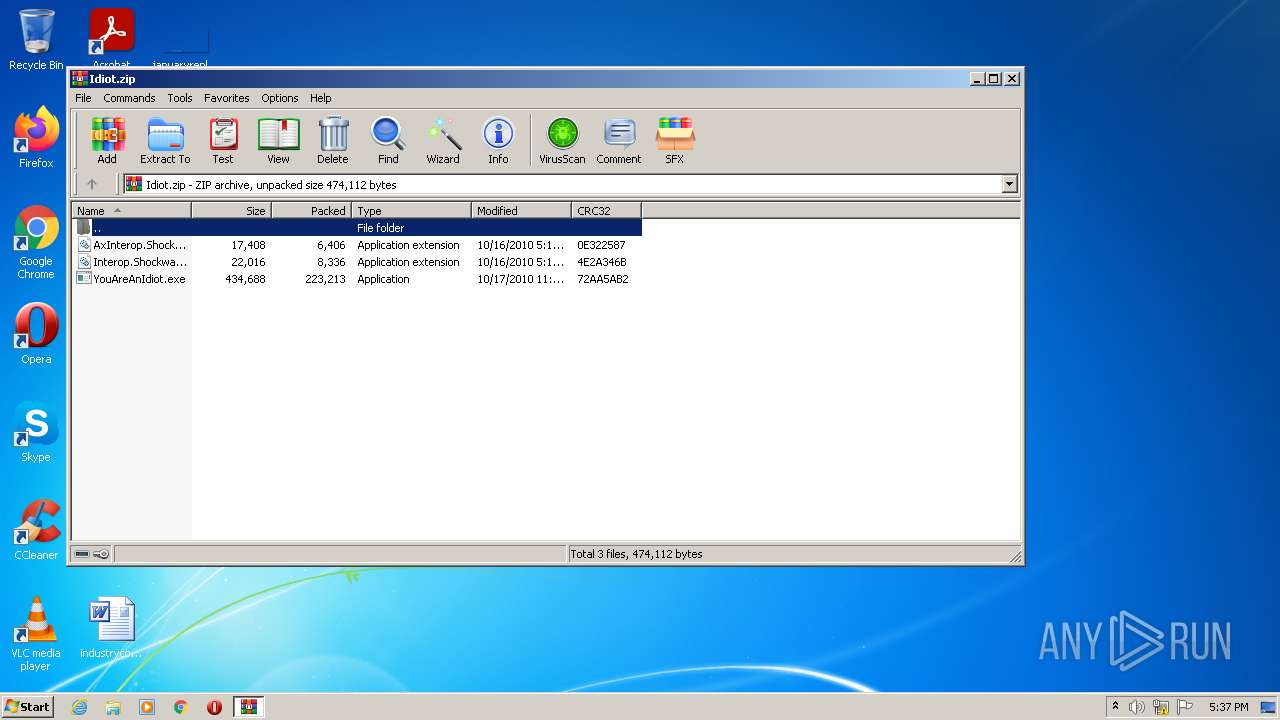
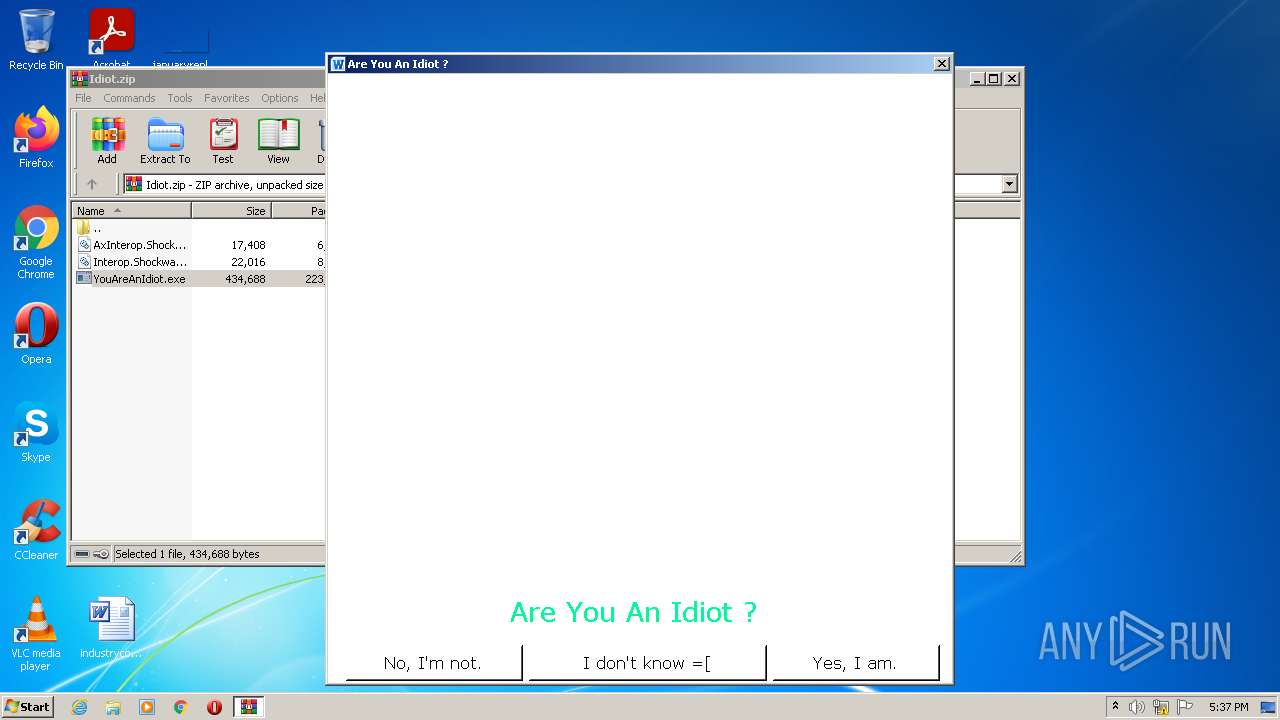
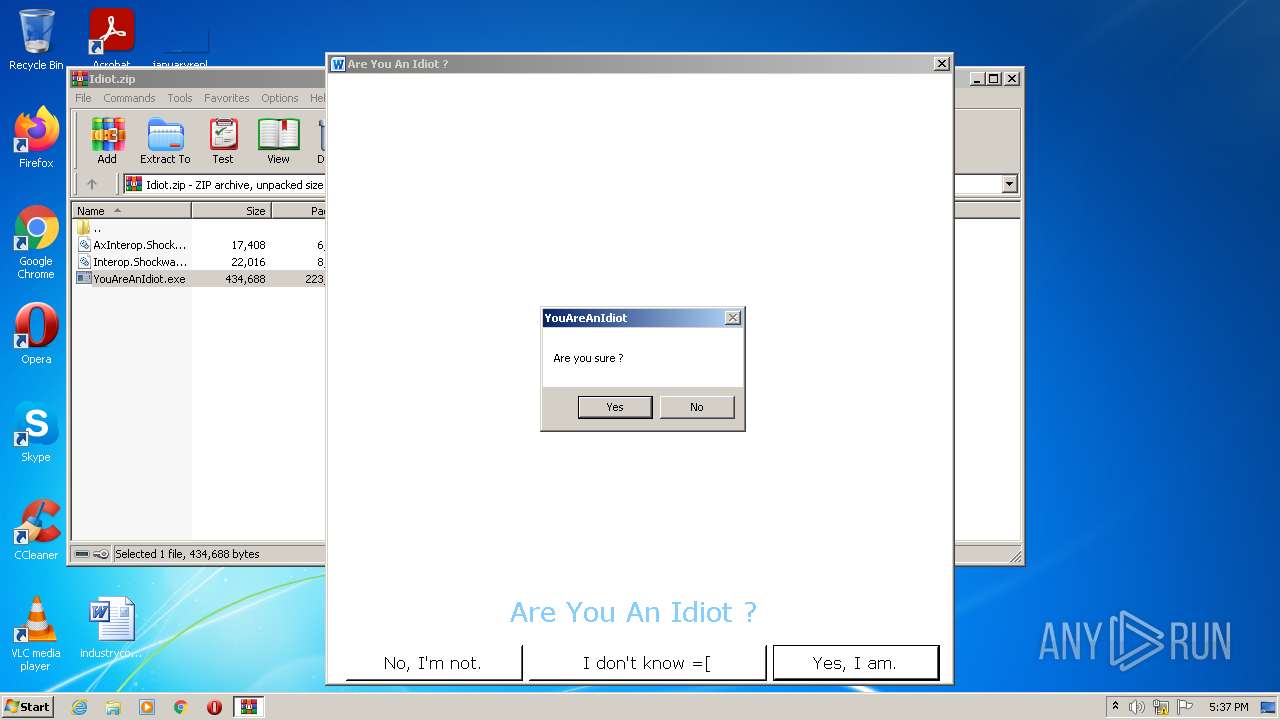
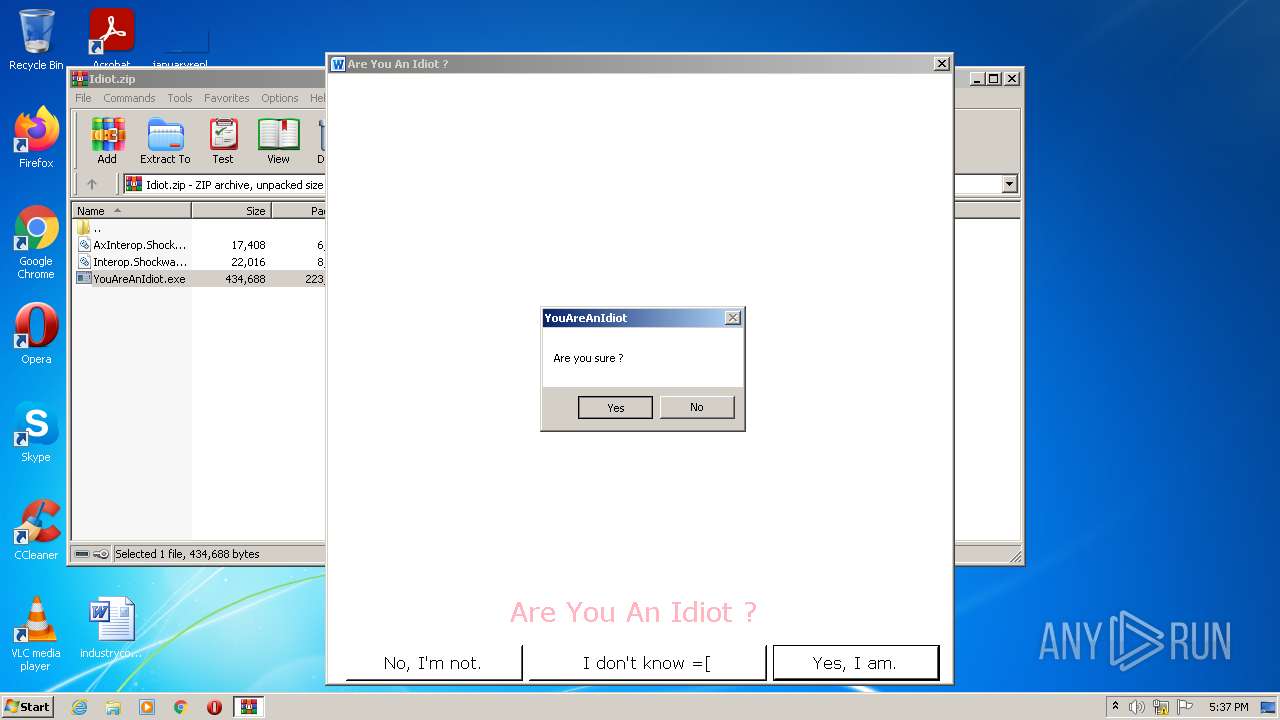
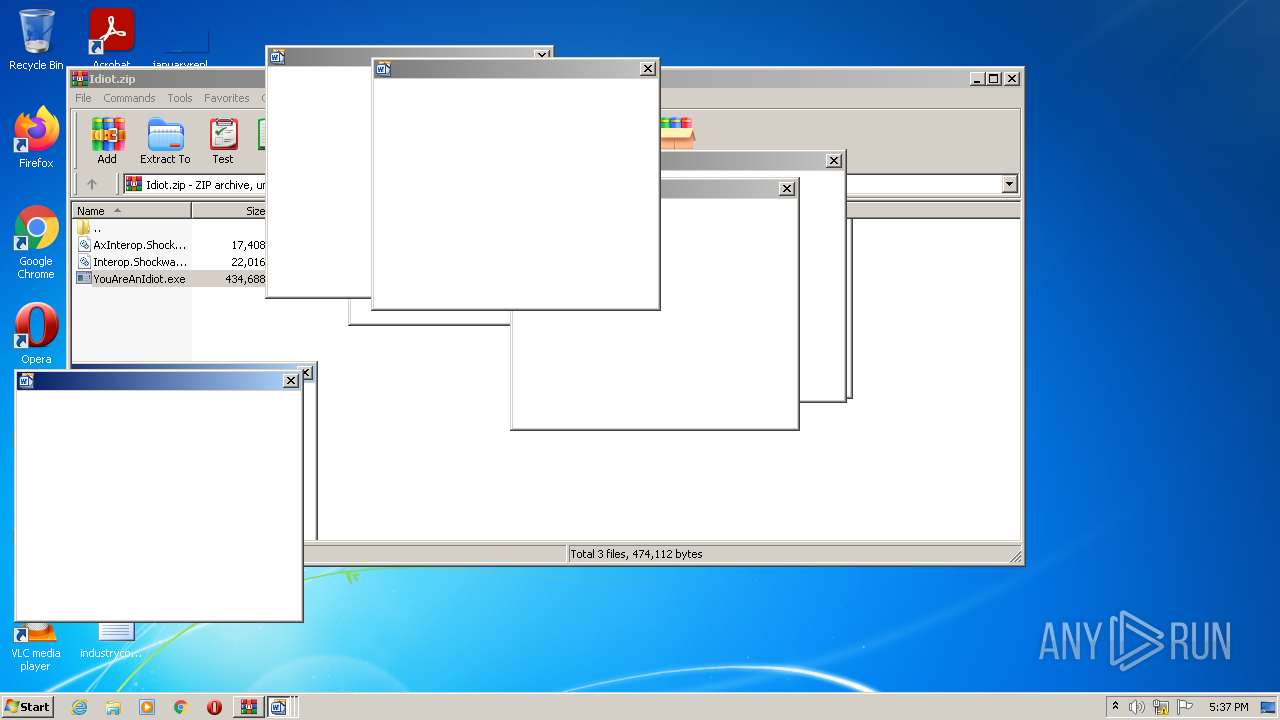
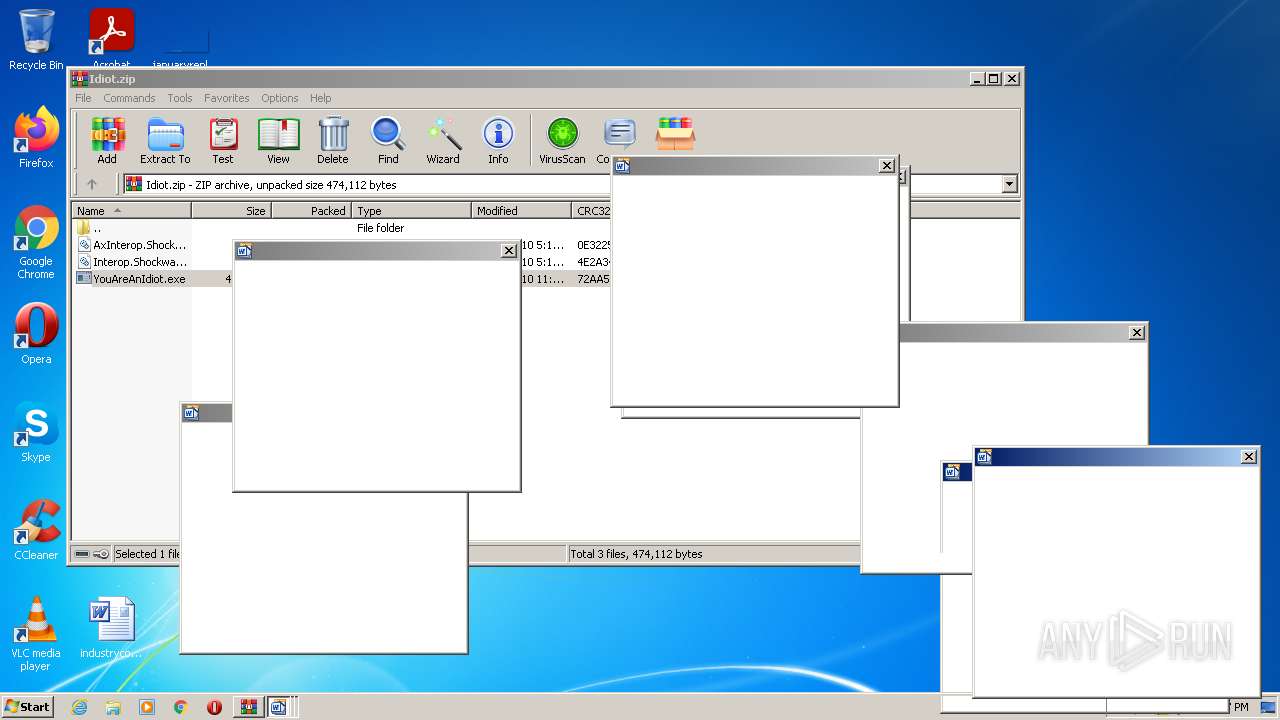
| File name: | Idiot.zip |
| Full analysis: | https://app.any.run/tasks/c81446c0-f7ee-4aa1-977e-187e0f686d7e |
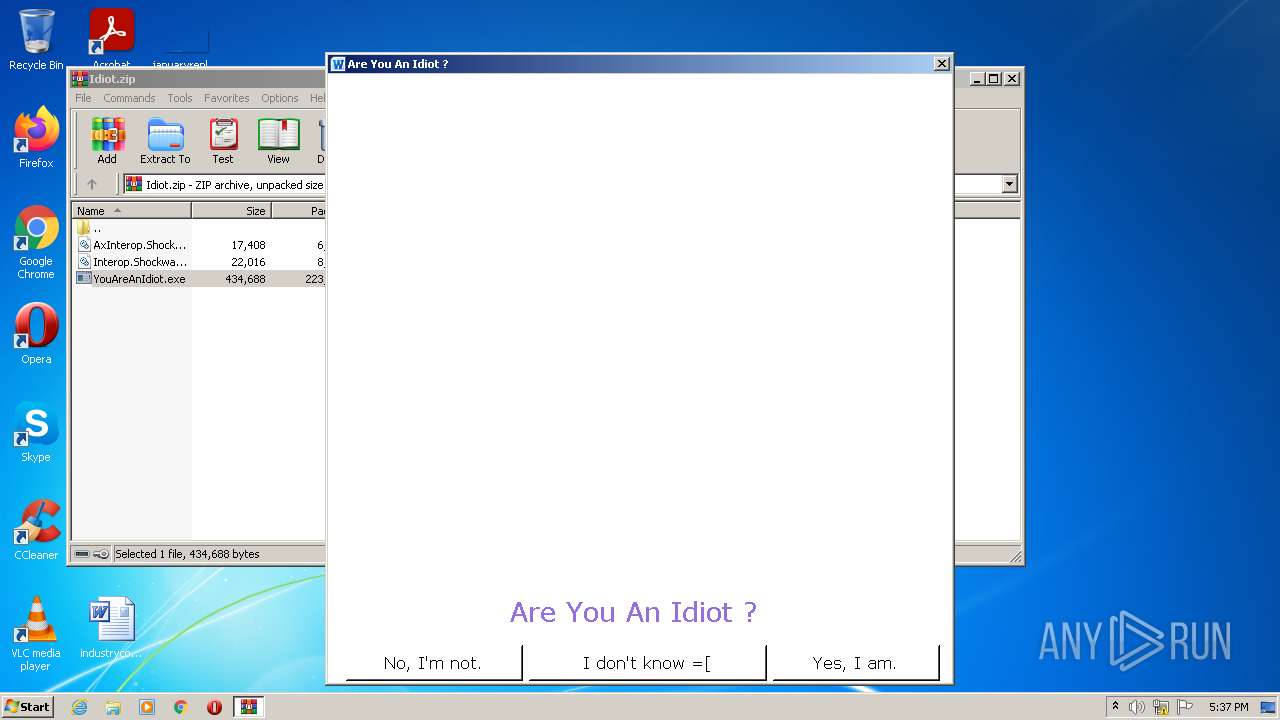
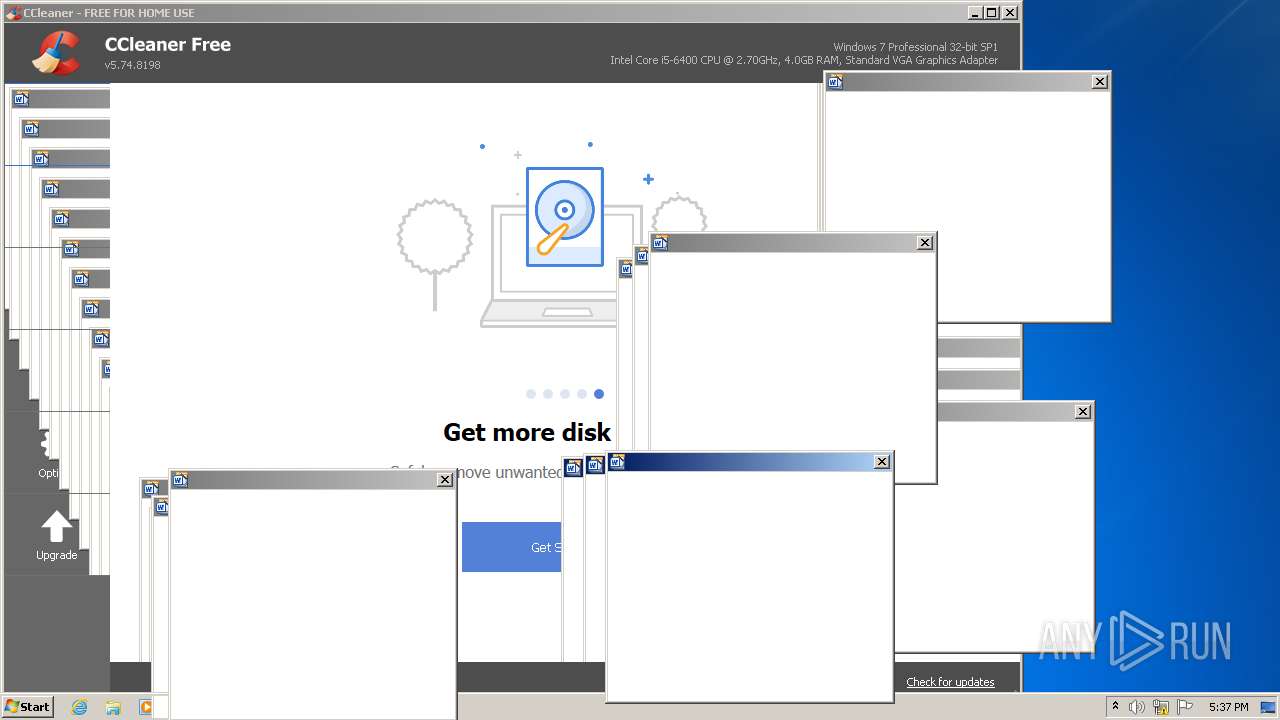
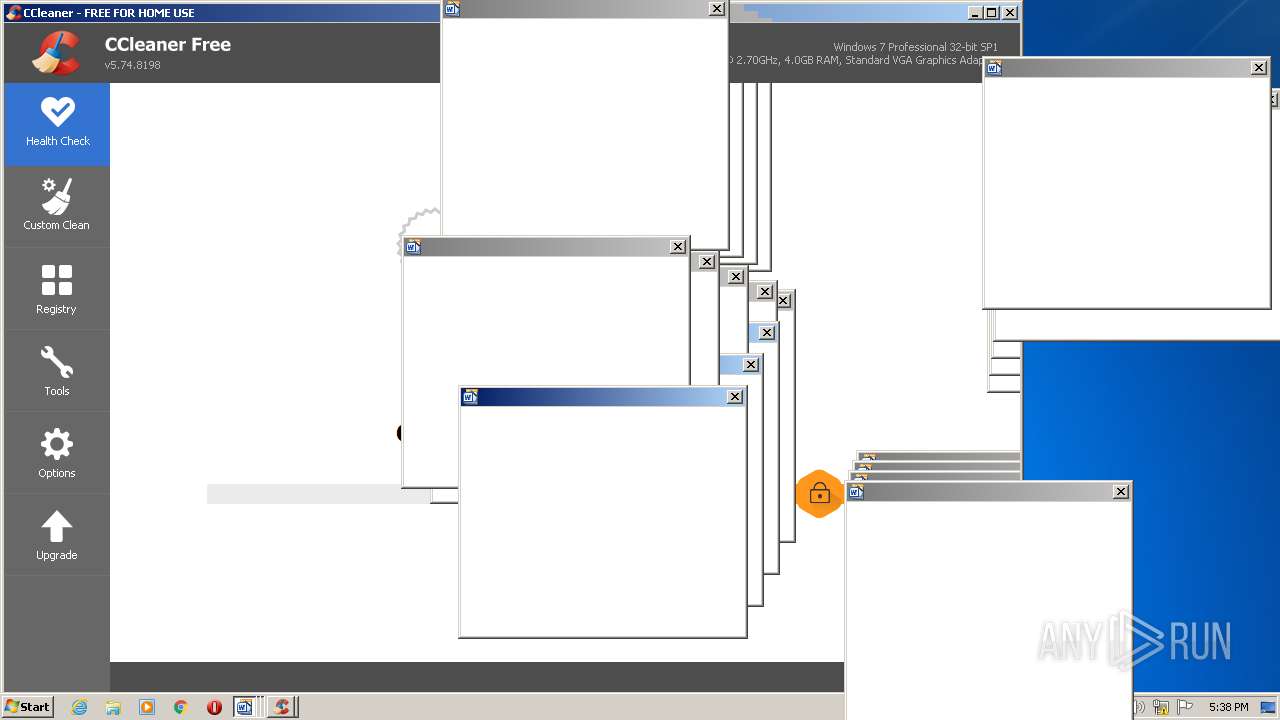
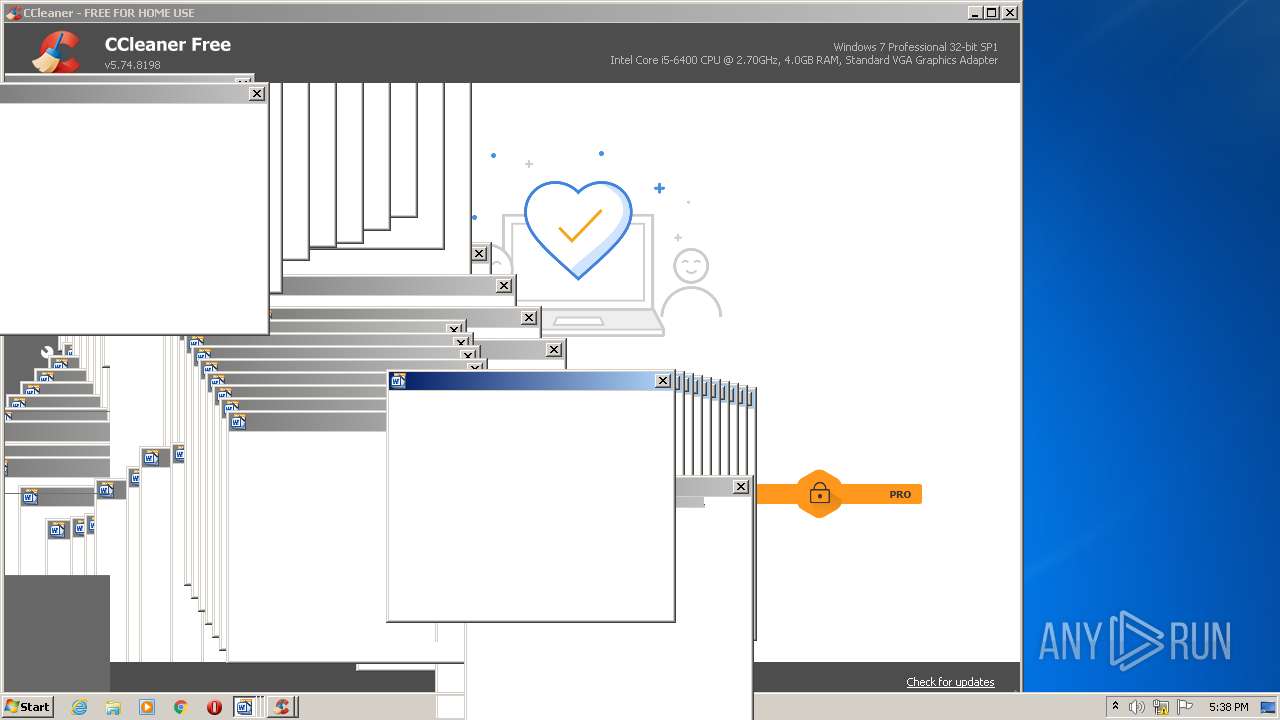
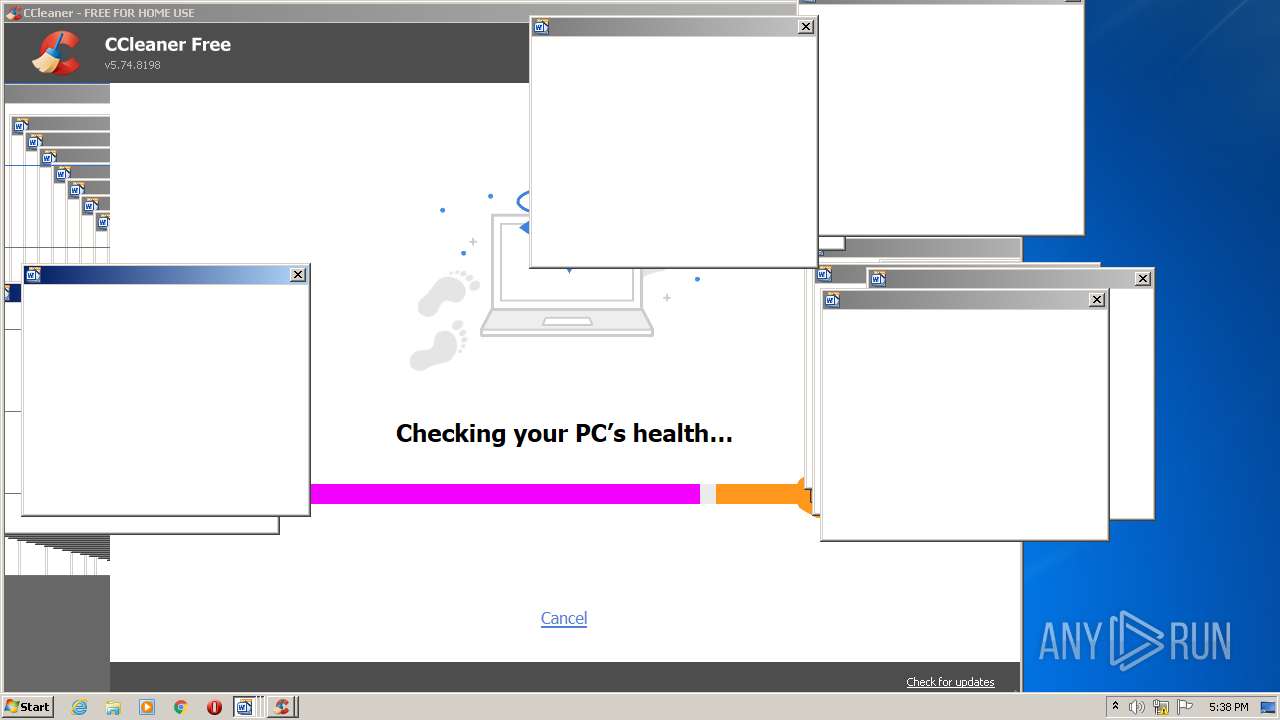
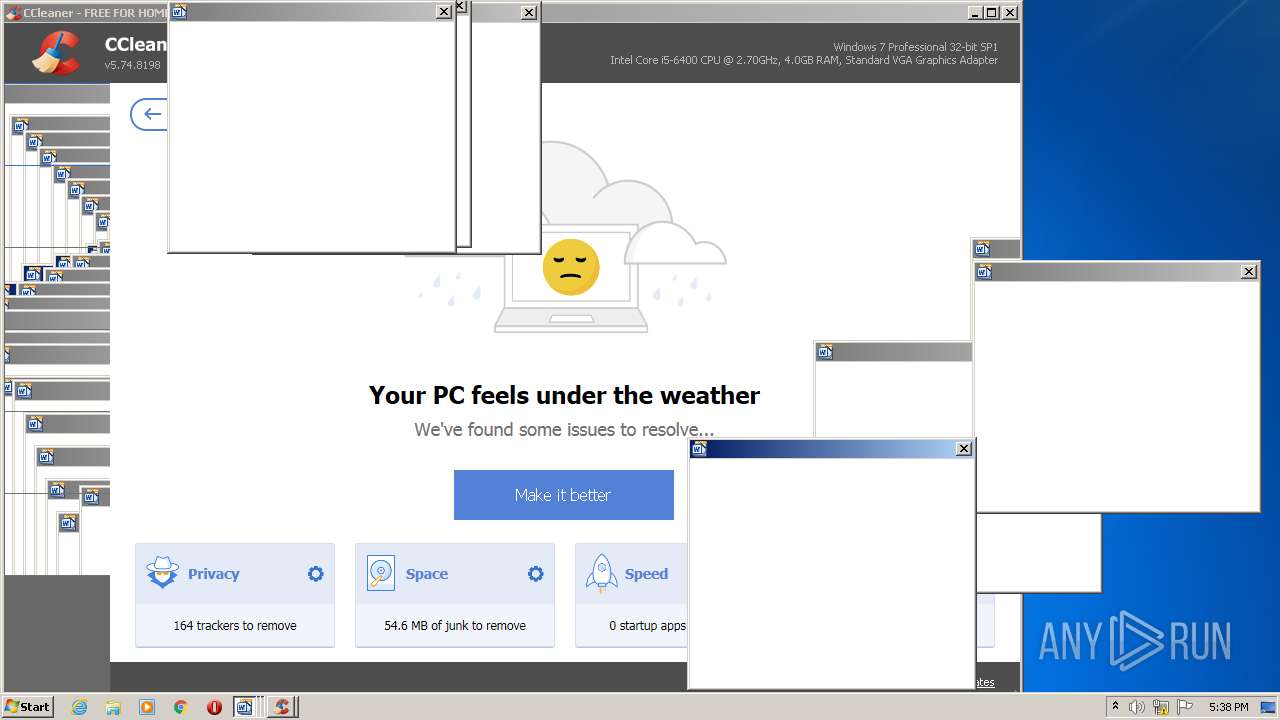
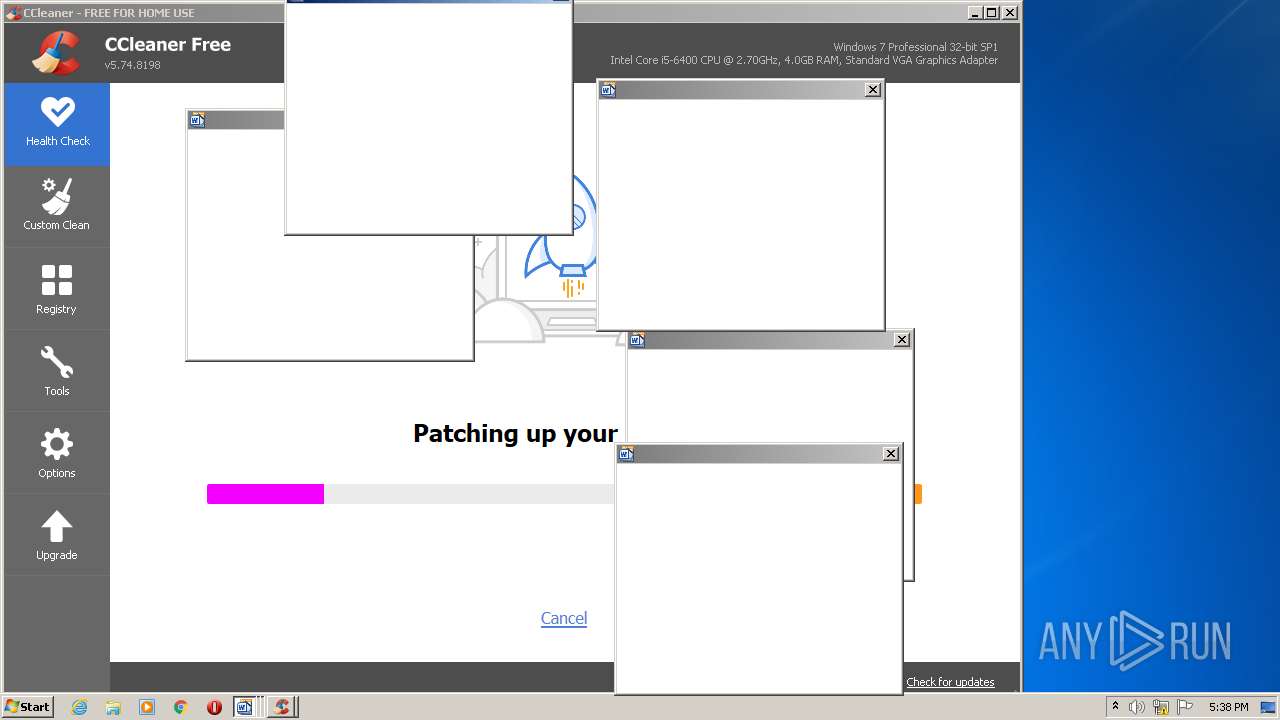
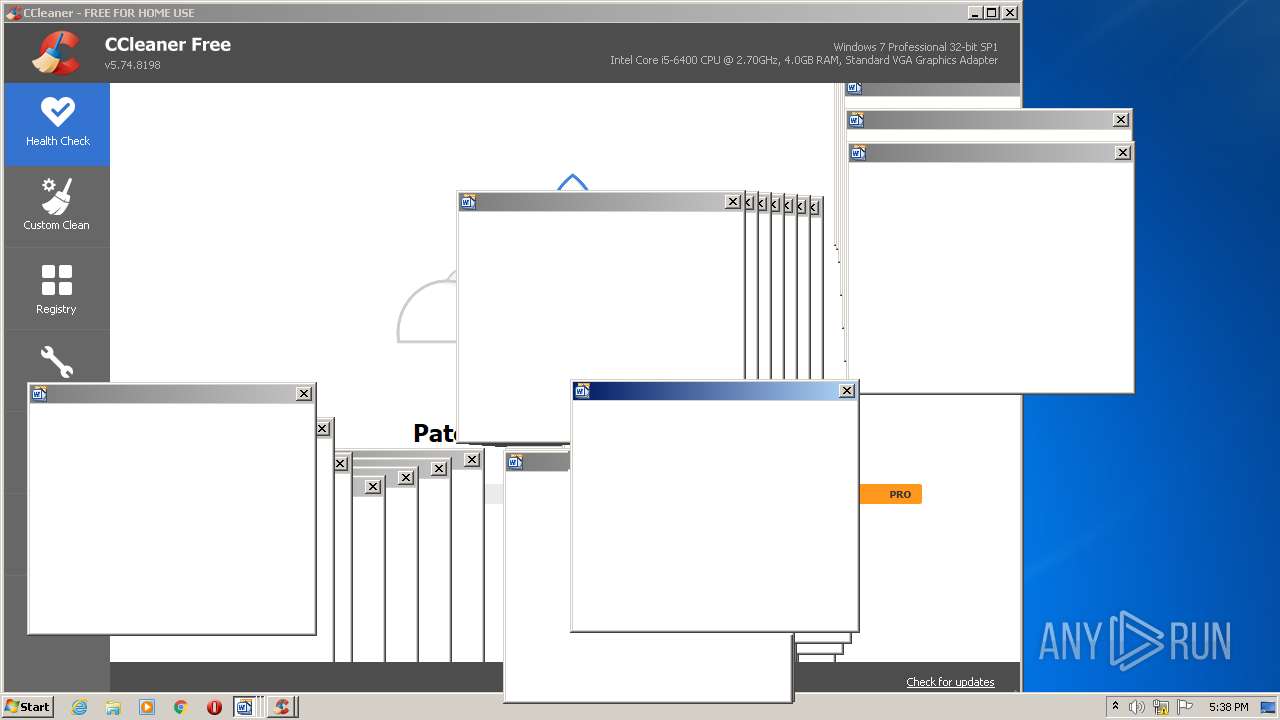
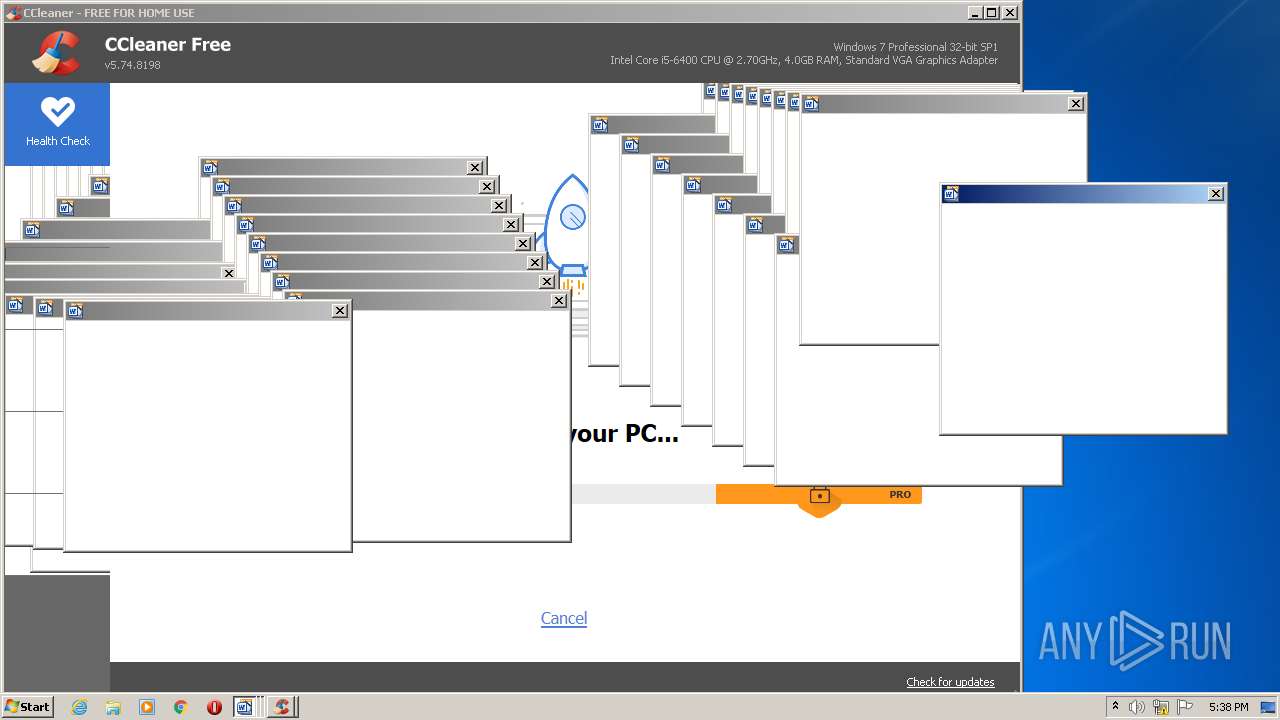
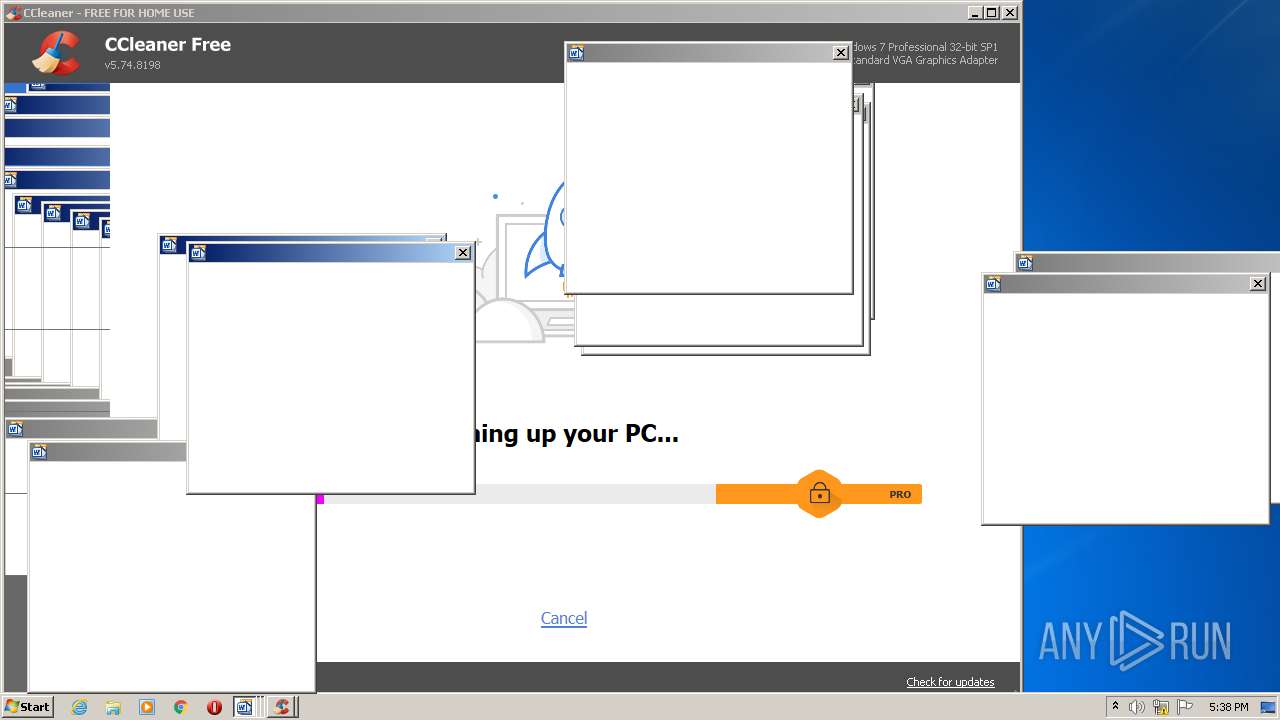
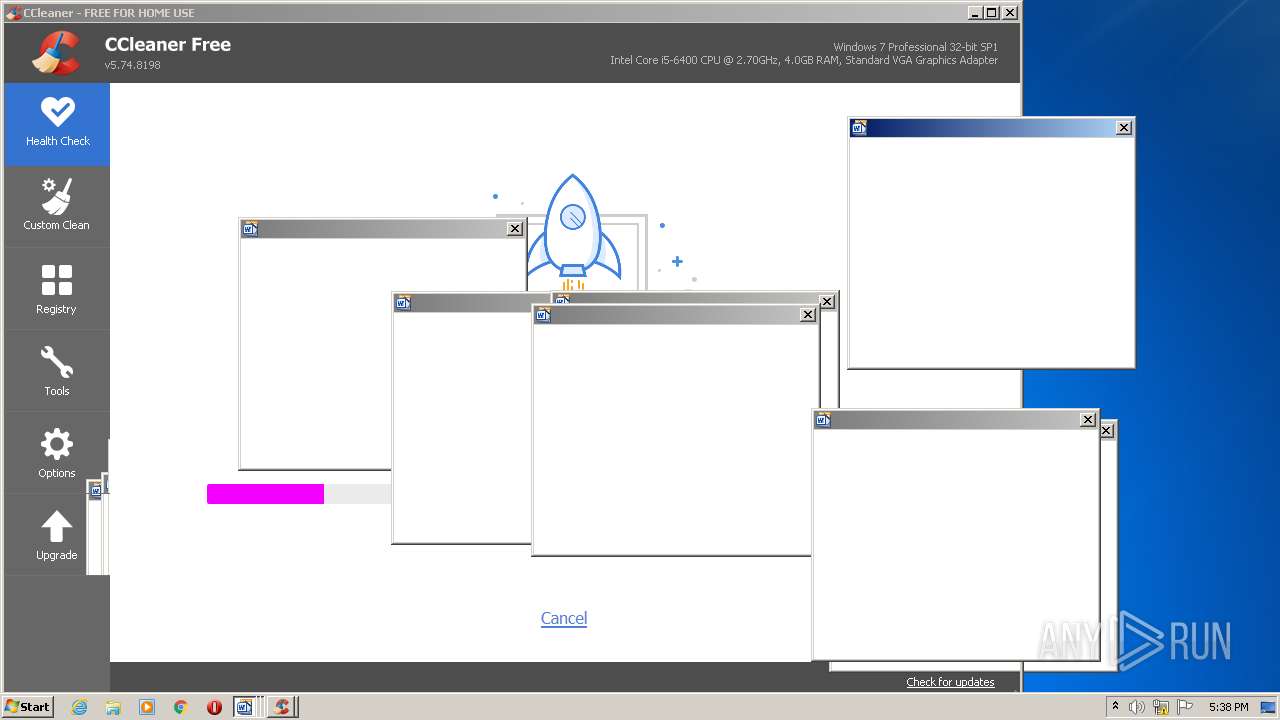
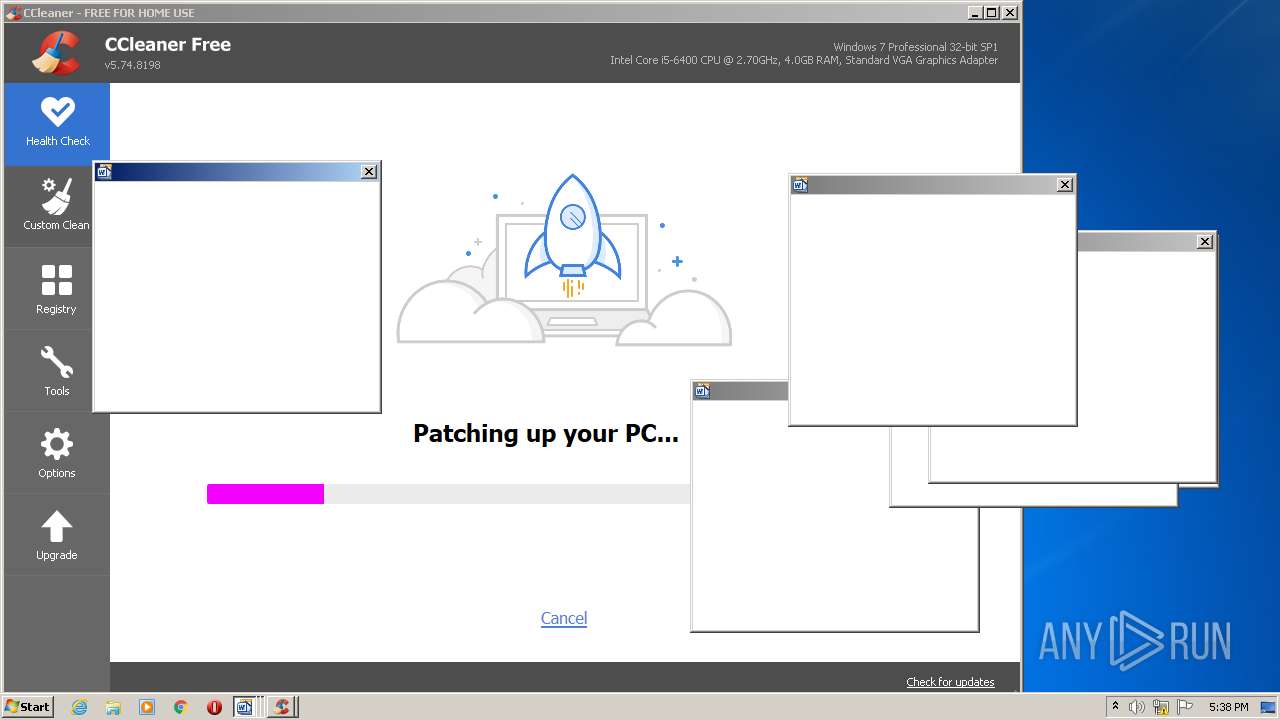
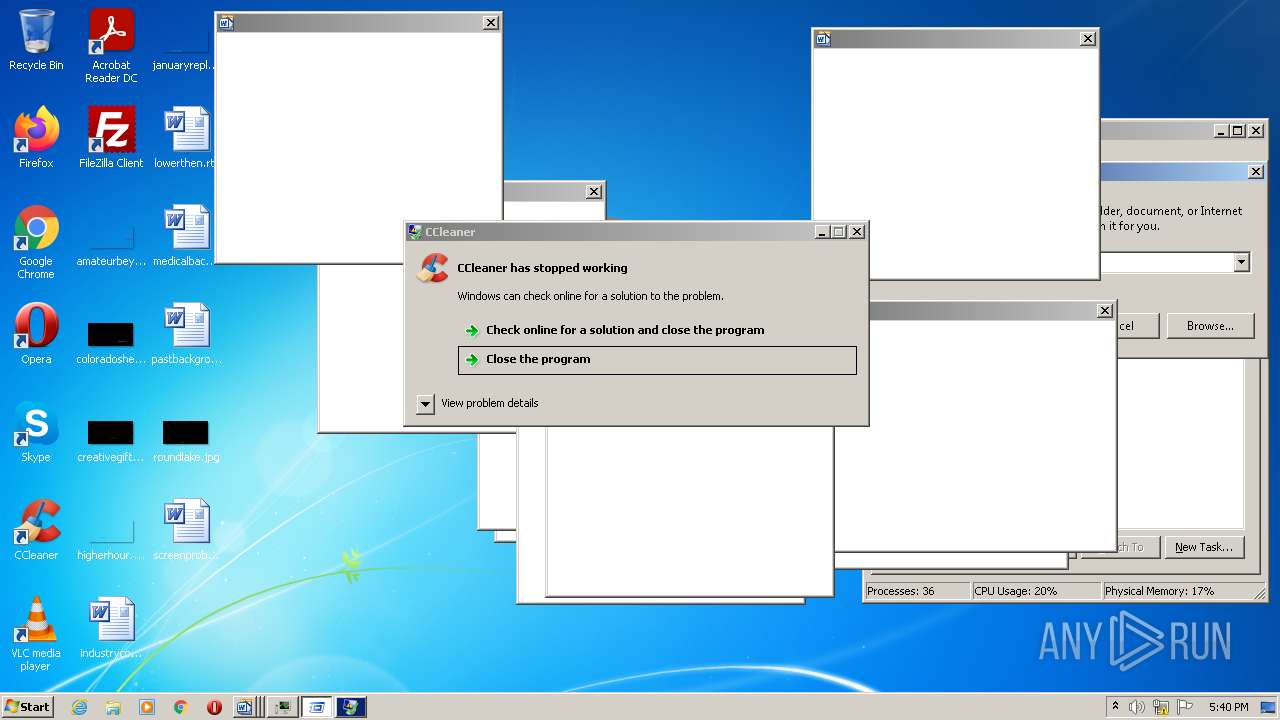
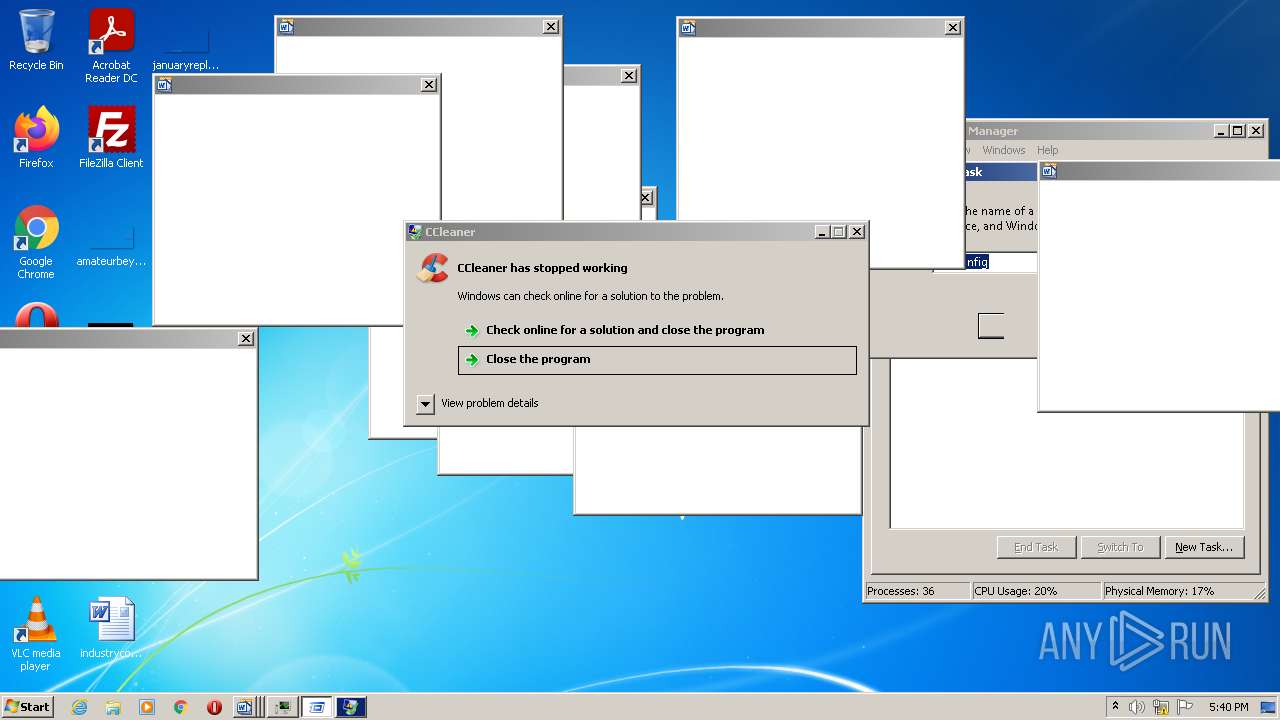
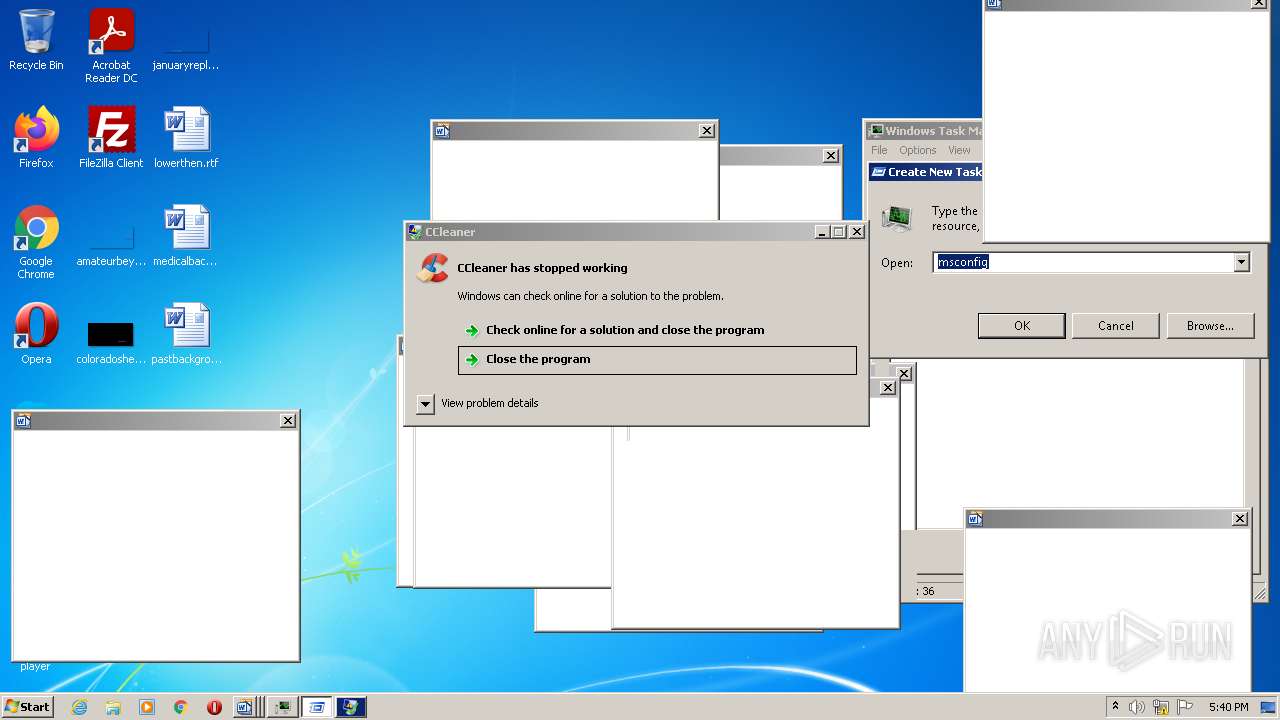
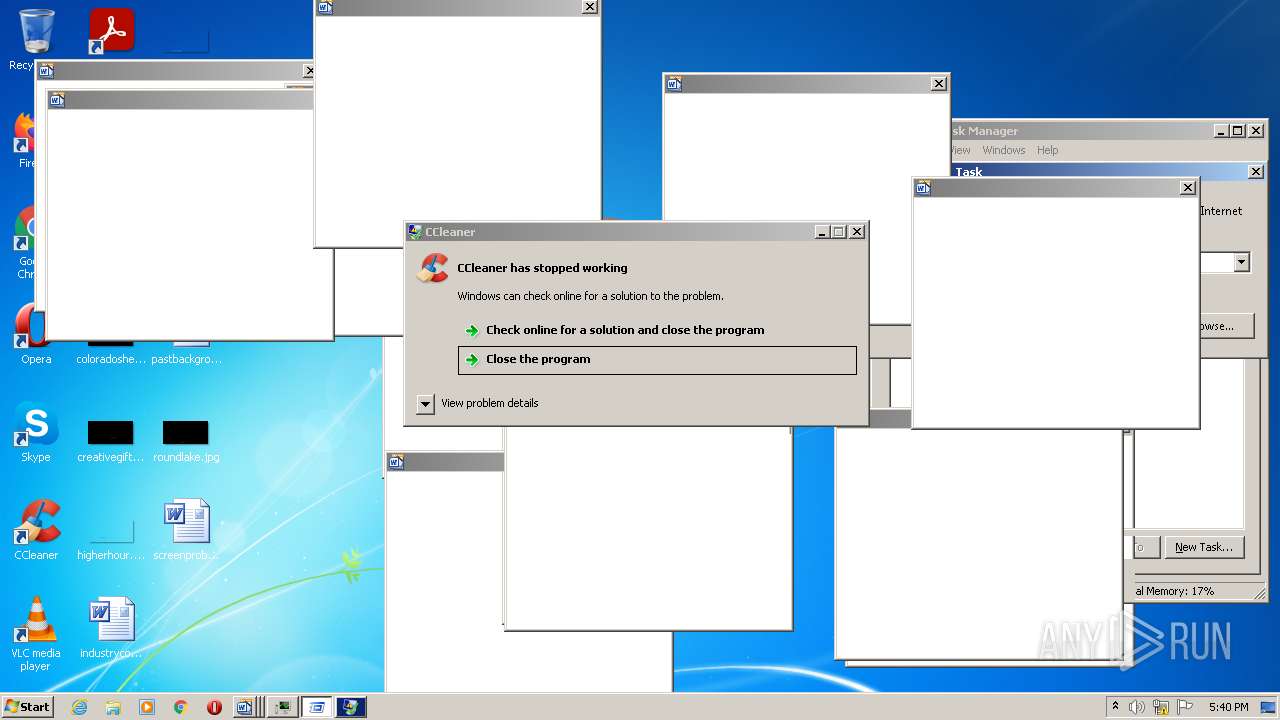
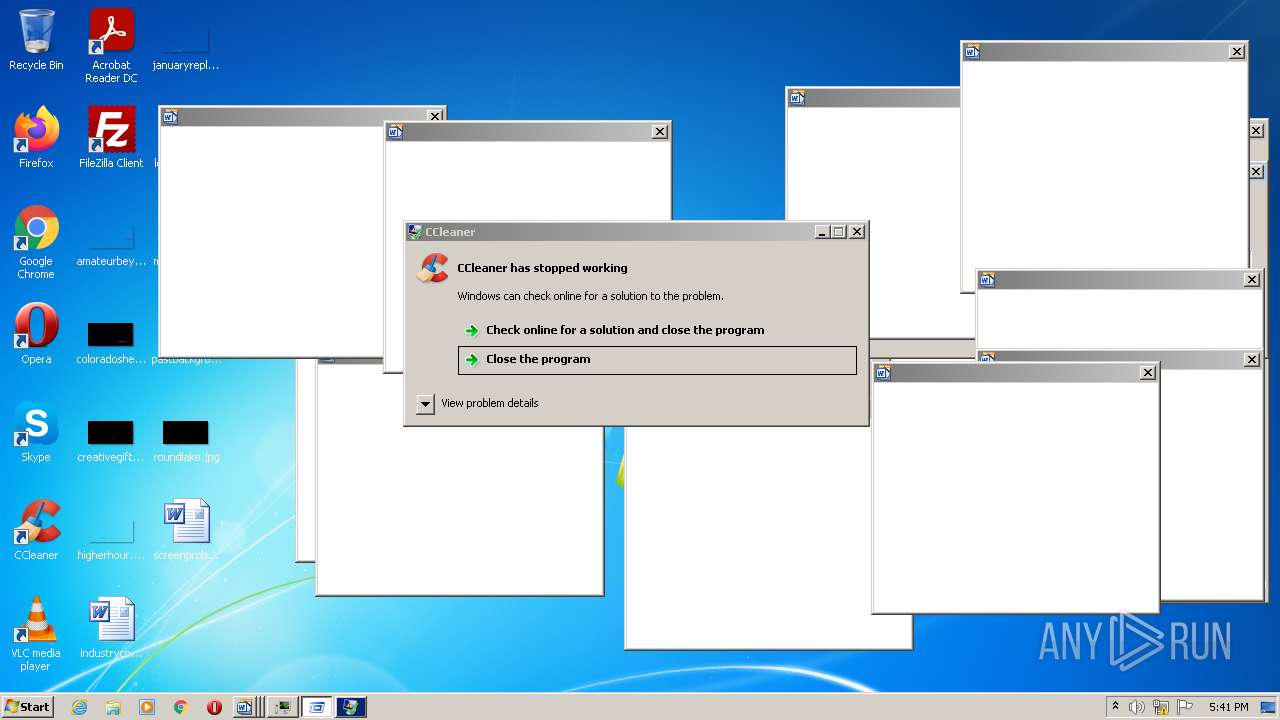
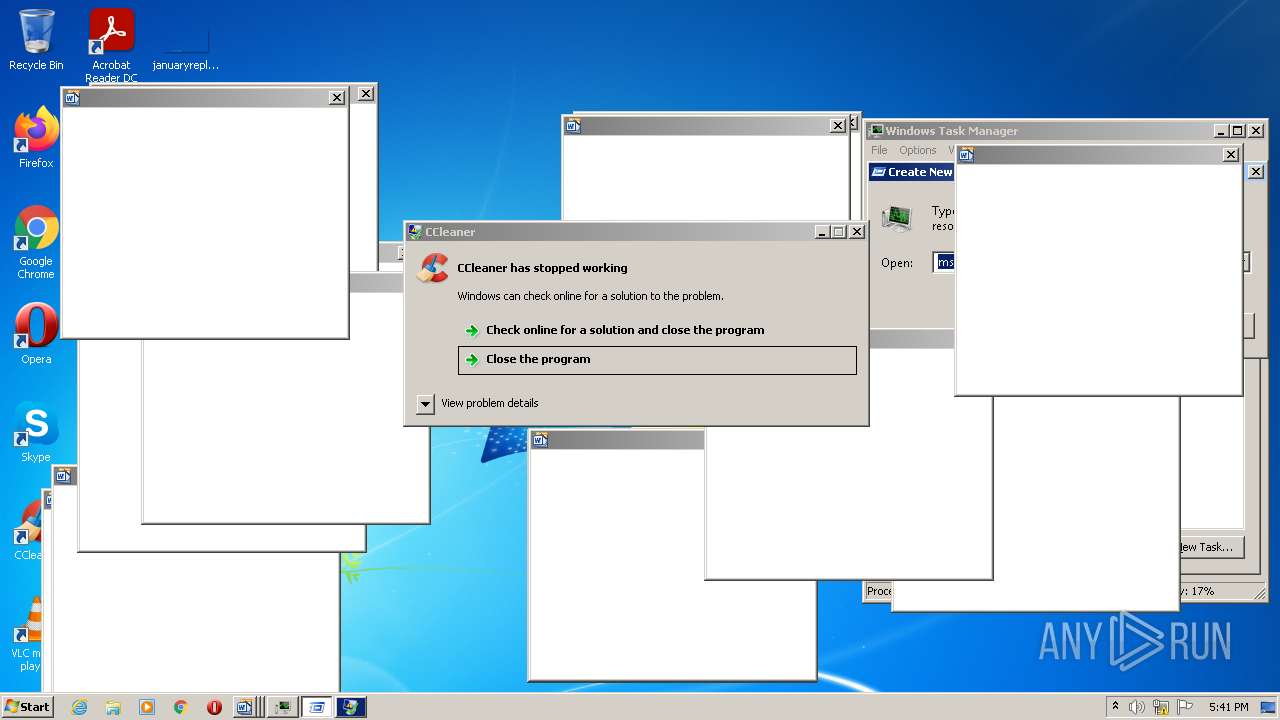
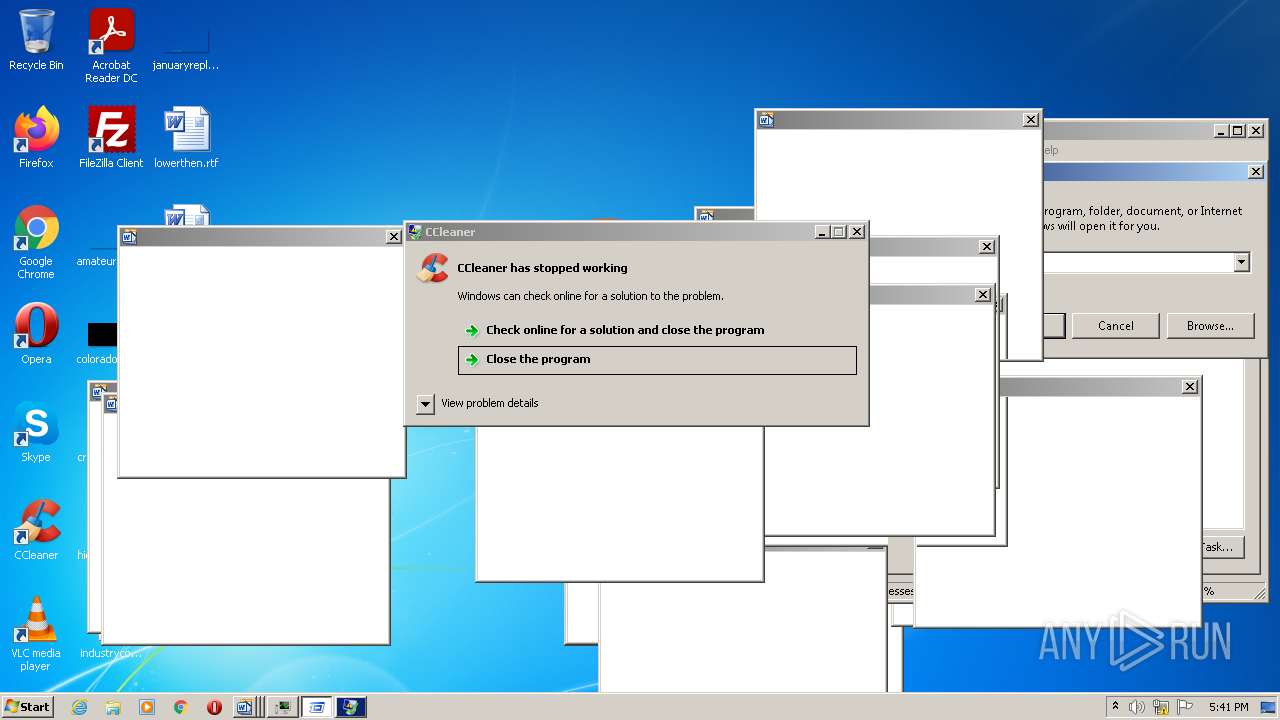
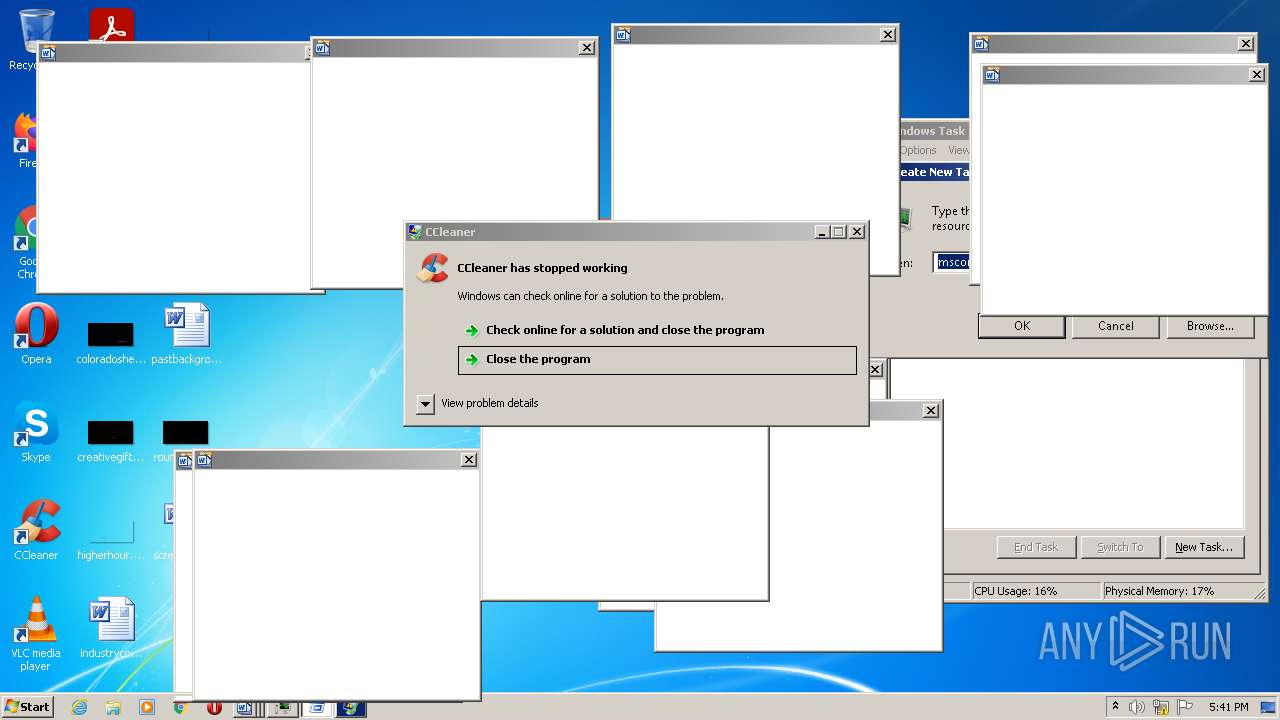
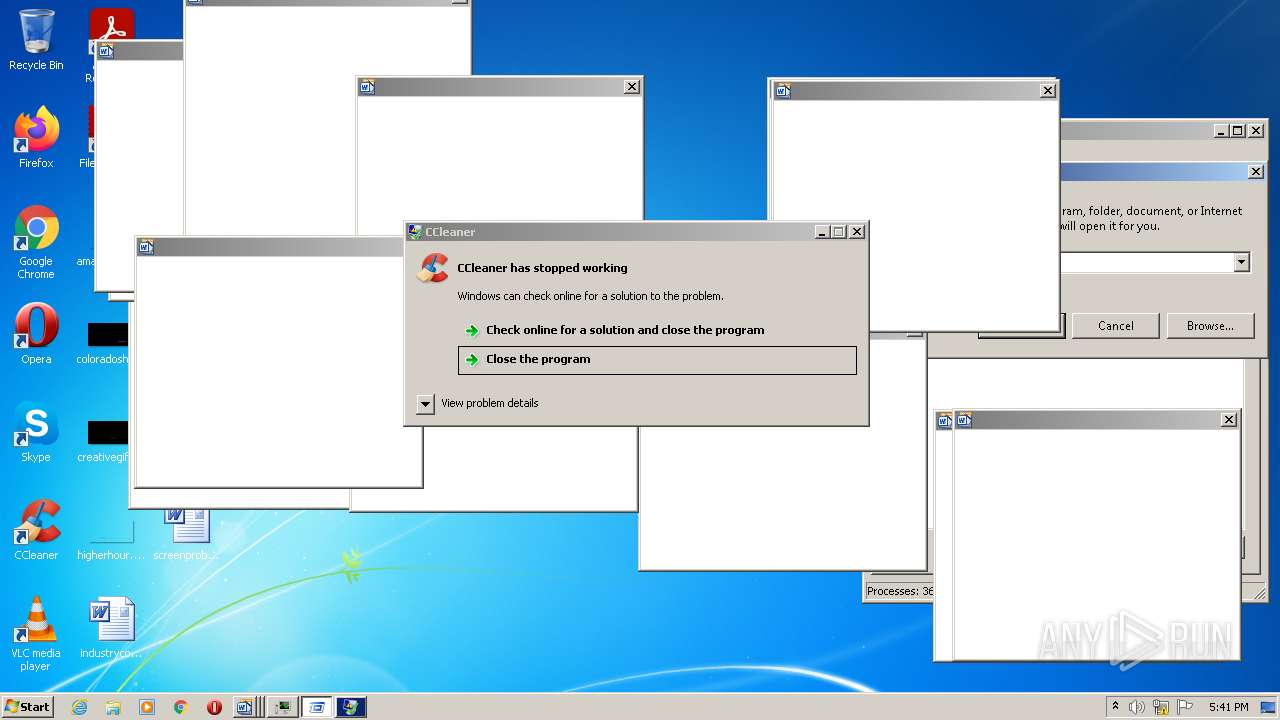
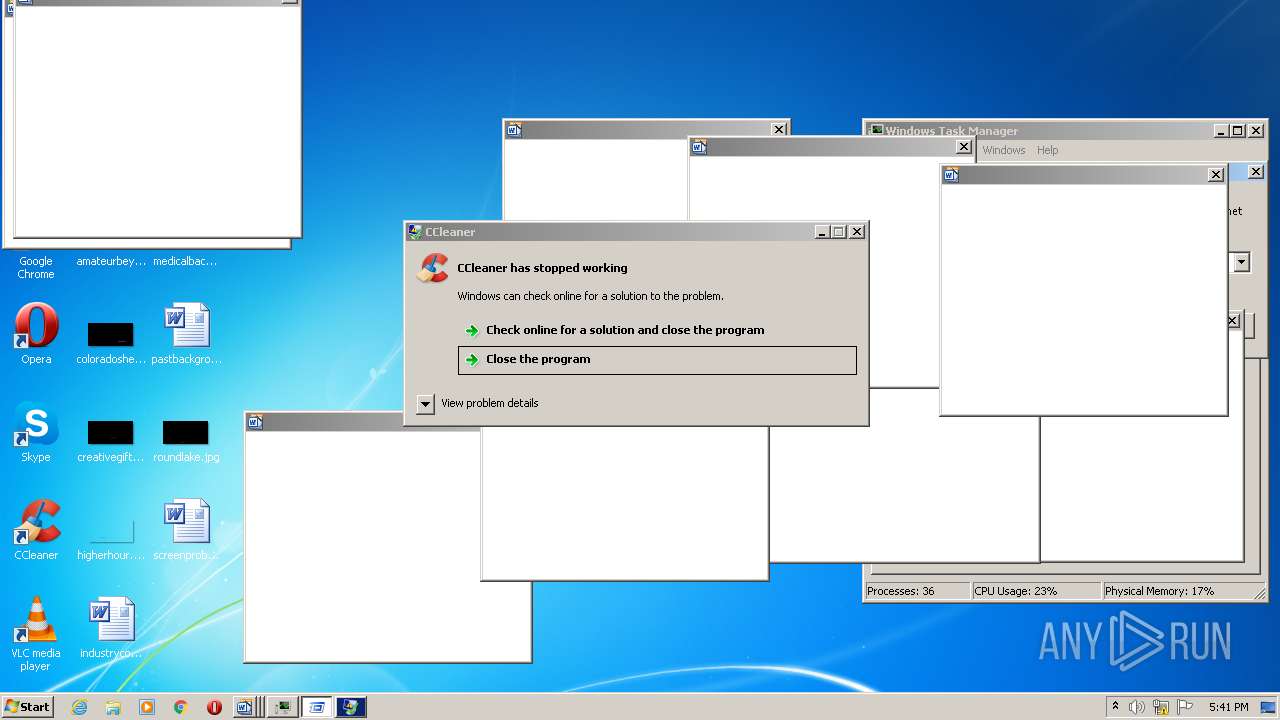
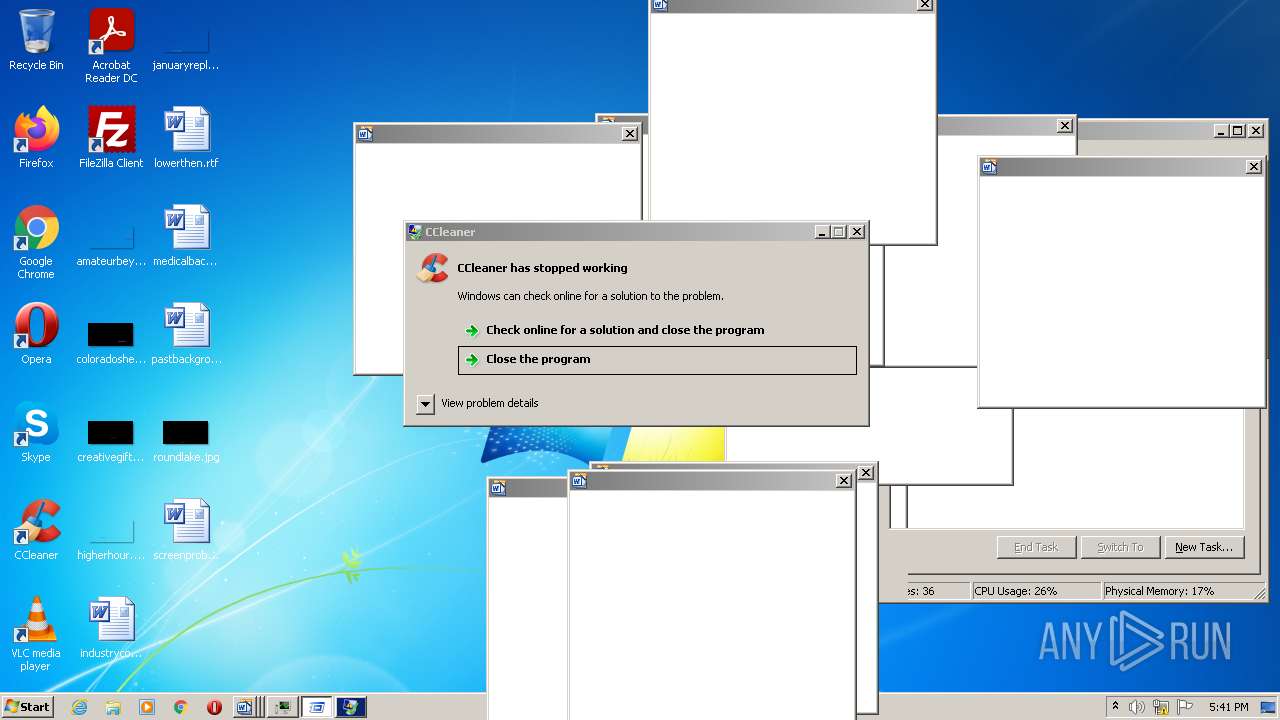
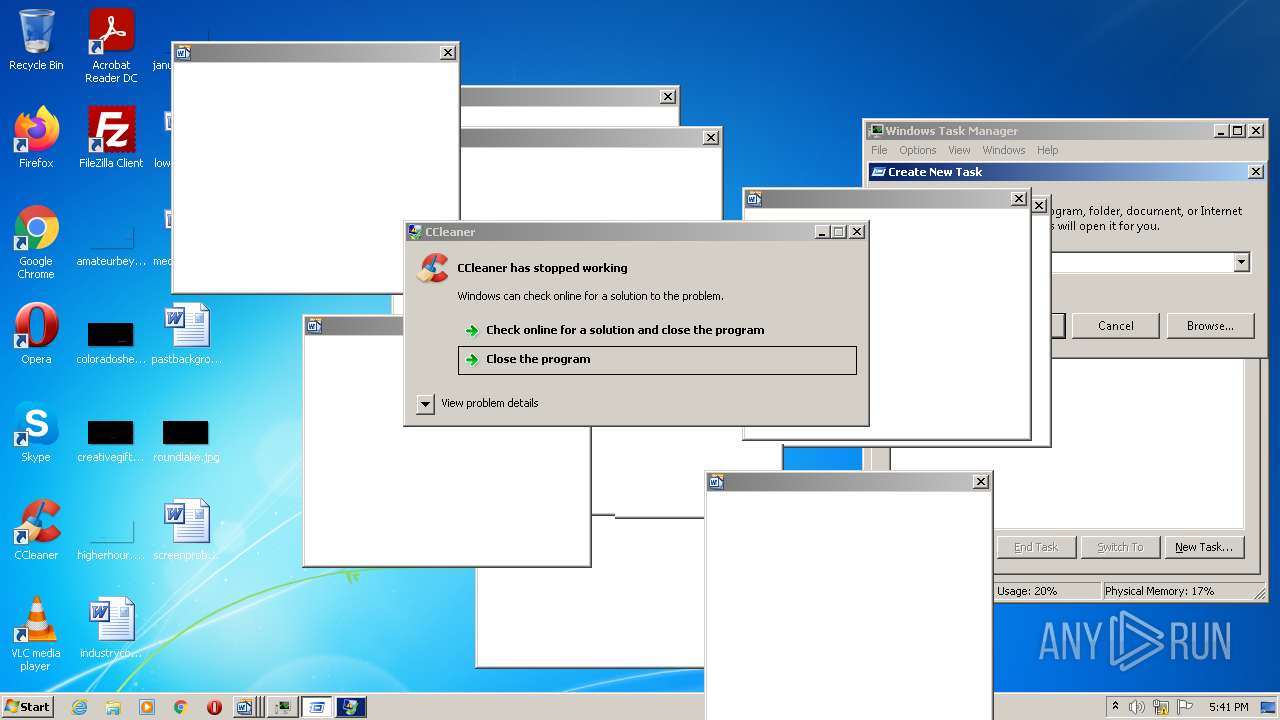
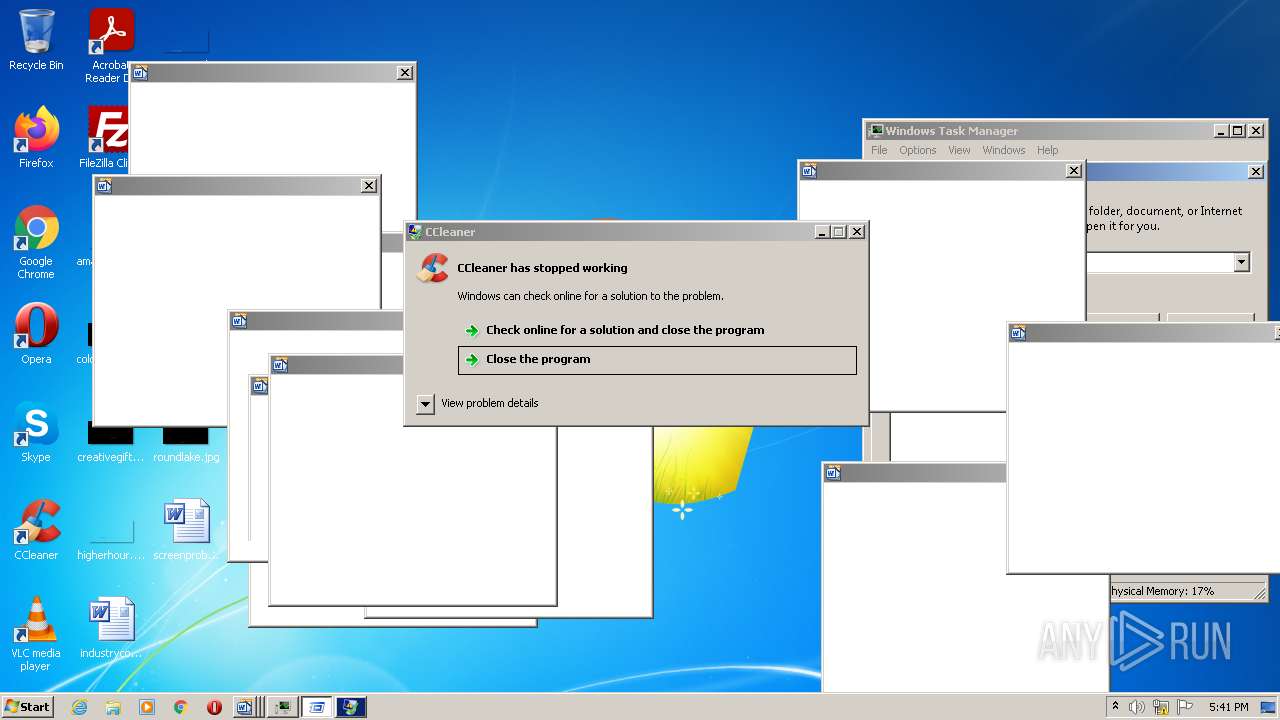
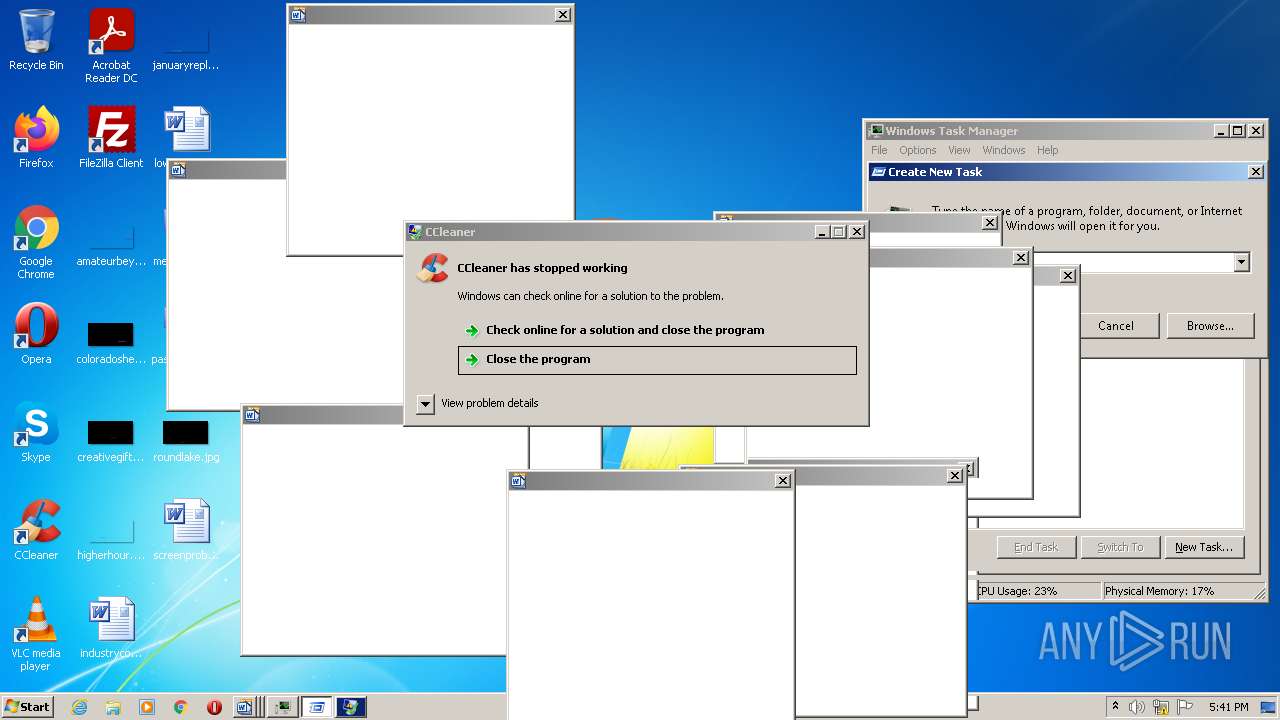
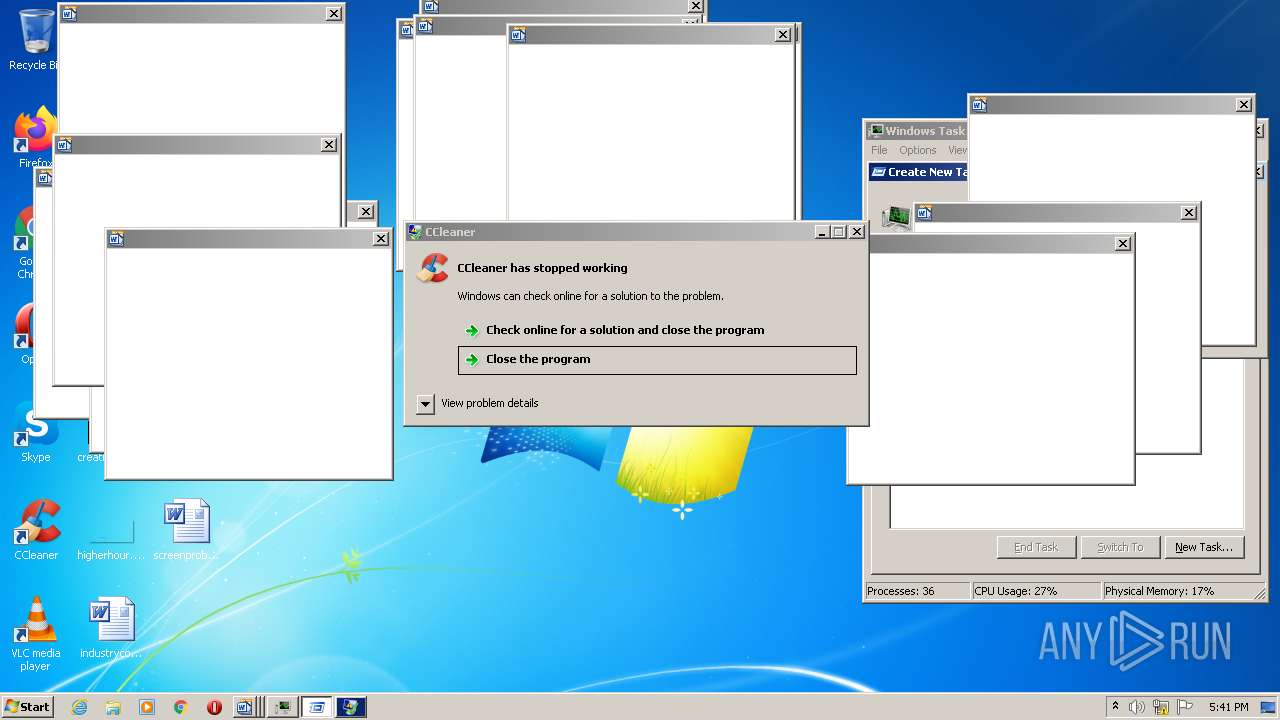
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2022, 17:37:17 |
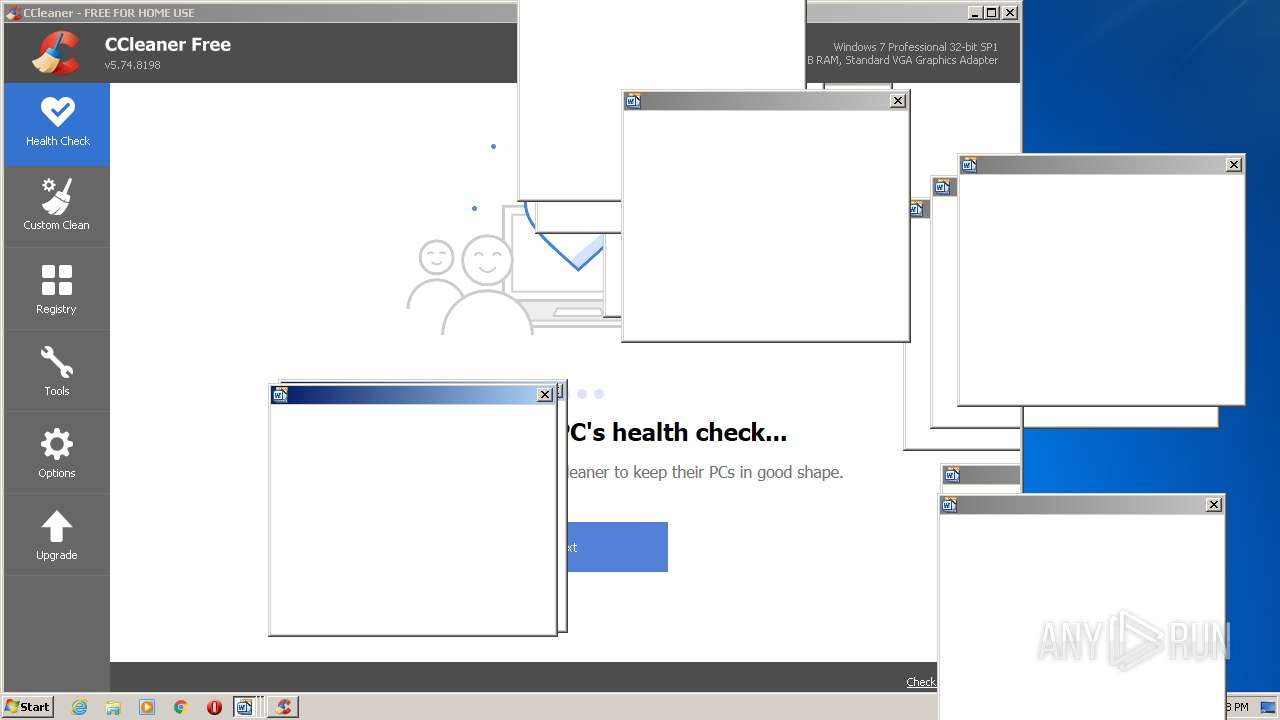
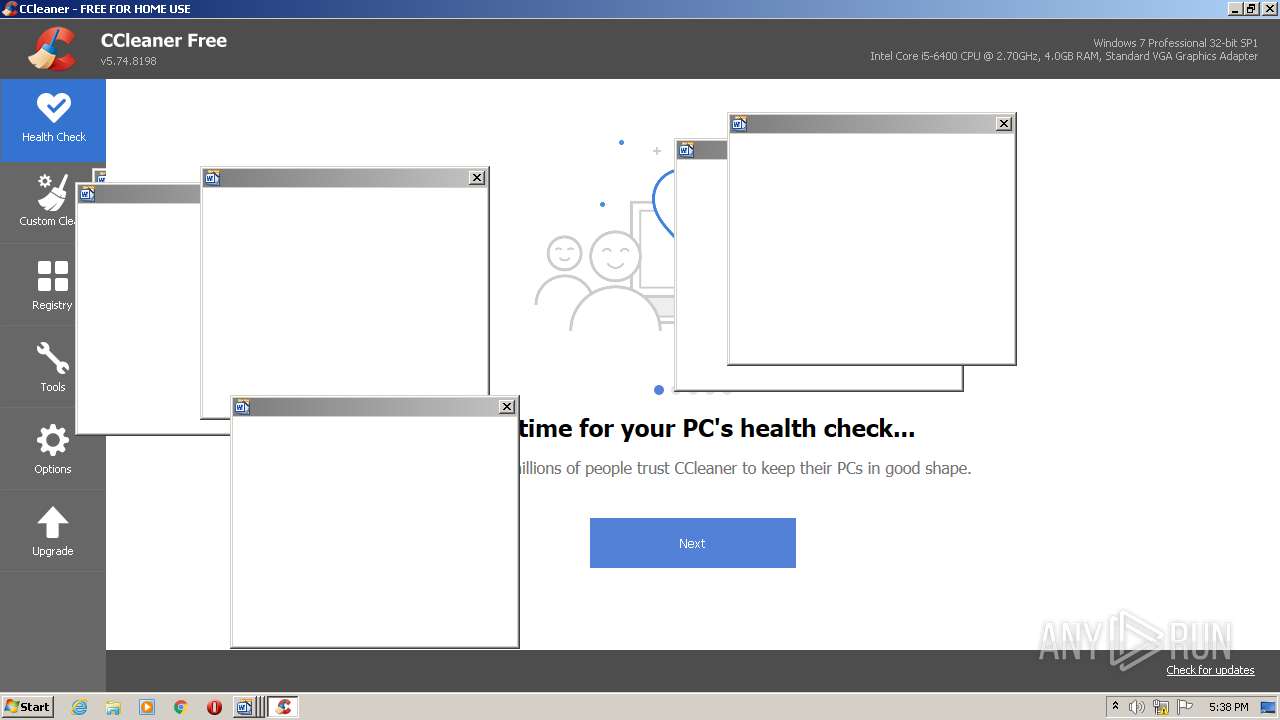
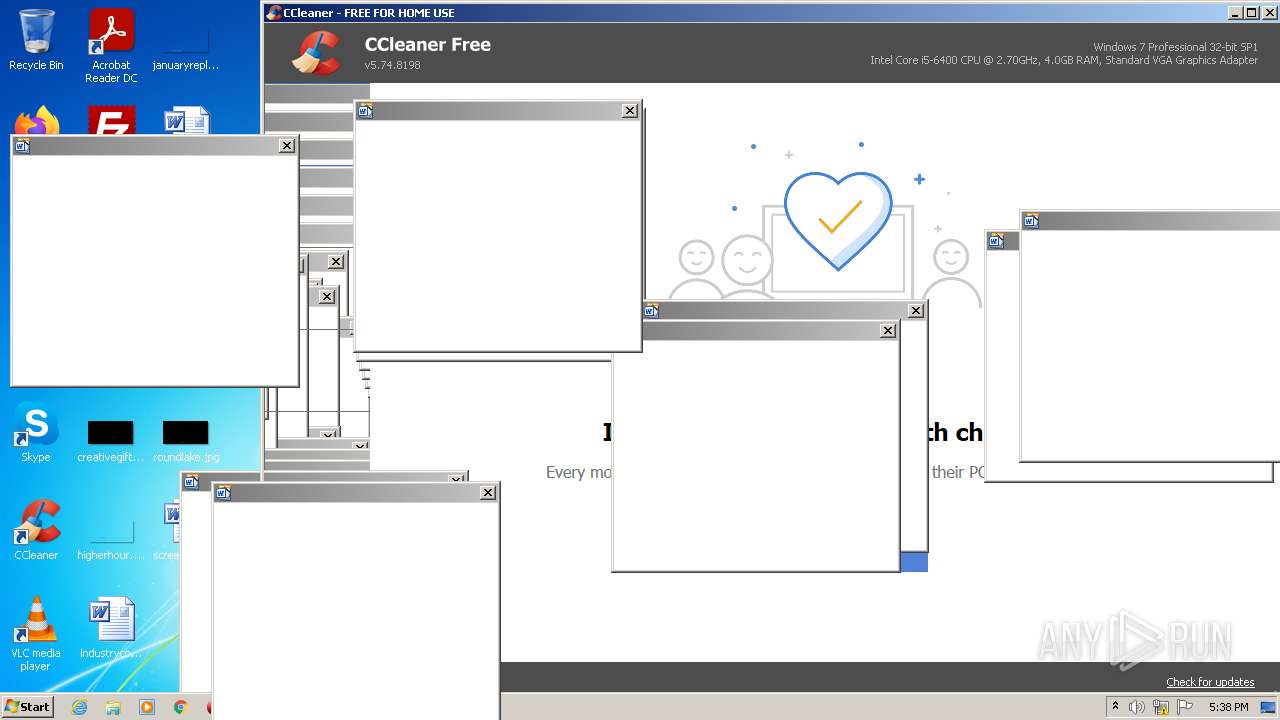
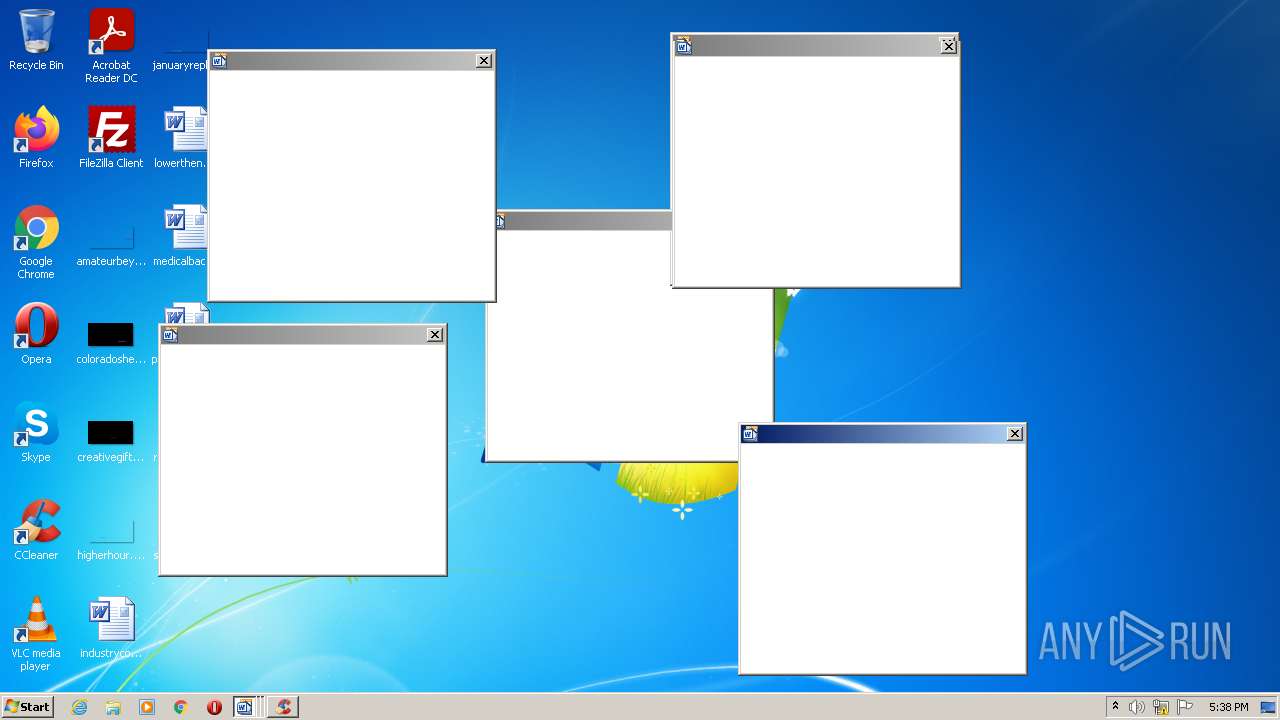
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D65CD3364F1054D810315C51EEDD837D |
| SHA1: | BAE2AAA5D0A5A34F7D58BACC4E0EB9ADD69DCEF1 |
| SHA256: | AC2AEF094F56AC3356CFDC41F722A055255C16F5908FBFC38F5B8F8A3B091812 |
| SSDEEP: | 3072:hq8U/w5N+g2KwsKW5pG5XzSGEdURp+p0kT/icf6913zsUJlytkFTFksFGhLu/Zza:h26+jUKWK5XmpSpi+bZ66ZGNu/hQd |
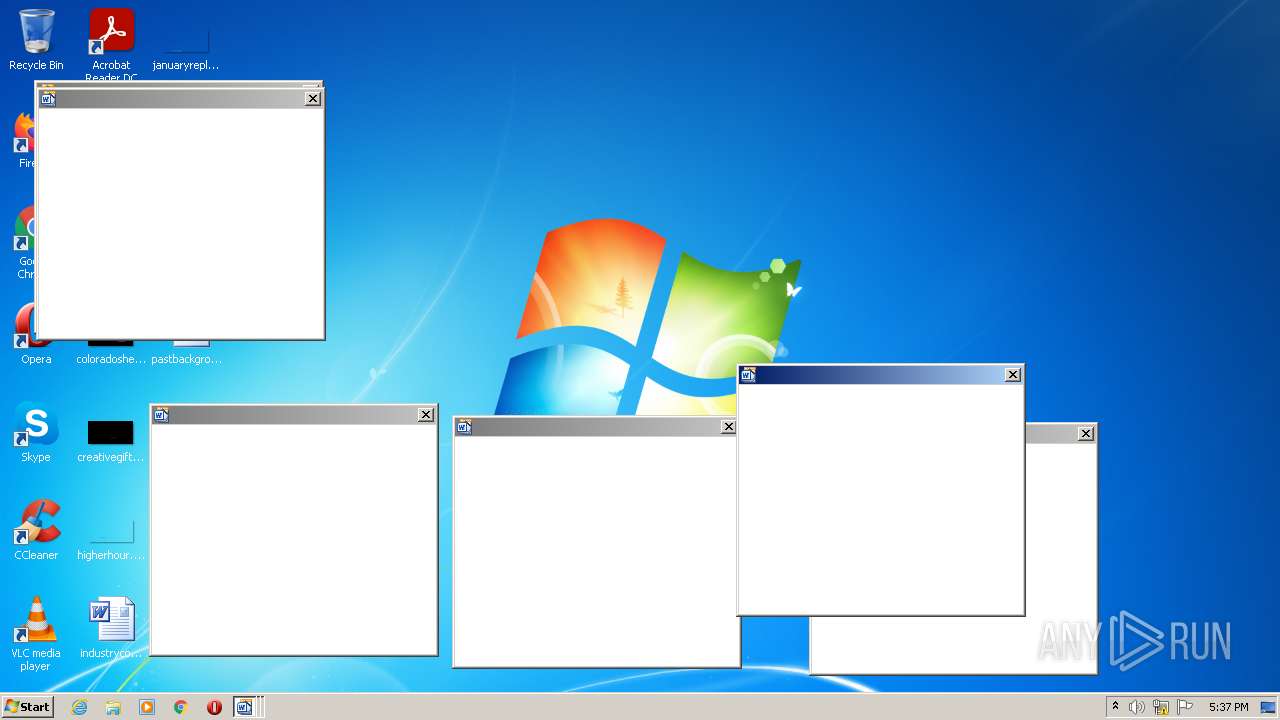
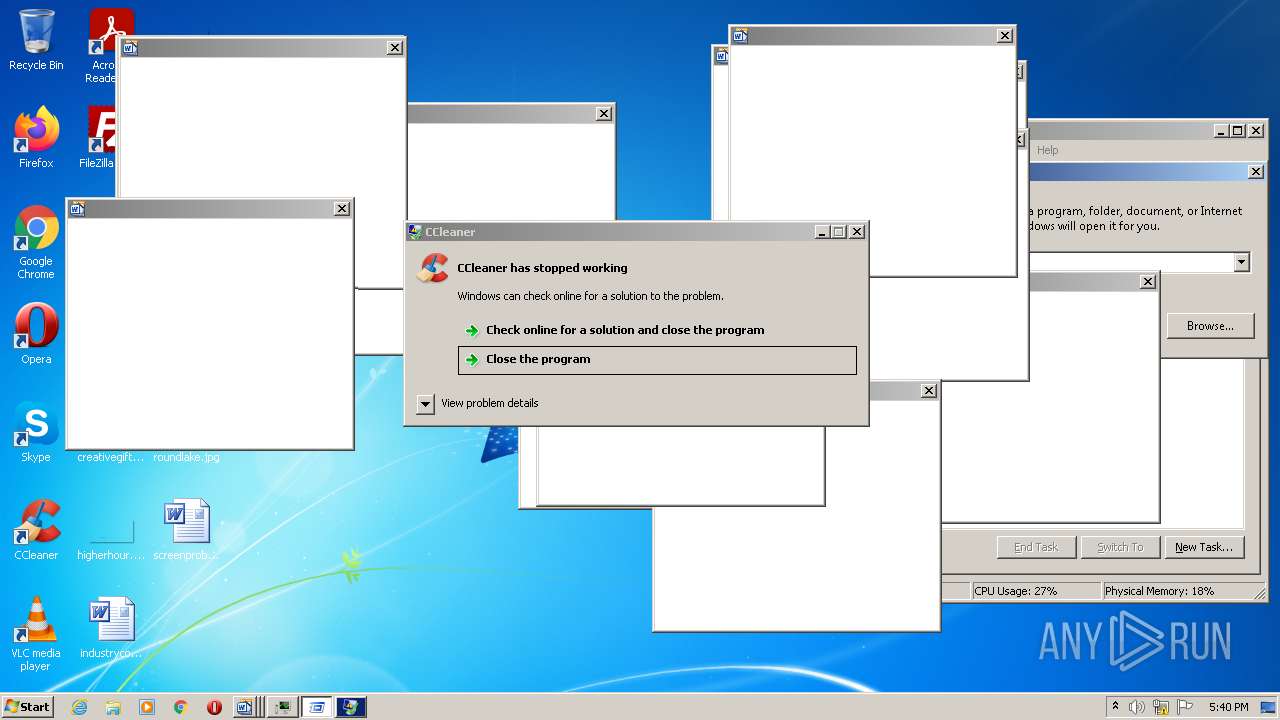
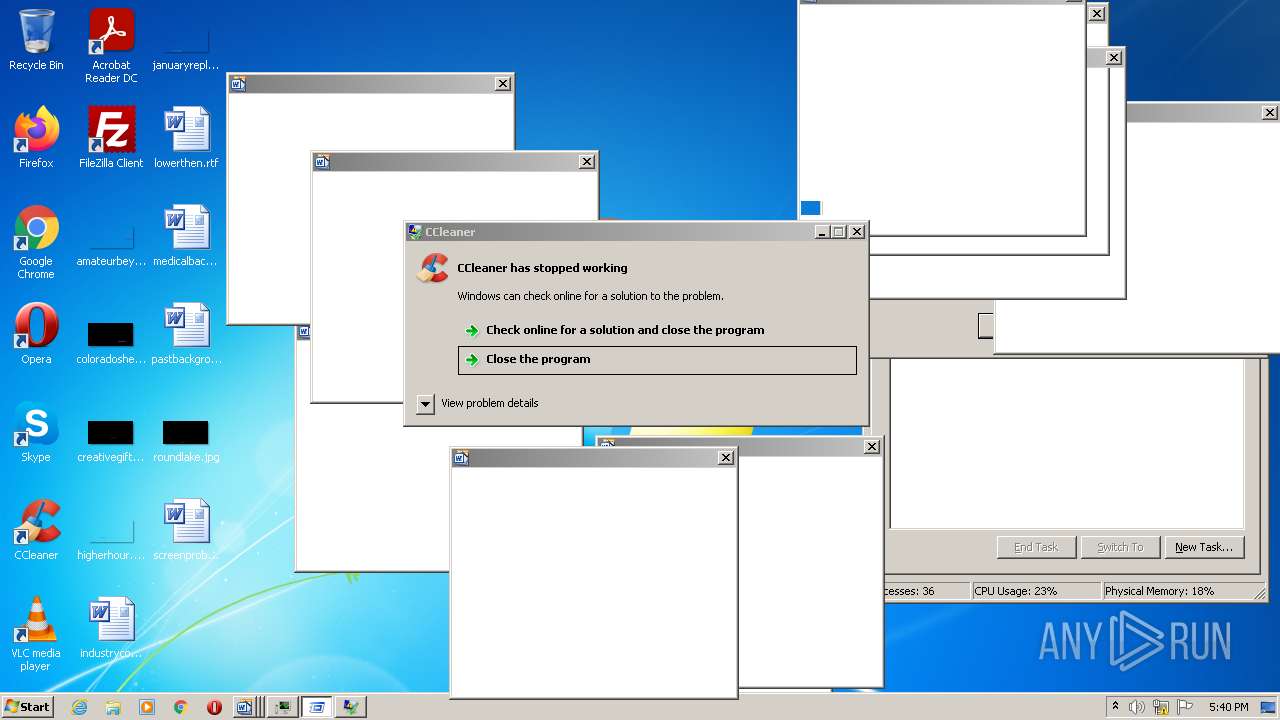
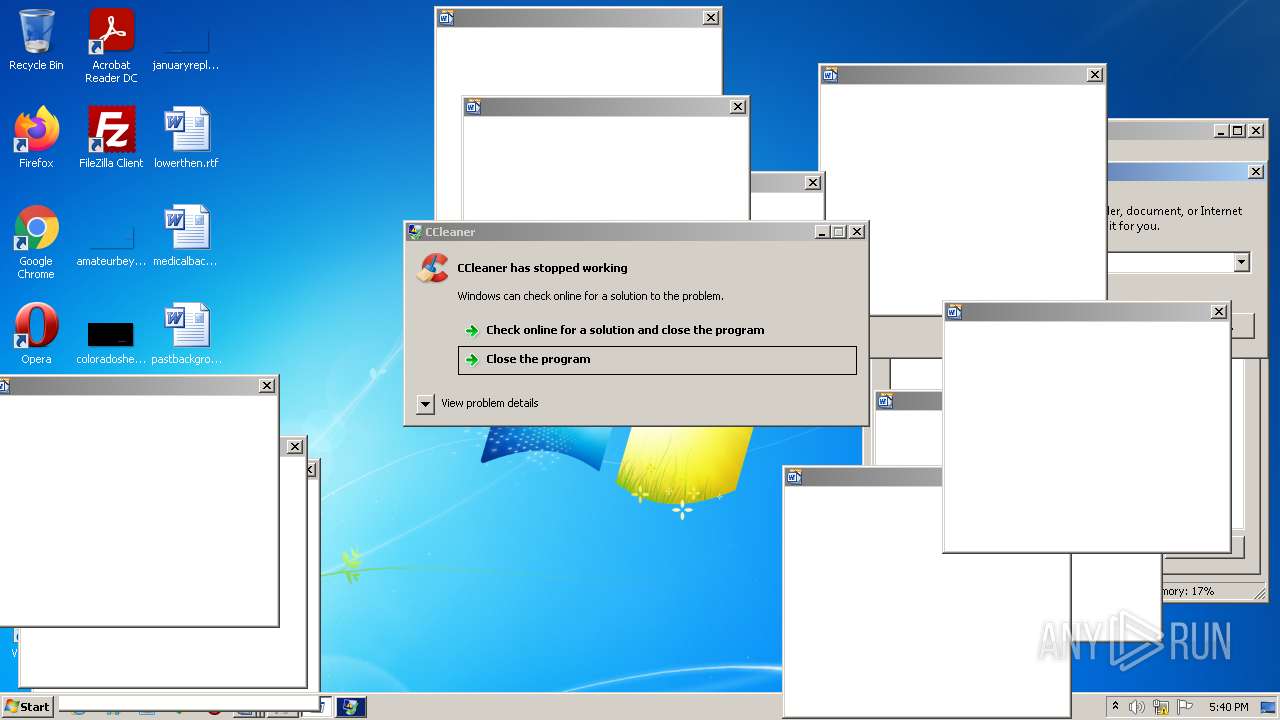
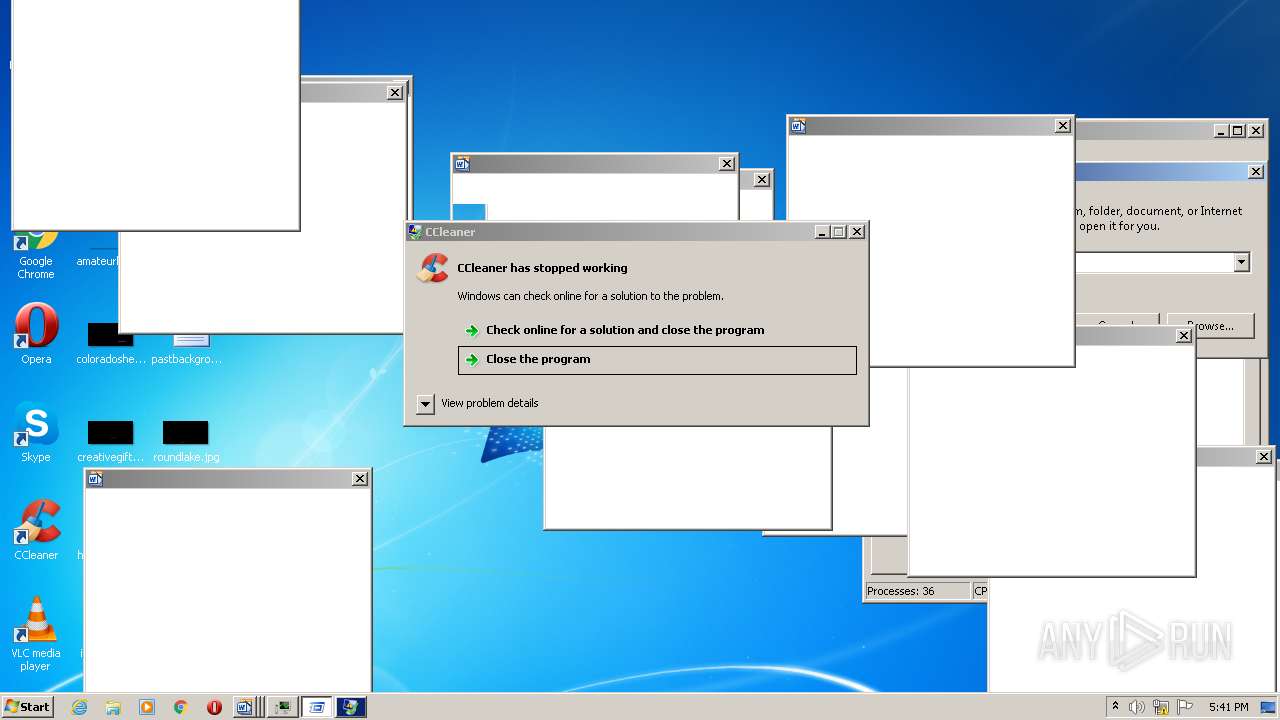
MALICIOUS
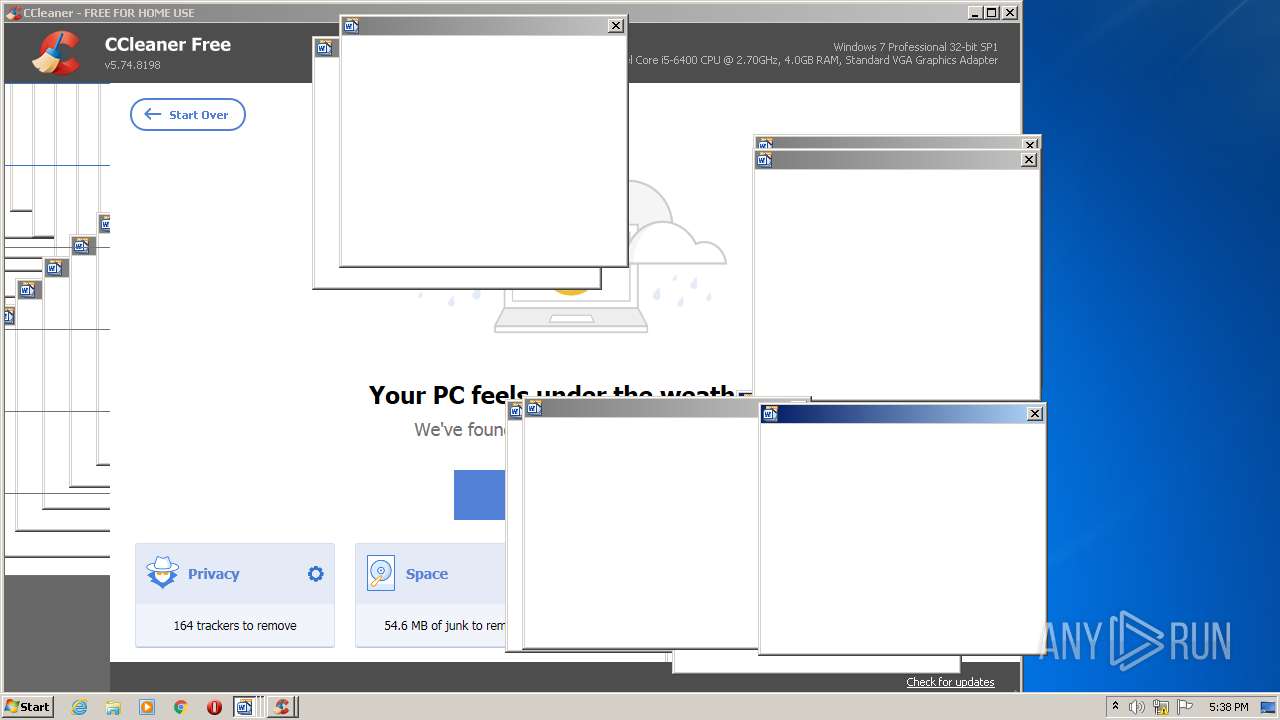
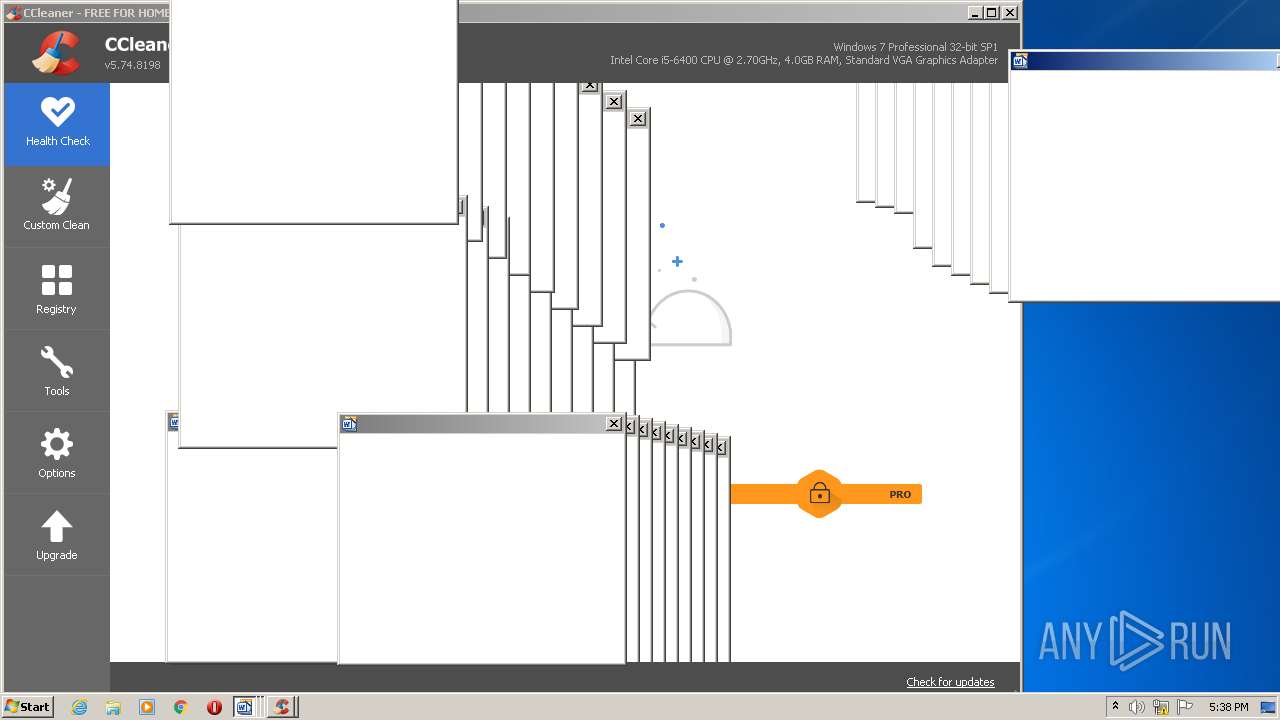
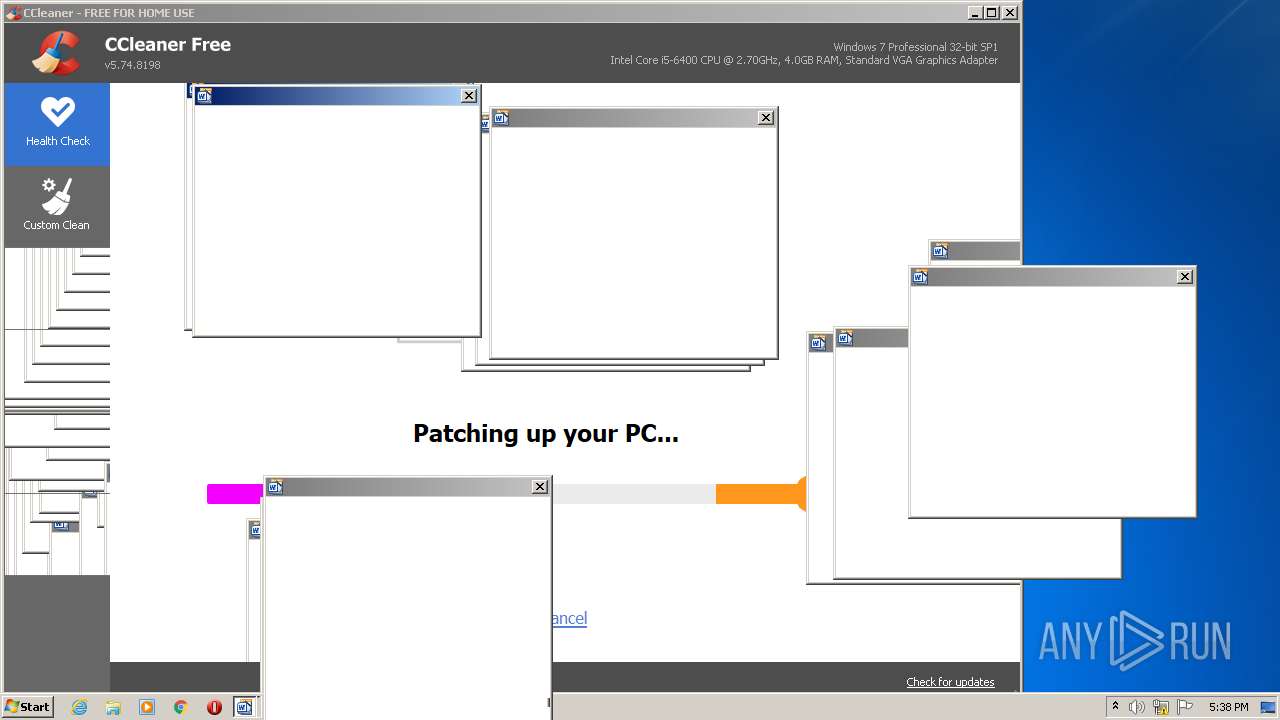
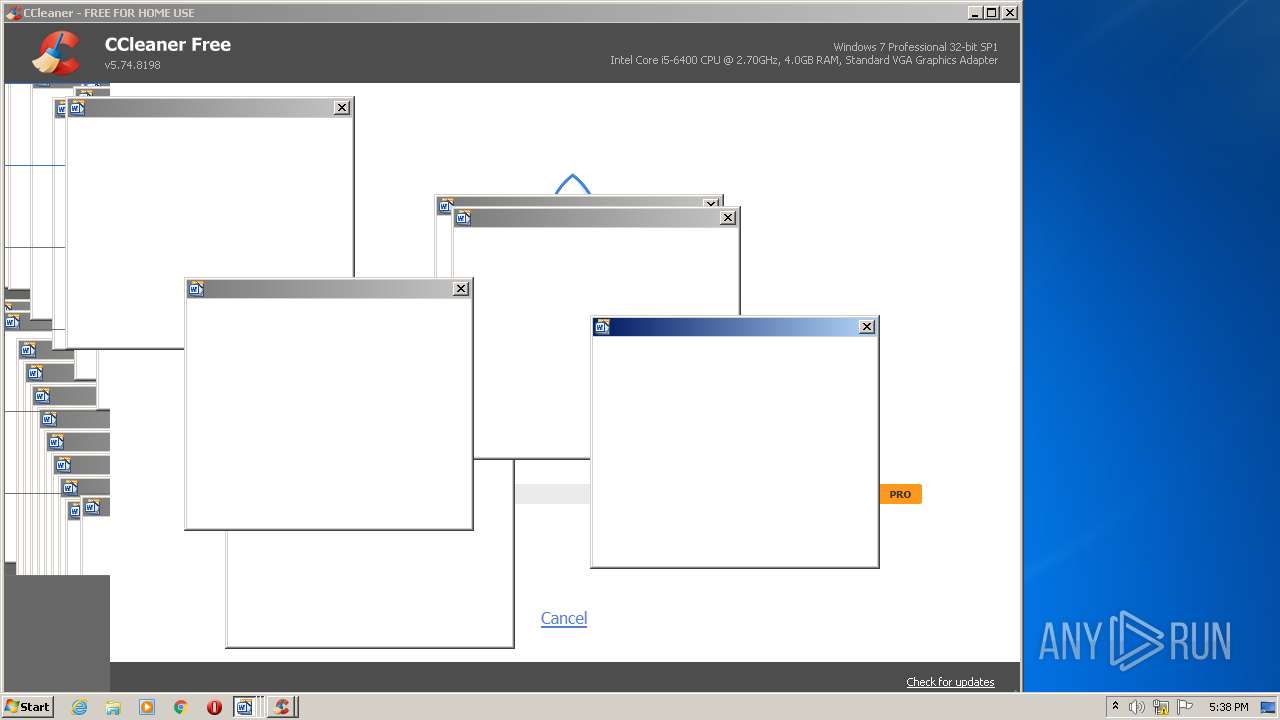
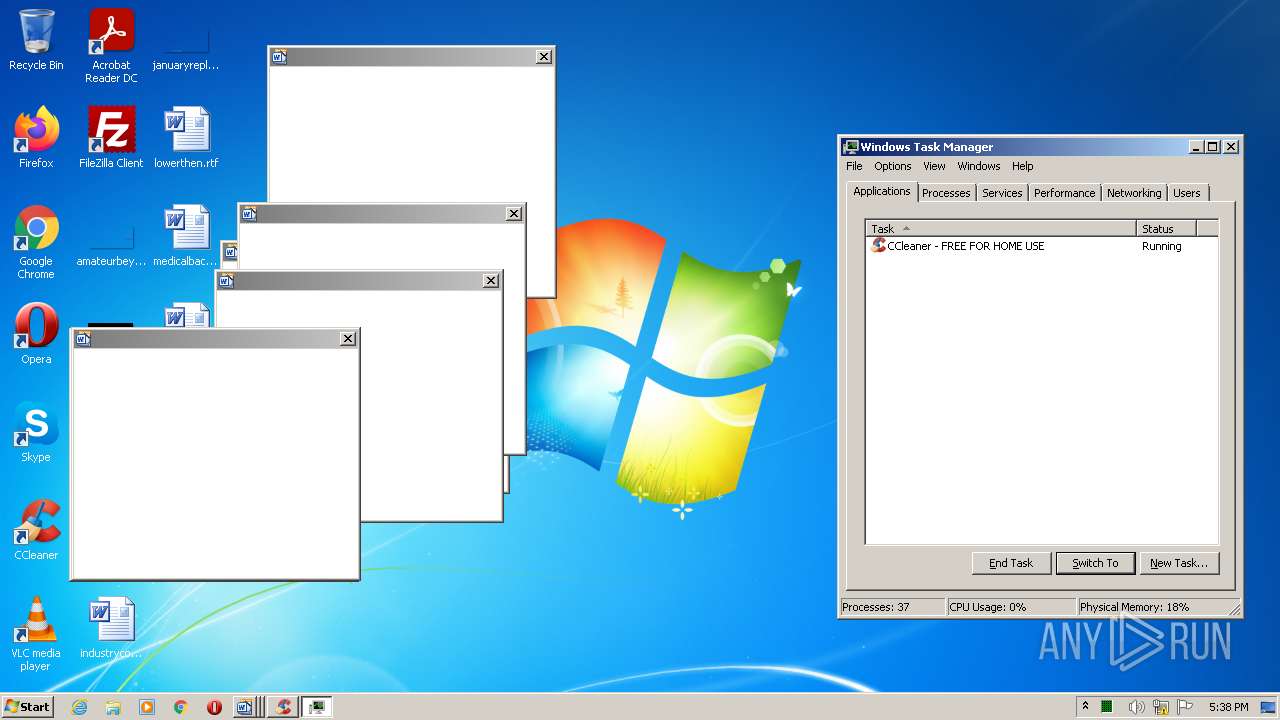
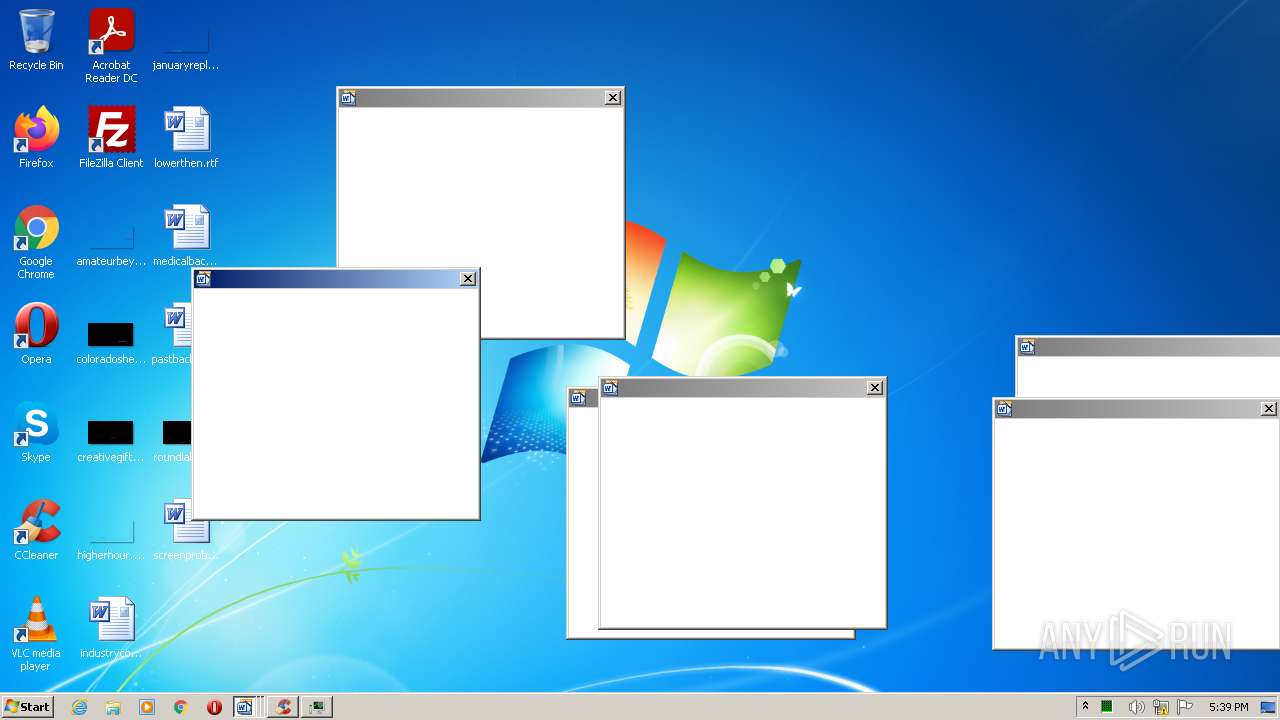
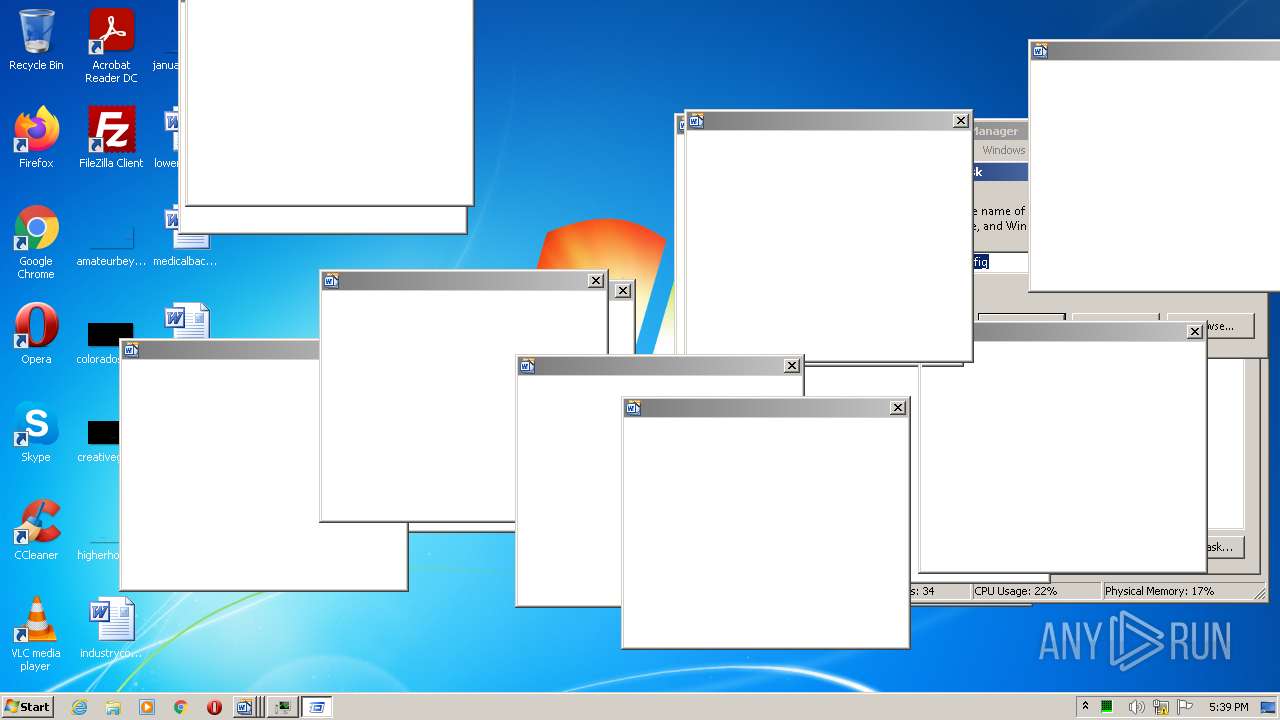
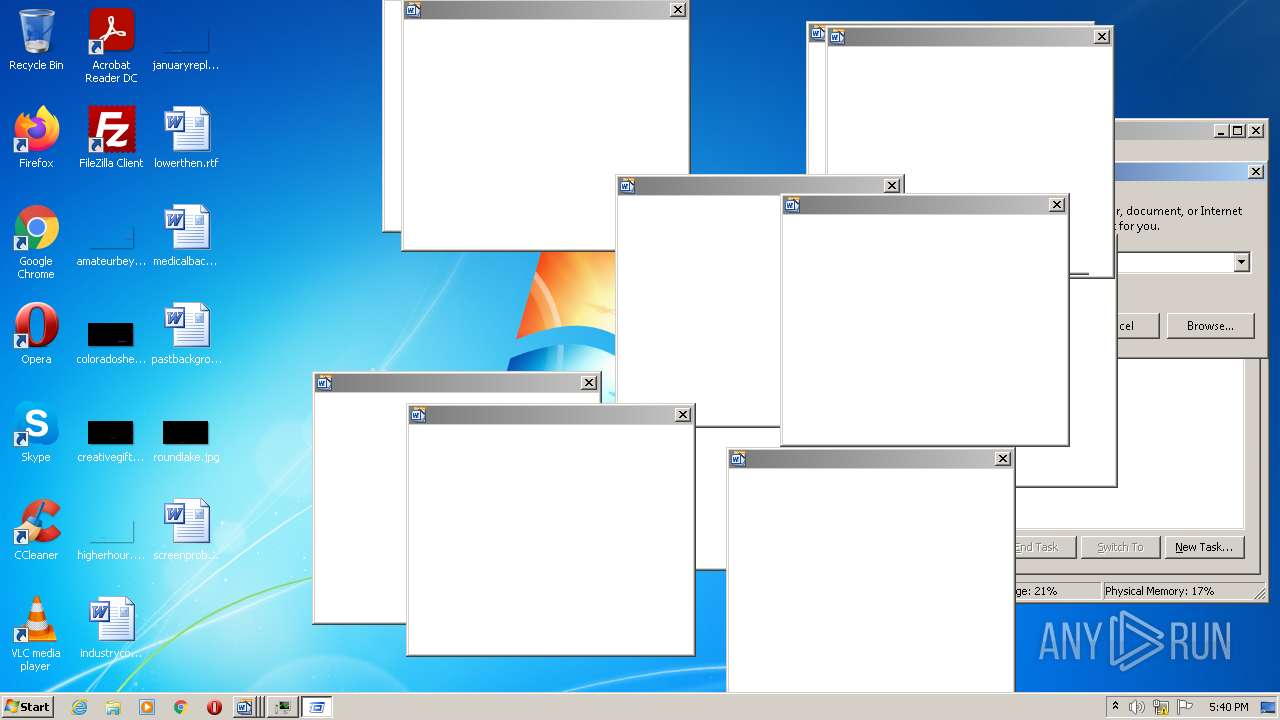
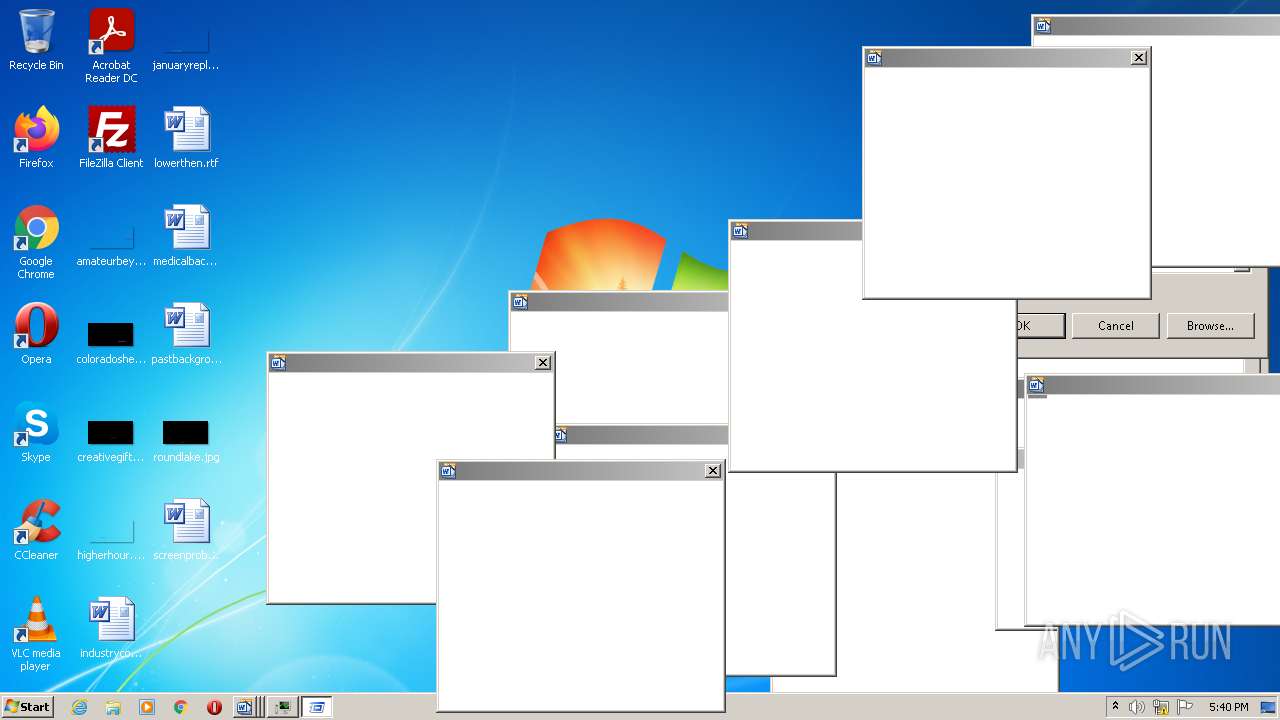
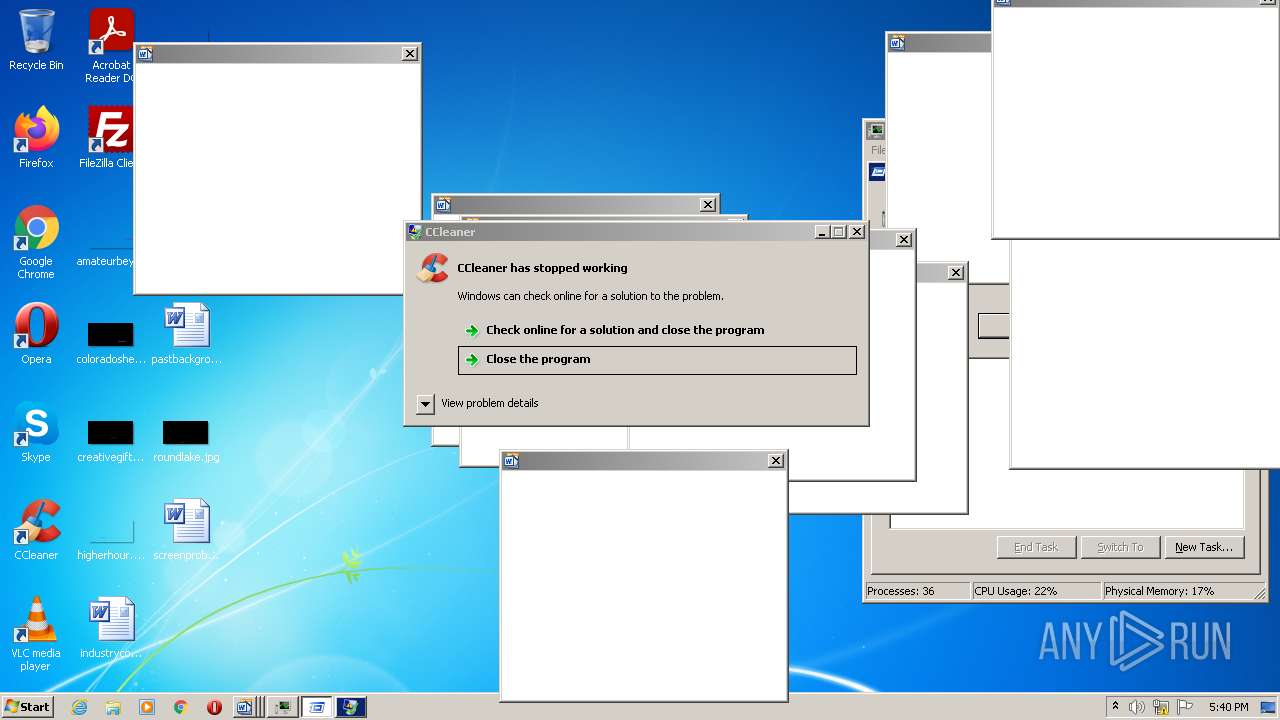
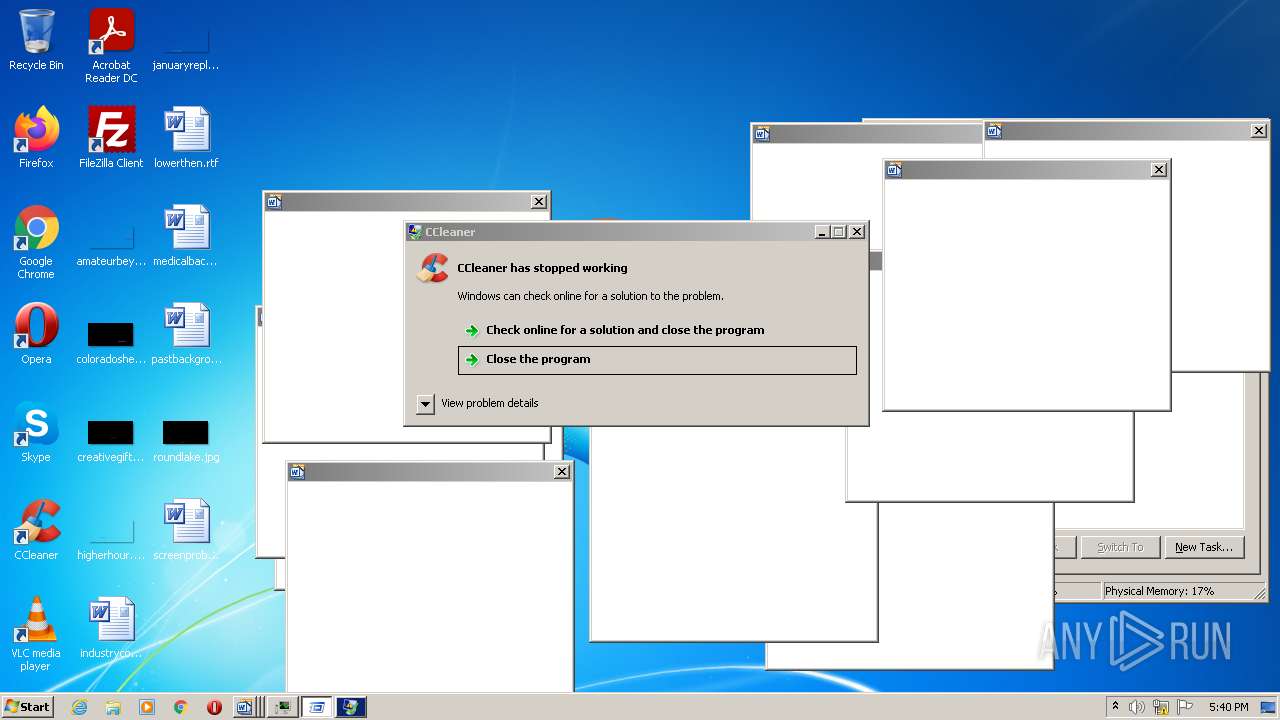
Application was dropped or rewritten from another process
- YouAreAnIdiot.exe (PID: 2028)
Loads dropped or rewritten executable
- YouAreAnIdiot.exe (PID: 2028)
- CCleaner.exe (PID: 2360)
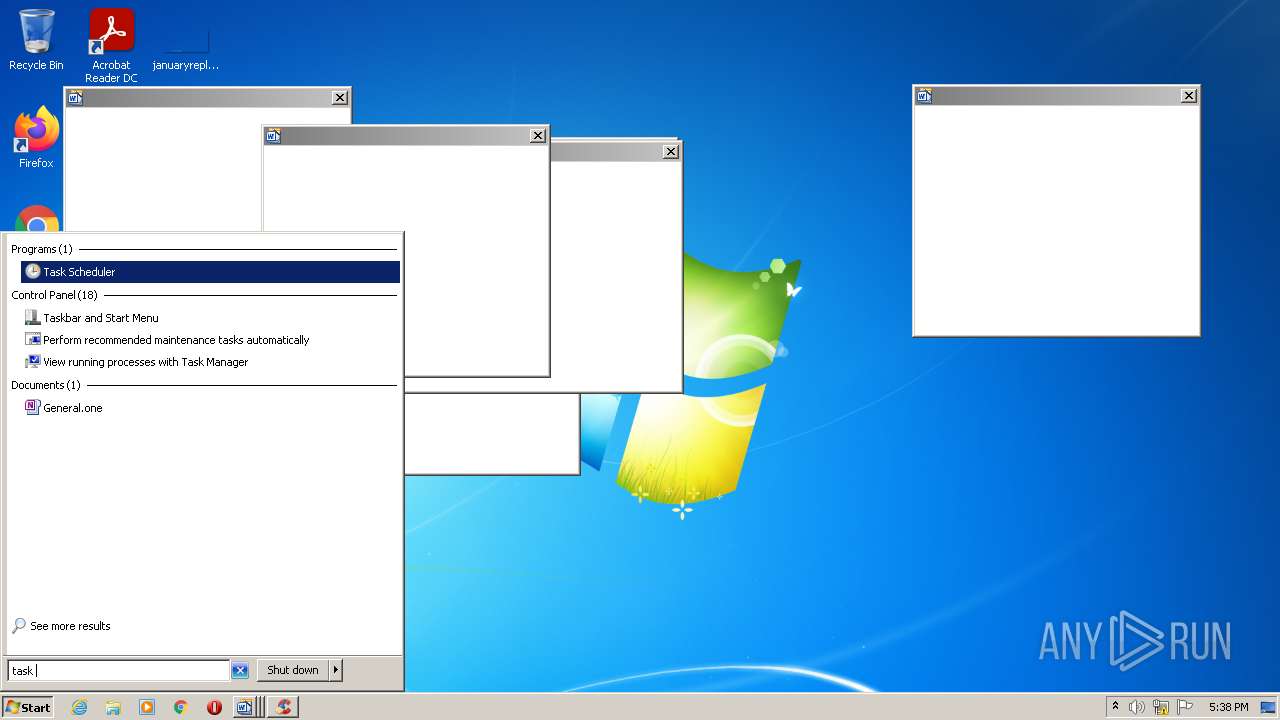
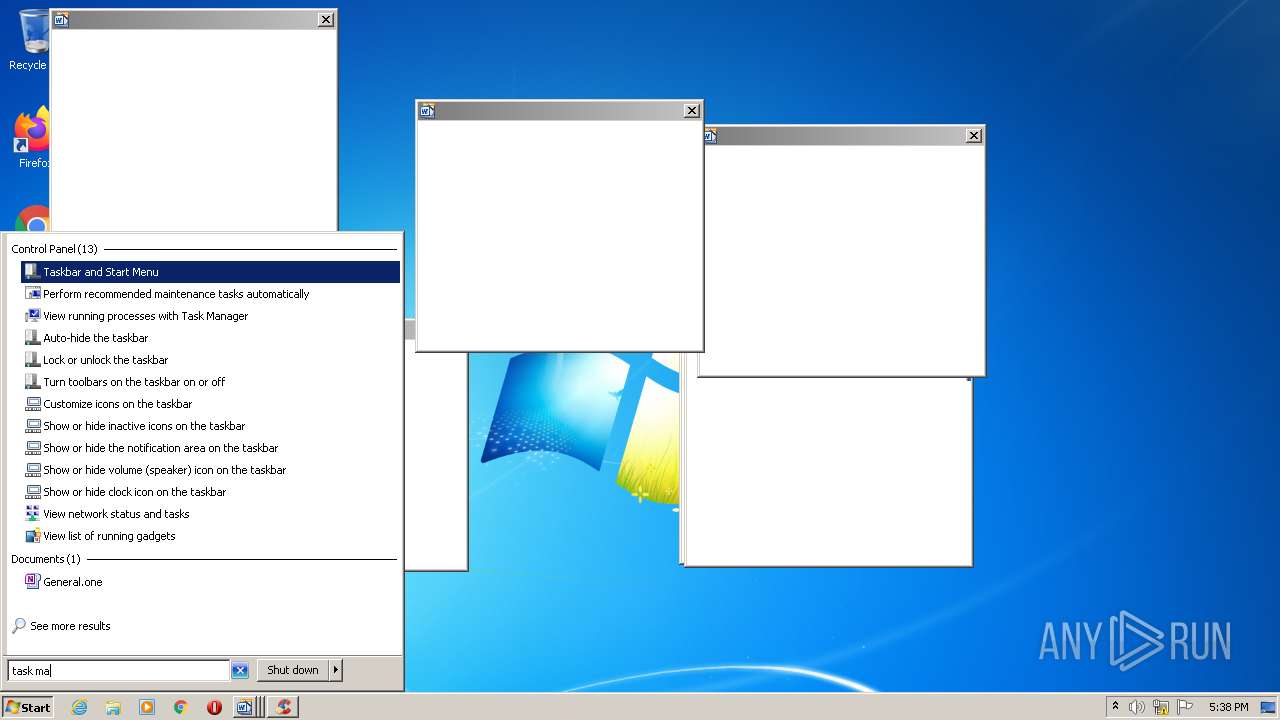
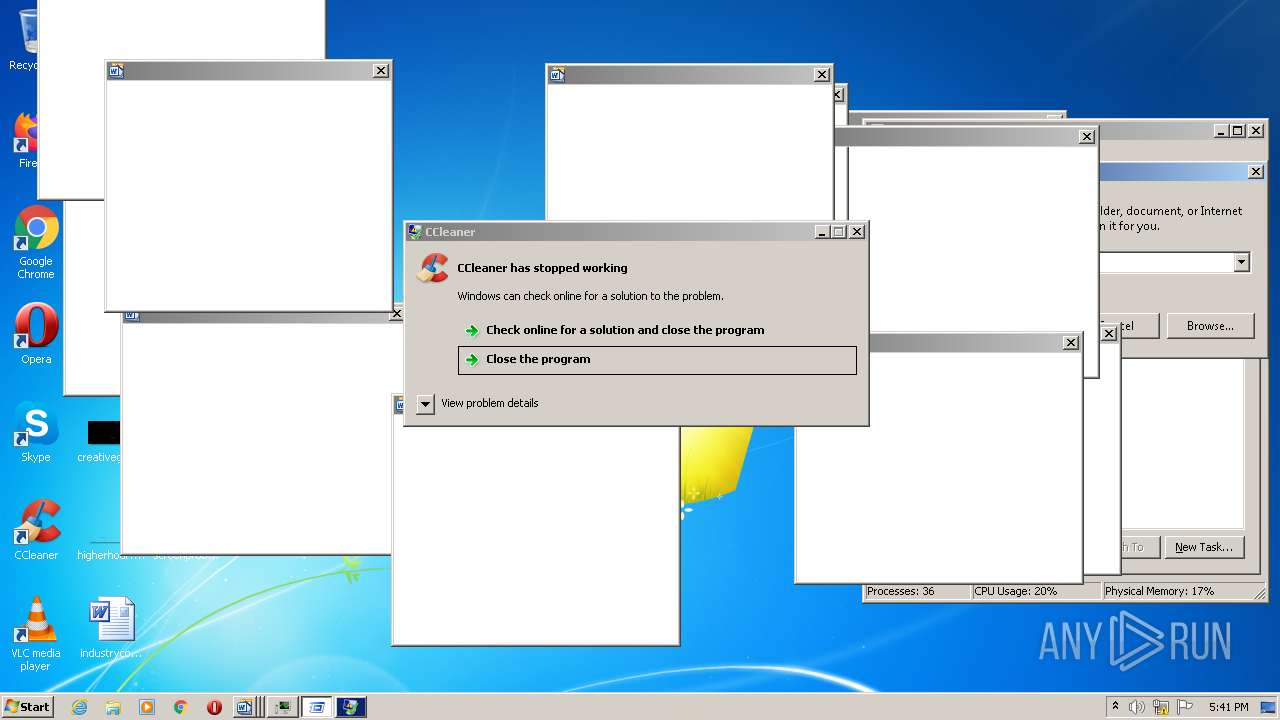
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 1700)
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 1304)
- CCleaner.exe (PID: 2360)
Drops executable file immediately after starts
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
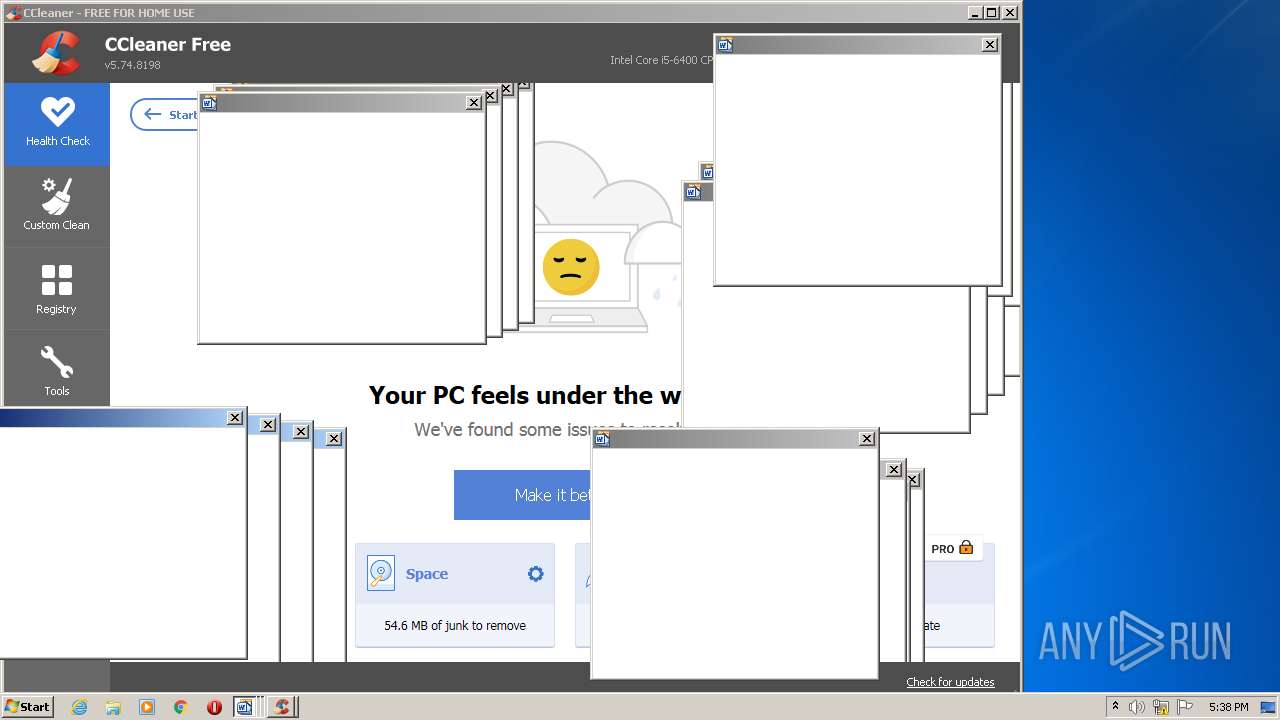
Changes settings of System certificates
- CCleaner.exe (PID: 2360)
Steals credentials from Web Browsers
- CCleaner.exe (PID: 2360)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 2360)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3736)
- YouAreAnIdiot.exe (PID: 2028)
- CCleaner.exe (PID: 1700)
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 1304)
- CCleaner.exe (PID: 2360)
Reads the computer name
- YouAreAnIdiot.exe (PID: 2028)
- WinRAR.exe (PID: 3736)
- CCleaner.exe (PID: 1700)
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 1304)
- CCleaner.exe (PID: 2360)
Creates files in the user directory
- YouAreAnIdiot.exe (PID: 2028)
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3736)
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3736)
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
Reads CPU info
- YouAreAnIdiot.exe (PID: 2028)
- CCleaner.exe (PID: 2360)
- CCleaner.exe (PID: 3976)
Reads Environment values
- CCleaner.exe (PID: 1700)
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 1304)
- CCleaner.exe (PID: 2360)
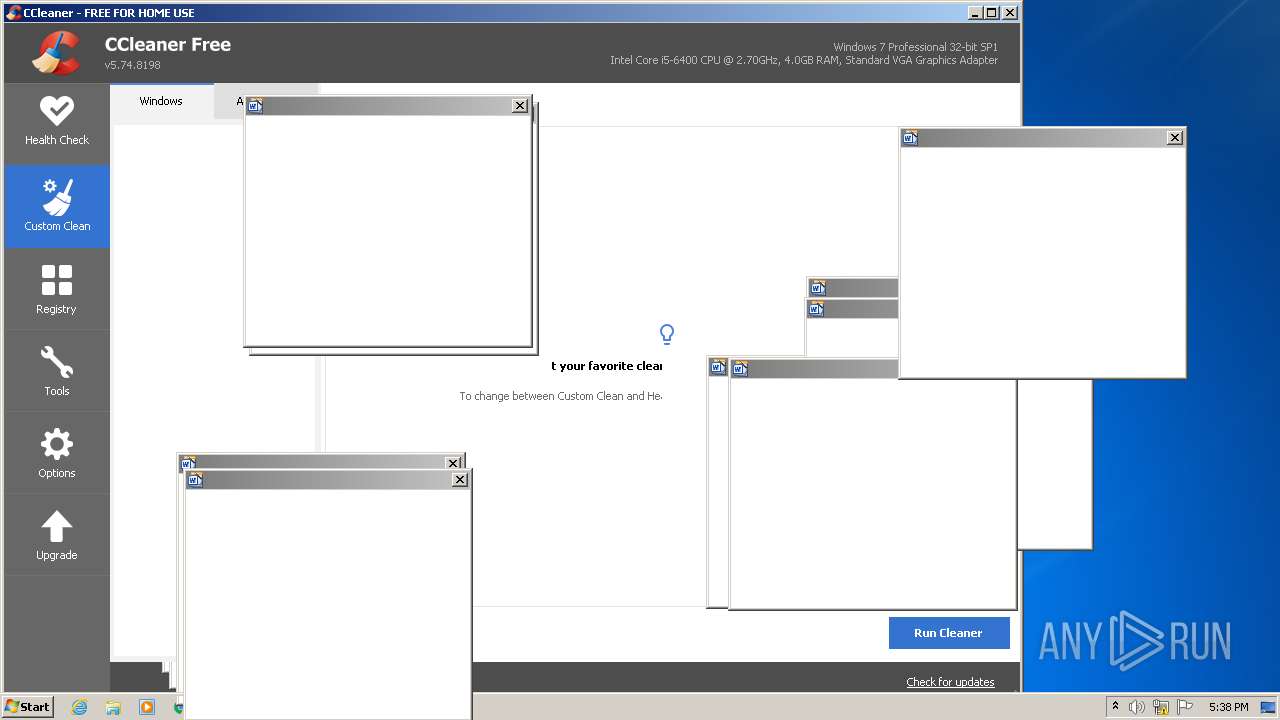
Executed via Task Scheduler
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
Creates files in the program directory
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
Reads internet explorer settings
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
Reads the date of Windows installation
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
Searches for installed software
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
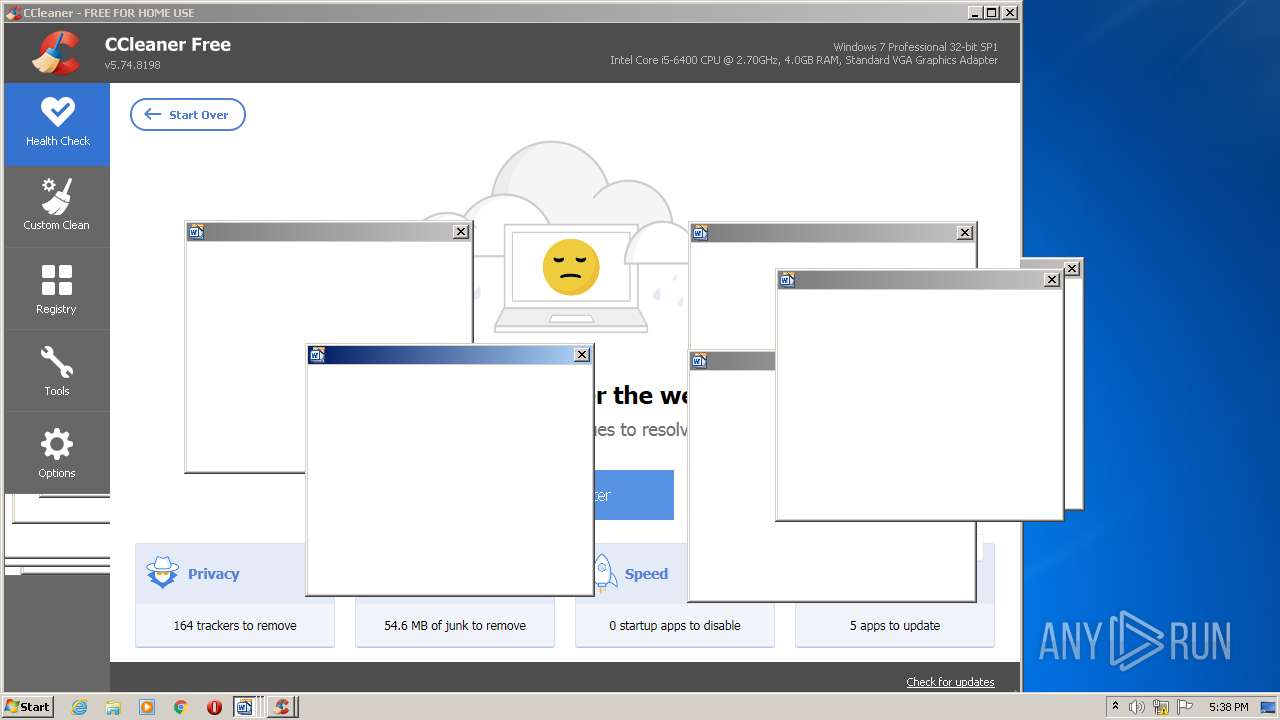
Adds / modifies Windows certificates
- CCleaner.exe (PID: 2360)
Executed as Windows Service
- taskhost.exe (PID: 3044)
- taskhost.exe (PID: 2612)
- taskhost.exe (PID: 1492)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 2360)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 2360)
Executed via COM
- DllHost.exe (PID: 2380)
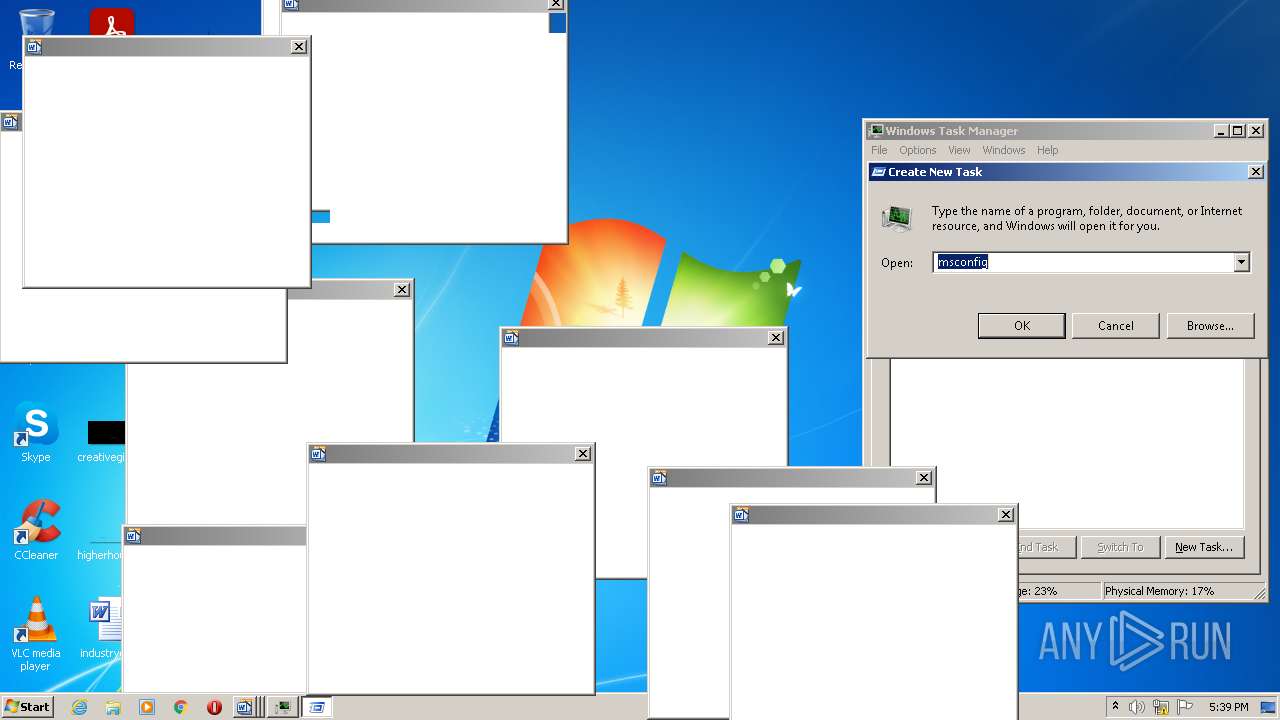
INFO
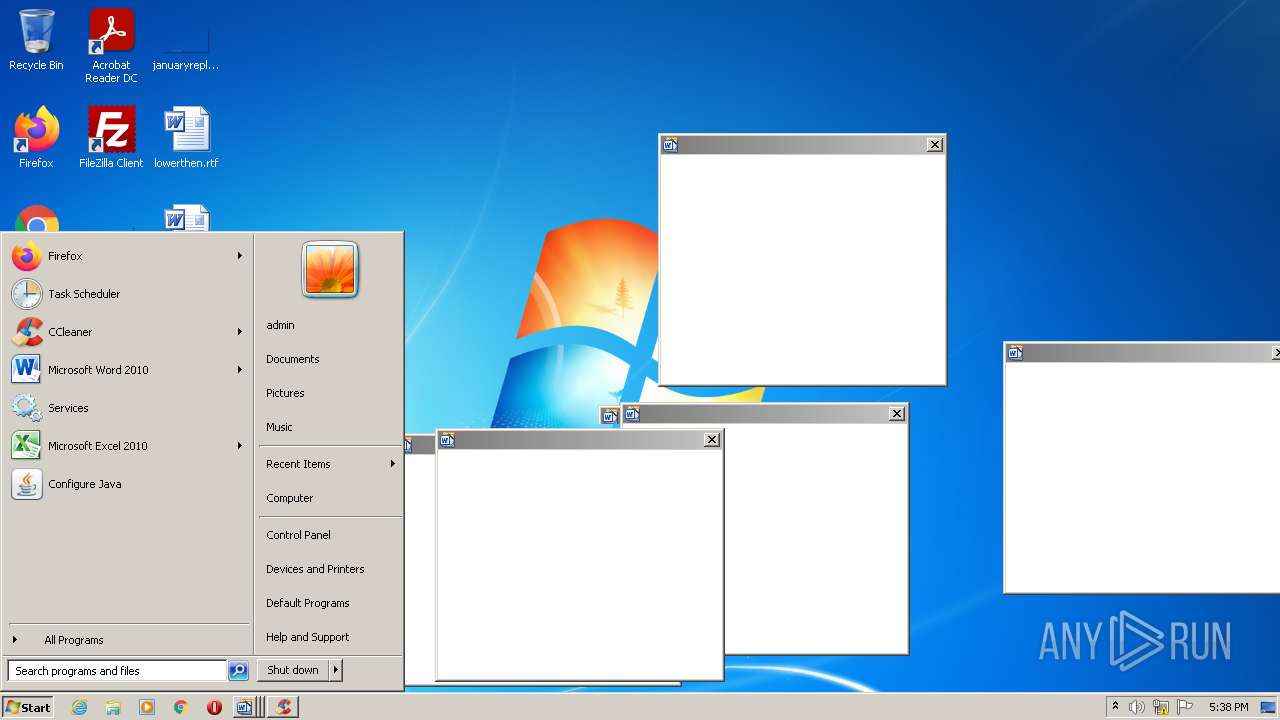
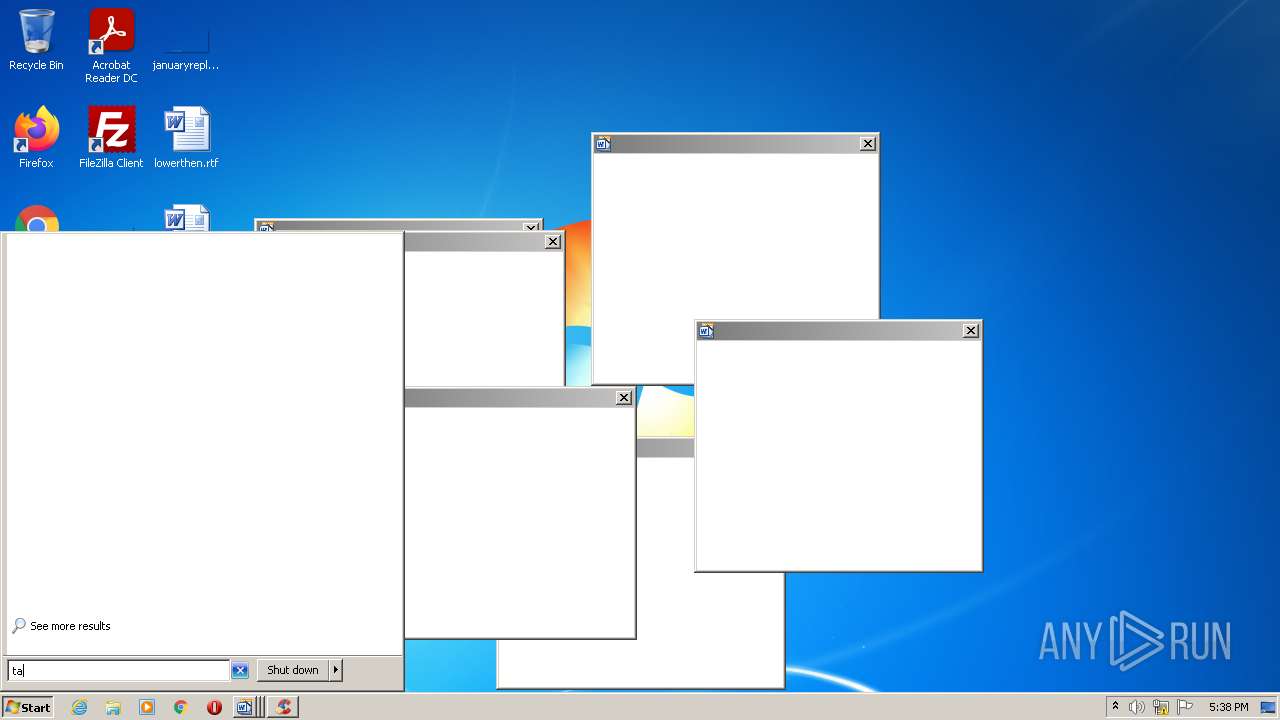
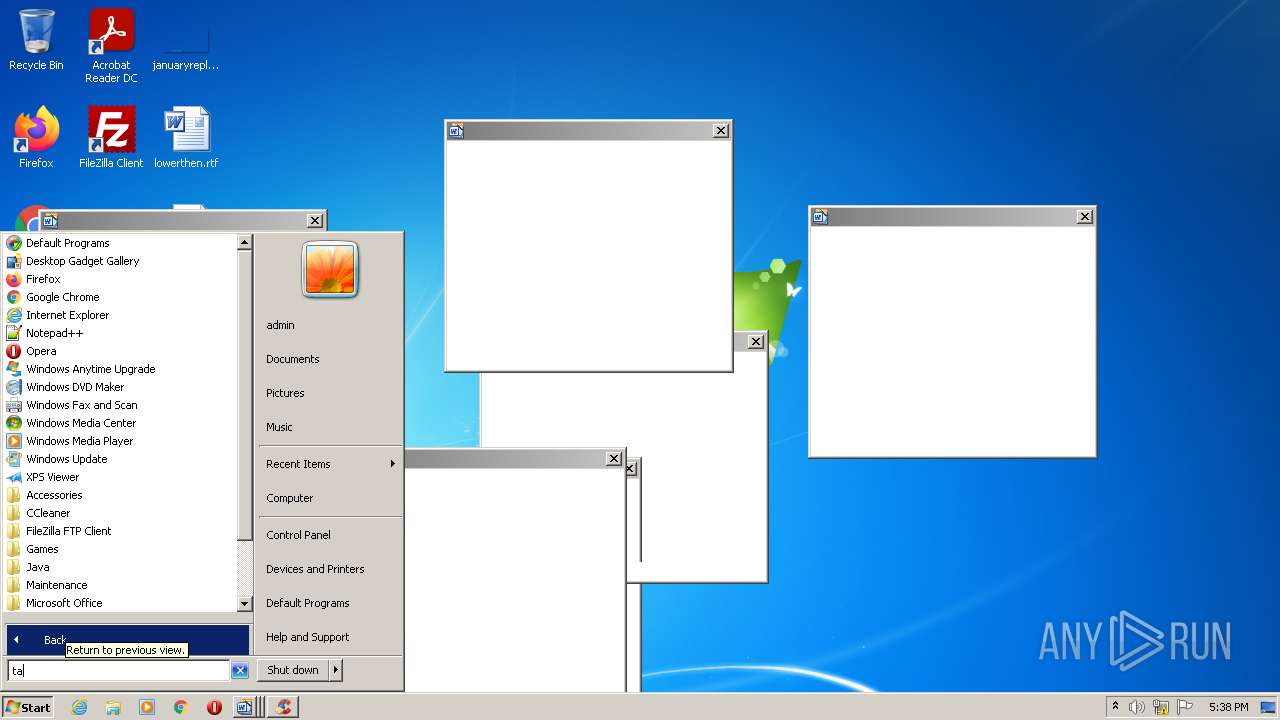
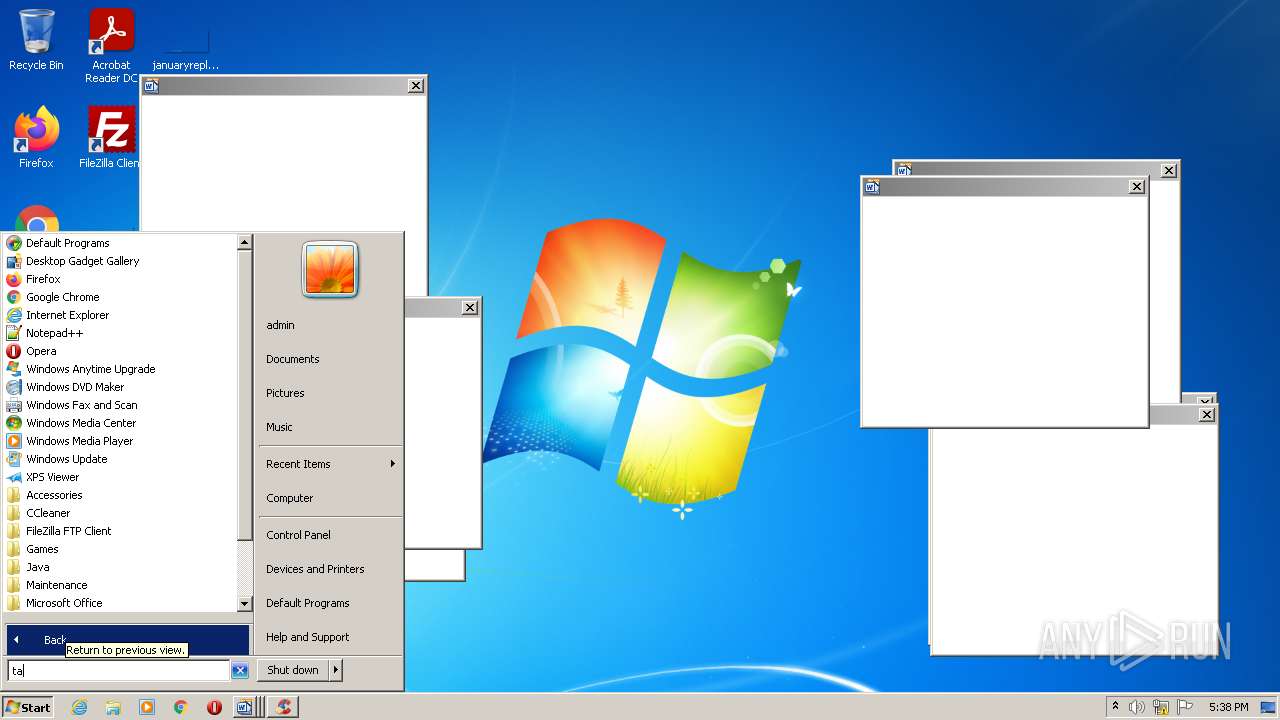
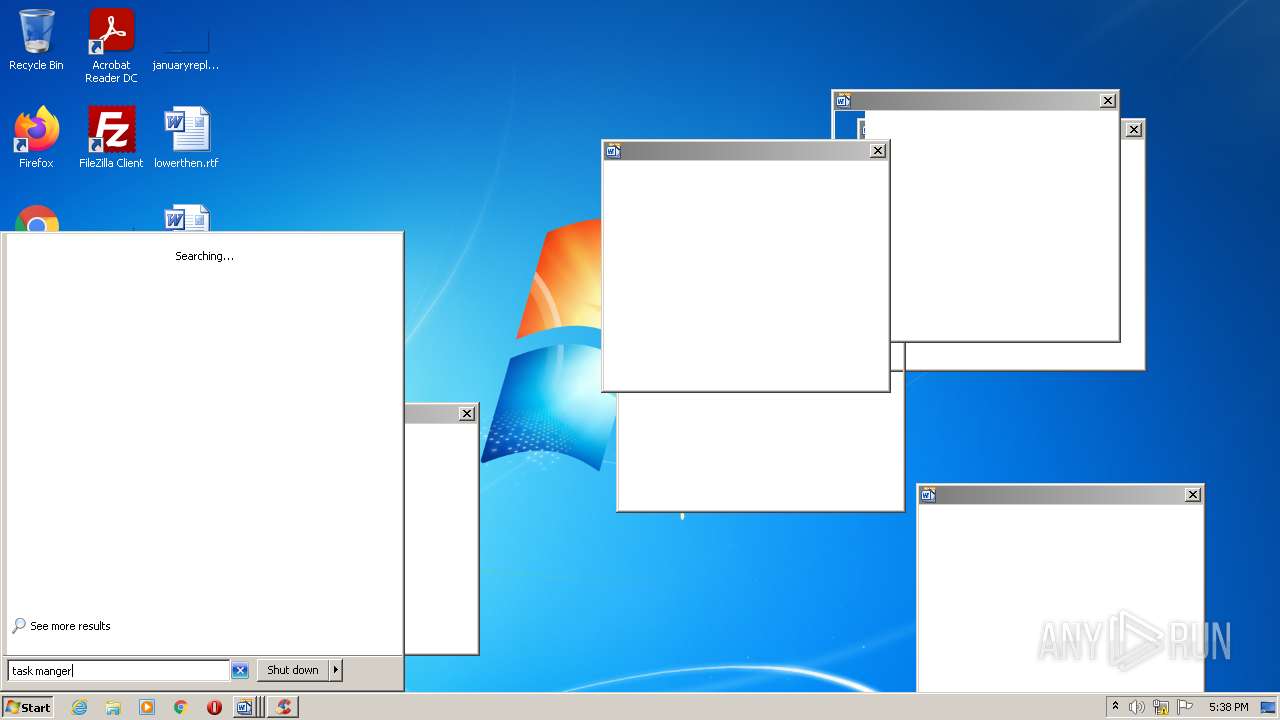
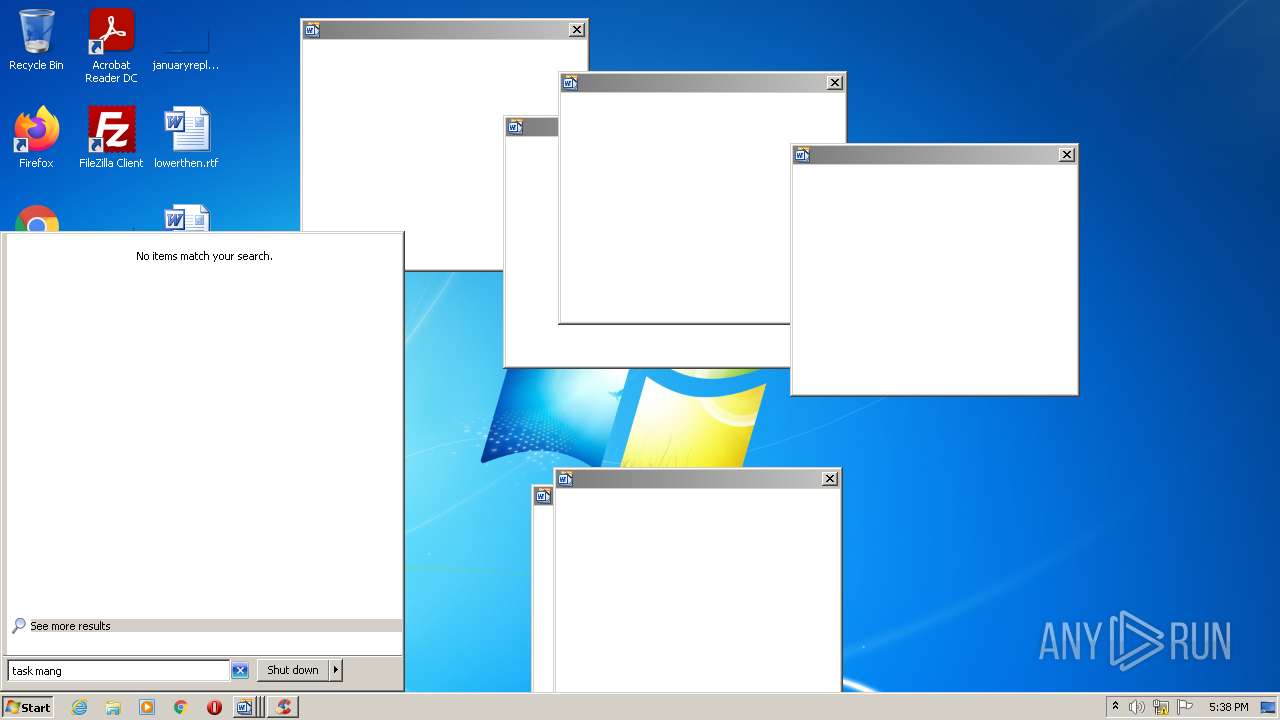
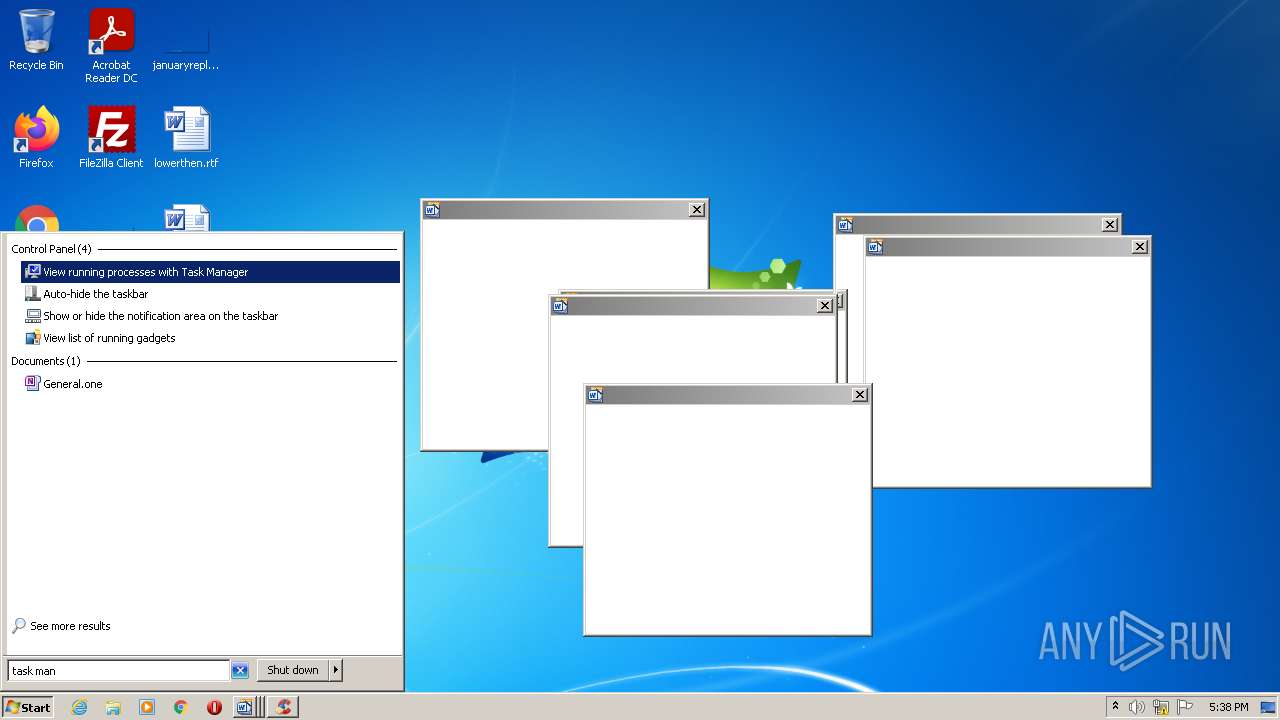
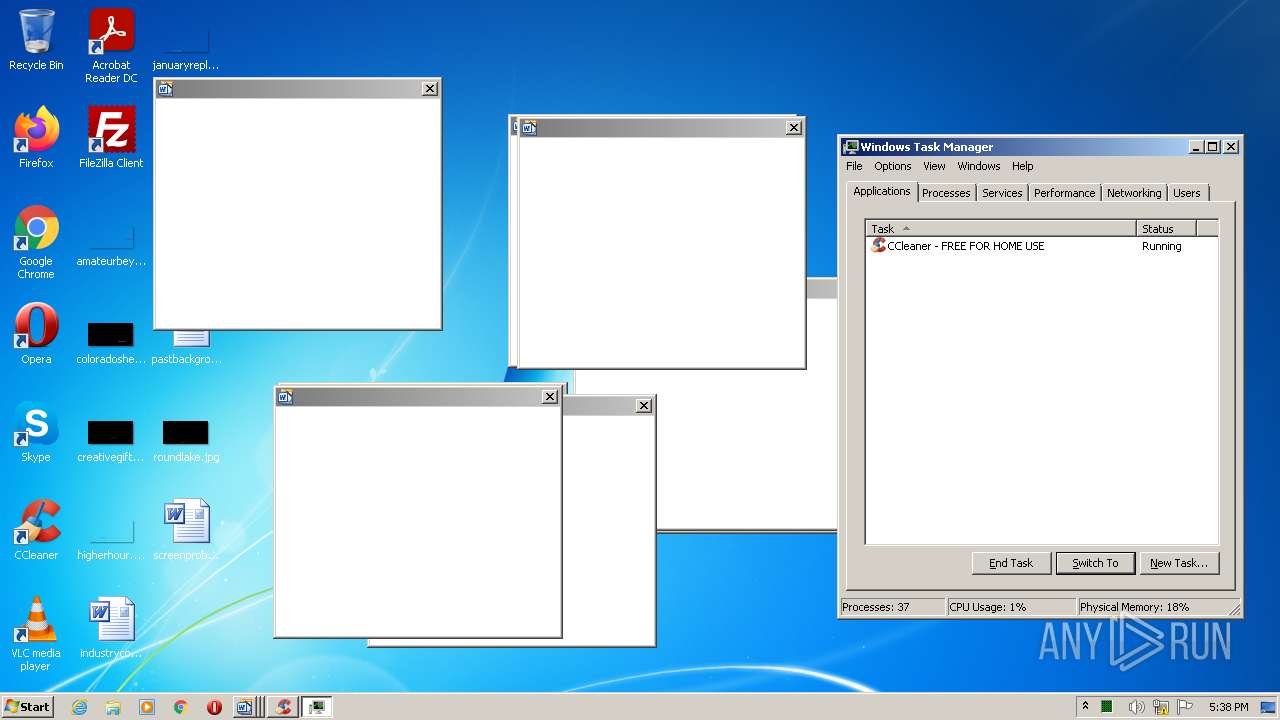
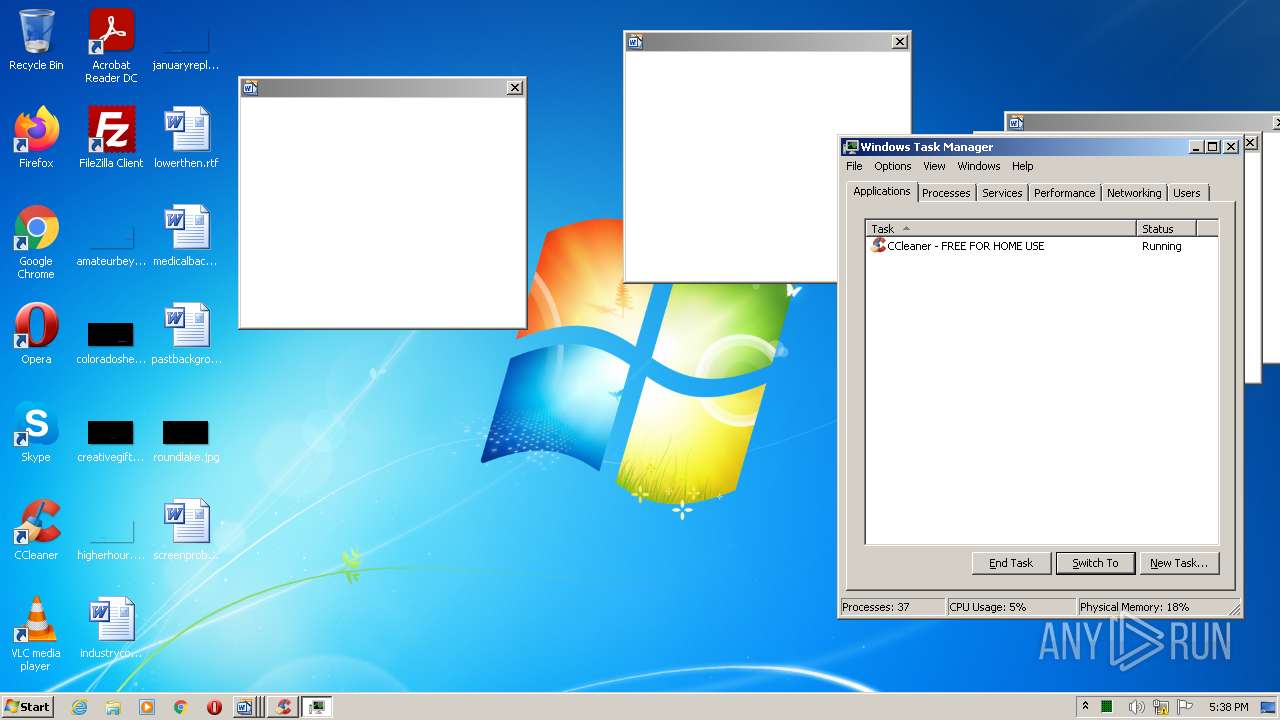
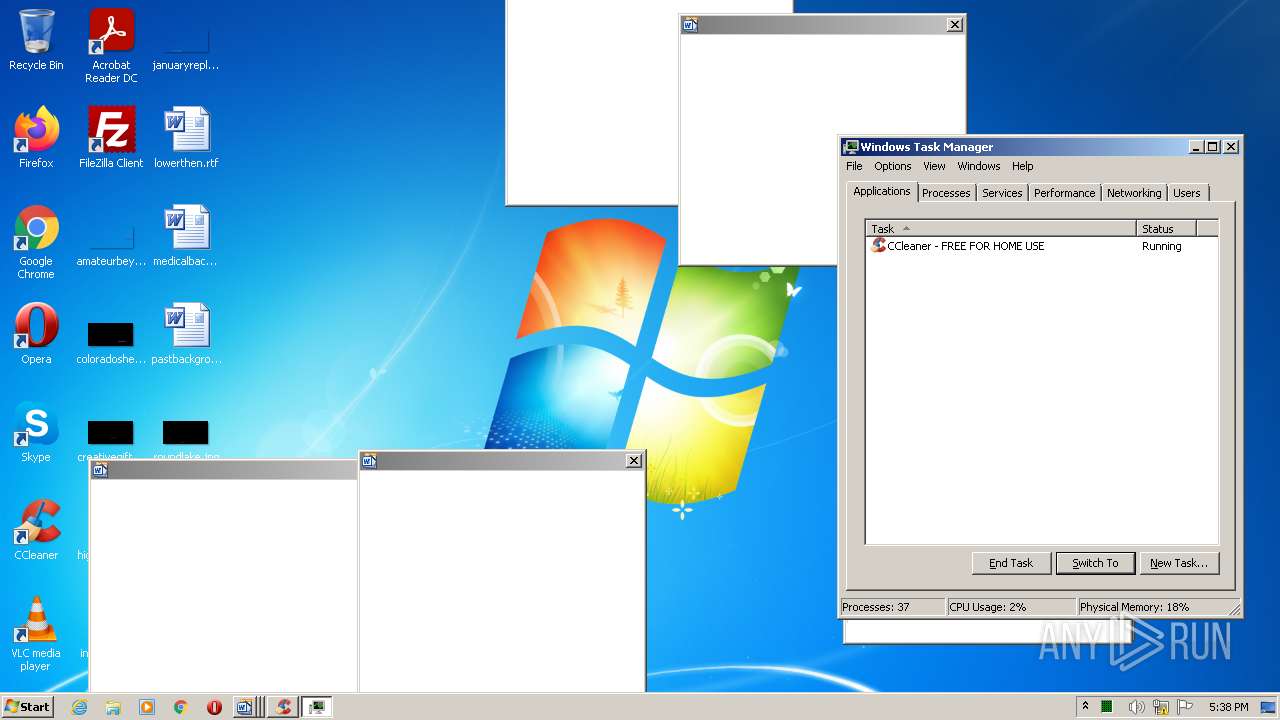
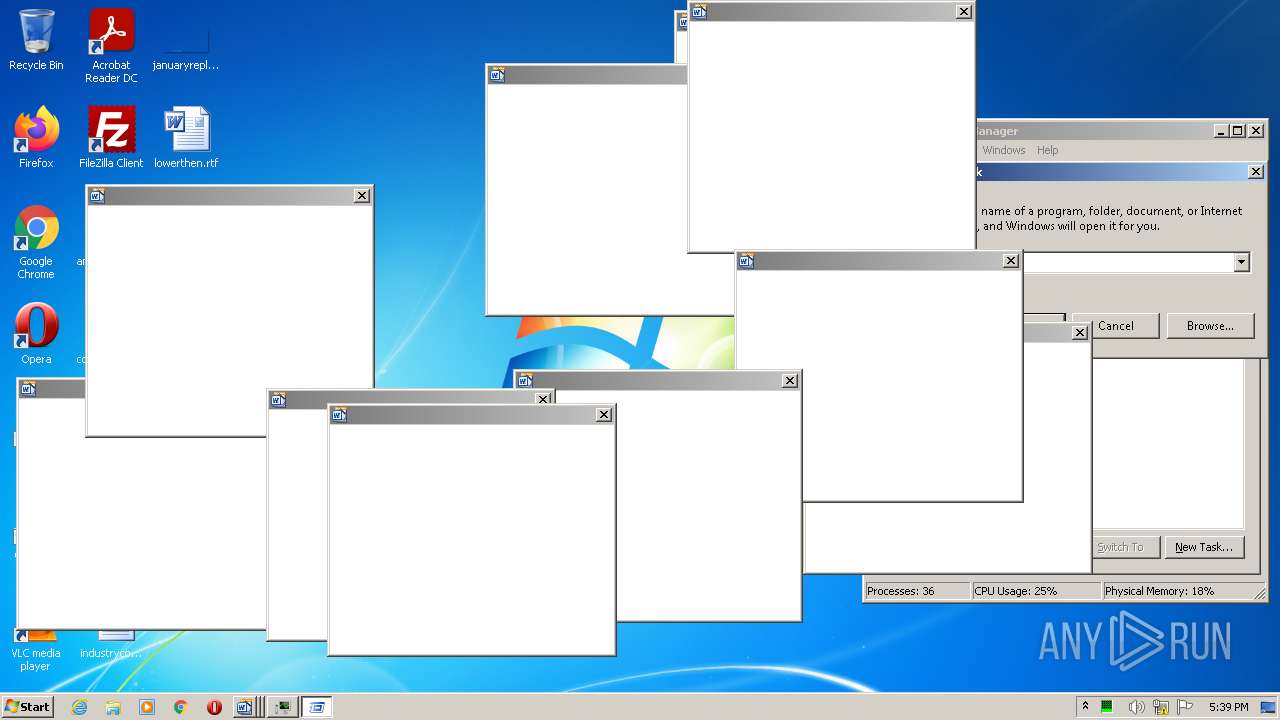
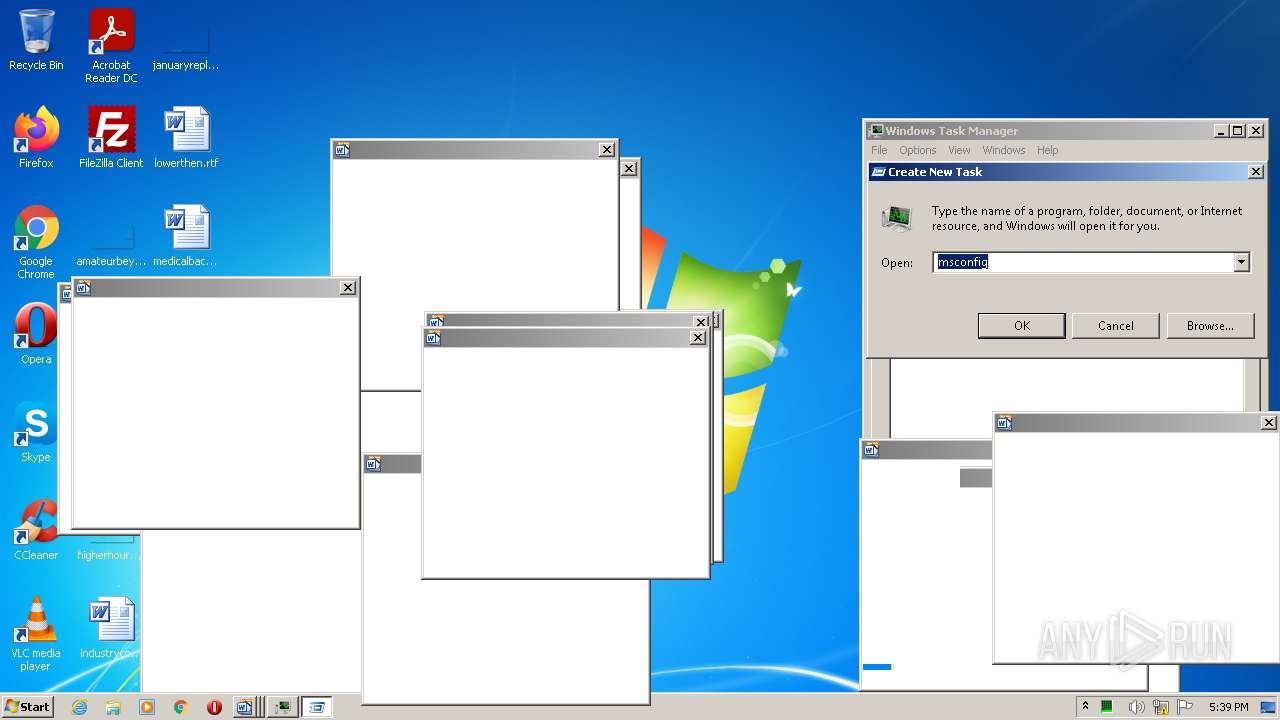
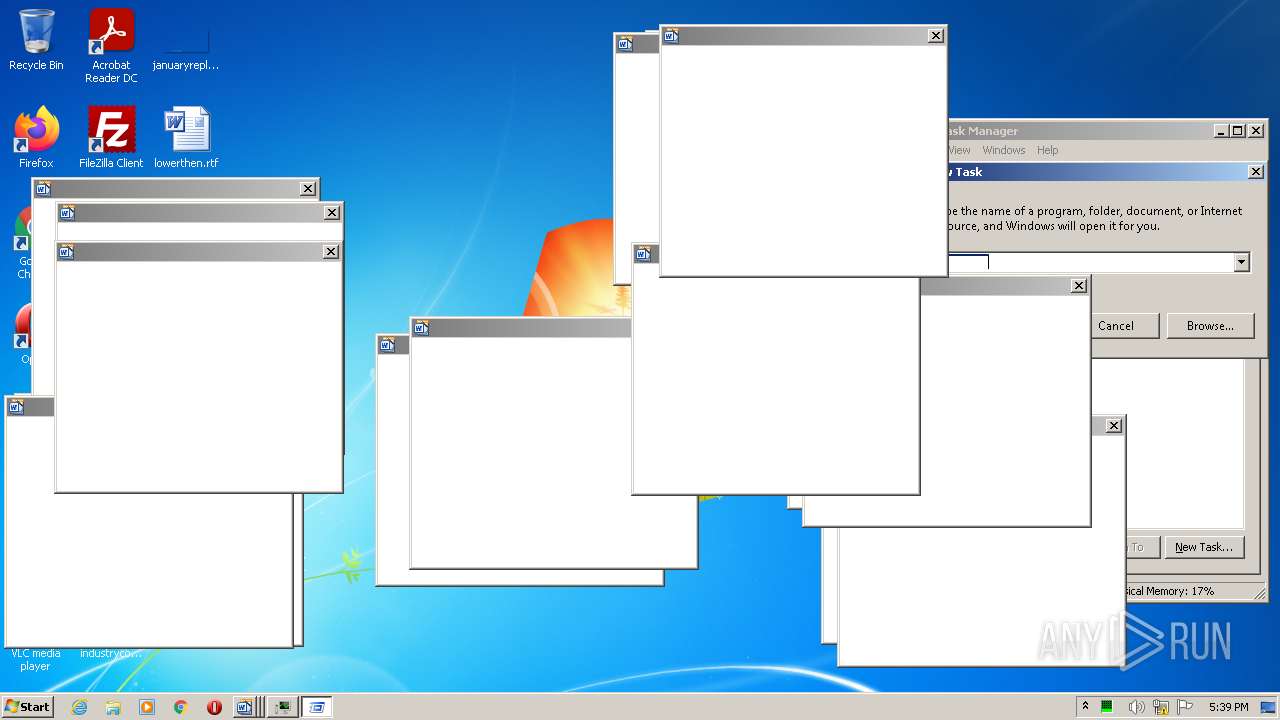
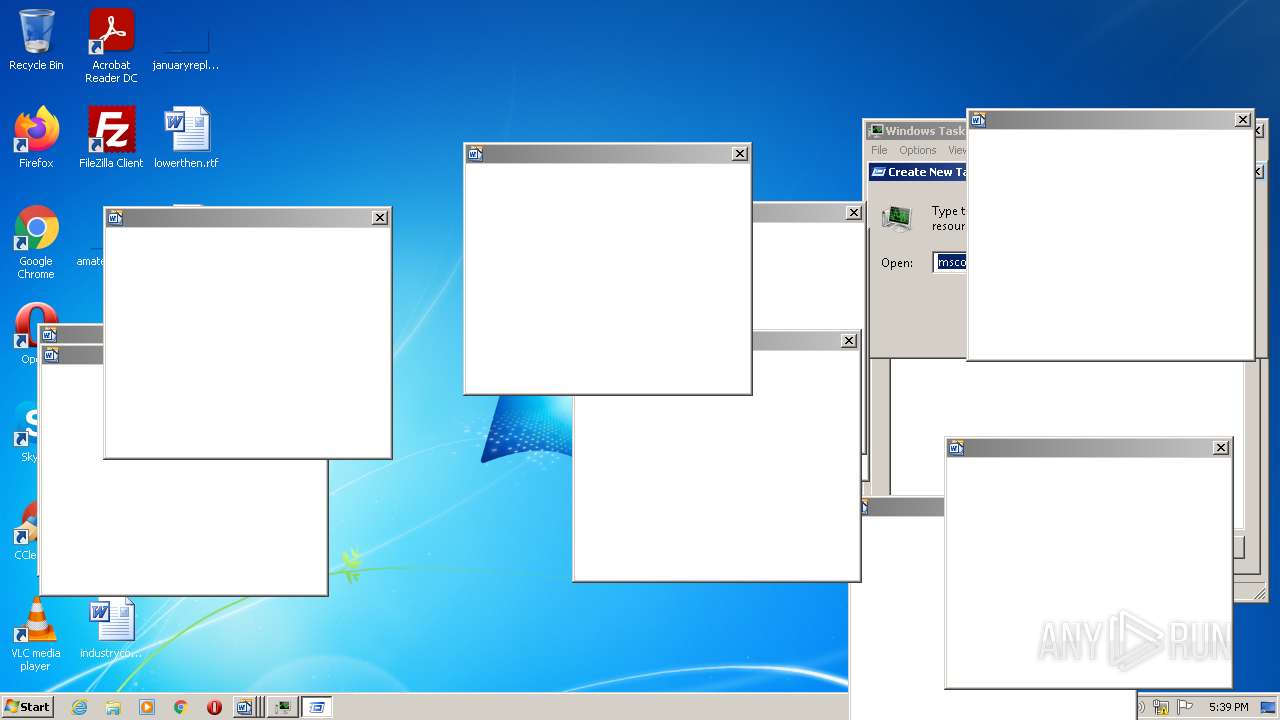
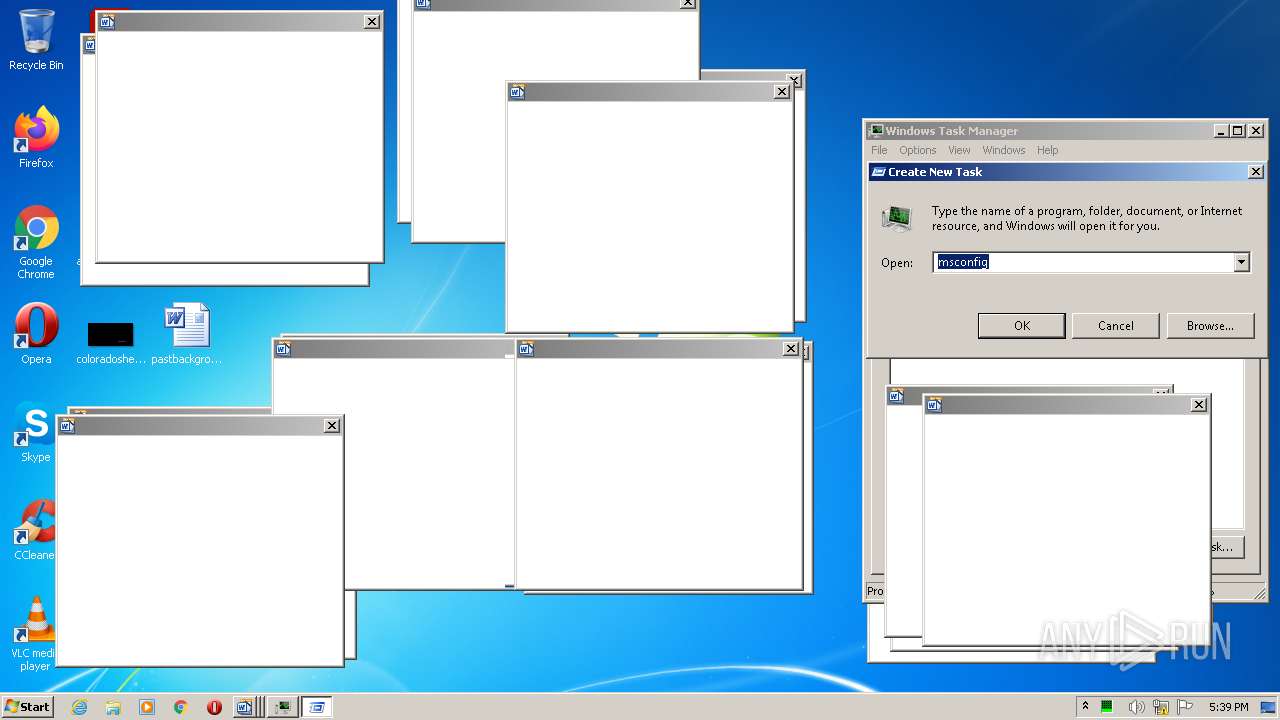
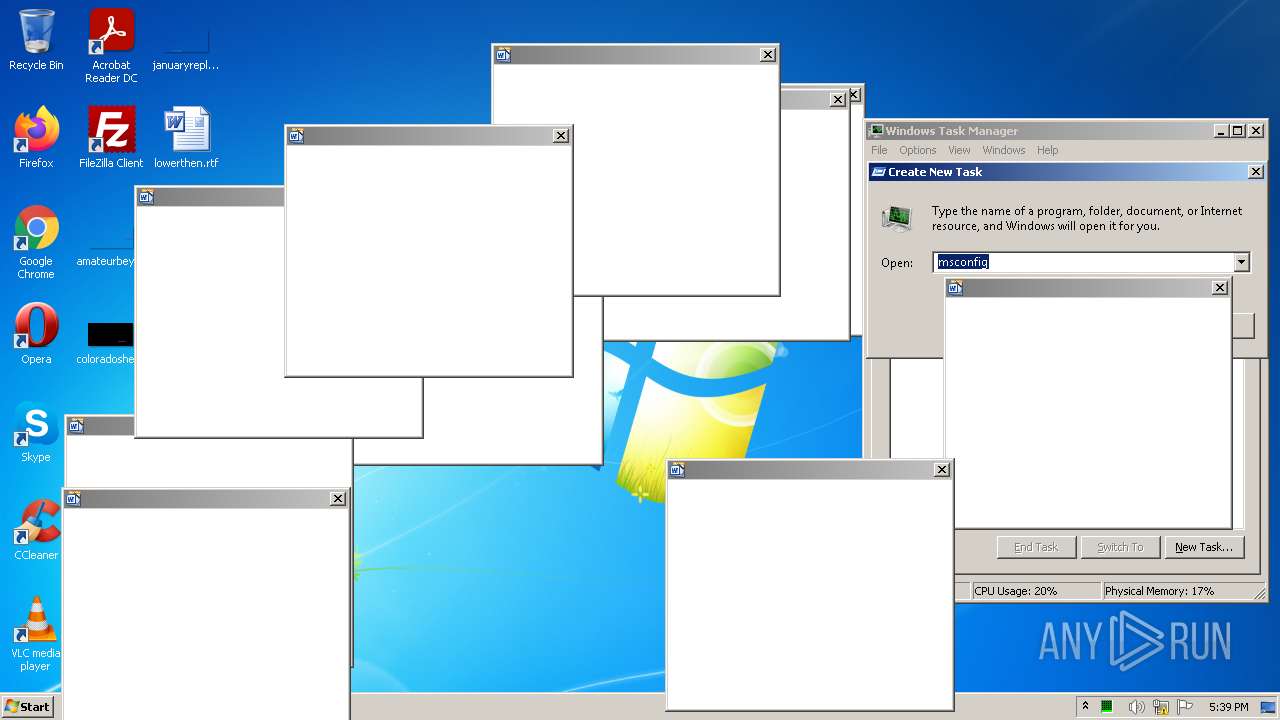
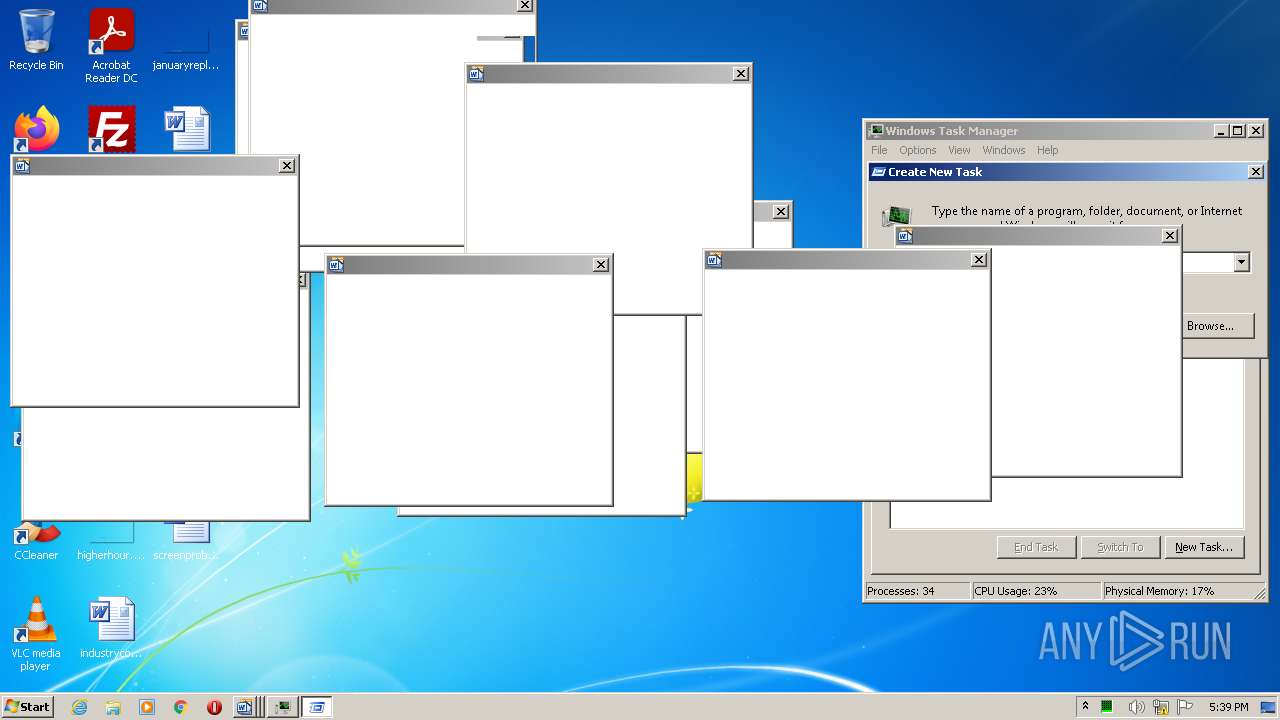
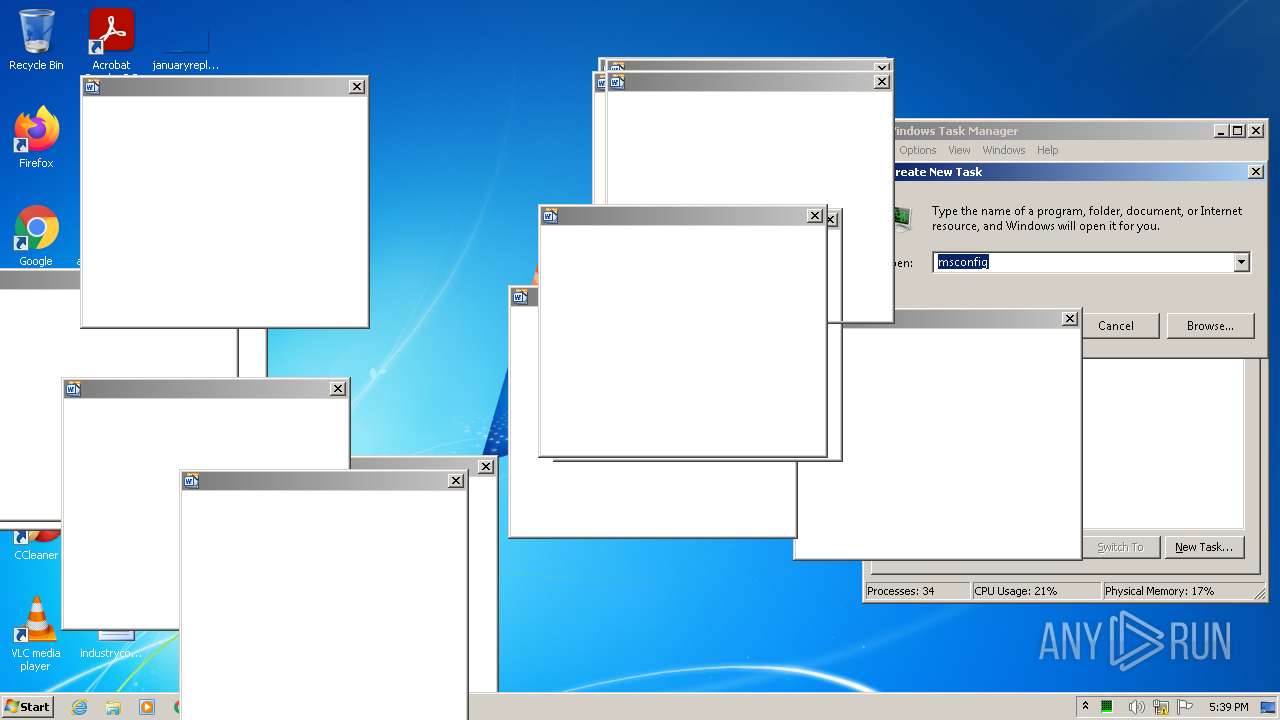
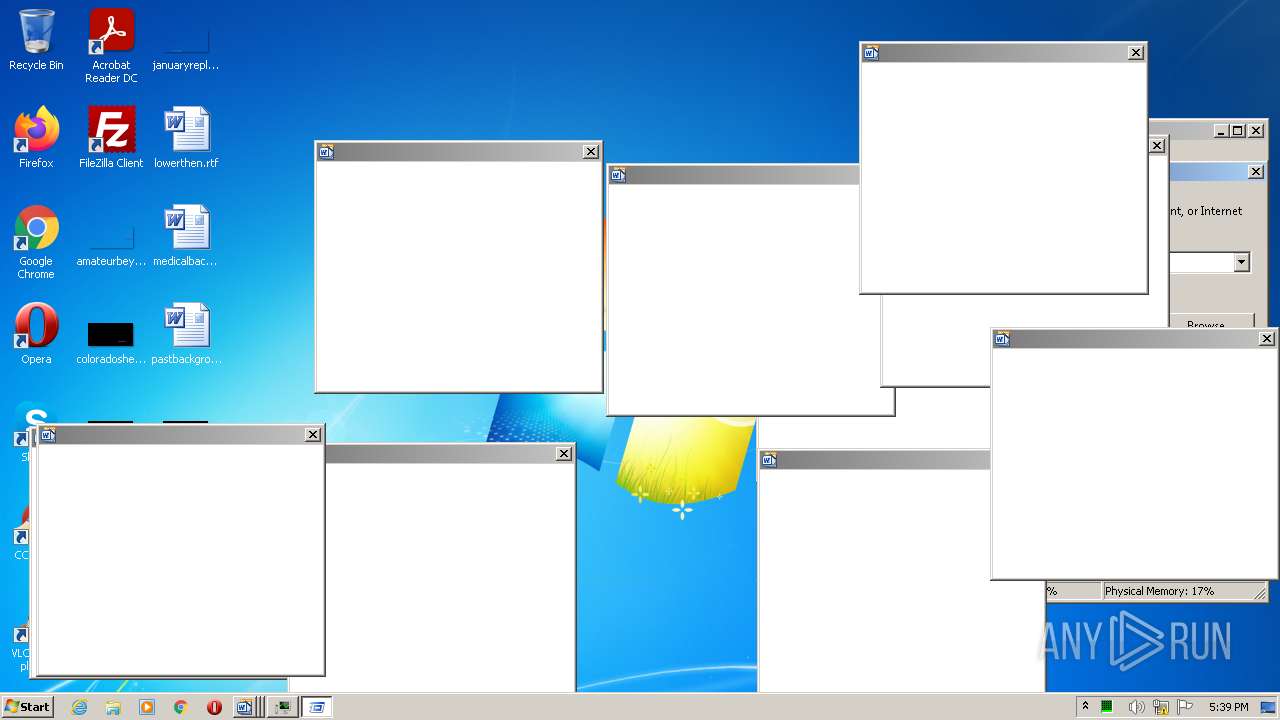
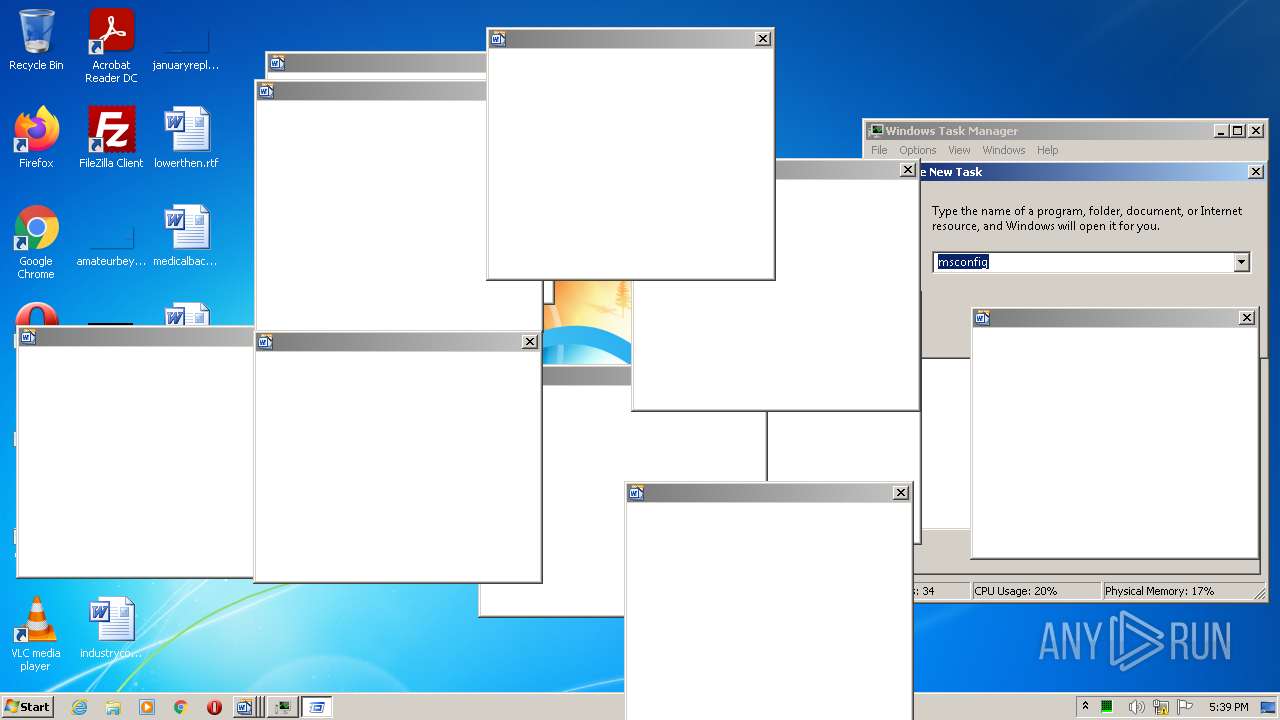
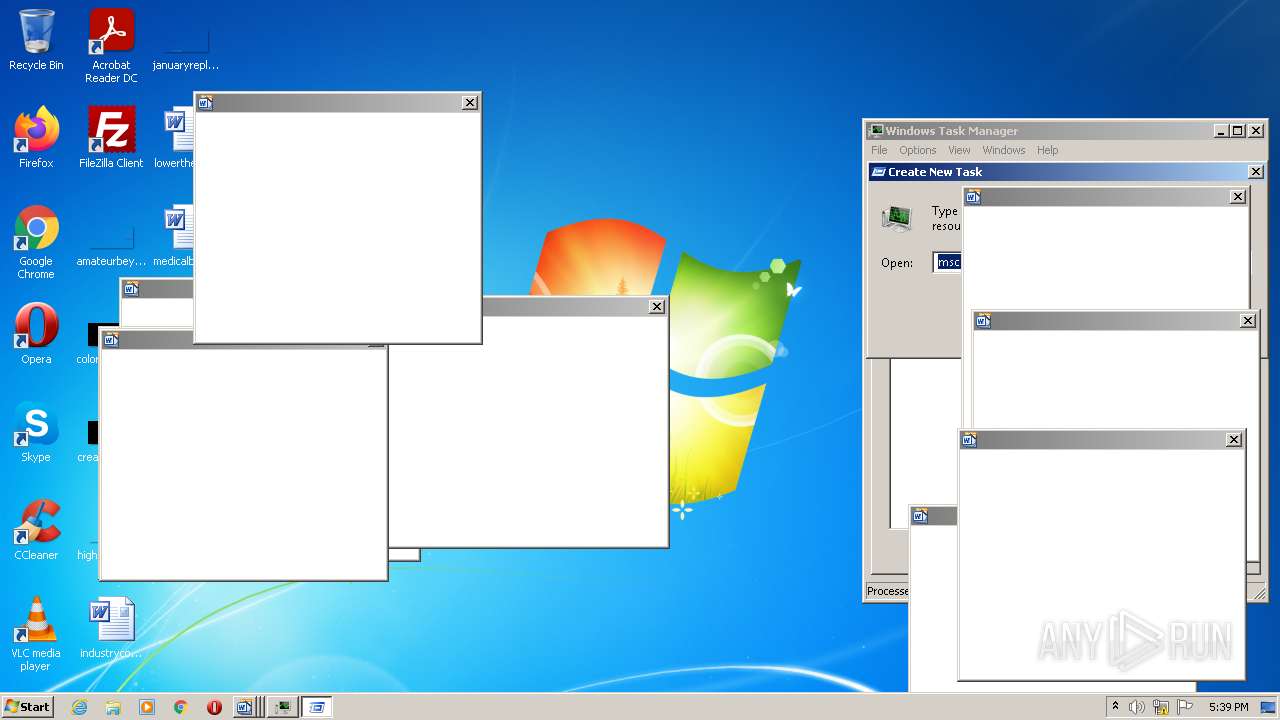
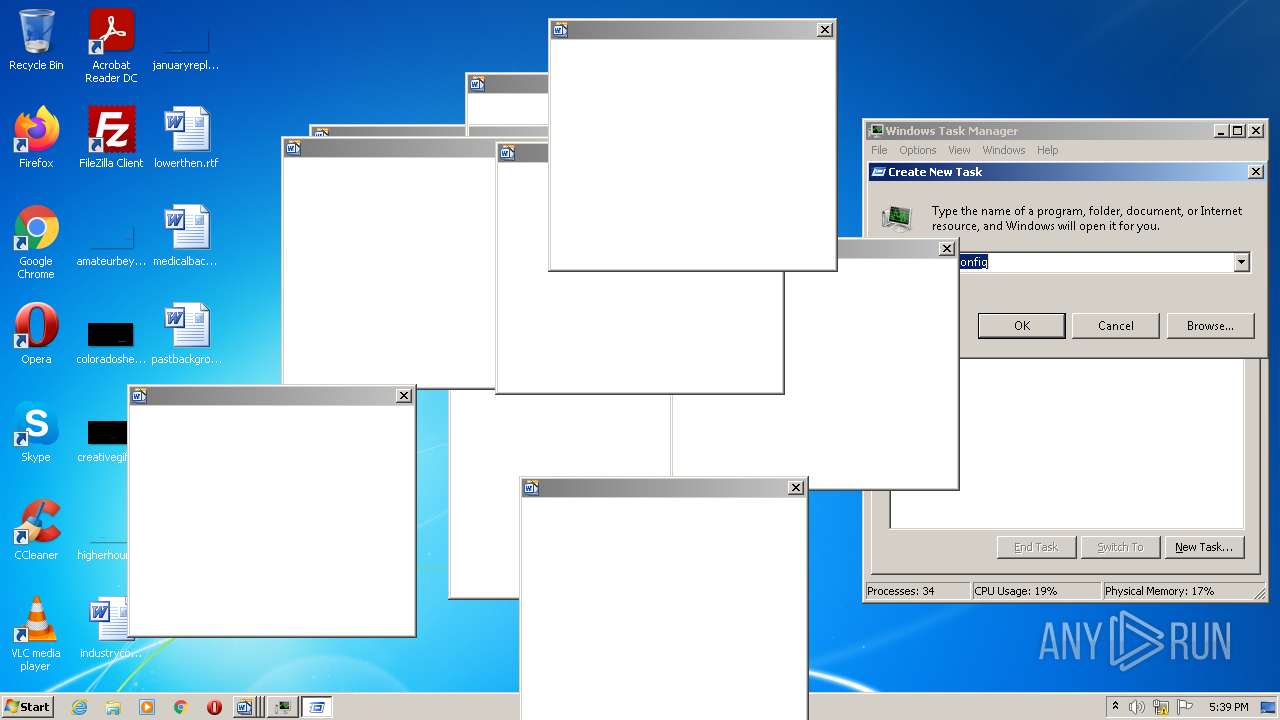
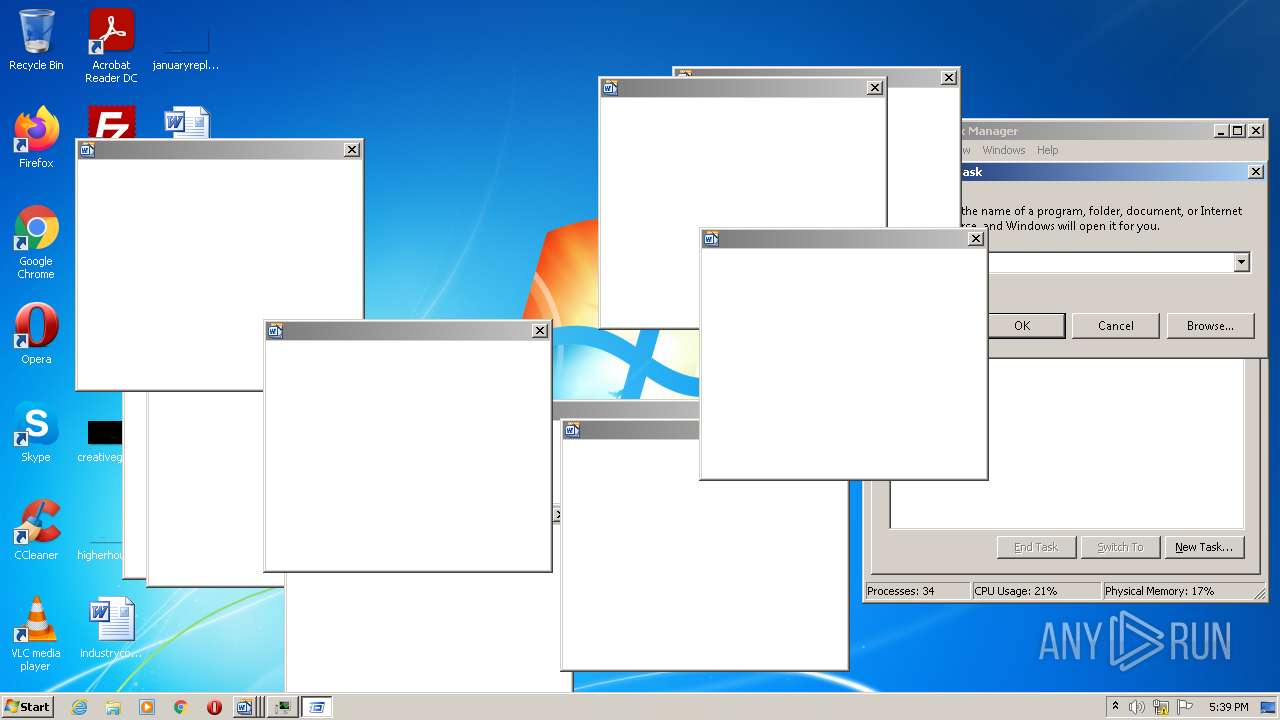
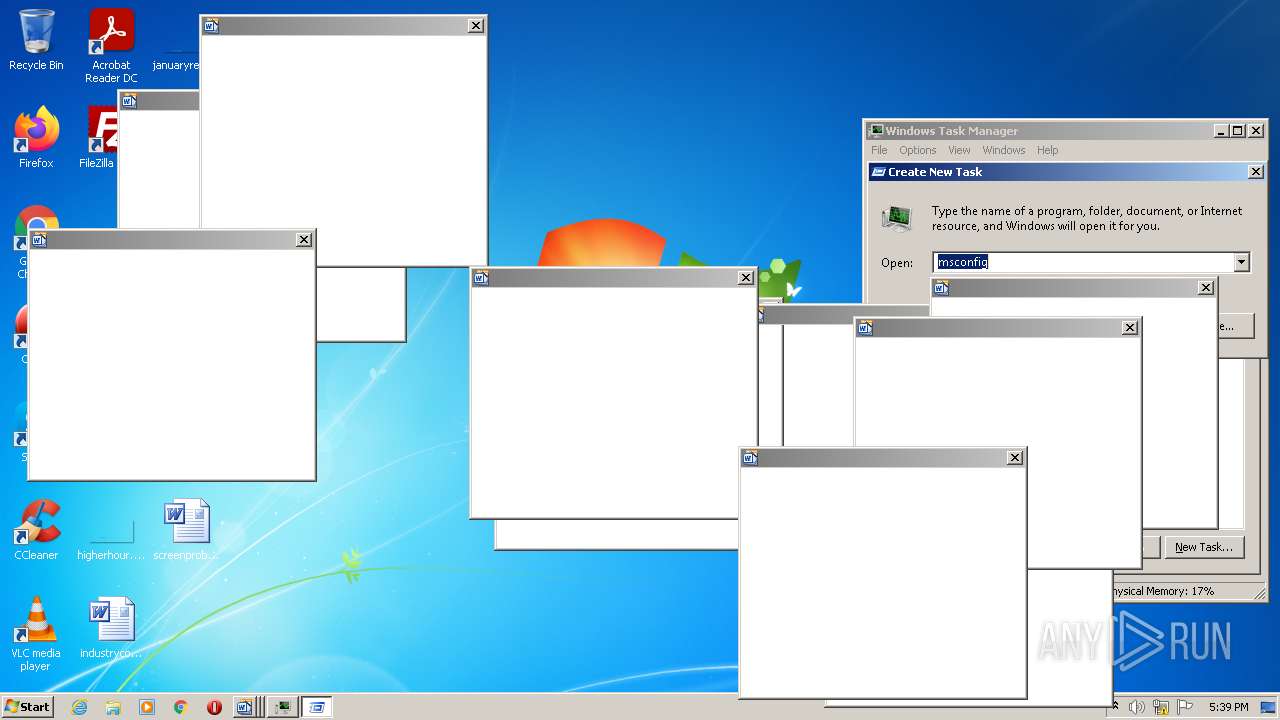
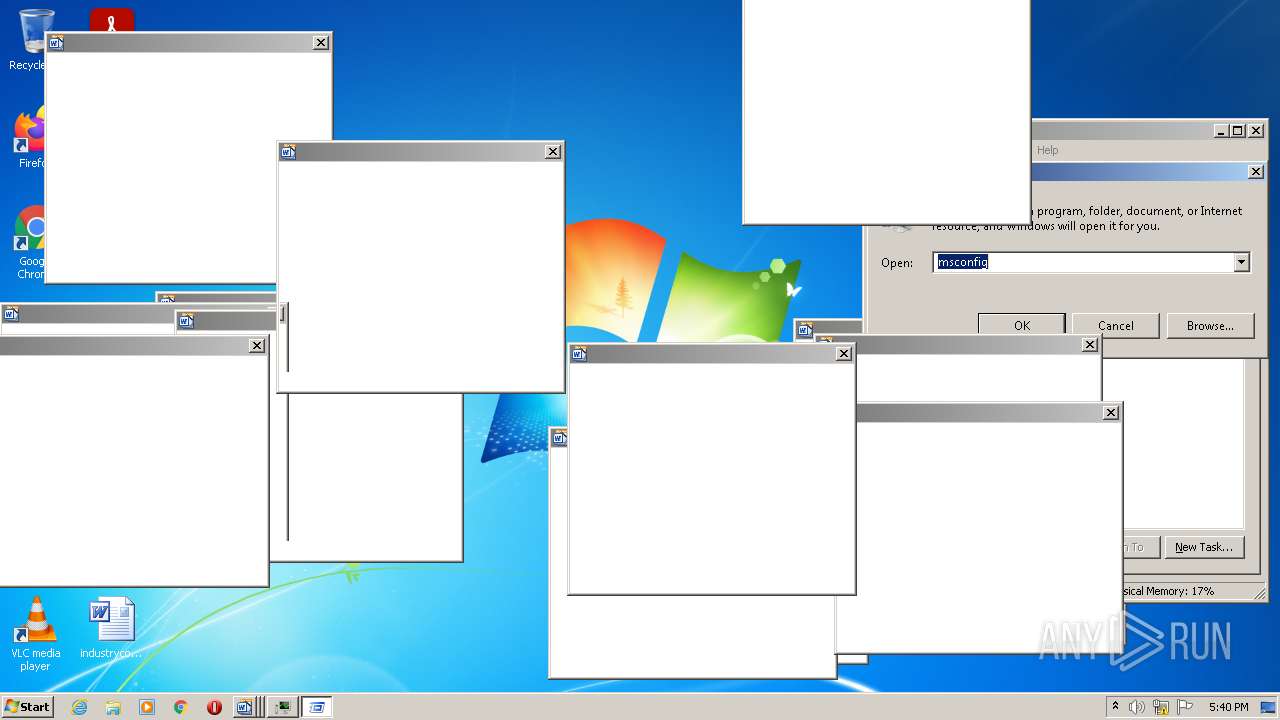
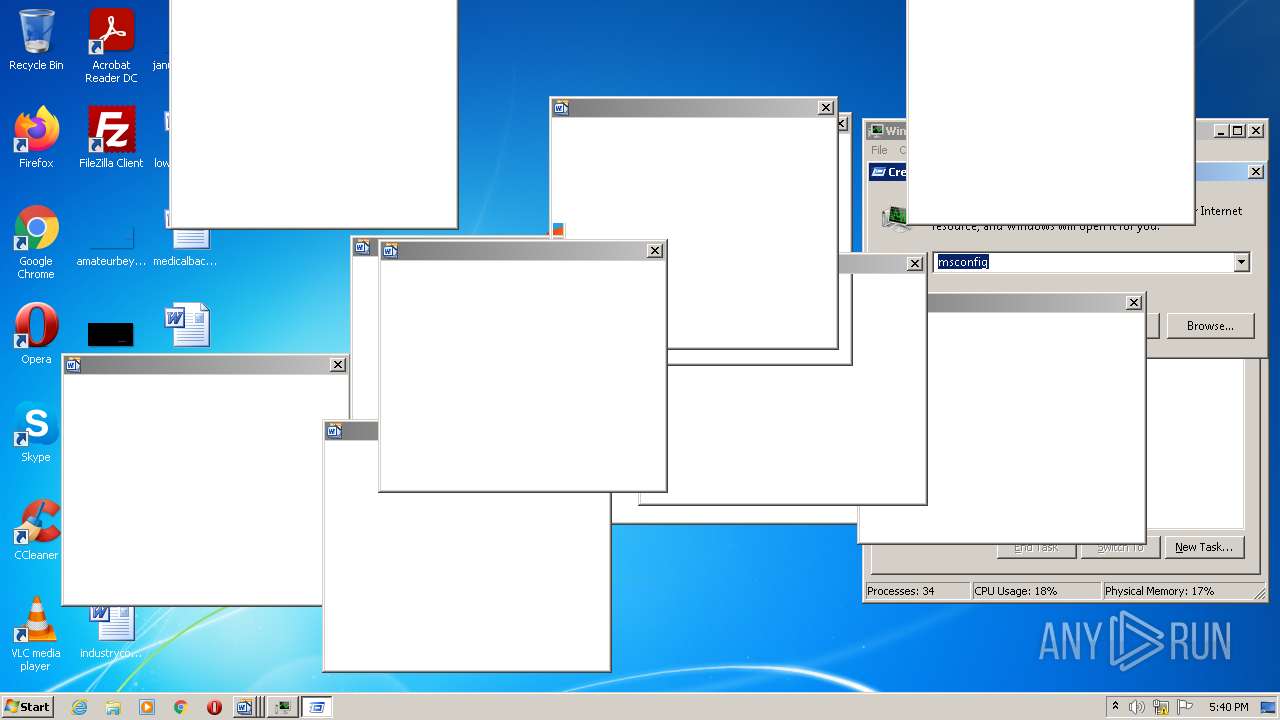
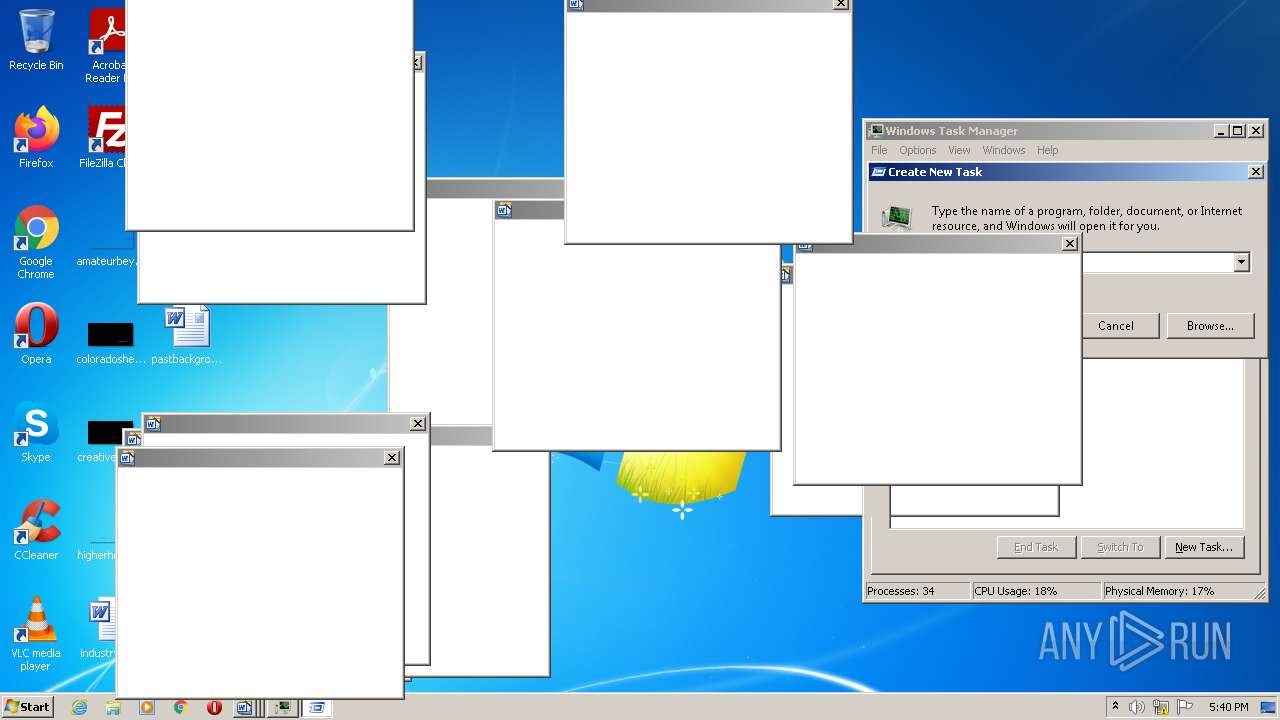
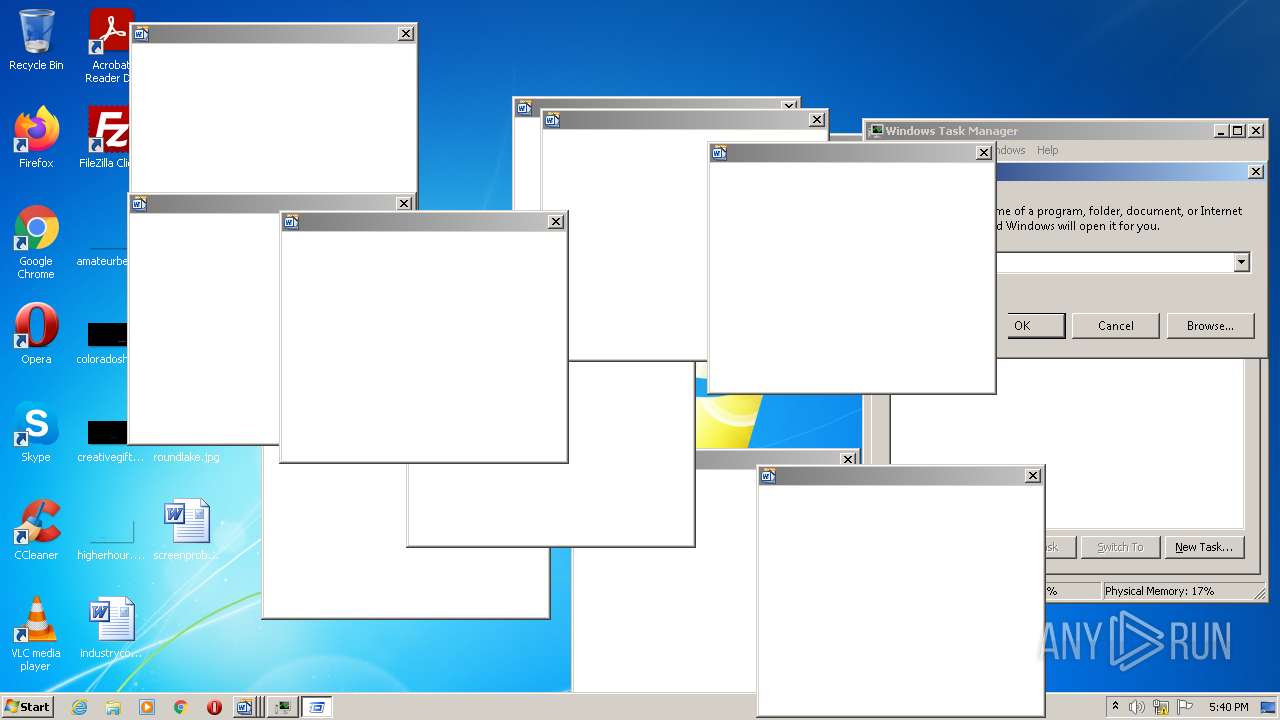
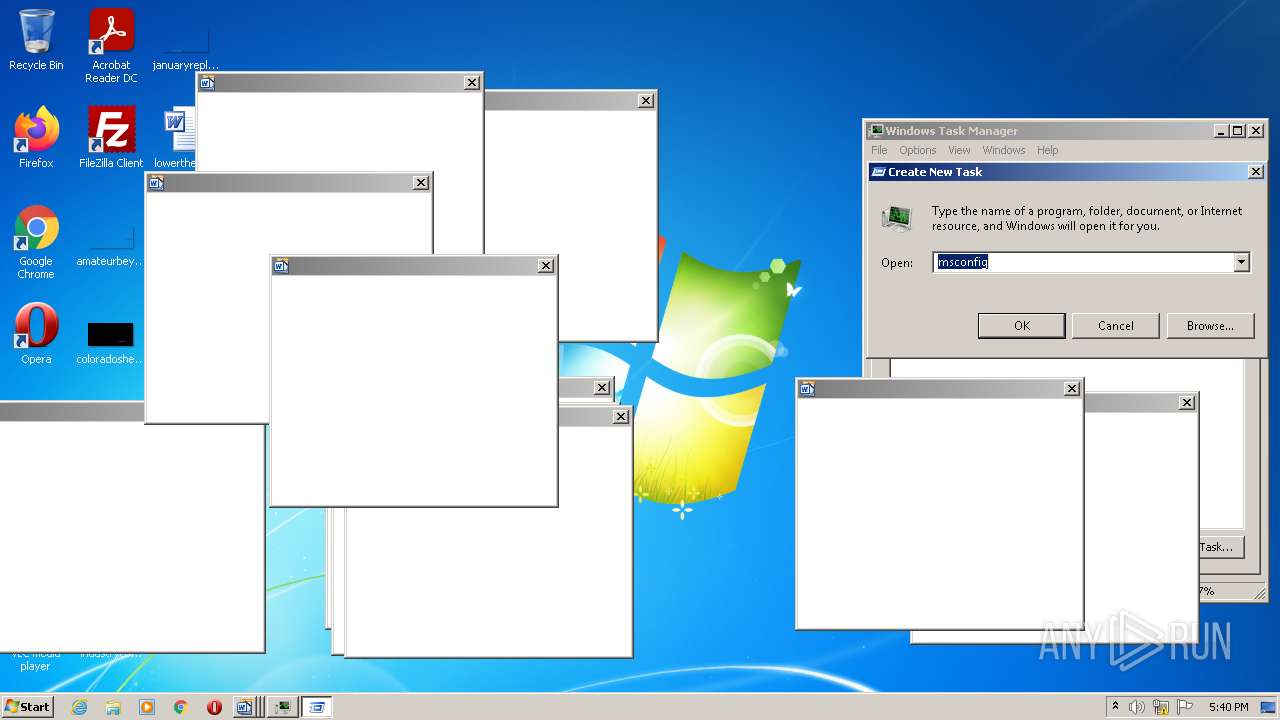
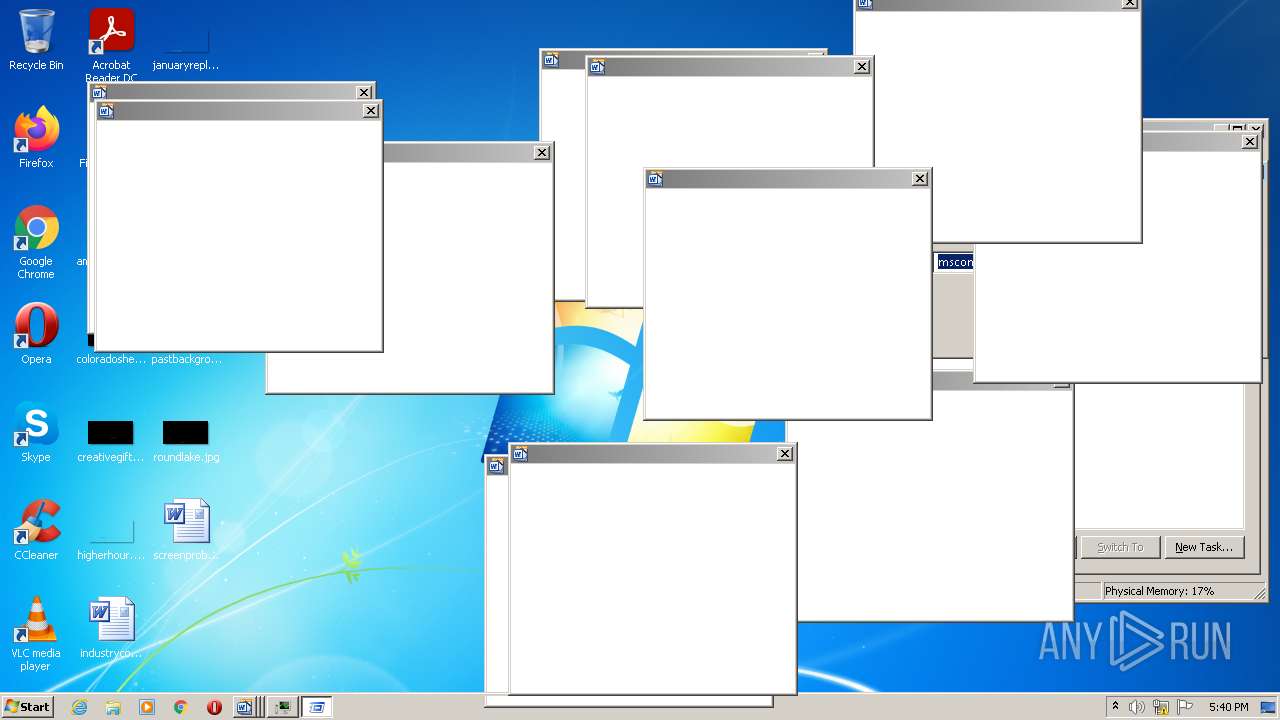
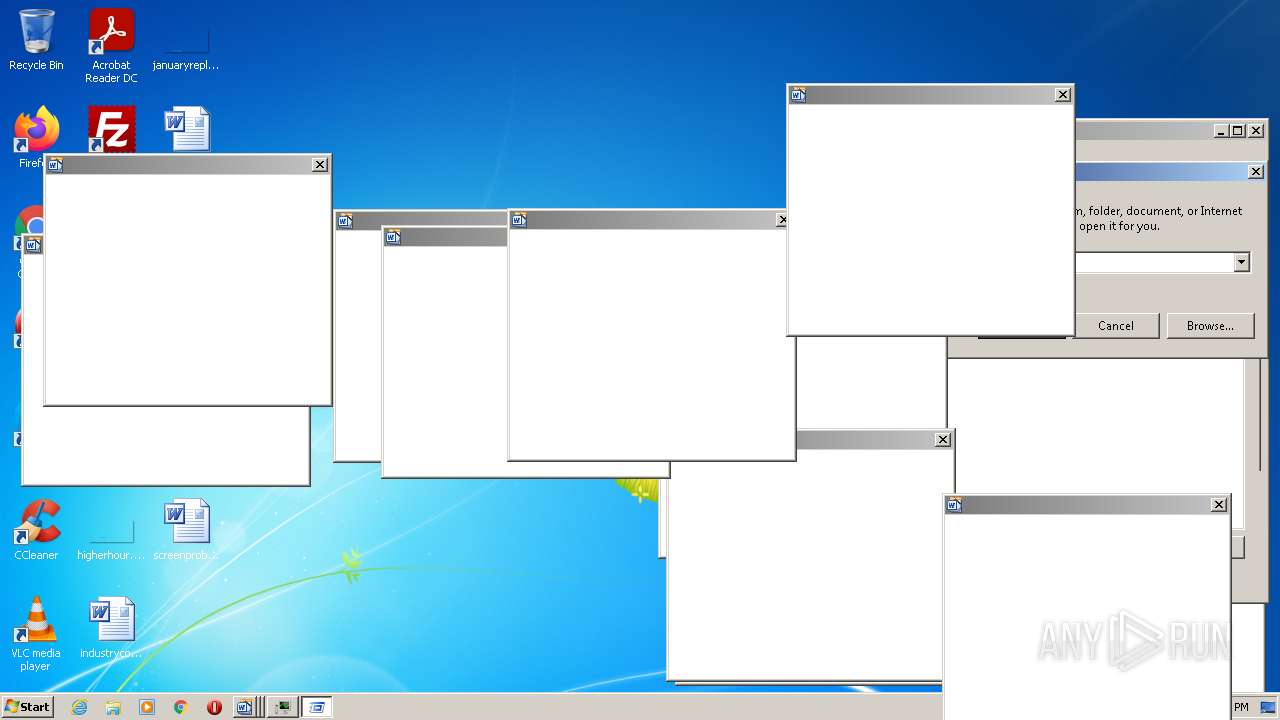
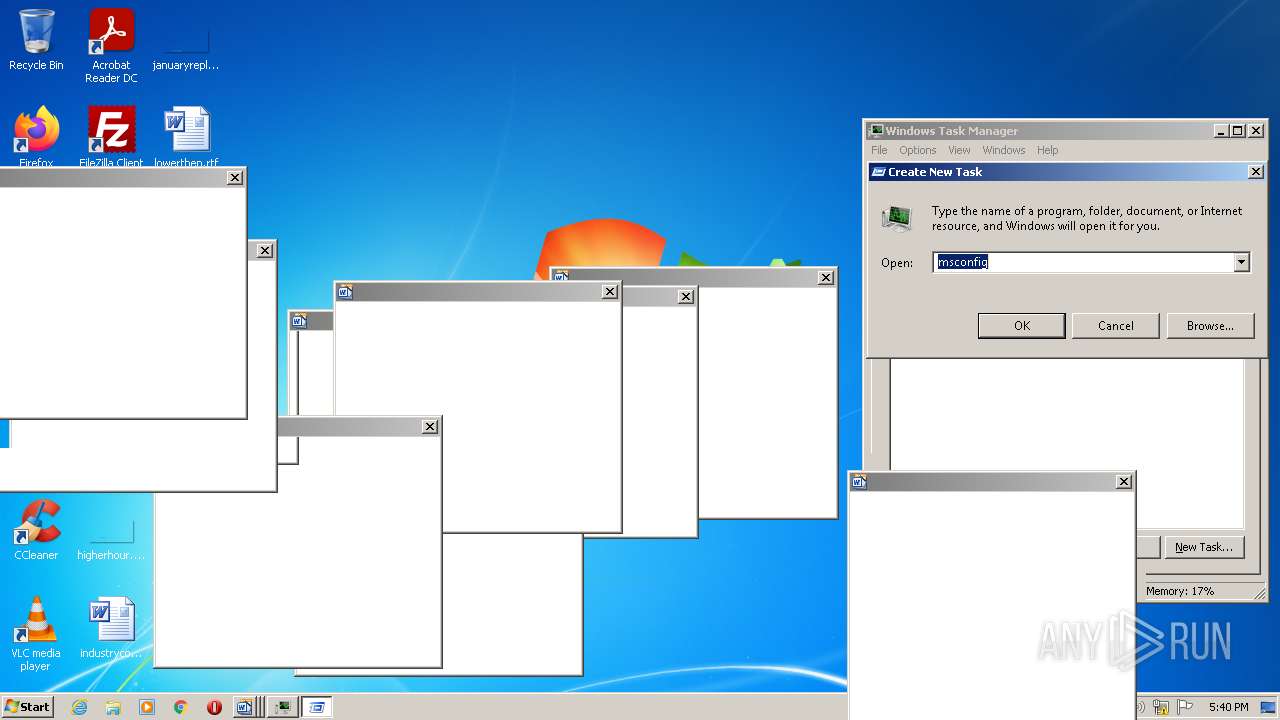
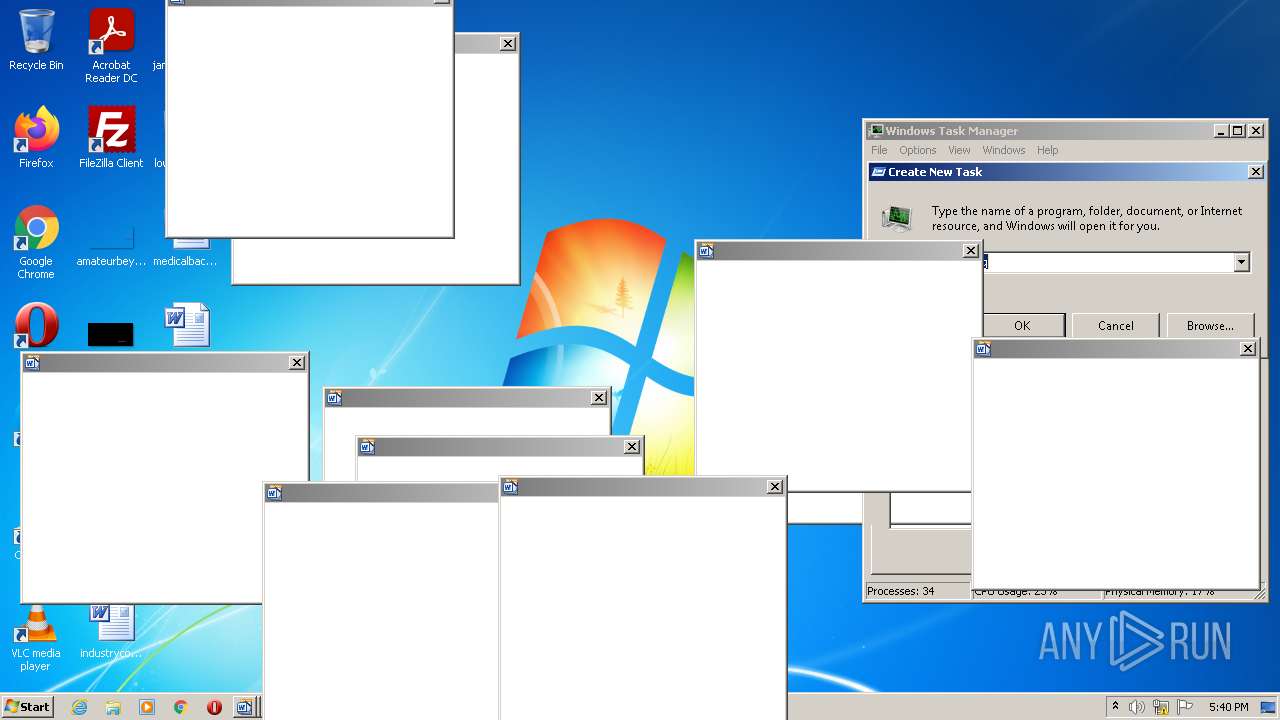
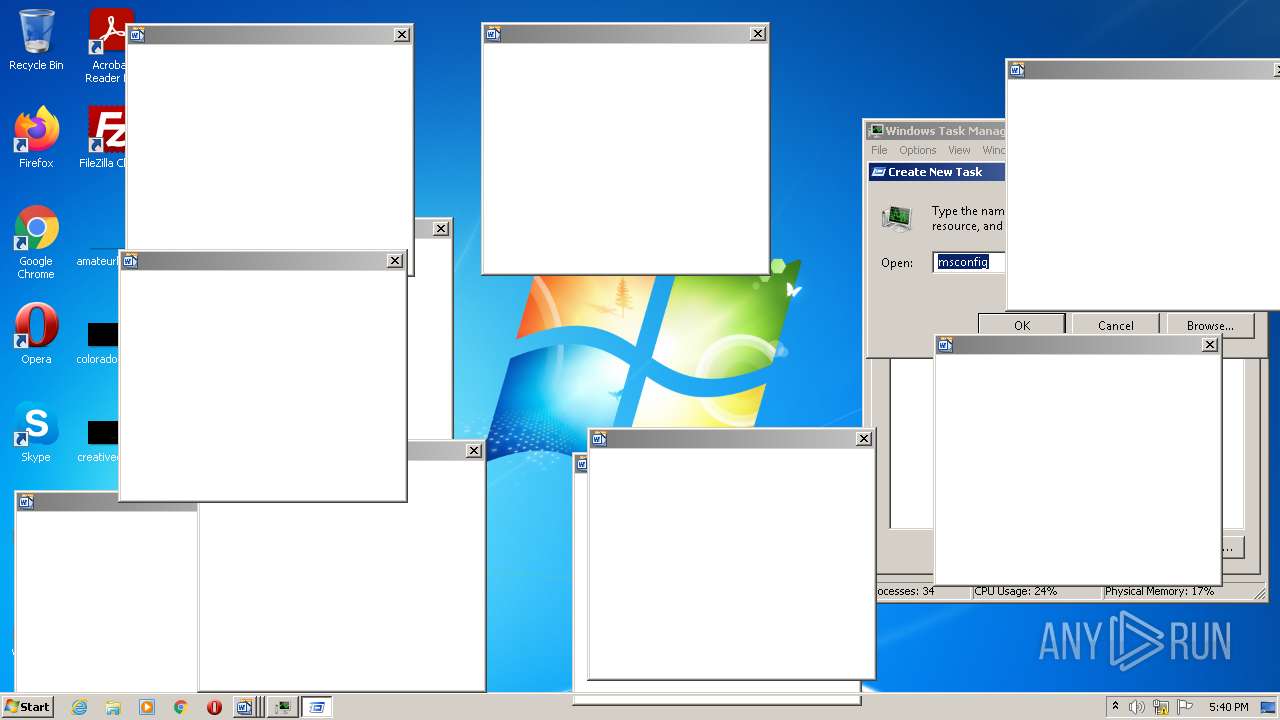
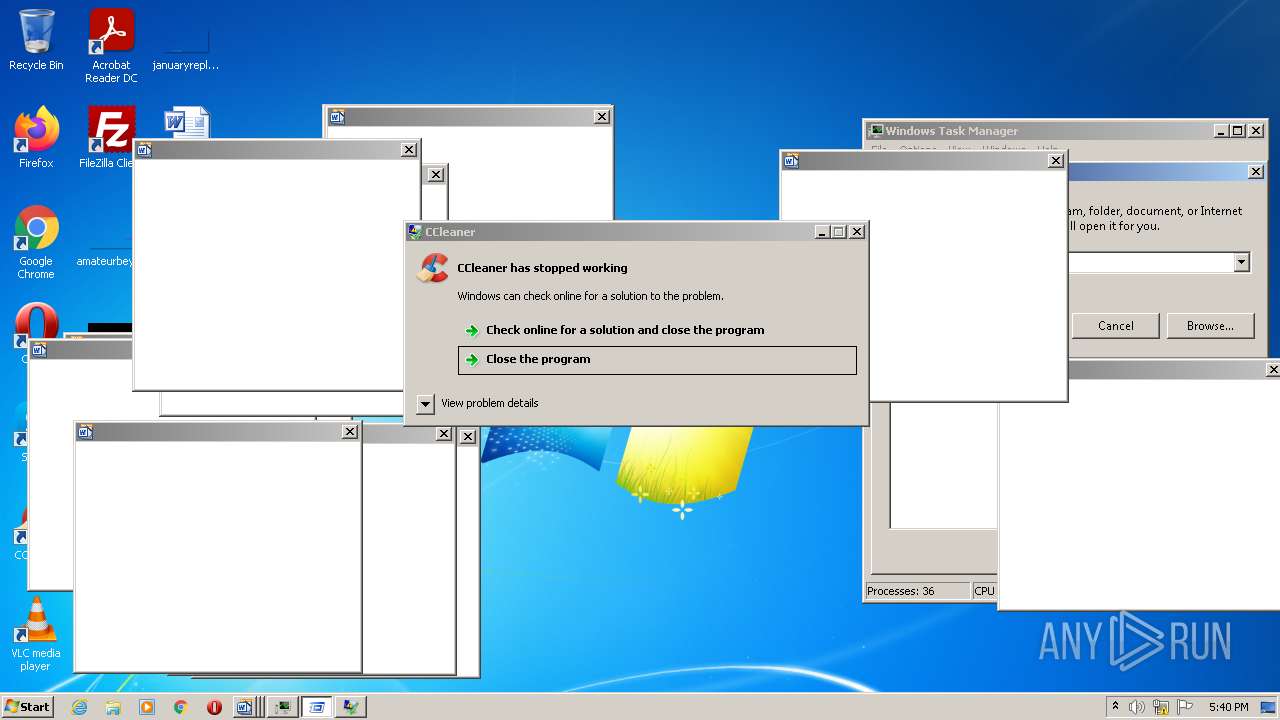
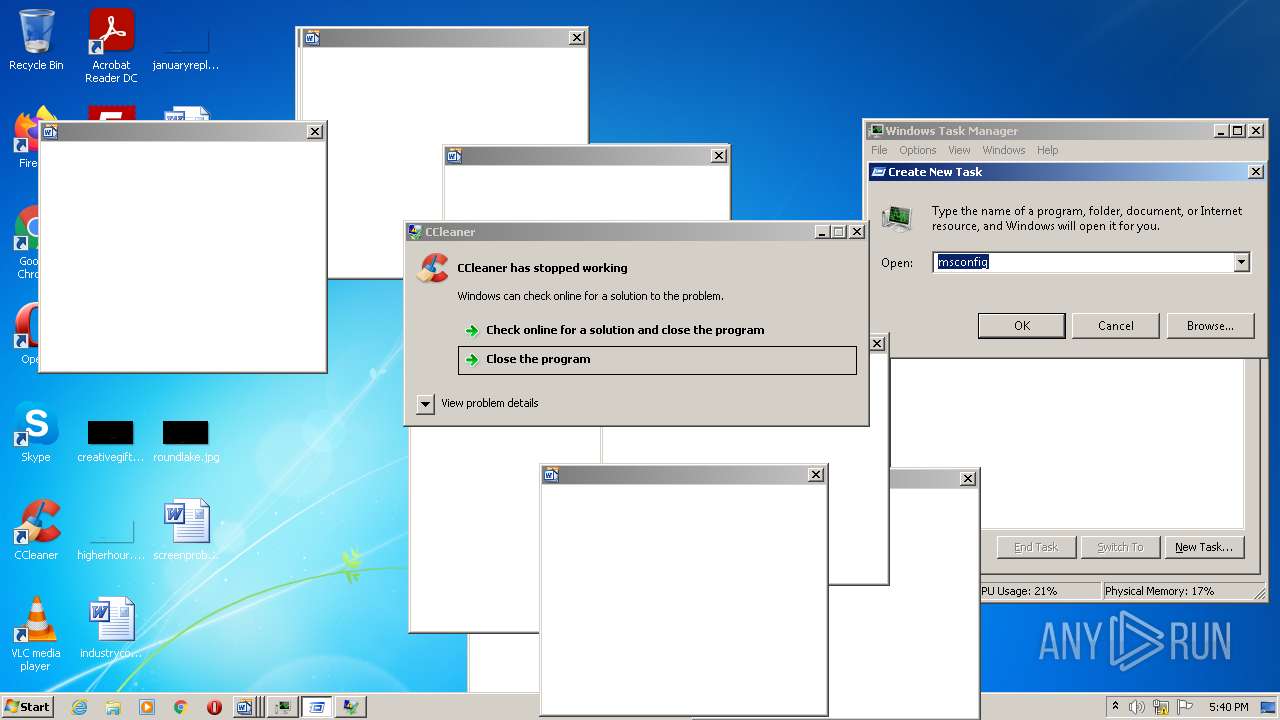
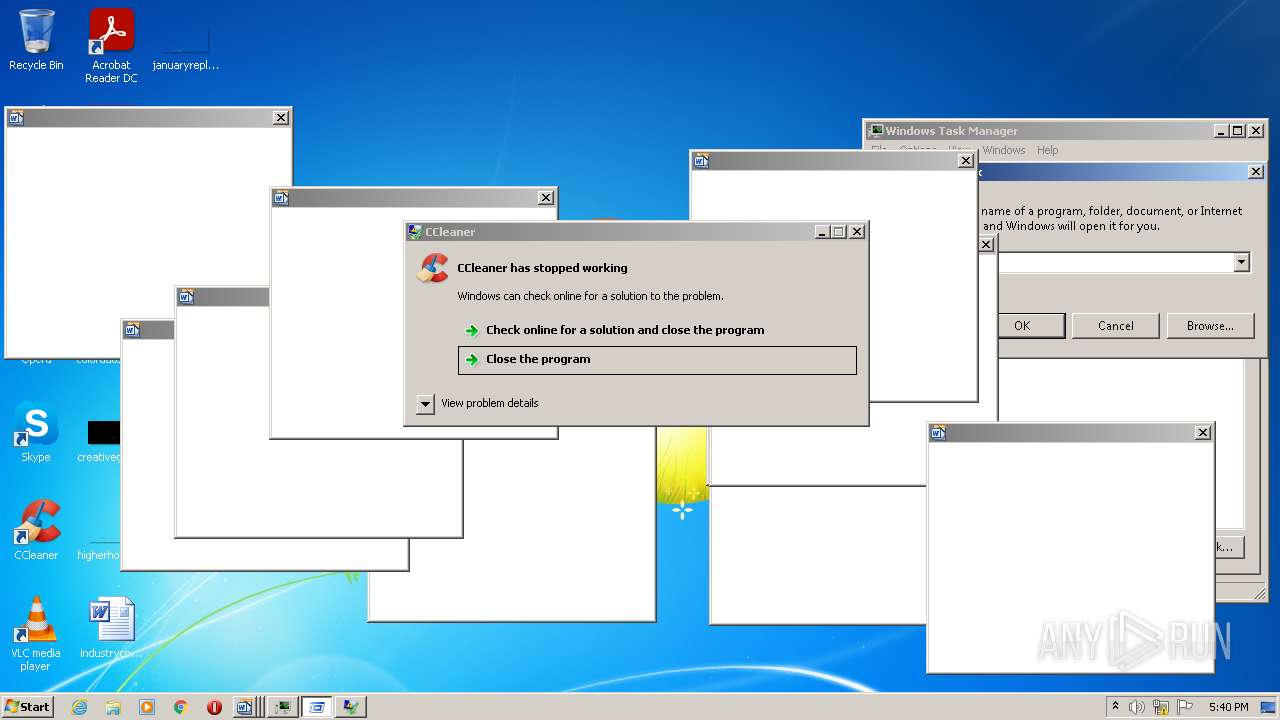
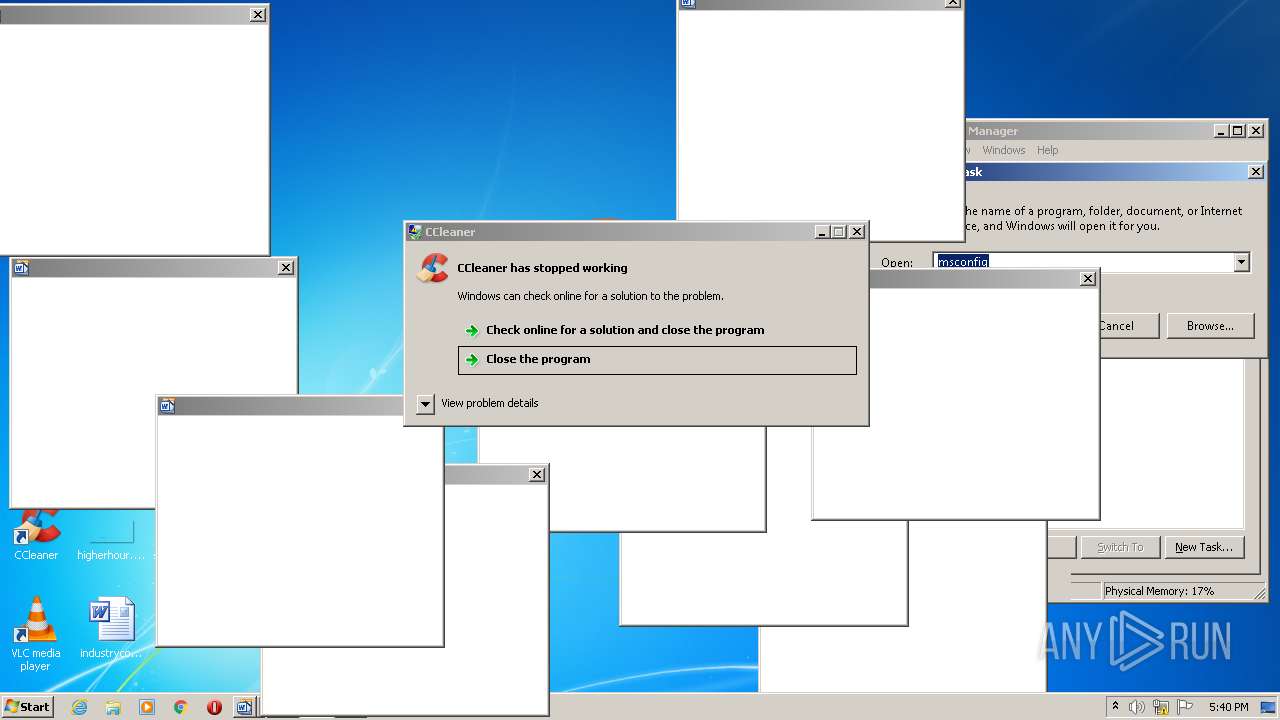
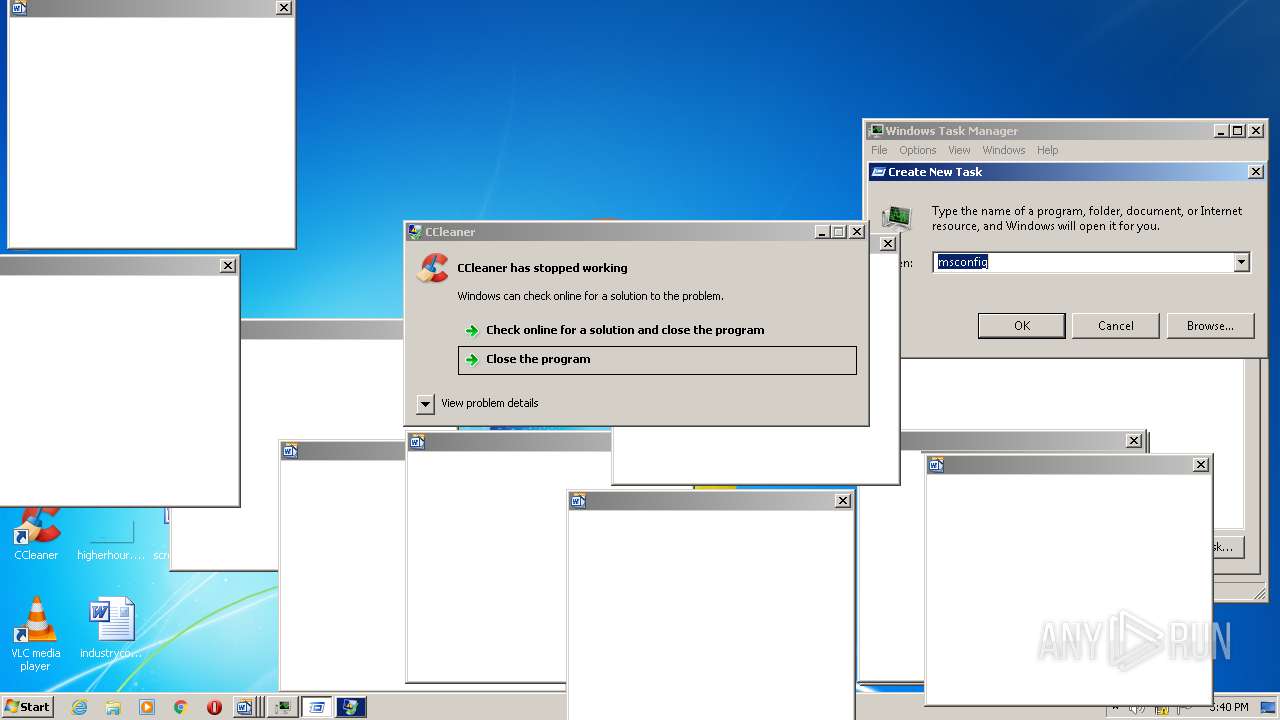
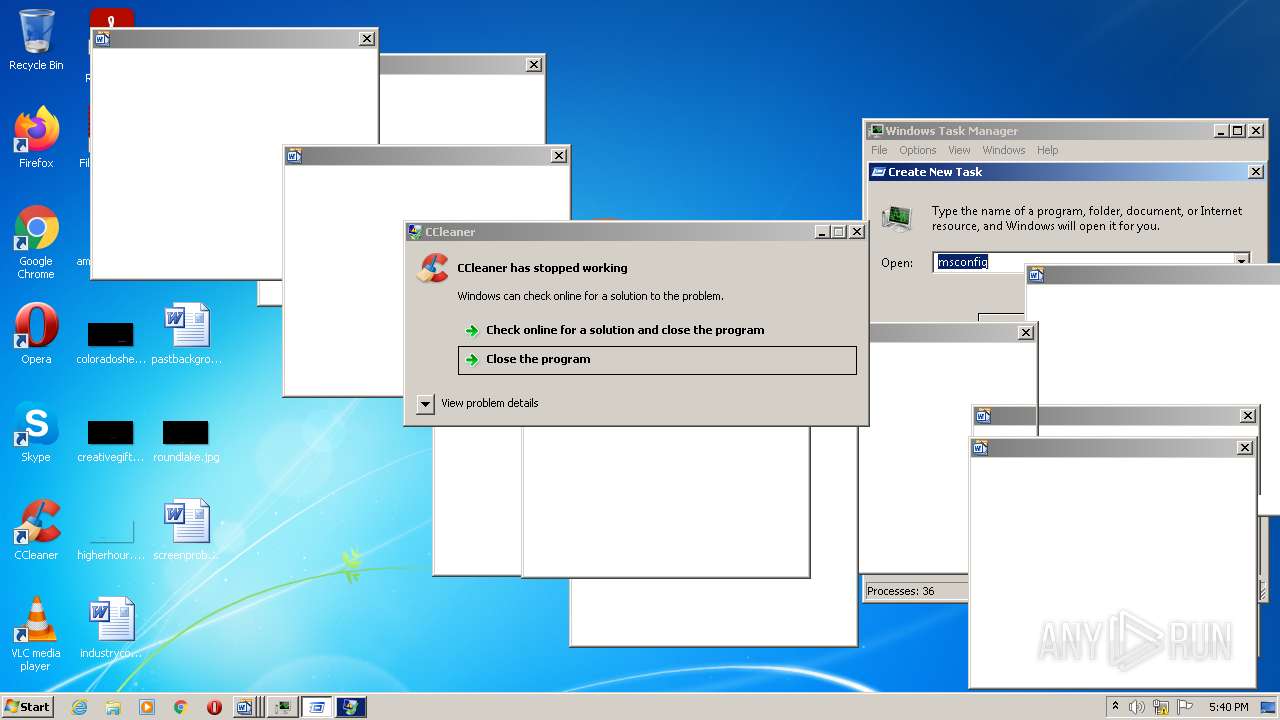
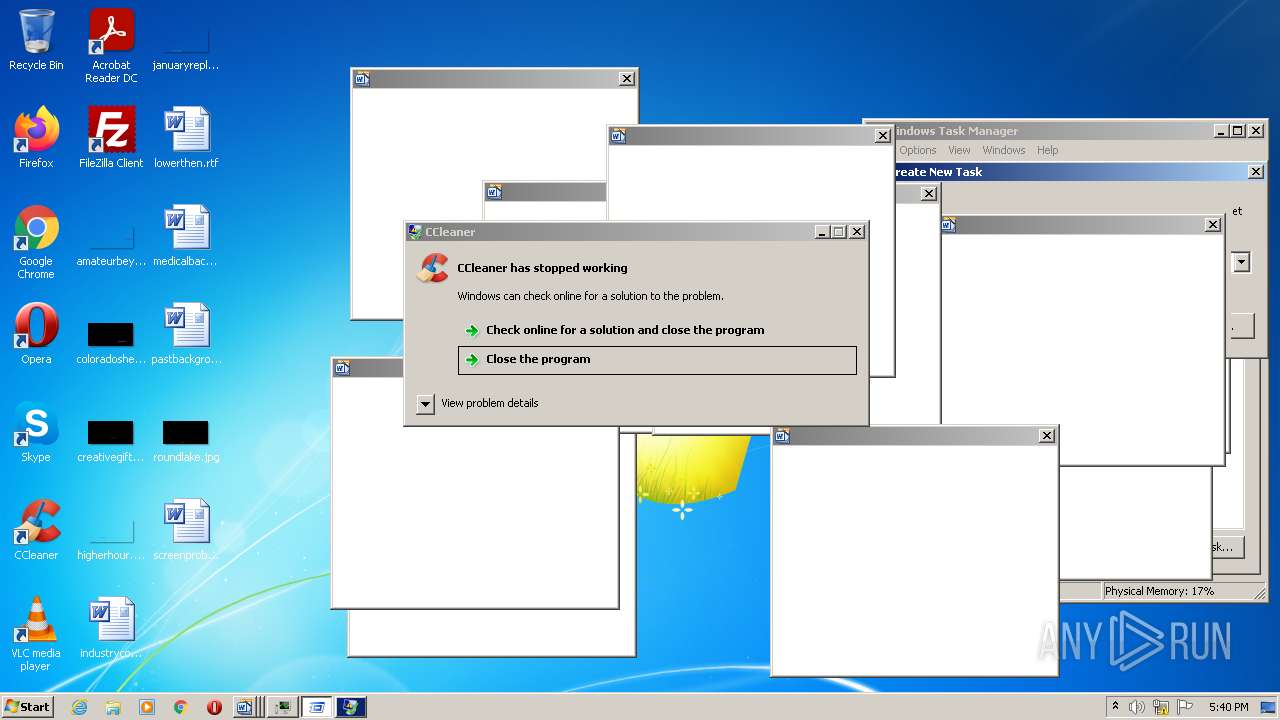
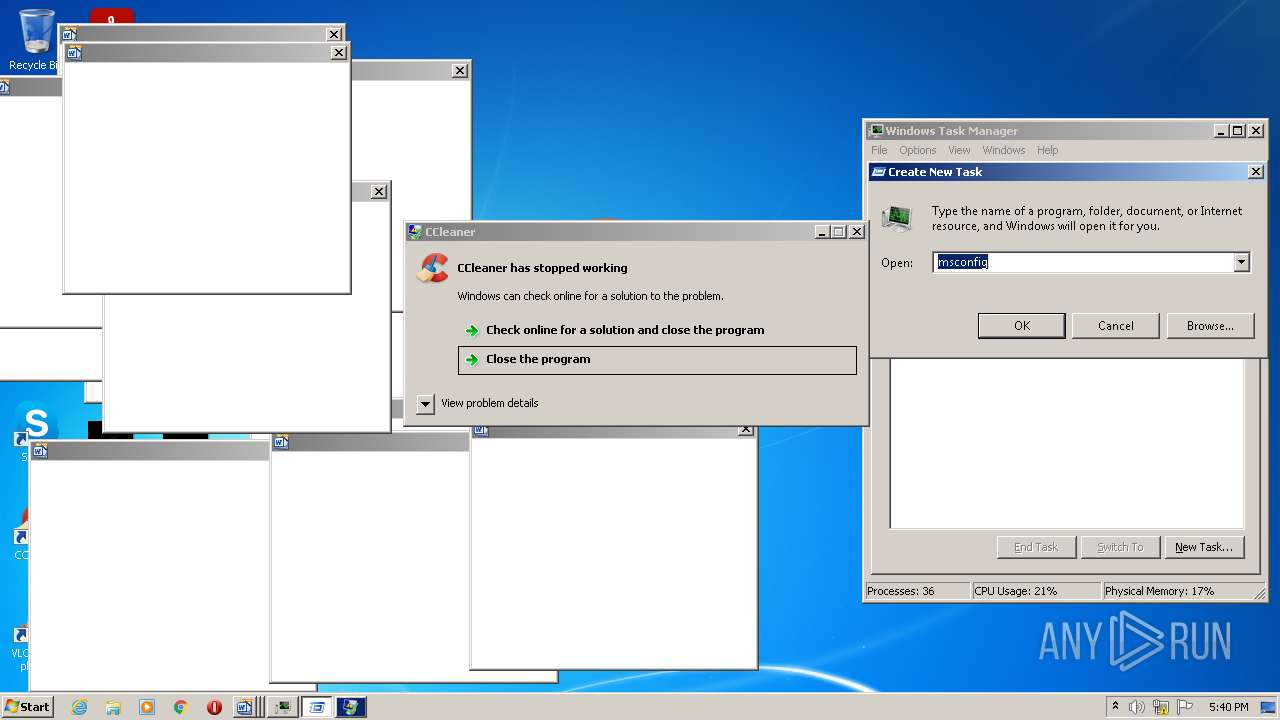
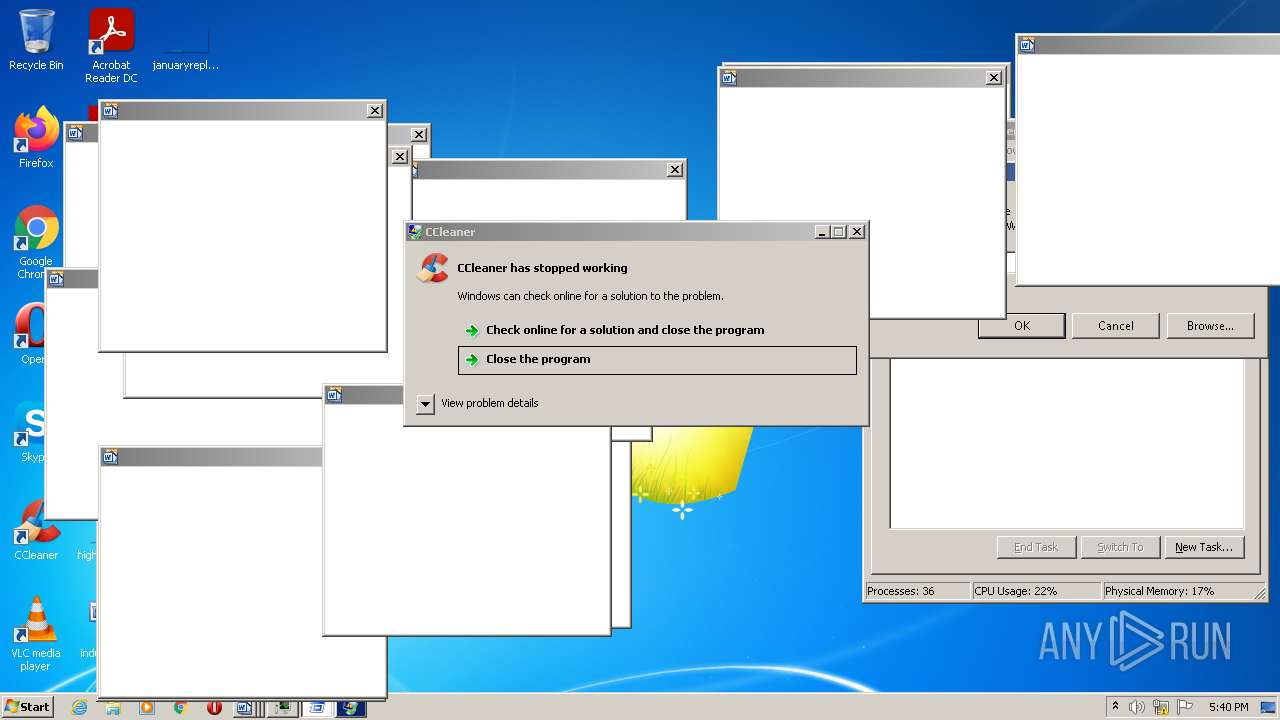
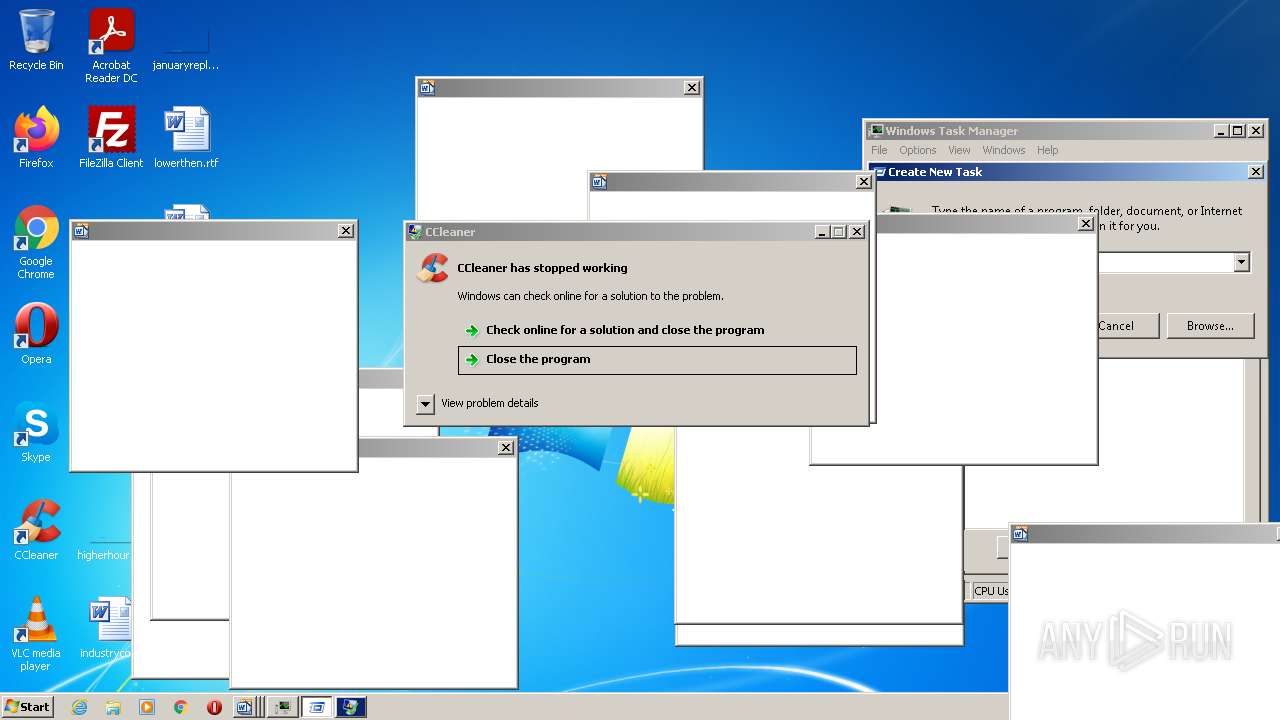
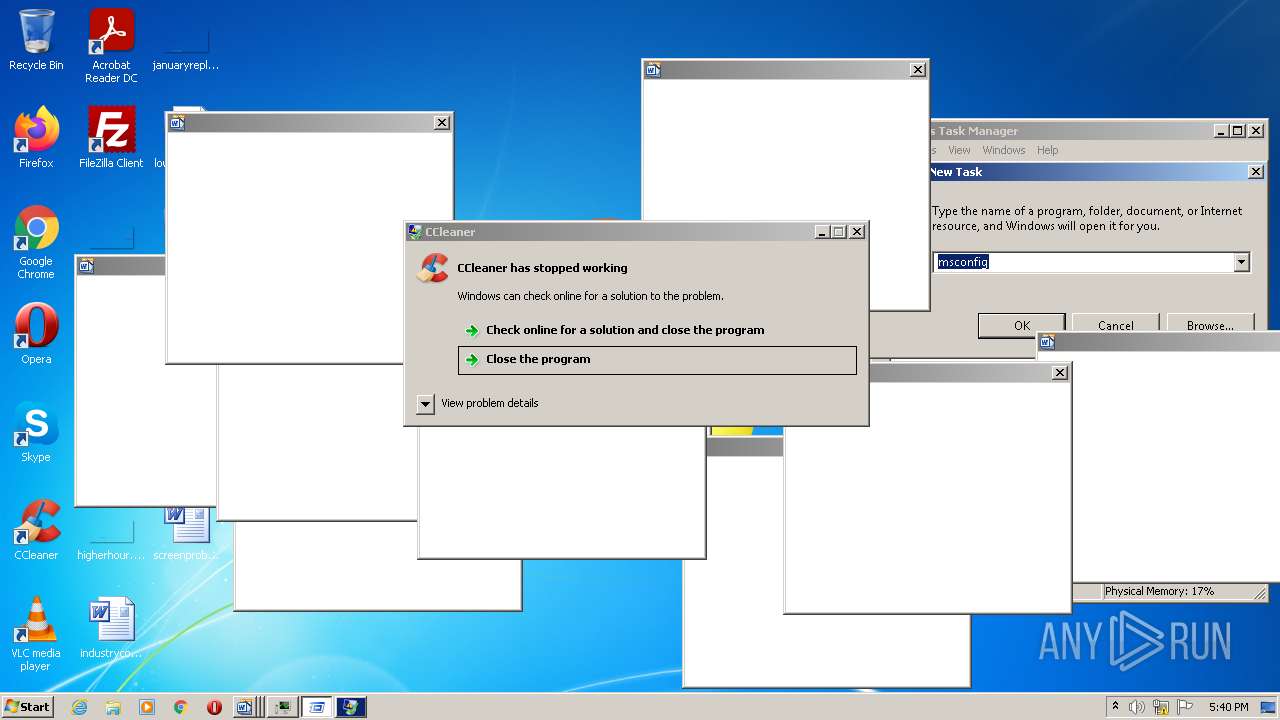
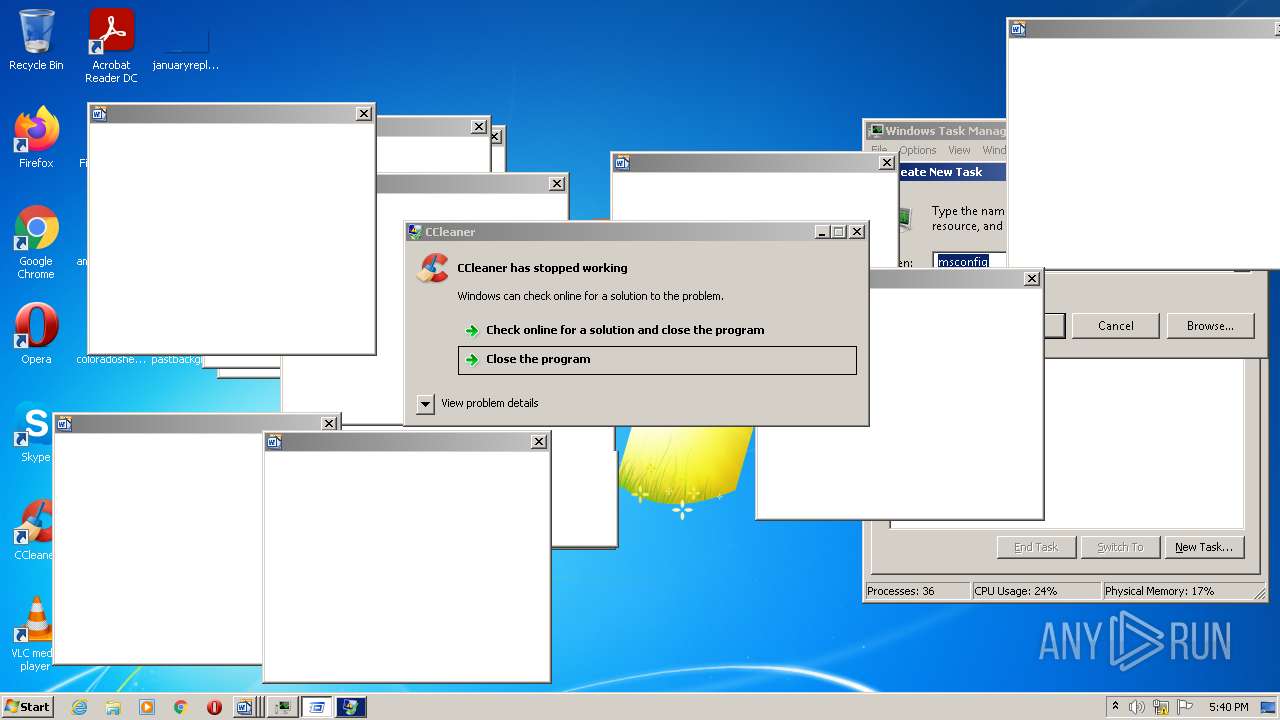
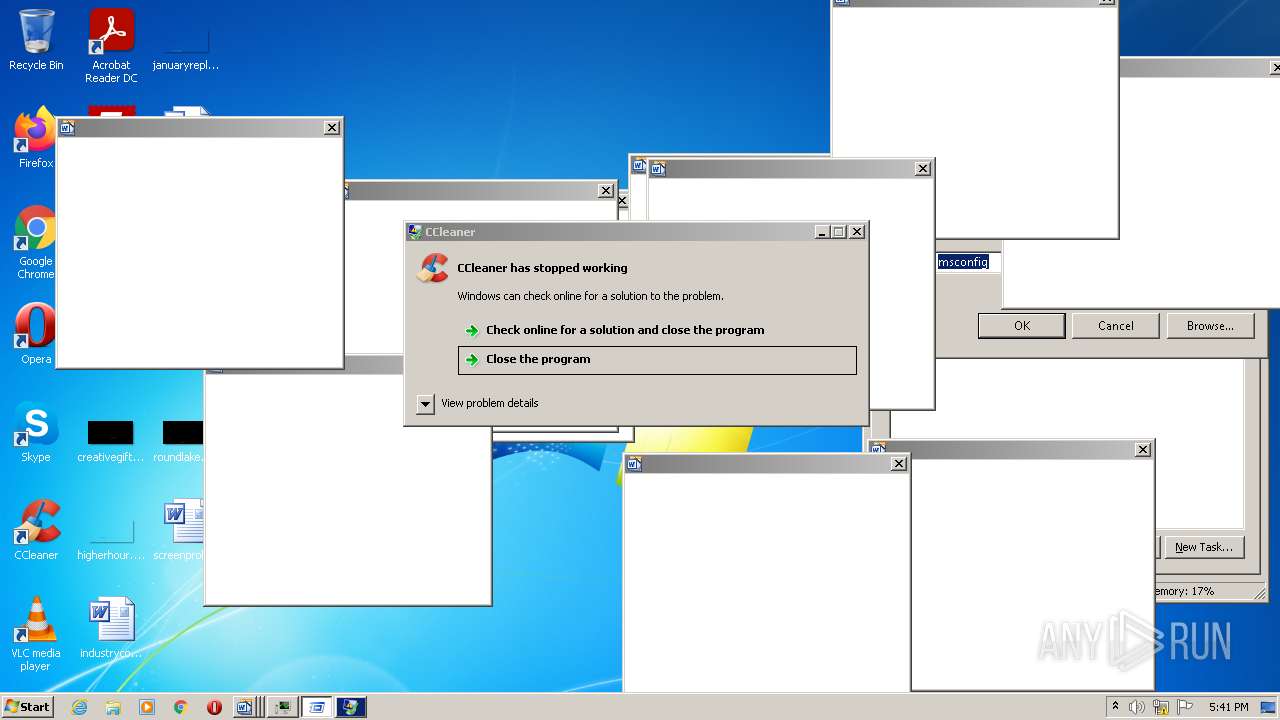
Manual execution by user
- CCleaner.exe (PID: 1700)
- CCleaner.exe (PID: 1304)
- taskmgr.exe (PID: 3568)
Reads settings of System Certificates
- YouAreAnIdiot.exe (PID: 2028)
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
Reads the hosts file
- CCleaner.exe (PID: 3976)
- CCleaner.exe (PID: 2360)
Checks Windows Trust Settings
- CCleaner.exe (PID: 2360)
- CCleaner.exe (PID: 3976)
Checks supported languages
- taskhost.exe (PID: 3044)
- taskhost.exe (PID: 2612)
- taskmgr.exe (PID: 3568)
- taskhost.exe (PID: 1492)
- DllHost.exe (PID: 2380)
Reads the computer name
- taskhost.exe (PID: 3044)
- DllHost.exe (PID: 2380)
- taskhost.exe (PID: 2612)
- taskmgr.exe (PID: 3568)
- taskhost.exe (PID: 1492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | AxInterop.ShockwaveFlashObjects.dll |
|---|---|
| ZipUncompressedSize: | 17408 |
| ZipCompressedSize: | 6406 |
| ZipCRC: | 0x0e322587 |
| ZipModifyDate: | 2010:10:16 17:13:18 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
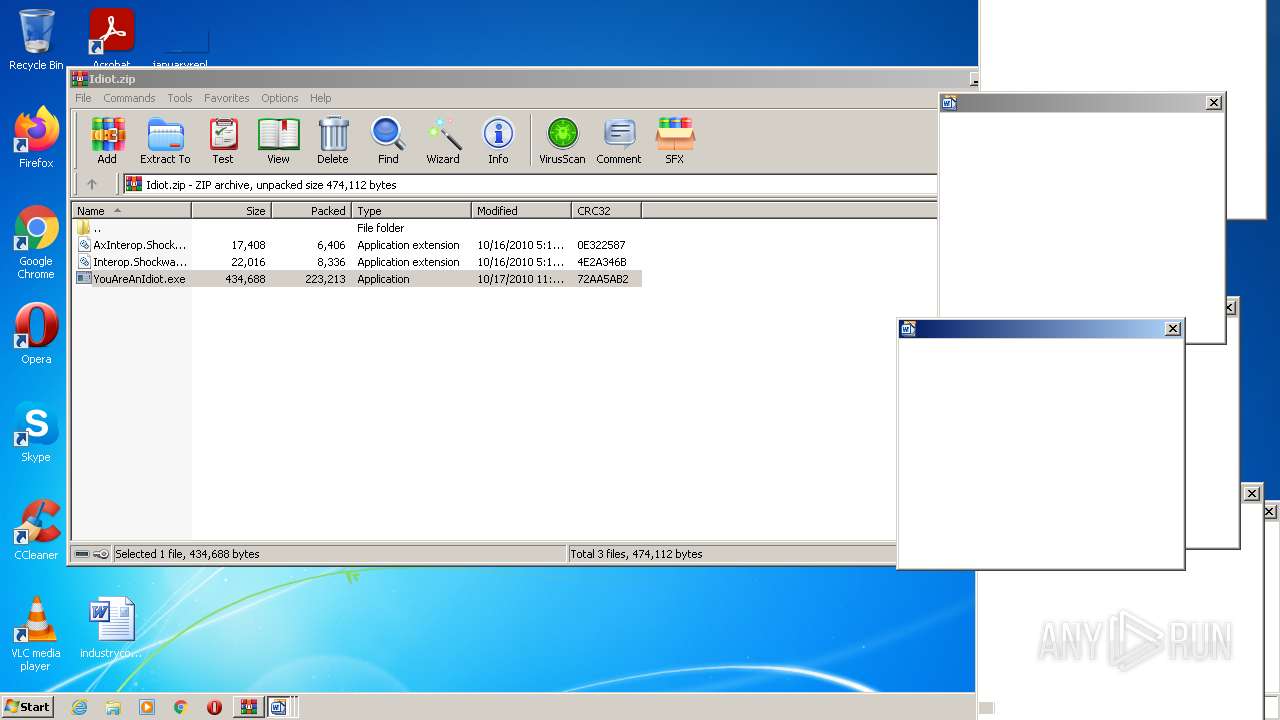
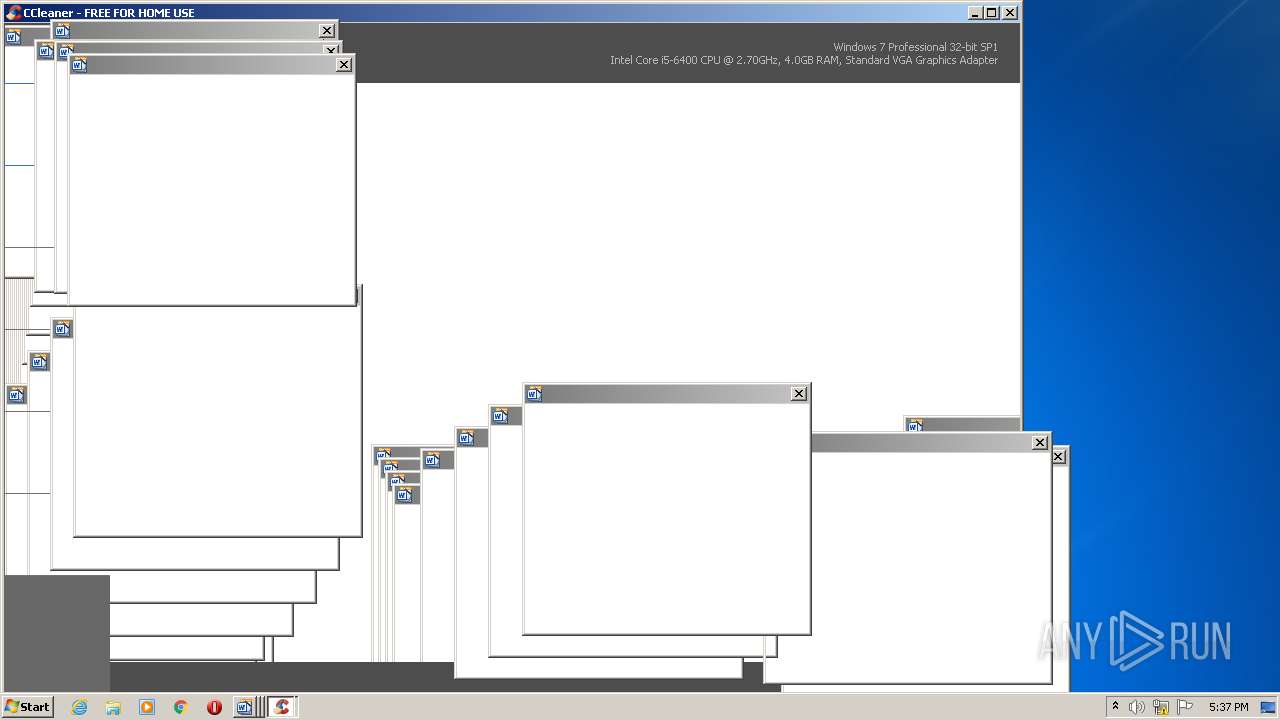
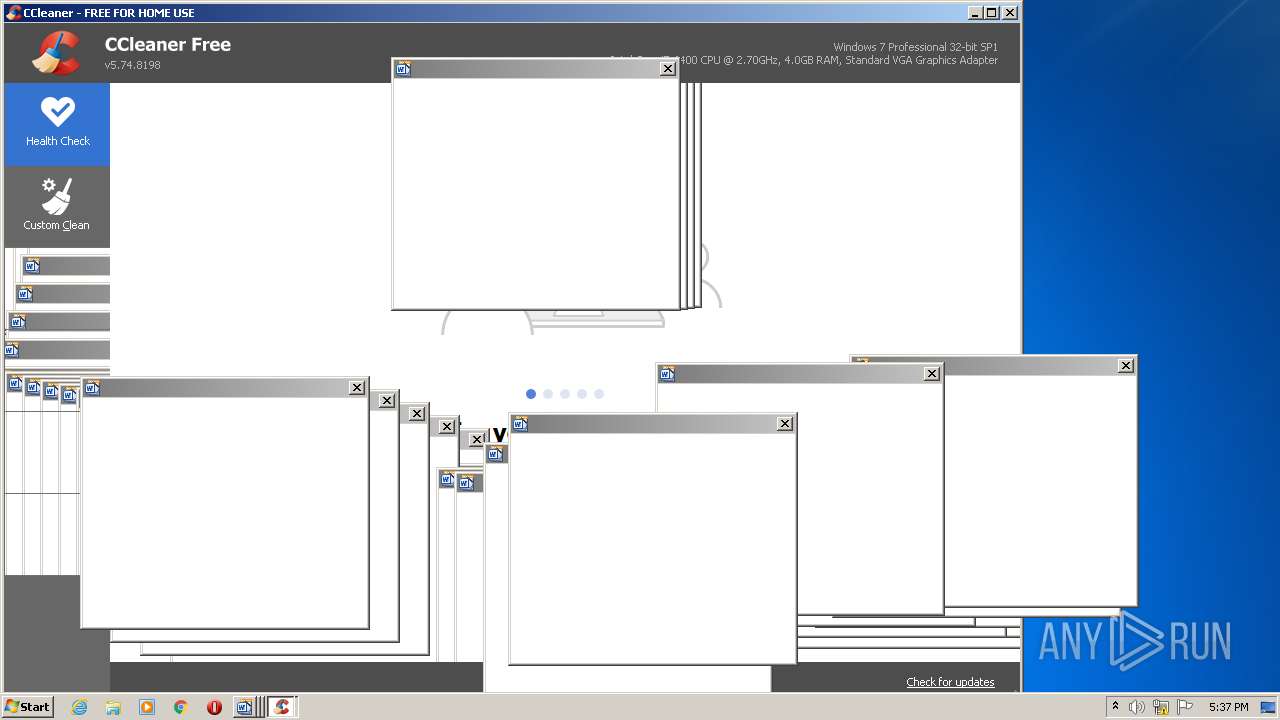
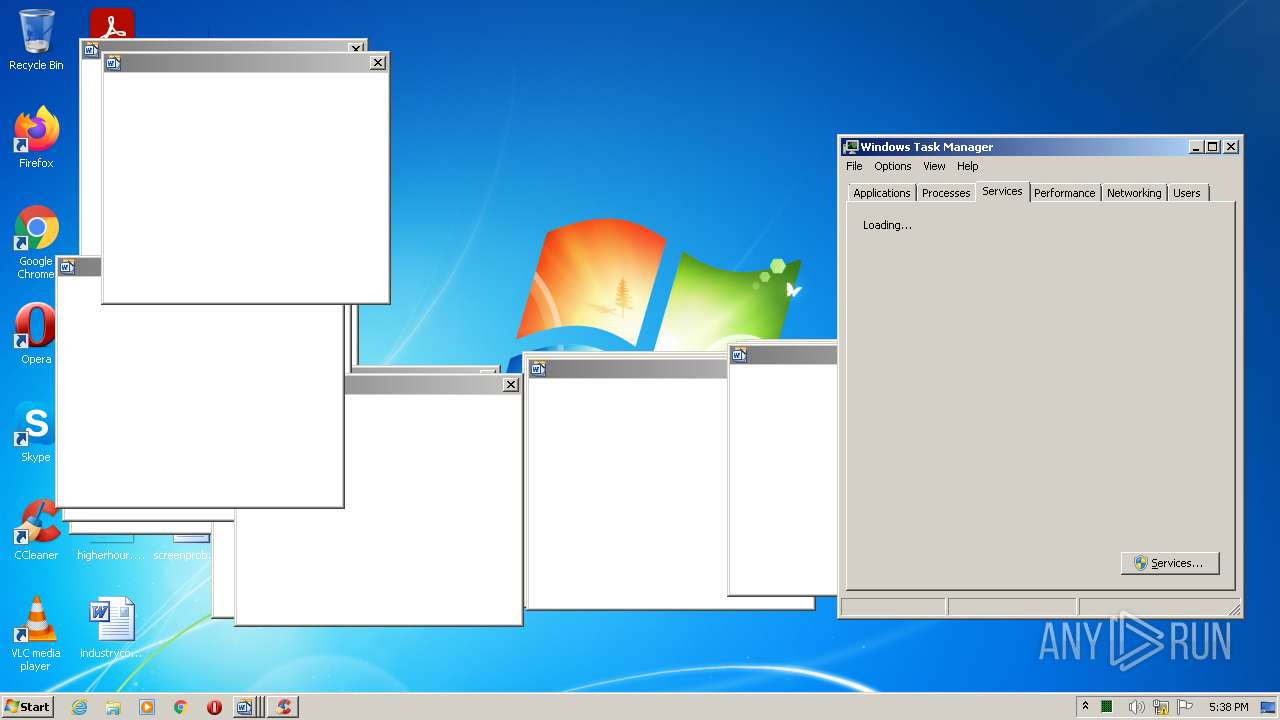
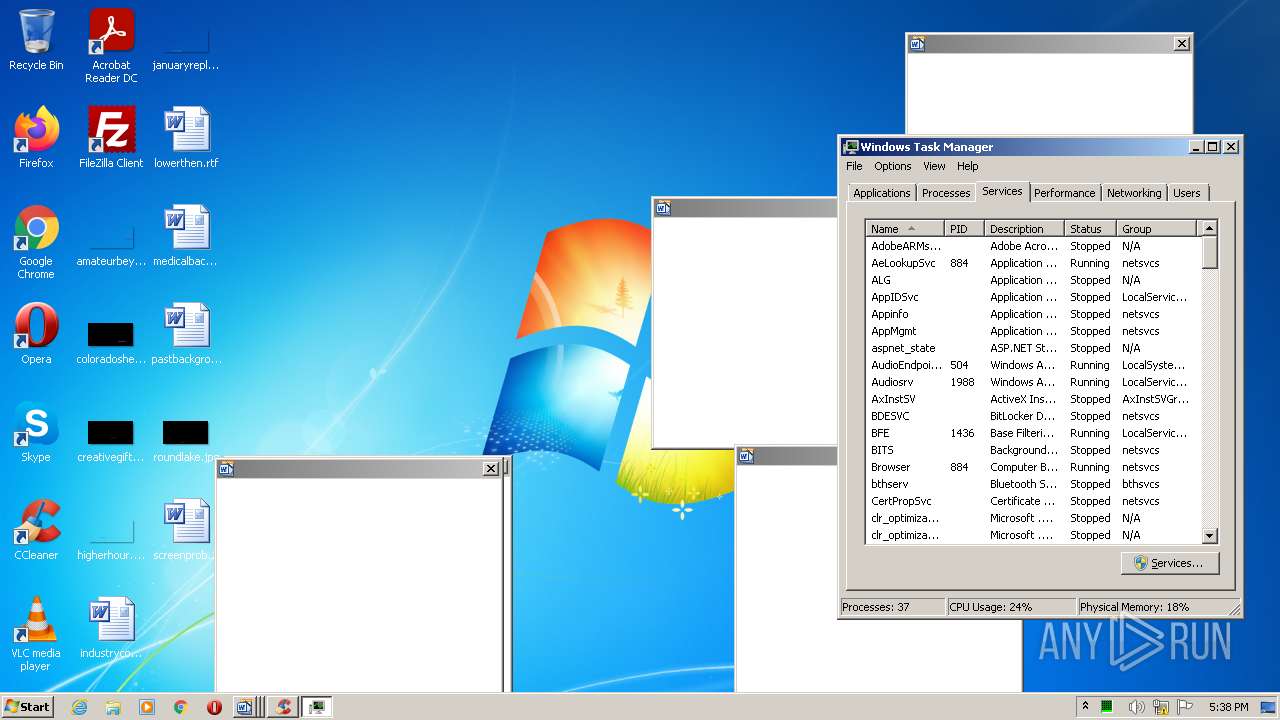
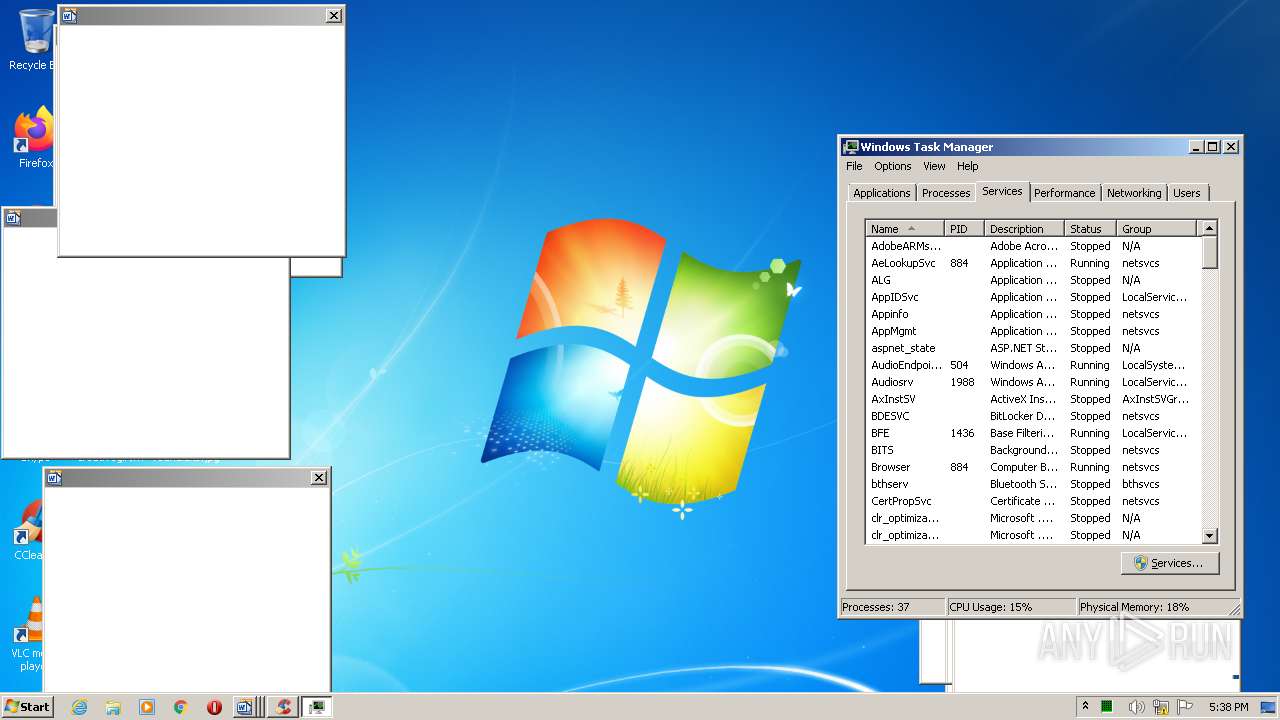
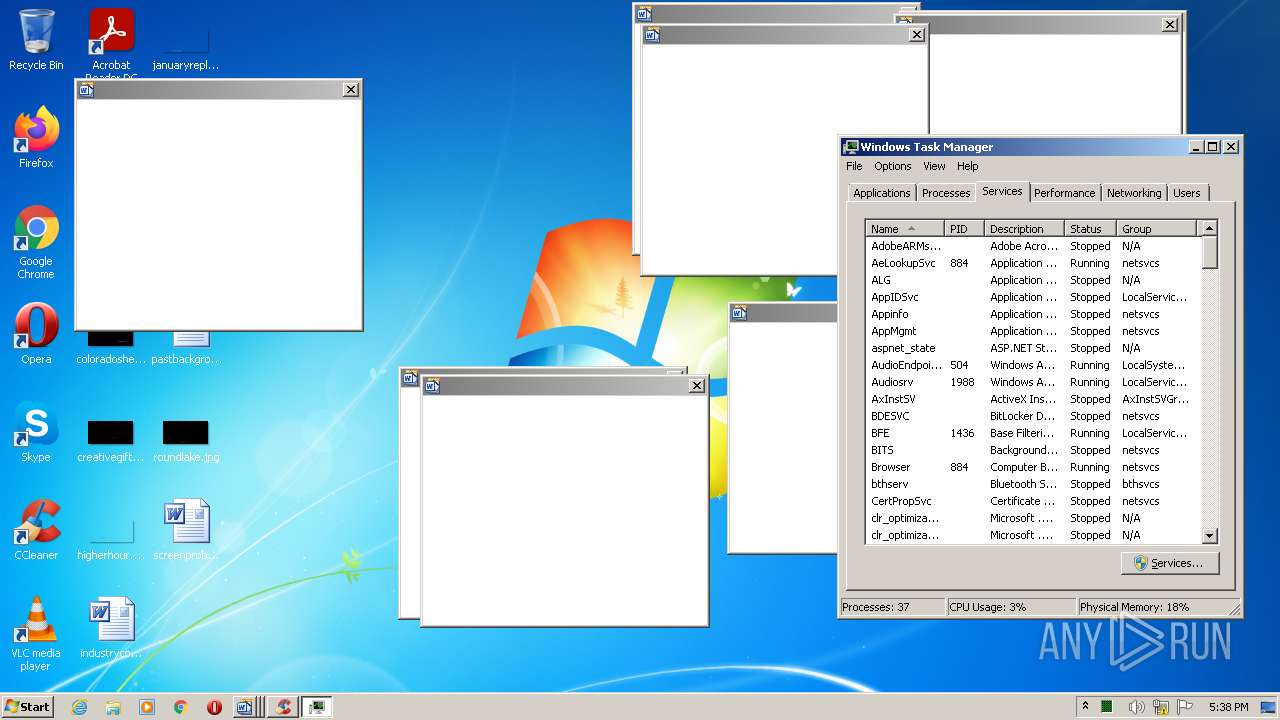
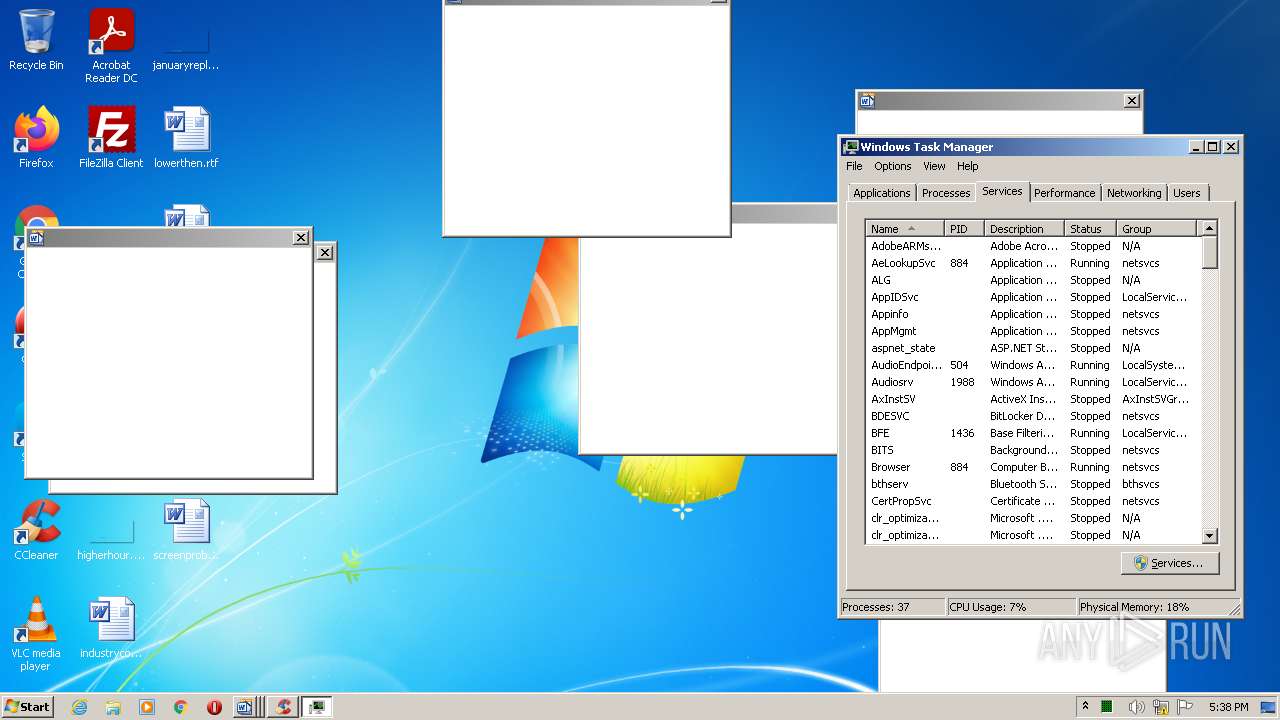
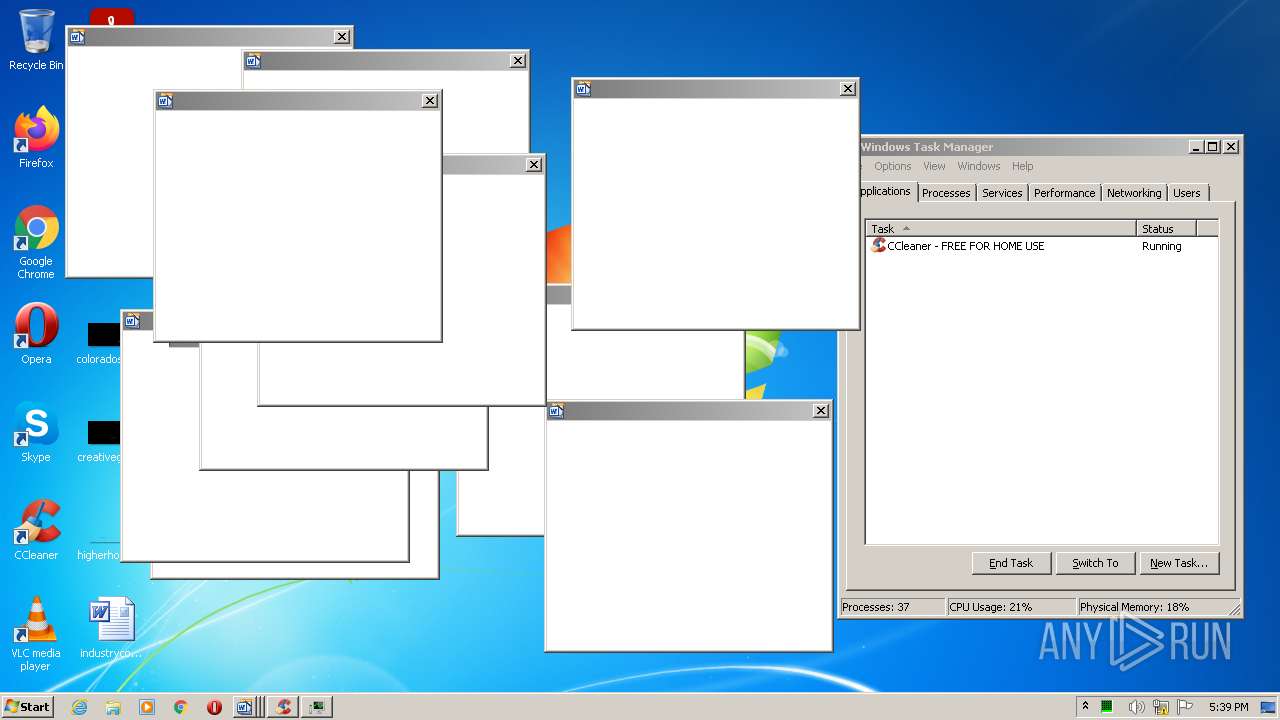
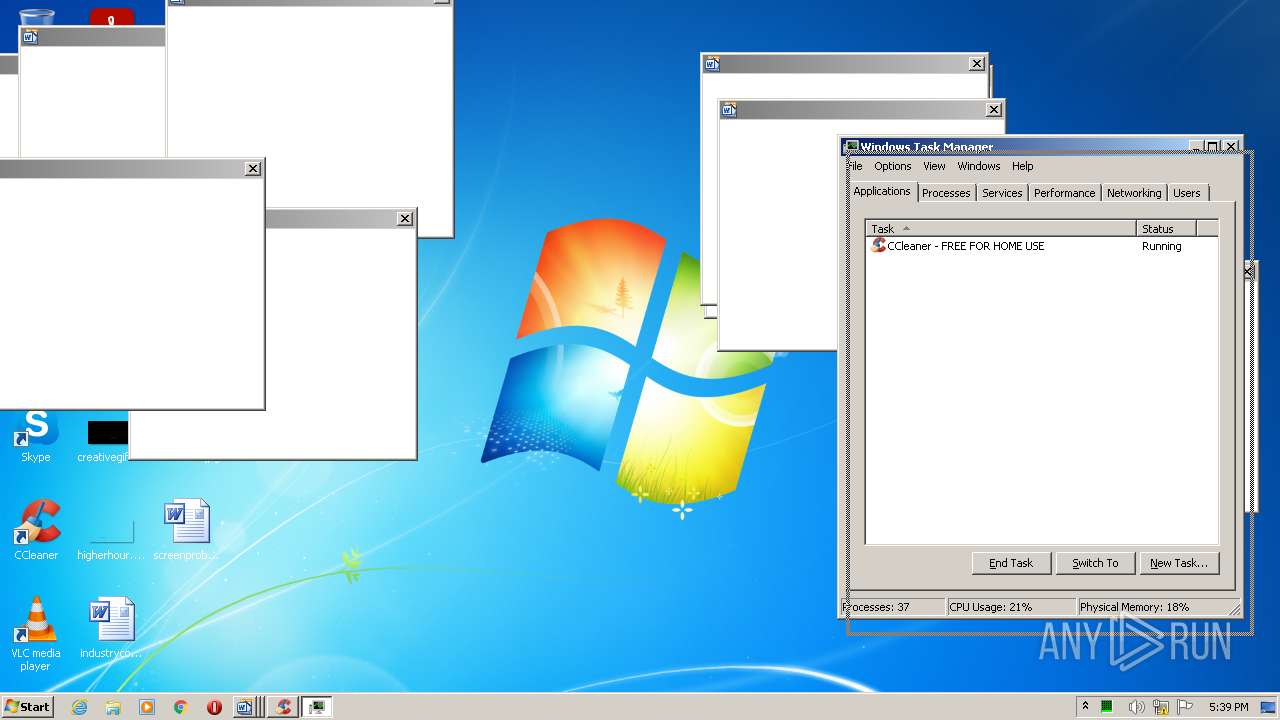
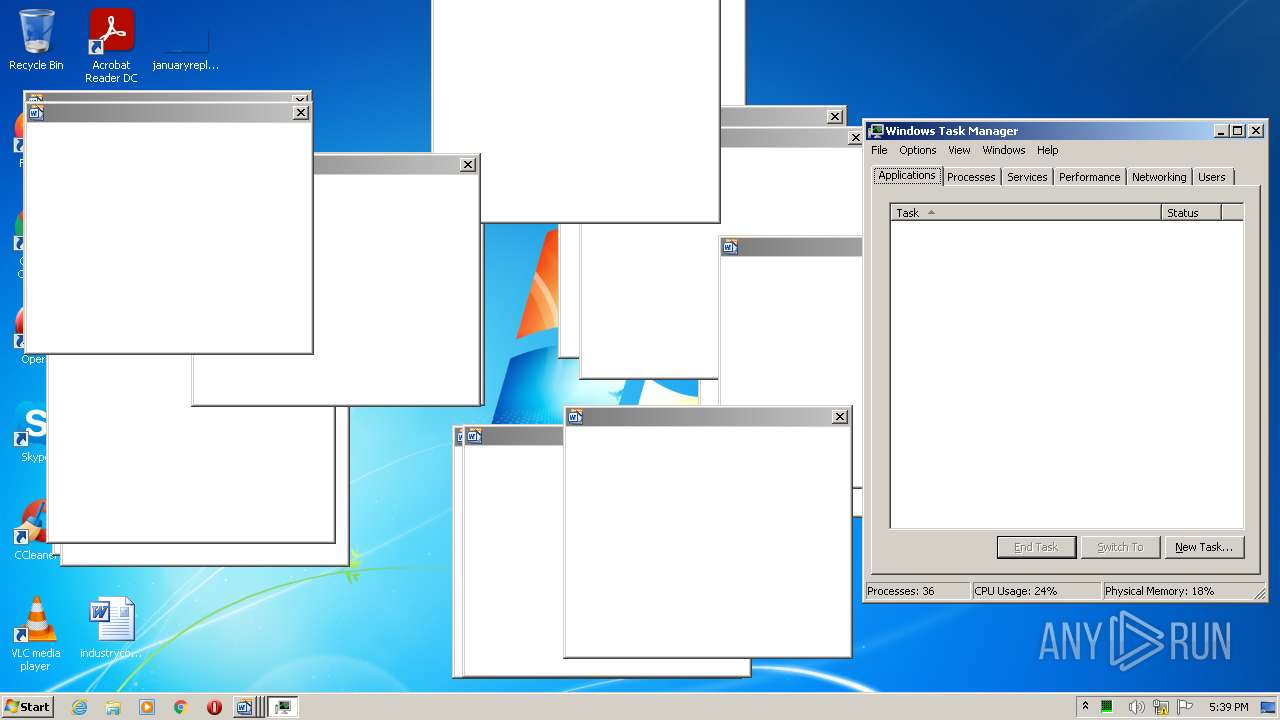
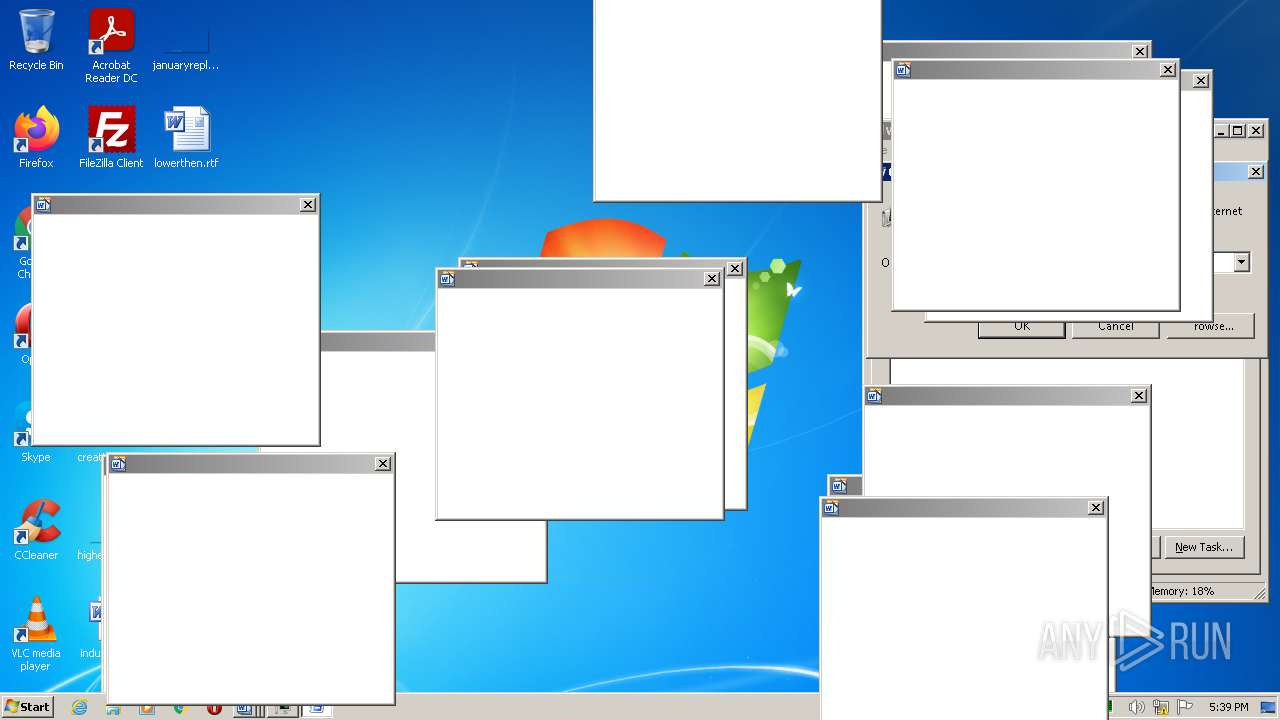
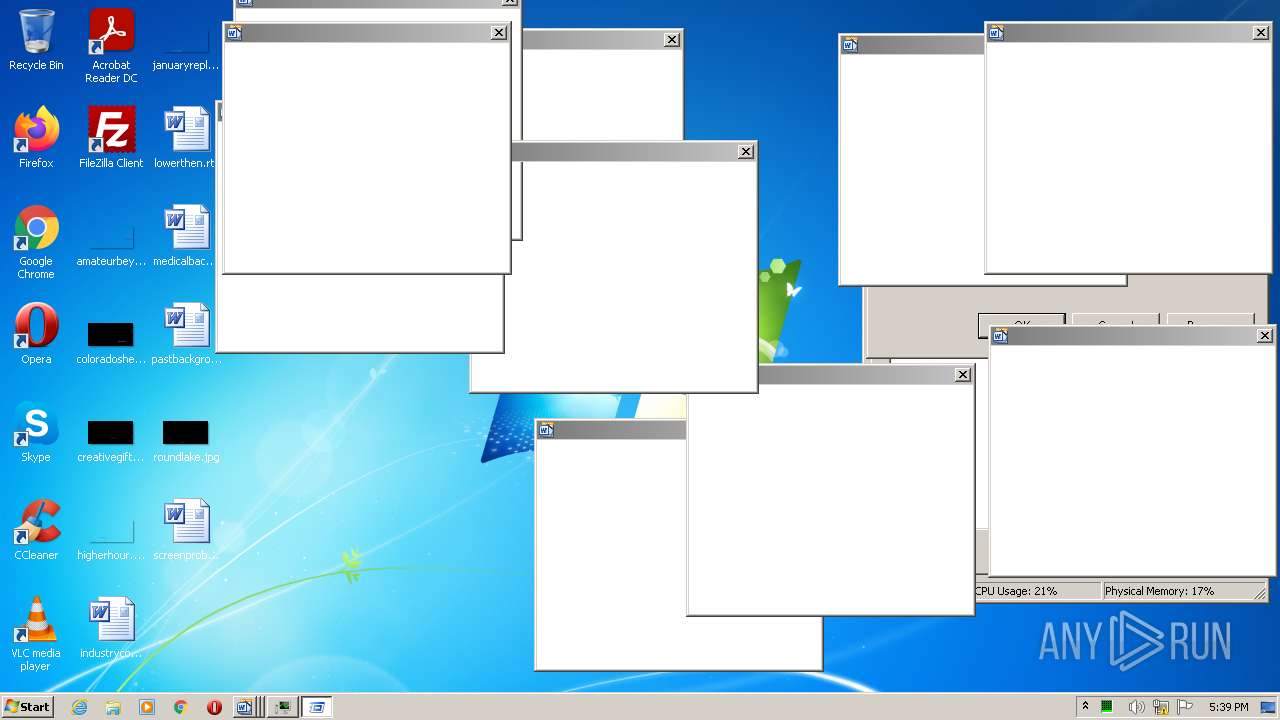
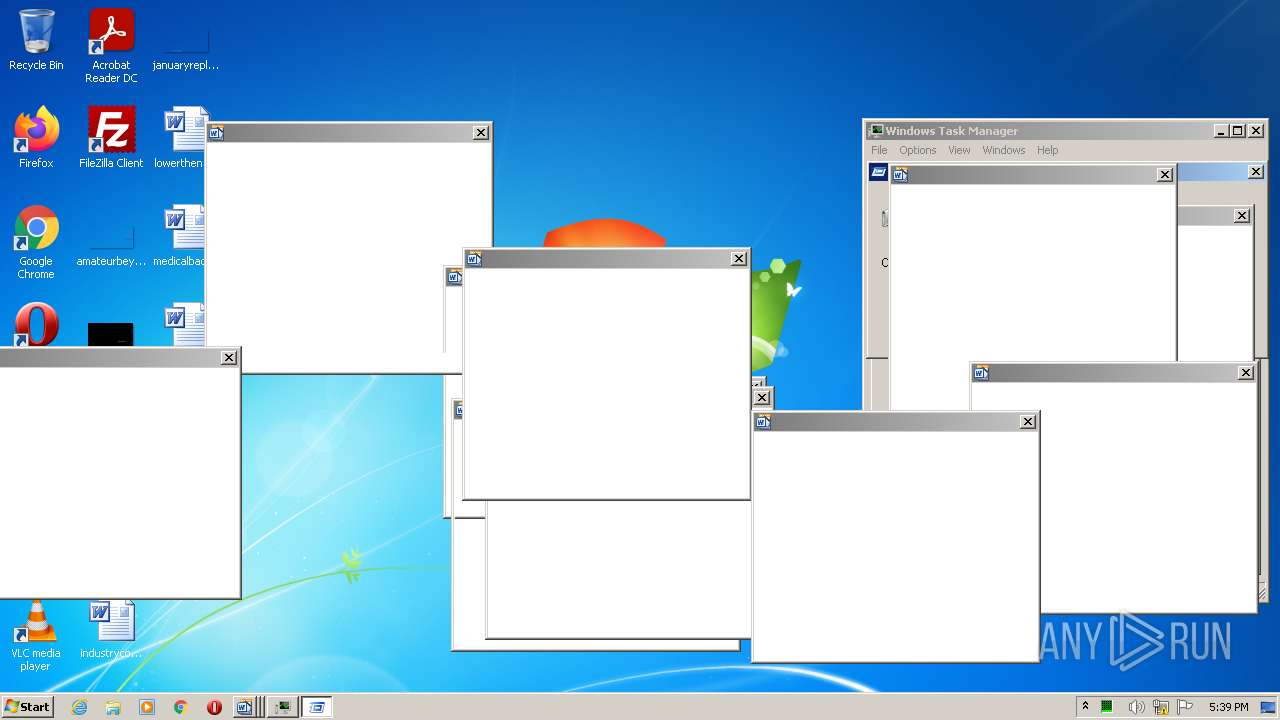
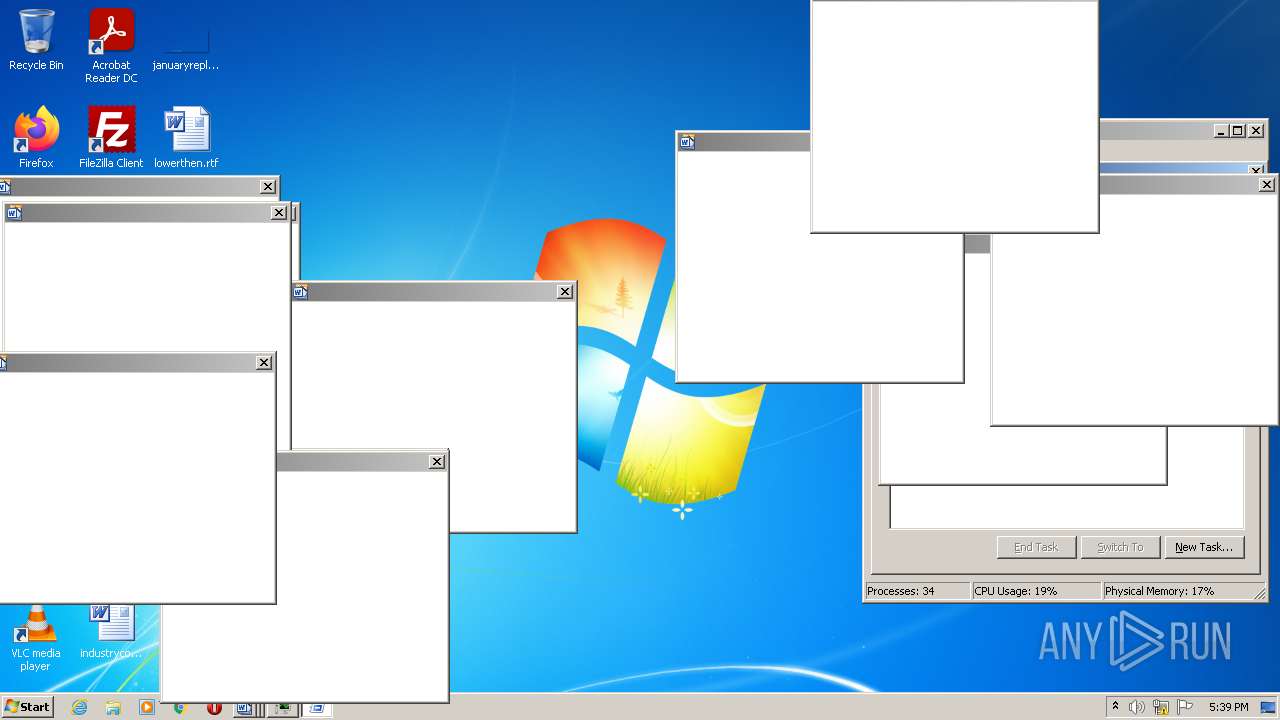
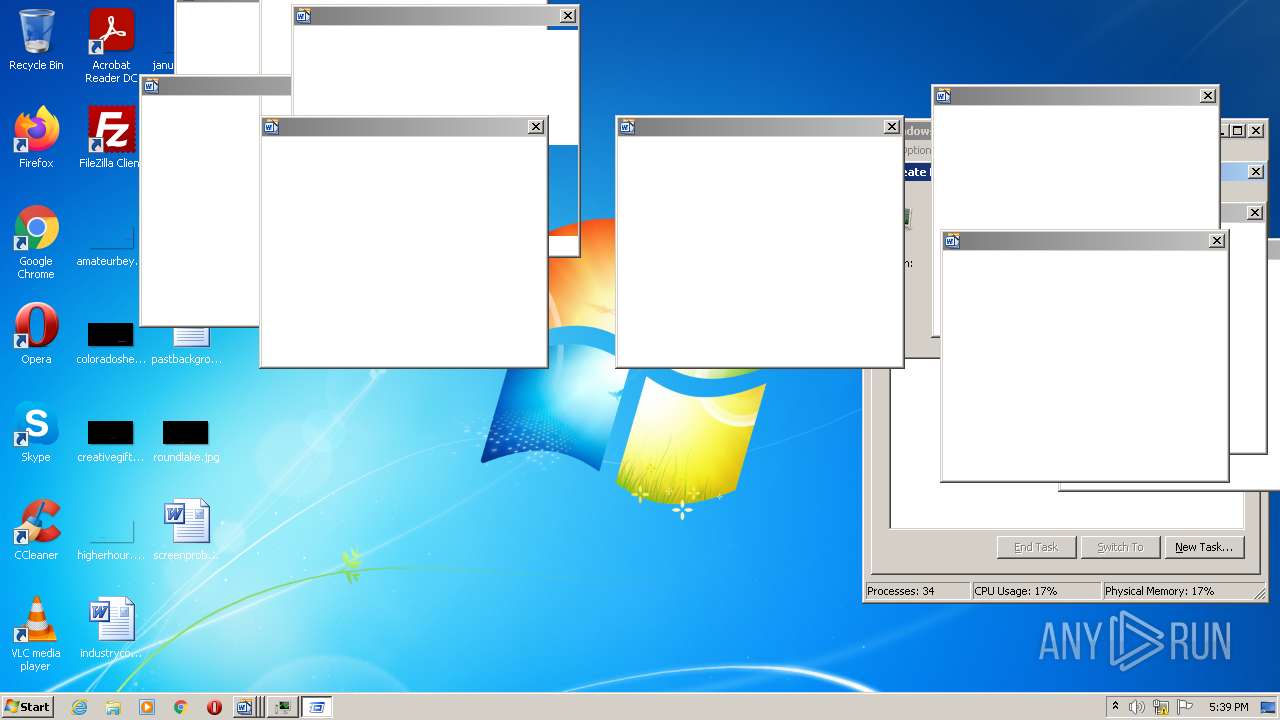
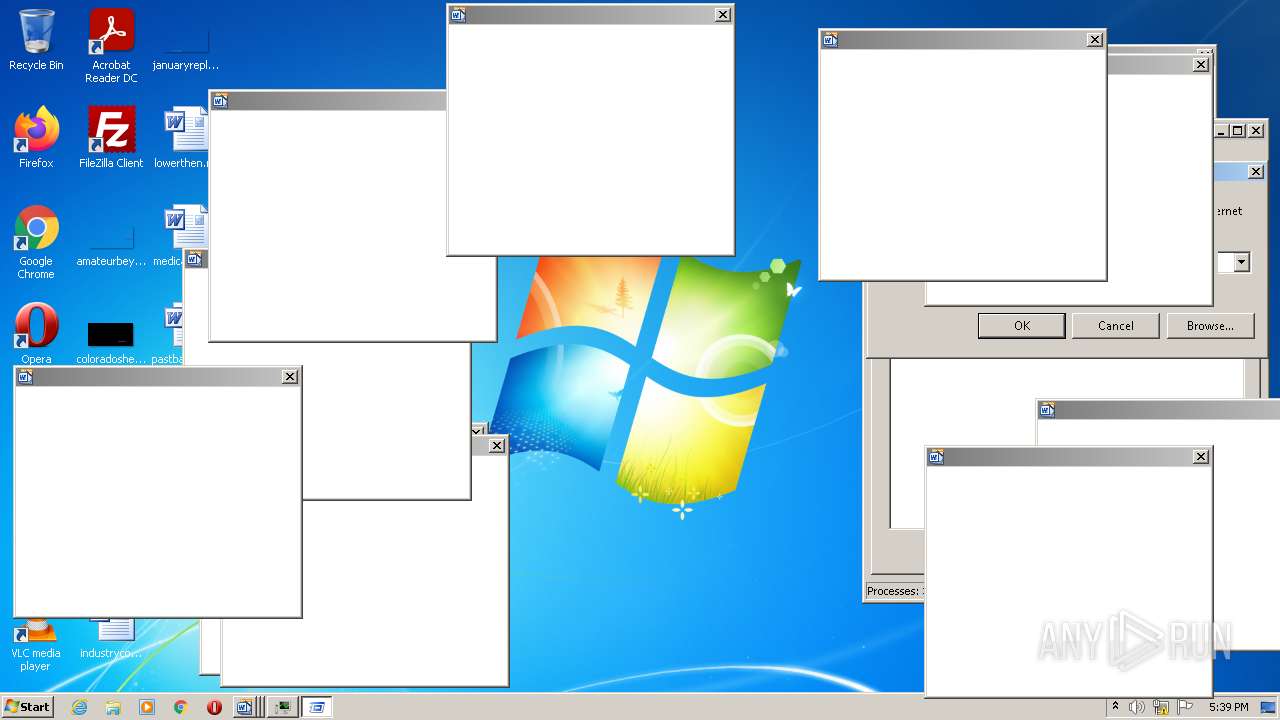
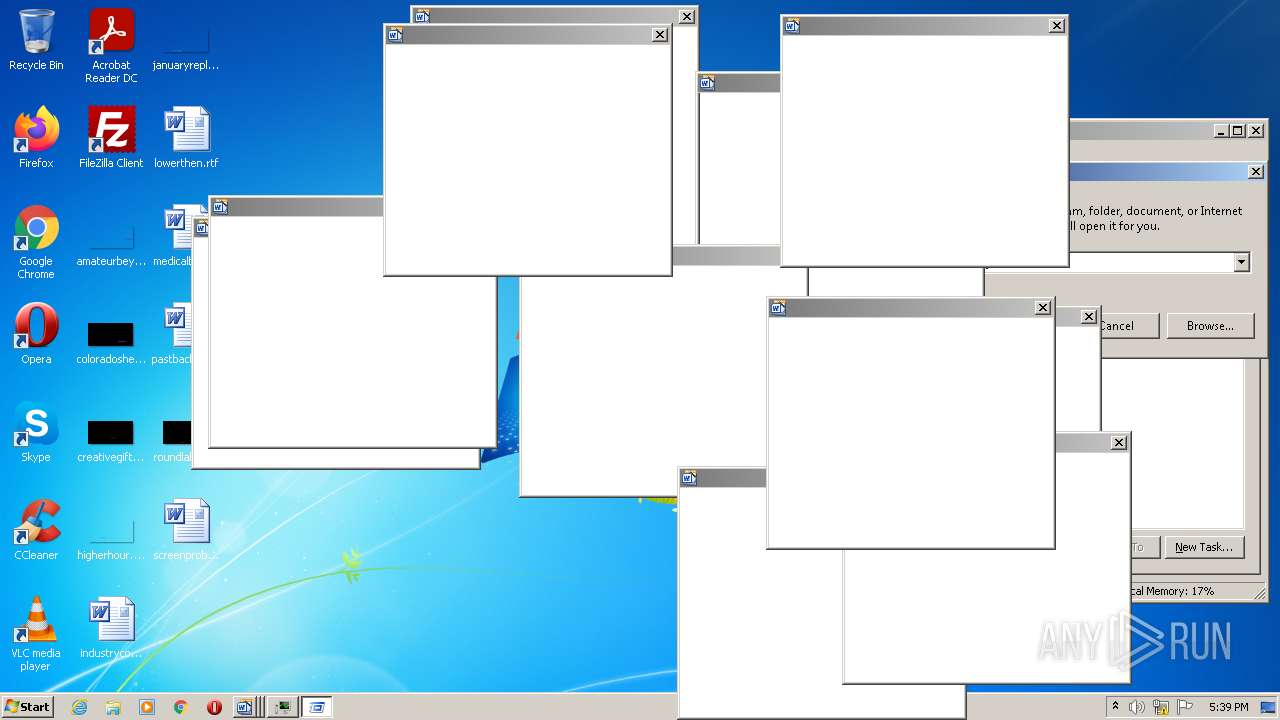
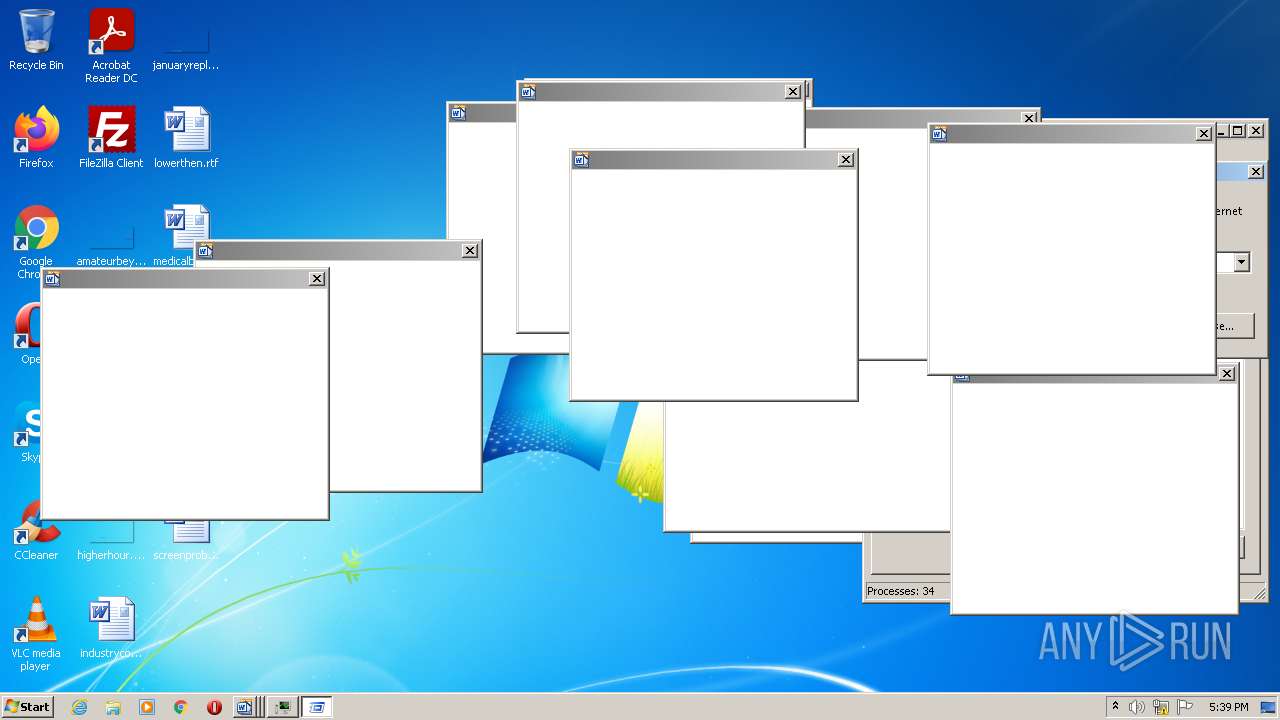
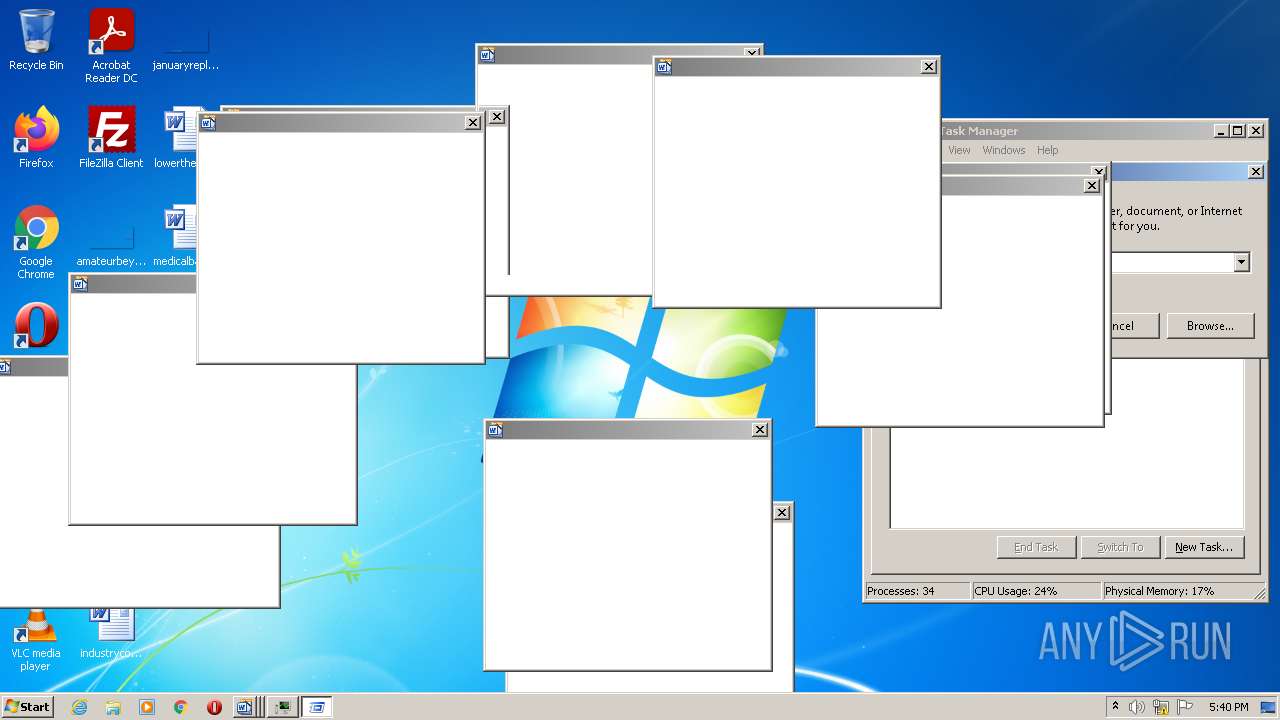
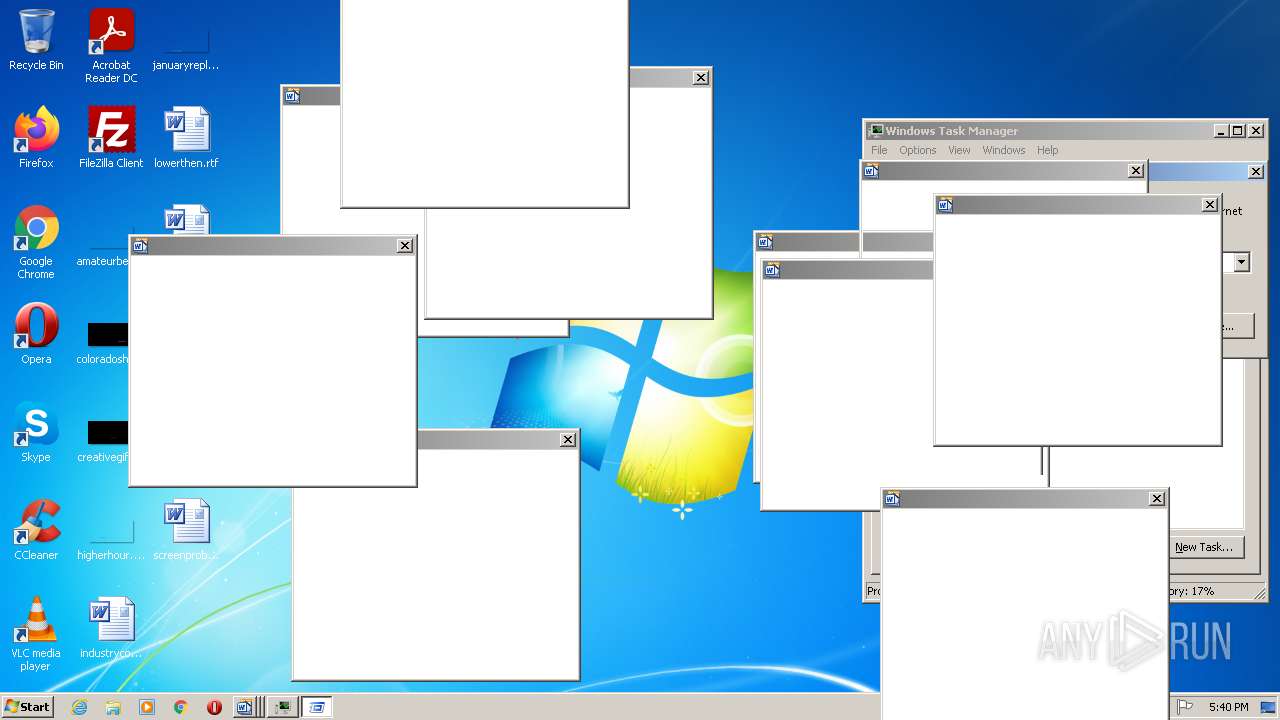
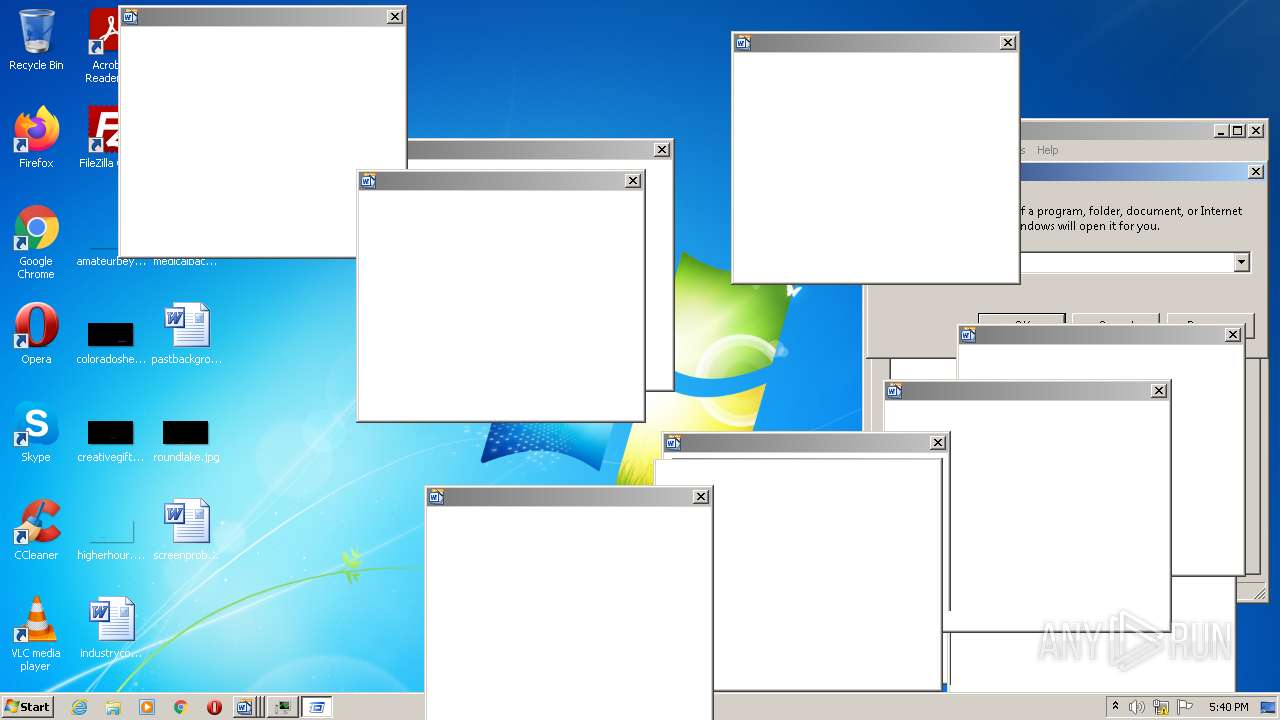
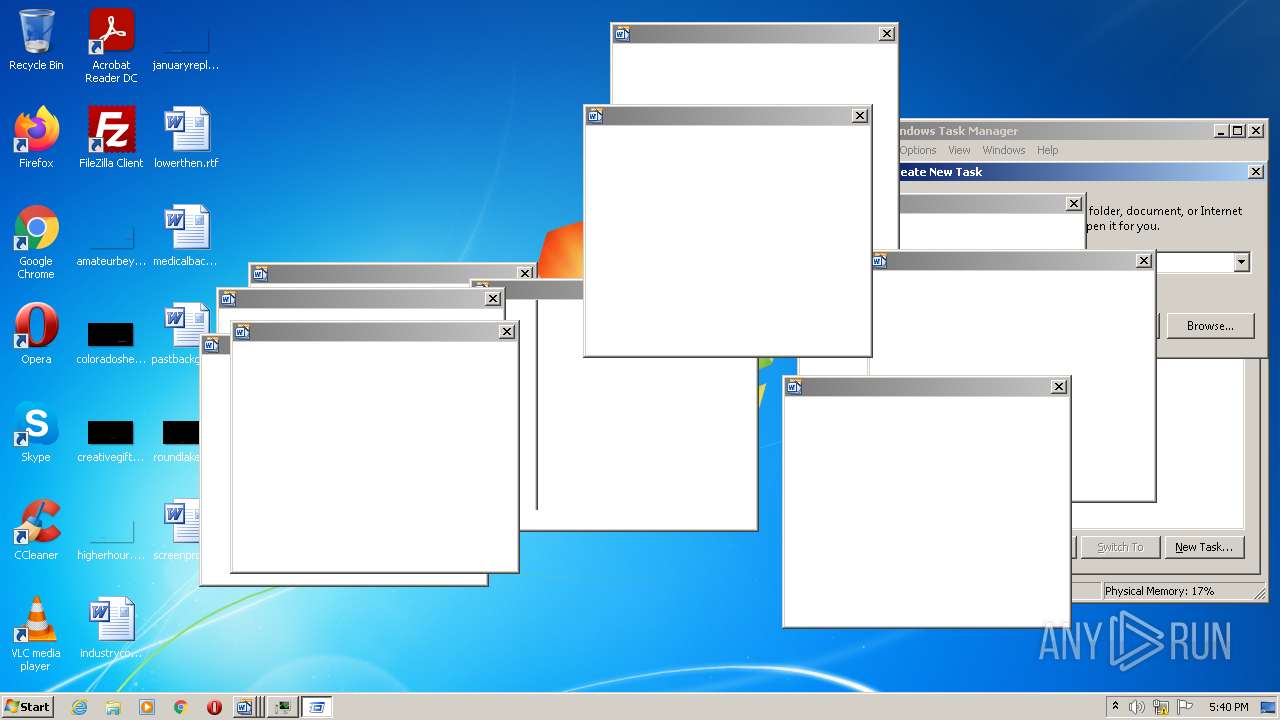
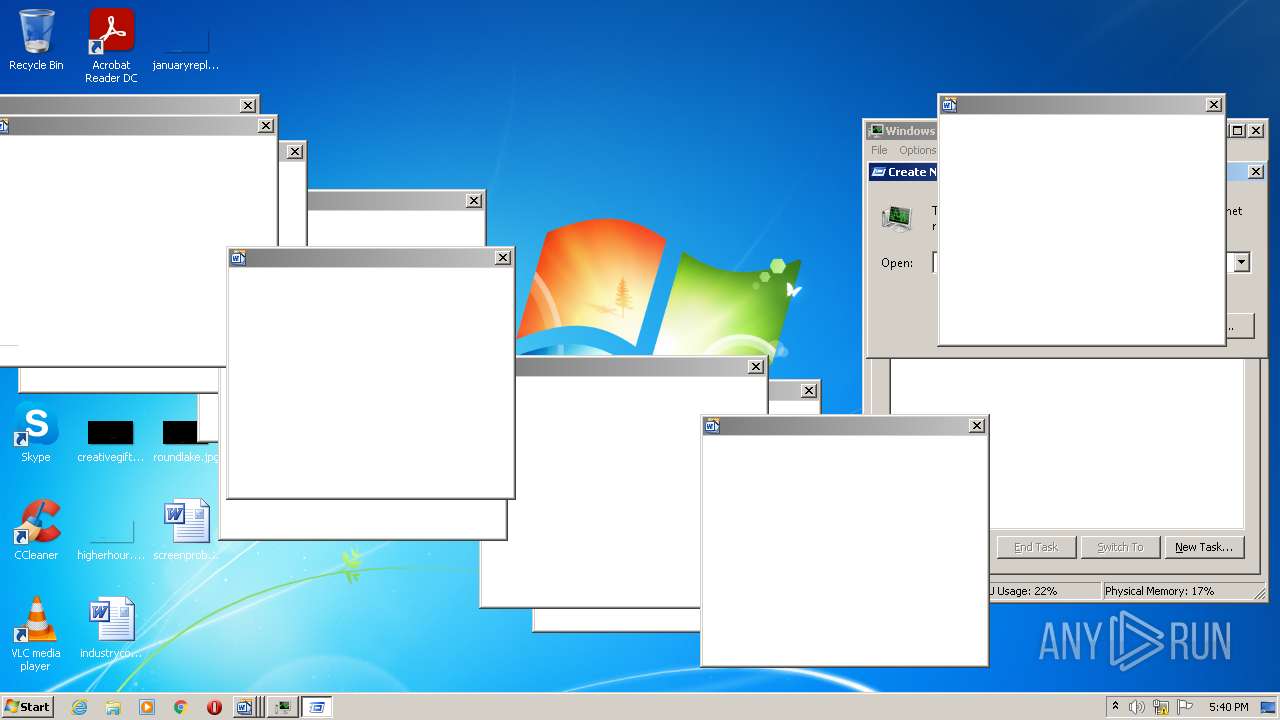
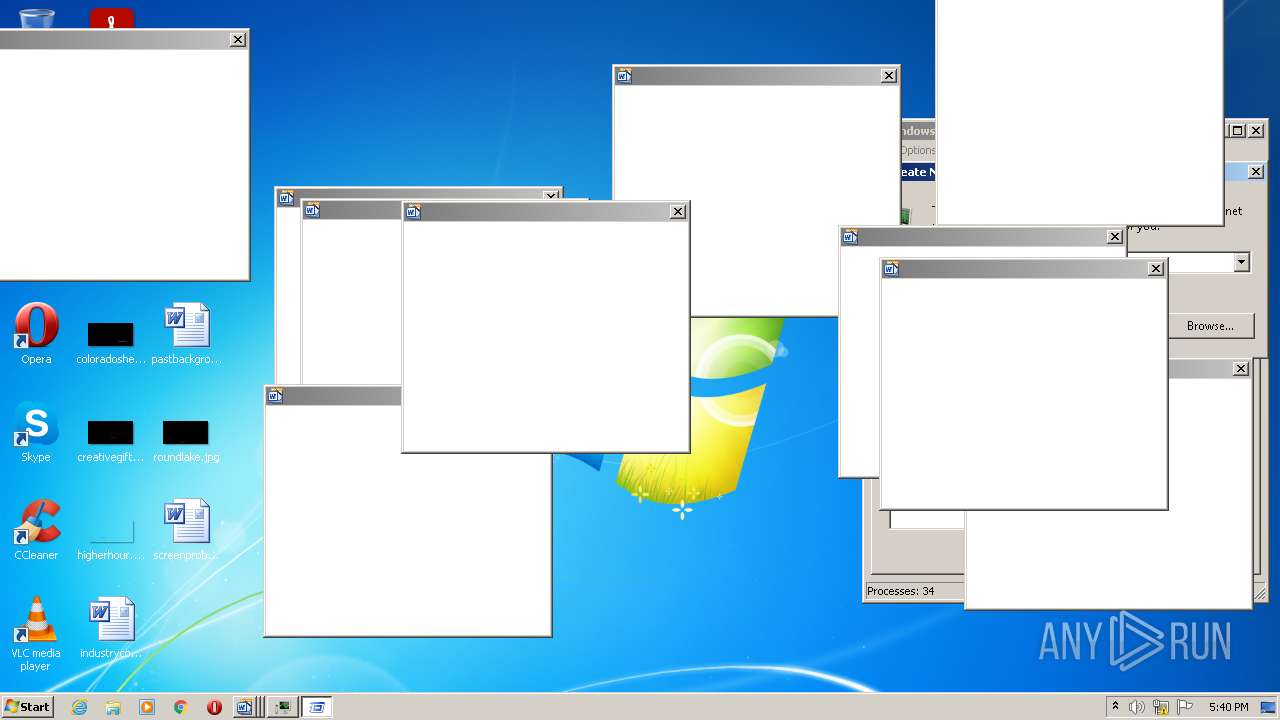
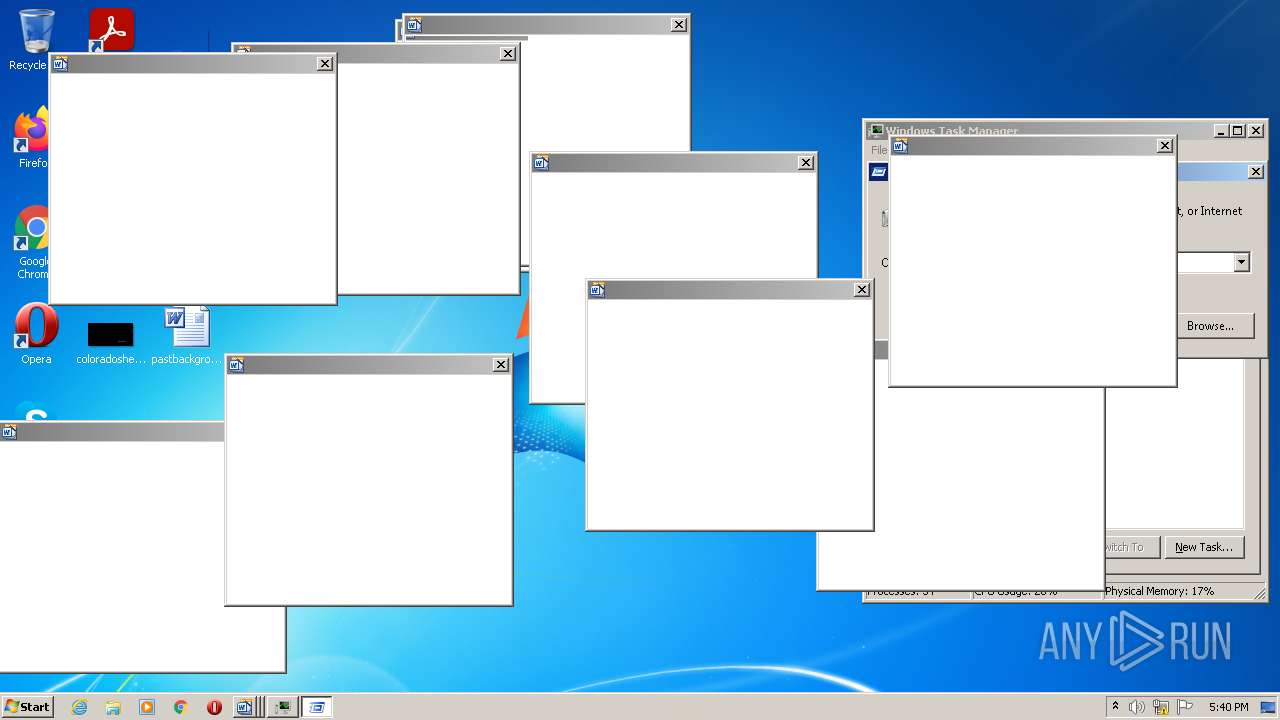
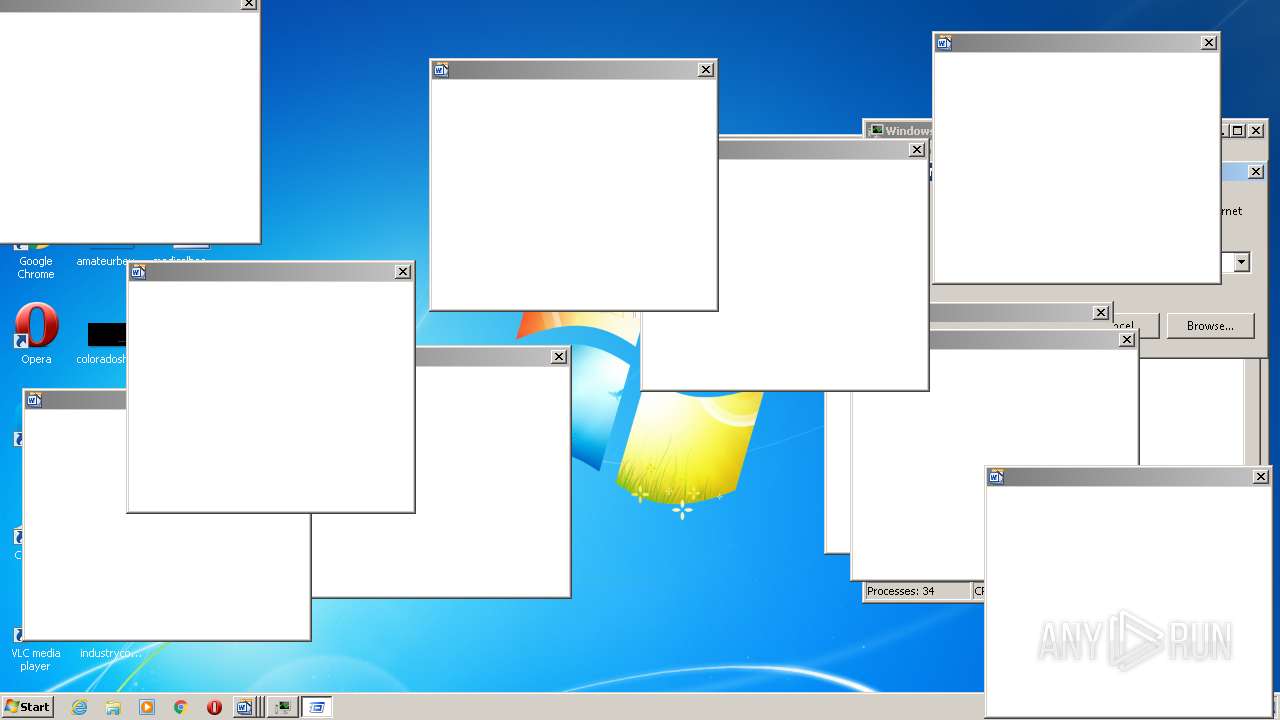
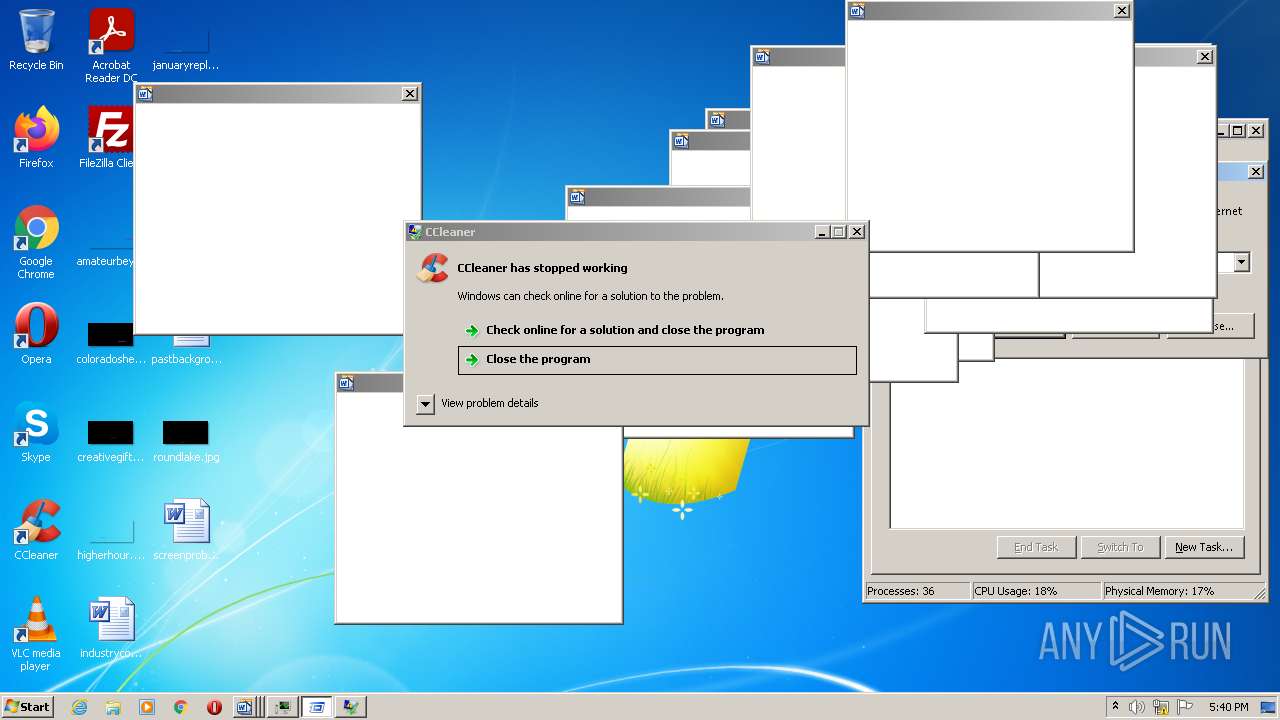
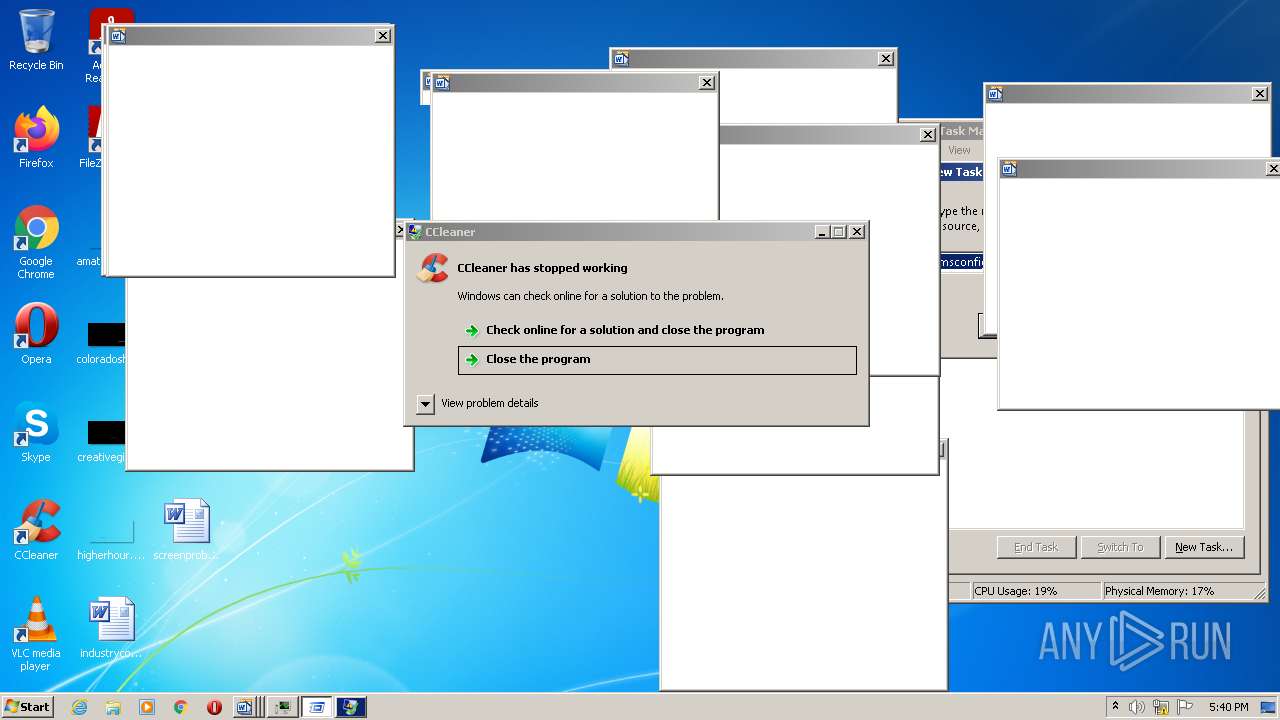
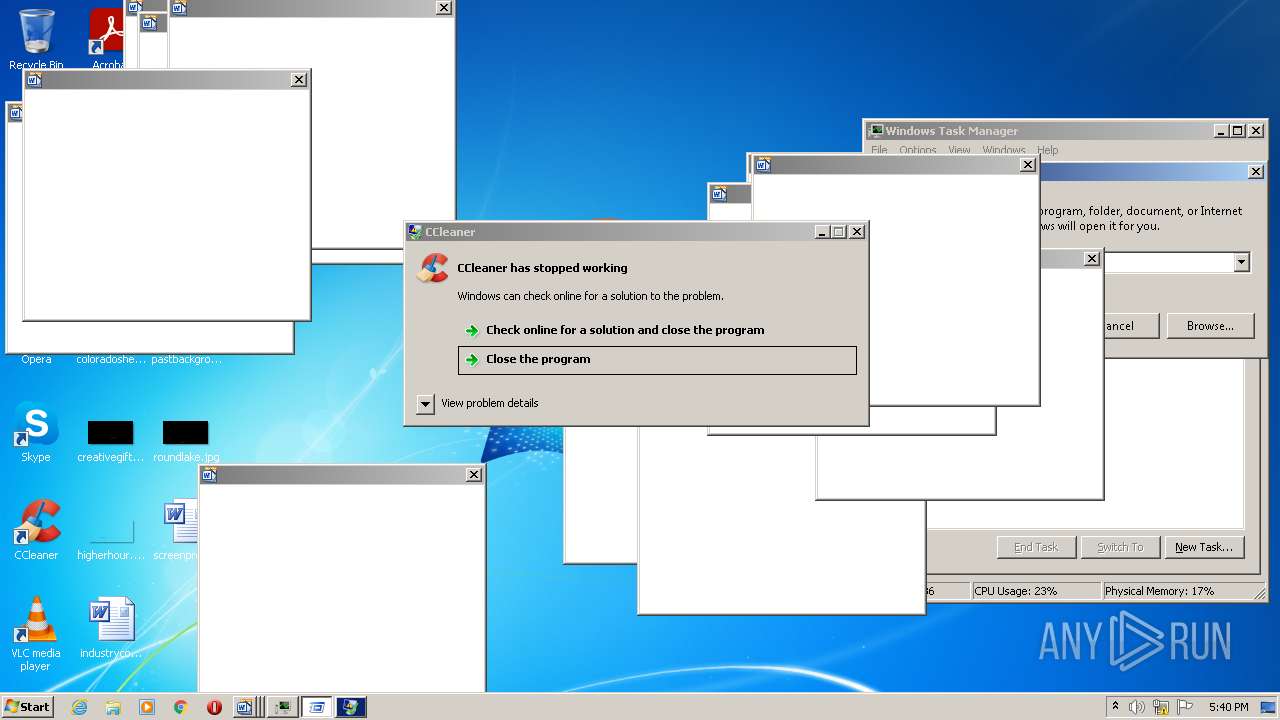
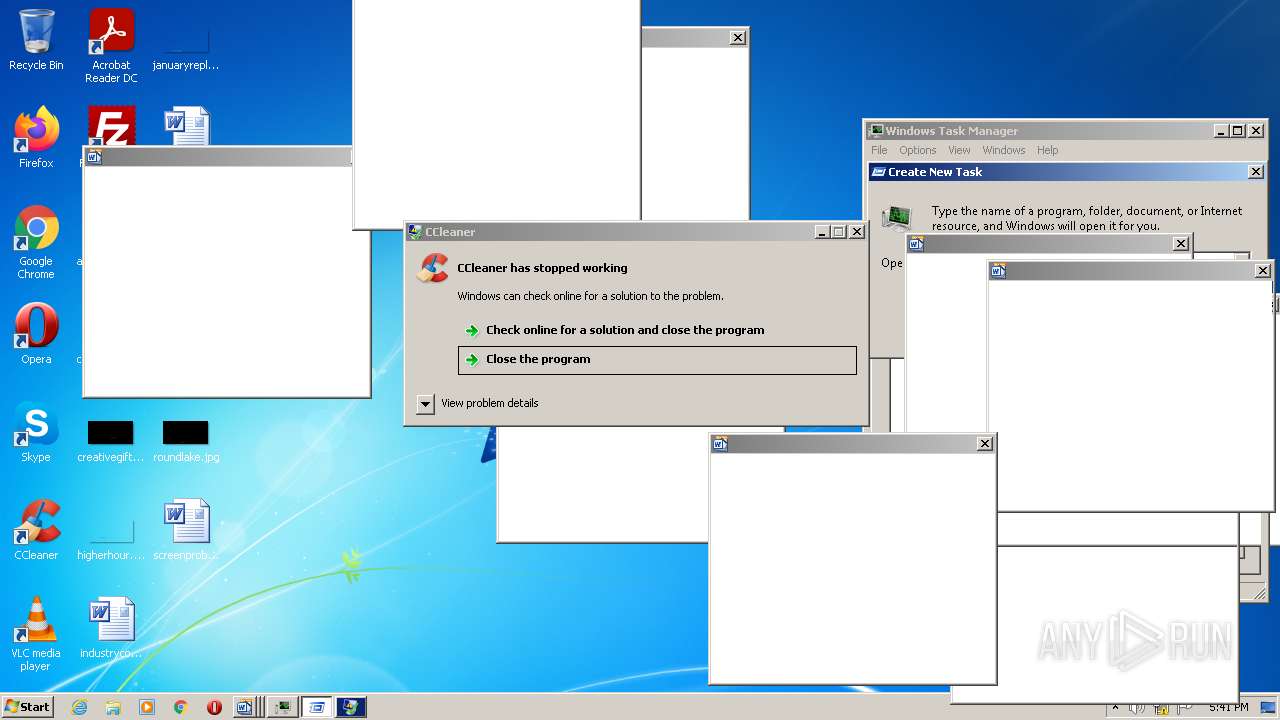
Total processes
49
Monitored processes
11
Malicious processes
3
Suspicious processes
2
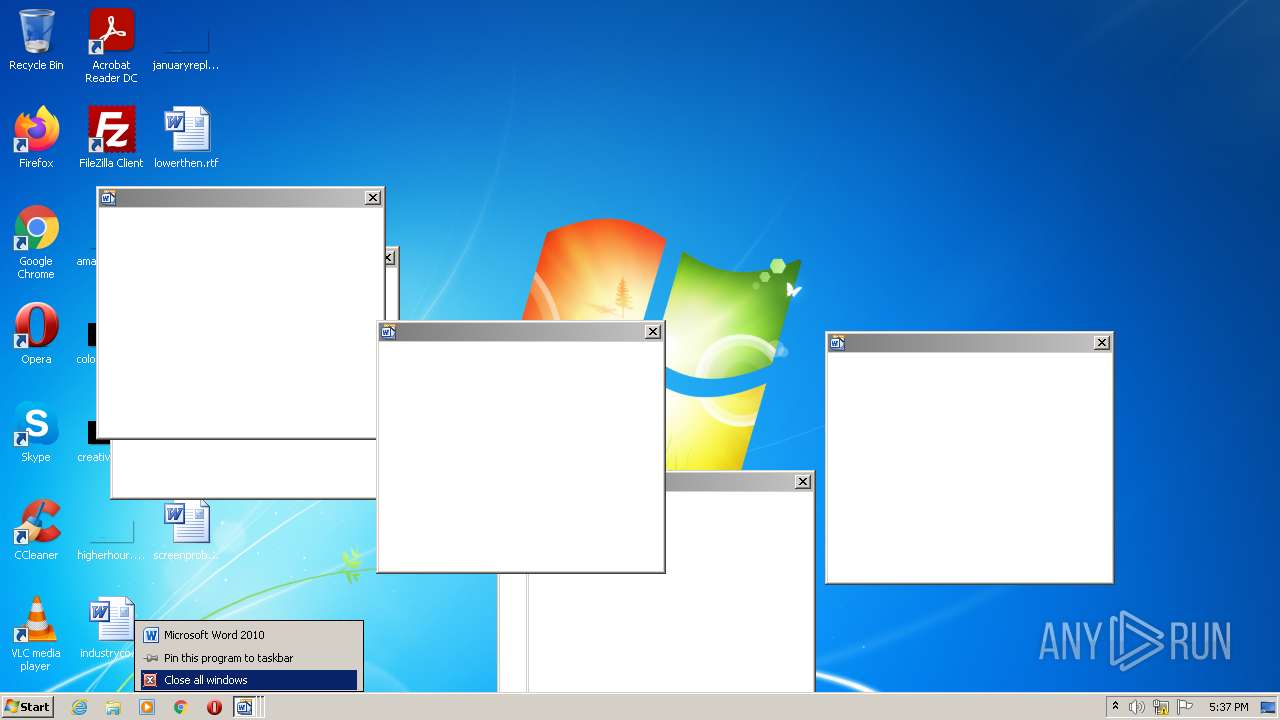
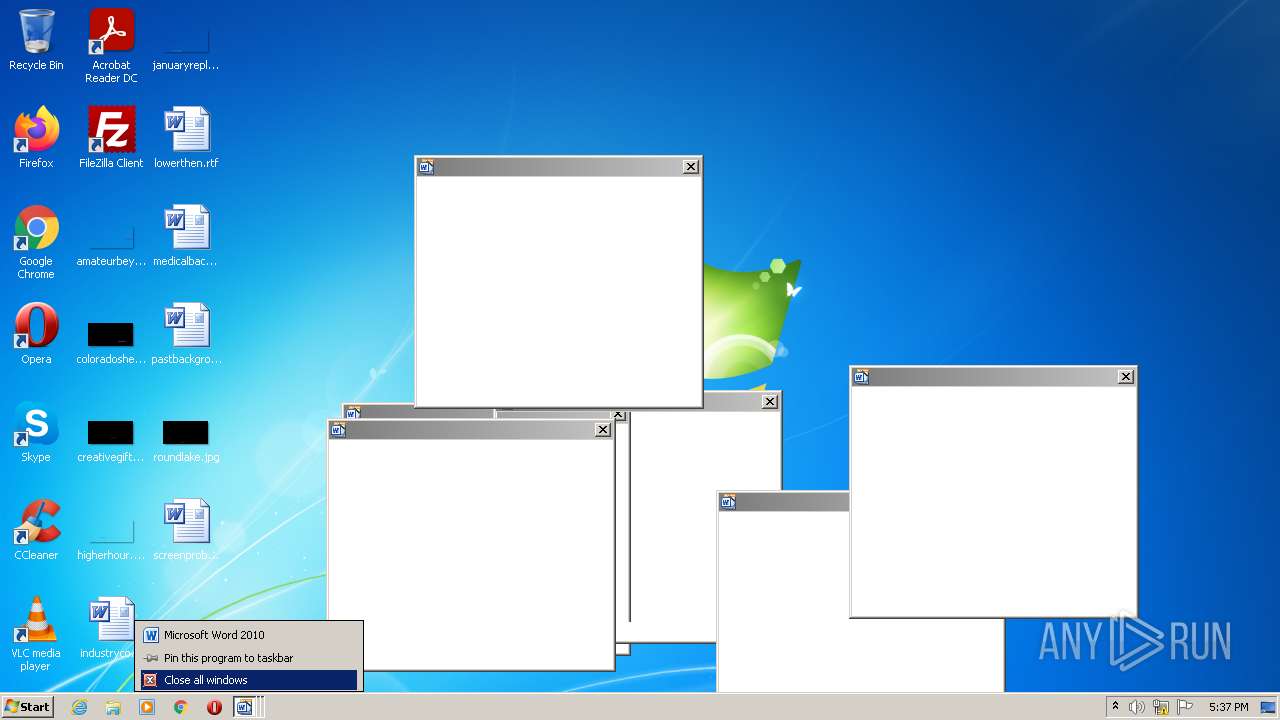
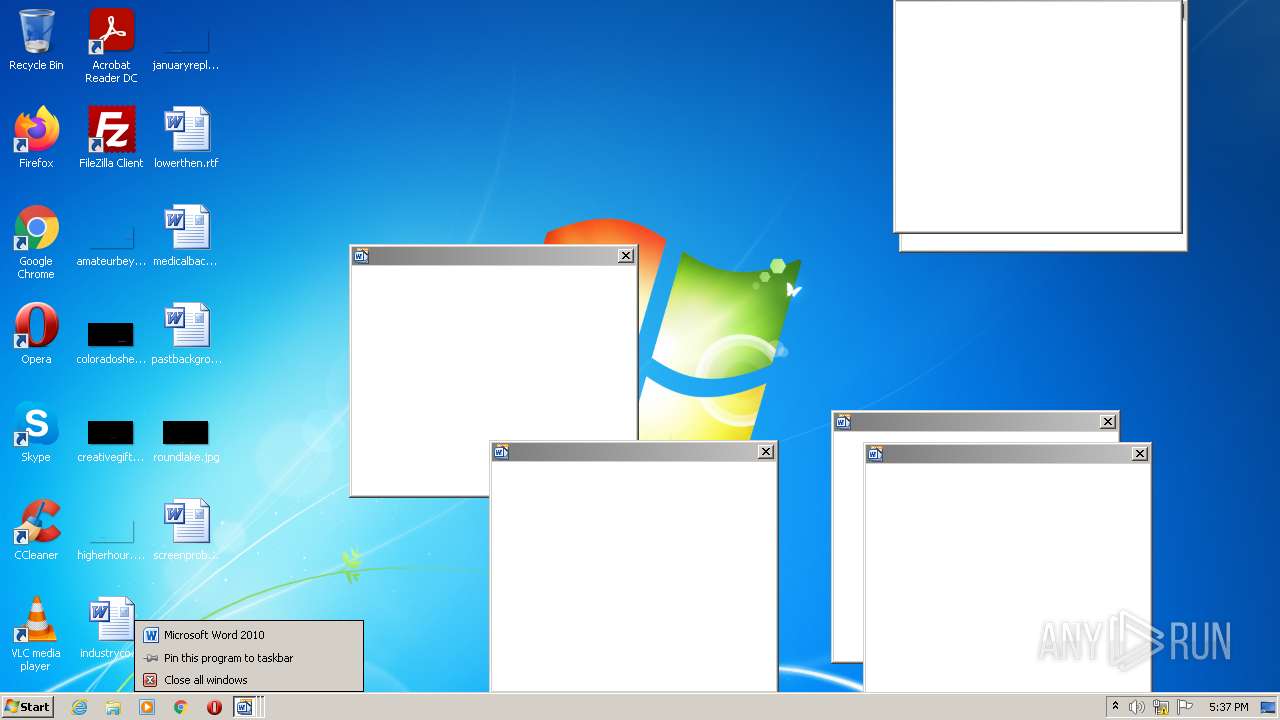
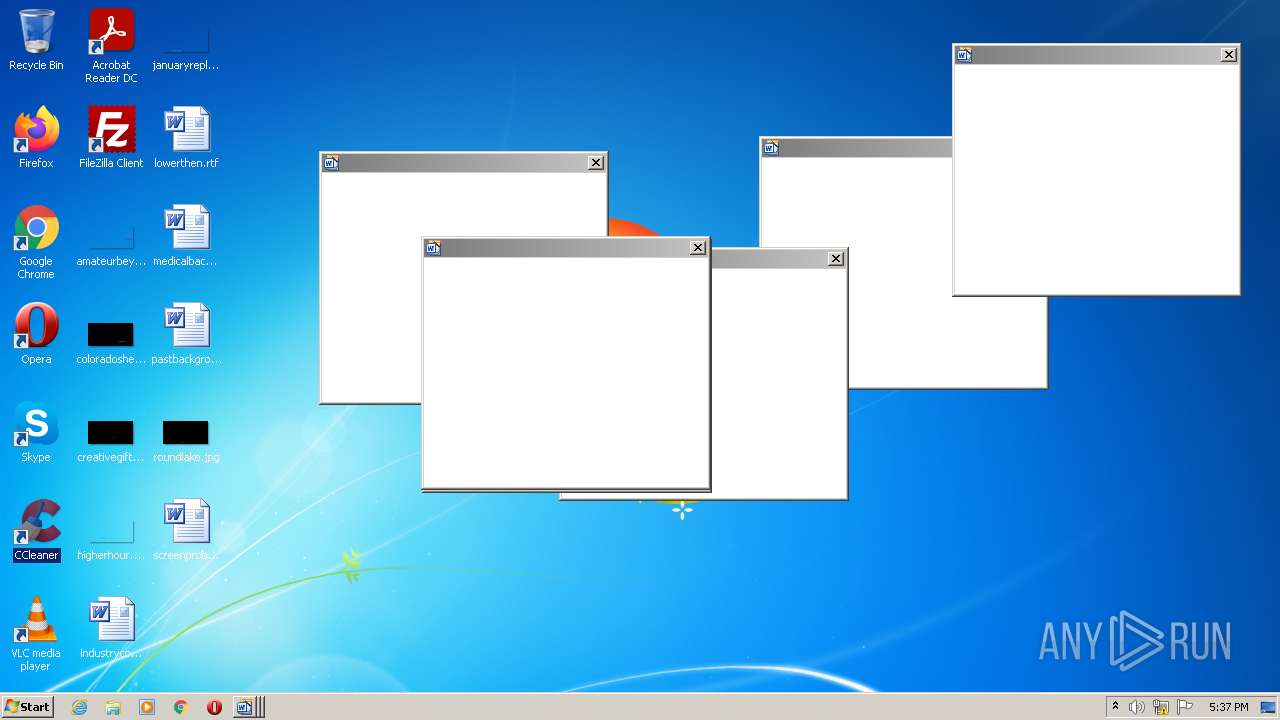
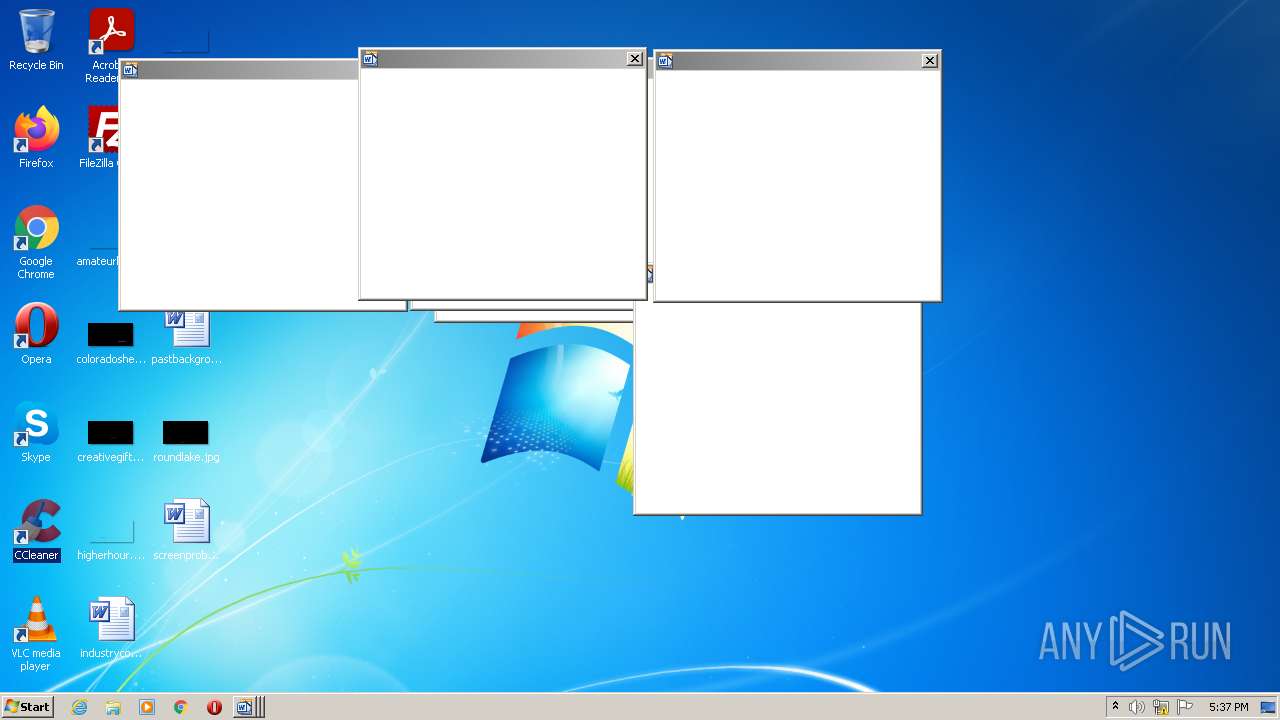
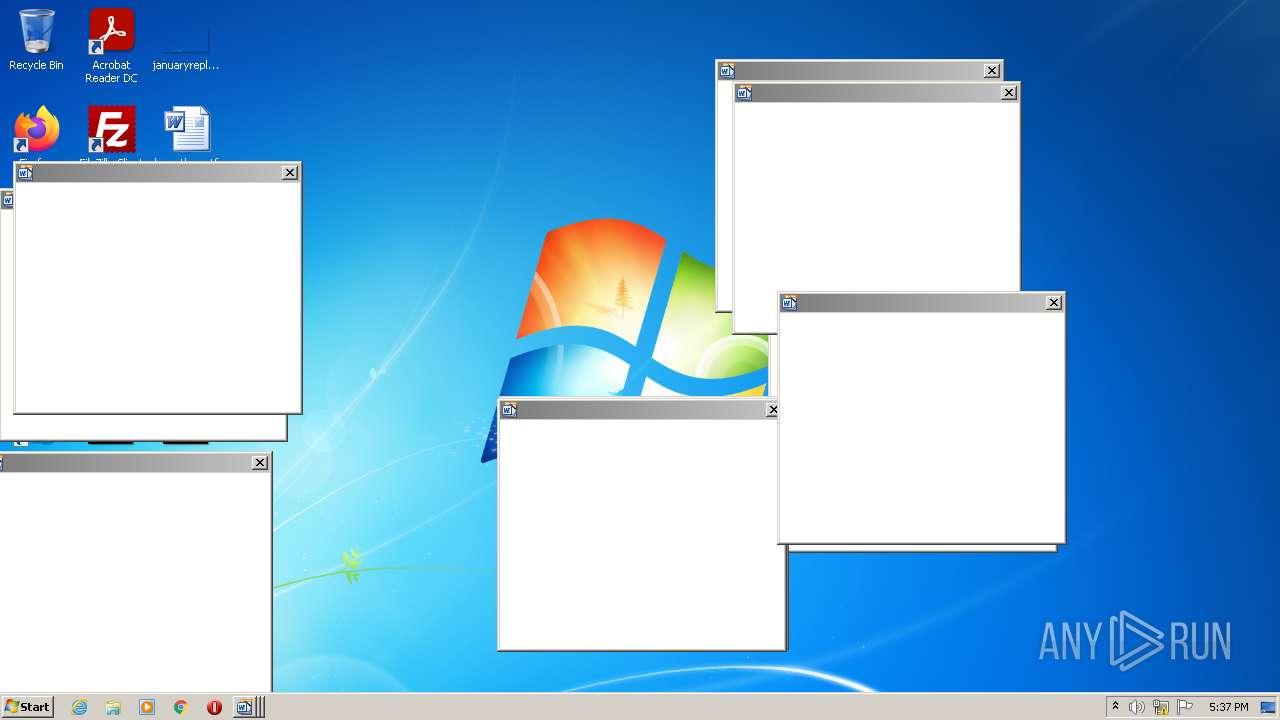
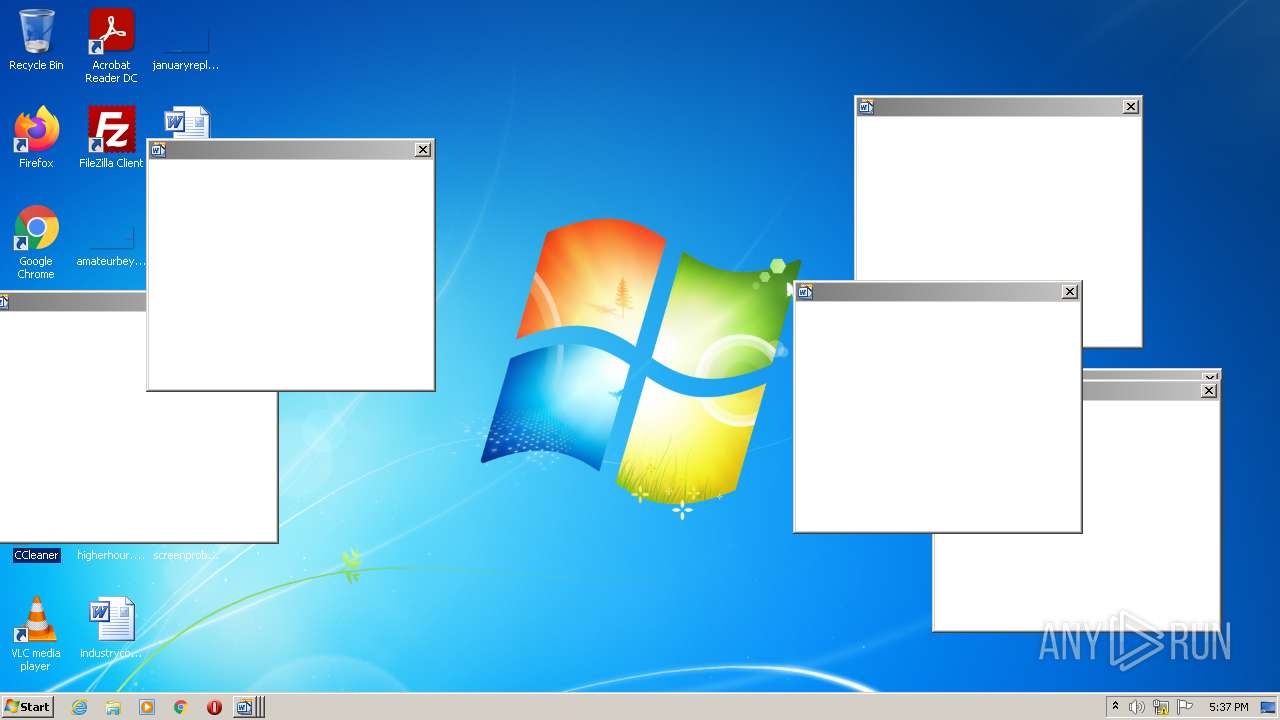
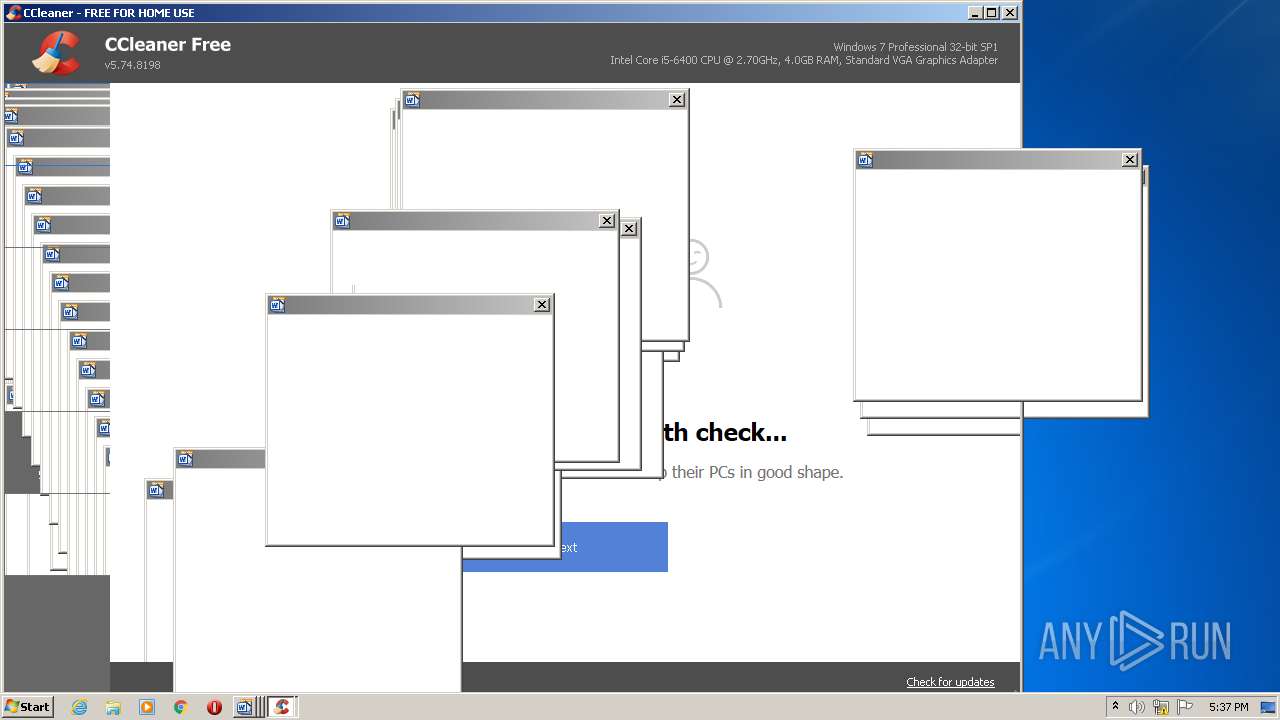
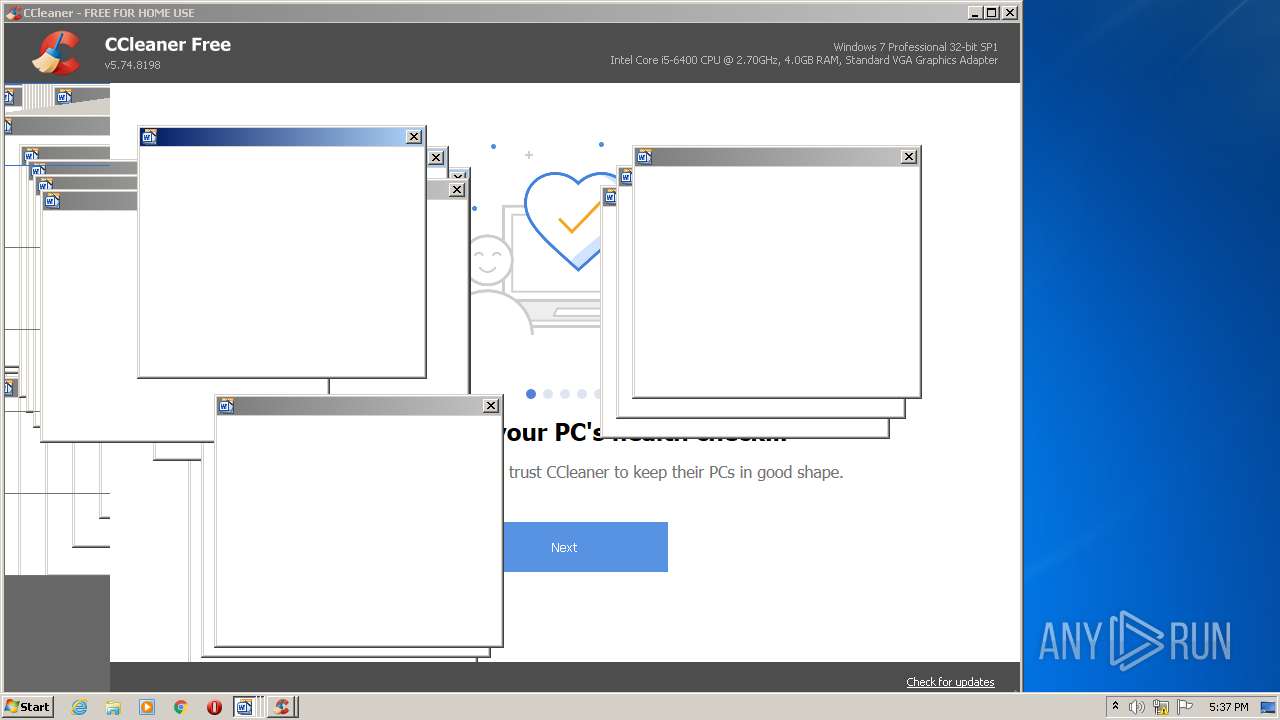
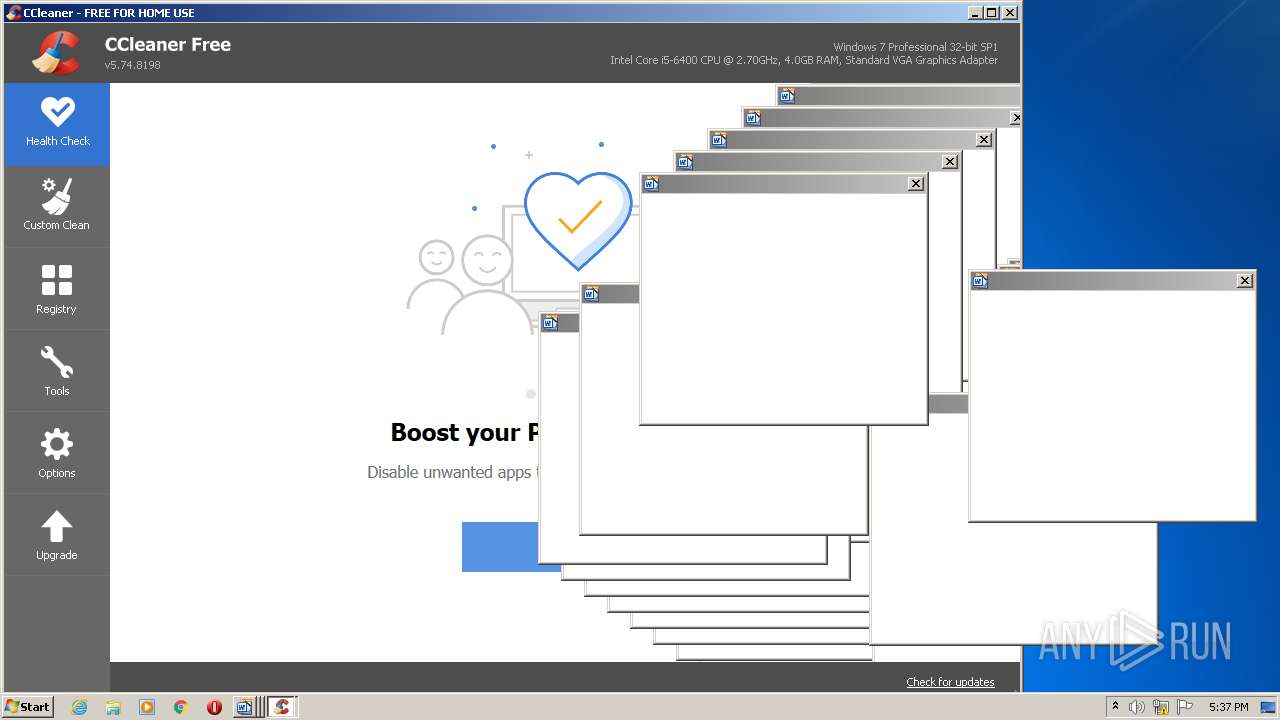
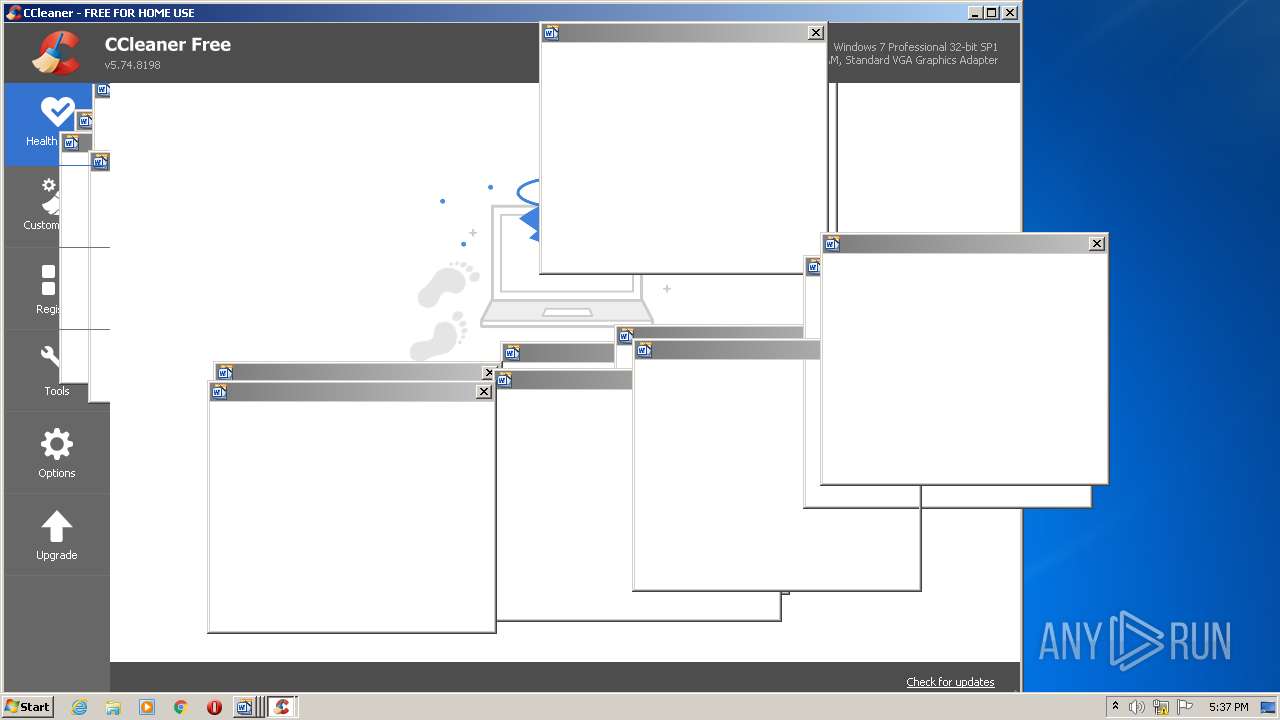
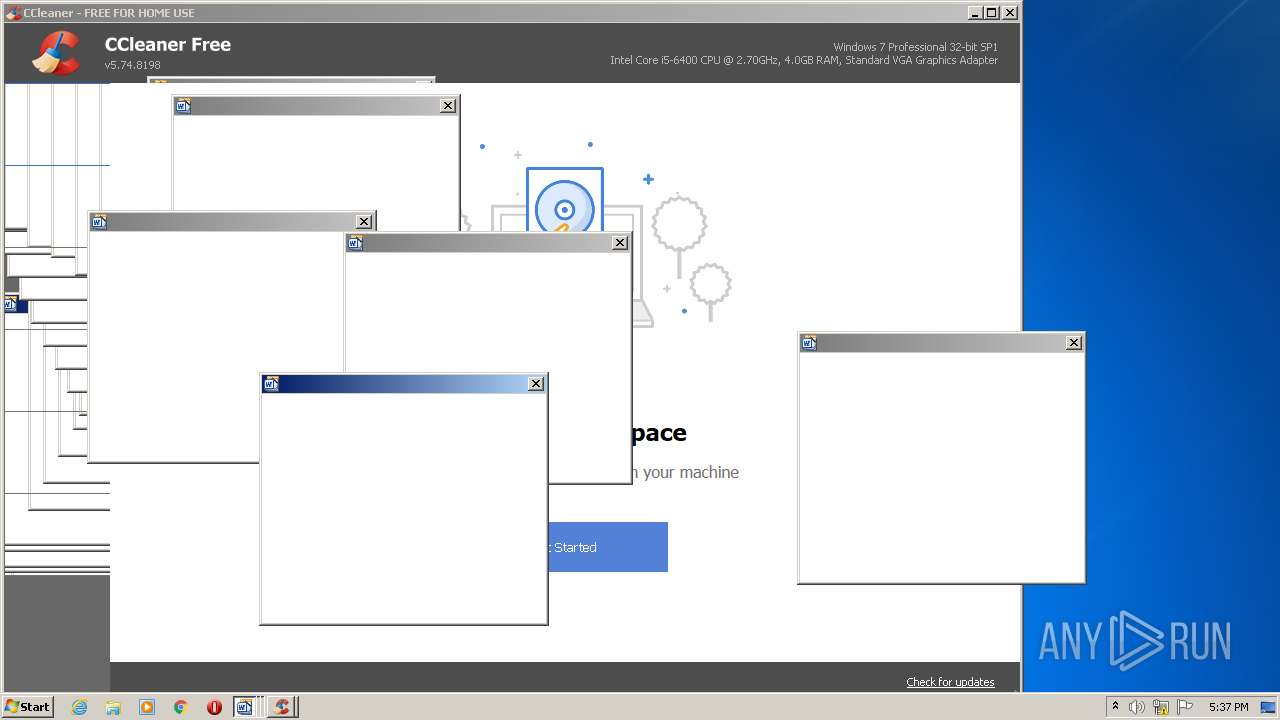
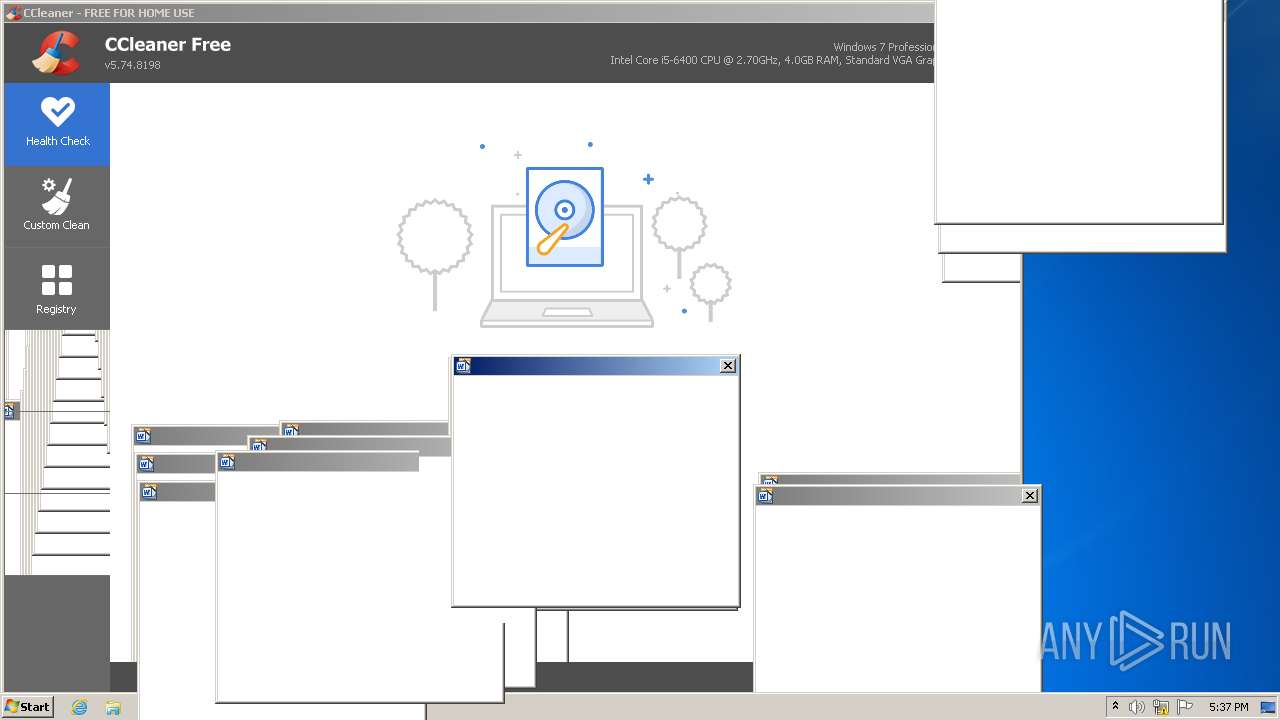
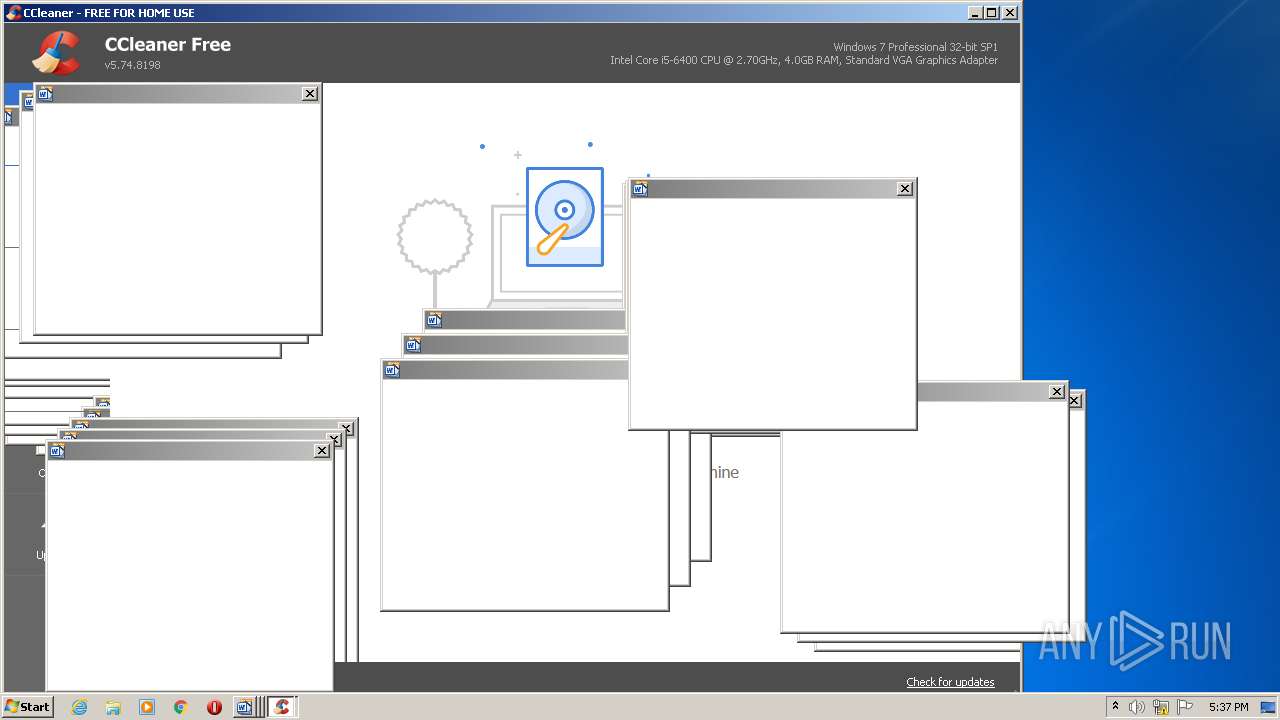
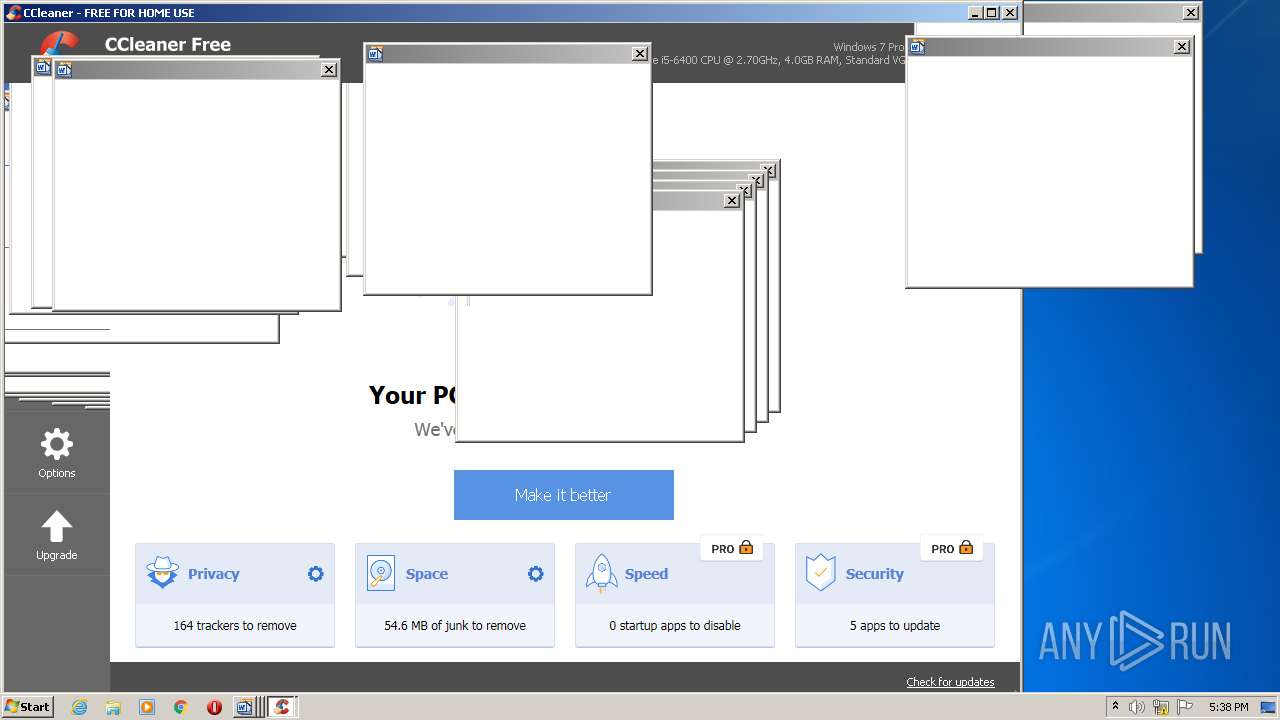
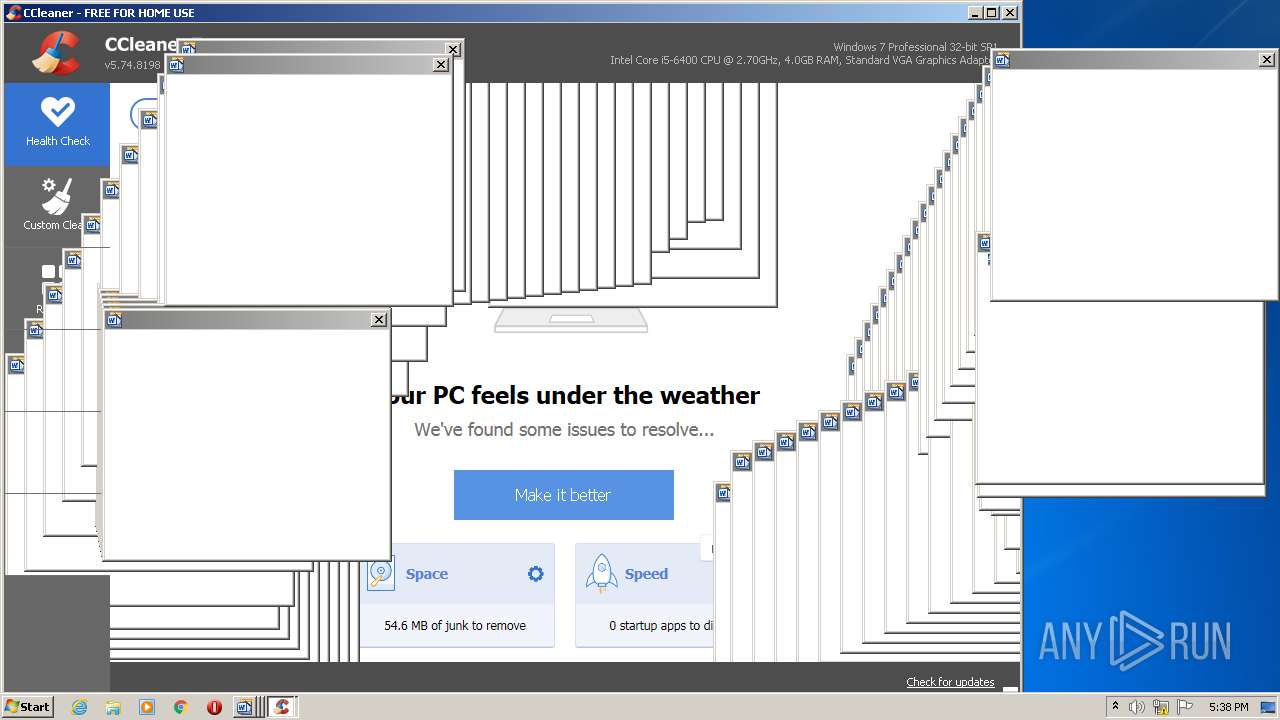
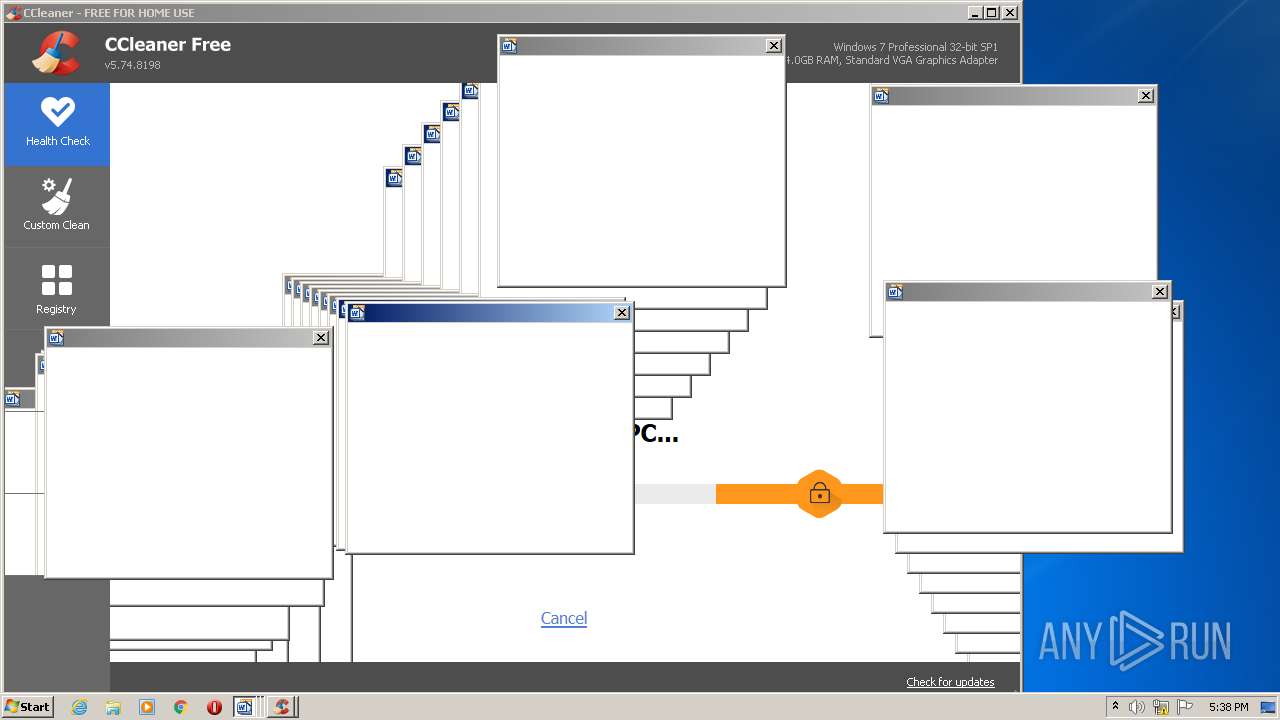
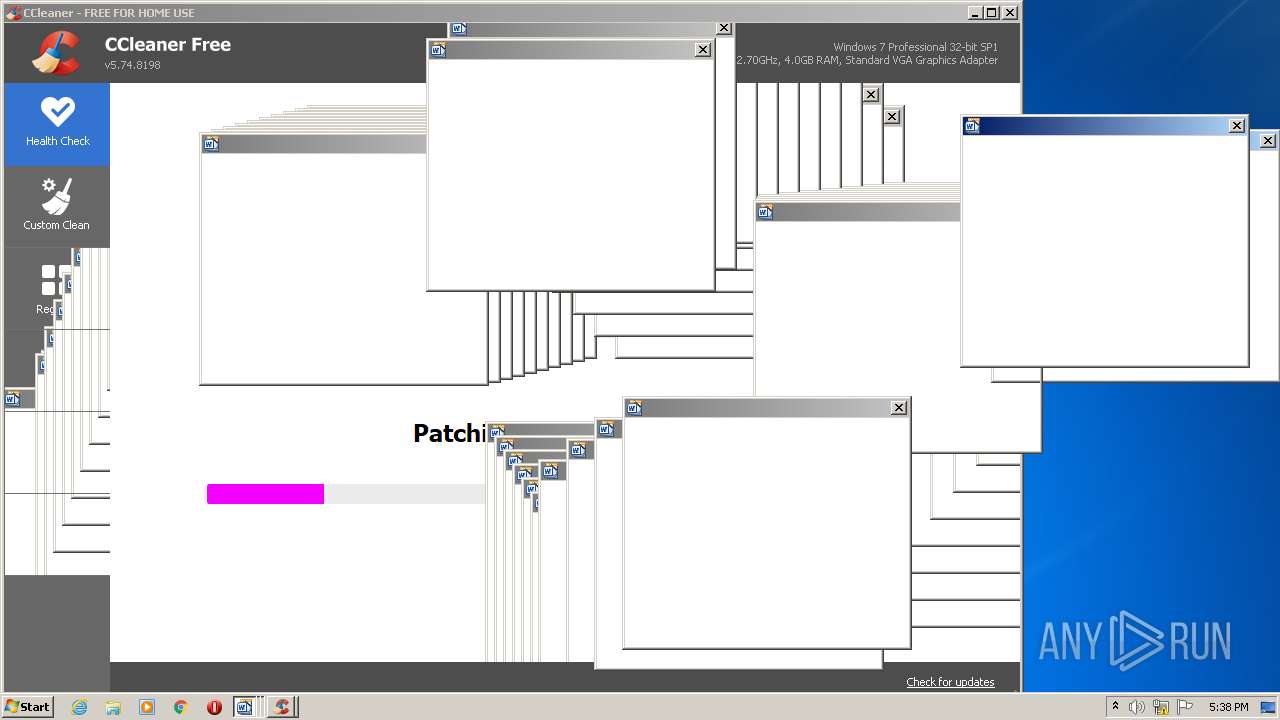
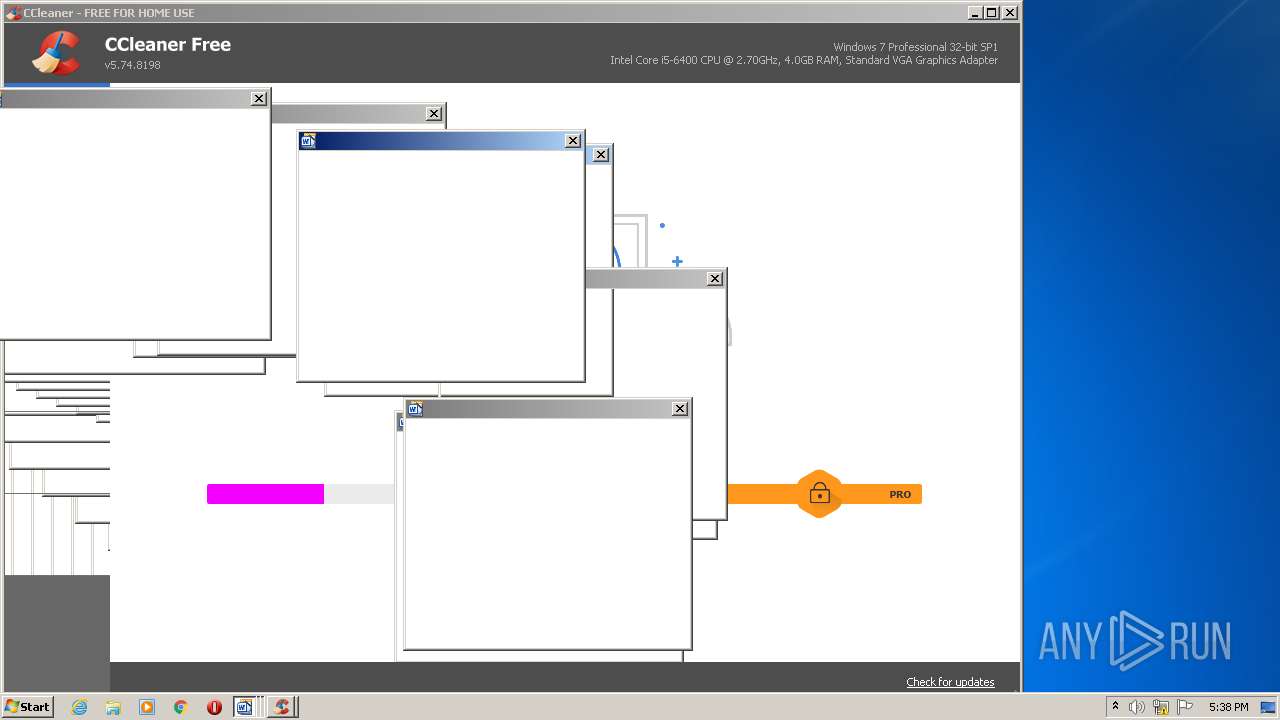
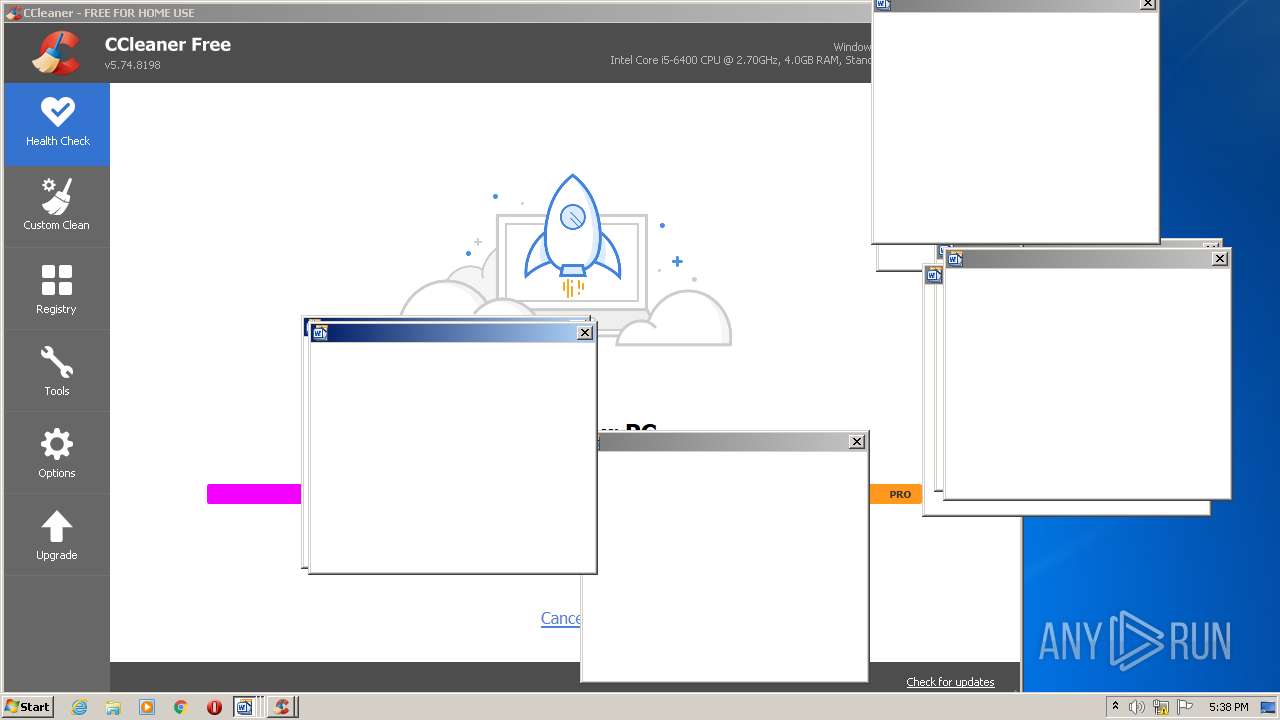
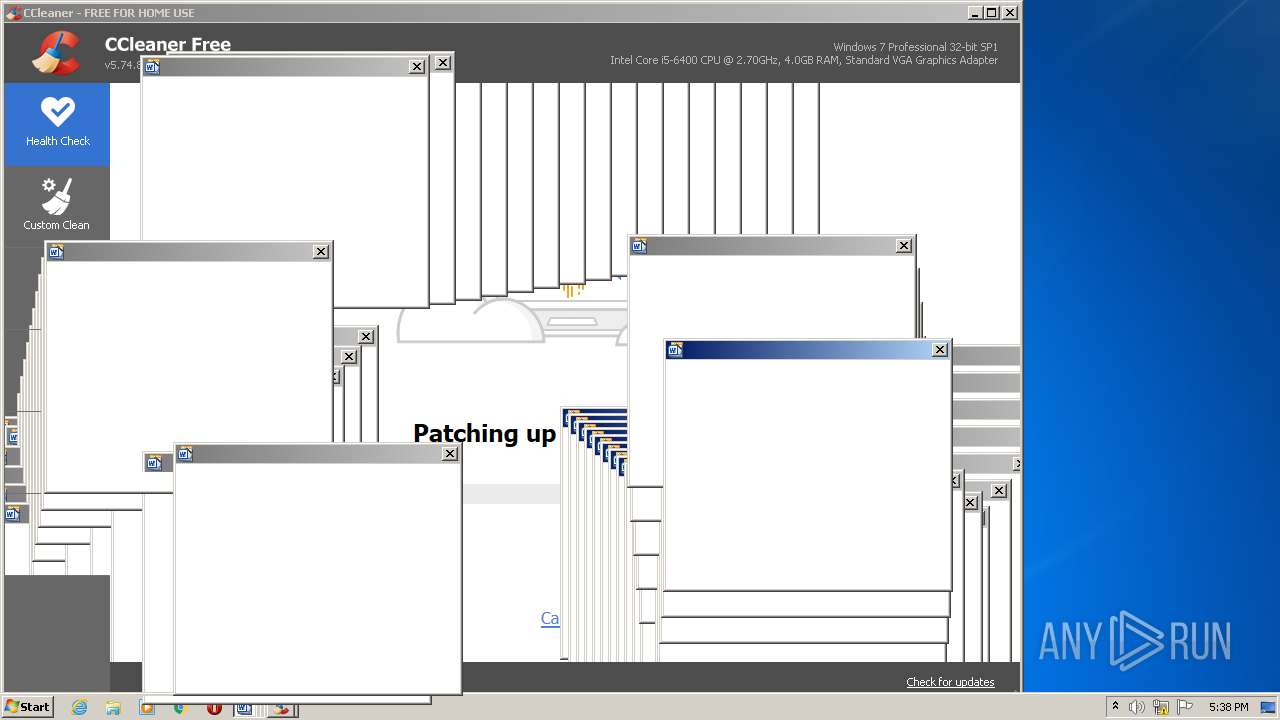
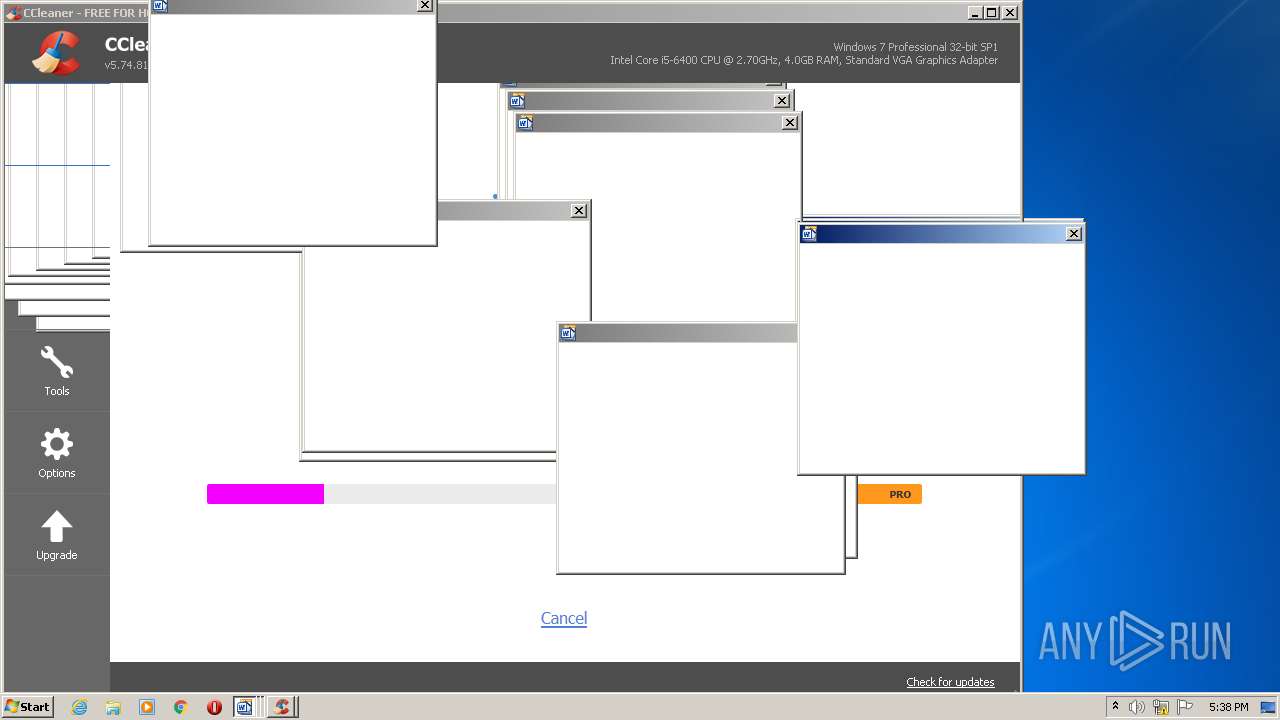
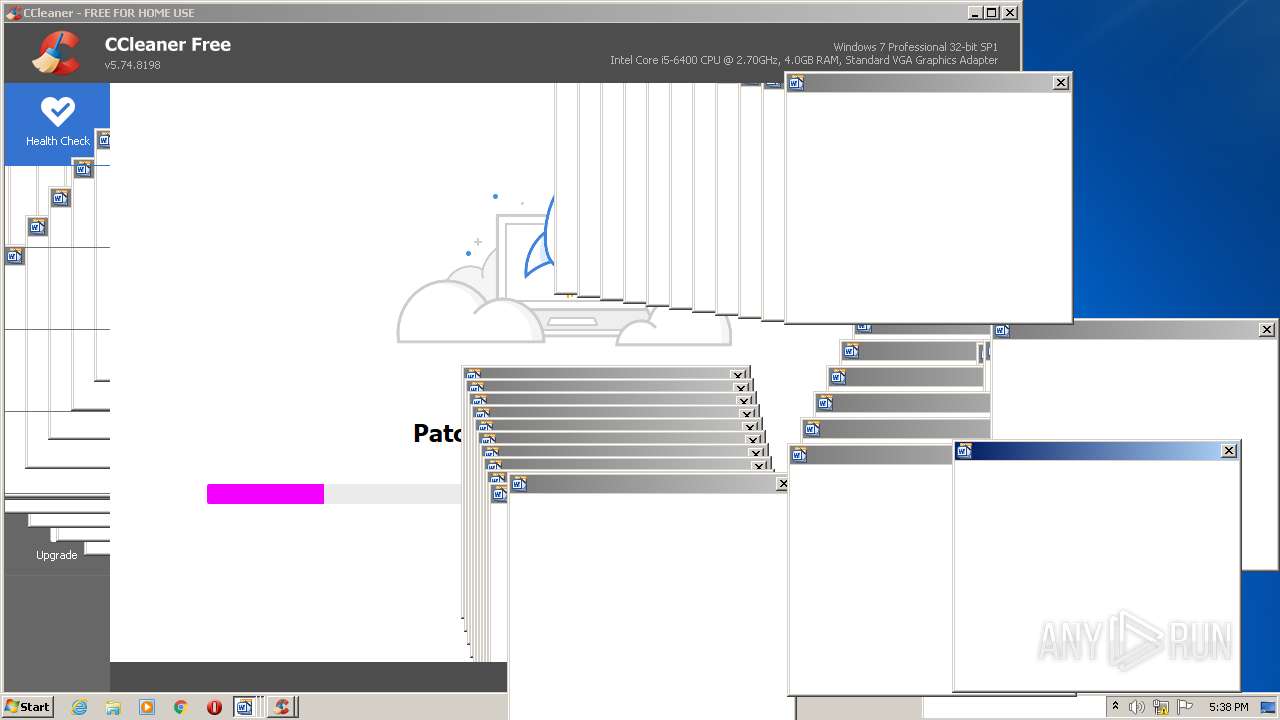
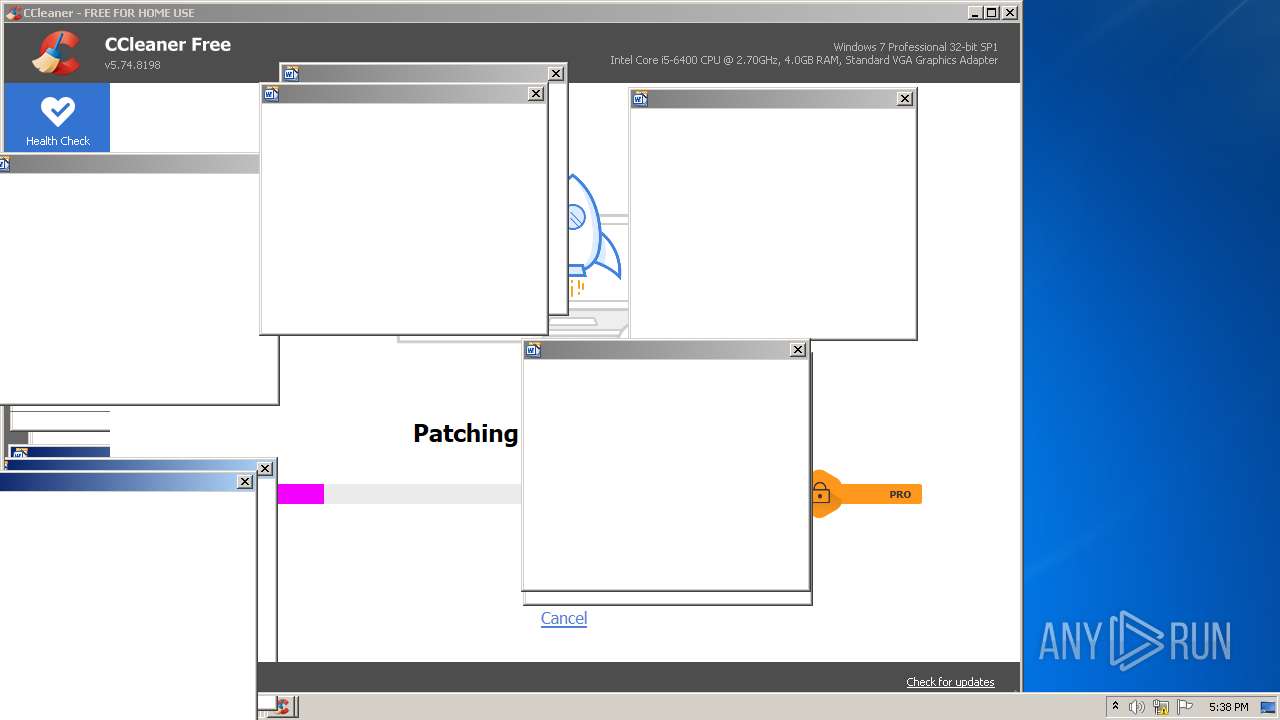
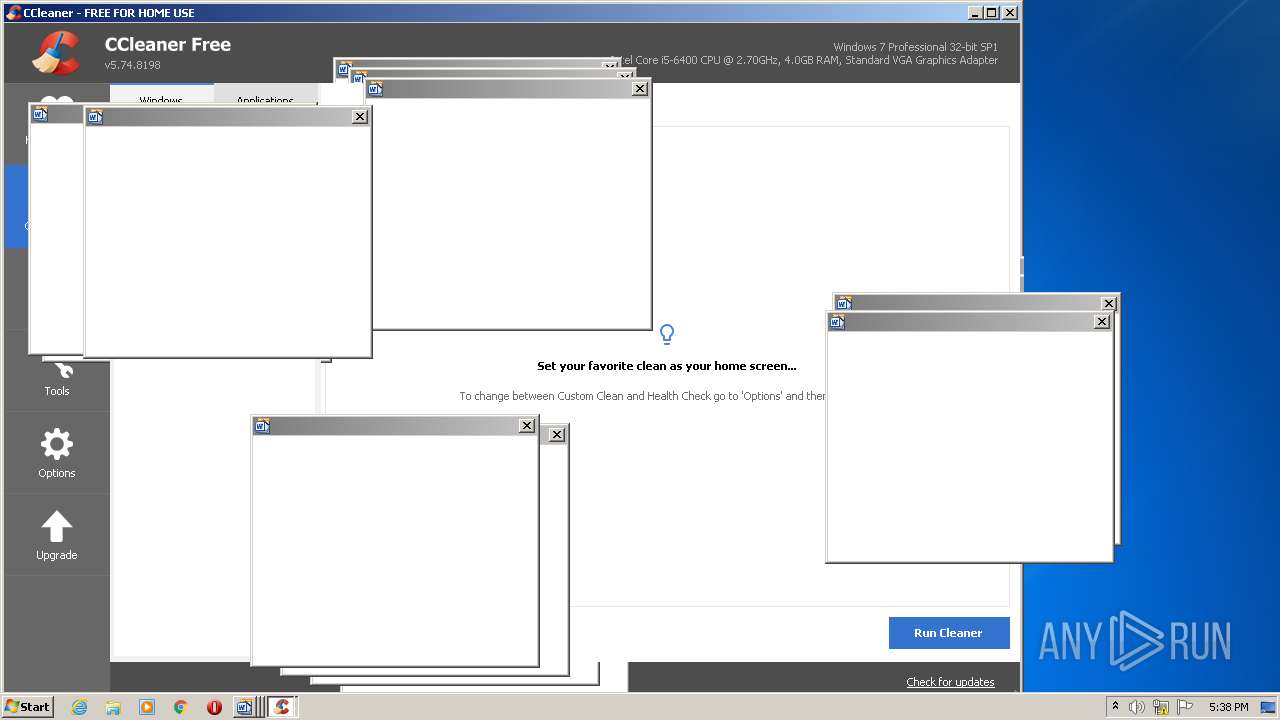
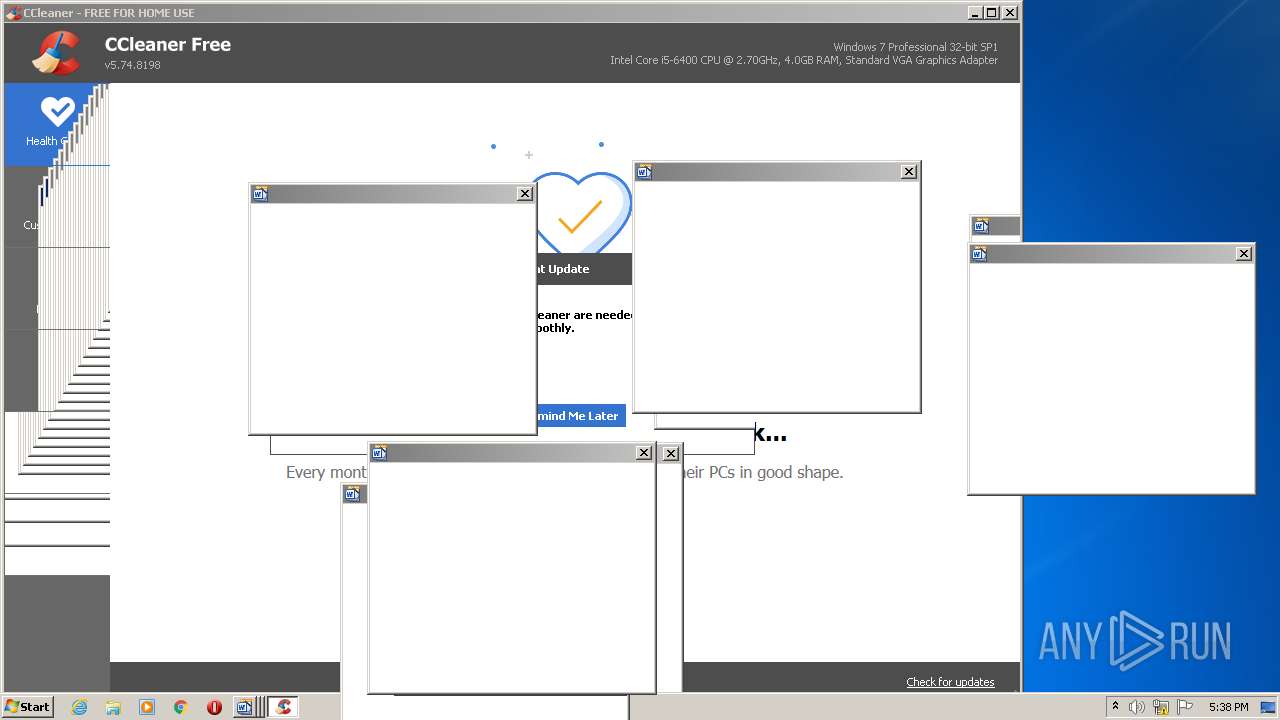
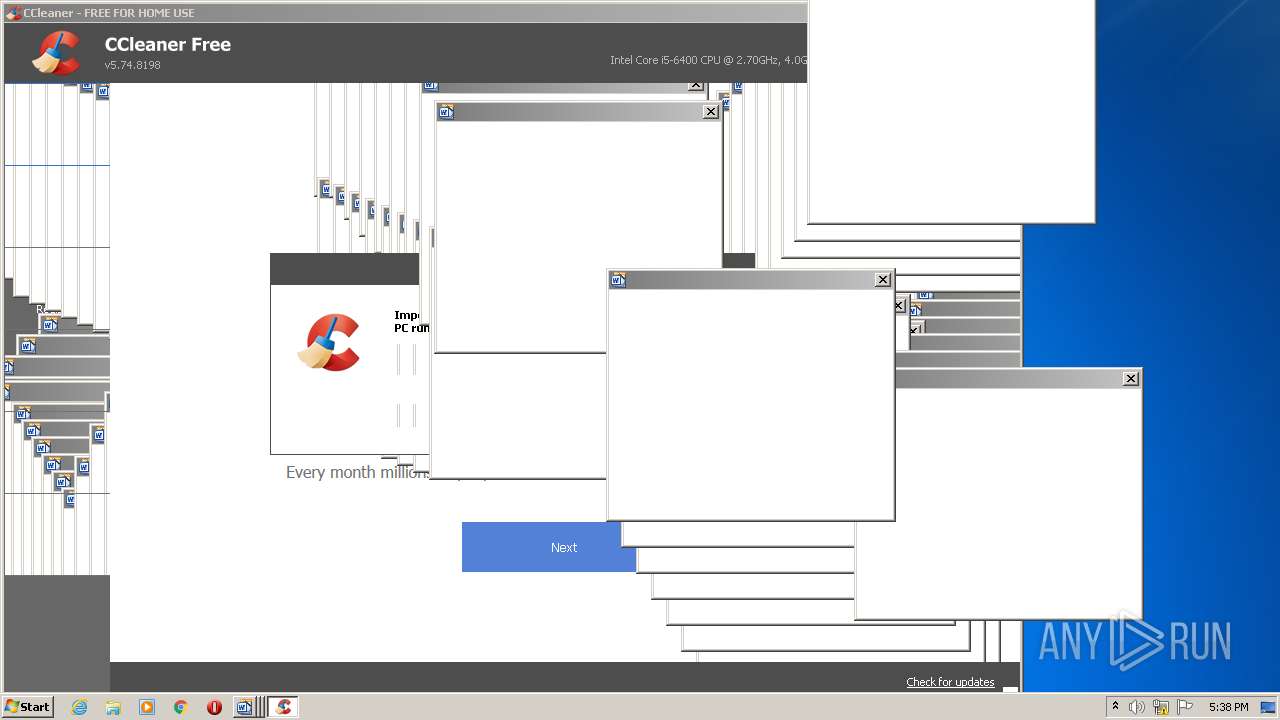
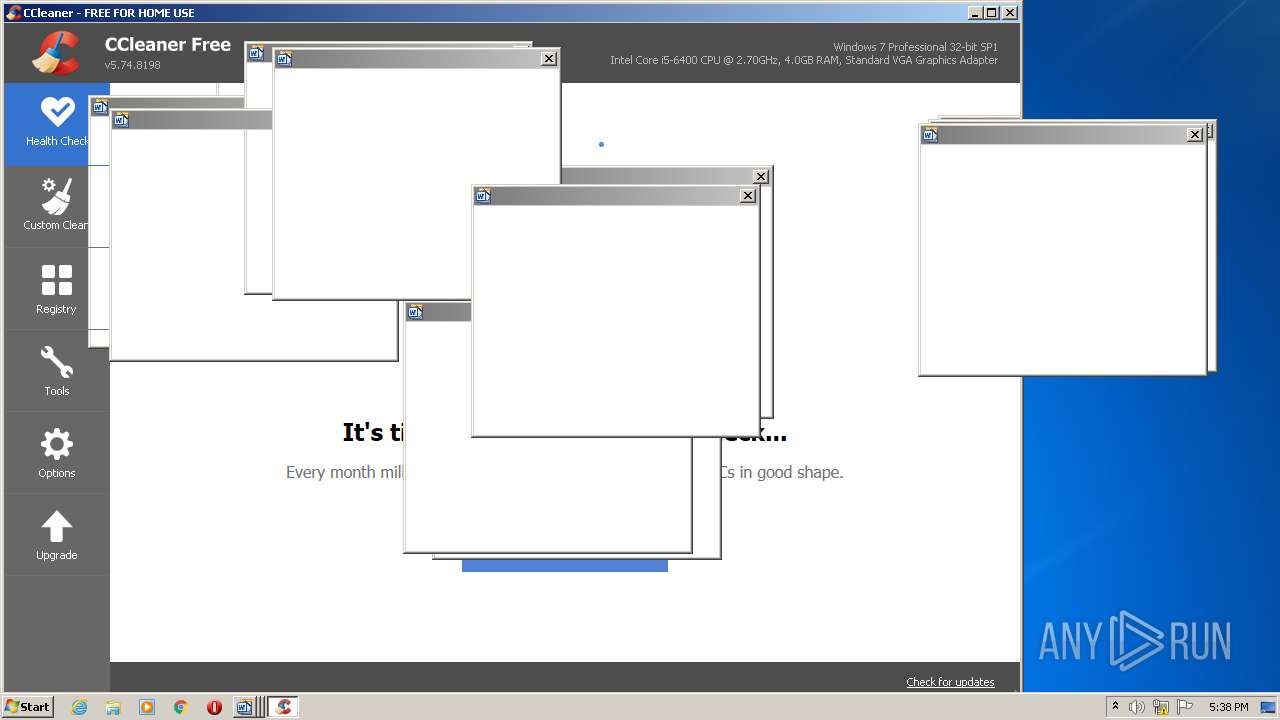
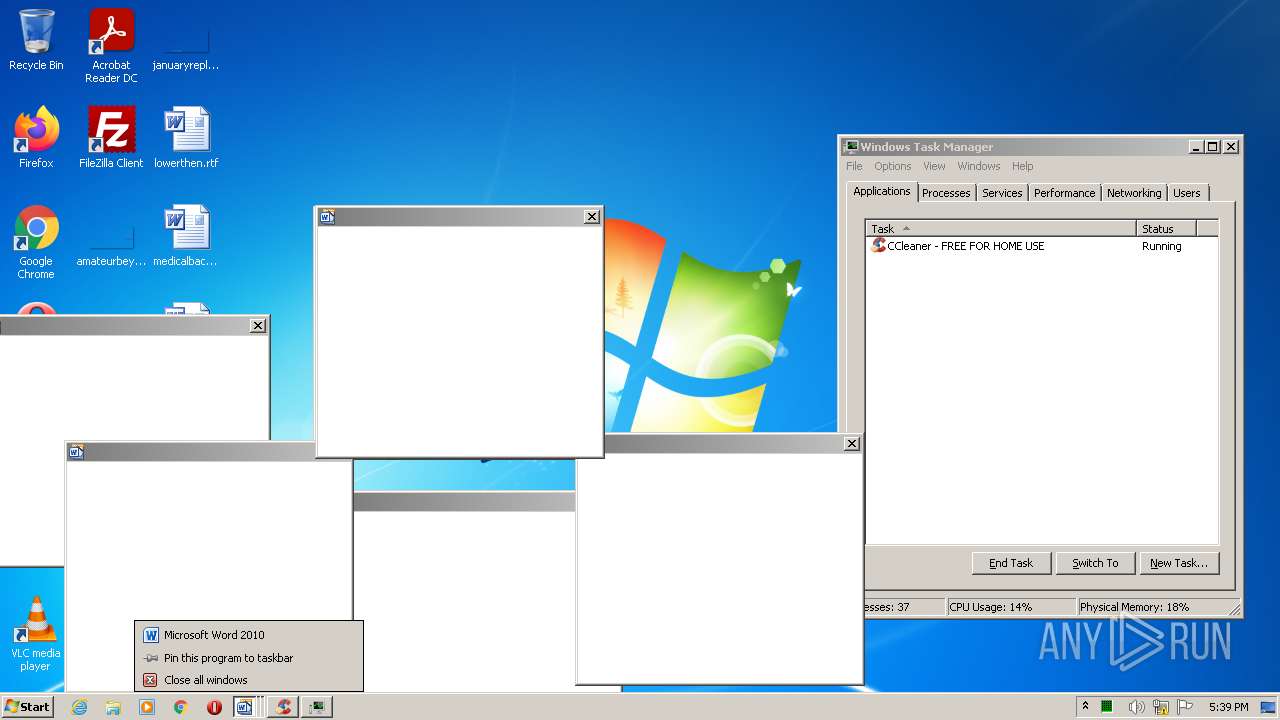
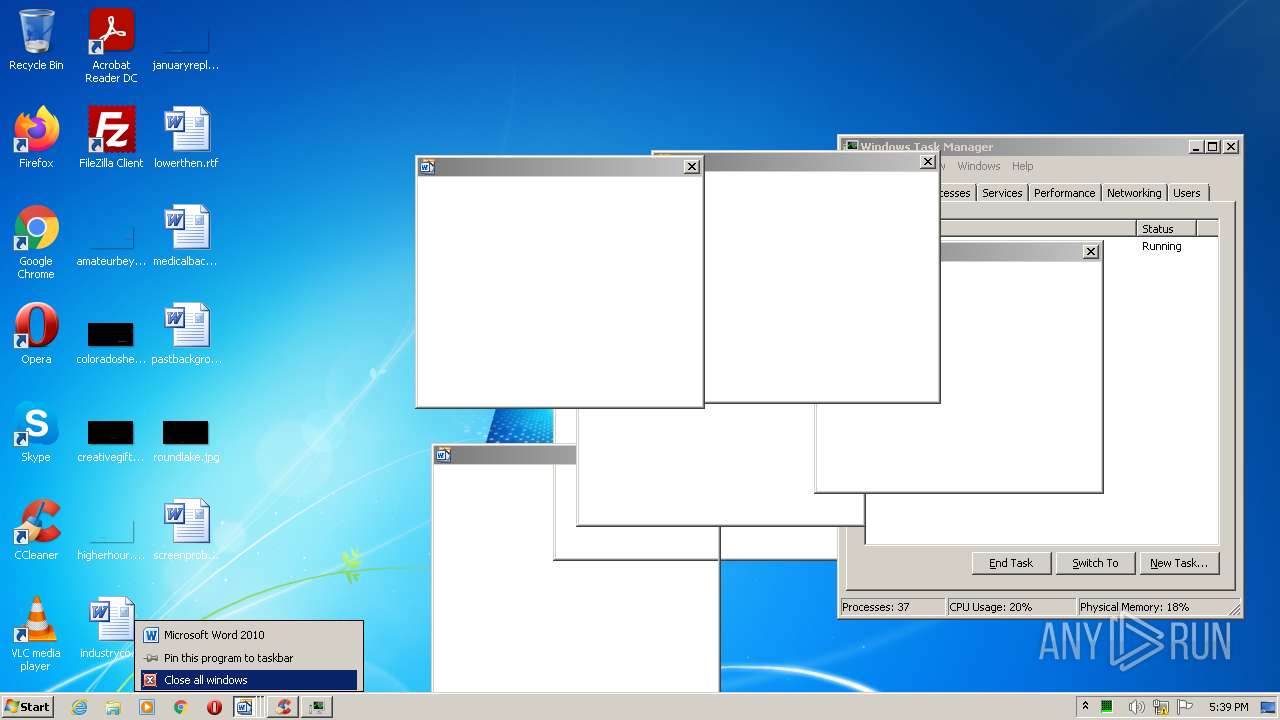
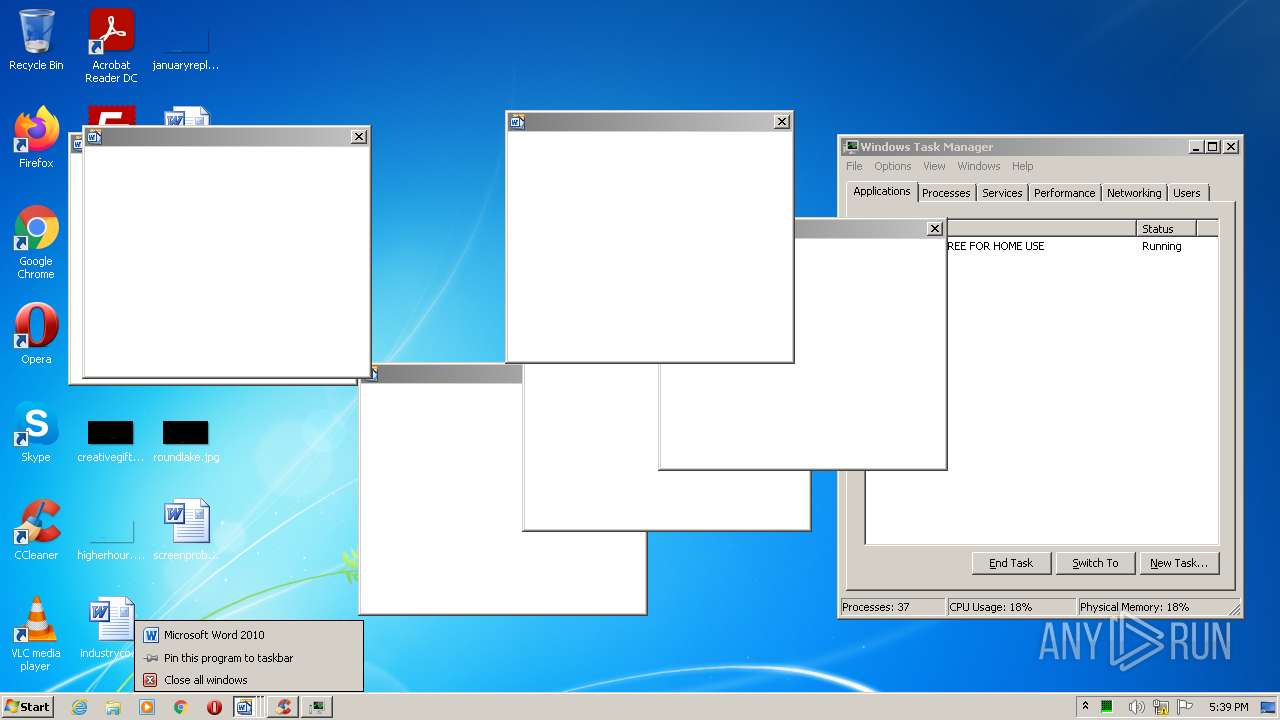
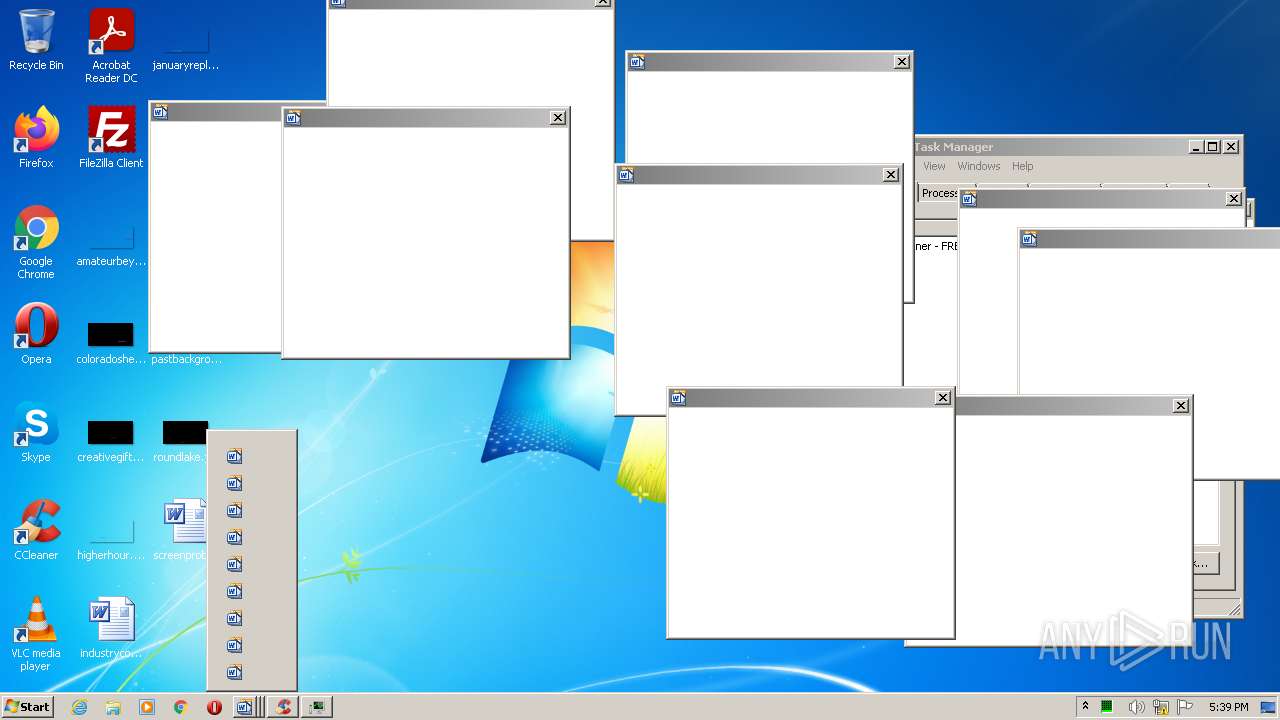
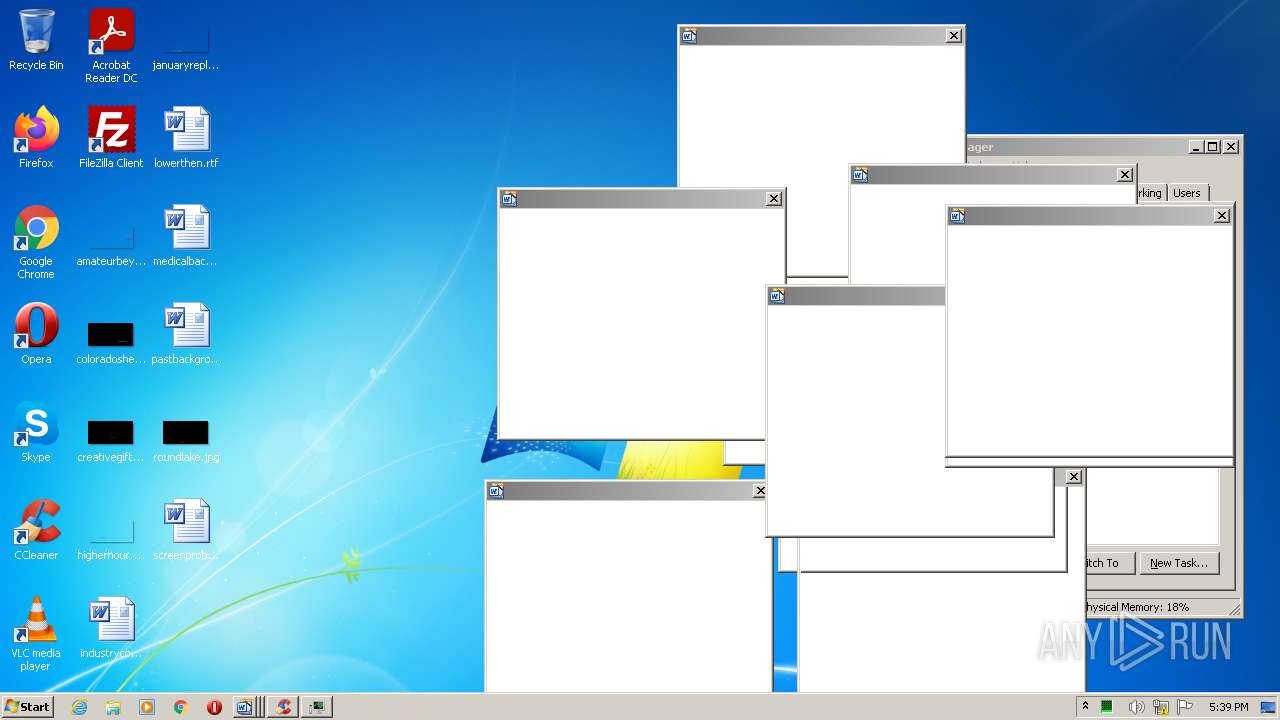
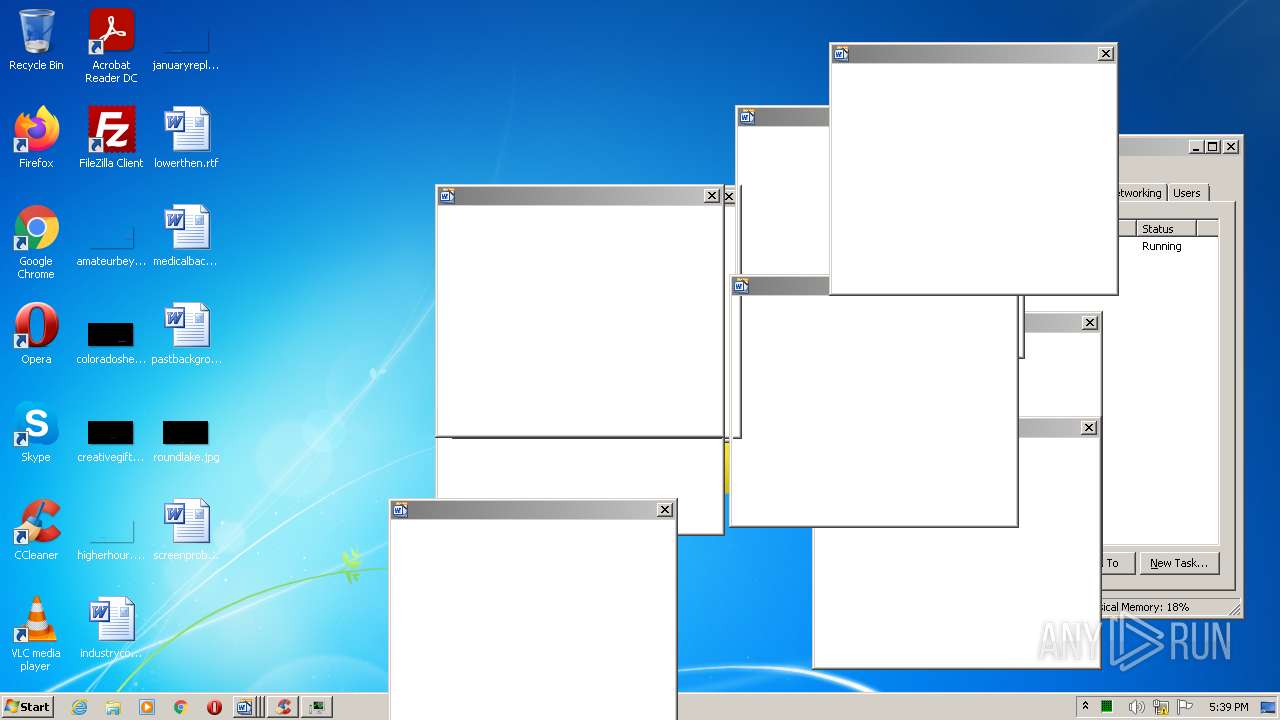
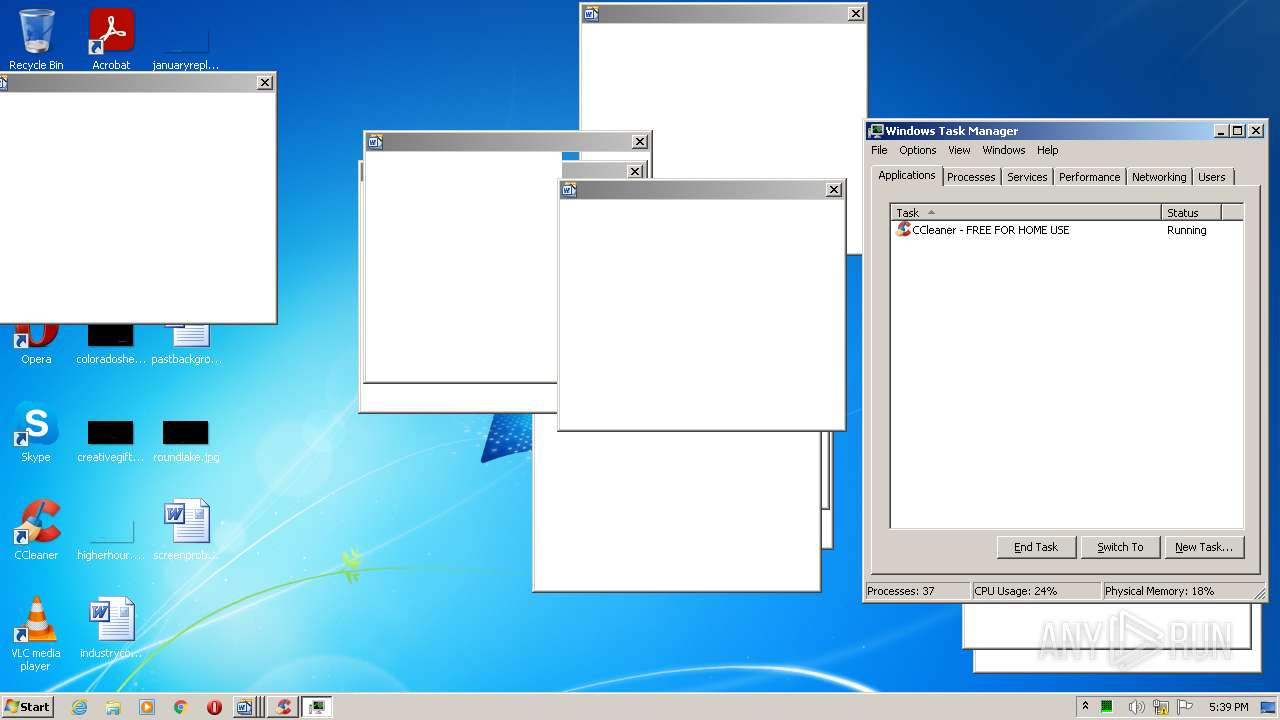
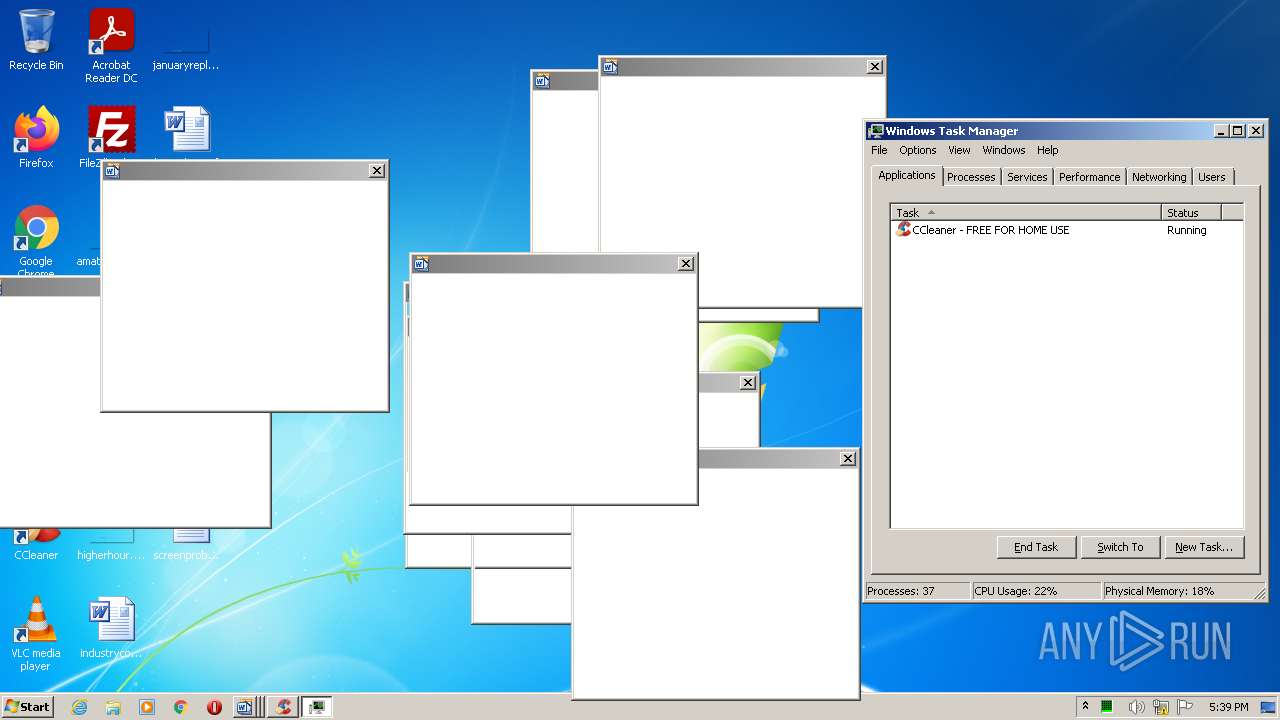
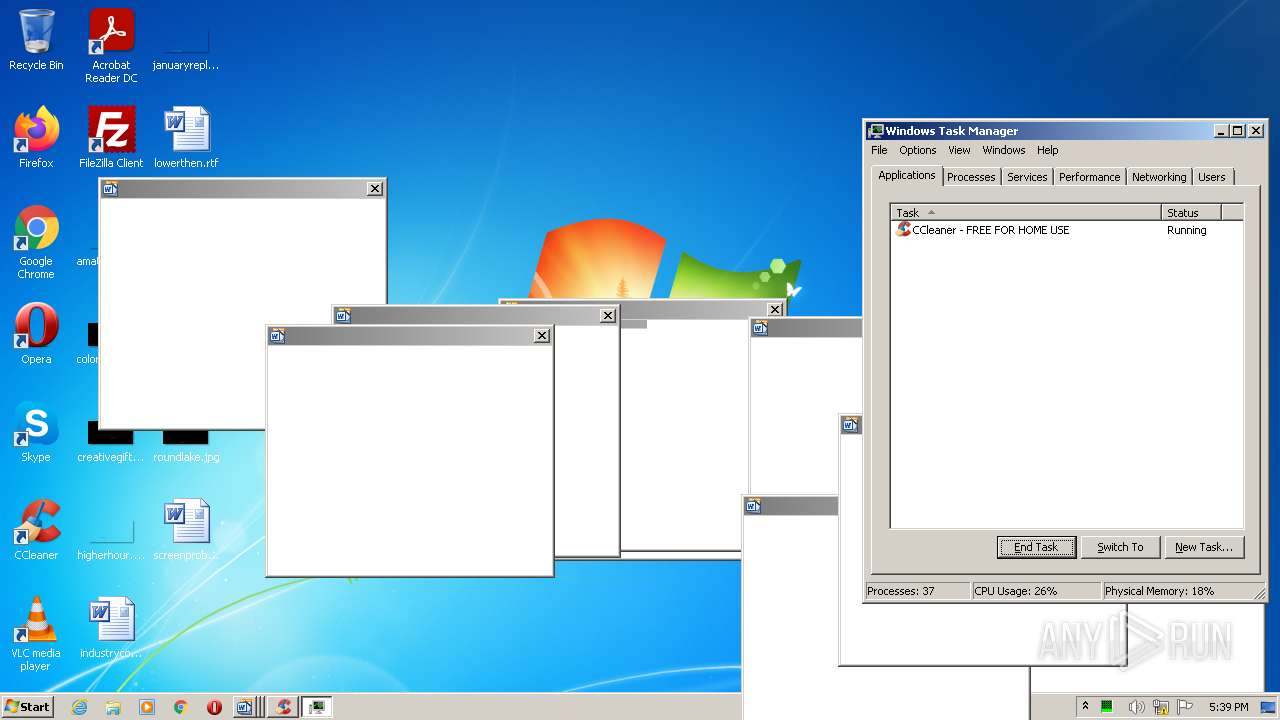
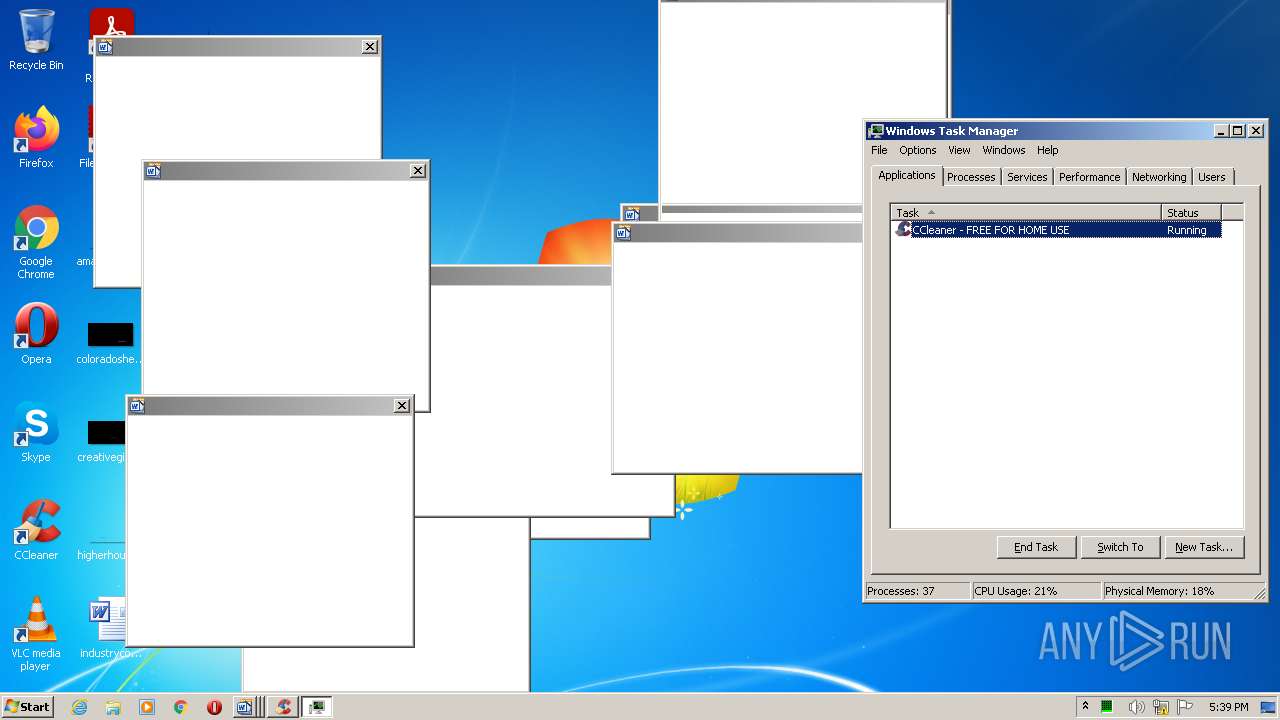
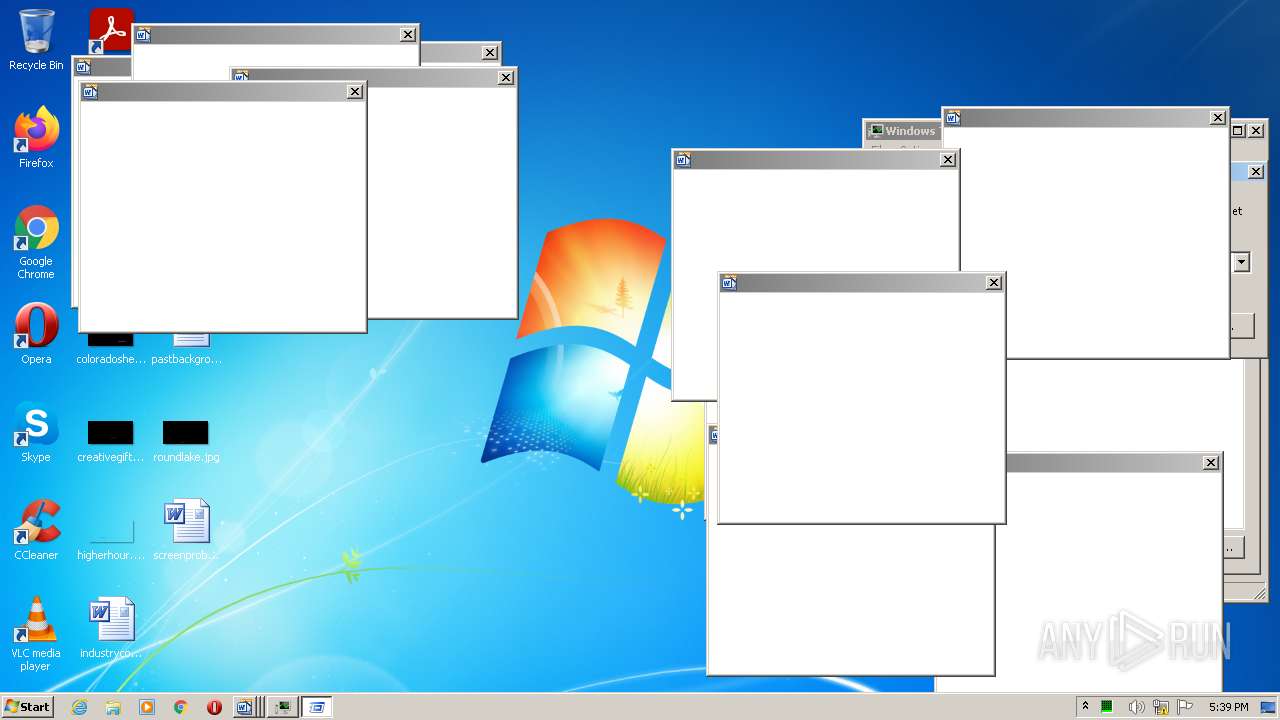
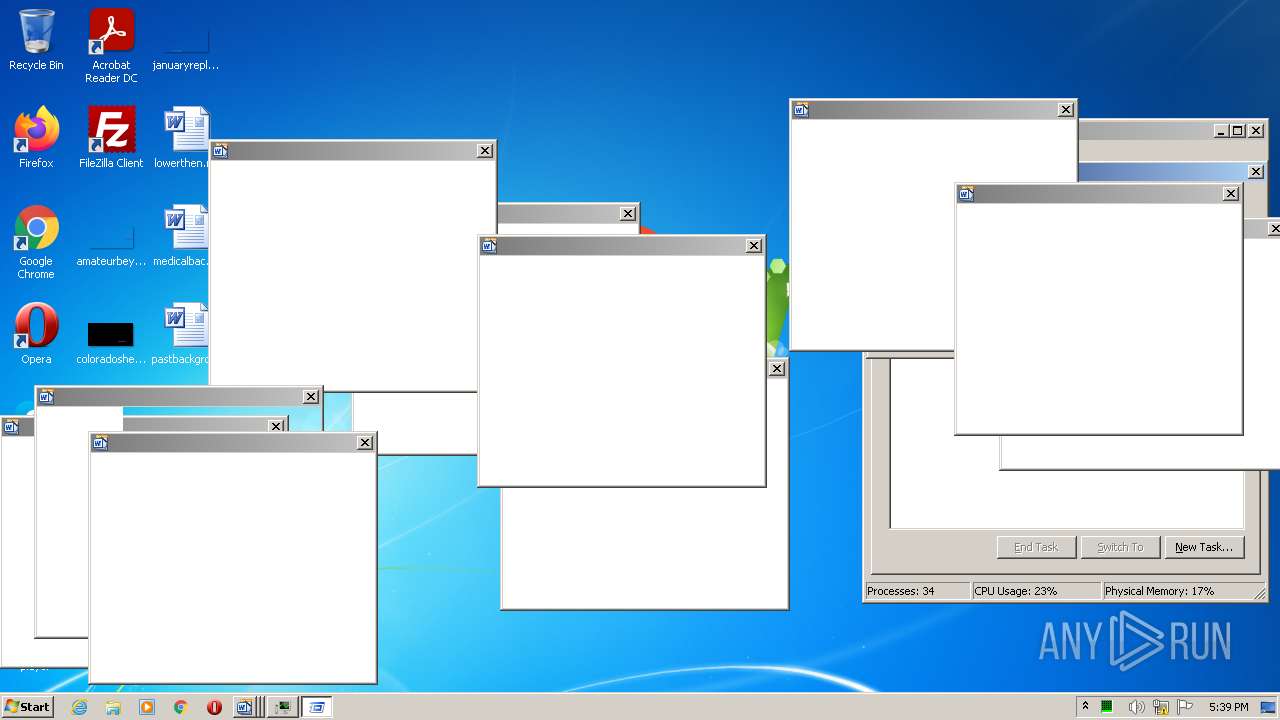
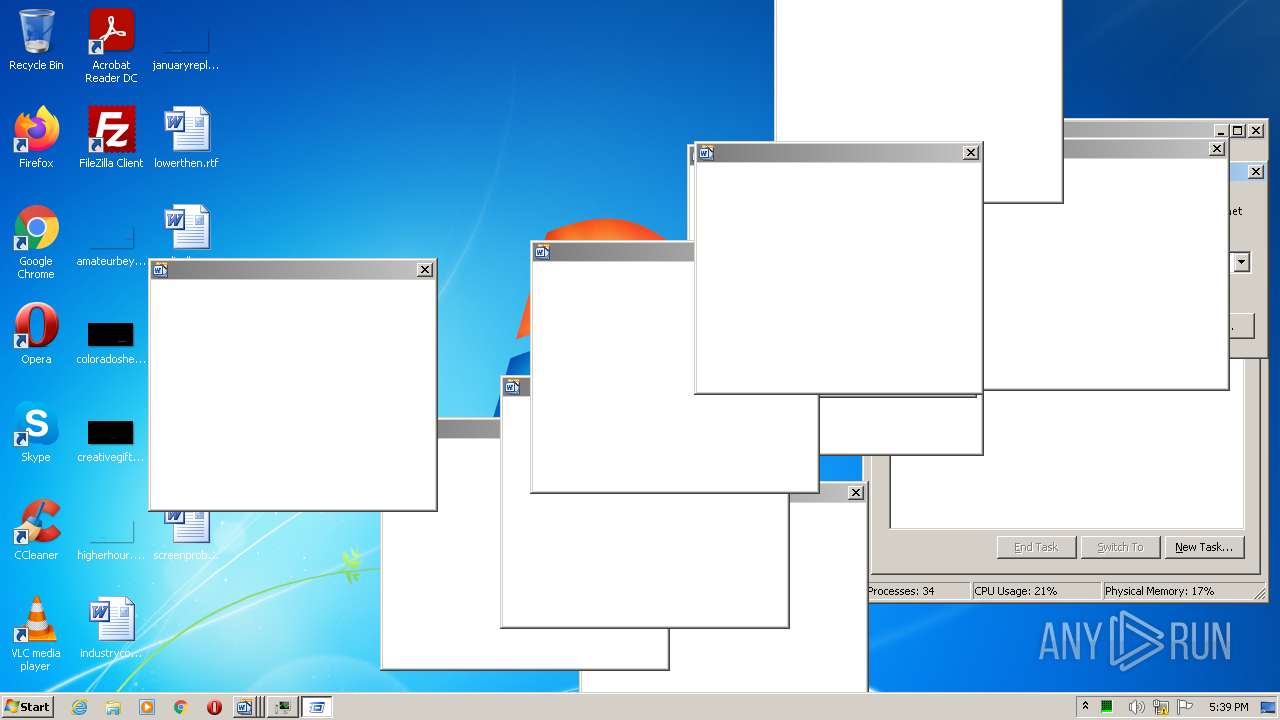
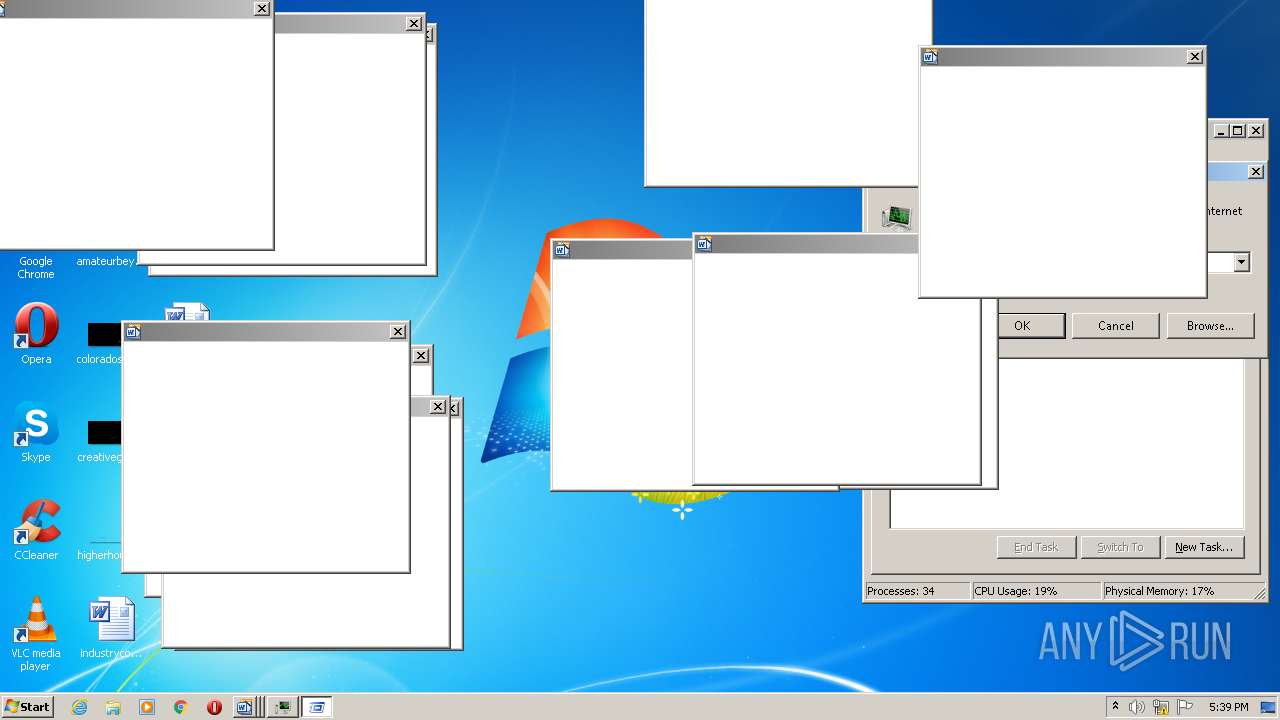
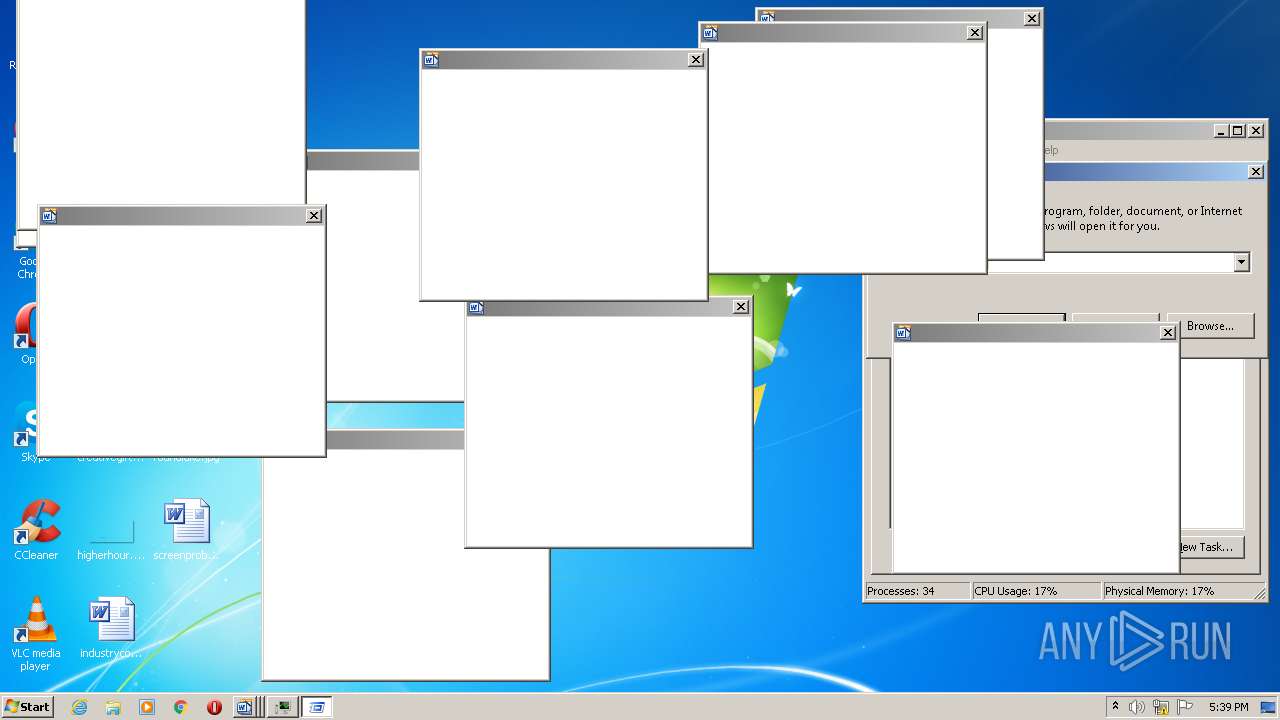
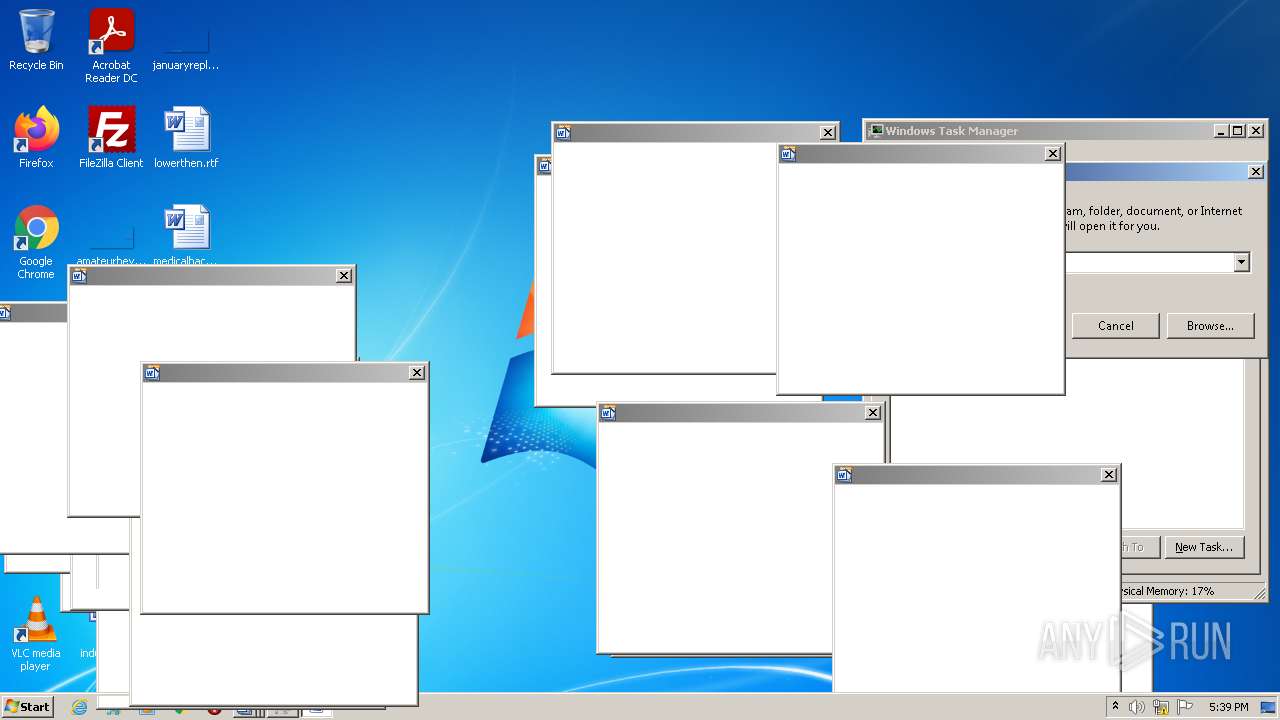
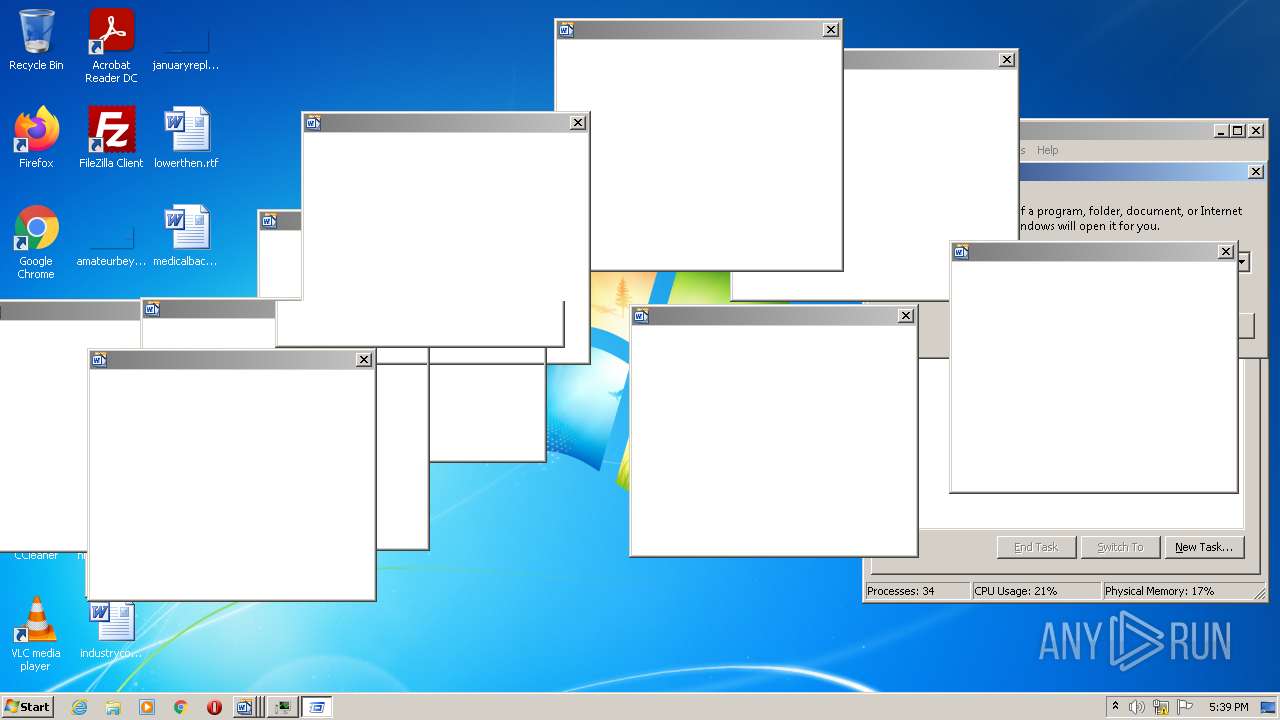
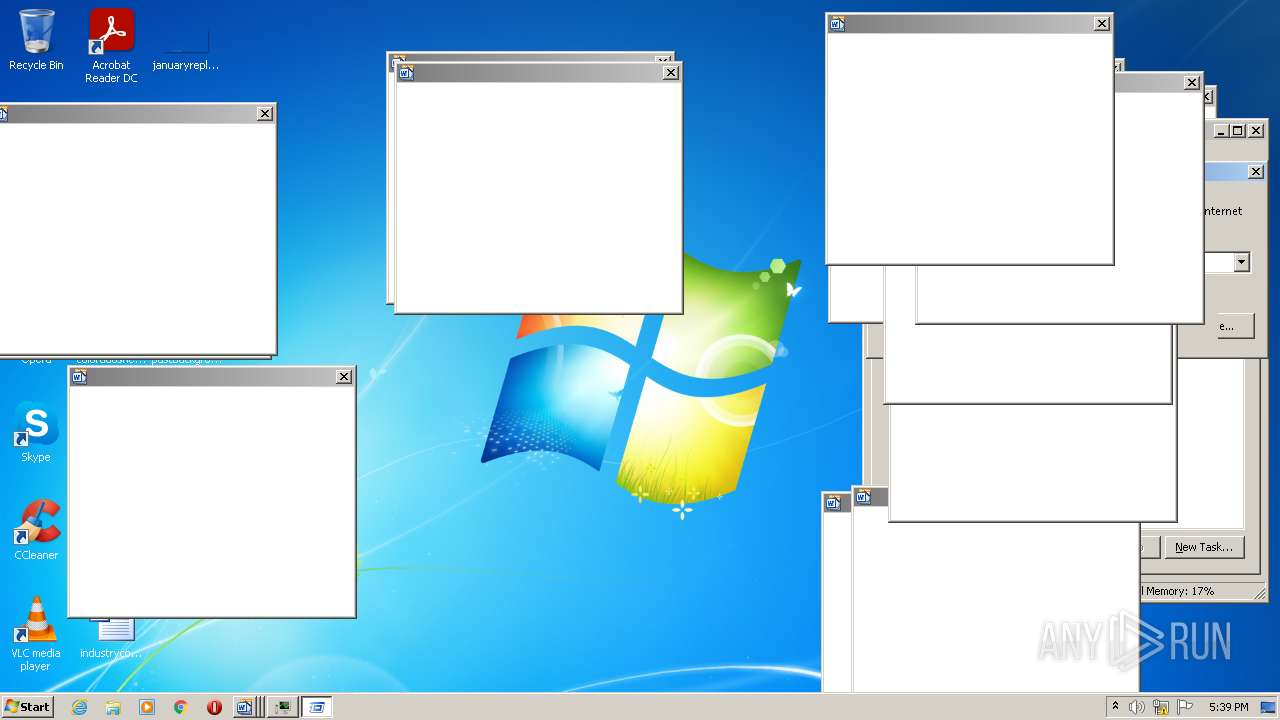
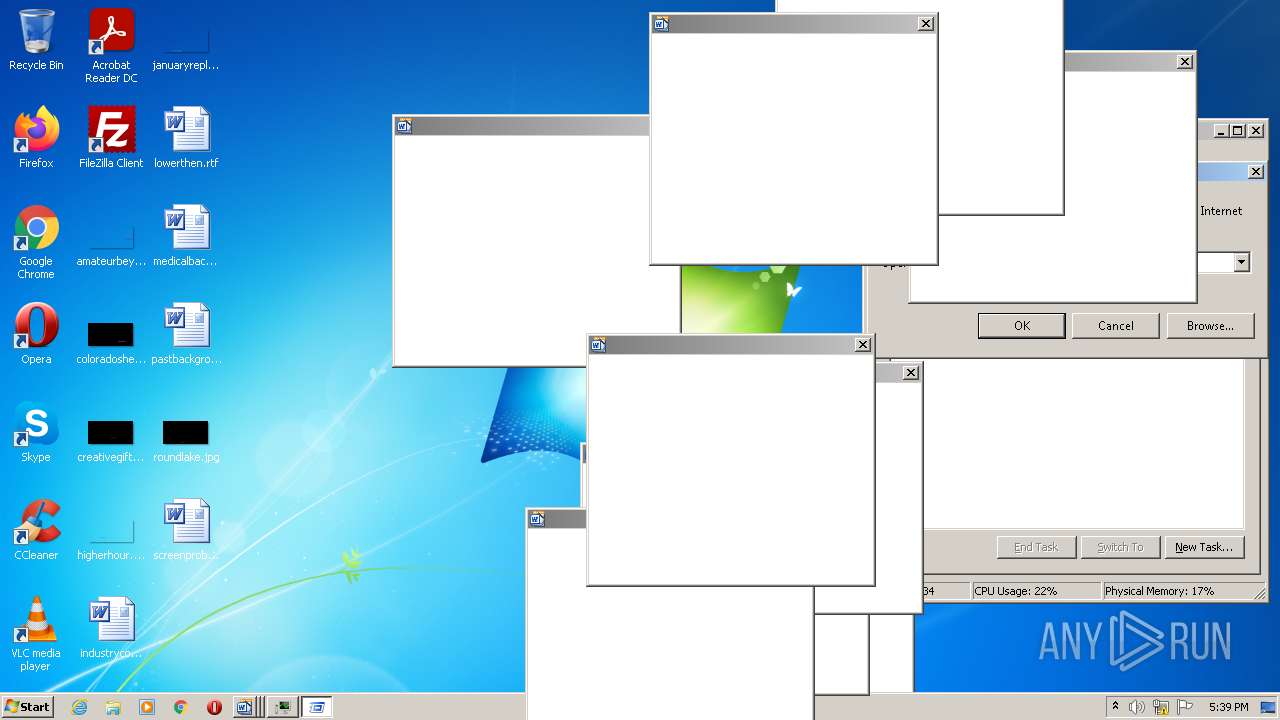
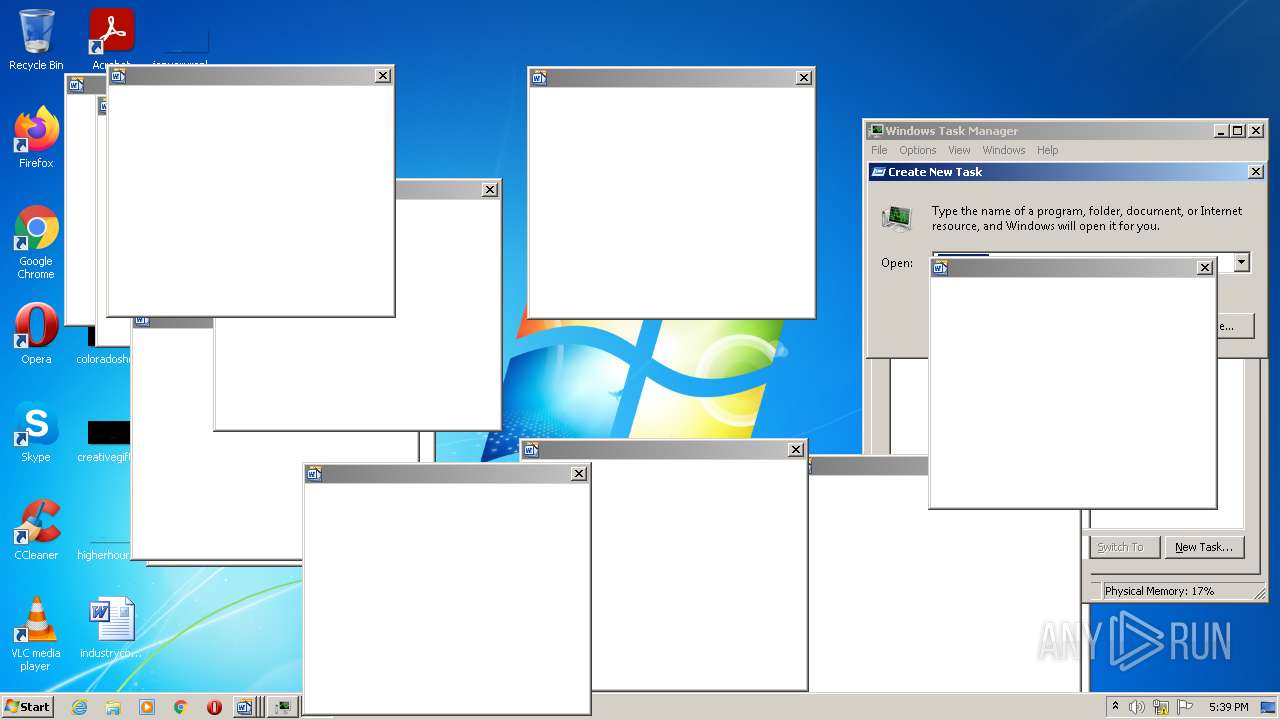
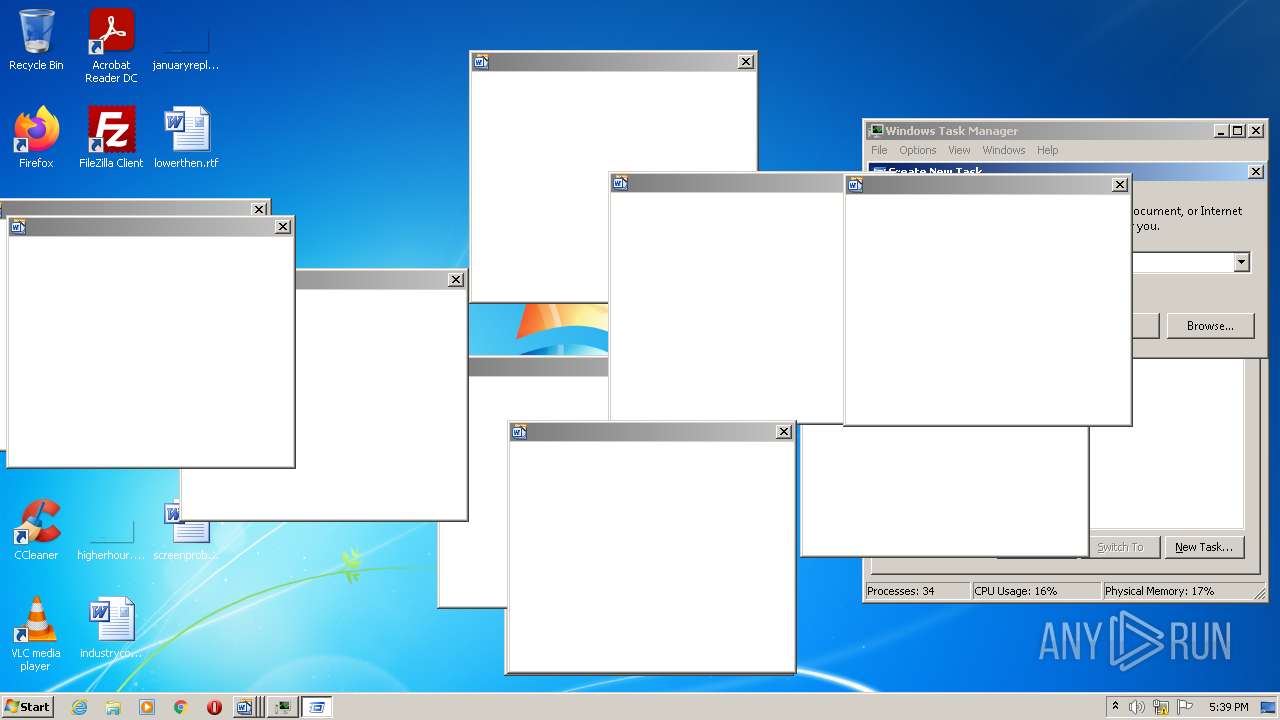
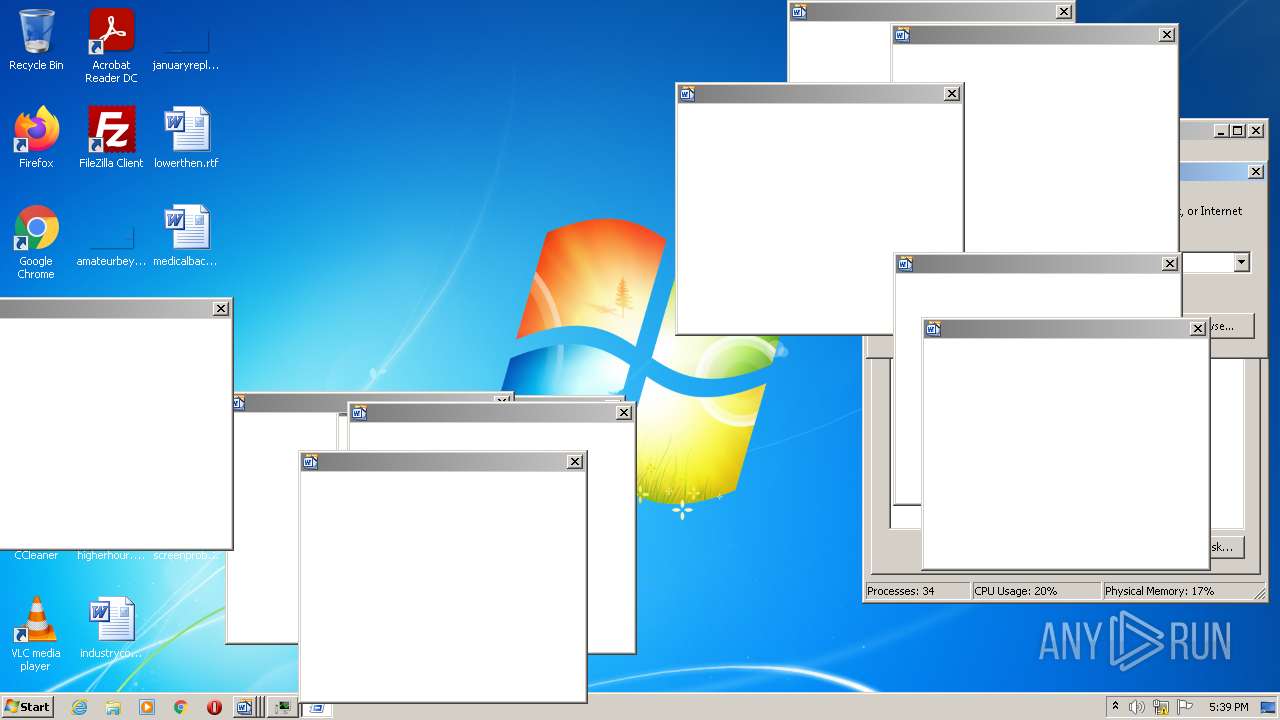
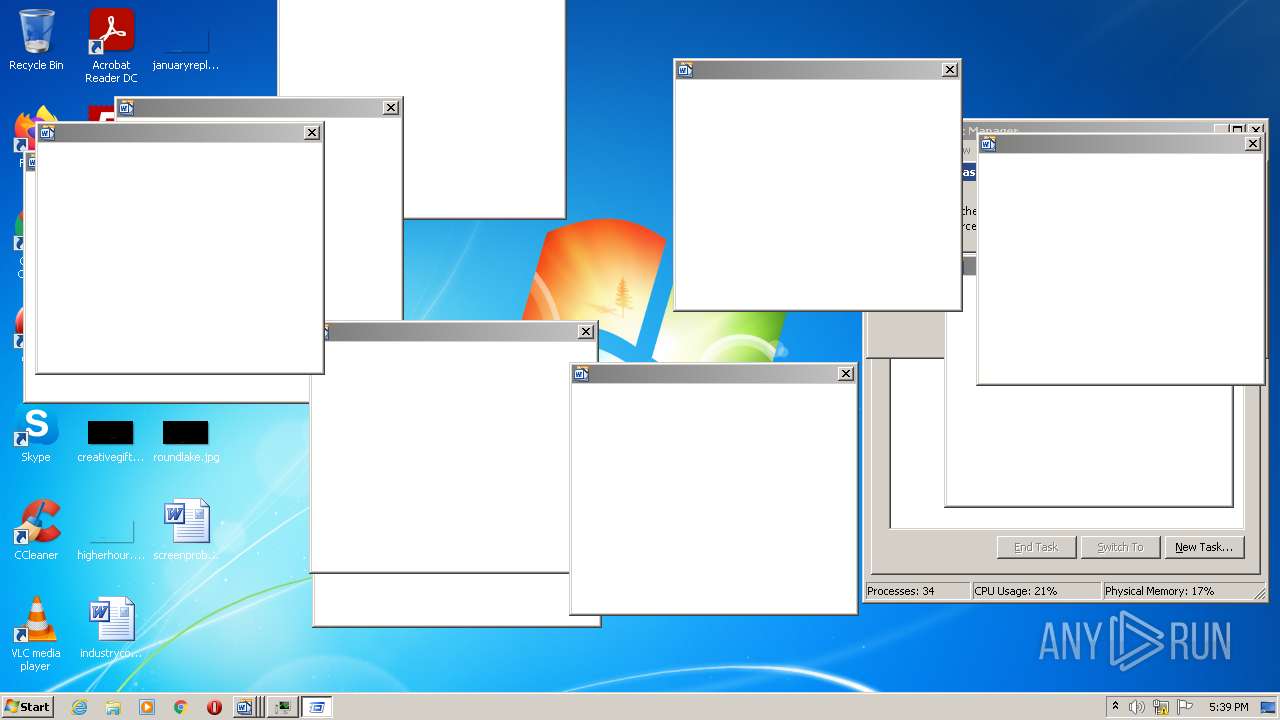
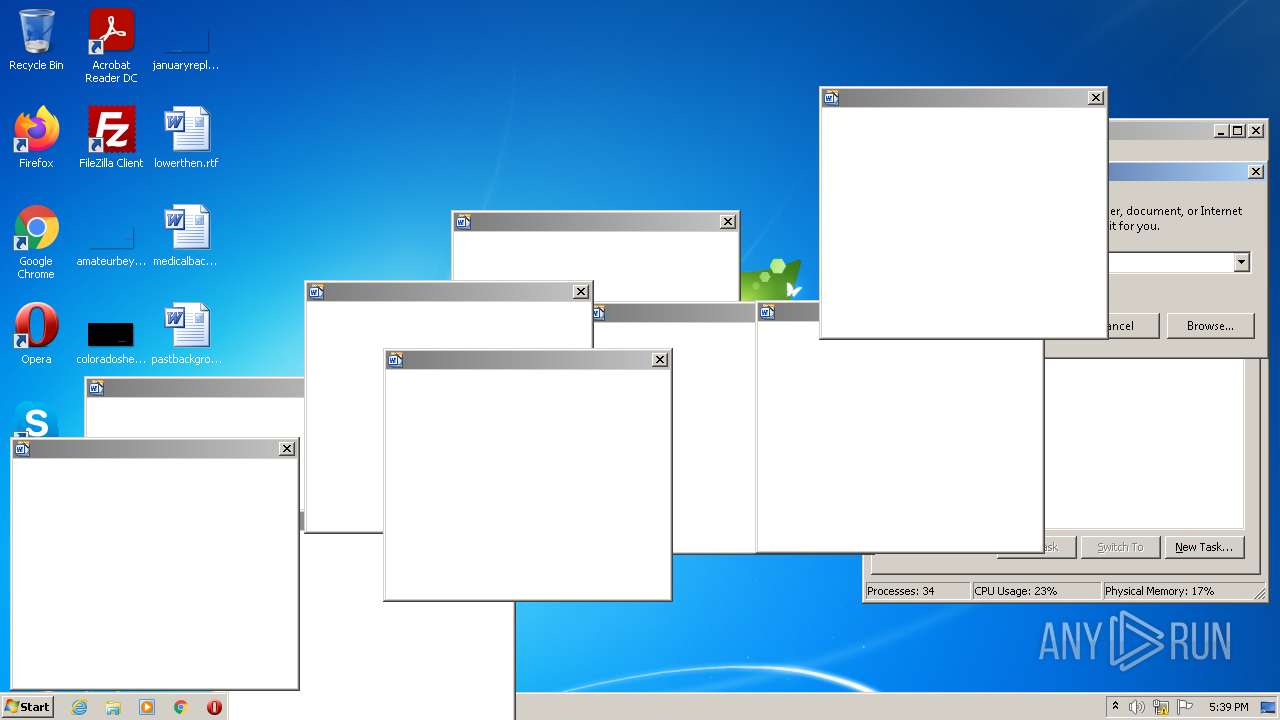
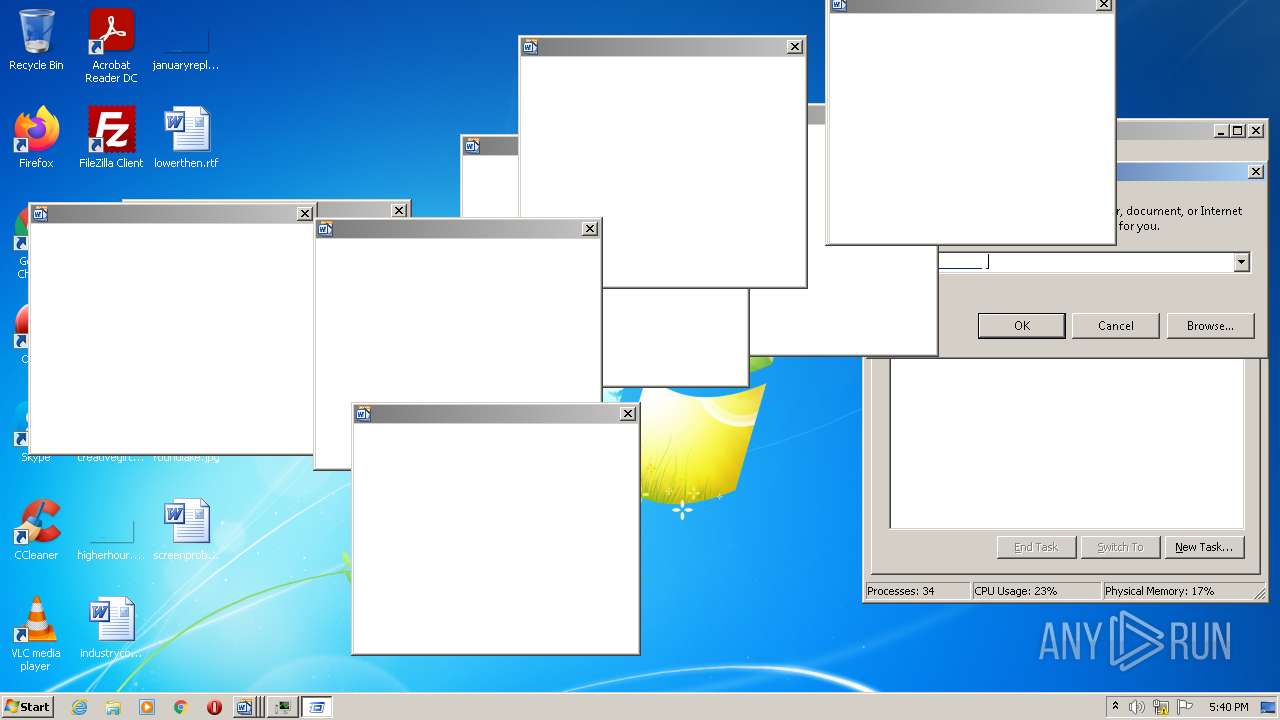
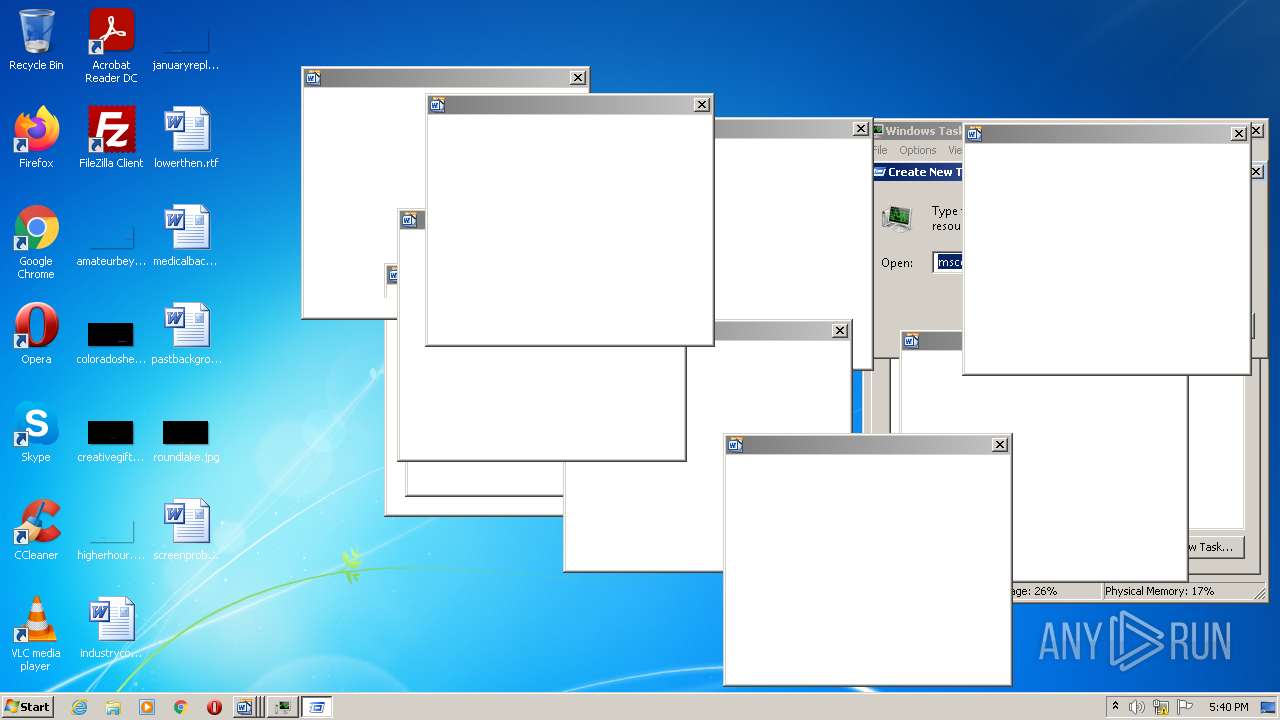
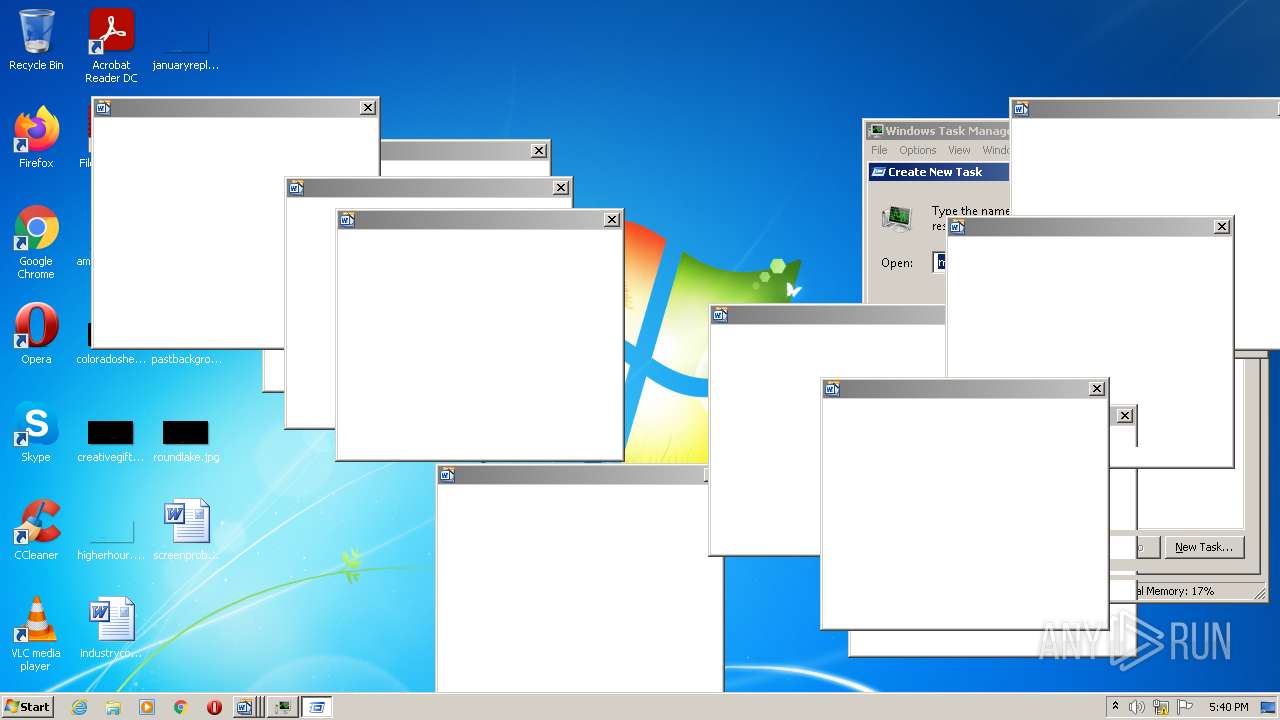
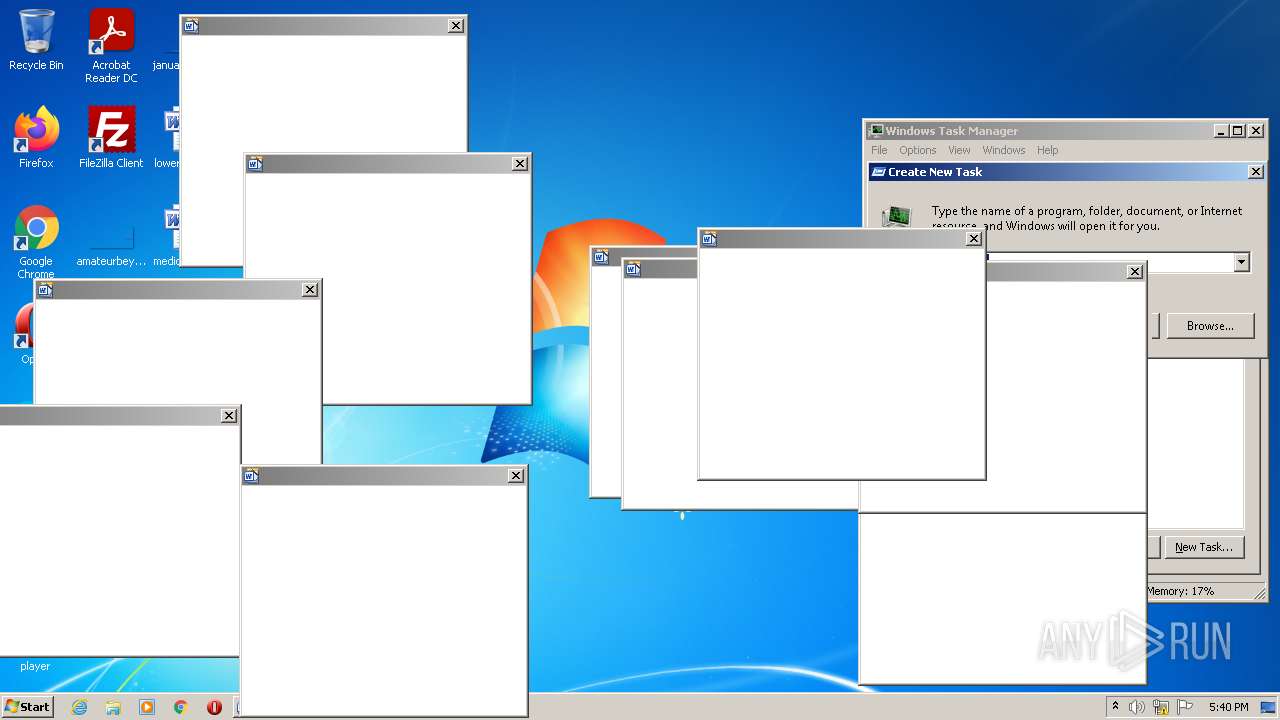
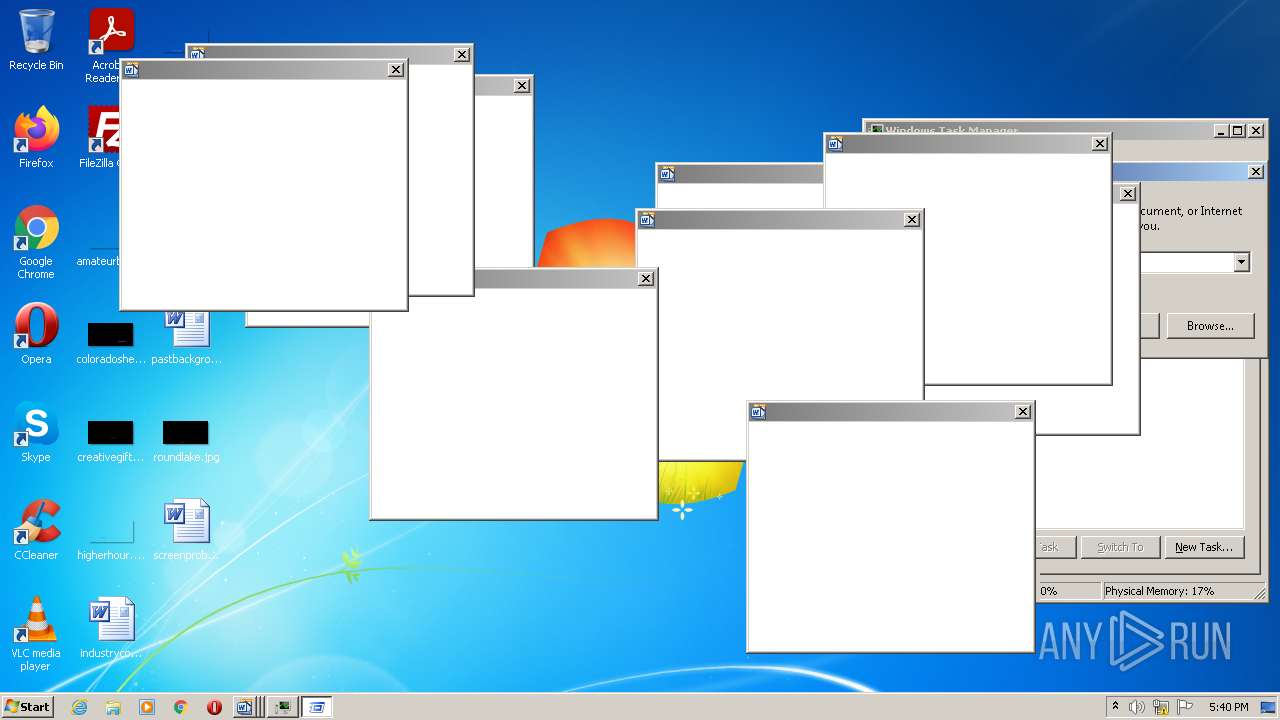
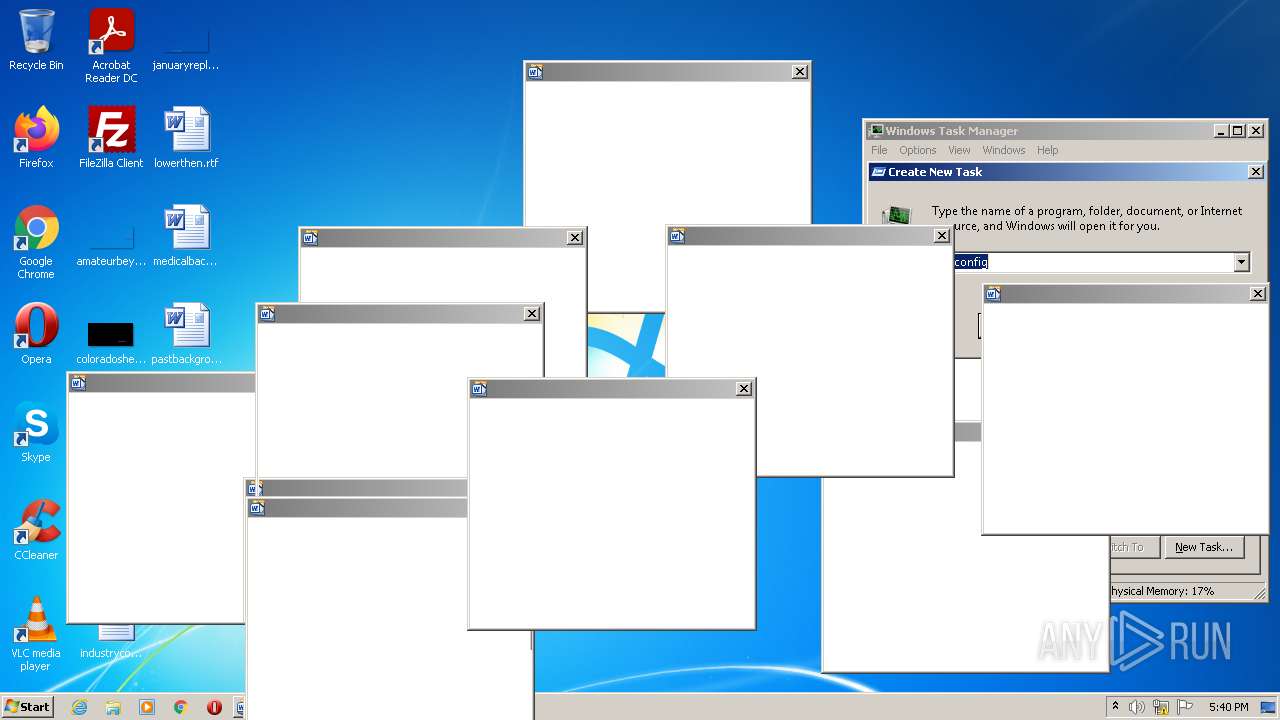
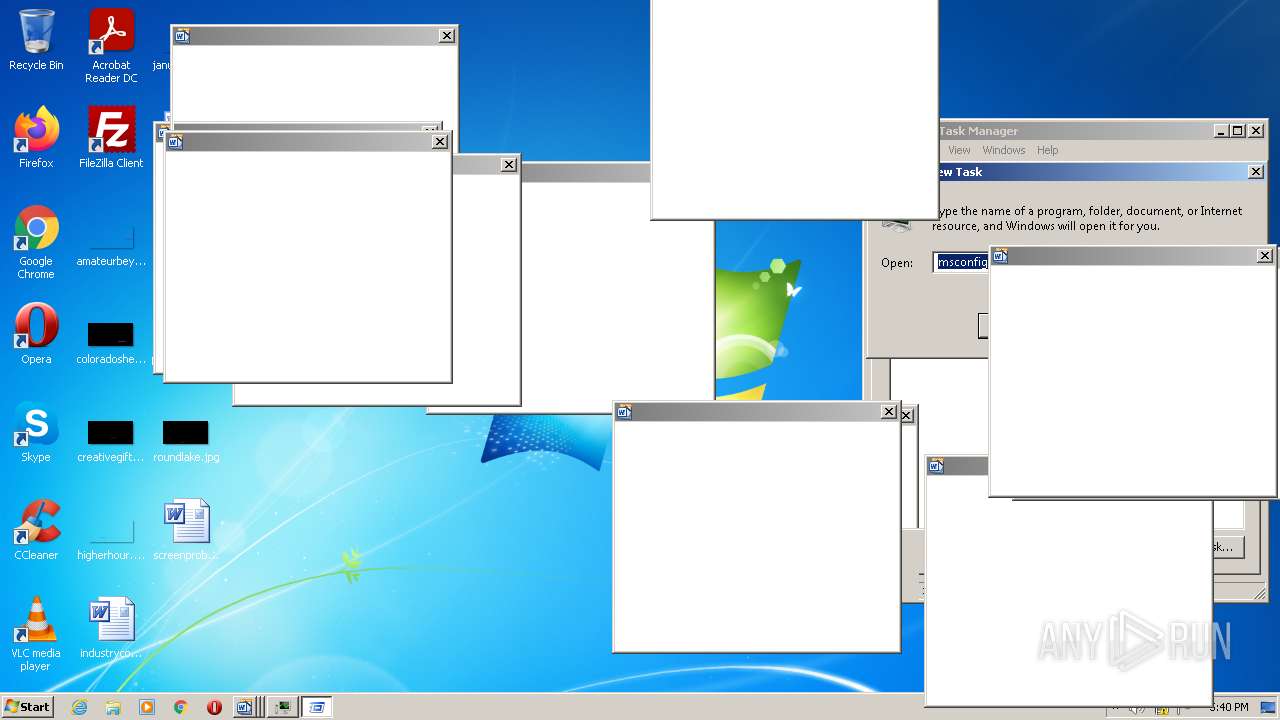
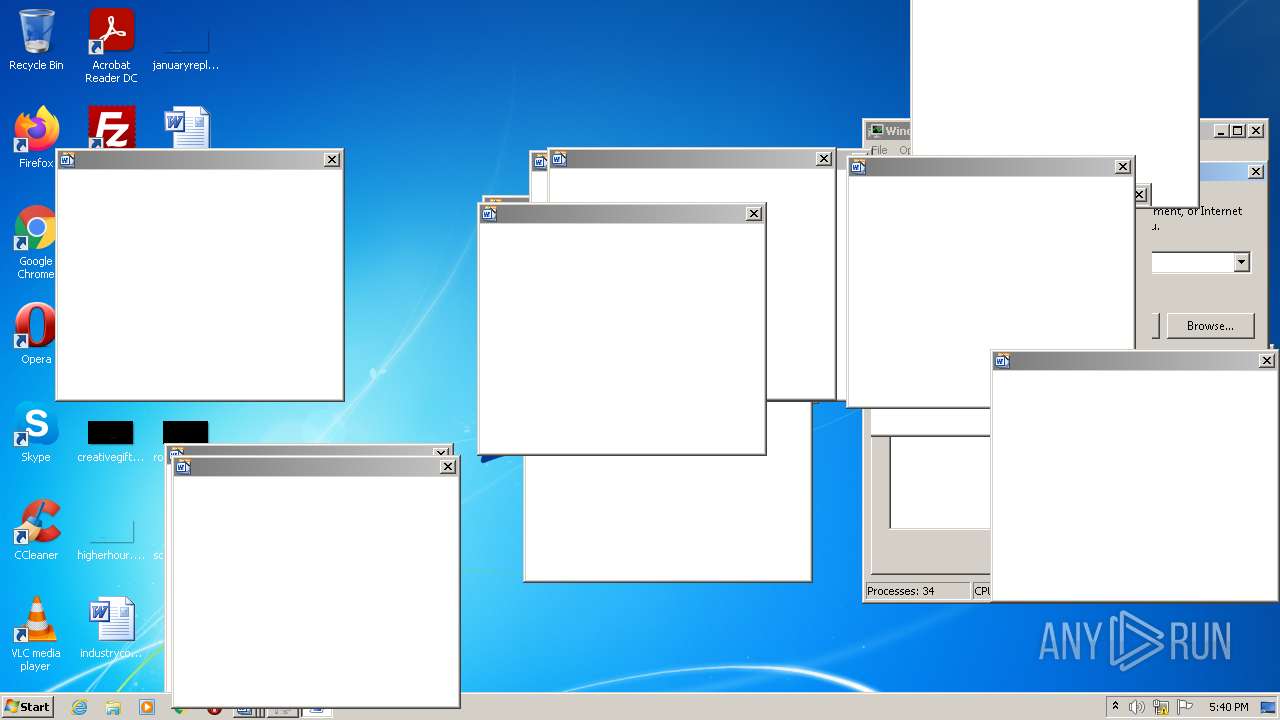
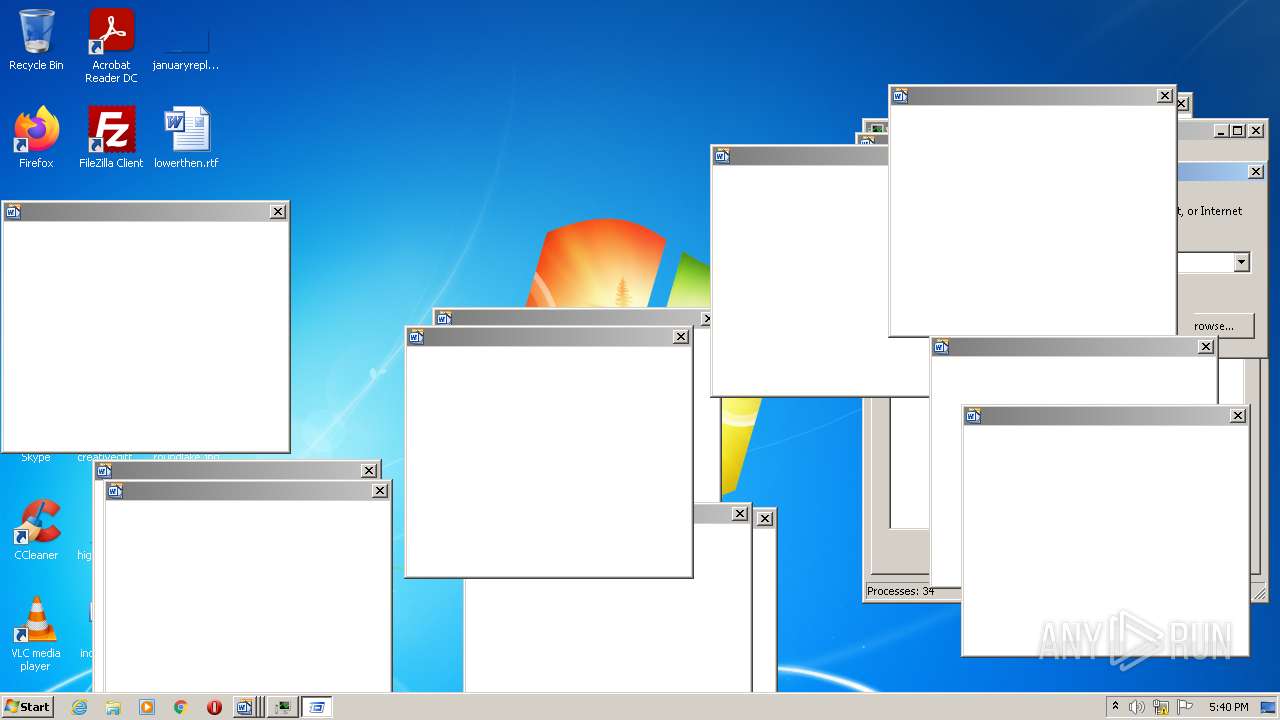
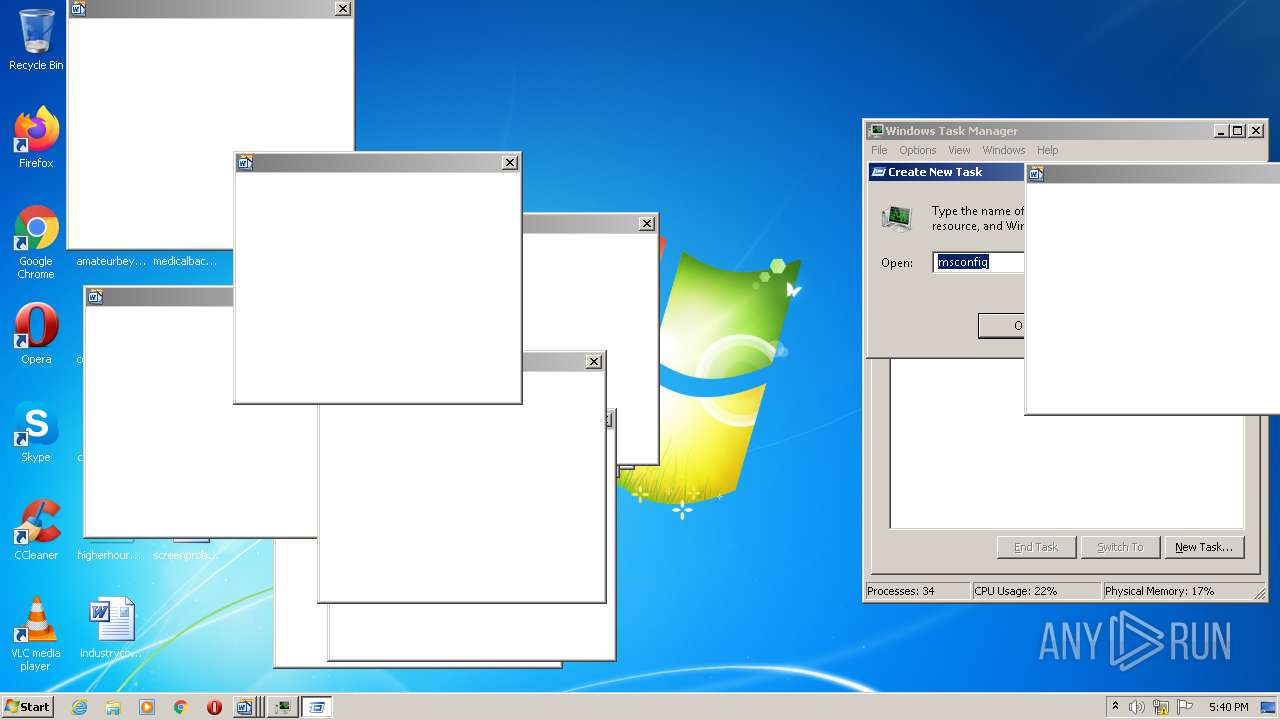
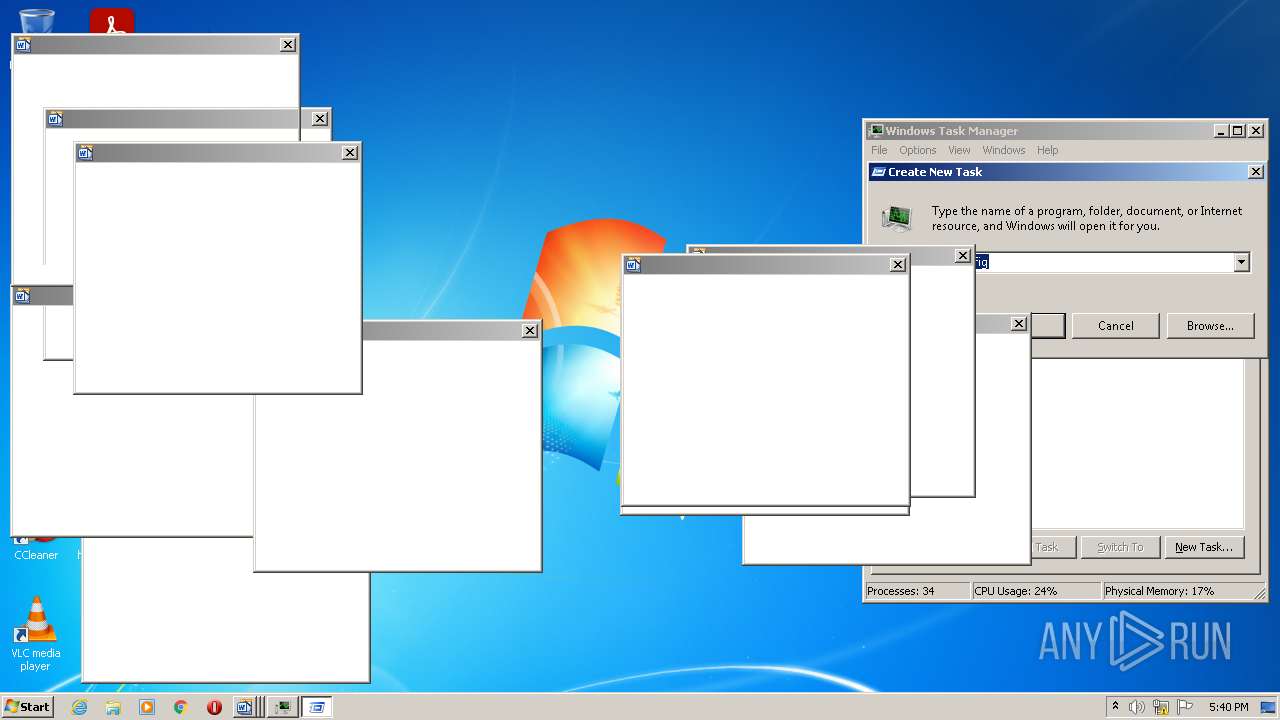
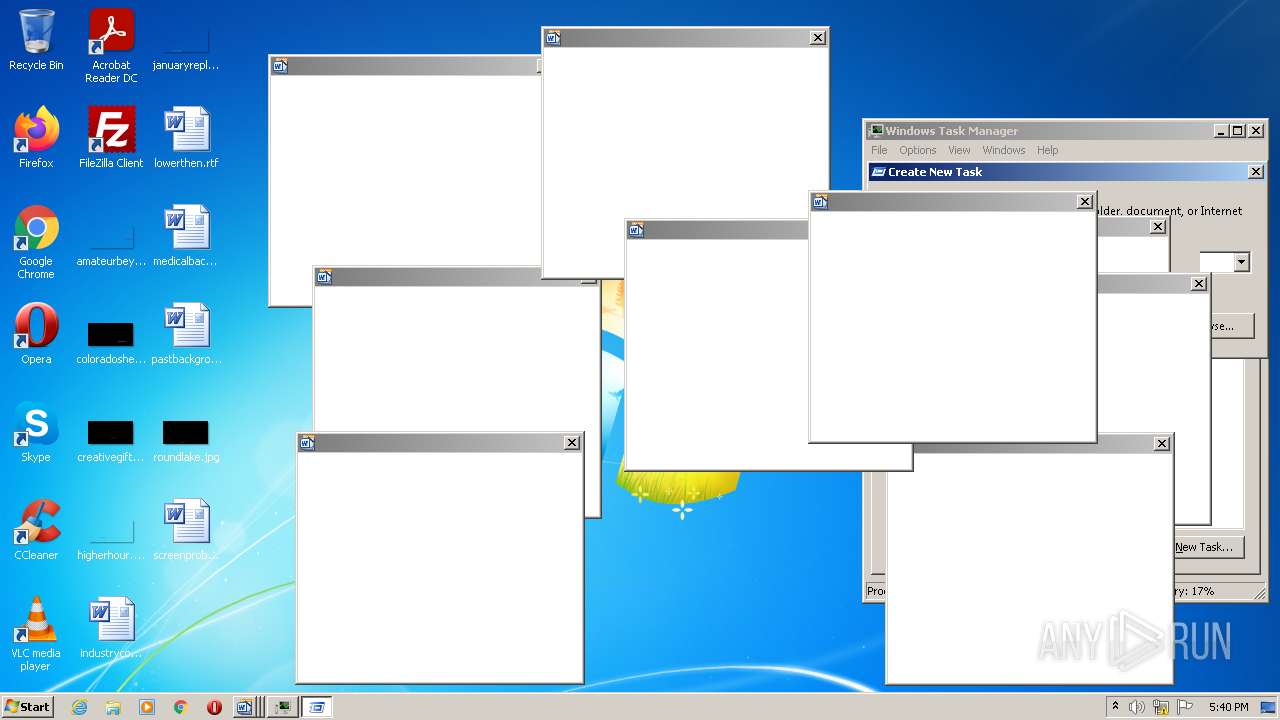
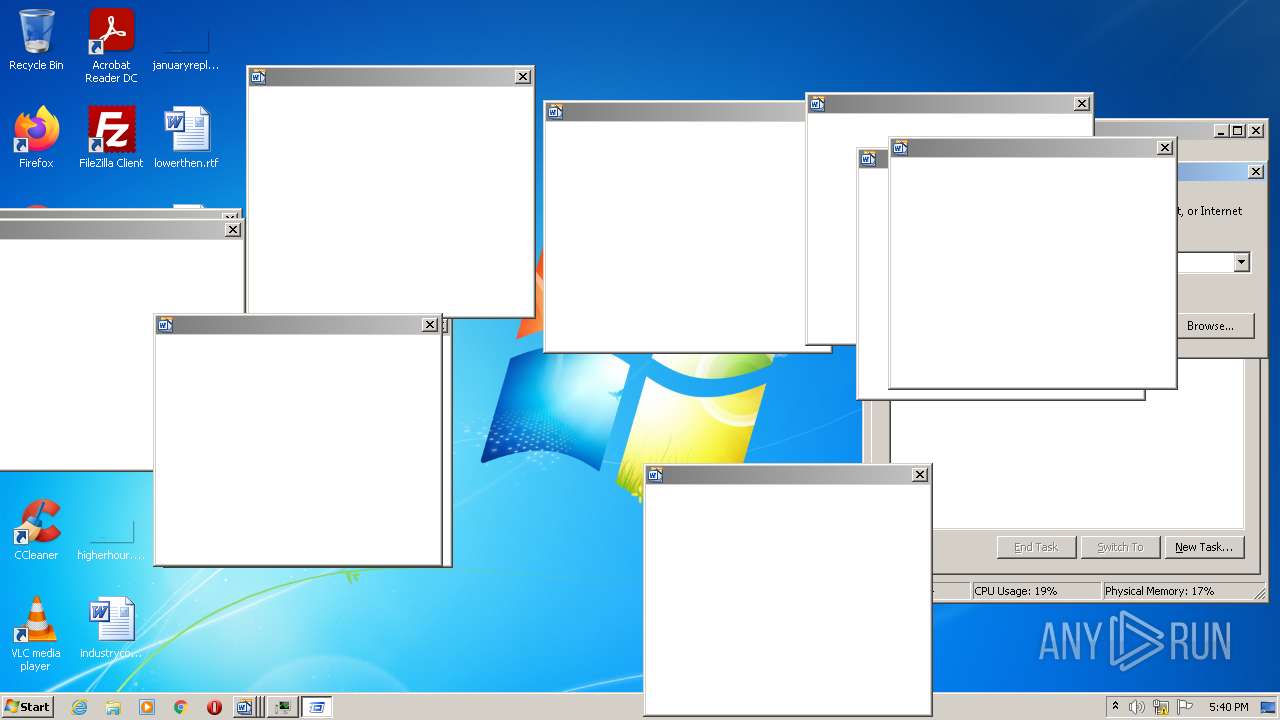
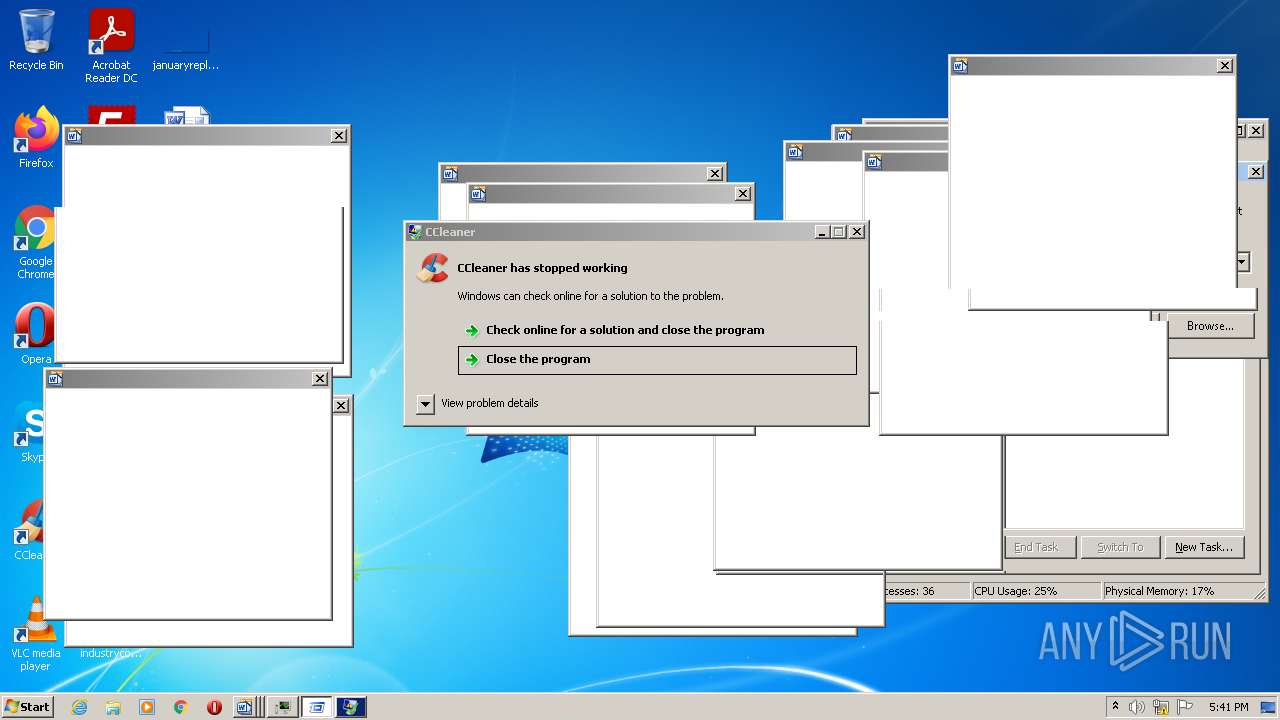
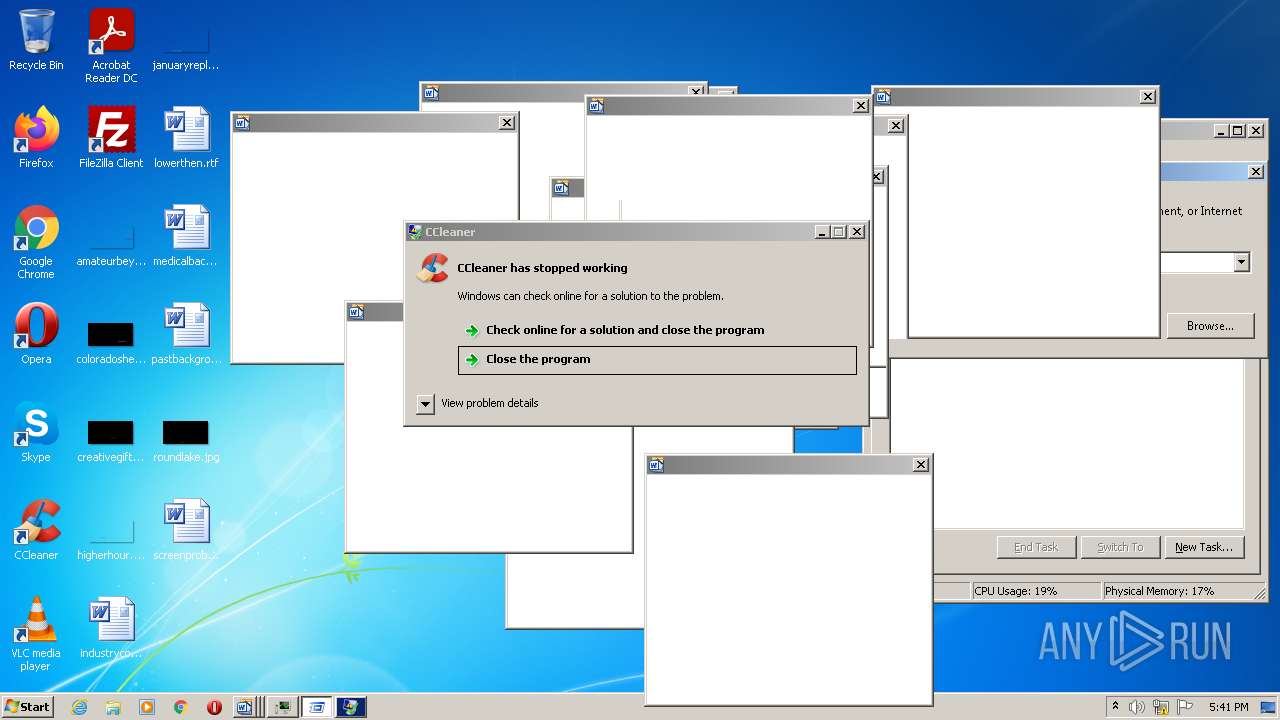
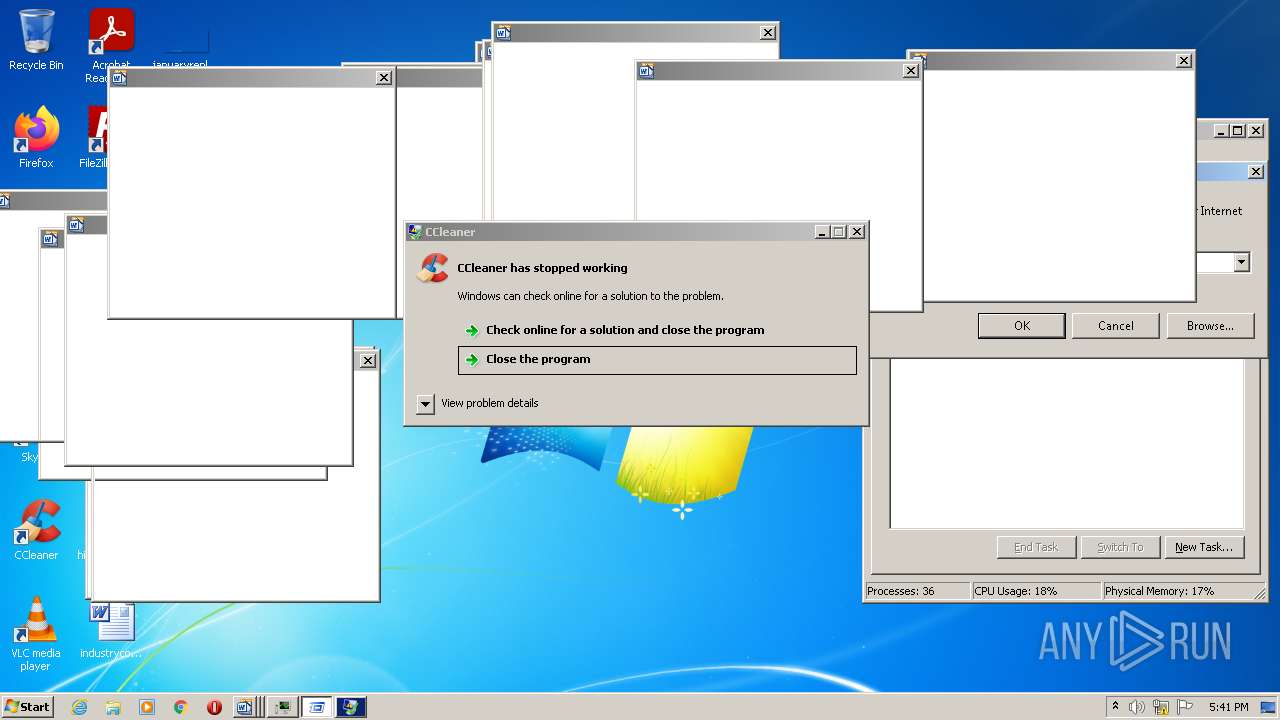
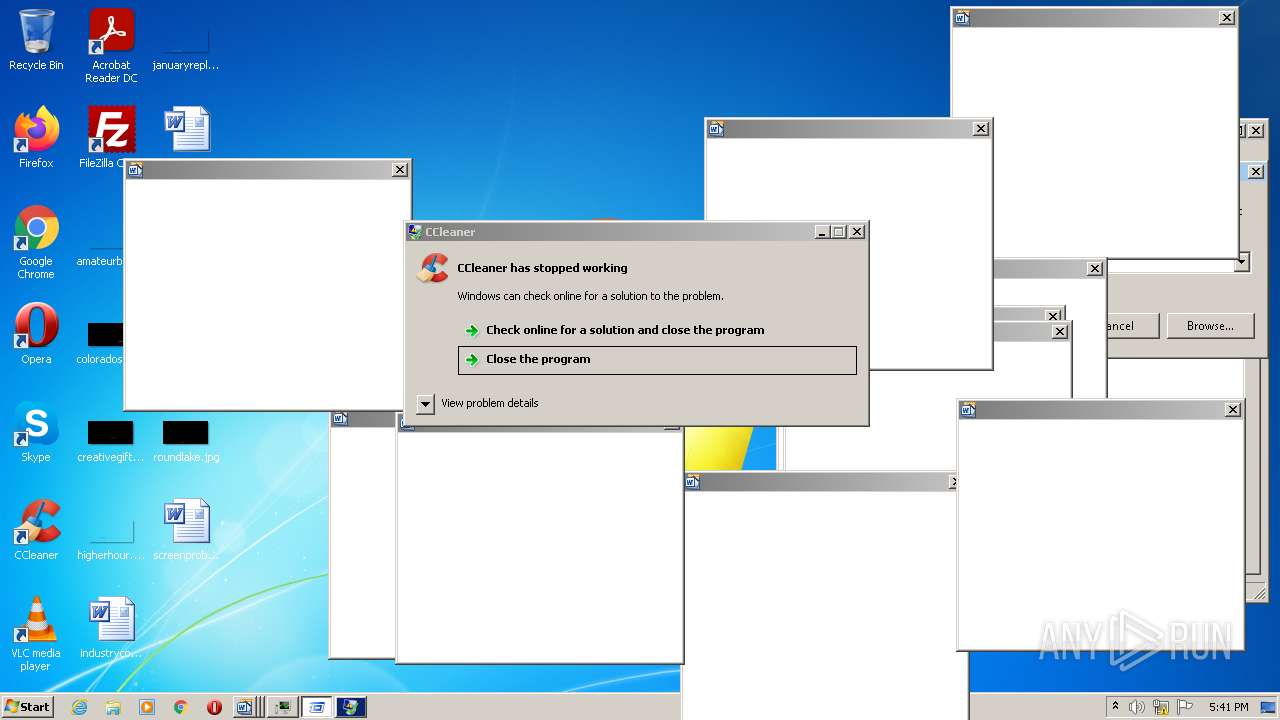
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
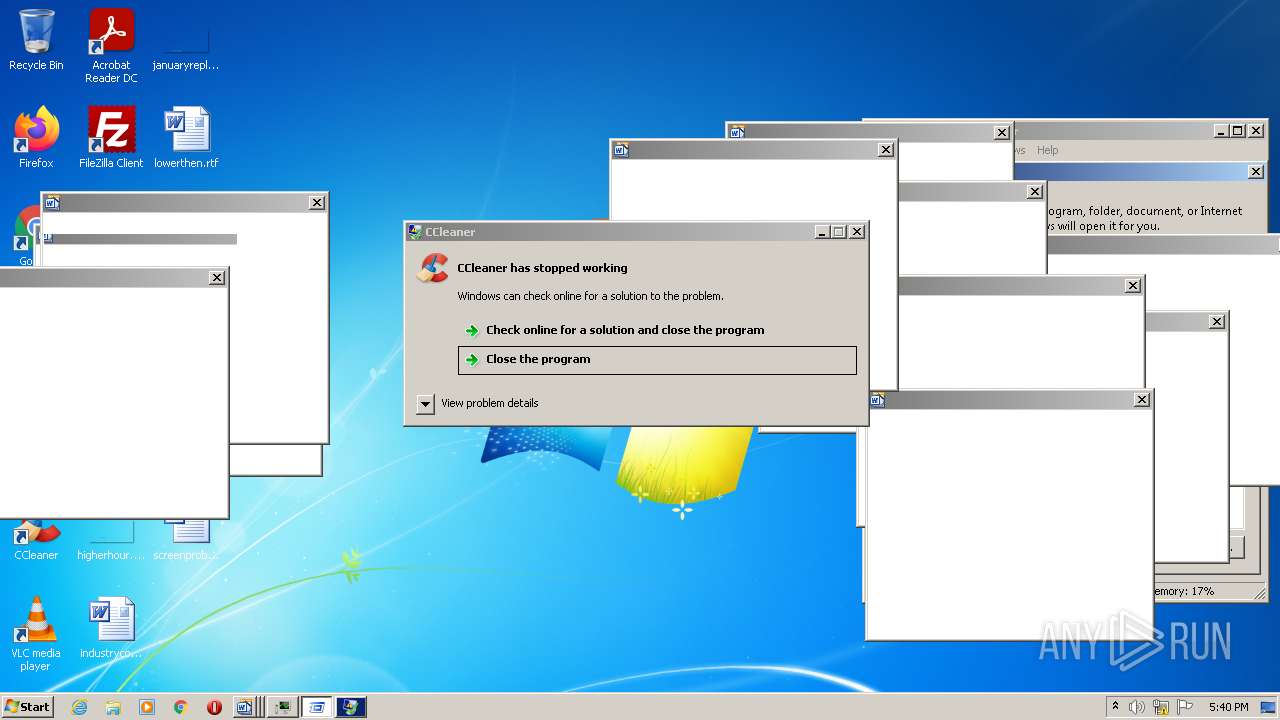
| 1304 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 1492 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1700 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
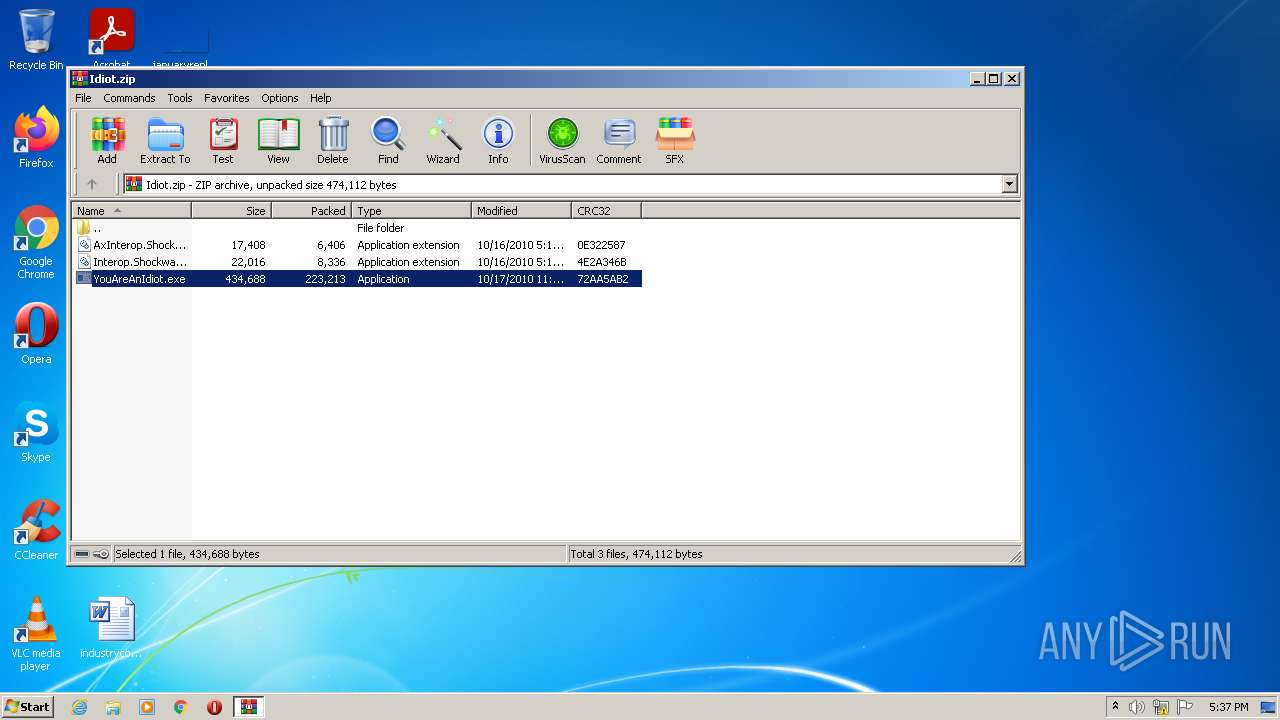
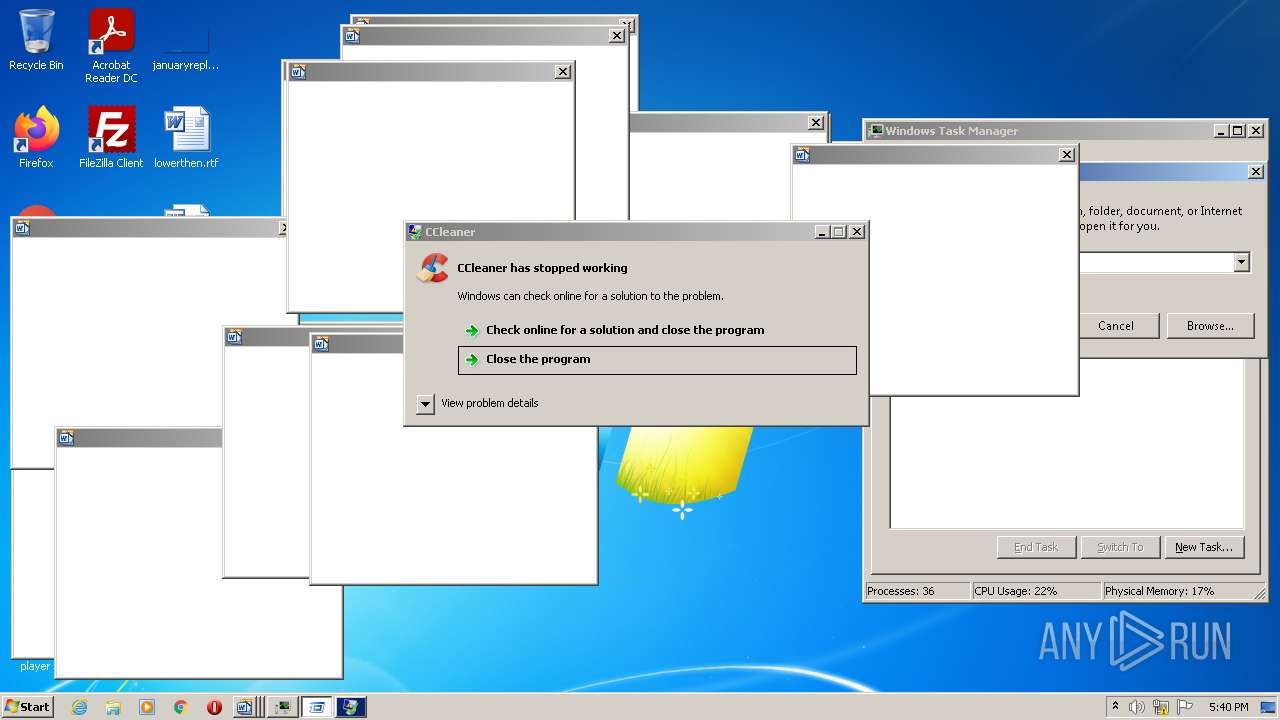
| 2028 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3736.19955\YouAreAnIdiot.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3736.19955\YouAreAnIdiot.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Microsoft Word 2010 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 2380 | C:\Windows\system32\DllHost.exe /Processid:{3EB3C877-1F16-487C-9050-104DBCD66683} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2612 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3044 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3568 | "C:\Windows\system32\taskmgr.exe" | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3736 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Idiot.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
56 057
Read events
55 607
Write events
335
Delete events
115
Modification events
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Idiot.zip | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
7
Suspicious files
17
Text files
11
Unknown types
93
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2360 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ed7a5cc3cca8d52a.customDestinations-ms | — | |
MD5:— | SHA256:— | |||
| 3976 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0WVMP8JDW9N4ECOX1RYI.temp | binary | |
MD5:— | SHA256:— | |||
| 2360 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UZTWU554KVCTZWLFVXIT.temp | binary | |
MD5:— | SHA256:— | |||
| 3976 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_B514E3306E9B5CC22C1D3DB90570477A | der | |
MD5:— | SHA256:— | |||
| 3736 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3736.19955\AxInterop.ShockwaveFlashObjects.dll | executable | |
MD5:451112D955AF4FE3C0D00F303D811D20 | SHA256:0D57A706D4E10CCA3AED49B341A651F29046F5EF1328878D616BE93C3B4CBCE9 | |||
| 3976 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3976 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ed7a5cc3cca8d52a.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3976 | CCleaner.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\auto[1].txt | text | |
MD5:— | SHA256:— | |||
| 3976 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_B514E3306E9B5CC22C1D3DB90570477A | binary | |
MD5:— | SHA256:— | |||
| 2028 | YouAreAnIdiot.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\openssl\cache\RevocationCacheFile.dat | gmc | |
MD5:0F343B0931126A20F133D67C2B018A3B | SHA256:5F70BF18A086007016E948B04AED3B82103A36BEA41755B6CDDFAF10ACE3C6EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
41
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2360 | CCleaner.exe | GET | 200 | 104.109.59.7:80 | http://license.piriform.com/verify/?p=ccpro&c=cc&cv=5.74.8198&l=1033&lk=CJ9T-J7CU-SPNV-GWMB-WBEC&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | NL | text | 14 b | whitelisted |
2028 | YouAreAnIdiot.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3976 | CCleaner.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/auto?a=0&p=cc&v=5.74.8198&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&o=6.1W3&au=0&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | US | text | 61 b | whitelisted |
3976 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3976 | CCleaner.exe | GET | 200 | 104.109.59.7:80 | http://license.piriform.com/verify/?p=ccpro&c=cc&cv=5.74.8198&l=1033&lk=CJ9T-J7CU-SPNV-GWMB-WBEC&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | NL | text | 14 b | whitelisted |
3976 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
3976 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2360 | CCleaner.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
2360 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2028 | YouAreAnIdiot.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2028 | YouAreAnIdiot.exe | 184.87.212.144:443 | geo2.adobe.com | Bharti Airtel Ltd., Telemedia Services | US | unknown |
2028 | YouAreAnIdiot.exe | 104.92.97.41:443 | fpdownload.macromedia.com | Akamai Technologies, Inc. | NL | unknown |
2360 | CCleaner.exe | 5.62.40.211:443 | analytics.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
2028 | YouAreAnIdiot.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3976 | CCleaner.exe | 151.101.2.202:80 | www.ccleaner.com | Fastly | US | suspicious |
3976 | CCleaner.exe | 5.62.45.68:443 | ipm-provider.ff.avast.com | AVAST Software s.r.o. | US | suspicious |
3976 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
3976 | CCleaner.exe | 92.123.225.56:80 | ncc.avast.com | Akamai International B.V. | — | suspicious |
3976 | CCleaner.exe | 67.26.81.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2360 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geo2.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fpdownload.macromedia.com |
| whitelisted |
ncc.avast.com |
| whitelisted |
analytics.ff.avast.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ipm-provider.ff.avast.com |
| whitelisted |
shepherd.ff.avast.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3976 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2360 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
Process | Message |
|---|---|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | Using Sciter version 4.4.4.4-r8057
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | observing CurrentIndex changed - 0
|
CCleaner.exe | observing CurrentIndex changed - Context.FirstTime=true CurrentIndex=0 LastIndex=4
|
CCleaner.exe | observing currentResultDetails changed - None
|
CCleaner.exe | SetStrings - Live Region updated: ,
|