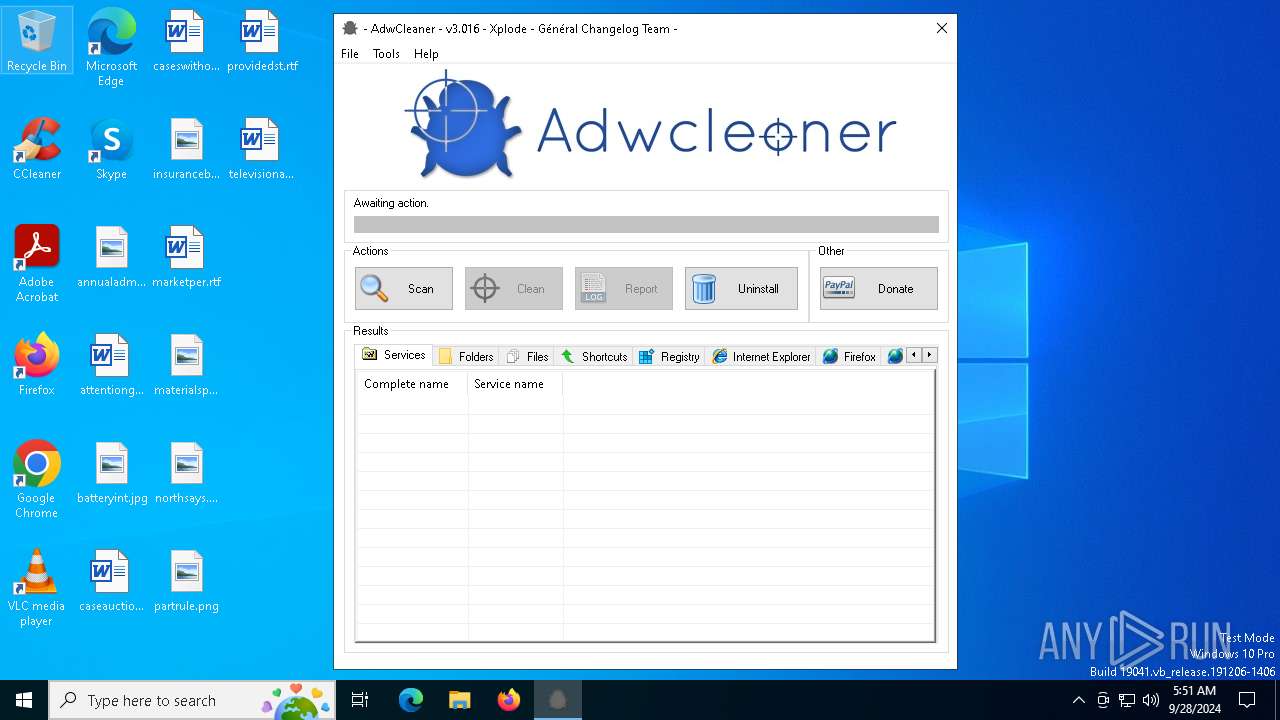
| File name: | adwcleaner.exe |
| Full analysis: | https://app.any.run/tasks/37e5b5a0-77e2-4b9c-baa4-bfbec589fb44 |
| Verdict: | Malicious activity |
| Analysis date: | September 28, 2024, 05:51:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | AF5C84446657B48C9B9B870C46438261 |
| SHA1: | 43BADA1A694B18D64B4358E6F9D746935C517FD1 |
| SHA256: | ABD5CC41FEAA7CDA8803FFB70F4C491ED7FE423A6372A77305E9D584DB90AB51 |
| SSDEEP: | 49152:M4Y2A1wjRsB5CExEf7BswBaTnxNFHjEpSdAzISLgMNUAPD25Q0zxWHV8dd0sY0d8:kzutsBUnPA9bESfE/PqpxWGdd0sYswXP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- adwcleaner.exe (PID: 5376)
Reads security settings of Internet Explorer
- adwcleaner.exe (PID: 5376)
Potential Corporate Privacy Violation
- adwcleaner.exe (PID: 5376)
INFO
Reads mouse settings
- adwcleaner.exe (PID: 5376)
Checks supported languages
- adwcleaner.exe (PID: 5376)
Reads the computer name
- adwcleaner.exe (PID: 5376)
Create files in a temporary directory
- adwcleaner.exe (PID: 5376)
UPX packer has been detected
- adwcleaner.exe (PID: 5376)
Checks proxy server information
- adwcleaner.exe (PID: 5376)
The process uses AutoIt
- adwcleaner.exe (PID: 5376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:01:29 21:32:28+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 274432 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | 577536 |
| EntryPoint: | 0xcfe90 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.1.6 |
| ProductVersionNumber: | 3.3.8.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | French |
| CharacterSet: | Unicode |
| FileVersion: | 3.0.1.6 |
Total processes
134
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3592 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | "C:\Users\admin\AppData\Local\Temp\adwcleaner.exe" | C:\Users\admin\AppData\Local\Temp\adwcleaner.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 3.0.1.6 Modules
| |||||||||||||||
| 5144 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | "C:\Users\admin\AppData\Local\Temp\adwcleaner.exe" | C:\Users\admin\AppData\Local\Temp\adwcleaner.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 3.0.1.6 Modules
| |||||||||||||||
Total events
614
Read events
609
Write events
5
Delete events
0
Modification events
| (PID) Process: | (5376) adwcleaner.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5376) adwcleaner.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5376) adwcleaner.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5376) adwcleaner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\AdwCleaner |
| Operation: | write | Name: | ScanCount |
Value: 0 | |||
| (PID) Process: | (5376) adwcleaner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\AdwCleaner |
| Operation: | write | Name: | CleanCount |
Value: 0 | |||
Executable files
