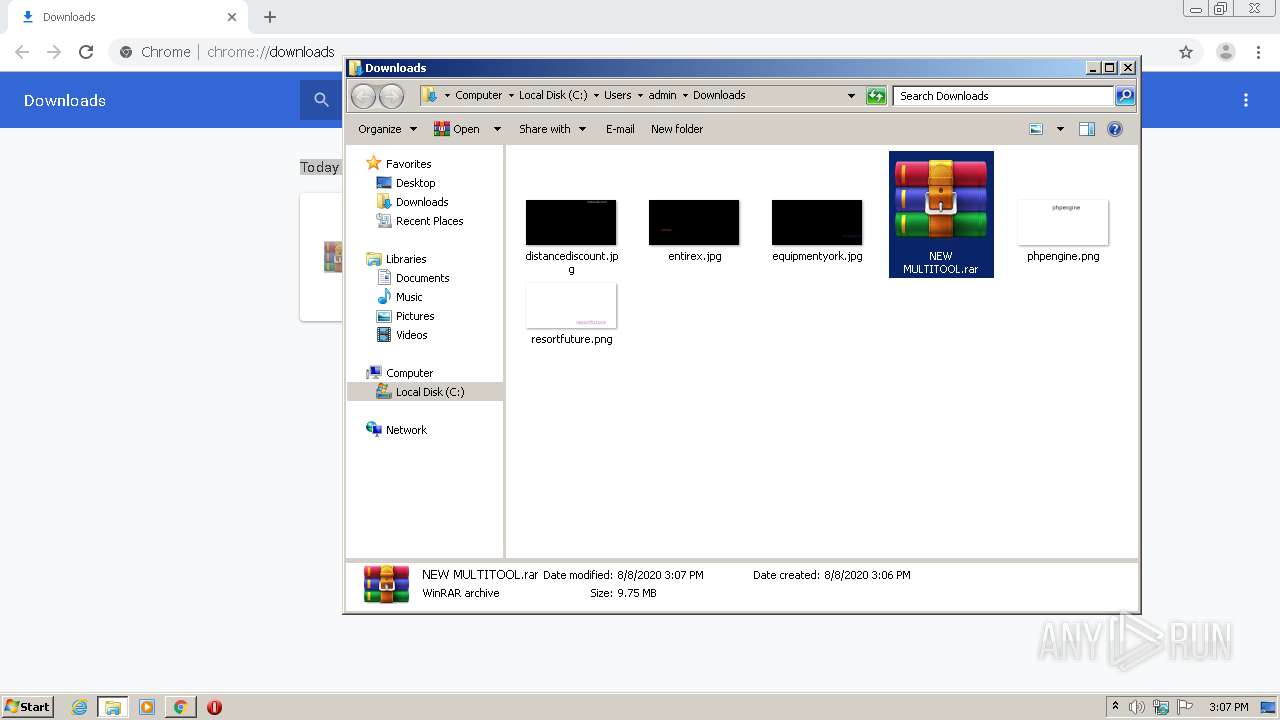
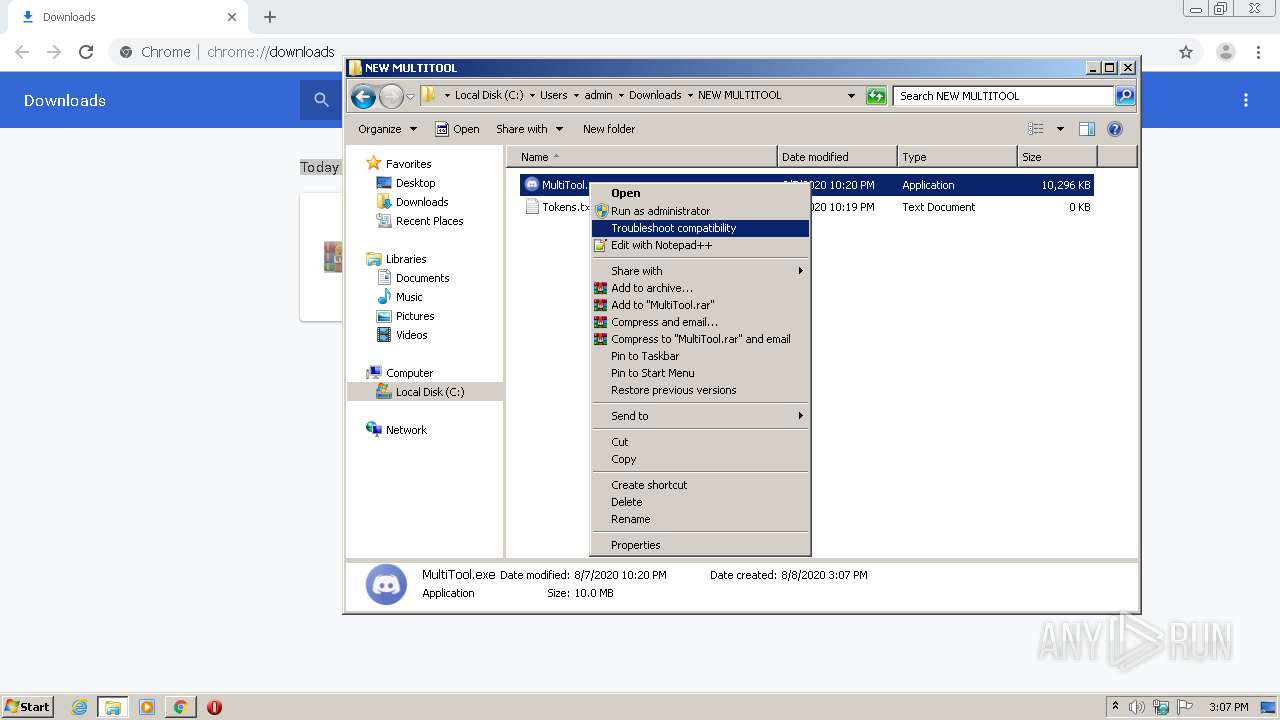
Manual execution by user
- WinRAR.exe (PID: 2852)
- MultiTool.exe (PID: 968)
Application launched itself
- chrome.exe (PID: 2268)
Dropped object may contain Bitcoin addresses
- MultiTool.exe (PID: 968)
Reads settings of System Certificates
- chrome.exe (PID: 2688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
25
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Users\admin\Downloads\NEW MULTITOOL\MultiTool.exe" | C:\Users\admin\Downloads\NEW MULTITOOL\MultiTool.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17330448331695133608,12932996924452269510,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14394380951086248284 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2264 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,17330448331695133608,12932996924452269510,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4864814163124452333 --mojo-platform-channel-handle=4220 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17330448331695133608,12932996924452269510,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4156459087757563029 --mojo-platform-channel-handle=4388 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17330448331695133608,12932996924452269510,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2546535204031264317 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17330448331695133608,12932996924452269510,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=990716545950224030 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17330448331695133608,12932996924452269510,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3714322642339705398 --mojo-platform-channel-handle=1980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17330448331695133608,12932996924452269510,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4971899856193613616 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://anonfiles.com/F3g0f9L8of/NEW_MULTITOOL_rar" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 044
Read events
934
Write events
105
Delete events
5
Modification events
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2268-13241369200854750 |
Value: 259 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2268-13241369200854750 |
Value: 259 | |||
Executable files
28
Suspicious files
67
Text files
1 001
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\db34ea5e-ec86-4e0f-bb66-bd0958f58f34.tmp | — | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe0897.TMP | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe08c6.TMP | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
75
DNS requests
55
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2688 | chrome.exe | 172.64.175.29:443 | anonfiles.com | Cloudflare Inc | US | shared |
2688 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2688 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2688 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
2688 | chrome.exe | 13.35.253.162:443 | djv99sxoqpv11.cloudfront.net | — | US | malicious |
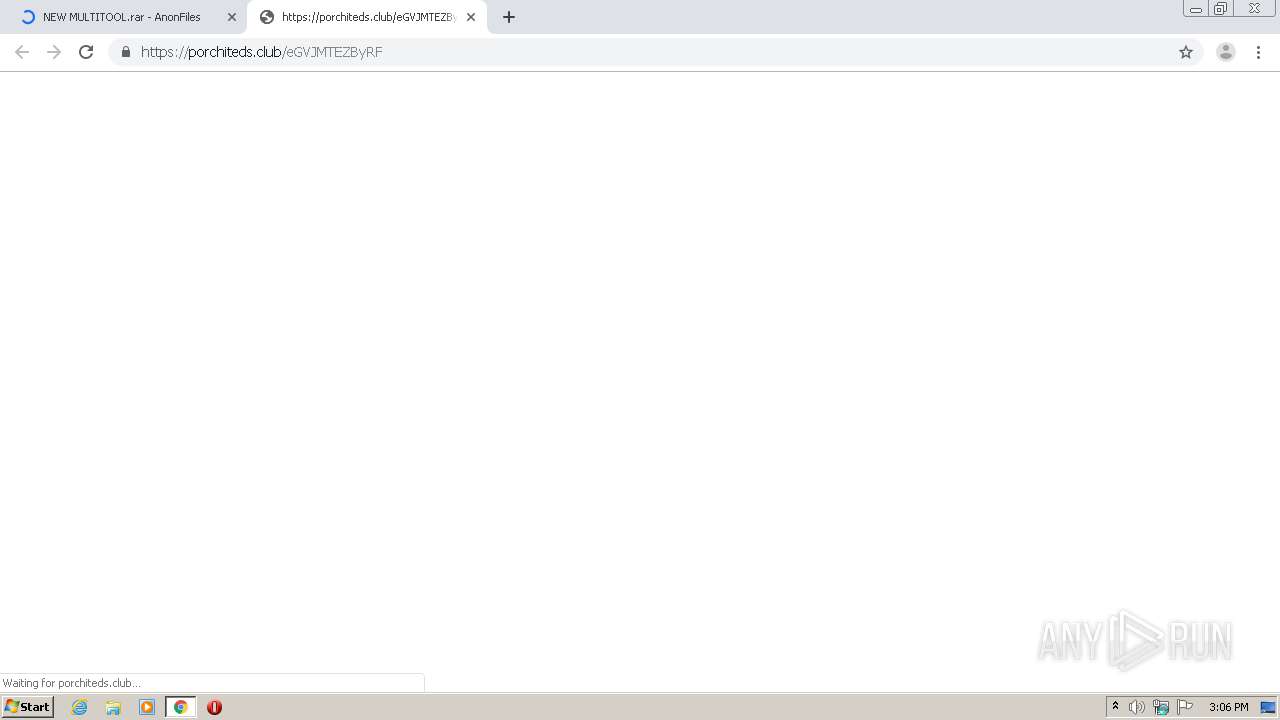
2688 | chrome.exe | 143.204.201.100:443 | porchiteds.club | — | US | suspicious |
2688 | chrome.exe | 34.196.151.230:443 | baconaces.pro | Amazon.com, Inc. | US | malicious |
2688 | chrome.exe | 143.204.201.101:443 | antrademic.club | — | US | malicious |
2688 | chrome.exe | 45.148.16.59:443 | cdn-35.anonfiles.com | — | — | suspicious |
2688 | chrome.exe | 52.86.219.129:443 | baconaces.pro | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
baconaces.pro |
| shared |
porchiteds.club |
| malicious |
antrademic.club |
| malicious |
providentsopport.site |
| whitelisted |
cdn-35.anonfiles.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4092 | MultiTool.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
4092 | MultiTool.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1 ETPRO signatures available at the full report