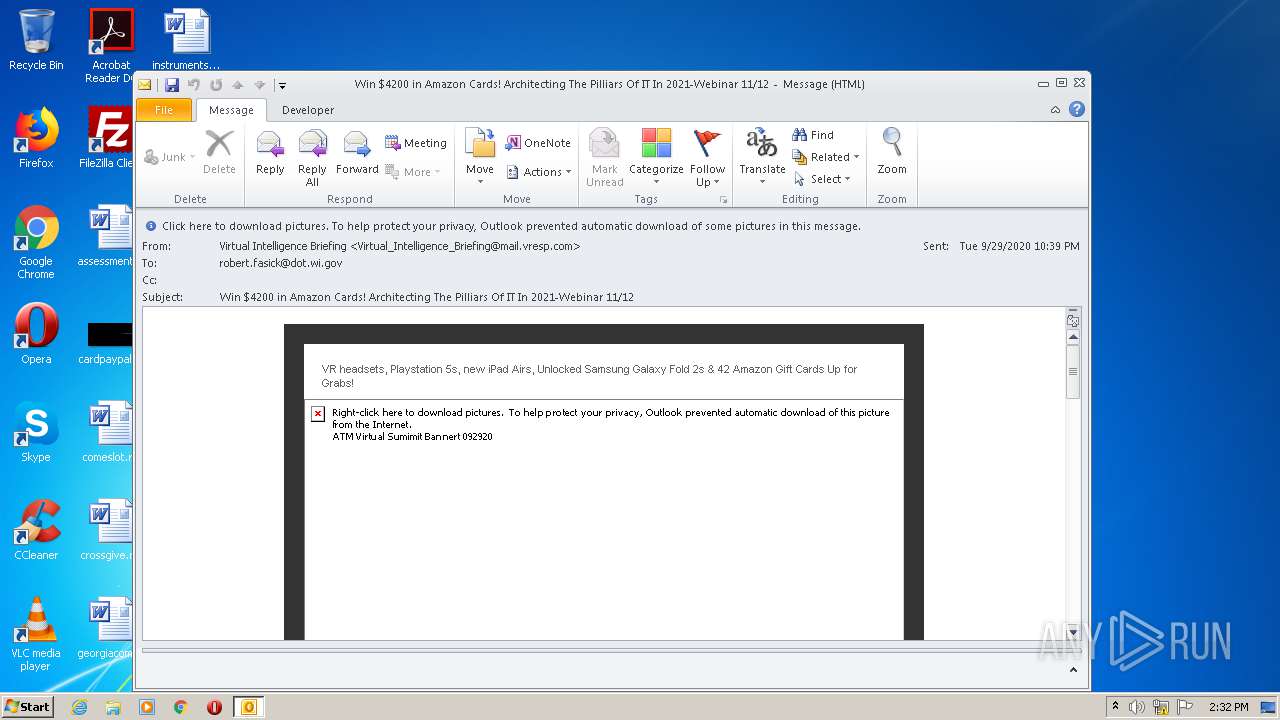
| File name: | Win $4200 in Amazon Cards! Architecting The Pilliars Of IT In 2021-Webinar 1112.msg |
| Full analysis: | https://app.any.run/tasks/972c40bc-0e3a-4234-81ec-168c4fbda0ff |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 13:31:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | DD964F4940043FA09DA3D1D8AF447C60 |
| SHA1: | 2BF16E9C7BE69A5CFC145D49E1B649E2EE5A7DF6 |
| SHA256: | ABFCA799EDA0398EF82BD7C789EDECCCC8FCE1637481984970547851E3F51B12 |
| SSDEEP: | 1536:dgmbQbxVeMhk9ePqc0cR9dRs8KO2K76EllmfRIT/ihmewueZg3CfTt1:dAS9eNpJKO2KTl6Rd5jeZKCfTt1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2620)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2620)
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 2620)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2620)
Reads the hosts file
- chrome.exe (PID: 2356)
- chrome.exe (PID: 2892)
Manual execution by user
- chrome.exe (PID: 2356)
Application launched itself
- chrome.exe (PID: 2356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
50
Monitored processes
13
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9752303692633816697,2943958687495518845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9396923175773857085 --mojo-platform-channel-handle=3428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9752303692633816697,2943958687495518845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2970167428697721186 --mojo-platform-channel-handle=2896 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9752303692633816697,2943958687495518845,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17782426989689725409 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9752303692633816697,2943958687495518845,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3964451231152528534 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Win $4200 in Amazon Cards! Architecting The Pilliars Of IT In 2021-Webinar 1112.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9752303692633816697,2943958687495518845,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6069153928564995043 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,9752303692633816697,2943958687495518845,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3472068601206870065 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9752303692633816697,2943958687495518845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17166171624604628332 --mojo-platform-channel-handle=1500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2760 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 798
Read events
1 187
Write events
589
Delete events
22
Modification events
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2620) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
58
Text files
96
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRC024.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\msoC620.tmp | — | |
MD5:— | SHA256:— | |||
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\Cab1098.tmp | — | |
MD5:— | SHA256:— | |||
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\Tar1099.tmp | — | |
MD5:— | SHA256:— | |||
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B0F2D31D2C32B49DCC8F7CC5C73F3C5D_2C8AAFA9D67255B0364928E0BF09B2FE | der | |
MD5:— | SHA256:— | |||
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2EE749B7E1A15635422518BB5EBFD338_2BE9BBF30BBE030BE7B79471EABFE00A | der | |
MD5:— | SHA256:— | |||
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2EE749B7E1A15635422518BB5EBFD338_2BE9BBF30BBE030BE7B79471EABFE00A | binary | |
MD5:— | SHA256:— | |||
| 2620 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_59F0782FF3907FFC80FBF97C26C59F4A | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
59
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2620 | OUTLOOK.EXE | GET | 200 | 35.156.70.210:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBRPT4HWWg2N6N2sdizmyiRTaupwfgQUmGq2LS6%2Fp6qf9vfWCa%2FVi1f5ircCFAJ6LdwhHmBeL%2BjGokwlqon6ciFk | DE | der | 1.81 Kb | whitelisted |
2620 | OUTLOOK.EXE | GET | 200 | 35.156.70.210:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBTyhcKR1A4XhQLFZRt5u%2BT8TDsYdQQUGoRivEhMMyUE1O7Q9gPEGUbRlGsCFHUXFneD0EN%2BtVbDV5RuRWO469Os | DE | der | 1.78 Kb | whitelisted |
2620 | OUTLOOK.EXE | GET | 200 | 35.156.70.210:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBTyhcKR1A4XhQLFZRt5u%2BT8TDsYdQQUGoRivEhMMyUE1O7Q9gPEGUbRlGsCFHUXFneD0EN%2BtVbDV5RuRWO469Os | DE | der | 1.78 Kb | whitelisted |
2620 | OUTLOOK.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA4fj70KQcPqzA7eSOL374Q%3D | US | der | 280 b | whitelisted |
2620 | OUTLOOK.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
2620 | OUTLOOK.EXE | GET | 200 | 35.156.70.210:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBRPT4HWWg2N6N2sdizmyiRTaupwfgQUmGq2LS6%2Fp6qf9vfWCa%2FVi1f5ircCFAJ6LdwhHmBeL%2BjGokwlqon6ciFk | DE | der | 1.81 Kb | whitelisted |
2620 | OUTLOOK.EXE | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEApYuMXoydkUzhHJOZjpTAY%3D | US | der | 471 b | whitelisted |
2620 | OUTLOOK.EXE | GET | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgO0pg3mWaw3Z4DOw6z09w3BVg%3D%3D | unknown | der | 527 b | whitelisted |
2620 | OUTLOOK.EXE | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2620 | OUTLOOK.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2620 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
— | — | 107.178.254.65:443 | pippio.com | Google Inc. | US | whitelisted |
— | — | 184.94.240.100:443 | secure-web.cisco.com | Cisco Systems Ironport Division | US | suspicious |
2620 | OUTLOOK.EXE | 35.193.67.164:443 | mr-p.alcmpn.com | Google Inc. | US | unknown |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
2620 | OUTLOOK.EXE | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
2620 | OUTLOOK.EXE | 54.164.226.138:443 | allaudience.com | Amazon.com, Inc. | US | unknown |
2620 | OUTLOOK.EXE | 44.238.151.153:443 | p.alocdn.com | University of California, San Diego | US | unknown |
2620 | OUTLOOK.EXE | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
secure-web.cisco.com |
| whitelisted |
pippio.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.quovadisglobal.com |
| whitelisted |
img-ak.verticalresponse.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
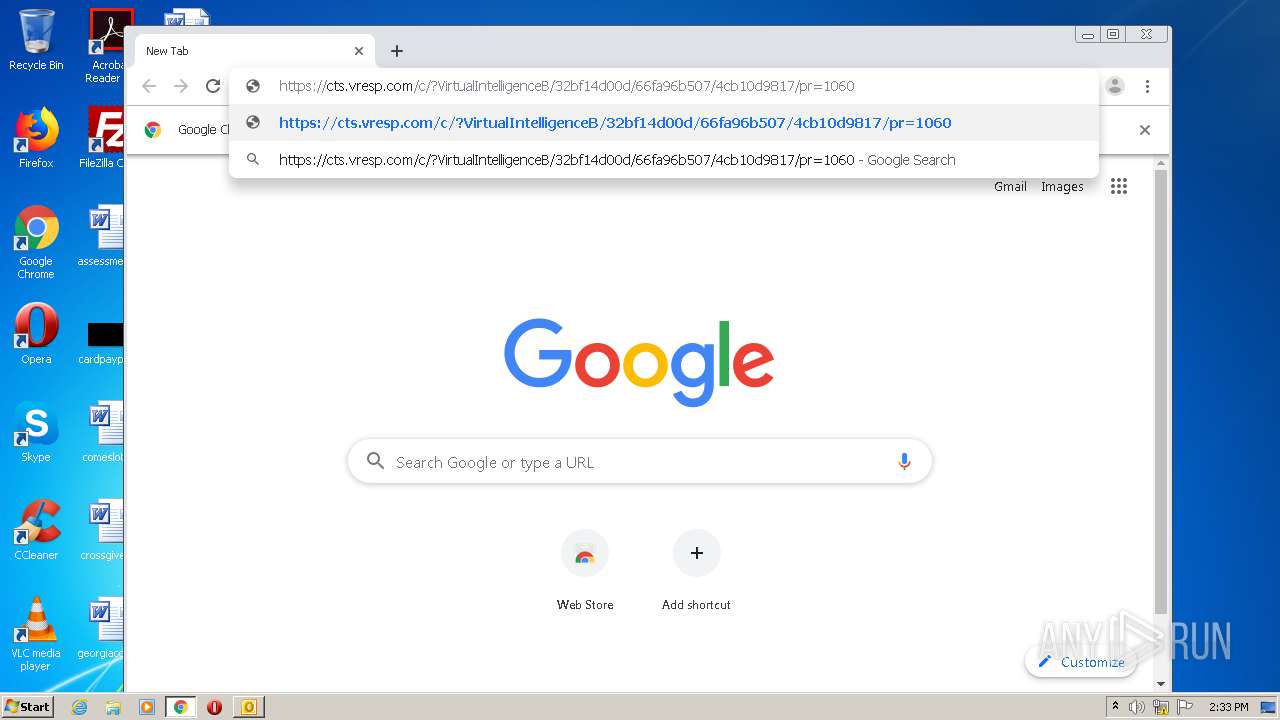
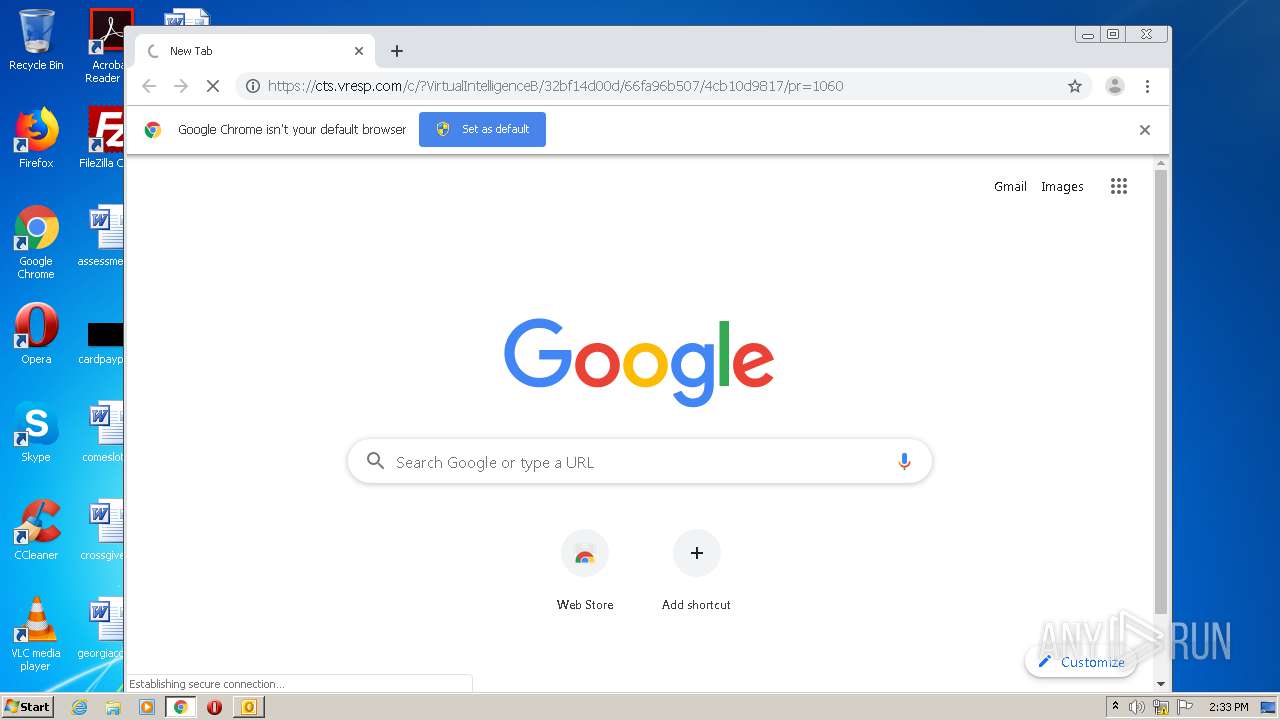
cts.vresp.com |
| whitelisted |
mr-p.alcmpn.com |
| unknown |
status.geotrust.com |
| whitelisted |