| File name: | 1.rtf |
| Full analysis: | https://app.any.run/tasks/d611d676-58ad-44bc-9d12-3bf3840b378c |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 13:29:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 44D3BBCB0051352C62005C1E227C56B6 |
| SHA1: | 65301DE7A9E71C09ADF61562E824DDAC2D8A2615 |
| SHA256: | AC1A5F8919FA46351EA60E1E346186360224C05980F6CCD04824AD87110480DA |
| SSDEEP: | 192:vuhg2qu1ovuGHlqJZSzrjNk2B0CS7nNcL0fJki2MJ9Uh7bdOr4yk9c/tVt:GZG5AcvjerCS7s03uZ4Rk9WB |
MALICIOUS
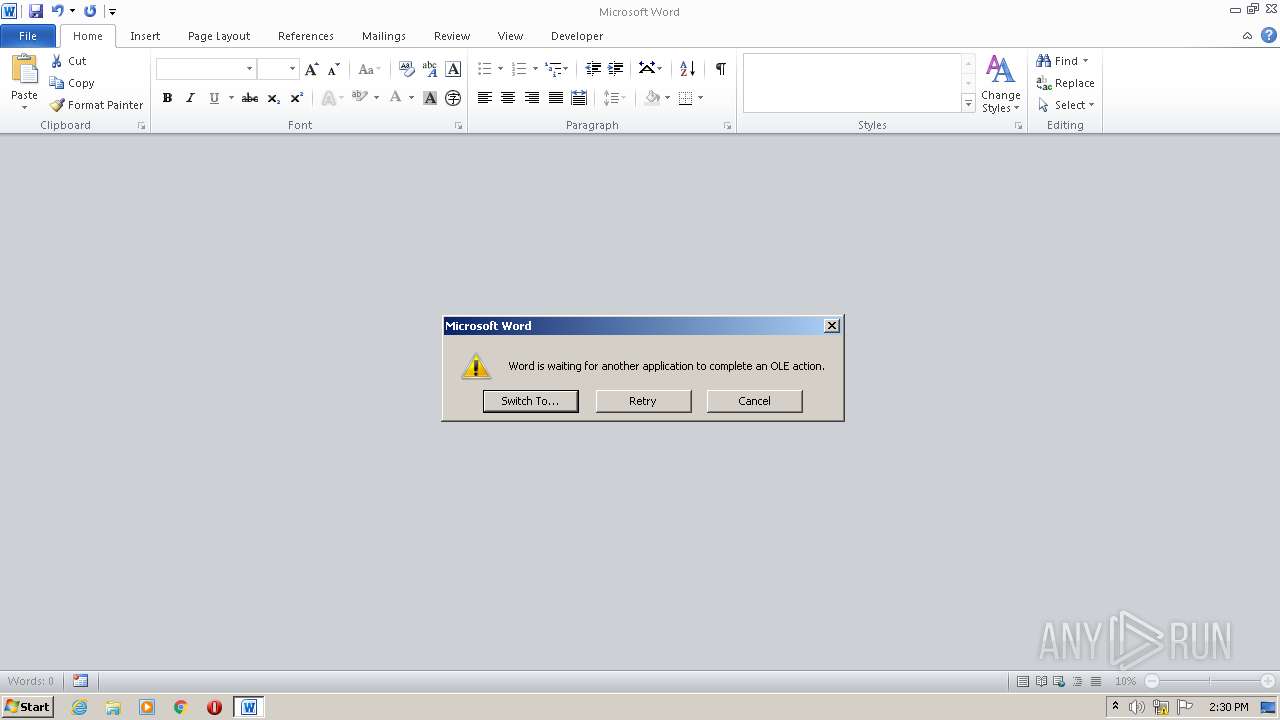
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2220)
SUSPICIOUS
Reads the computer name
- EQNEDT32.EXE (PID: 2360)
Checks supported languages
- EQNEDT32.EXE (PID: 2360)
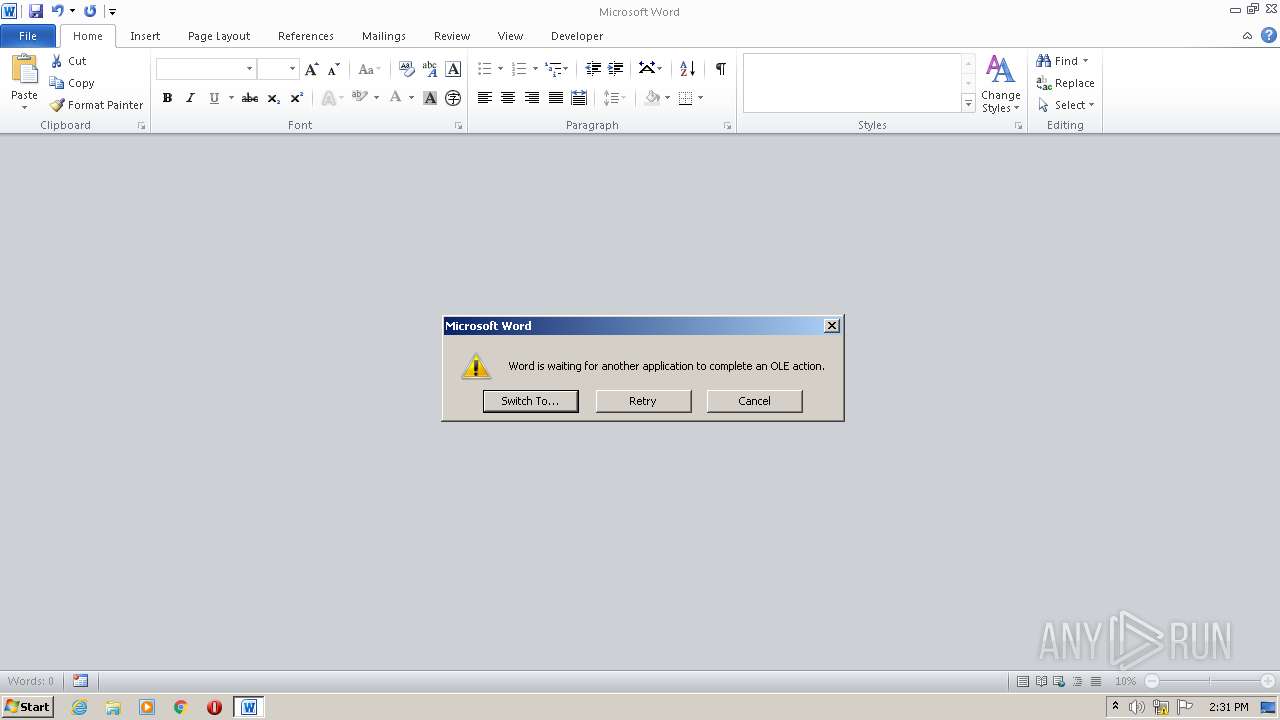
Executed via COM
- EQNEDT32.EXE (PID: 2360)
INFO
Checks supported languages
- WINWORD.EXE (PID: 2220)
- taskmgr.exe (PID: 3364)
Reads the computer name
- WINWORD.EXE (PID: 2220)
- taskmgr.exe (PID: 3364)
Creates files in the user directory
- WINWORD.EXE (PID: 2220)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
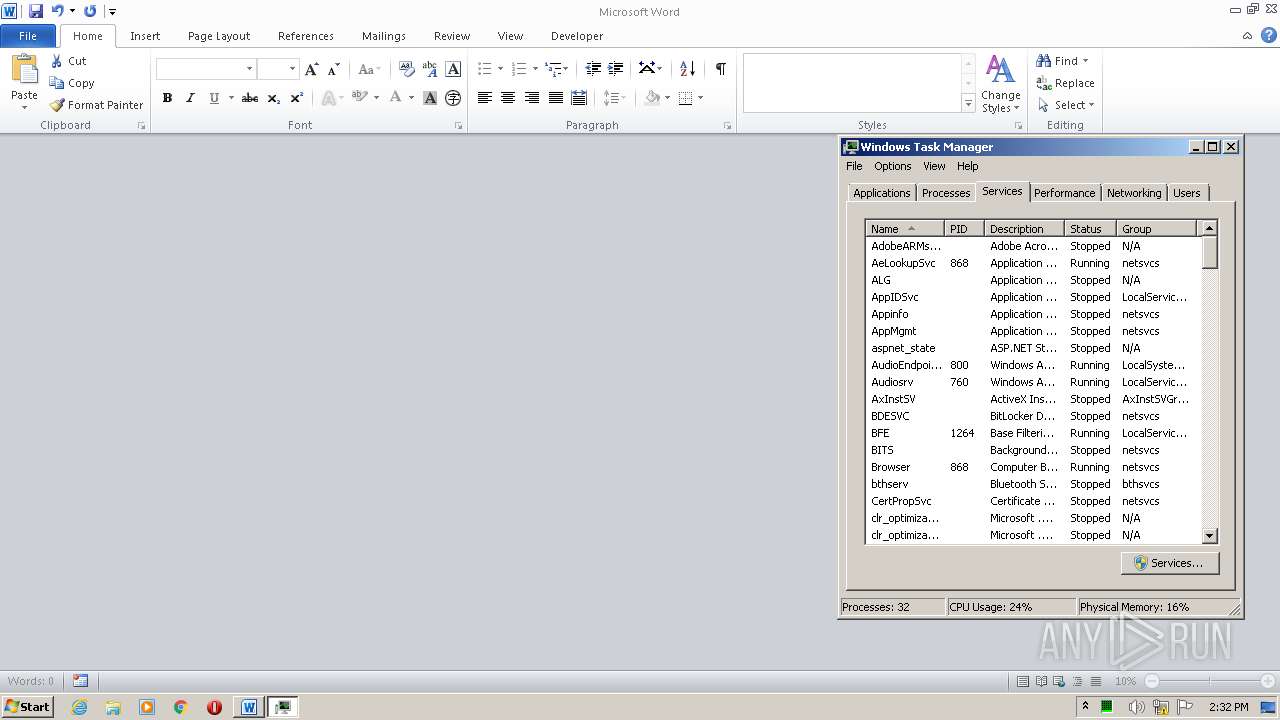
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2220 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\1.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3364 | "C:\Windows\system32\taskmgr.exe" | C:\Windows\system32\taskmgr.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 263
Read events
1 192
Write events
68
Delete events
3
Modification events
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | j.7 |
Value: 6A2E3700AC080000010000000000000000000000 | |||
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2220) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2220 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR966A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2220 | WINWORD.EXE | C:\Users\admin\Desktop\~$1.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2220 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2360 | EQNEDT32.EXE | GET | — | 2.58.149.41:80 | http://2.58.149.41/ikmerozx.exe | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2360 | EQNEDT32.EXE | 2.58.149.41:80 | — | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |