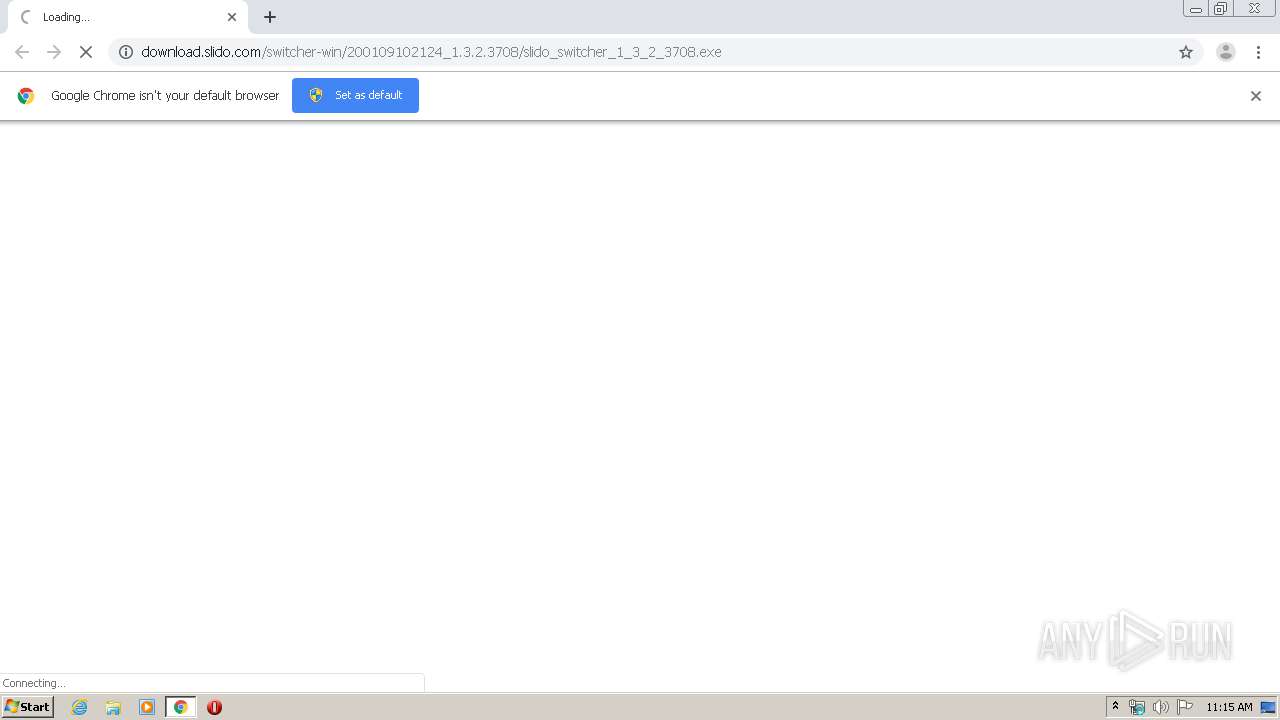
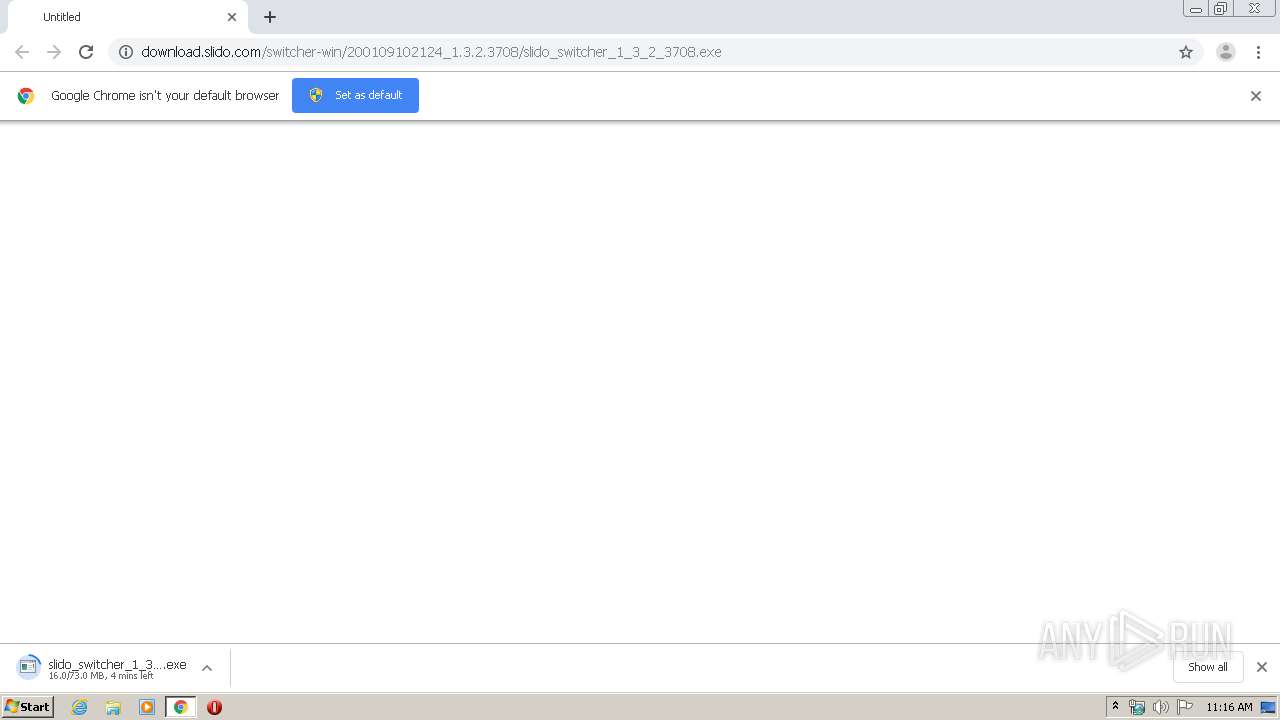
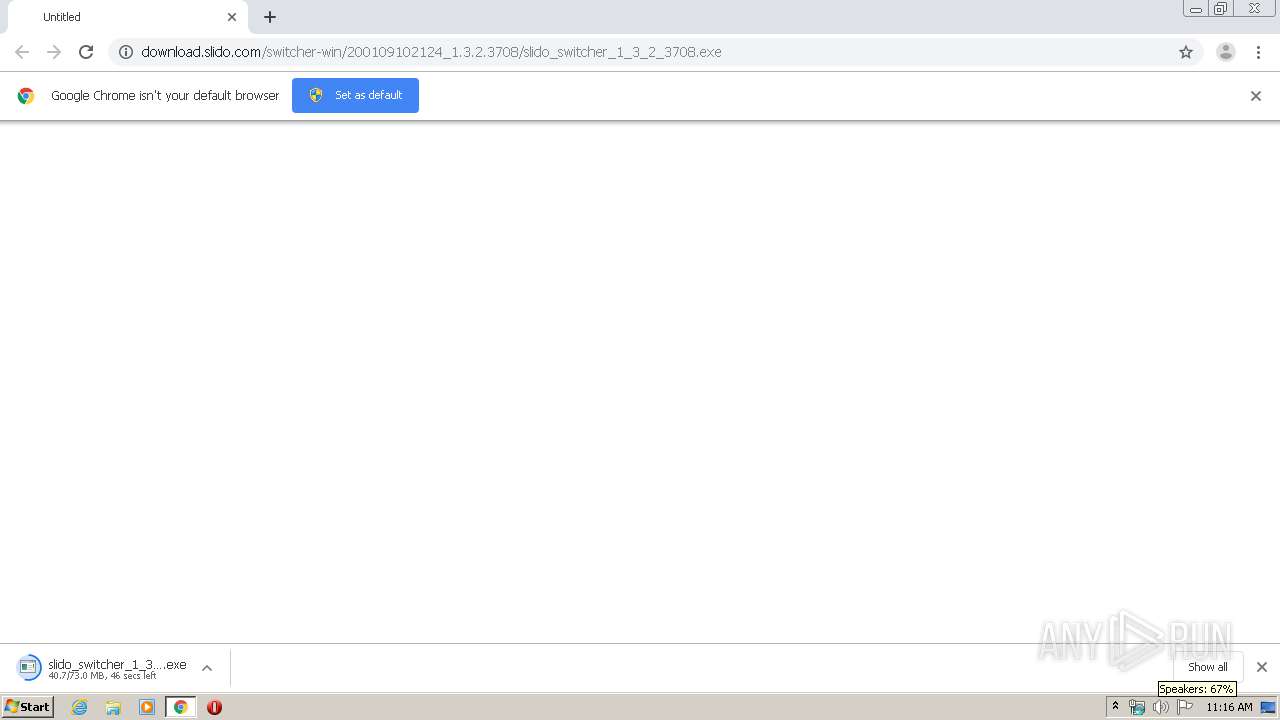
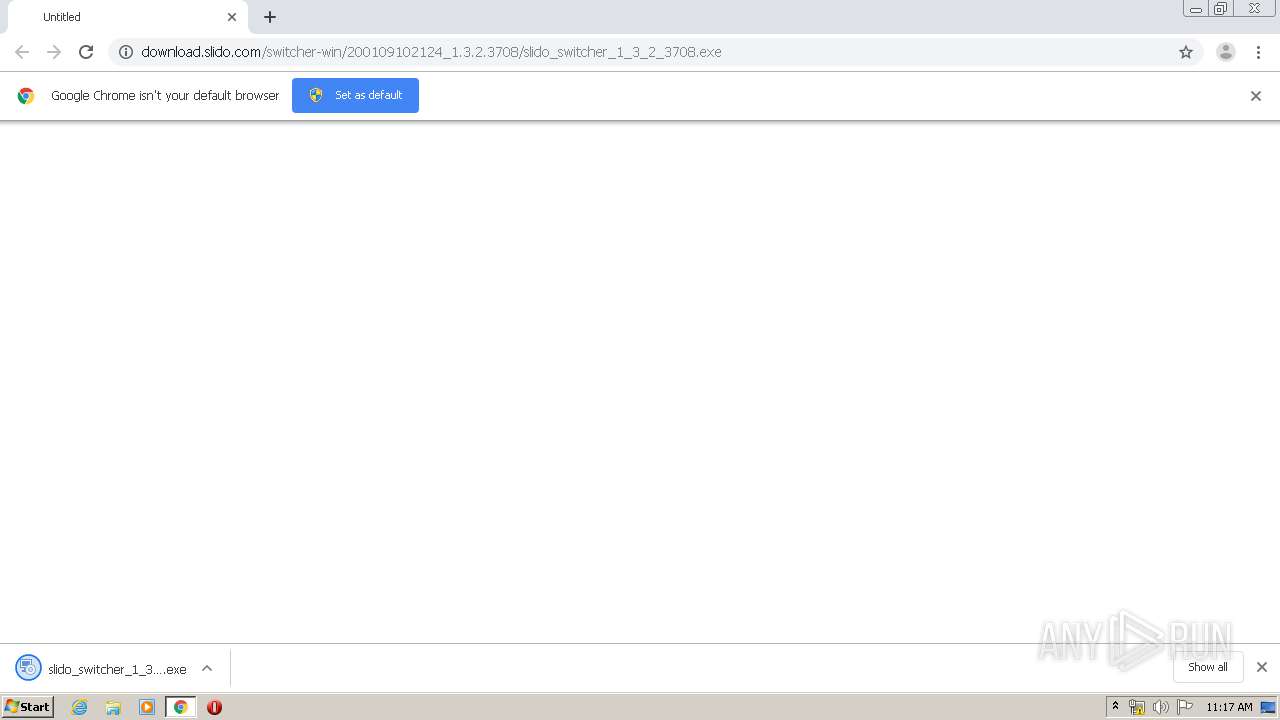
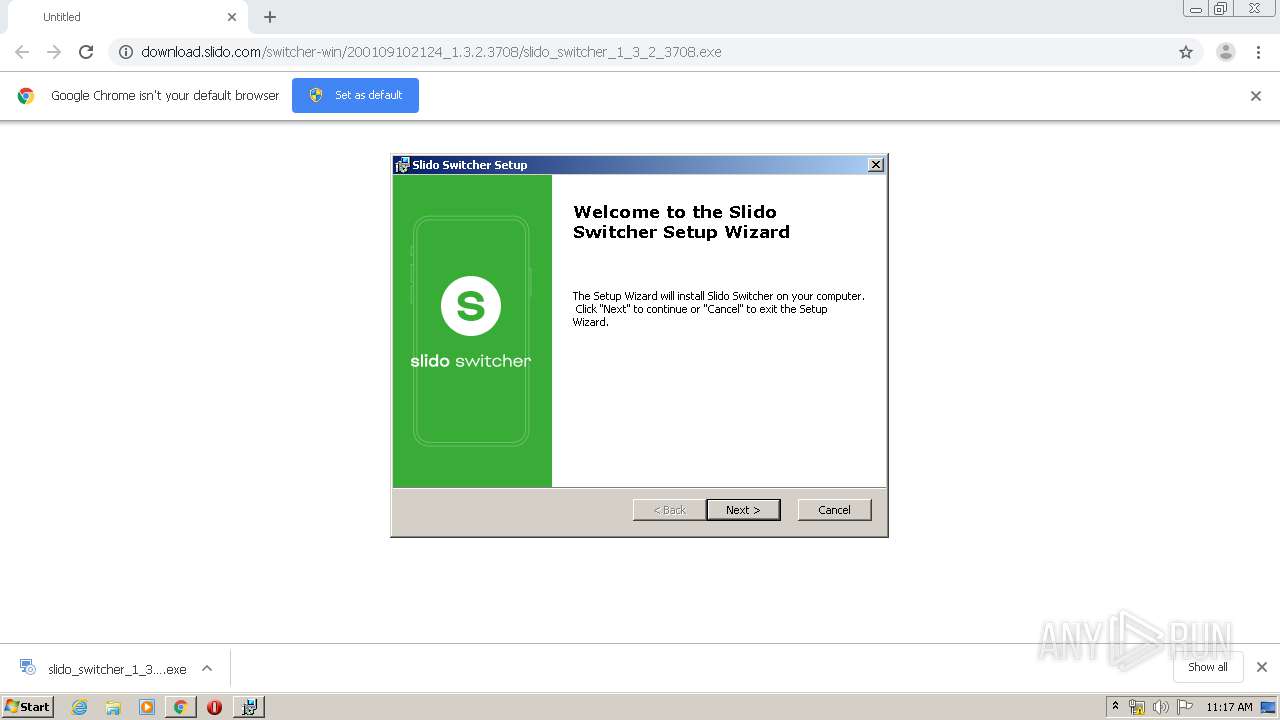
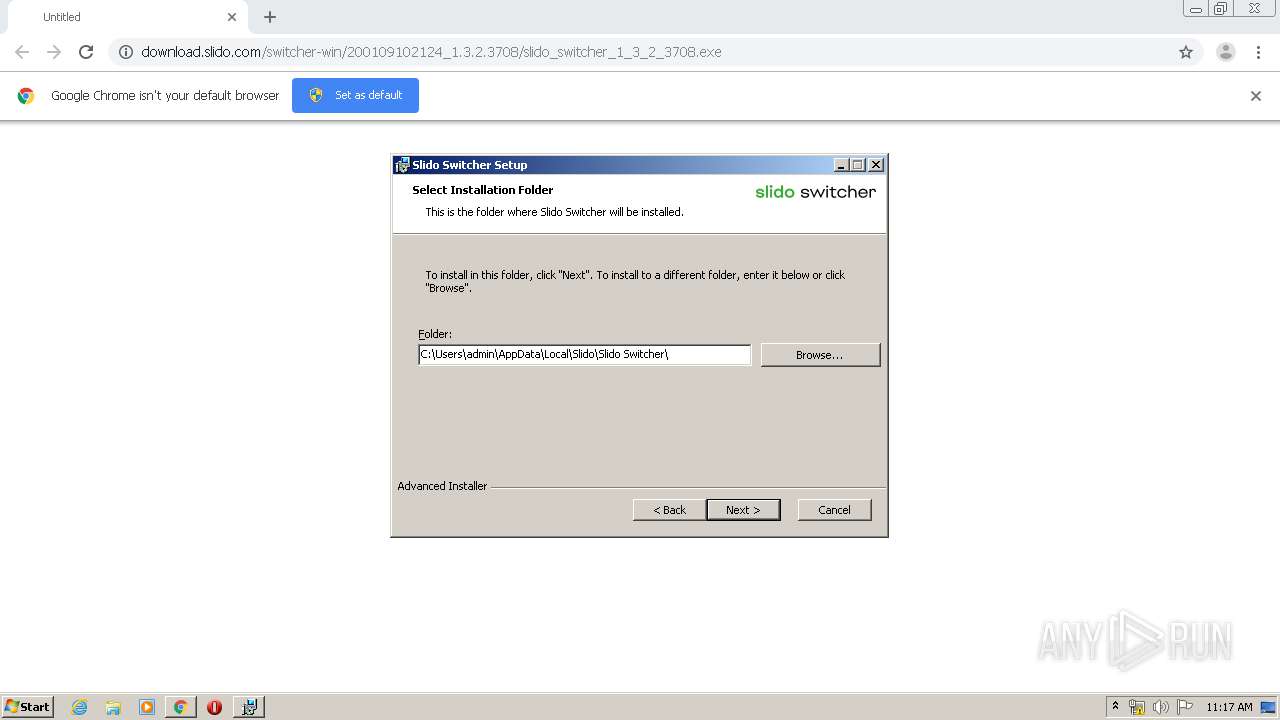
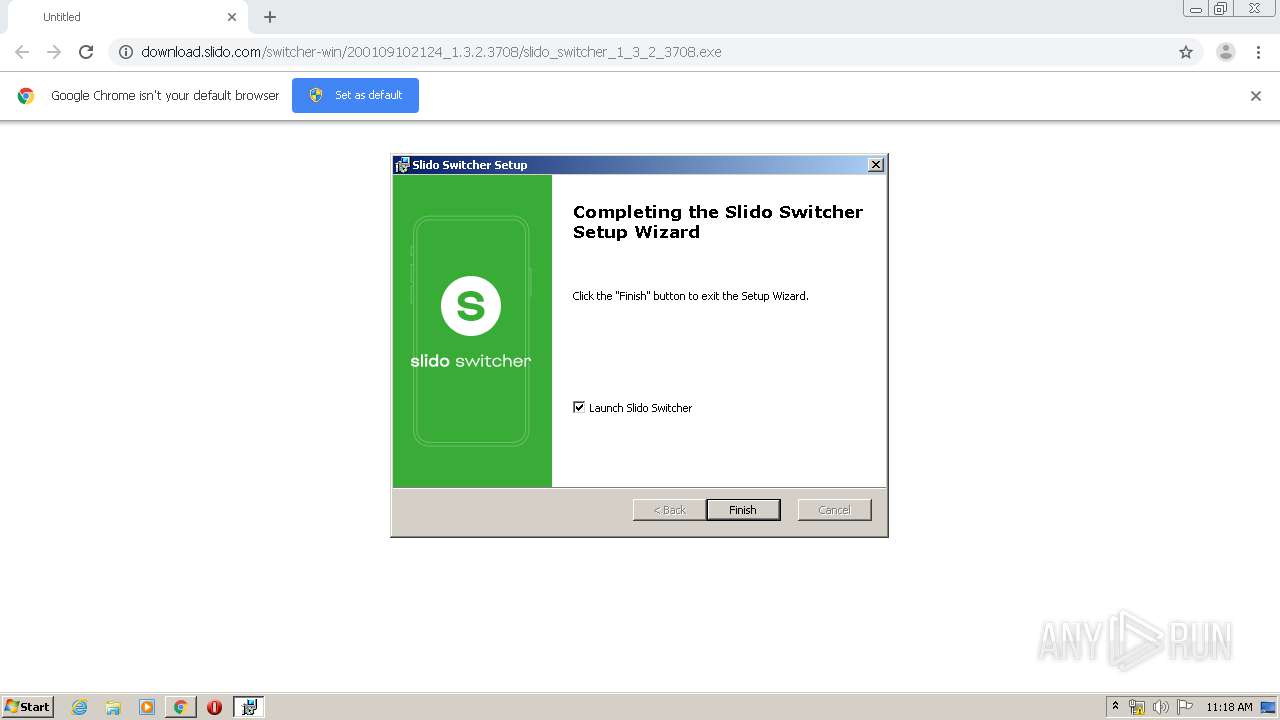
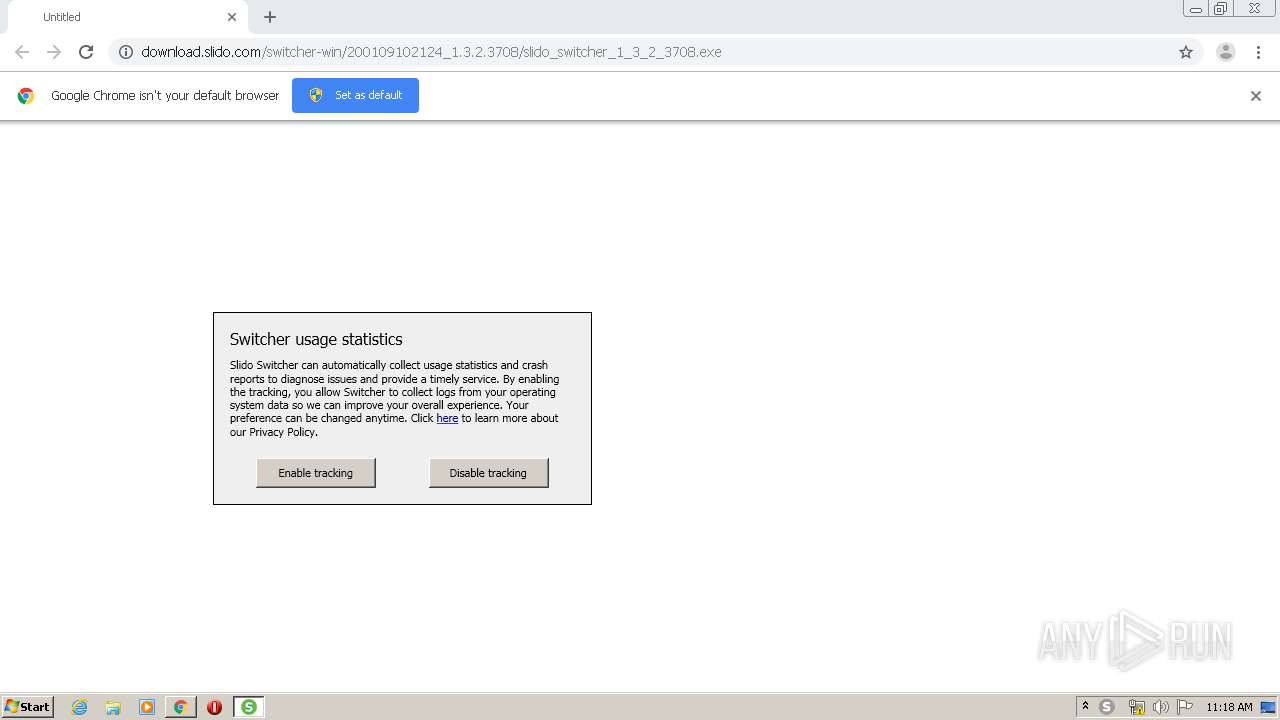
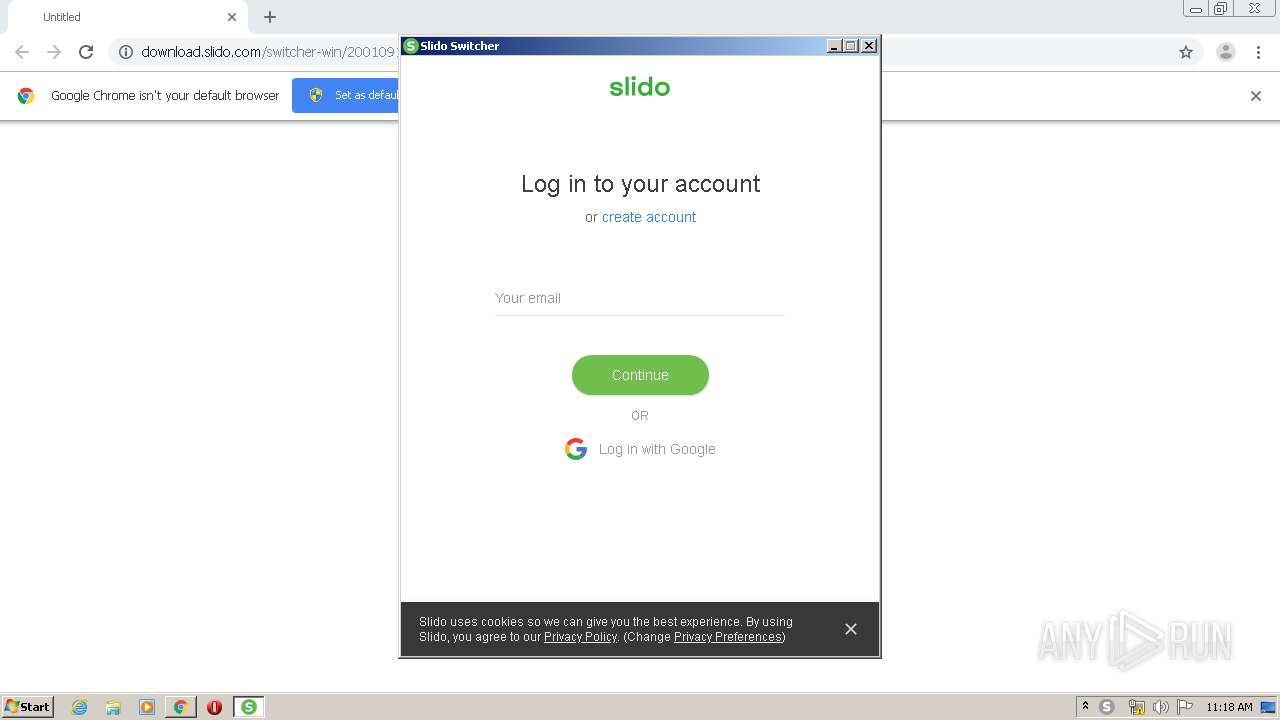
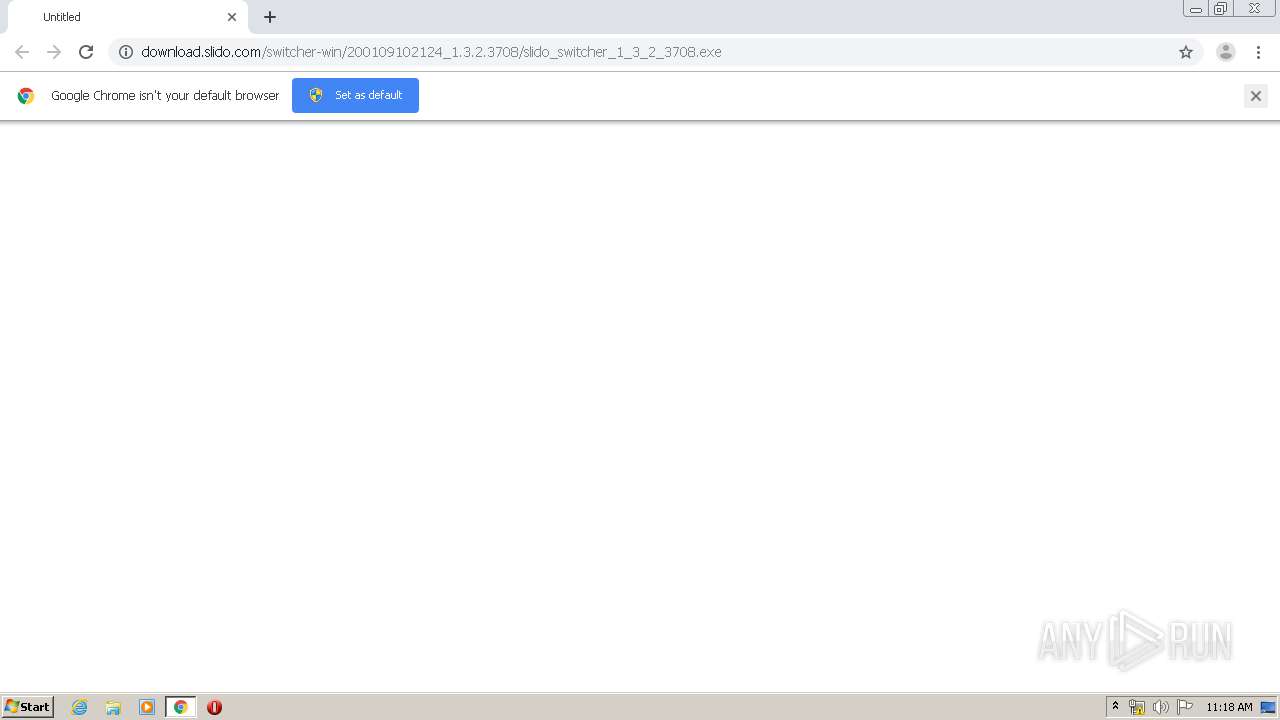
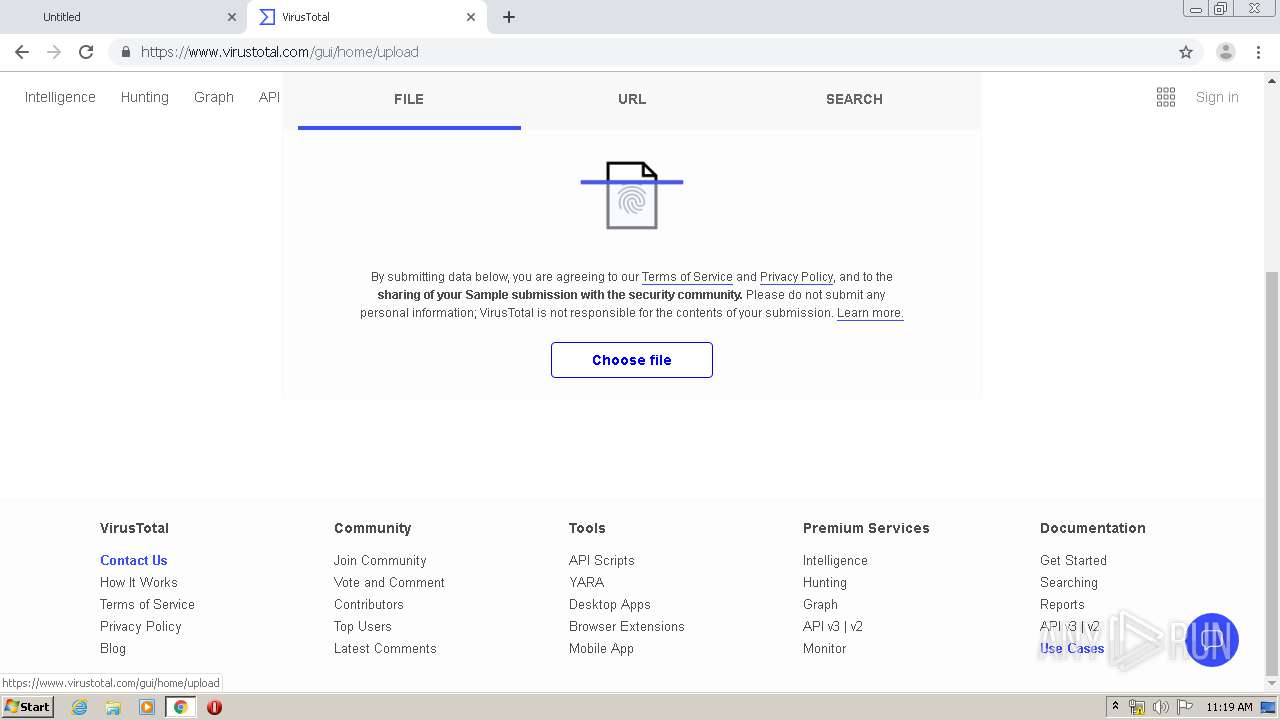
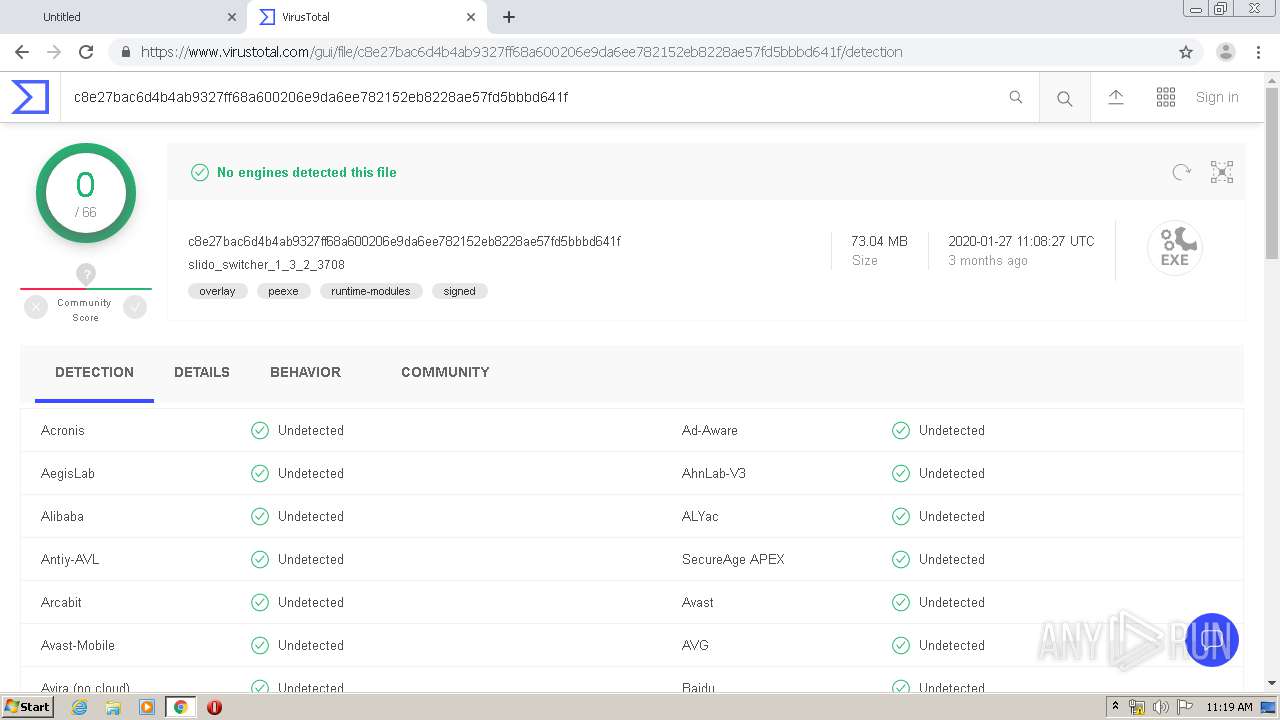
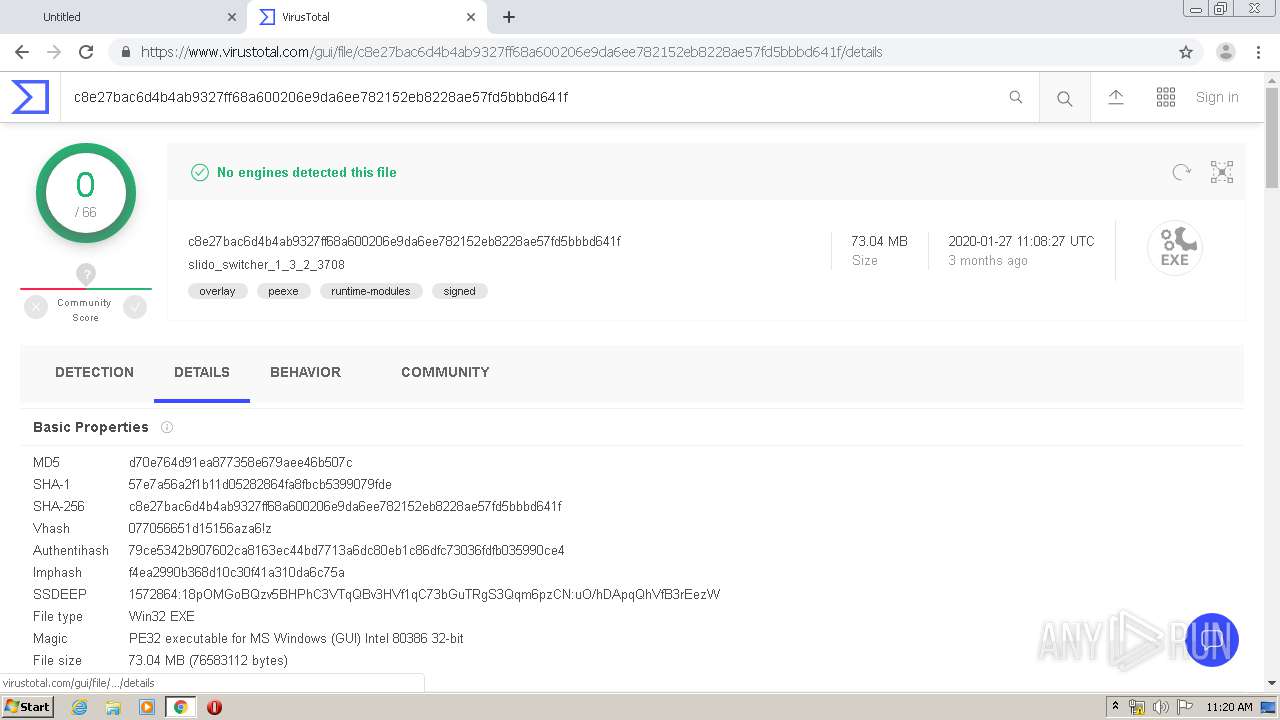
| URL: | http://download.slido.com/switcher-win/200109102124_1.3.2.3708/slido_switcher_1_3_2_3708.exe |
| Full analysis: | https://app.any.run/tasks/e954c6f3-f446-42b7-b798-5facf12c5ac0 |
| Verdict: | Malicious activity |
| Analysis date: | May 06, 2020, 10:15:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
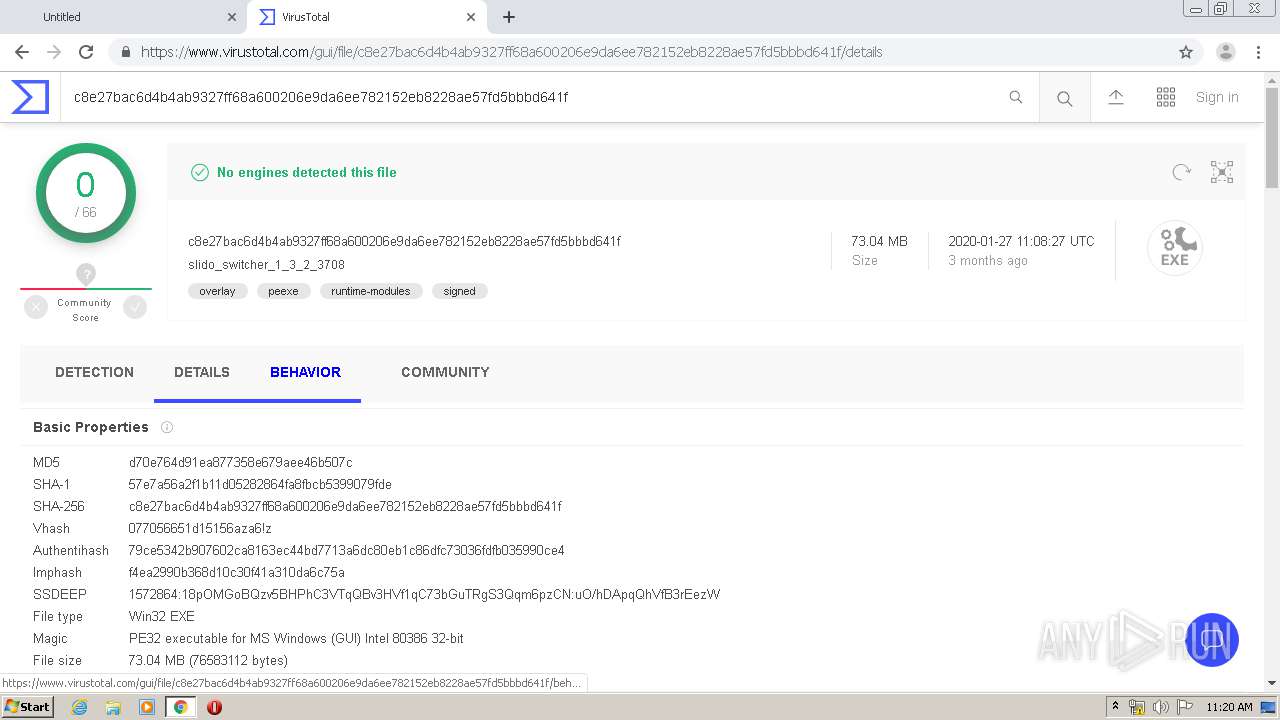
| MD5: | 152B6E656DC3E5BD3C10A196EDBDEB0C |
| SHA1: | 9486F8855AA0640424C841AFB23ED90AD01E34B3 |
| SHA256: | ABF26C0F72657BD6204260BA0E2E027F8E78FCD3C9530CD98AC01F91D824AA56 |
| SSDEEP: | 3:N1KaKElobByISxVU9UhM/dNCK+NyAX6L:Ca5otyIQVUFdNwNyAX6L |
MALICIOUS
Application was dropped or rewritten from another process
- slido_switcher_1_3_2_3708.exe (PID: 856)
- Slido Switcher.exe (PID: 3644)
- CefSharp.BrowserSubprocess.exe (PID: 3244)
- CefSharp.BrowserSubprocess.exe (PID: 3168)
- CefSharp.BrowserSubprocess.exe (PID: 2608)
Loads dropped or rewritten executable
- CefSharp.BrowserSubprocess.exe (PID: 3244)
- Slido Switcher.exe (PID: 3644)
- CefSharp.BrowserSubprocess.exe (PID: 2608)
- CefSharp.BrowserSubprocess.exe (PID: 3168)
Loads the Task Scheduler DLL interface
- slido_switcher_1_3_2_3708.exe (PID: 856)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1156)
- msiexec.exe (PID: 3344)
- slido_switcher_1_3_2_3708.exe (PID: 856)
- msiexec.exe (PID: 2244)
Executed as Windows Service
- vssvc.exe (PID: 852)
Creates files in the user directory
- msiexec.exe (PID: 2244)
- slido_switcher_1_3_2_3708.exe (PID: 856)
Starts Microsoft Installer
- slido_switcher_1_3_2_3708.exe (PID: 856)
Reads Environment values
- Slido Switcher.exe (PID: 3644)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1156)
INFO
Application launched itself
- chrome.exe (PID: 1156)
- msiexec.exe (PID: 2244)
Reads the hosts file
- chrome.exe (PID: 1156)
- chrome.exe (PID: 2728)
- CefSharp.BrowserSubprocess.exe (PID: 3244)
- Slido Switcher.exe (PID: 3644)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2536)
- MsiExec.exe (PID: 3640)
- MsiExec.exe (PID: 564)
Reads Internet Cache Settings
- chrome.exe (PID: 1156)
Searches for installed software
- msiexec.exe (PID: 2244)
Low-level read access rights to disk partition
- vssvc.exe (PID: 852)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2244)
Creates a software uninstall entry
- msiexec.exe (PID: 2244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
47
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1071742923819723109 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | C:\Windows\system32\MsiExec.exe -Embedding 2746C49F715EC1474DA03156200E15DC | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
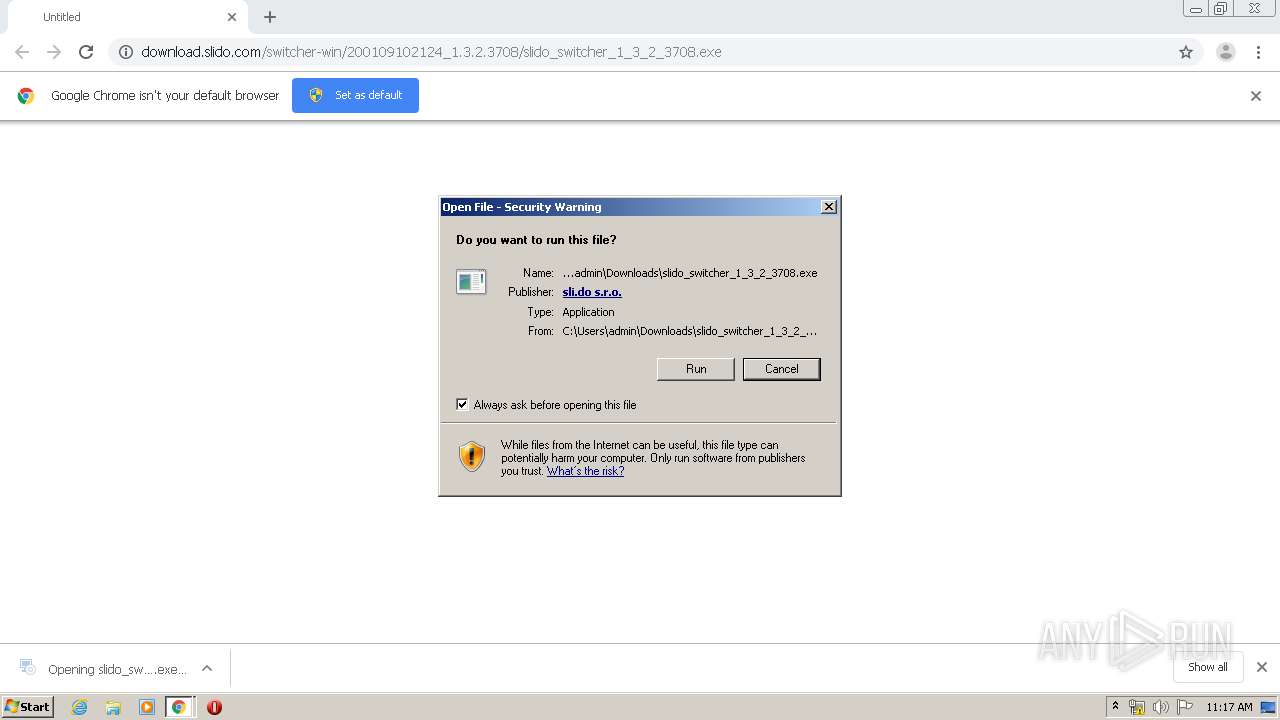
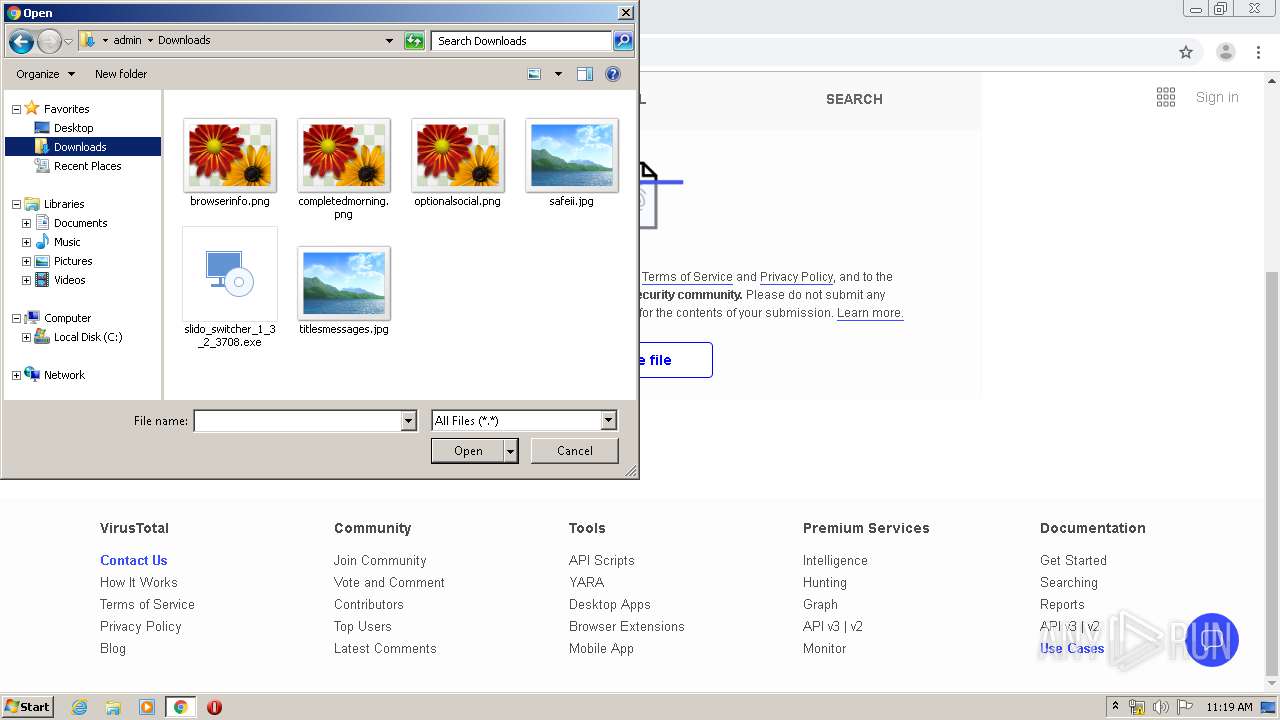
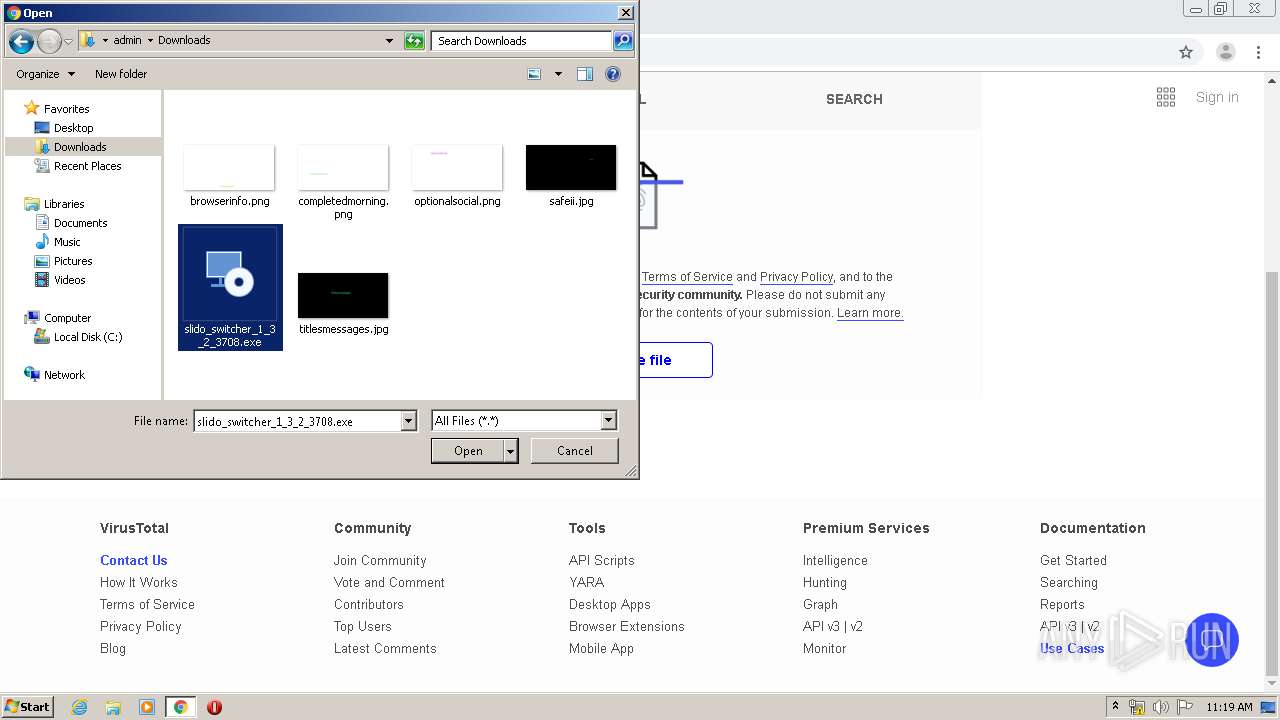
| 856 | "C:\Users\admin\Downloads\slido_switcher_1_3_2_3708.exe" | C:\Users\admin\Downloads\slido_switcher_1_3_2_3708.exe | chrome.exe | ||||||||||||
User: admin Company: sli.do s. r. o Integrity Level: MEDIUM Description: Slido Switcher Installer Exit code: 0 Version: 1.3.2.3708 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2253773738816737512 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://download.slido.com/switcher-win/200109102124_1.3.2.3708/slido_switcher_1_3_2_3708.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14808921748125408917 --mojo-platform-channel-handle=5264 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9613616644789707109 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9419493780819553829 --mojo-platform-channel-handle=5180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8244386065002574074,10736527974754046981,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13657001582377520551 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 359
Read events
2 749
Write events
592
Delete events
18
Modification events
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1156-13233233755880000 |
Value: 259 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1156) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
82
Suspicious files
94
Text files
191
Unknown types
78
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EB28E5C-484.pma | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5605923a-d7b8-4b10-8a14-e23f6bb491d3.tmp | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e1cd.TMP | text | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFa6e2b7.TMP | text | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e344.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
49
DNS requests
32
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2728 | chrome.exe | GET | 200 | 74.125.173.231:80 | http://r2---sn-4g5ednz7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=92.118.13.5&mm=28&mn=sn-4g5ednz7&ms=nvh&mt=1588760235&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
2728 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
2728 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
2728 | chrome.exe | GET | 200 | 74.125.173.233:80 | http://r4---sn-4g5ednz7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=92.118.13.5&mm=28&mn=sn-4g5ednz7&ms=nvh&mt=1588760299&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2728 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2728 | chrome.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2728 | chrome.exe | 143.204.202.15:80 | download.slido.com | — | US | suspicious |
2728 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2728 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2728 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3244 | CefSharp.BrowserSubprocess.exe | 216.58.205.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
— | — | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
3644 | Slido Switcher.exe | 54.217.226.25:20000 | api.logentries.com | Amazon.com, Inc. | IE | unknown |
3244 | CefSharp.BrowserSubprocess.exe | 54.182.0.92:443 | cdn.statuspage.io | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.slido.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
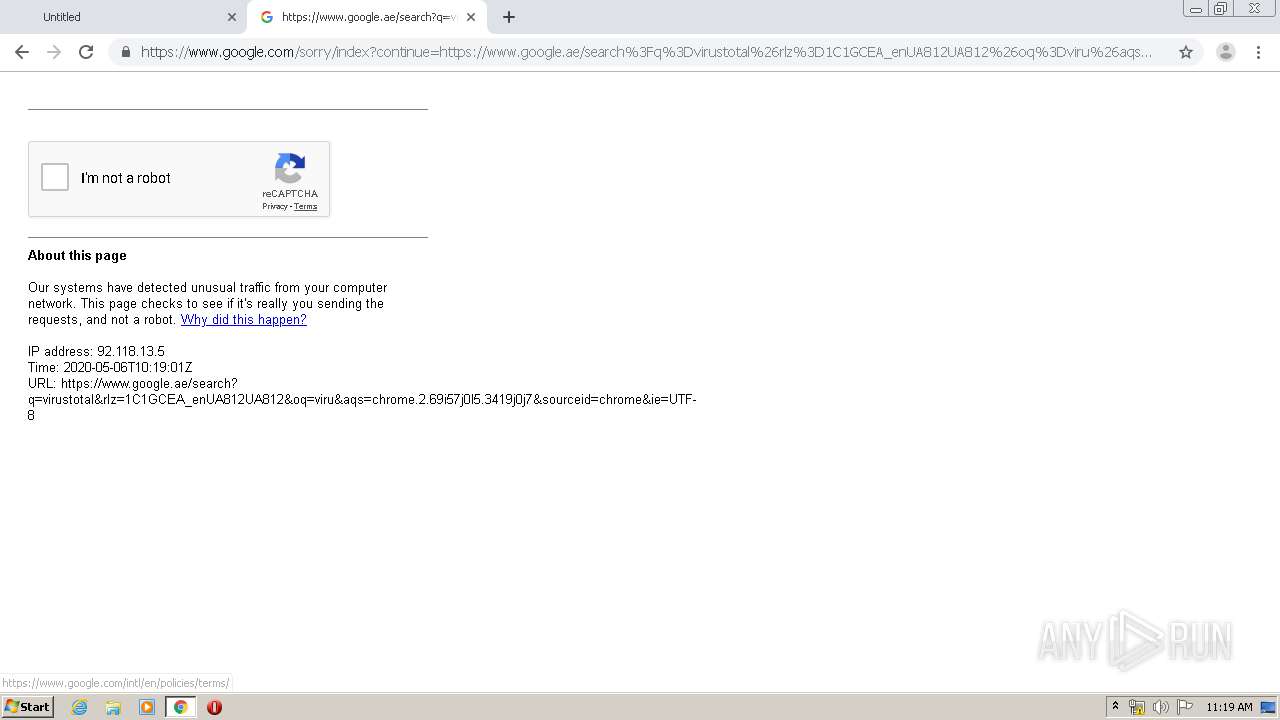
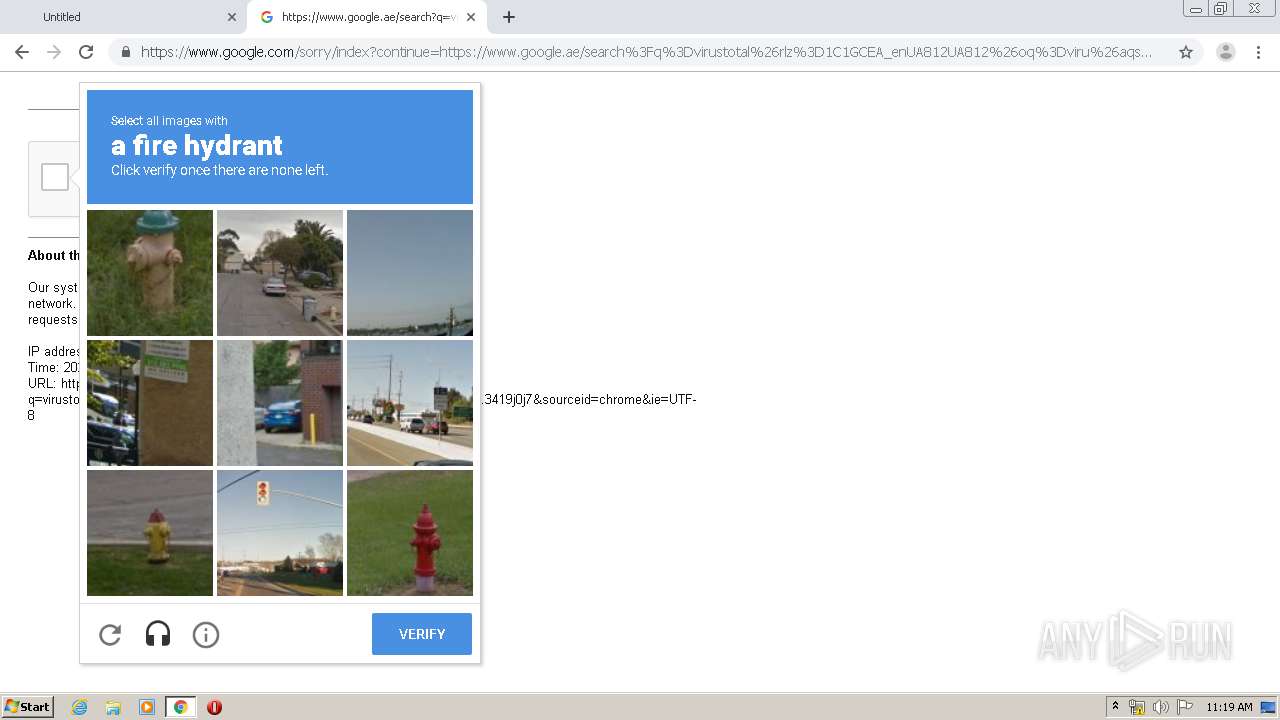
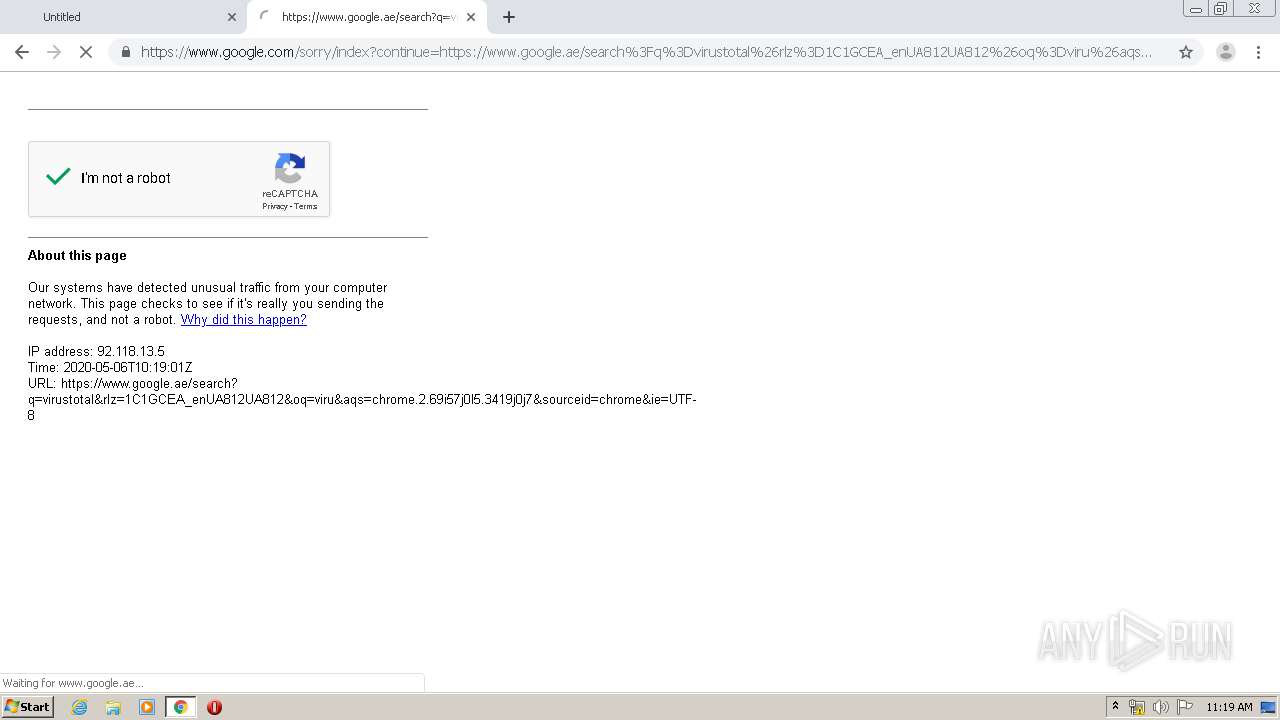
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
api.logentries.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2728 | chrome.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
2728 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
slido_switcher_1_3_2_3708.exe | [AVX_CRT_Fix][C:\Users\admin\Downloads\slido_switcher_1_3_2_3708.exe] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSI2912.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSI29A0.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSI2B25.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSI2BB3.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSI2BD3.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSI2C13.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSI2C23.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIE5BB.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIE8E9.tmp] CPU: __isa_available = 5
|