2
Suspicious files
6
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\Cleaning.ico | image | |
MD5:CF07AC6C4C4E1E040C5D728B69A80069 | SHA256:3C17249CDA19D715431492A4FD2F8F3AEE3F277C0361650692DD682A69E4BDE9 | |||
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\Donate.ico | image | |
MD5:E6676D0A8C4DD19FB7552CB146C055BD | SHA256:35A737BDEC77AA595180AA7E30E7F39294996E17130067D386A6A321A010581B | |||
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\aut510B.tmp | image | |
MD5:94E302CF8C760F9A35EE4B02CA3869E8 | SHA256:738C761278EA5FB238A50C7D9A0DCDAE8E51A4C9D65849E1DF966D539C71C085 | |||
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\AdwCleaner.jpg | image | |
MD5:94E302CF8C760F9A35EE4B02CA3869E8 | SHA256:738C761278EA5FB238A50C7D9A0DCDAE8E51A4C9D65849E1DF966D539C71C085 | |||
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\aut513E.tmp | binary | |
MD5:96898098E62003CE3891D2DDCD446FE1 | SHA256:7F6DFA58B11D5AD9A92FDA878F8CF080B6E23C1ED83A7FDA96FB1E8F17ED271F | |||
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\aut515F.tmp | executable | |
MD5:F0A5B44B9B8A23E2F2950B346B5C7718 | SHA256:445FFEEF94FFEFBAD8545FD870748991087B673296FB1895D5274DFF023B7E05 | |||
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\aut512C.tmp | binary | |
MD5:A06A9D20DE746774A4910478182E3BF4 | SHA256:BA699482D91895E93E54C623F6F7F7CBA1DA666D40F52225EE8215EDDCC40432 | |||
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\aut511C.tmp | binary | |
MD5:81392B8F2979C790246B61D133A47935 | SHA256:59E6AA055B535CBE7DEA7598E02E9FB790AC49607F5CBAB110CD90FD1A0C0650 | |||
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\Uninstall.ico | image | |
MD5:CC64696634EDC8E7217DF66563125786 | SHA256:746C6F7BB65A32E8ECDB4610021680D842AAB1BCA5A46C3450F493459A71FB59 | |||
| 5376 | adwcleaner.exe | C:\Users\admin\AppData\Local\Temp\aut513D.tmp | binary | |
MD5:6C5974F3E678E2186BED3DEED8B3F7A2 | SHA256:27E882128A364A5D2272A0957AD17B94117EE3C3E44EA5E86EBE99A90A347701 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
45
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5376 | adwcleaner.exe | GET | 404 | 54.38.45.96:80 | http://sd-1.archive-host.com/membres/up/17959594961240255/Version.txt | unknown | — | — | malicious |
2536 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5056 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5056 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6536 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6336 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5376 | adwcleaner.exe | 54.38.45.96:80 | sd-1.archive-host.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
sd-1.archive-host.com |
| unknown |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5376 | adwcleaner.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |