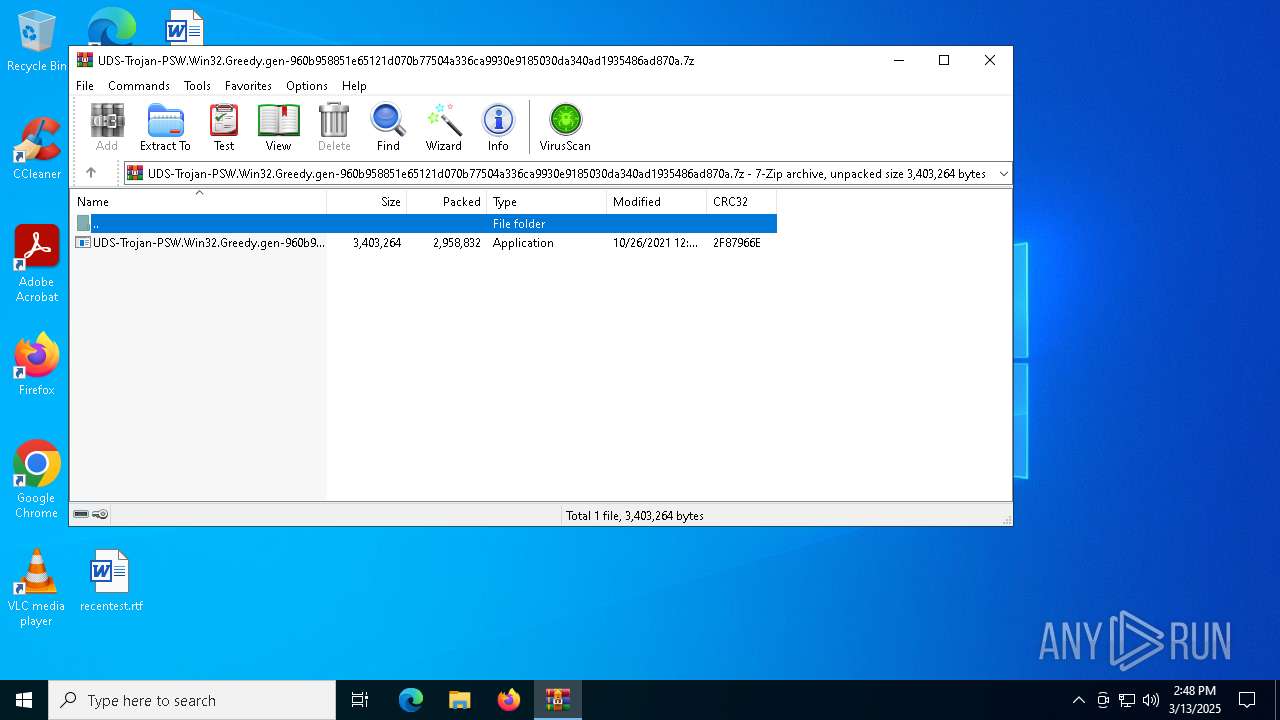
| File name: | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.7z |
| Full analysis: | https://app.any.run/tasks/f313ba6e-049f-4886-b1b7-773ffdfa629e |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2025, 14:48:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | DFFAB0B646FF678E78AC00933DB2E732 |
| SHA1: | 4CDC9D0E3A687BFD7FE27330822FEBE5D1349391 |
| SHA256: | ABCEEB4C960F3709C8022F5FCB0B732A5246E3B98A5B44ECADBEFE352E474D85 |
| SSDEEP: | 98304:0GYM8aVOyCuLvKdNWcjTYRoId8/jRwH9mqzoZlNyG4YGo0aoWV11U+hq18Iv52HN:sPaK |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5868)
SUSPICIOUS
Checks for external IP
- UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe (PID: 1128)
- svchost.exe (PID: 2196)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe (PID: 1128)
INFO
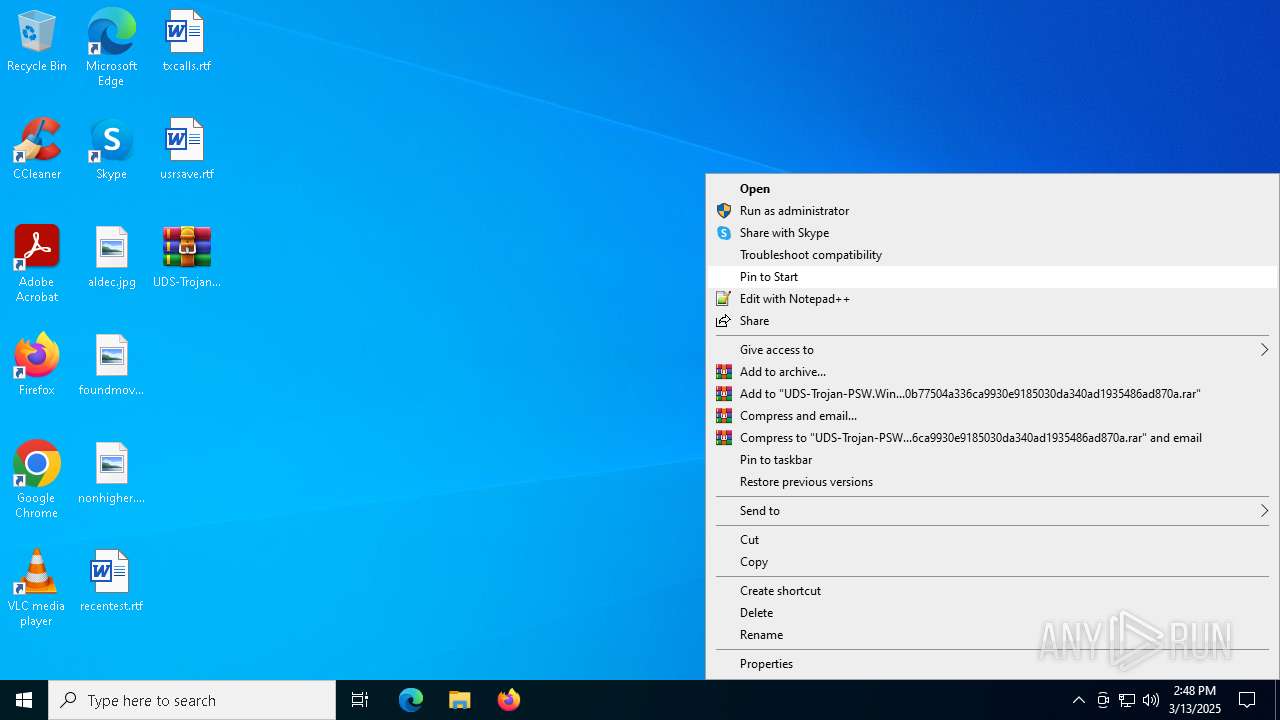
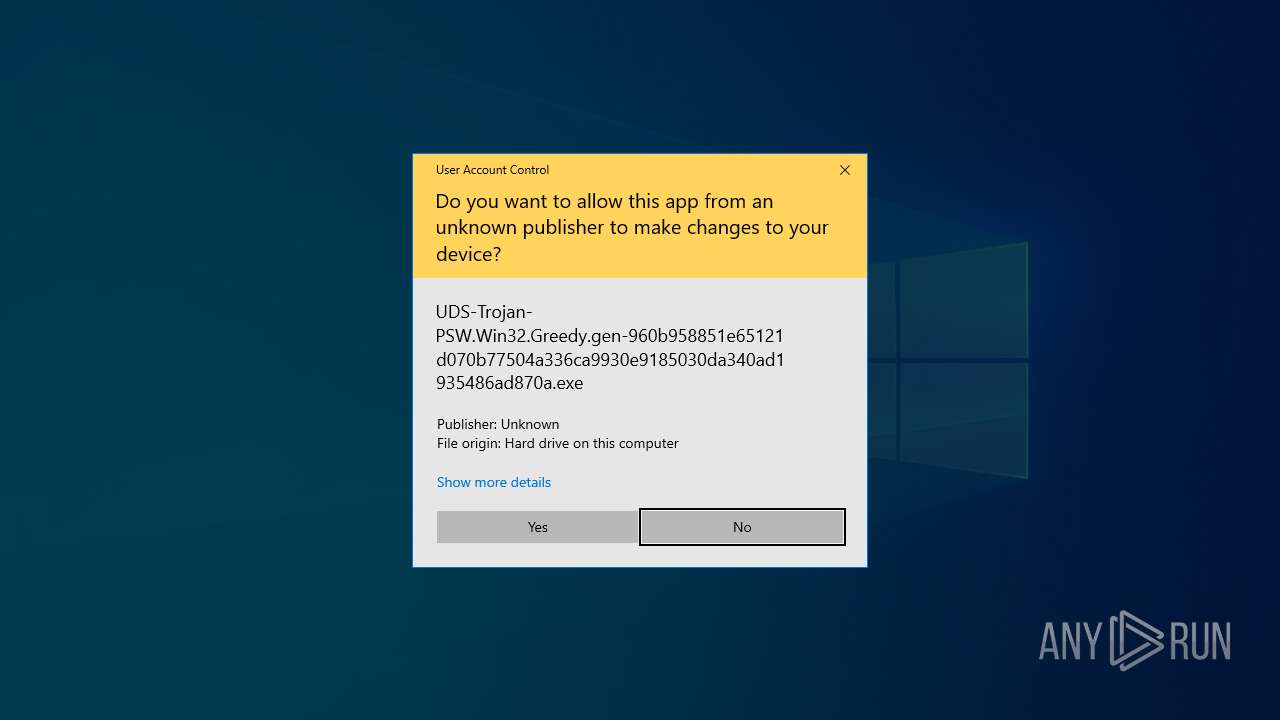
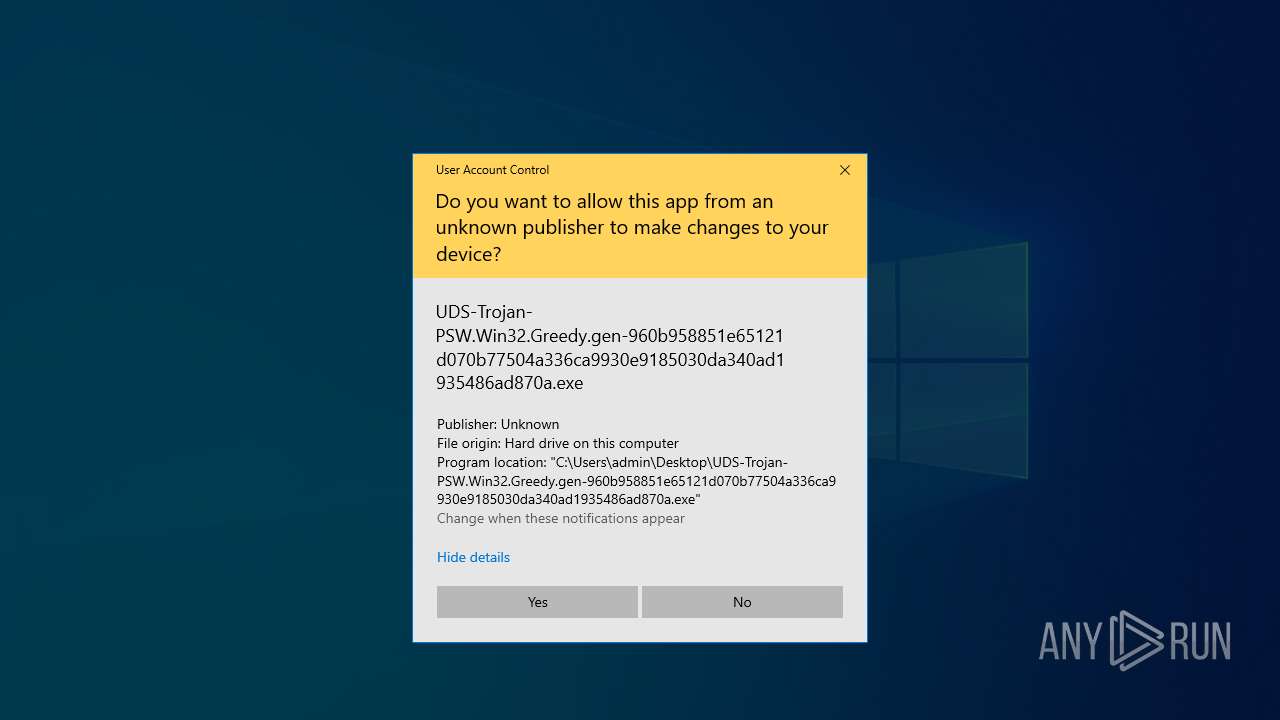
Manual execution by a user
- UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe (PID: 1128)
The sample compiled with english language support
- WinRAR.exe (PID: 5868)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2021:10:26 12:04:04+00:00 |
| ArchivedFileName: | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe |
Total processes
145
Monitored processes
10
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1128 | "C:\Users\admin\Desktop\UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe" | C:\Users\admin\Desktop\UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1324 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3896 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
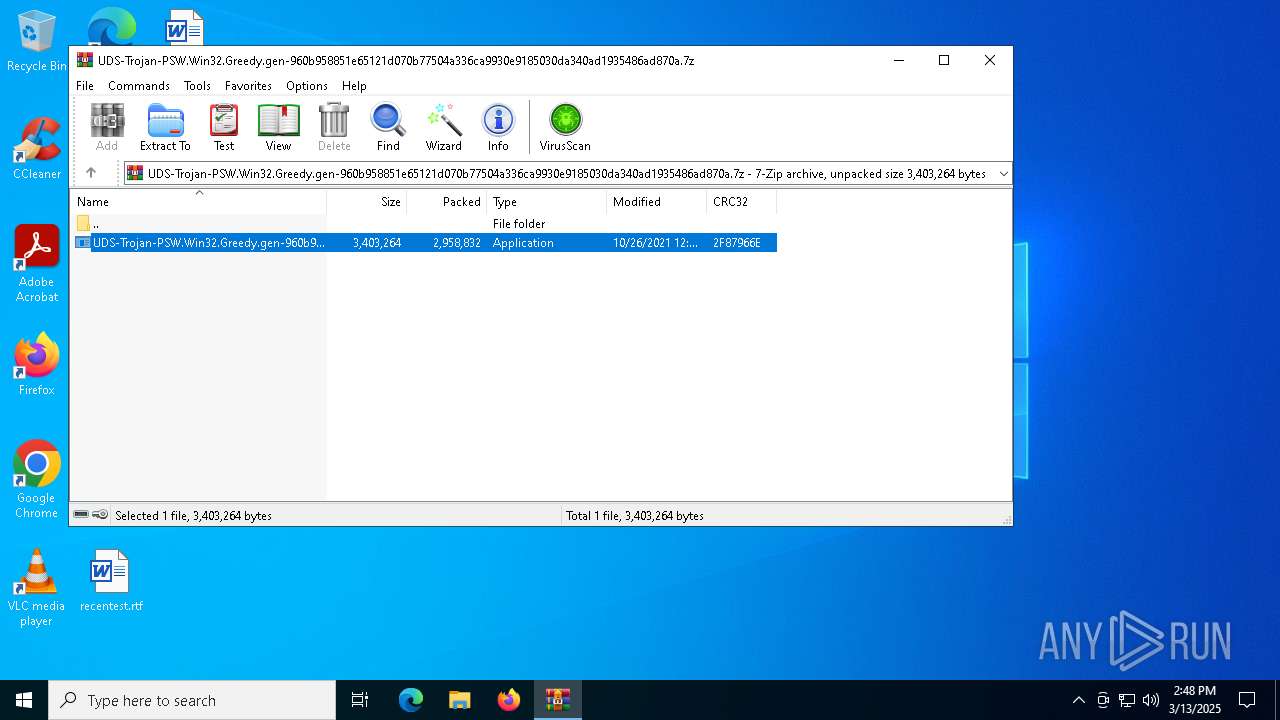
| 5868 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6576 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6700 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 354
Read events
3 320
Write events
34
Delete events
0
Modification events
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.7z | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
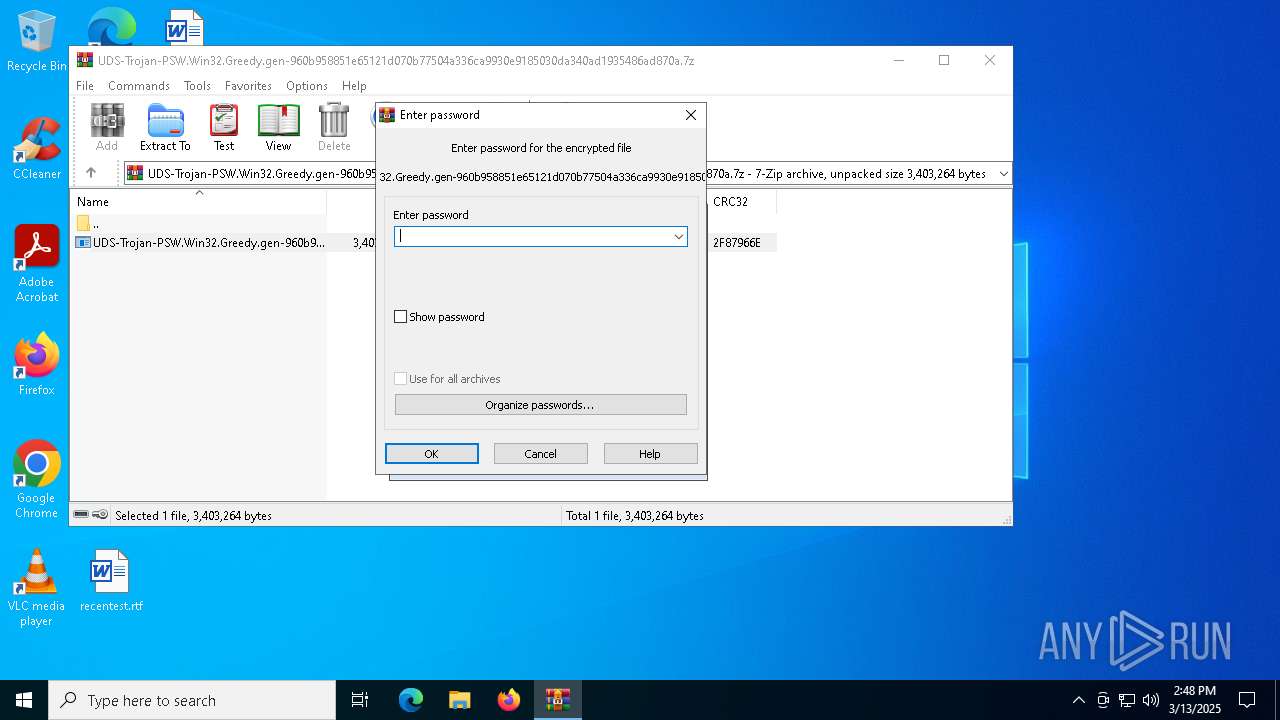
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5868) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
1
Suspicious files
8
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6700 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\a83c89d9-d669-4111-a89f-370682032bc7.down_data | — | |
MD5:— | SHA256:— | |||
| 6700 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\a83c89d9-d669-4111-a89f-370682032bc7.3be0c4dc-2641-4e62-a7c8-cc2abc355539.down_meta | binary | |
MD5:2AD554A7C5A7A6617F10F7963AF780CD | SHA256:DEC394648286A4E8DDFC33DE2CE6FA65E2193F9BC0DDEA07839CEC8FAB51E4EE | |||
| 6700 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:9FA7CCABC494A5328612D36DD19B8E46 | SHA256:0D0B2B024CD660B45A6646F77B717CCD34A8C0D3EC4D5451D53DD436E87F531D | |||
| 6700 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:E398FD732C8FC2A4445C0197E1733502 | SHA256:C8B6CF399A67742A7BA7057EF9432FCFF486E2D4E1EC399C46D986DE0A15C698 | |||
| 1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | C:\Users\admin\AppData\Local\Temp\DE_ZNzCCdNWxg.zip | compressed | |
MD5:F18BE7F7249D671DD8AAE45CA3D11DFA | SHA256:33A9589E6F7DEBF33F0CA9C57520F8802EEA8476FA1C09A4C1FB9713FA8EC5B6 | |||
| 1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | C:\Users\admin\AppData\Local\Temp\5SF1v6JpjQ | binary | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
| 1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | C:\Users\admin\AppData\Local\Temp\Web Data | binary | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 5868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb5868.13311\UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | executable | |
MD5:3DC4229DC260FB03AAB49C38278C9C22 | SHA256:960B958851E65121D070B77504A336CA9930E9185030DA340AD1935486AD870A | |||
| 1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | C:\Users\admin\AppData\Local\Temp\NNZAAuC0lr.png | image | |
MD5:D3653C5C82A1942BDB74DD0EF9817D7E | SHA256:87F037391FF8D7BBABA28D25B09649E225A9FD67C79B9669E9C4961778DD6F90 | |||
| 1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | C:\Users\admin\AppData\Local\Temp\w2ZmiWfICb.png | image | |
MD5:D3653C5C82A1942BDB74DD0EF9817D7E | SHA256:87F037391FF8D7BBABA28D25B09649E225A9FD67C79B9669E9C4961778DD6F90 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
28
DNS requests
20
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4424 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=countryCode | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQDflMUbWnbjyw%3D%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | unknown | — | — | whitelisted |
3008 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6700 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3008 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6480 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4424 | backgroundTaskHost.exe | 20.103.156.88:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4424 | backgroundTaskHost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ip-api.com |
| whitelisted |
api.telegram.org |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
1128 | UDS-Trojan-PSW.Win32.Greedy.gen-960b958851e65121d070b77504a336ca9930e9185030da340ad1935486ad870a.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |