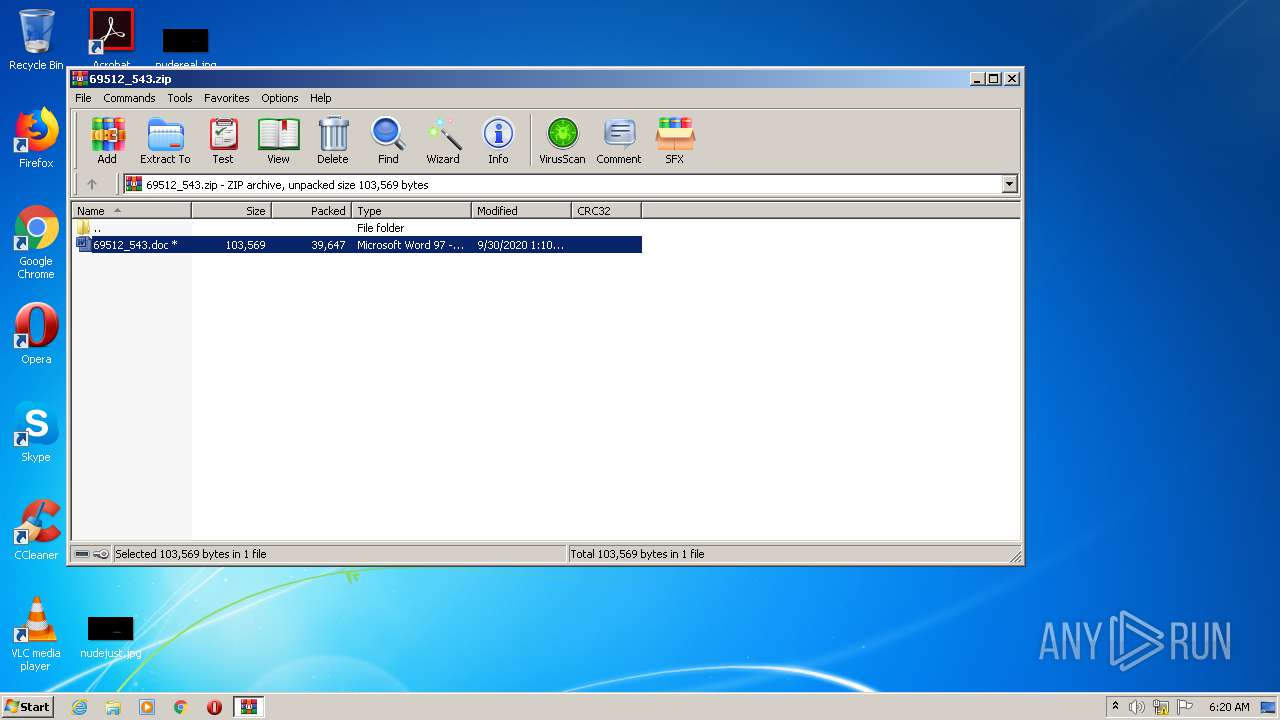
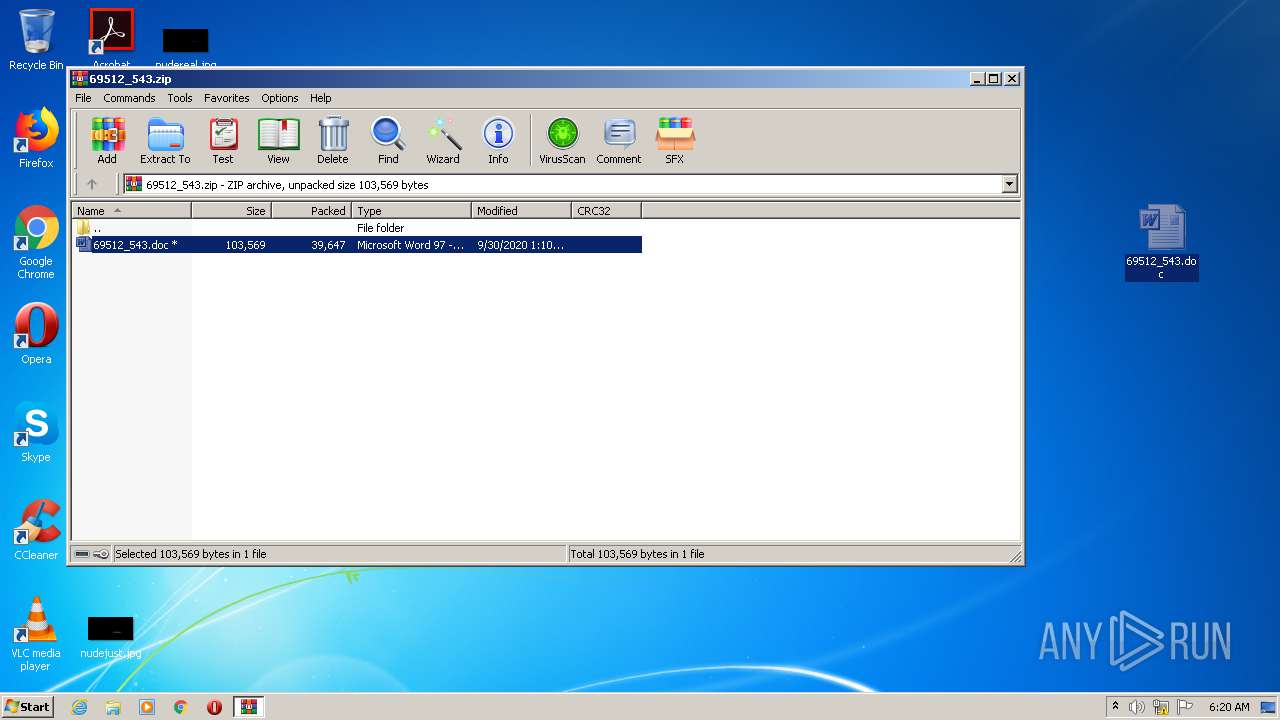
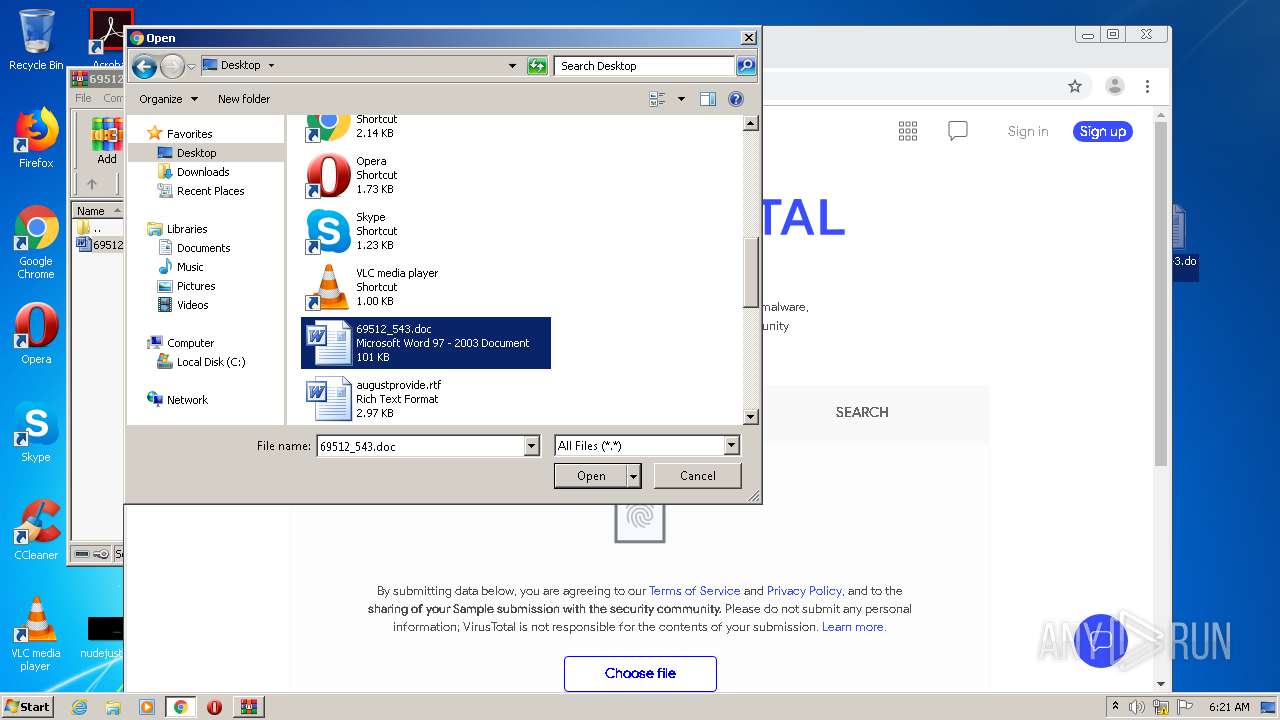
| File name: | 69512_543.zip |
| Full analysis: | https://app.any.run/tasks/537fe7f4-16a5-47d5-b0b8-33cc5a97da98 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 05:18:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
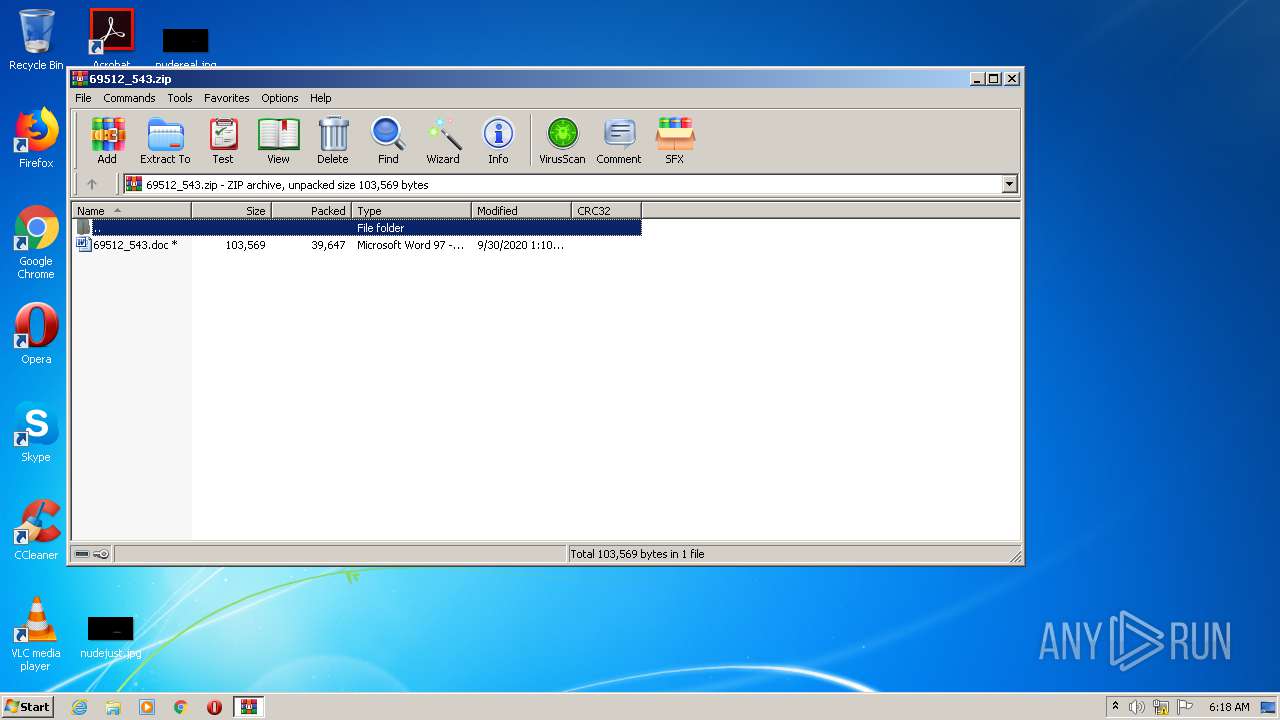
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 31600250D692BBC755DFB5E09B64CF90 |
| SHA1: | FBC7BD44BFBCC14EFC356DC627C00417FCC75452 |
| SHA256: | AC0486B1B00FBD3C6FD98BFFD5B6485D71263928ED94648B3206B4AB80CFFD93 |
| SSDEEP: | 768:gizl4jSiEo2z6d1x5LyIeCtSykHTlvzrrq5/EP8LXyLMw5c+Qg473dhBVTyuZ+3:gQ2HDkIItTtPnULUMw5DaLdhBVyuZs |
MALICIOUS
Application was dropped or rewritten from another process
- Slk0lv.exe (PID: 3280)
- StructuredQuery.exe (PID: 2176)
Connects to CnC server
- StructuredQuery.exe (PID: 2176)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 3720)
EMOTET was detected
- StructuredQuery.exe (PID: 2176)
Changes the autorun value in the registry
- StructuredQuery.exe (PID: 2176)
SUSPICIOUS
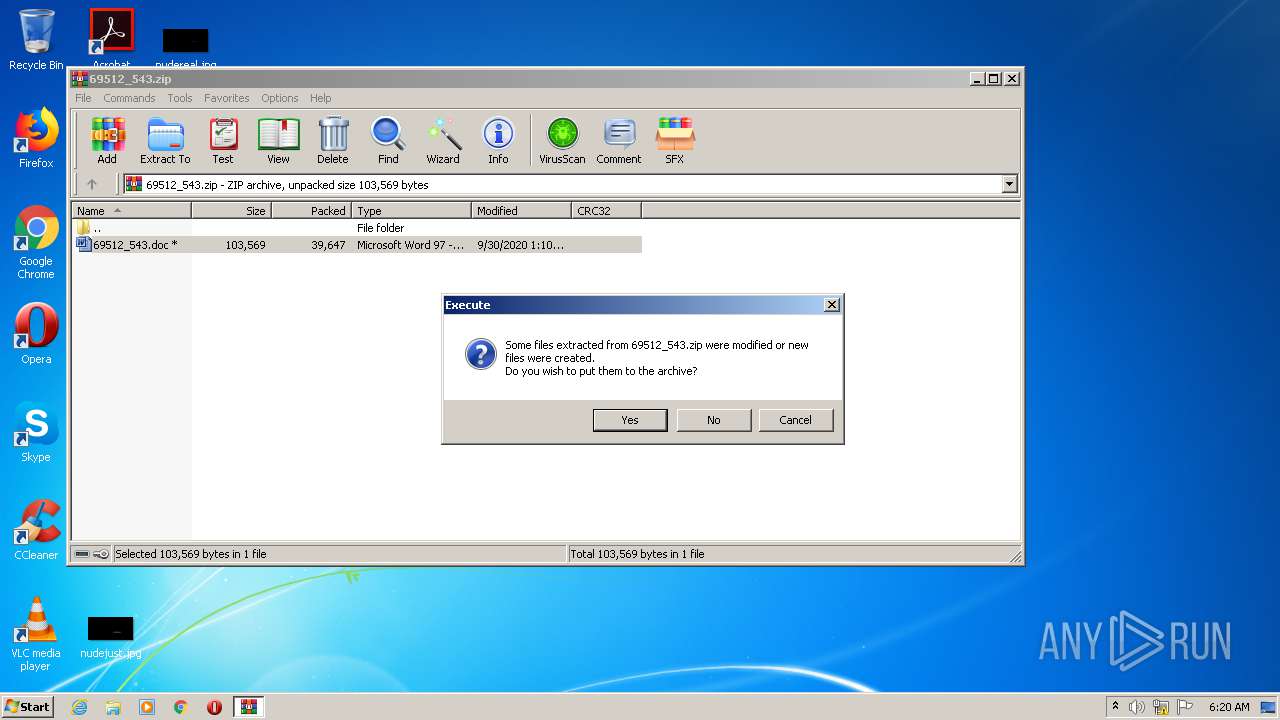
Starts Microsoft Office Application
- WinRAR.exe (PID: 1688)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3720)
- Slk0lv.exe (PID: 3280)
Executed via WMI
- POwersheLL.exe (PID: 3720)
PowerShell script executed
- POwersheLL.exe (PID: 3720)
Creates files in the user directory
- POwersheLL.exe (PID: 3720)
Starts itself from another location
- Slk0lv.exe (PID: 3280)
Reads Internet Cache Settings
- StructuredQuery.exe (PID: 2176)
Connects to server without host name
- StructuredQuery.exe (PID: 2176)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3928)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3928)
Reads the hosts file
- chrome.exe (PID: 1828)
- chrome.exe (PID: 3884)
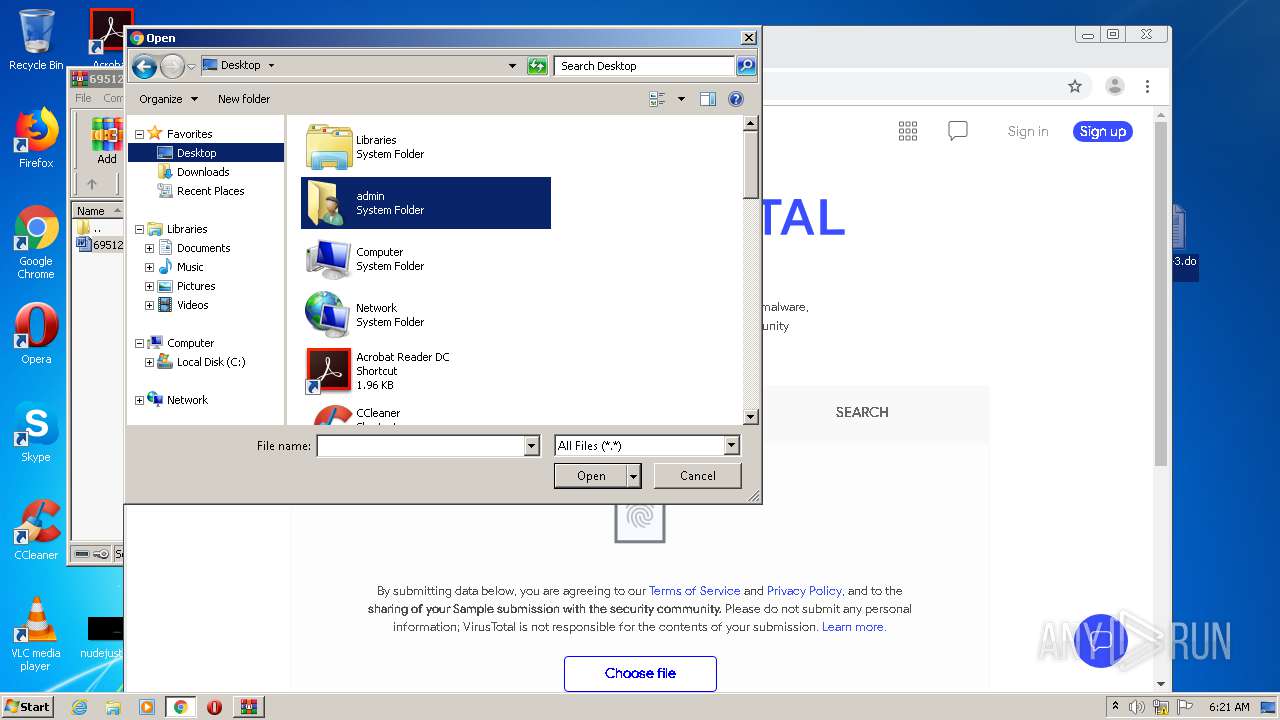
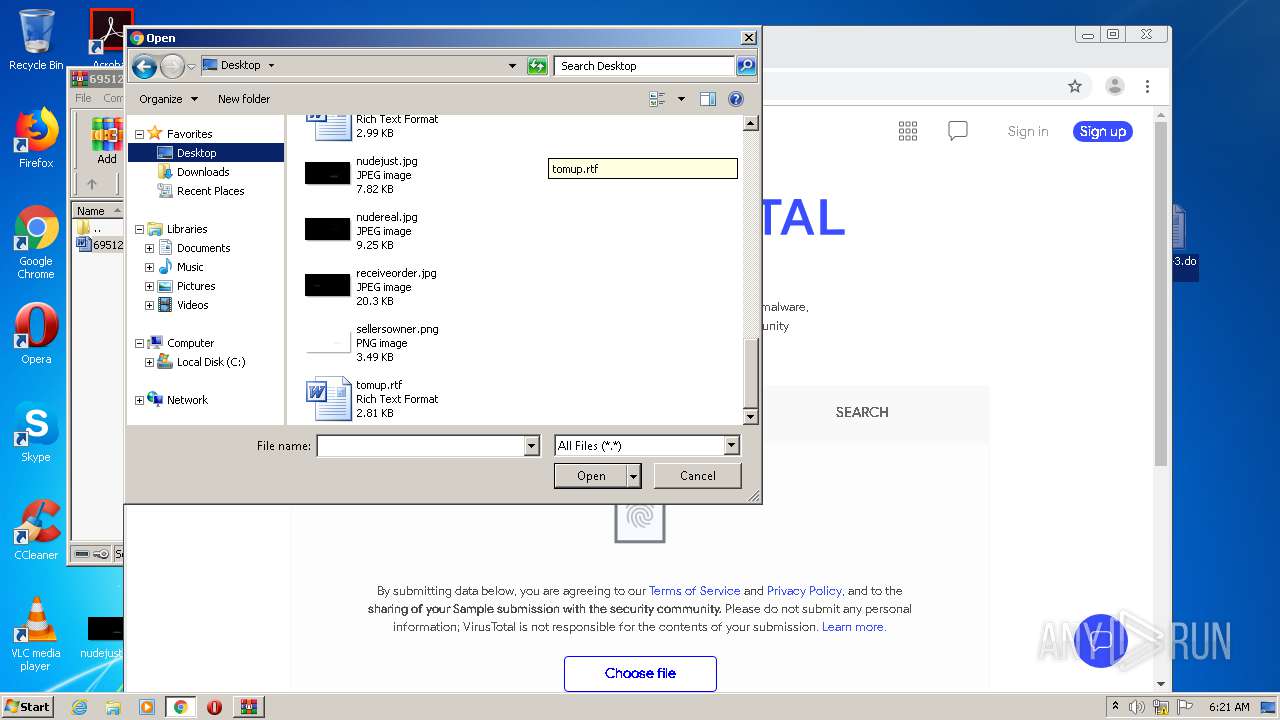
Manual execution by user
- chrome.exe (PID: 3884)
Application launched itself
- chrome.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
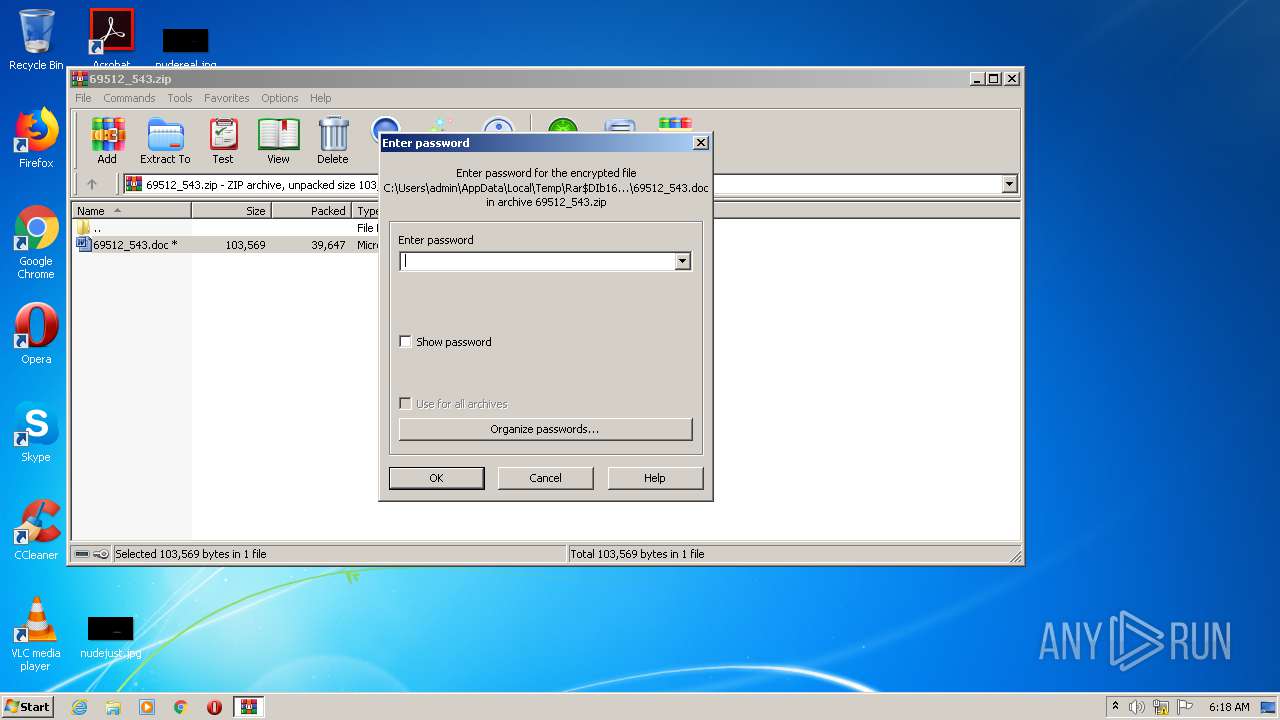
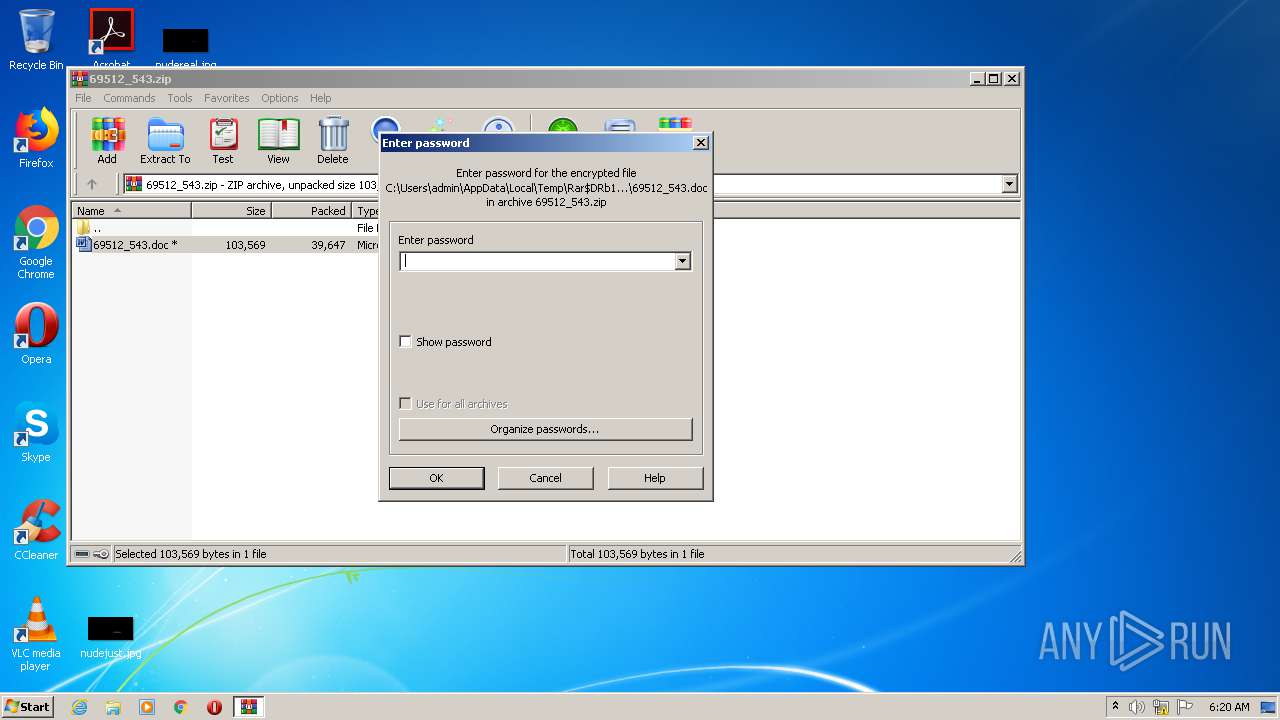
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:09:30 01:10:01 |
| ZipCRC: | 0x22b15148 |
| ZipCompressedSize: | 39647 |
| ZipUncompressedSize: | 103569 |
| ZipFileName: | 69512_543.doc |
Total processes
68
Monitored processes
25
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2768 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\69512_543.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d07a9d0,0x6d07a9e0,0x6d07a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,12152149464899452927,14717231960527147609,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5050404383131507877 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\mtxdm\StructuredQuery.exe" | C:\Users\admin\AppData\Local\mtxdm\StructuredQuery.exe | Slk0lv.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,12152149464899452927,14717231960527147609,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4713721526442537980 --mojo-platform-channel-handle=2368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,12152149464899452927,14717231960527147609,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17764478240811613306 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,12152149464899452927,14717231960527147609,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12942052053964881236 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,12152149464899452927,14717231960527147609,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15452131124676655779 --mojo-platform-channel-handle=2900 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,12152149464899452927,14717231960527147609,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3435540485957674062 --mojo-platform-channel-handle=3516 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 108
Read events
3 044
Write events
872
Delete events
192
Modification events
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\69512_543.zip | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1363017790 | |||
Executable files
2
Suspicious files
53
Text files
76
Unknown types
3
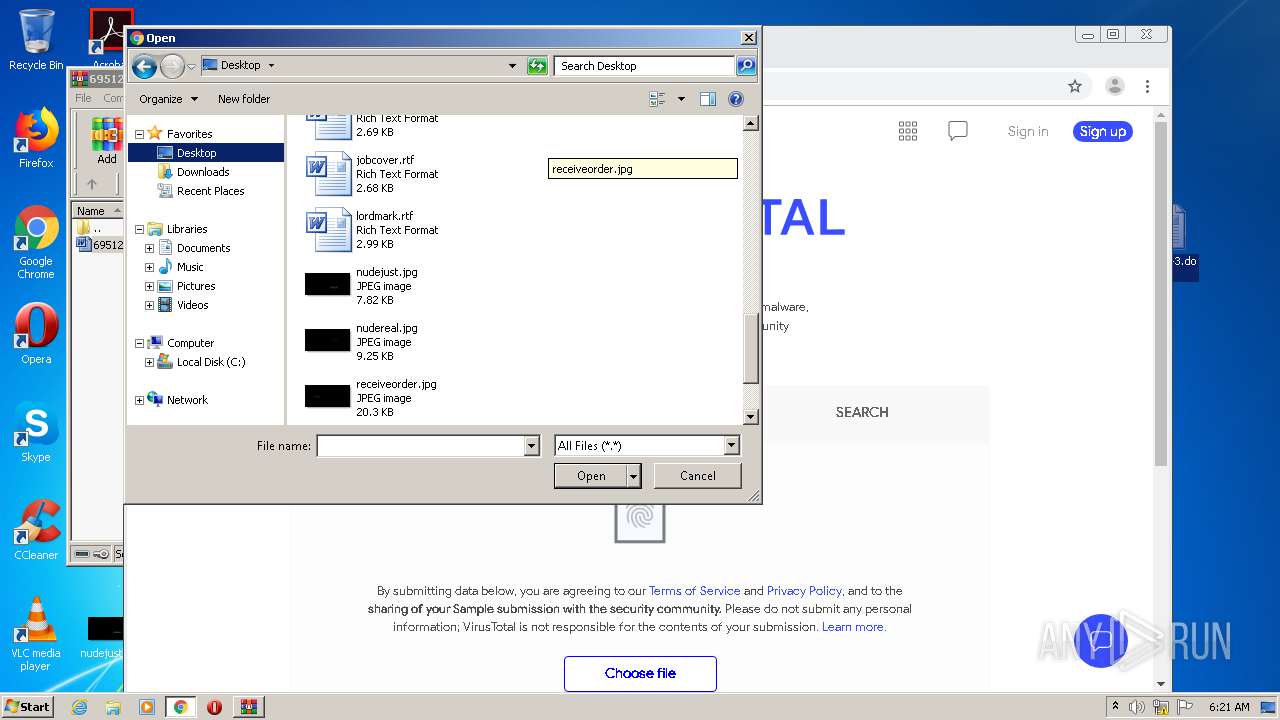
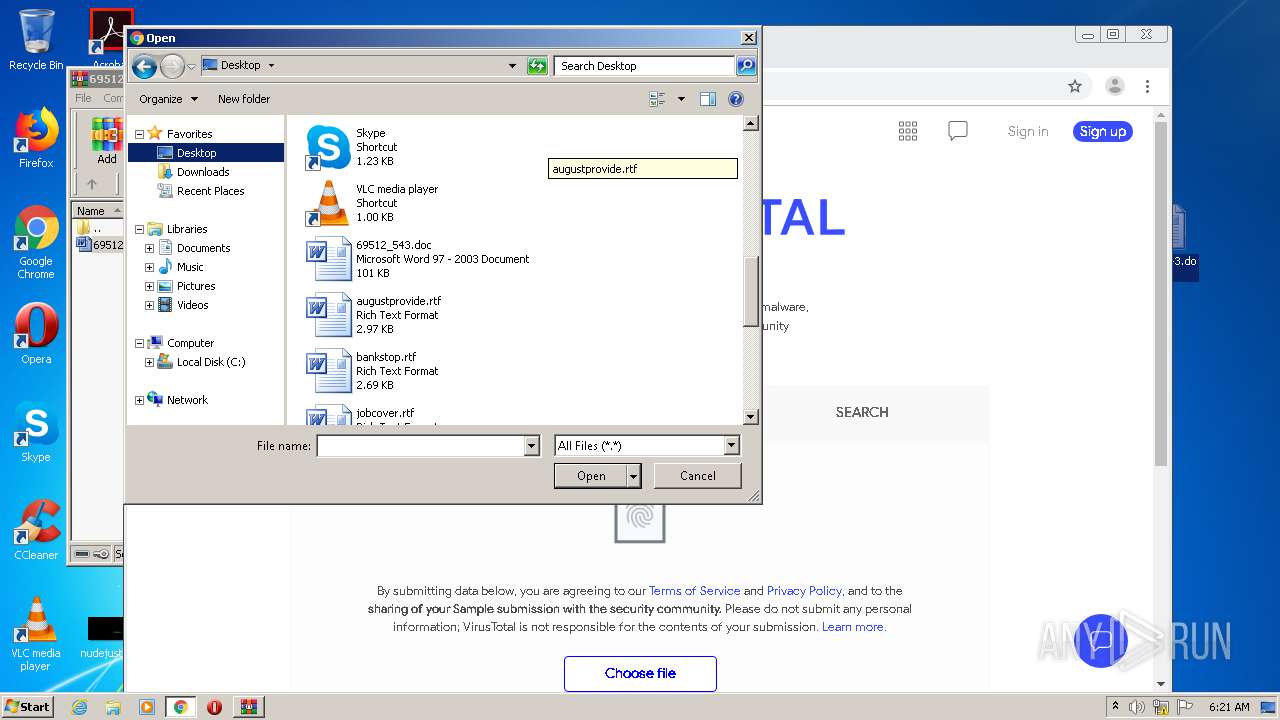
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1614.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3720 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\A70MTEYOAFDAUG6YXFHA.temp | — | |
MD5:— | SHA256:— | |||
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFADB32C816ED229D8.TMP | — | |
MD5:— | SHA256:— | |||
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF7F7DAC8CDE143BF9.TMP | — | |
MD5:— | SHA256:— | |||
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF4C57BC0D3D53070A.TMP | — | |
MD5:— | SHA256:— | |||
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{D8C11A4F-1C21-4042-8087-E6D164FF16AC}.tmp | — | |
MD5:— | SHA256:— | |||
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA9FCCA760671796C.TMP | — | |
MD5:— | SHA256:— | |||
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{3143E316-F27E-4505-AF26-7C4AF7CF7C02}.tmp | — | |
MD5:— | SHA256:— | |||
| 1688 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1688.6610\69512_543.doc | — | |
MD5:— | SHA256:— | |||
| 3884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F7415BA-F2C.pma | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
28
DNS requests
21
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3720 | POwersheLL.exe | GET | — | 66.97.41.90:80 | http://lblcomputacion.com/services/eY3/ | US | — | — | suspicious |
3720 | POwersheLL.exe | GET | 200 | 34.67.97.45:80 | http://shop.homenhealthy.com/wp-includes/Ltj/ | US | executable | 149 Kb | suspicious |
2176 | StructuredQuery.exe | POST | 200 | 128.92.203.42:80 | http://128.92.203.42/AmW3/RPfOlD/9yc3PXu/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1828 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3720 | POwersheLL.exe | 34.67.97.45:80 | shop.homenhealthy.com | — | US | suspicious |
1828 | chrome.exe | 142.250.74.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 172.217.23.110:443 | consent.google.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 142.250.74.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3720 | POwersheLL.exe | 66.97.41.90:80 | lblcomputacion.com | Peer 1 Network (USA) Inc. | US | suspicious |
1828 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lblcomputacion.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
shop.homenhealthy.com |
| suspicious |
clients2.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3720 | POwersheLL.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
3720 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3720 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3720 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3720 | POwersheLL.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2176 | StructuredQuery.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 4 |
2176 | StructuredQuery.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |