| File name: | Gerador de Crypter anonymous rat V4.exe |
| Full analysis: | https://app.any.run/tasks/5550ec13-8a56-49e0-bbae-985fa8ce4d68 |
| Verdict: | Malicious activity |
| Analysis date: | October 17, 2018, 21:49:29 |
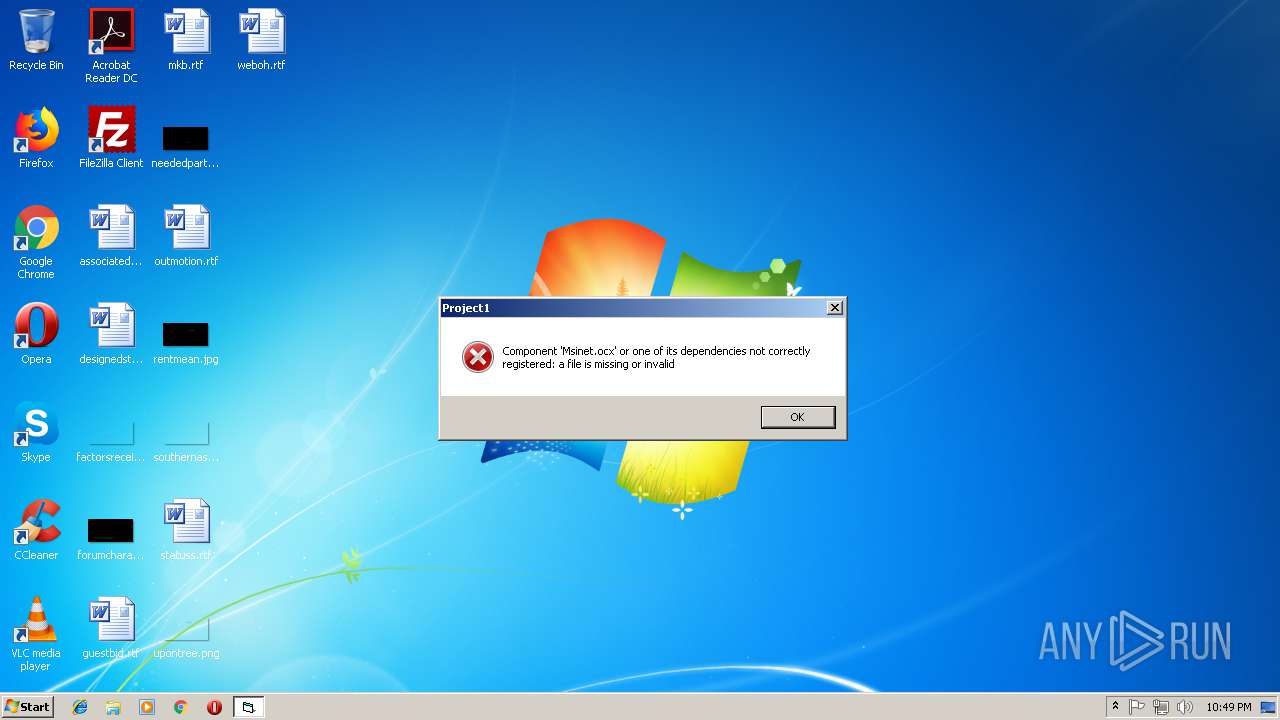
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 76B9FE5901E8350140F4560D3CCBEB62 |
| SHA1: | C5B5F8C32D1FC83A8376AE216C3C059E2291C5C3 |
| SHA256: | AC221A15B572DAEE6956CF41892AAE44EA8D9B7BEF954CB378B2738E7B6E1920 |
| SSDEEP: | 24576:LNBI0w/93q5fWwe6/zb+kTYXgW3ySd1X+0+y6S+JM24bh5T270JBRttEdc:UrNq5fWczKkTYX3yku0+STbh5i0JnEW |
MALICIOUS
Changes the autorun value in the registry
- 22W2W2W2W2W22W.exe (PID: 3992)
Application was dropped or rewritten from another process
- 22W2W2W2W2W22W.exe (PID: 3992)
- Grador de Crypter anonymous rat V4.exe (PID: 1716)
- 22W2W2W2W2W22W.exe (PID: 4000)
- explorer.exe (PID: 3792)
- explorer.exe (PID: 844)
- 22W2W2W2W2W22W.exe (PID: 3544)
Runs injected code in another process
- 22W2W2W2W2W22W.exe (PID: 3992)
Application was injected by another process
- explorer.exe (PID: 1604)
SUSPICIOUS
Application launched itself
- 22W2W2W2W2W22W.exe (PID: 3544)
- 22W2W2W2W2W22W.exe (PID: 3992)
- explorer.exe (PID: 3792)
Executable content was dropped or overwritten
- 22W2W2W2W2W22W.exe (PID: 3992)
- Gerador de Crypter anonymous rat V4.exe (PID: 3428)
Creates executable files which already exist in Windows
- 22W2W2W2W2W22W.exe (PID: 3992)
Creates files in the user directory
- 22W2W2W2W2W22W.exe (PID: 3992)
- 22W2W2W2W2W22W.exe (PID: 4000)
Starts itself from another location
- 22W2W2W2W2W22W.exe (PID: 3992)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:01 09:08:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 153088 |
| InitializedDataSize: | 39424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d728 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Dec-2013 08:08:23 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 01-Dec-2013 08:08:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000254E8 | 0x00025600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69647 |
.rdata | 0x00027000 | 0x00004F33 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.31236 |
.data | 0x0002C000 | 0x000215E0 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.54741 |
.rsrc | 0x0004E000 | 0x0000345C | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49148 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22792 | 1600 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.18906 | 536 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 2.95673 | 288 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.77928 | 186 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.66523 | 162 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
38
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | "C:\Users\admin\AppData\Roaming\install\explorer.exe" | C:\Users\admin\AppData\Roaming\install\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Dropbox , Inc. Integrity Level: MEDIUM Description: Dropbox , Inc. Exit code: 0 Version: 5.06.0003 Modules
| |||||||||||||||
| 1604 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1716 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\Grador de Crypter anonymous rat V4.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\Grador de Crypter anonymous rat V4.exe | — | Gerador de Crypter anonymous rat V4.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3428 | "C:\Users\admin\AppData\Local\Temp\Gerador de Crypter anonymous rat V4.exe" | C:\Users\admin\AppData\Local\Temp\Gerador de Crypter anonymous rat V4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1000 Modules
| |||||||||||||||
| 3544 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\22W2W2W2W2W22W.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\22W2W2W2W2W22W.exe | — | Gerador de Crypter anonymous rat V4.exe | |||||||||||
User: admin Company: Dropbox , Inc. Integrity Level: MEDIUM Description: Dropbox , Inc. Exit code: 3221225547 Version: 5.06.0003 Modules
| |||||||||||||||
| 3792 | "C:\Users\admin\AppData\Roaming\install\explorer.exe" | C:\Users\admin\AppData\Roaming\install\explorer.exe | — | 22W2W2W2W2W22W.exe | |||||||||||
User: admin Company: Dropbox , Inc. Integrity Level: MEDIUM Description: Dropbox , Inc. Exit code: 3221225547 Version: 5.06.0003 Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\22W2W2W2W2W22W.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\22W2W2W2W2W22W.exe | 22W2W2W2W2W22W.exe | ||||||||||||
User: admin Company: Dropbox , Inc. Integrity Level: MEDIUM Description: Dropbox , Inc. Exit code: 0 Version: 5.06.0003 Modules
| |||||||||||||||
| 4000 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\22W2W2W2W2W22W.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\22W2W2W2W2W22W.exe | 22W2W2W2W2W22W.exe | ||||||||||||
User: admin Company: Dropbox , Inc. Integrity Level: MEDIUM Description: Dropbox , Inc. Exit code: 0 Version: 5.06.0003 Modules
| |||||||||||||||
Total events
1 084
Read events
1 066
Write events
16
Delete events
2
Modification events
| (PID) Process: | (3428) Gerador de Crypter anonymous rat V4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3428) Gerador de Crypter anonymous rat V4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3544) 22W2W2W2W2W22W.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{C86ED247-AF32-4F23-82CE-90B26C7CA90B} |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3992) 22W2W2W2W2W22W.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Update* |
Value: C:\Users\admin\AppData\Roaming\install\explorer.exe | |||
| (PID) Process: | (3992) 22W2W2W2W2W22W.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Update* |
Value: C:\Users\admin\AppData\Roaming\install\explorer.exe | |||
| (PID) Process: | (3992) 22W2W2W2W2W22W.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{2HS8CB06-OUR7-D06Y-7MRF-10GO2N70564W} |
| Operation: | write | Name: | StubPath |
Value: C:\Users\admin\AppData\Roaming\install\explorer.exe Restart | |||
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\EneFSK0\Tenqbe qr Pelcgre nabalzbhf eng I4.rkr |
Value: 000000000000000000000000F70B0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002500000032000000C68D1000090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000E0000002FCA04007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E006500780065000000740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7A24E800006751EA7AD8E728028291917524E828028CD800007351EA7AECE72802B69C917590D8D4034C06000004E8280200D4D40311000000F0443500E844350040B0C37504E8280220D4D40374E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (4000) 22W2W2W2W2W22W.exe | Key: | HKEY_CURRENT_USER\Software\Hacked |
| Operation: | write | Name: | FirstExecution |
Value: 17/10/2018 -- 22:49 | |||
| (PID) Process: | (4000) 22W2W2W2W2W22W.exe | Key: | HKEY_CURRENT_USER\Software\Hacked |
| Operation: | write | Name: | NewIdentification |
Value: Hacked | |||
Executable files
3
Suspicious files
1
Text files
883
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3428 | Gerador de Crypter anonymous rat V4.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Credits.txt | text | |
MD5:— | SHA256:— | |||
| 3992 | 22W2W2W2W2W22W.exe | C:\Users\admin\AppData\Local\Temp\admin2.txt | binary | |
MD5:— | SHA256:— | |||
| 3428 | Gerador de Crypter anonymous rat V4.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Credits1.txt | text | |
MD5:— | SHA256:— | |||
| 4000 | 22W2W2W2W2W22W.exe | C:\Users\admin\AppData\Roaming\C4BA3647\ak.tmp | text | |
MD5:— | SHA256:— | |||
| 3428 | Gerador de Crypter anonymous rat V4.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Grador de Crypter anonymous rat V4.exe | executable | |
MD5:— | SHA256:— | |||
| 4000 | 22W2W2W2W2W22W.exe | C:\Users\admin\AppData\Local\Temp\admin8 | text | |
MD5:F2F4BFACA4F3F0F11961028310583C32 | SHA256:092AF896284DD9D8719A4DA8697535E109E62808509F7B69E9857AB5E7F0354C | |||
| 3428 | Gerador de Crypter anonymous rat V4.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\22W2W2W2W2W22W.exe | executable | |
MD5:— | SHA256:— | |||
| 4000 | 22W2W2W2W2W22W.exe | C:\Users\admin\AppData\Local\Temp\admin7 | text | |
MD5:F2F4BFACA4F3F0F11961028310583C32 | SHA256:092AF896284DD9D8719A4DA8697535E109E62808509F7B69E9857AB5E7F0354C | |||
| 4000 | 22W2W2W2W2W22W.exe | C:\Users\admin\AppData\Roaming\admin-wchelper.dll | text | |
MD5:CF43D0F929AE3335692D014F4DF05E6D | SHA256:B3EE6953FF49705AE90CE8B2CAFBED7DF9674B227F4AED0279FDF44F358D3E8E | |||
| 3992 | 22W2W2W2W2W22W.exe | C:\Users\admin\AppData\Roaming\install\explorer.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft.aliveddns.com.br |
| unknown |