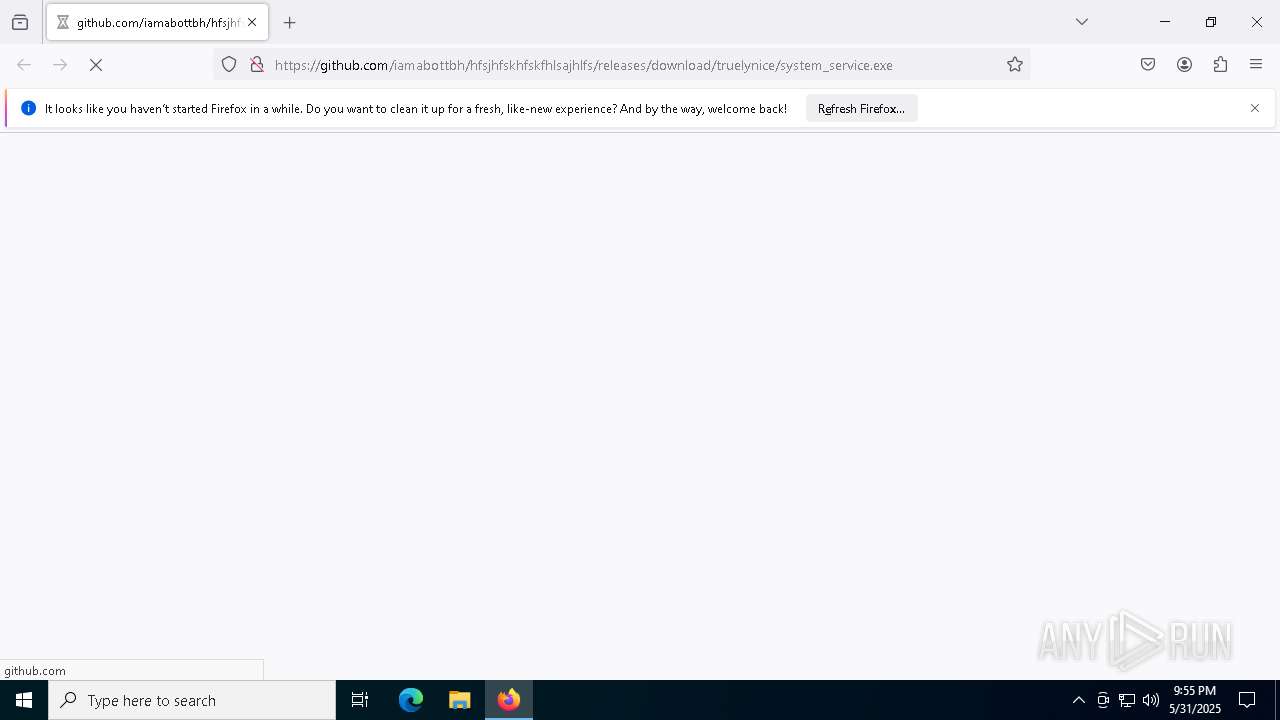
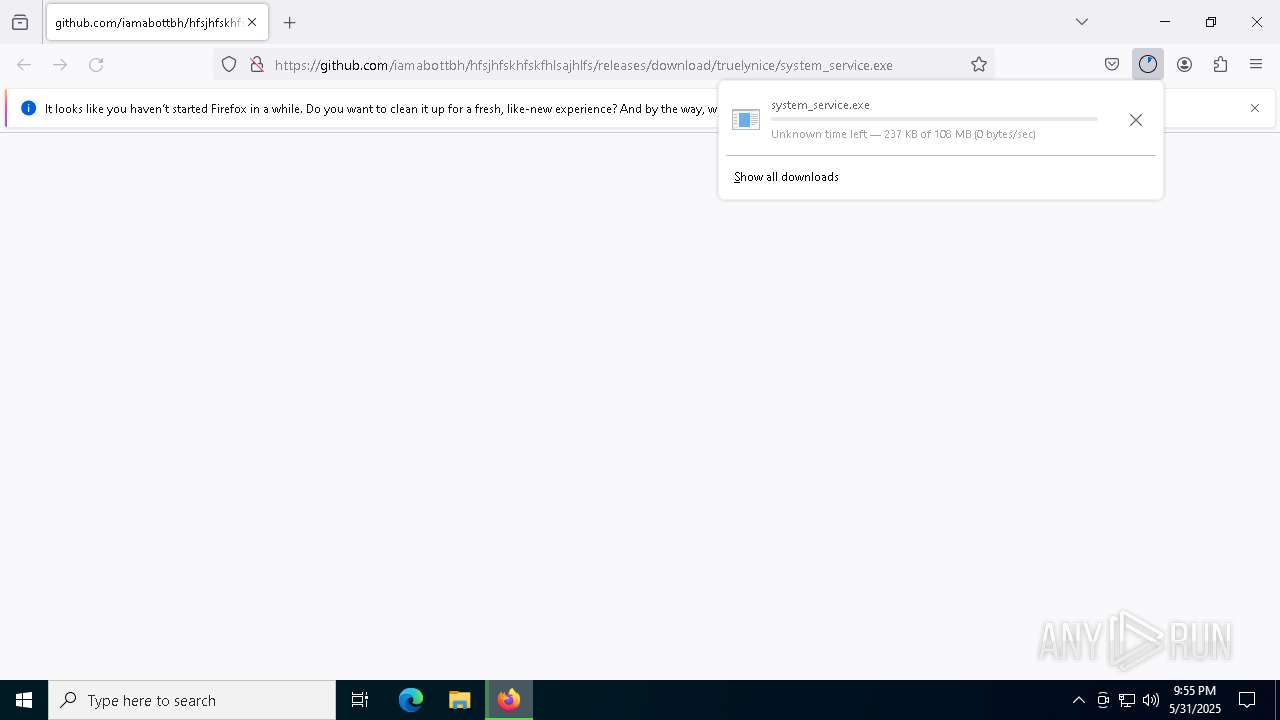
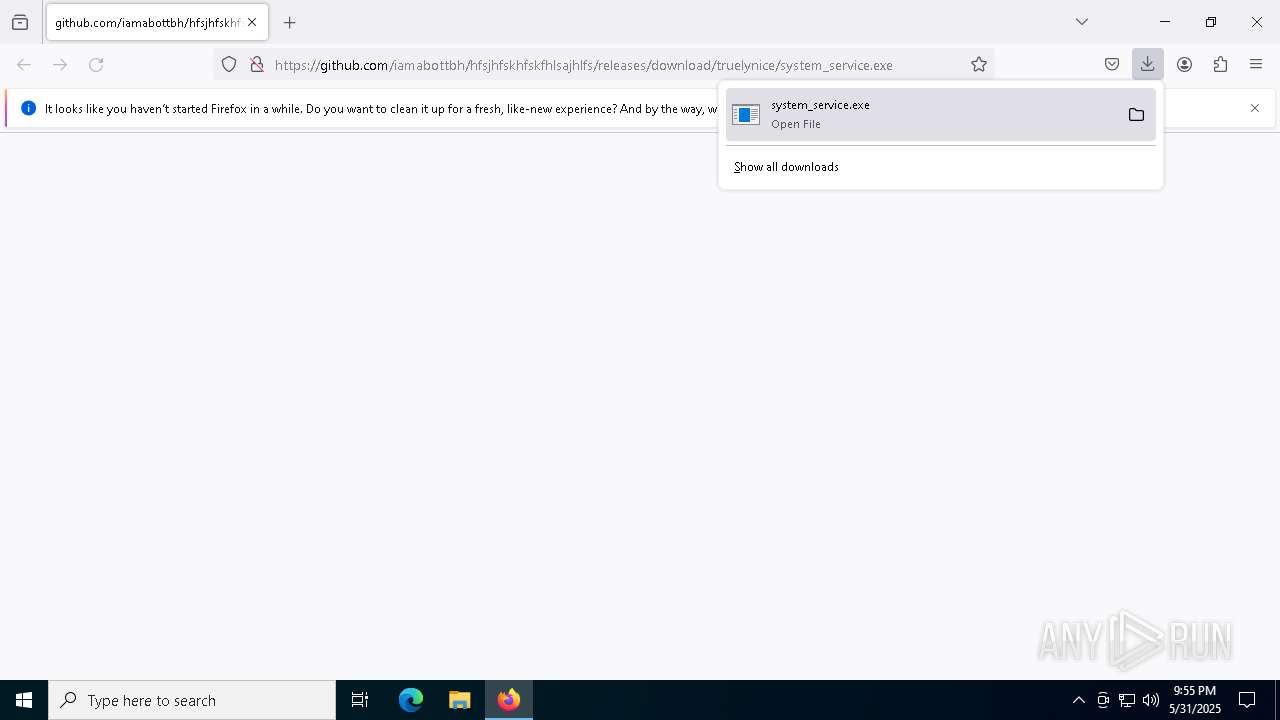
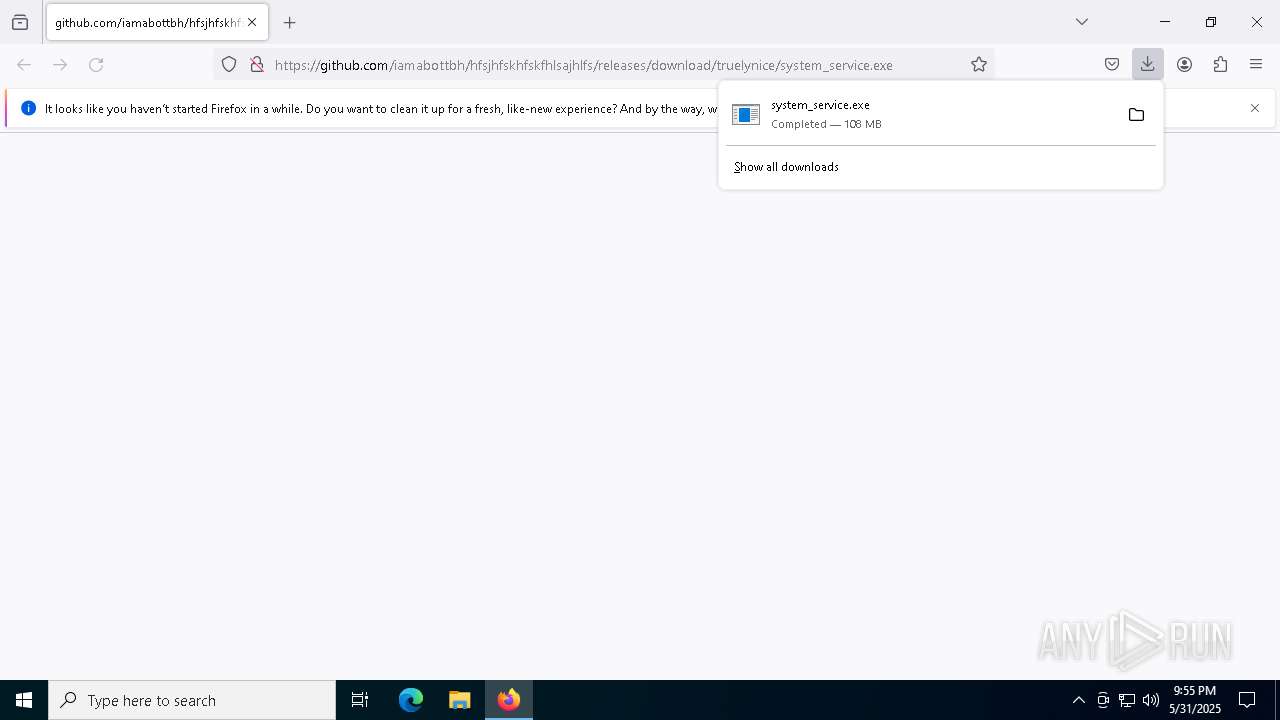
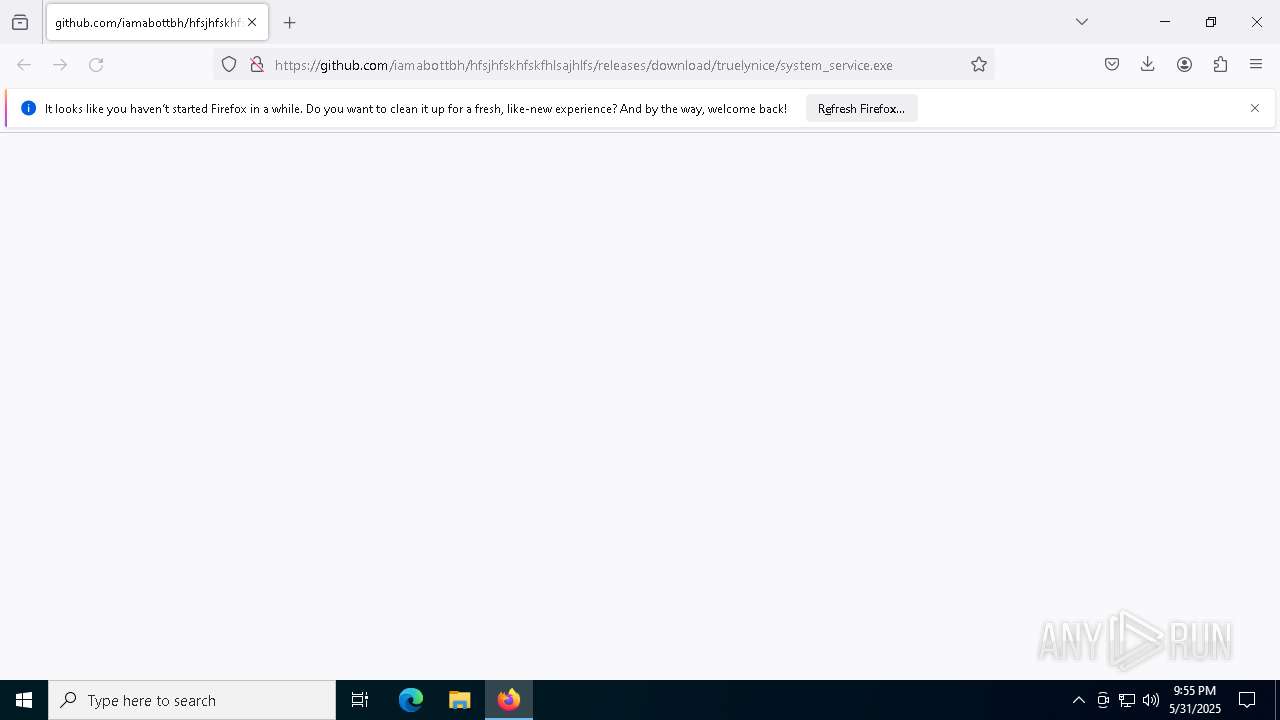
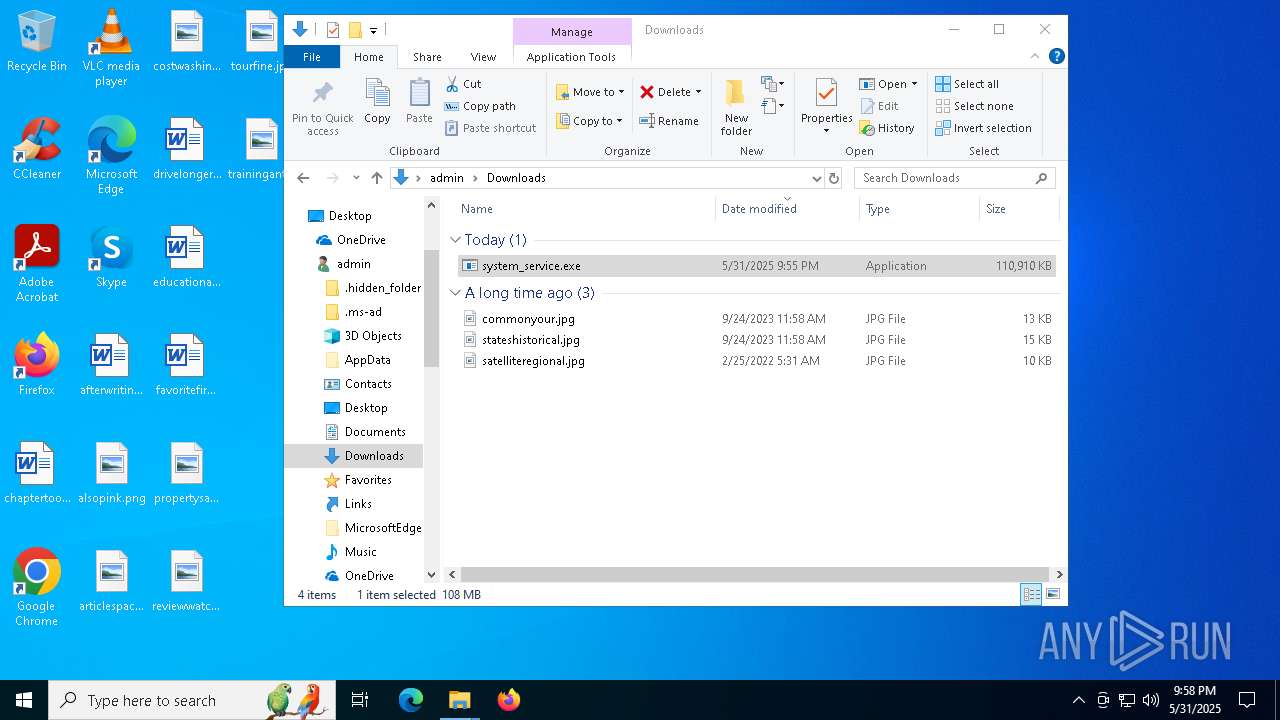
| URL: | https://github.com/iamabottbh/hfsjhfskhfskfhlsajhlfs/releases/download/truelynice/system_service.exe |
| Full analysis: | https://app.any.run/tasks/aeb17db3-d66f-466e-9ef4-d2b9f9b767fd |
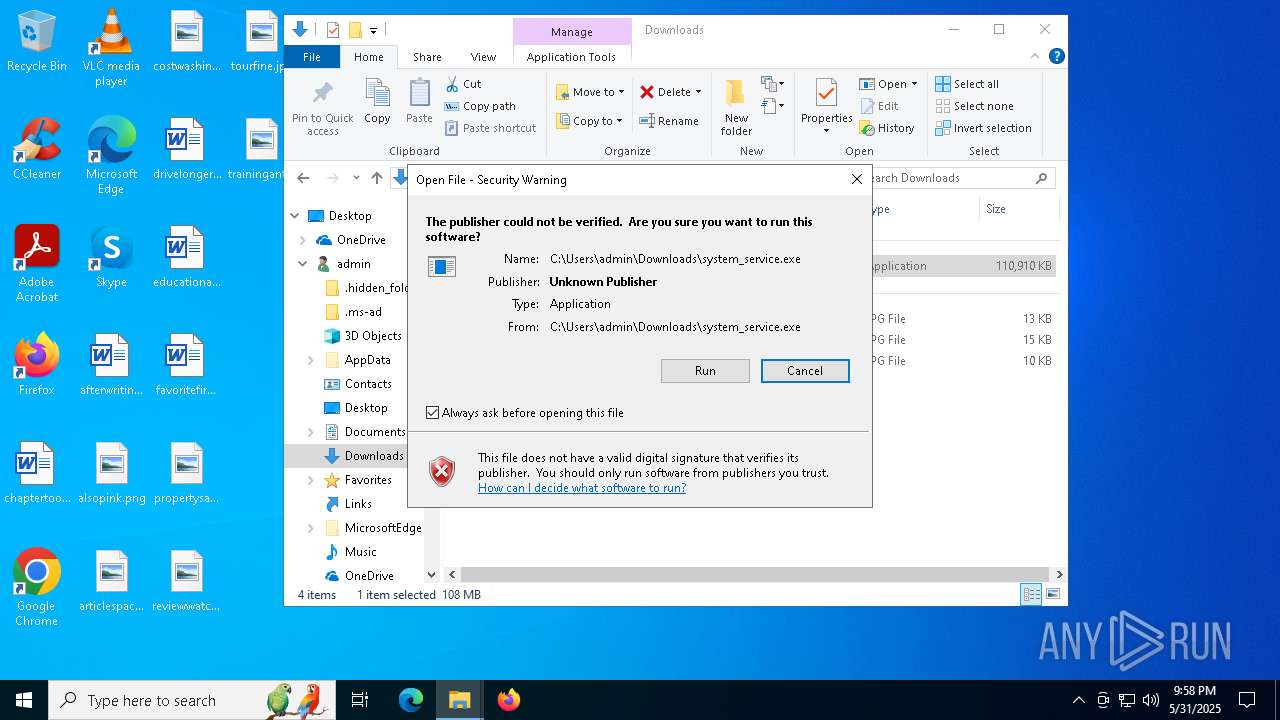
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2025, 21:55:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 423C68CBD10920BF82A7E17203BDB037 |
| SHA1: | AF01728EA0F1F33DA6C76EBA1E9C2BDB20B9E9F9 |
| SHA256: | ABC95A4C110C4F2A6DCBD671CE368F6909F01F0D027DC54A0B9860A1D6F32AA7 |
| SSDEEP: | 3:N8tEd8hEqtHRJNVRJLkCWsnGvUiXTHlA:2uqzZRJNVRJL4hXjlA |
MALICIOUS
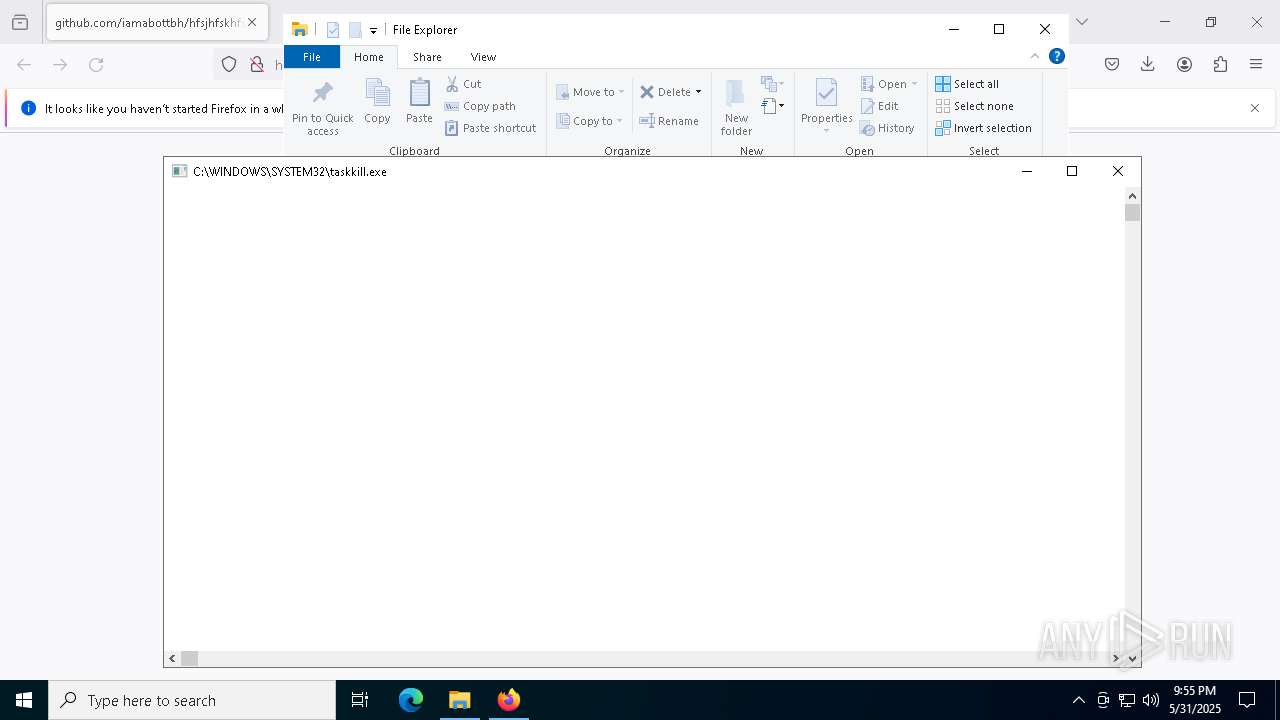
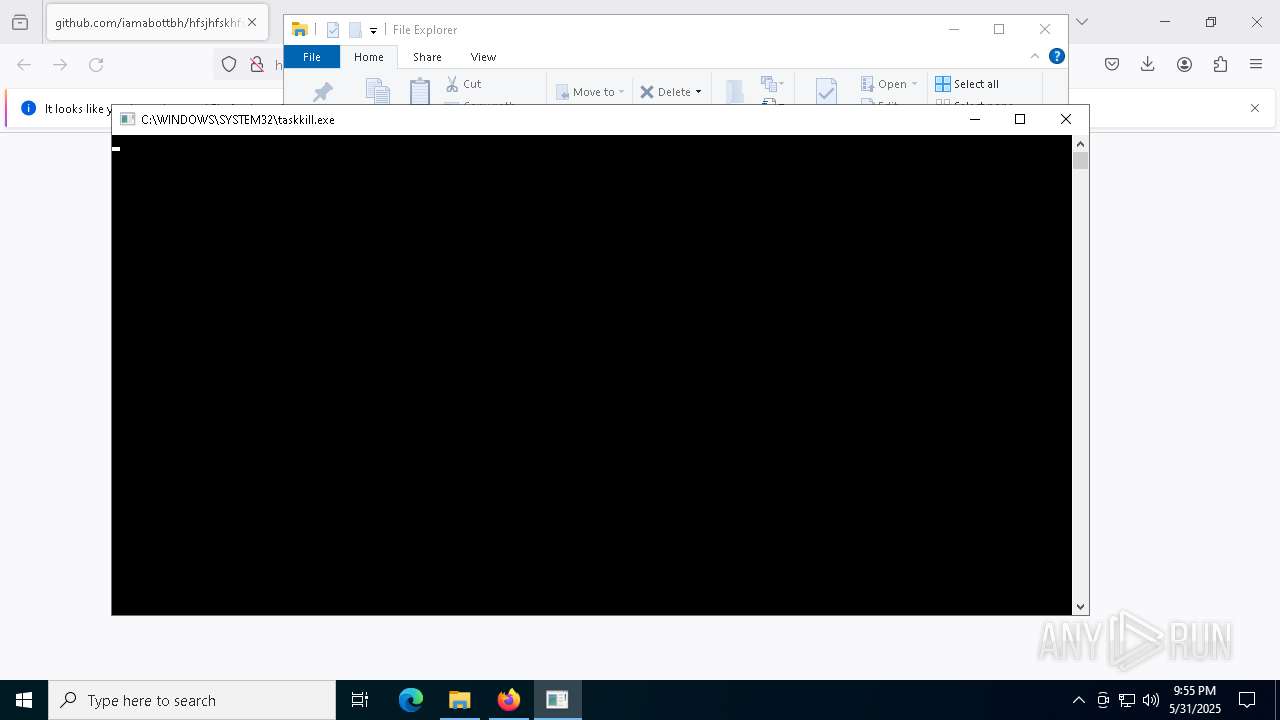
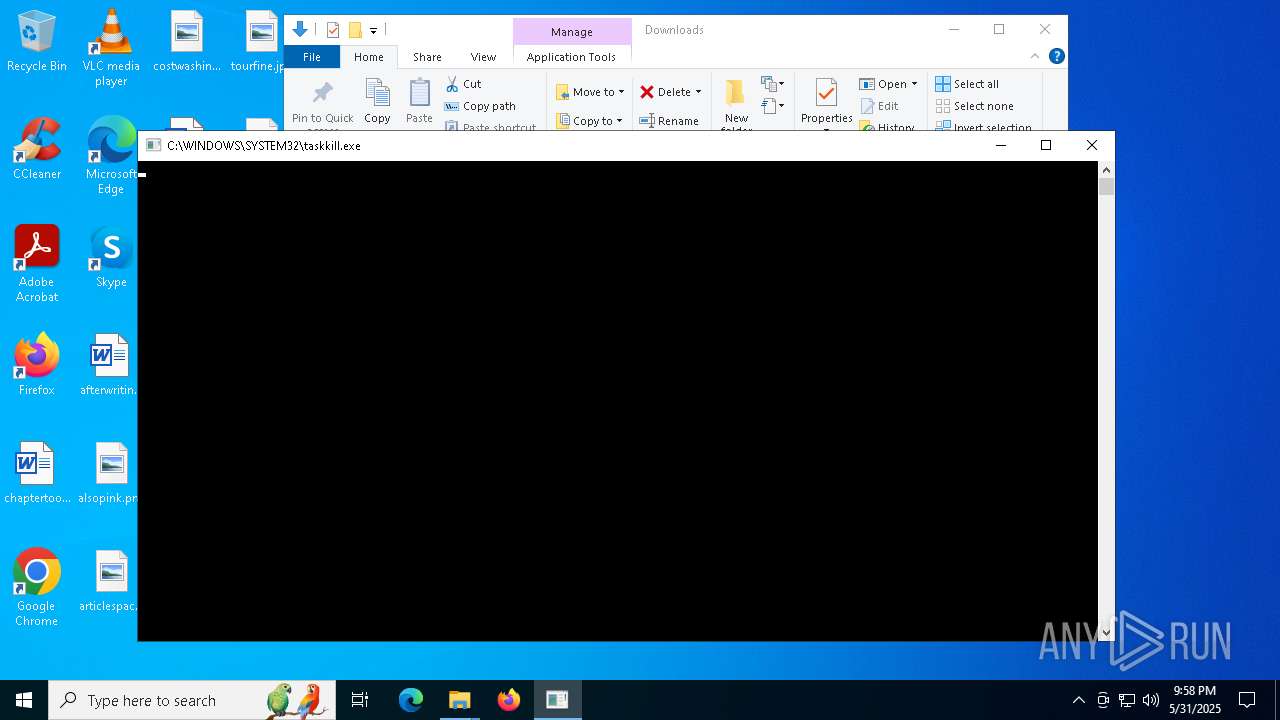
Uses TASKKILL.EXE to kill security tools
- system_service.exe (PID: 7788)
- system_service.exe (PID: 7436)
SUSPICIOUS
Executable content was dropped or overwritten
- system_service.exe (PID: 472)
- system_service.exe (PID: 668)
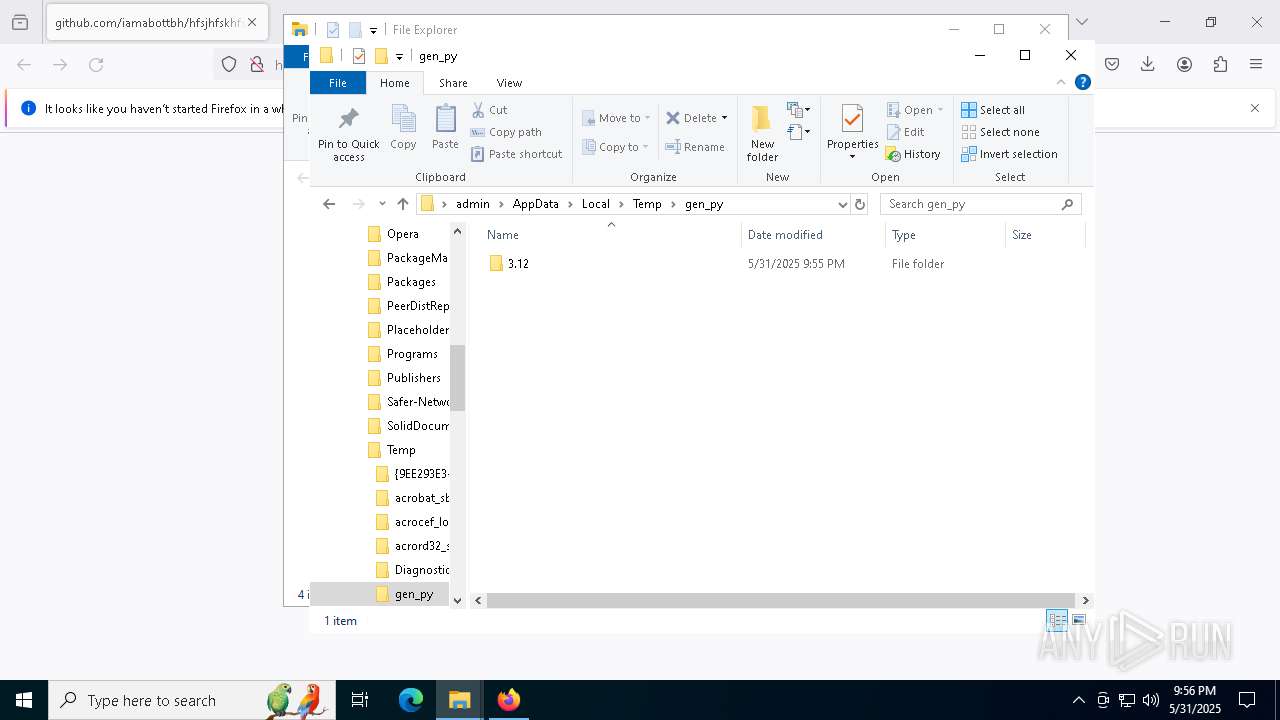
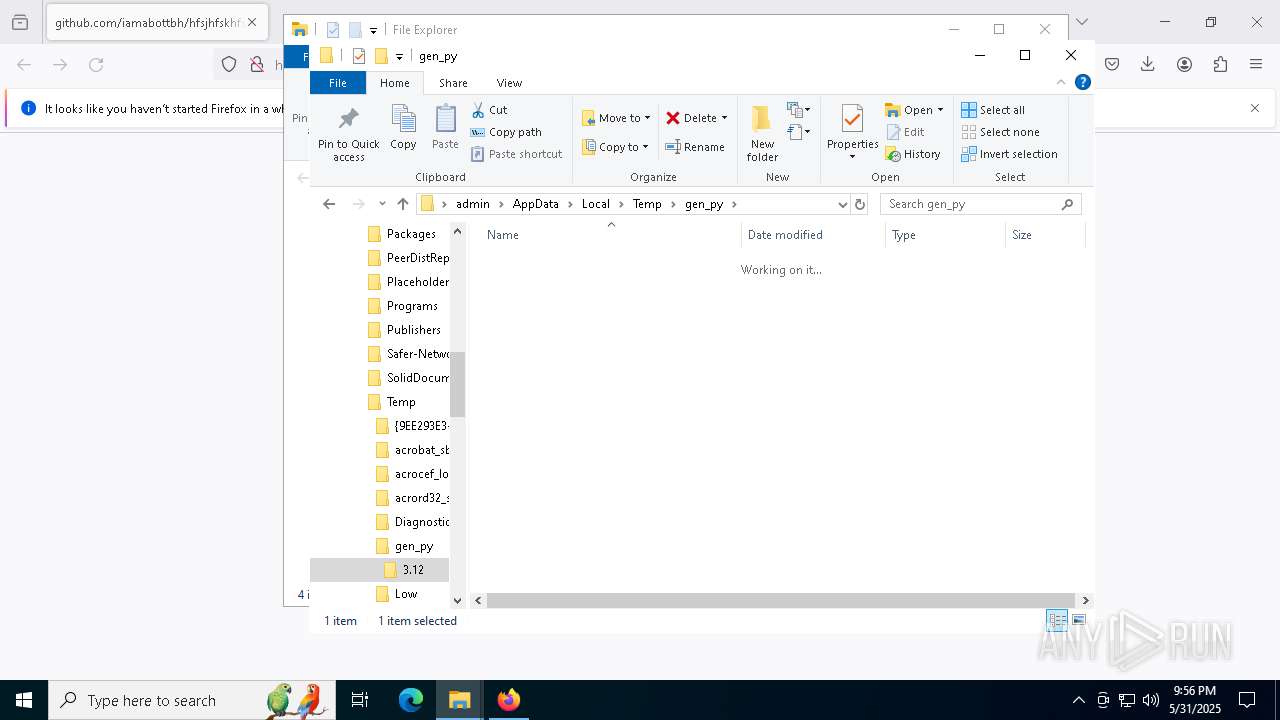
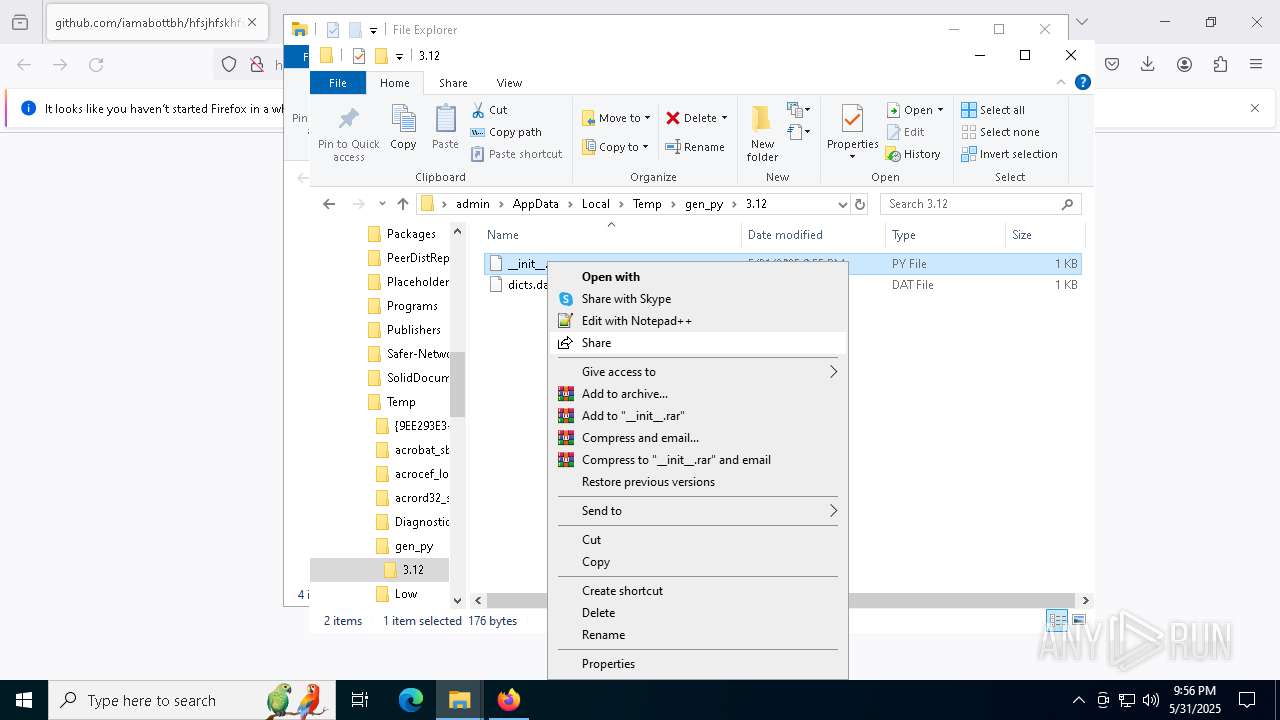
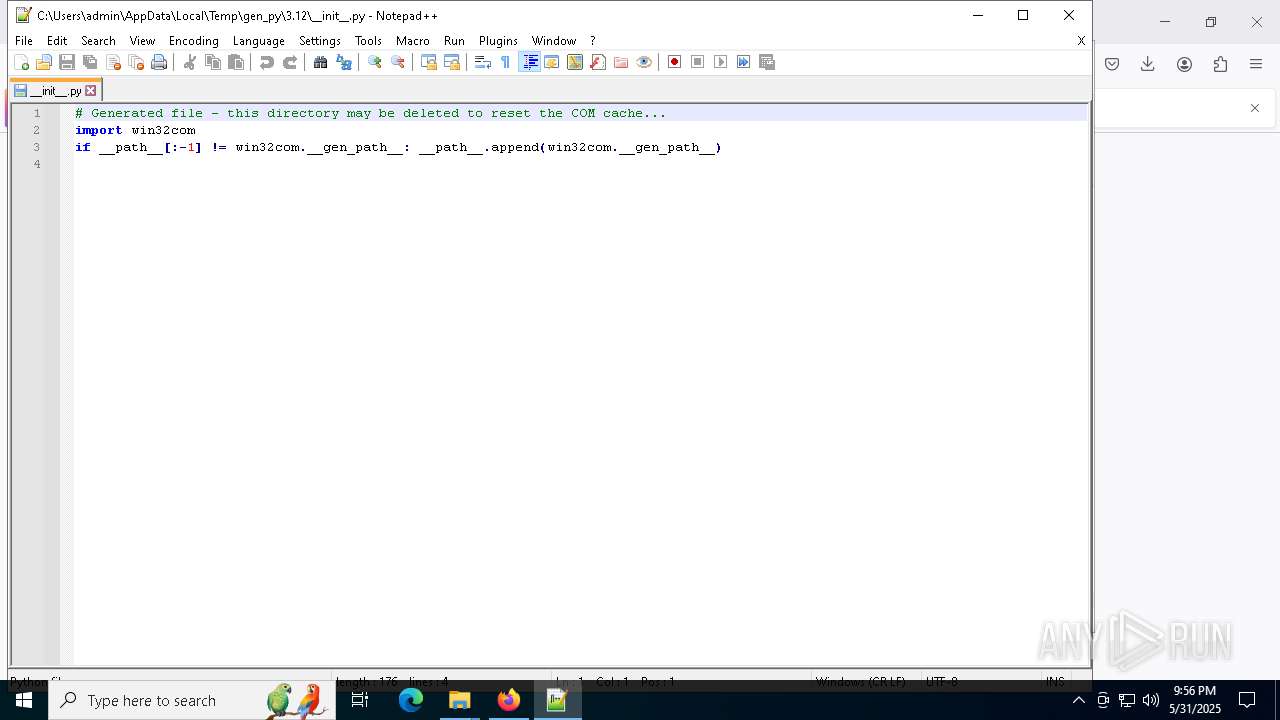
Process drops python dynamic module
- system_service.exe (PID: 472)
- system_service.exe (PID: 668)
The process drops C-runtime libraries
- system_service.exe (PID: 472)
- system_service.exe (PID: 668)
Process drops legitimate windows executable
- system_service.exe (PID: 472)
- system_service.exe (PID: 668)
Application launched itself
- system_service.exe (PID: 472)
- system_service.exe (PID: 668)
Loads Python modules
- system_service.exe (PID: 7788)
Starts CMD.EXE for commands execution
- system_service.exe (PID: 7788)
- system_service.exe (PID: 7436)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 7228)
- WMIC.exe (PID: 7500)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 7280)
- cmd.exe (PID: 456)
- cmd.exe (PID: 2124)
- cmd.exe (PID: 6676)
Uses TASKKILL.EXE to kill process
- system_service.exe (PID: 7788)
- system_service.exe (PID: 7436)
Uses WMIC.EXE to obtain physical disk drive information
- system_service.exe (PID: 7436)
- system_service.exe (PID: 7788)
The process checks if it is being run in the virtual environment
- system_service.exe (PID: 7788)
INFO
Application launched itself
- firefox.exe (PID: 3364)
- firefox.exe (PID: 2600)
Executable content was dropped or overwritten
- firefox.exe (PID: 2600)
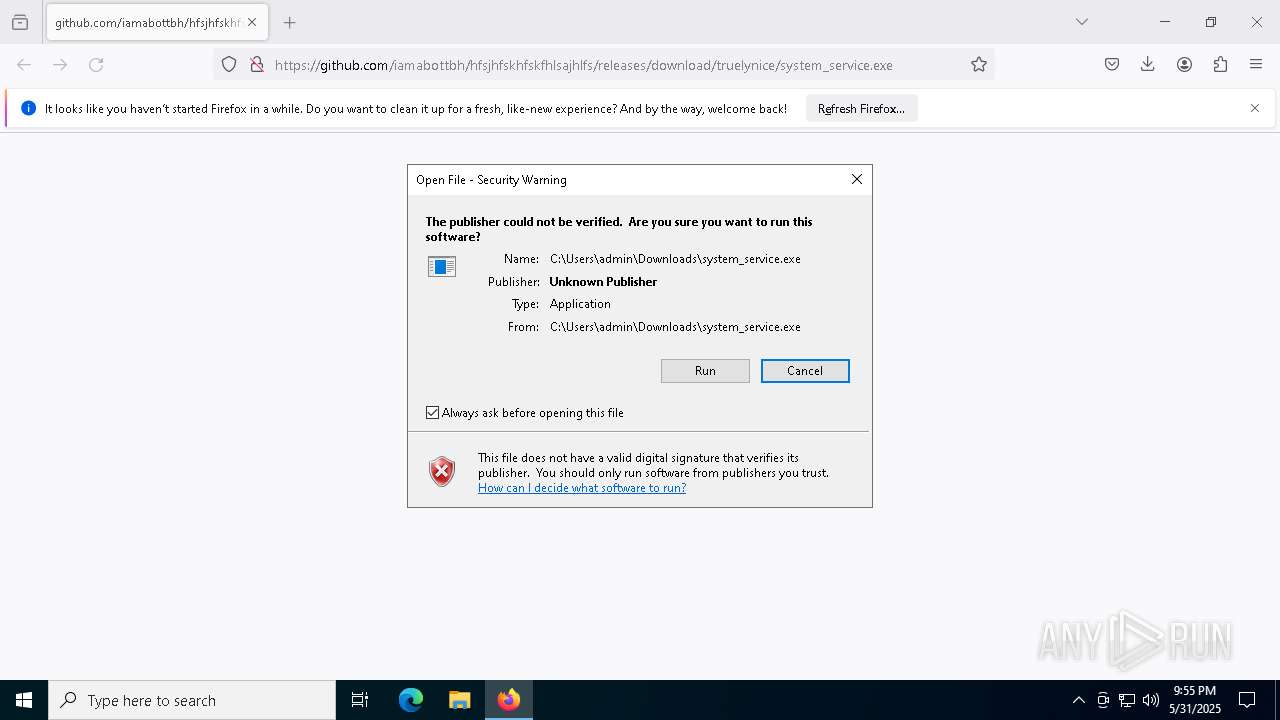
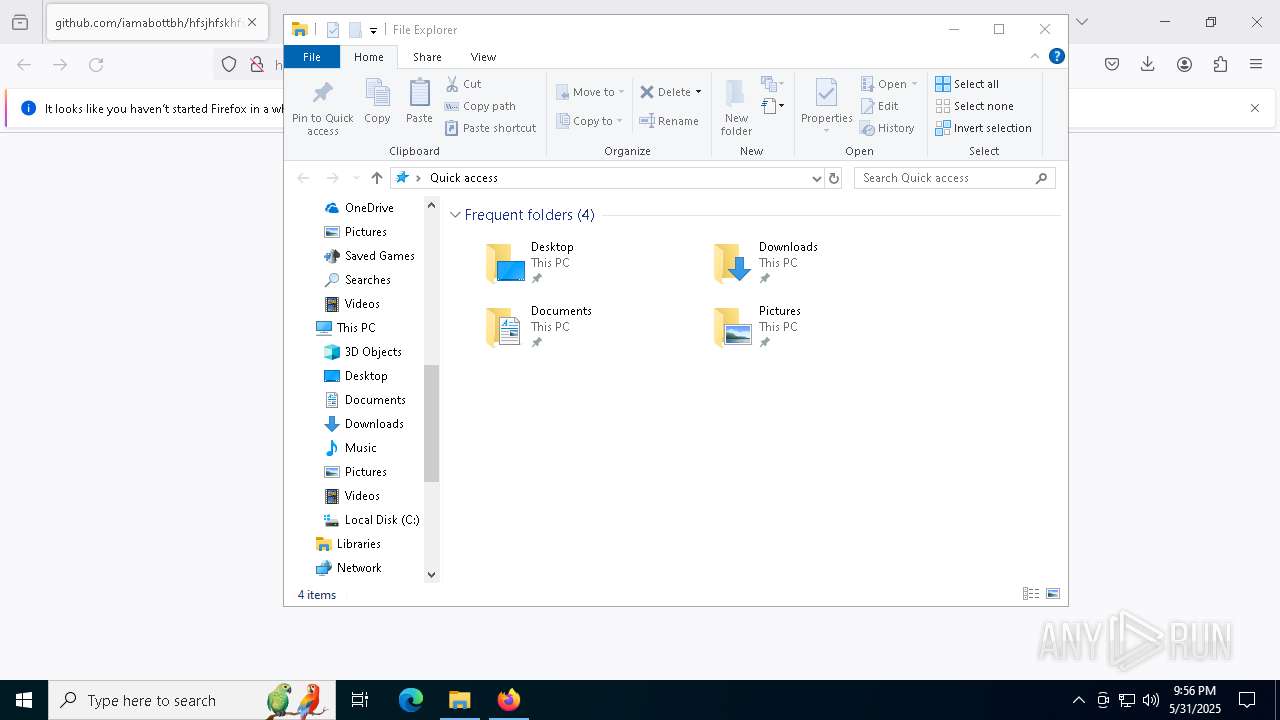
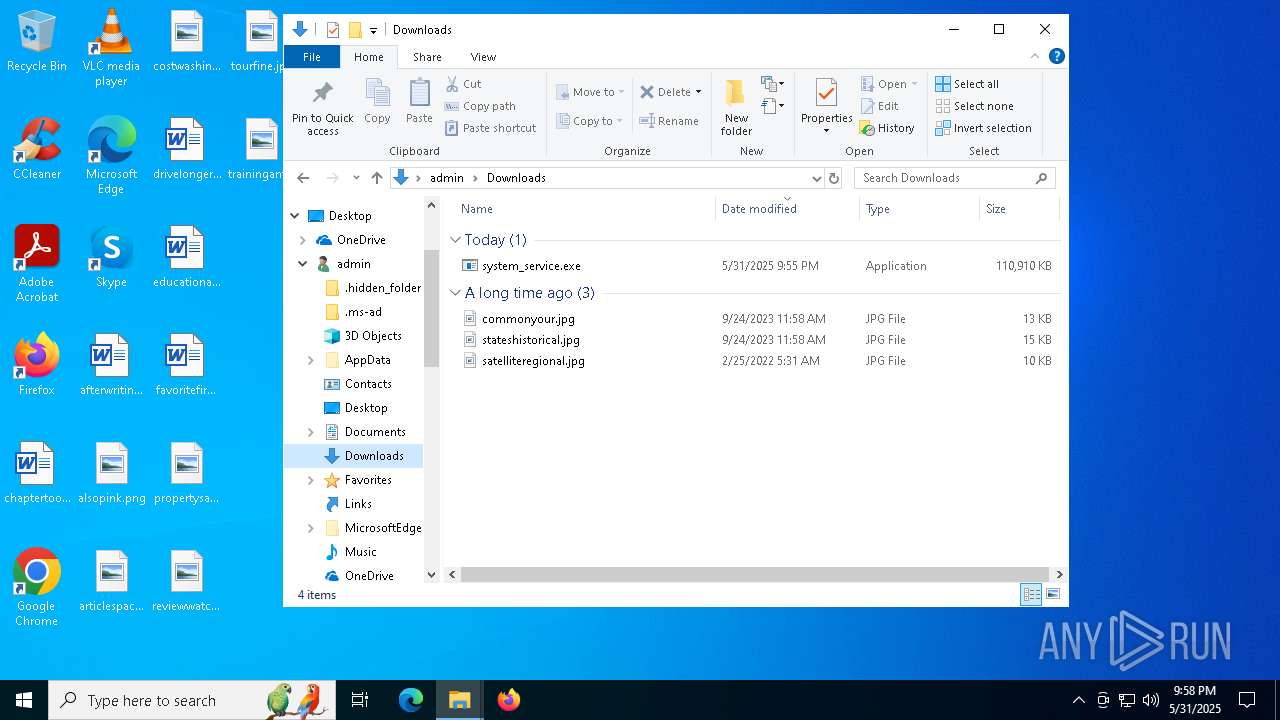
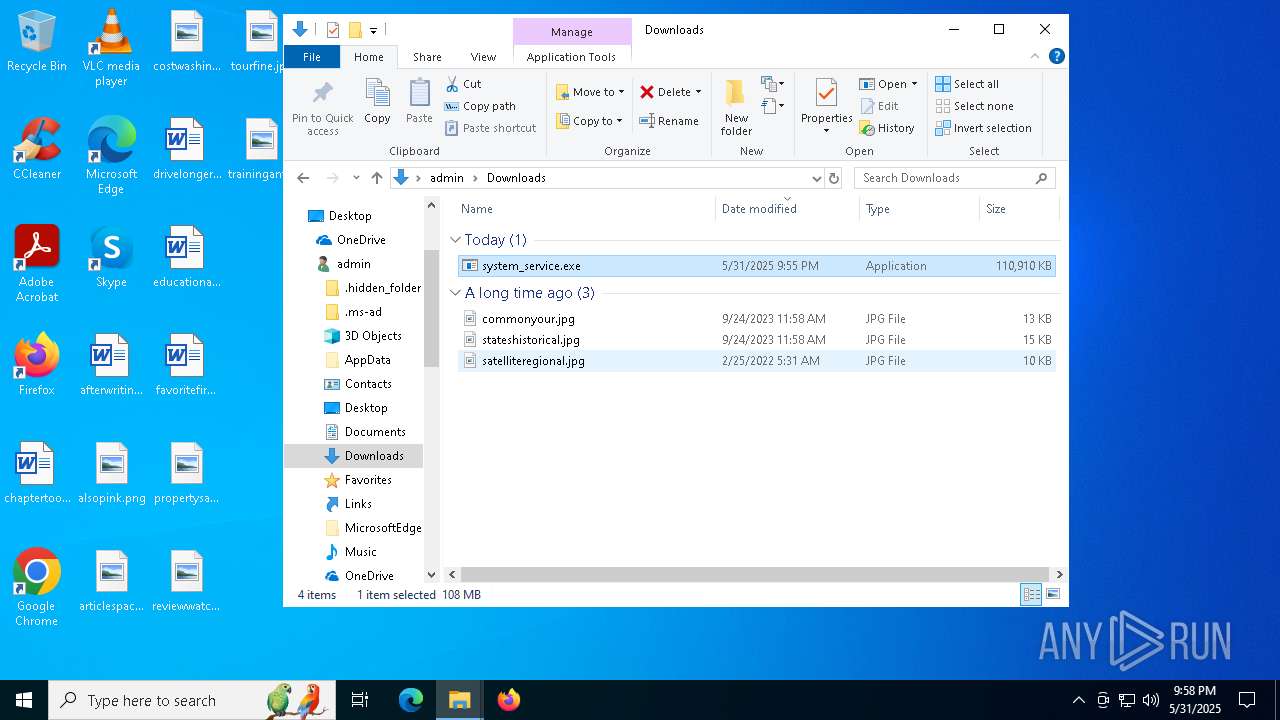
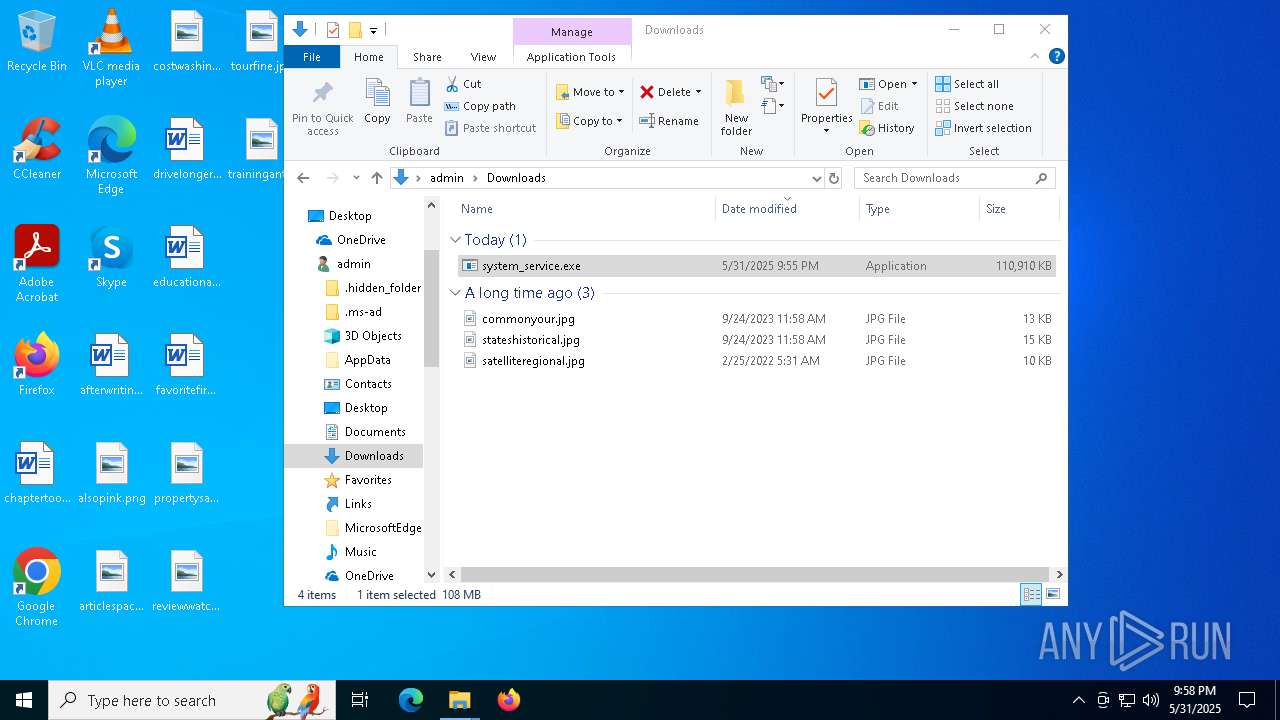
Launch of the file from Downloads directory
- firefox.exe (PID: 2600)
Checks supported languages
- system_service.exe (PID: 472)
- system_service.exe (PID: 7788)
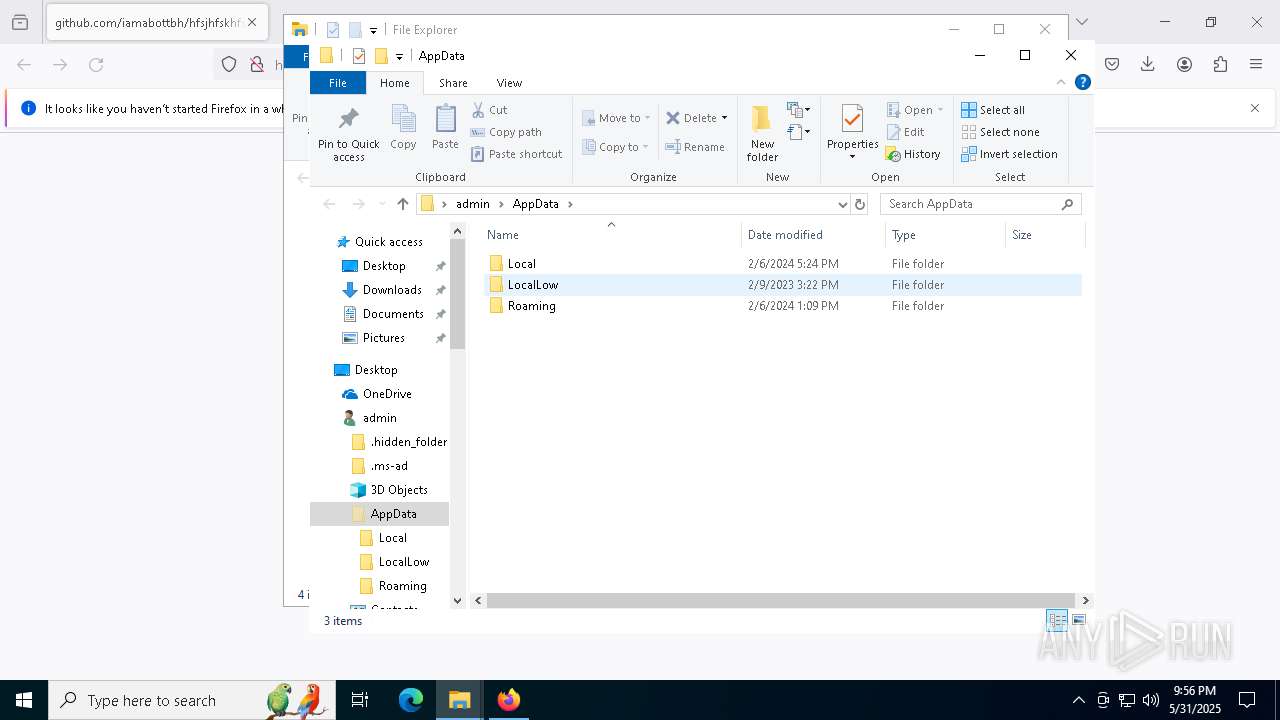
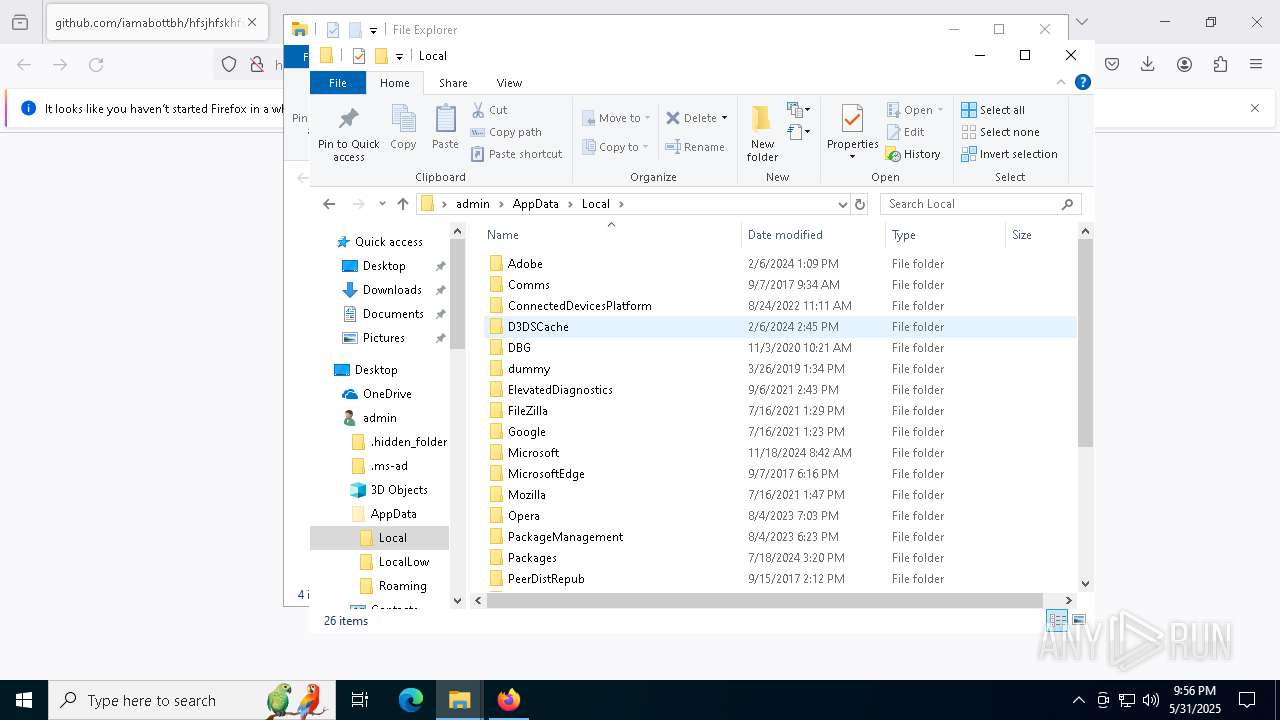
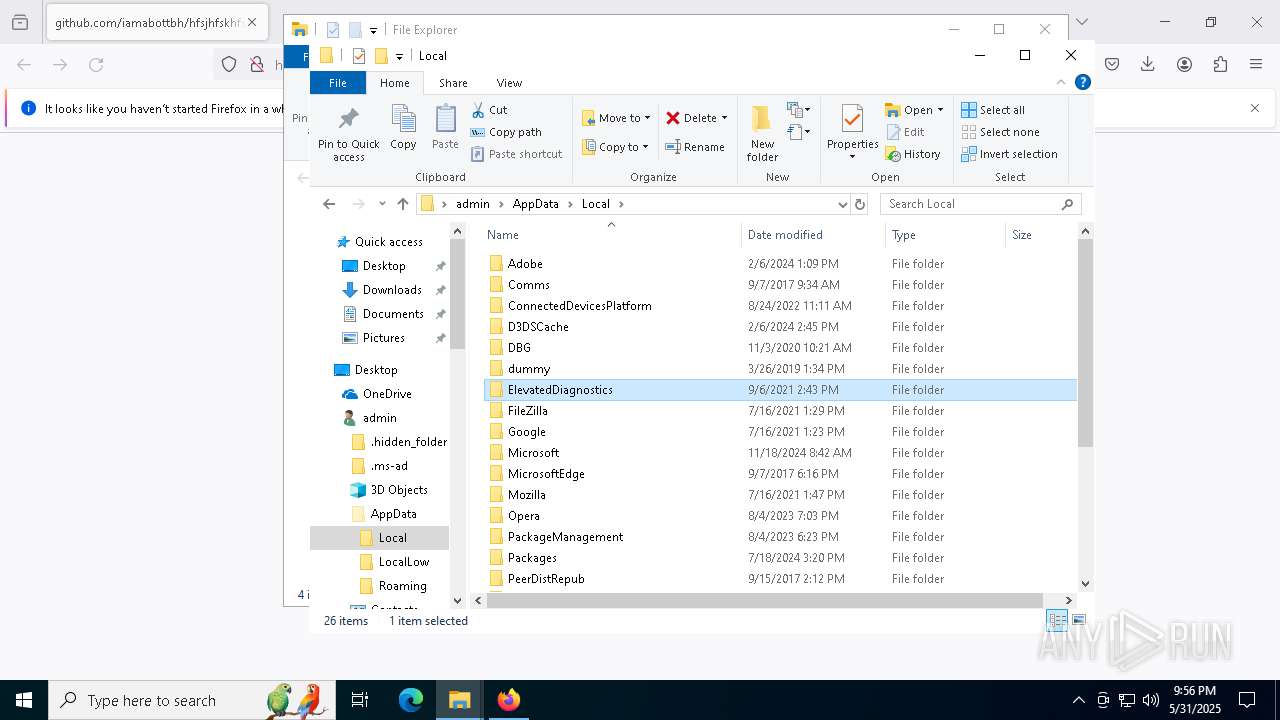
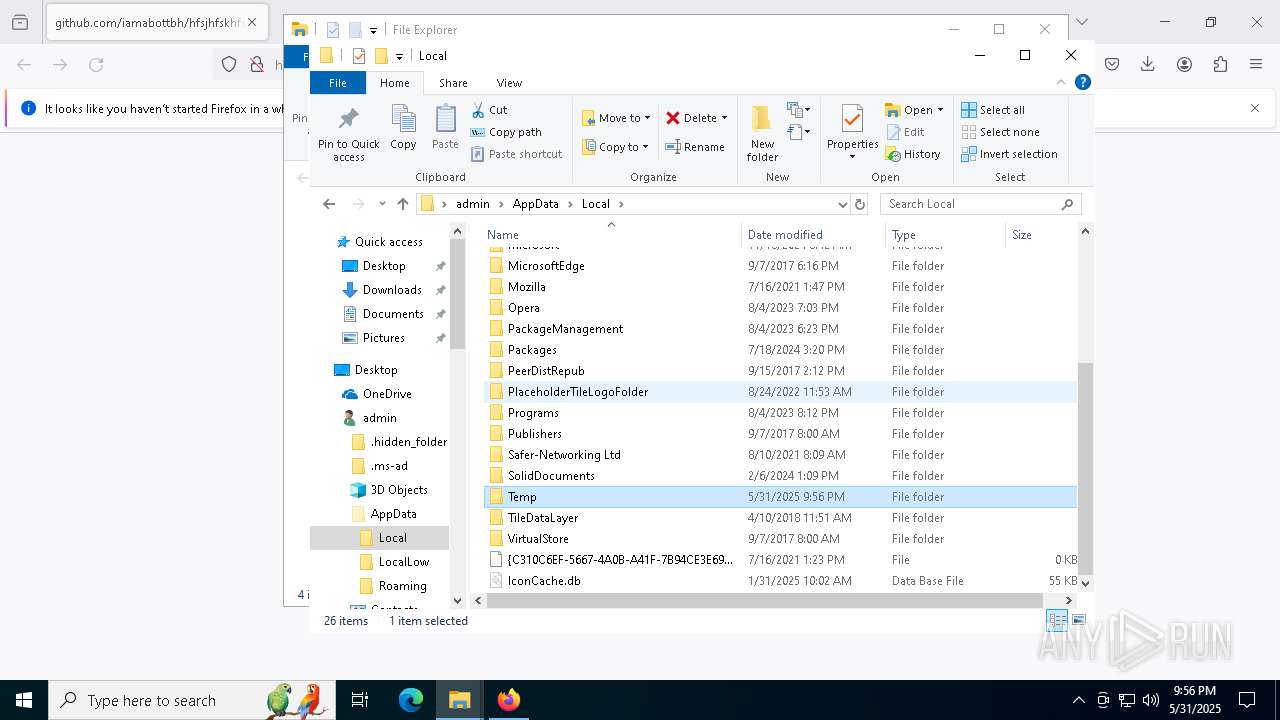
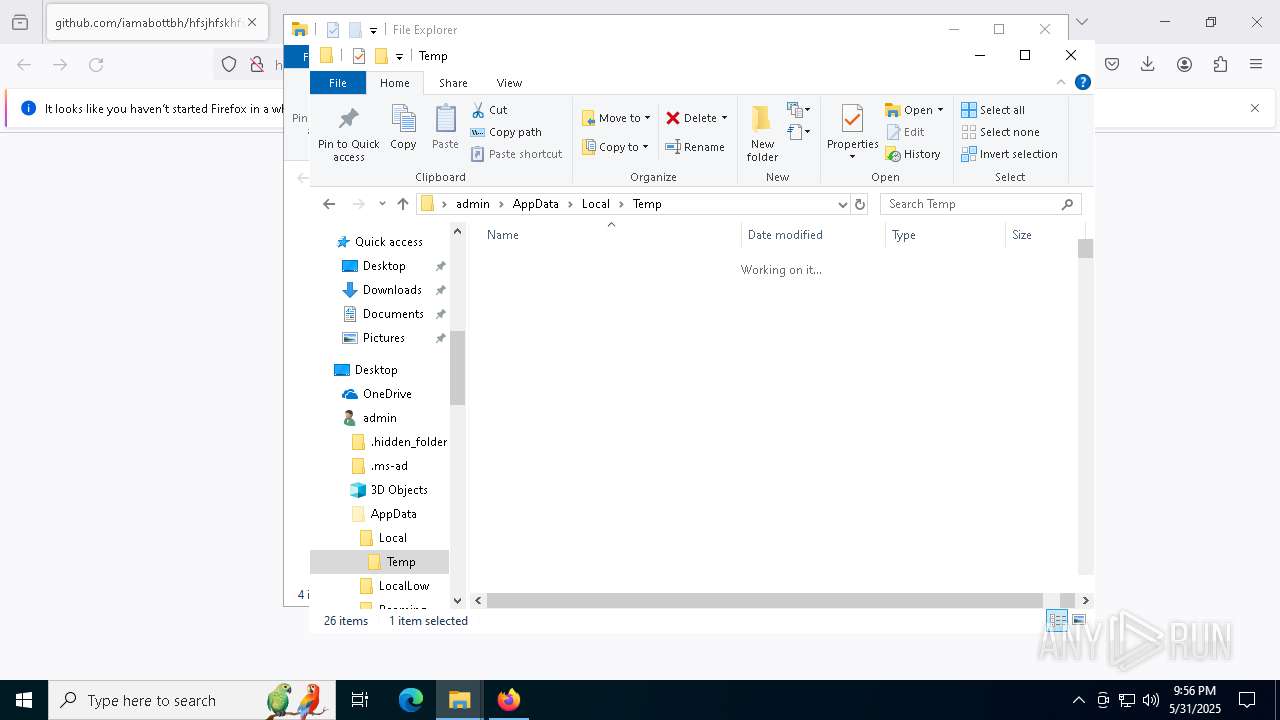
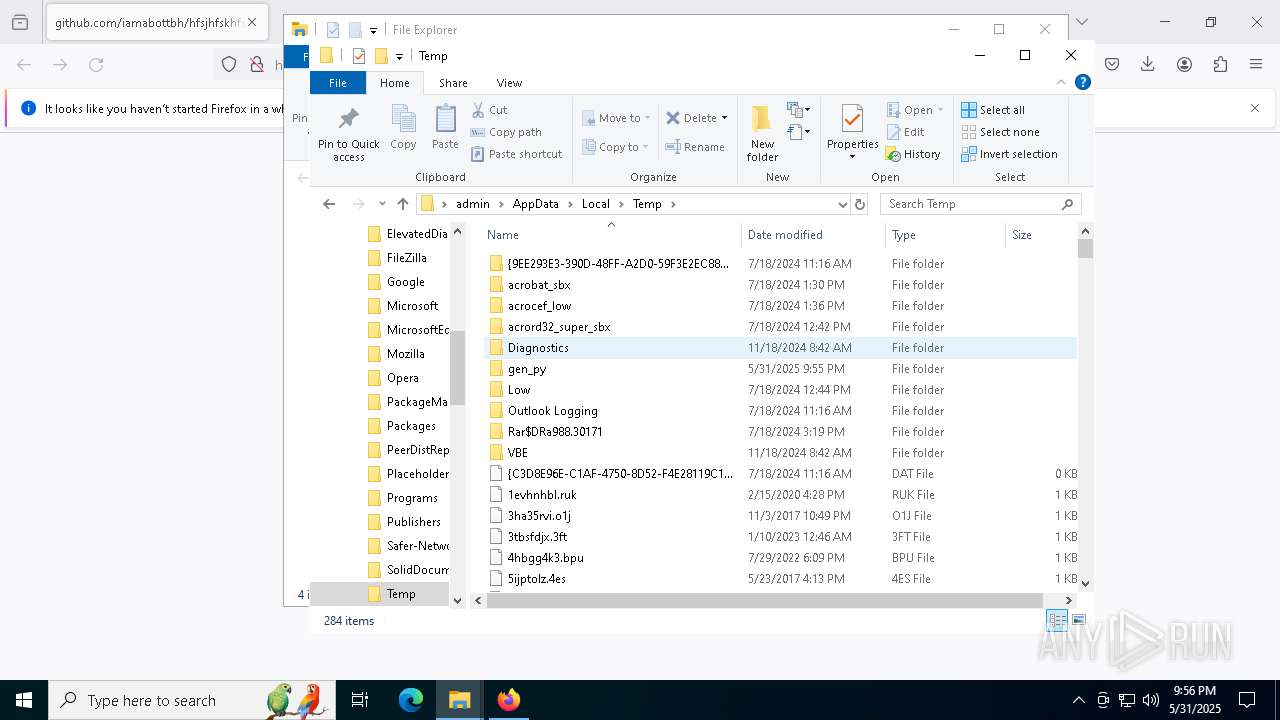
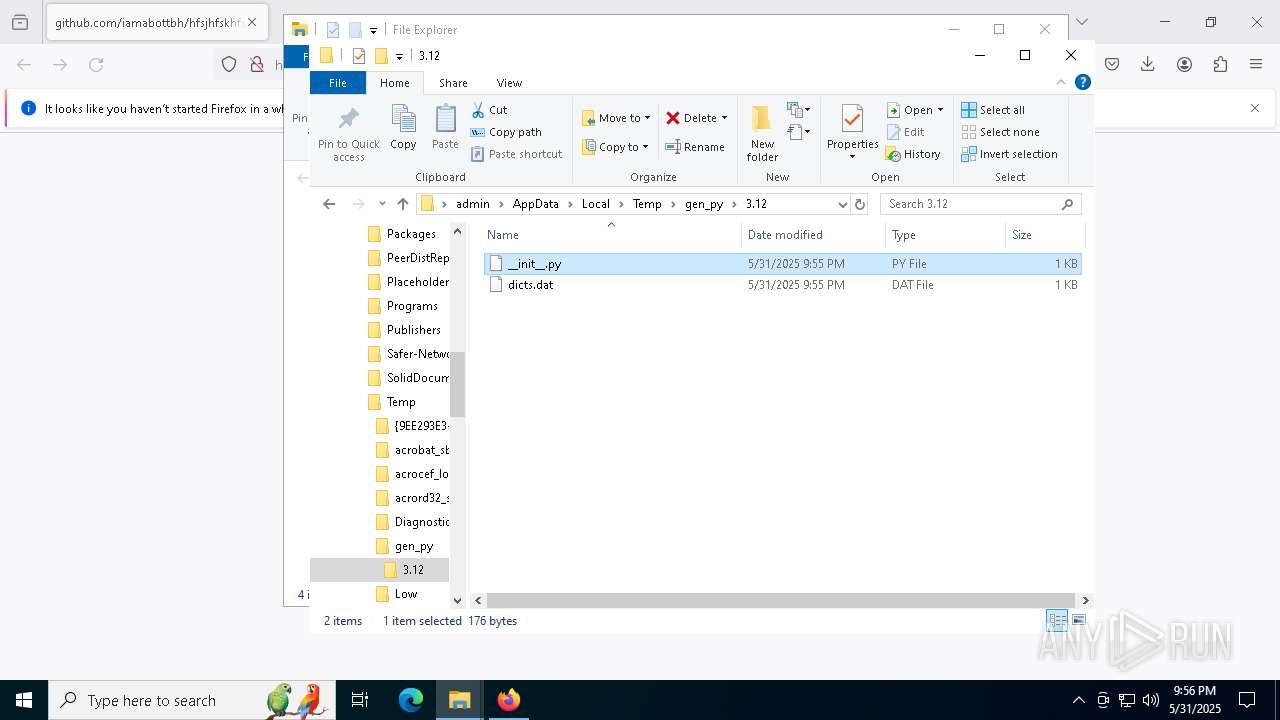
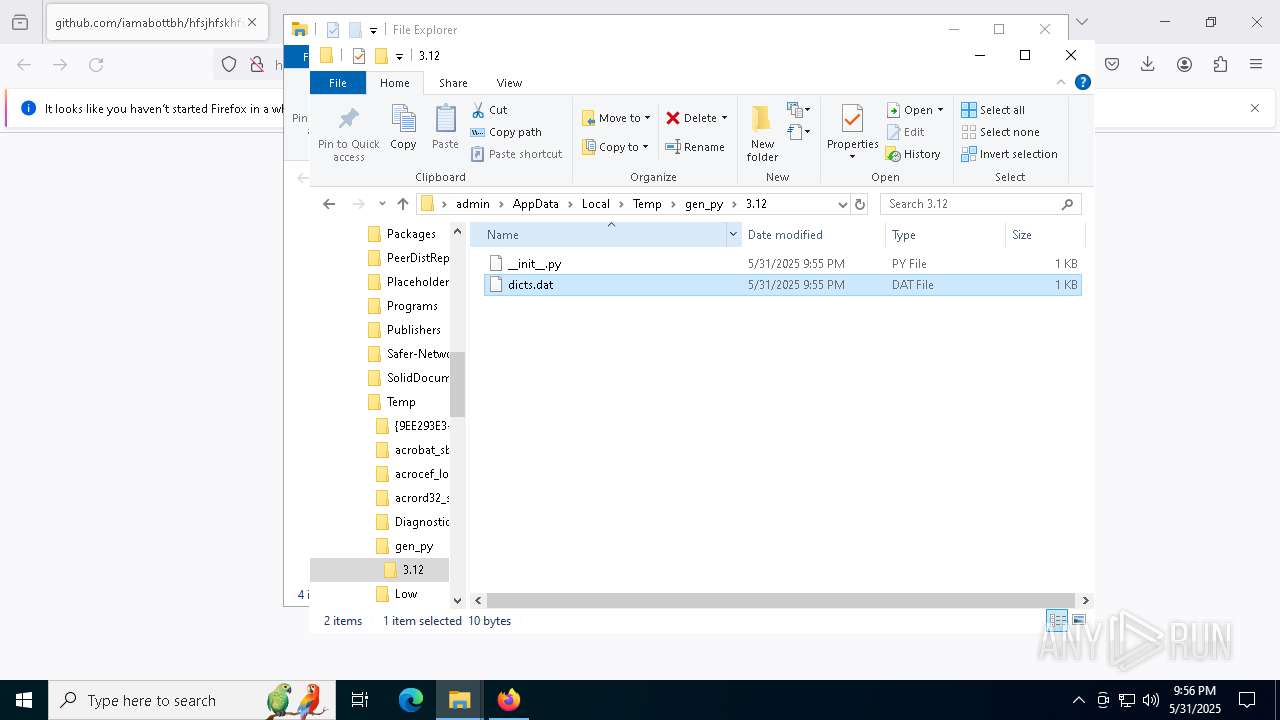
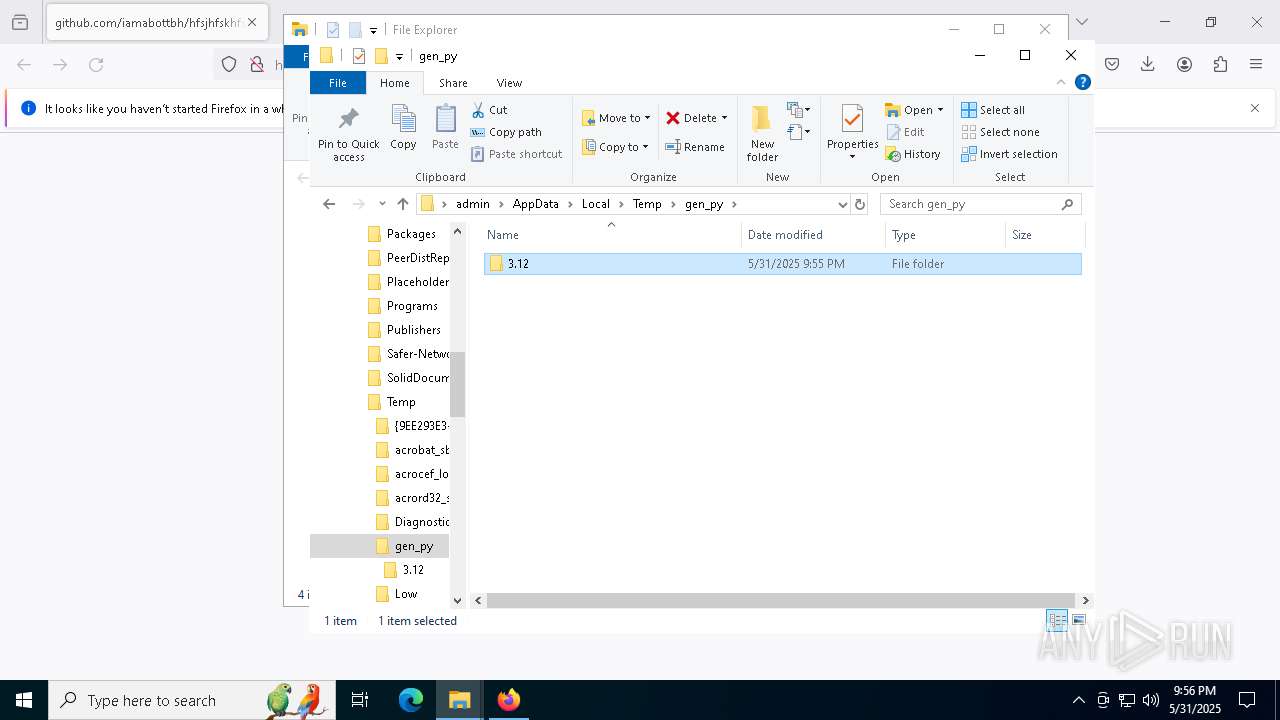
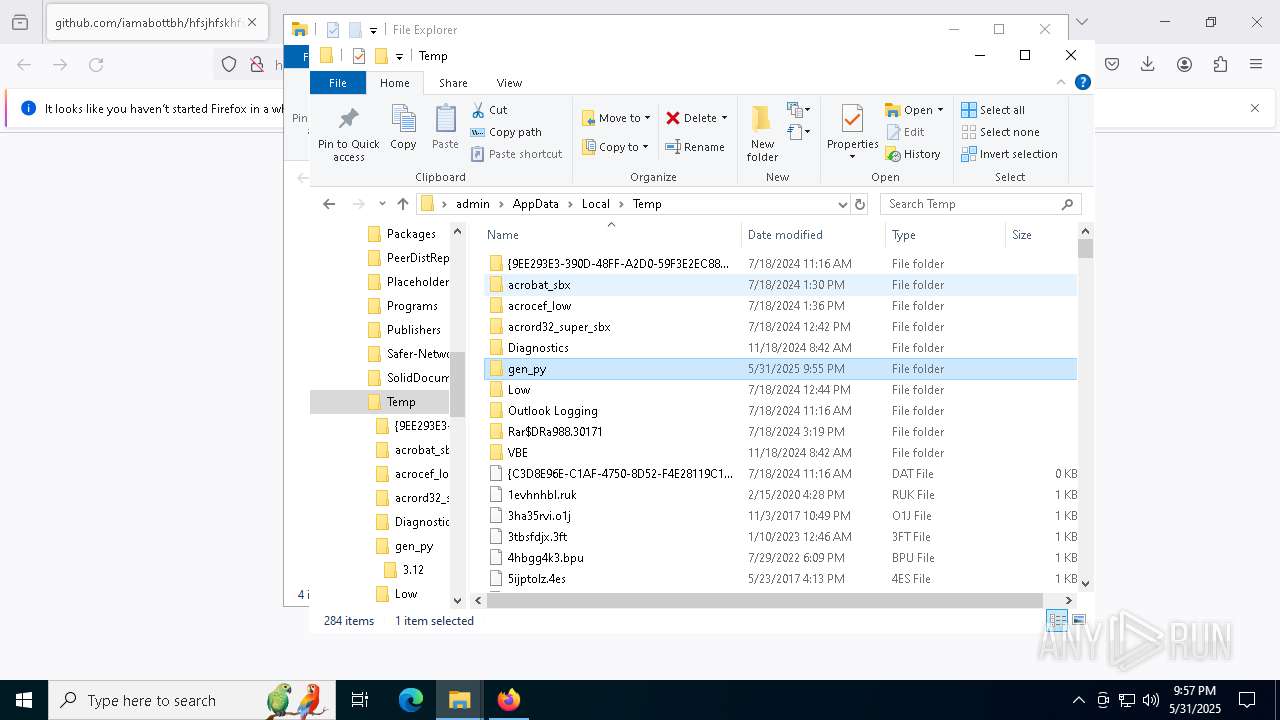
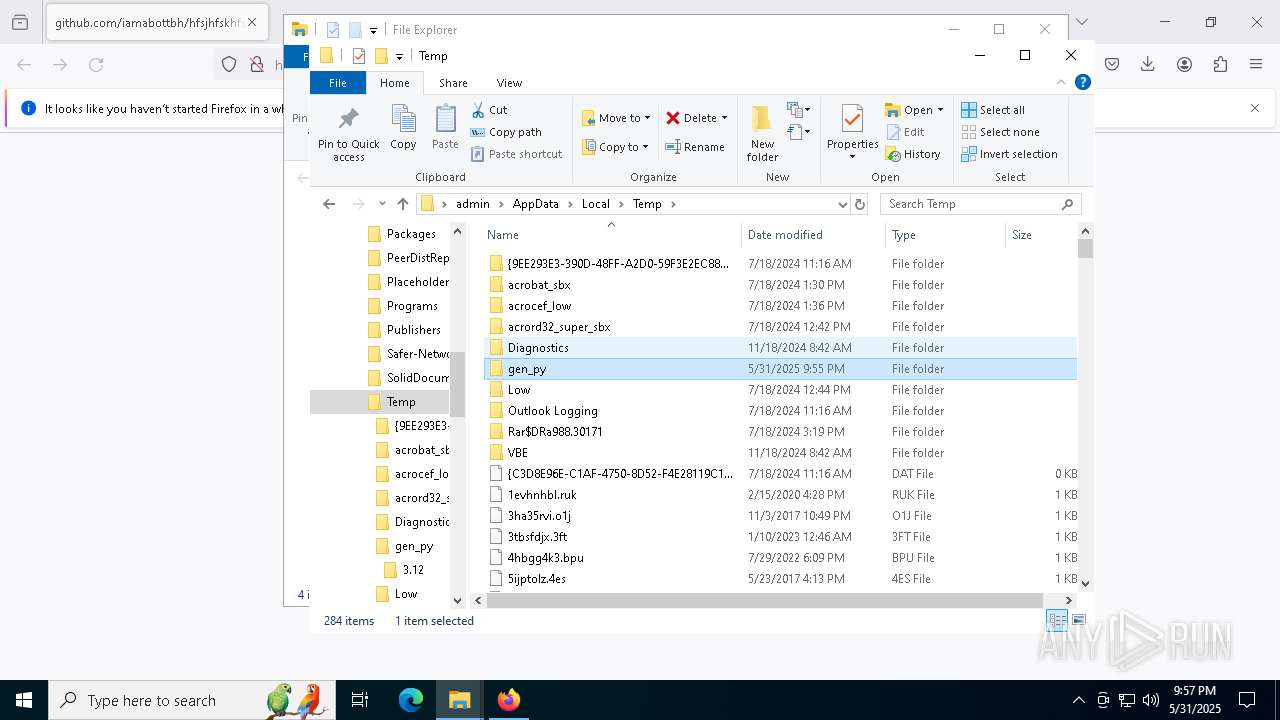
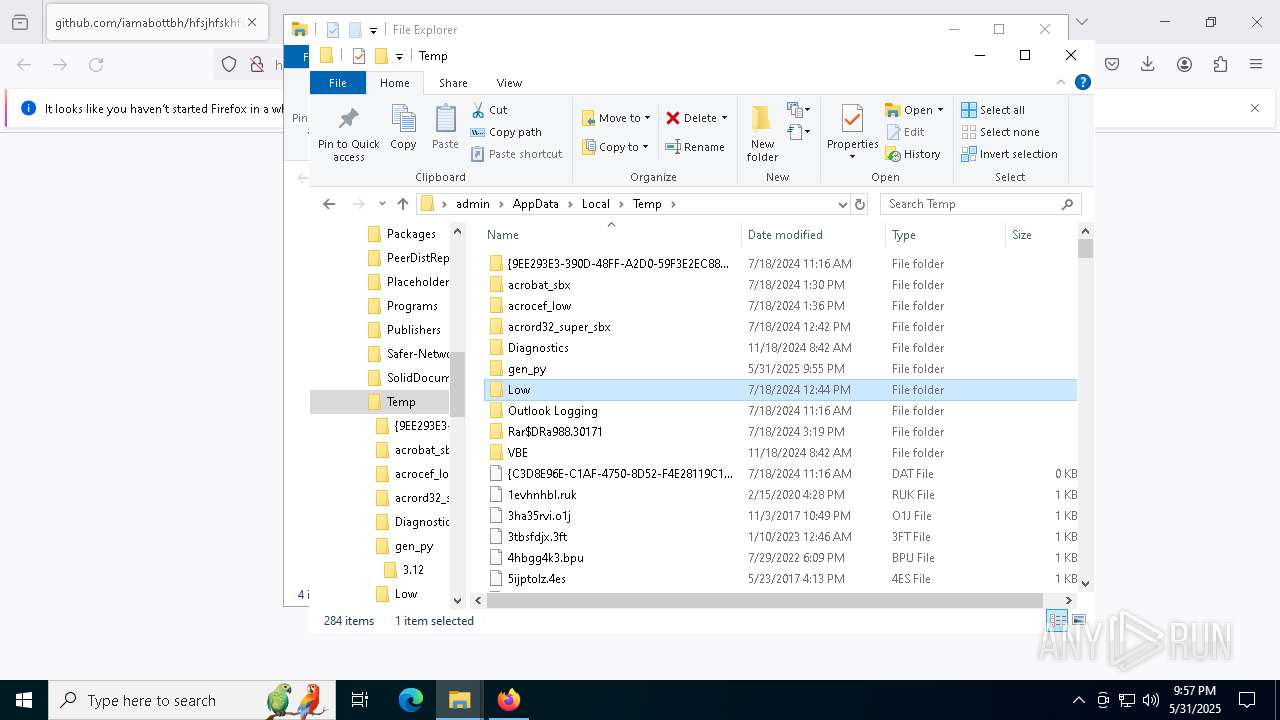
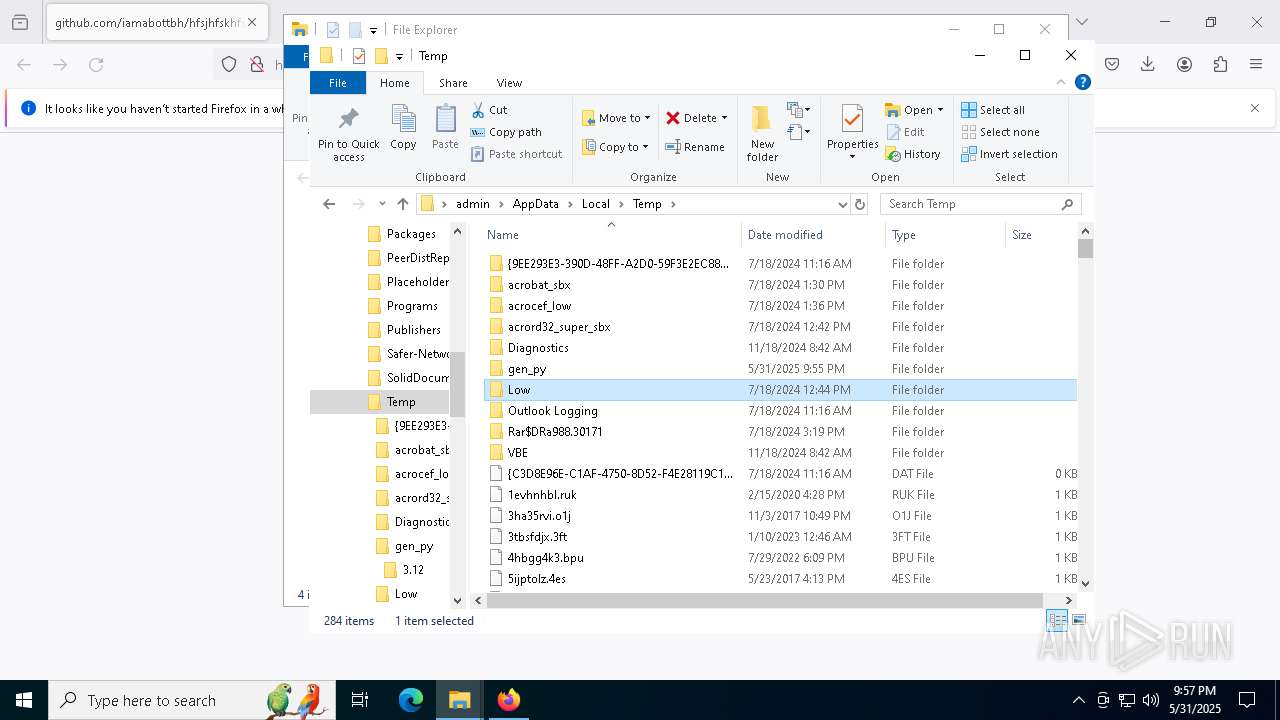
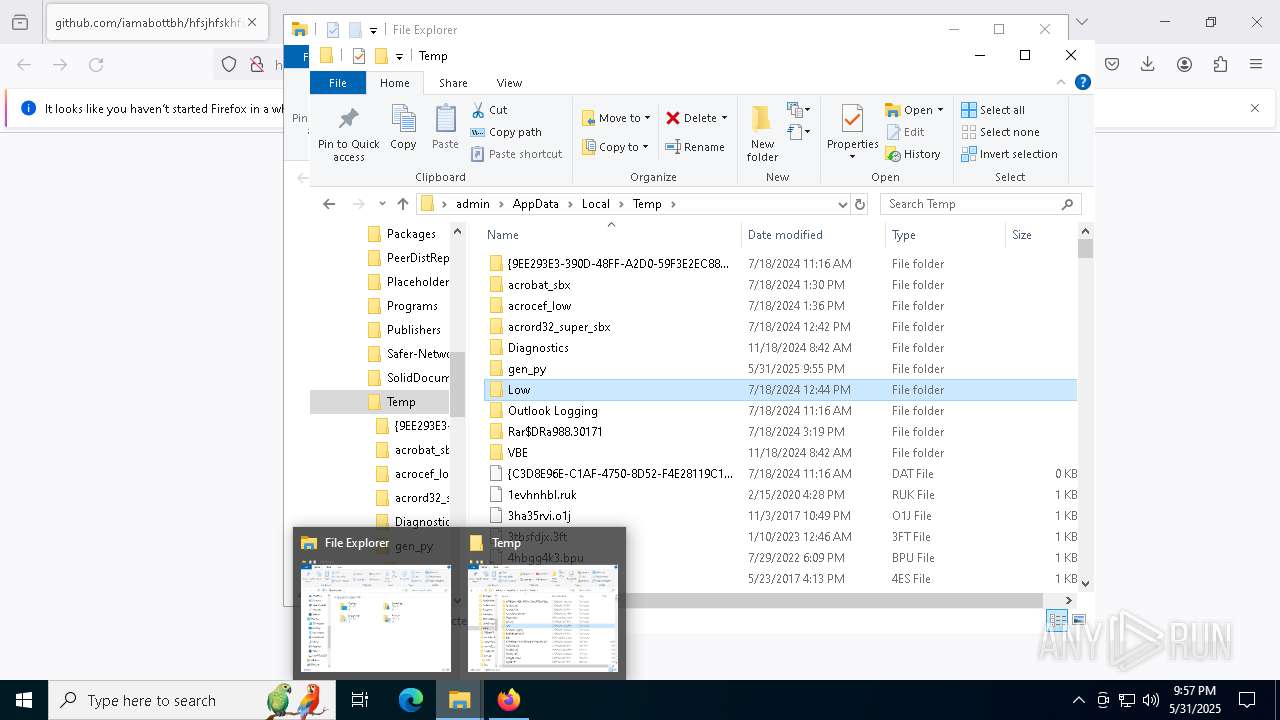
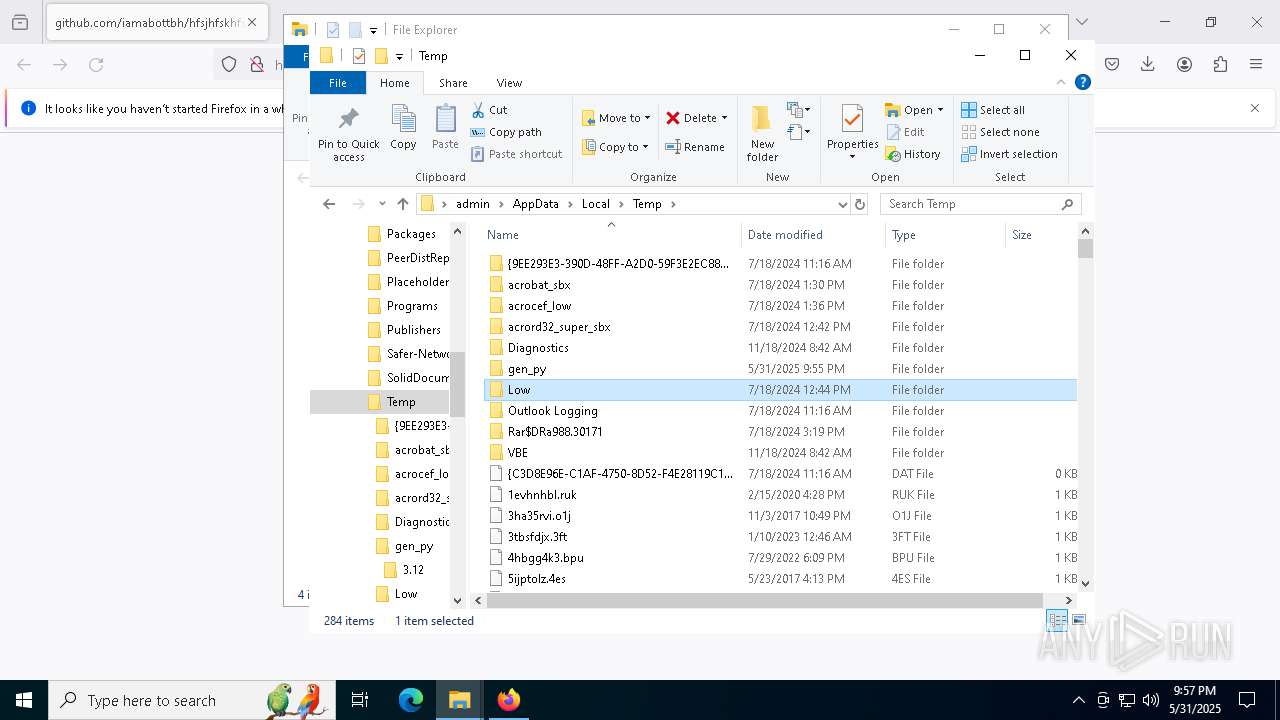
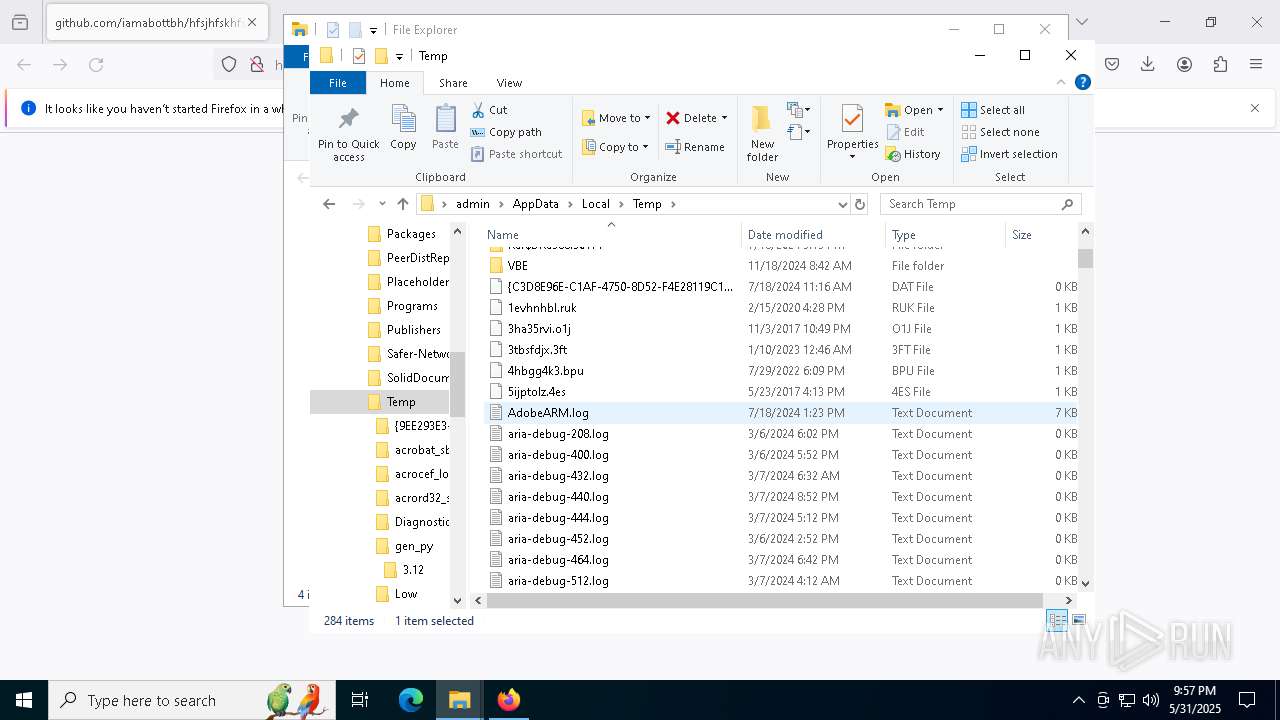
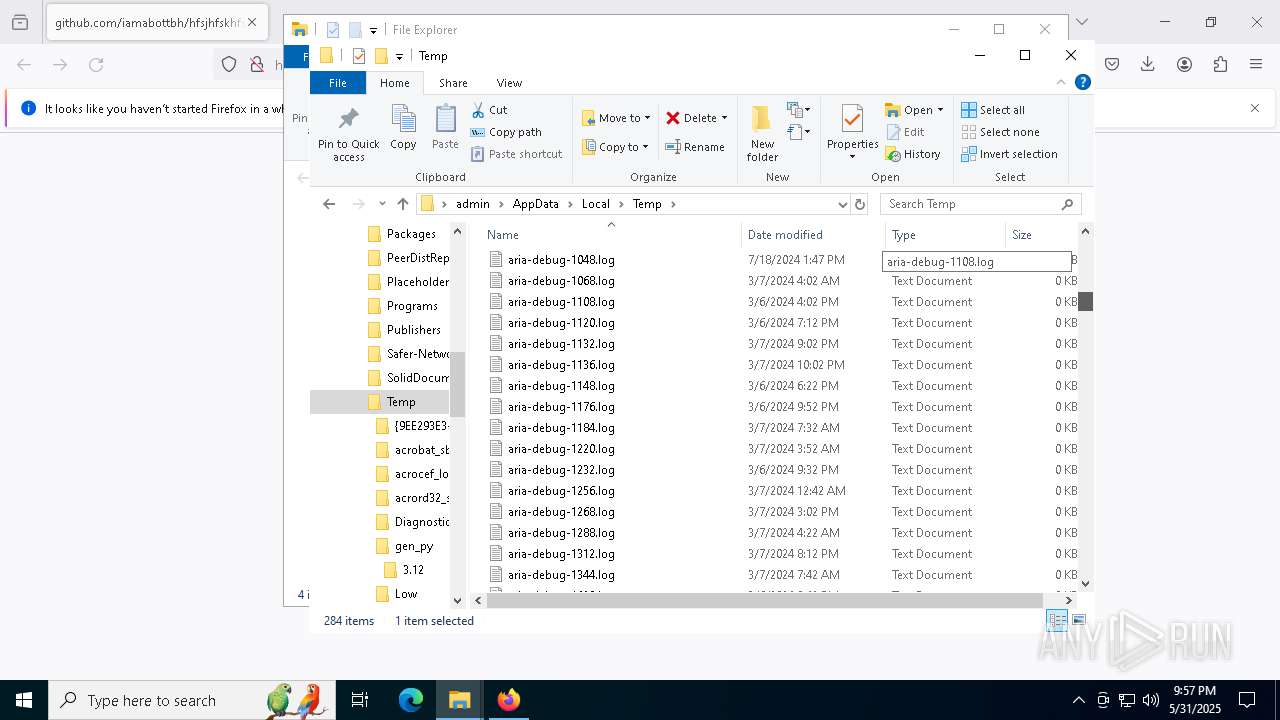
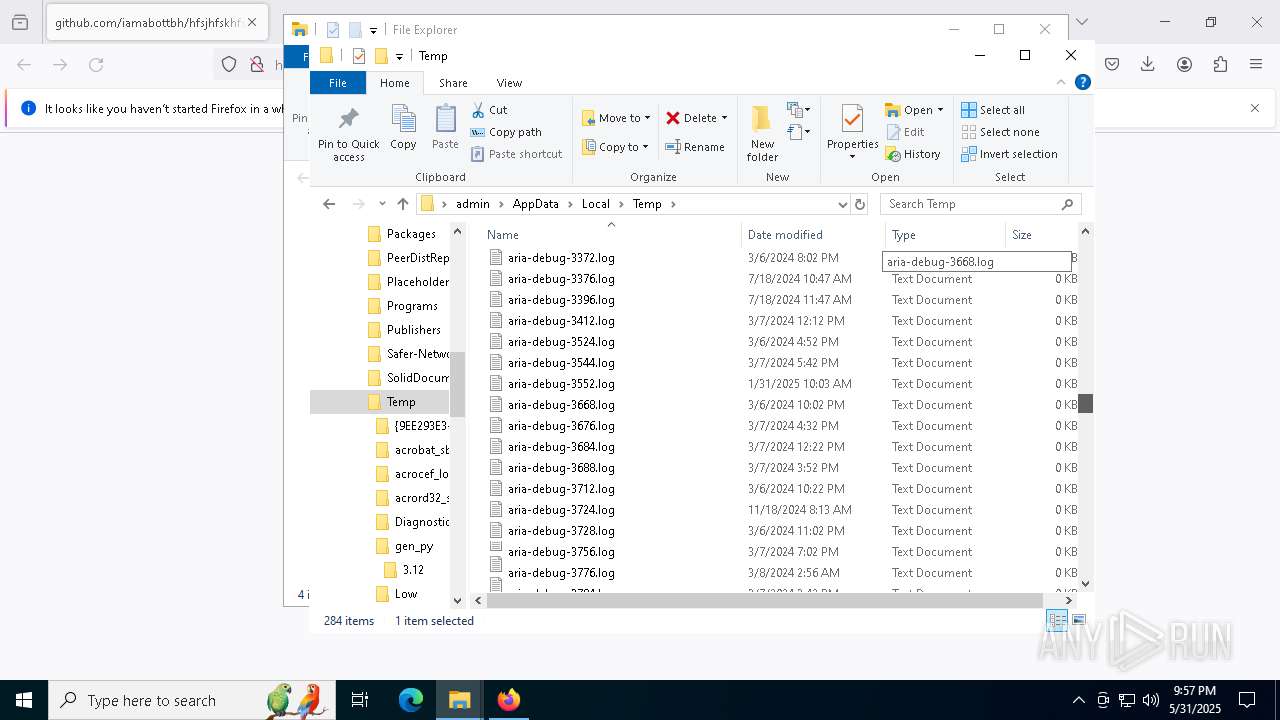
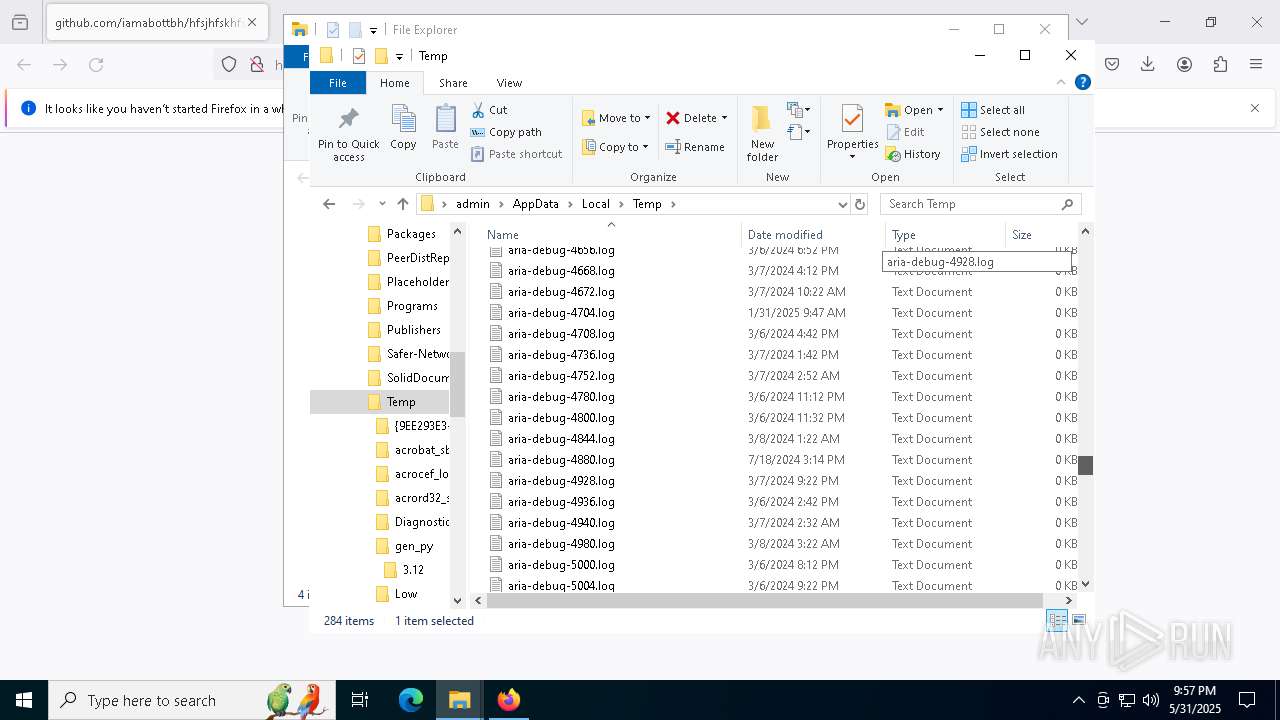
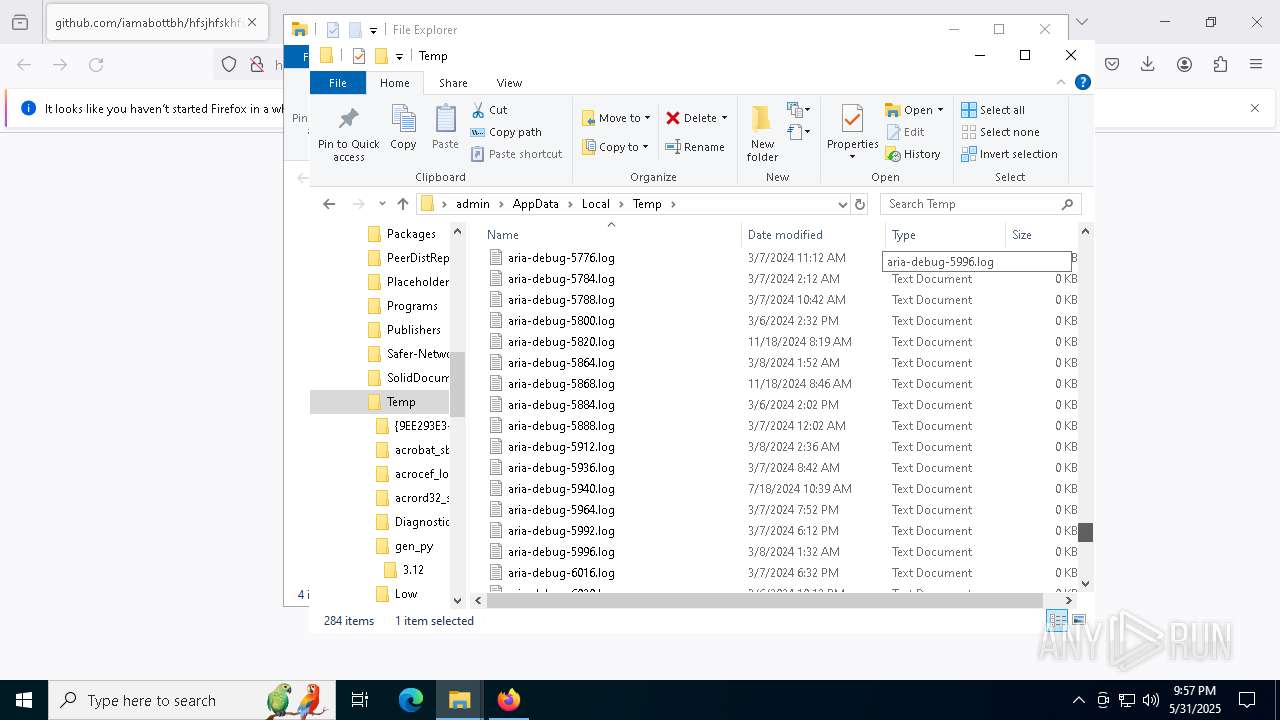
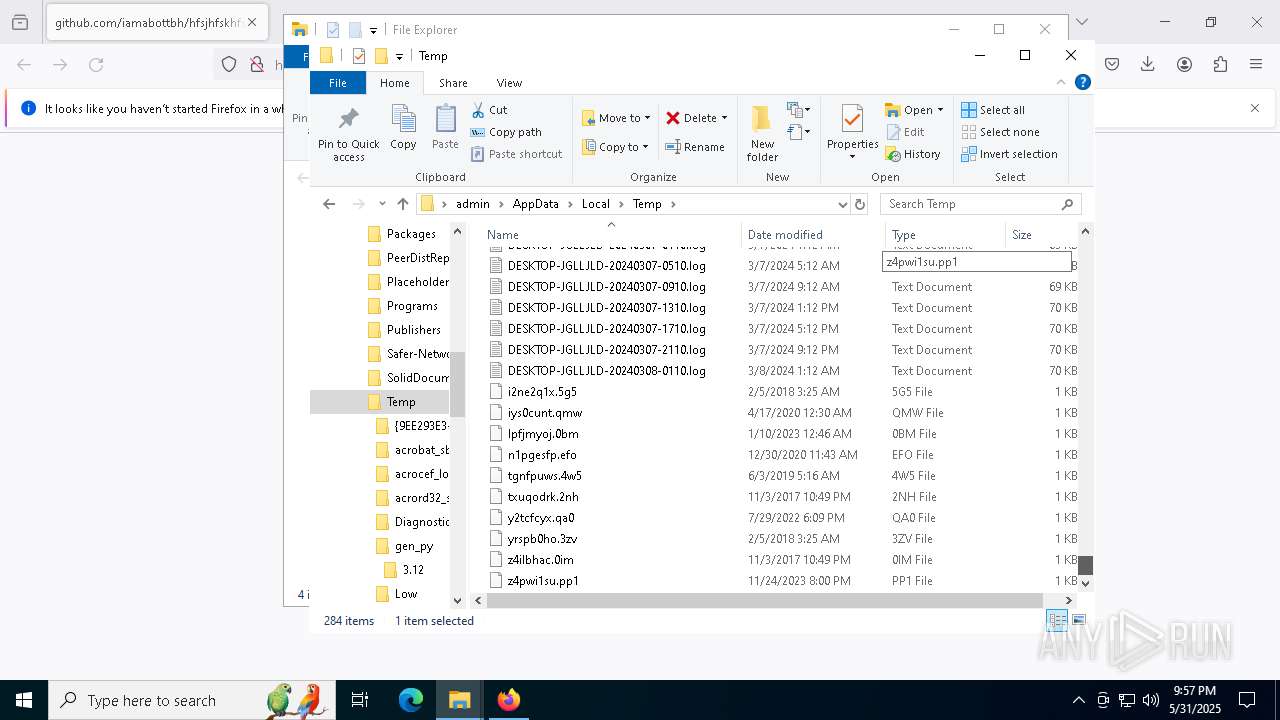
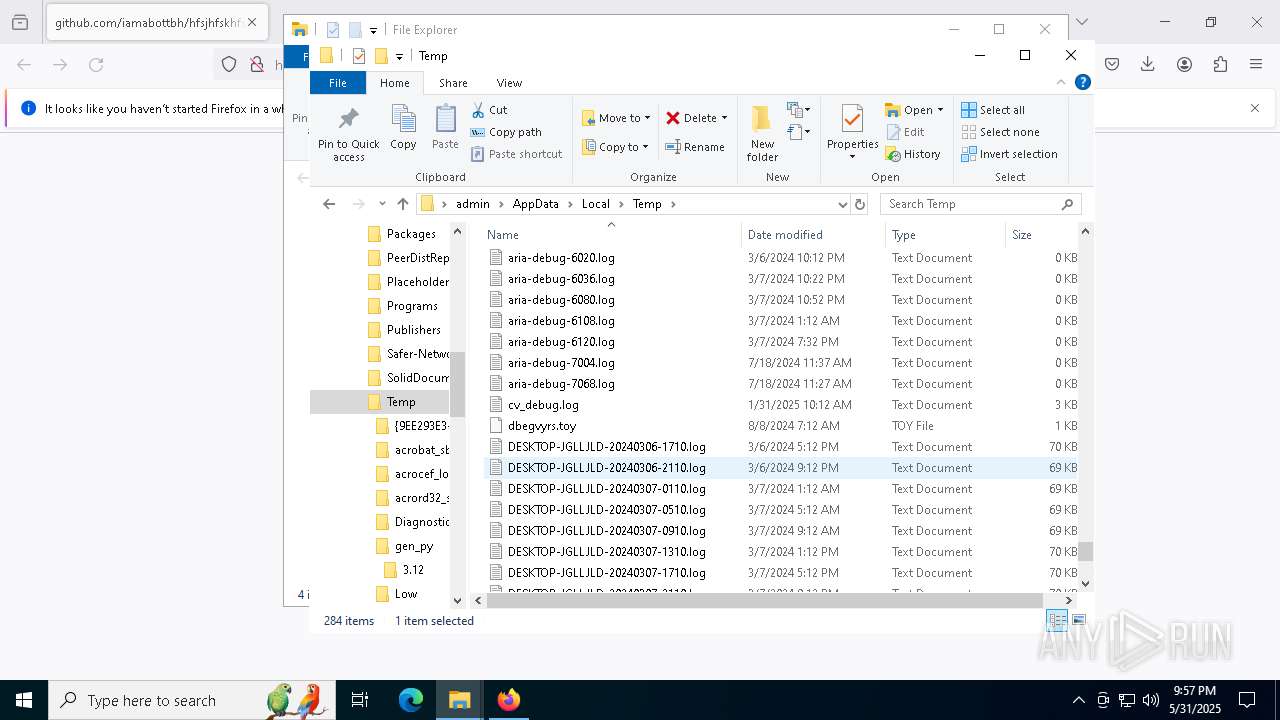
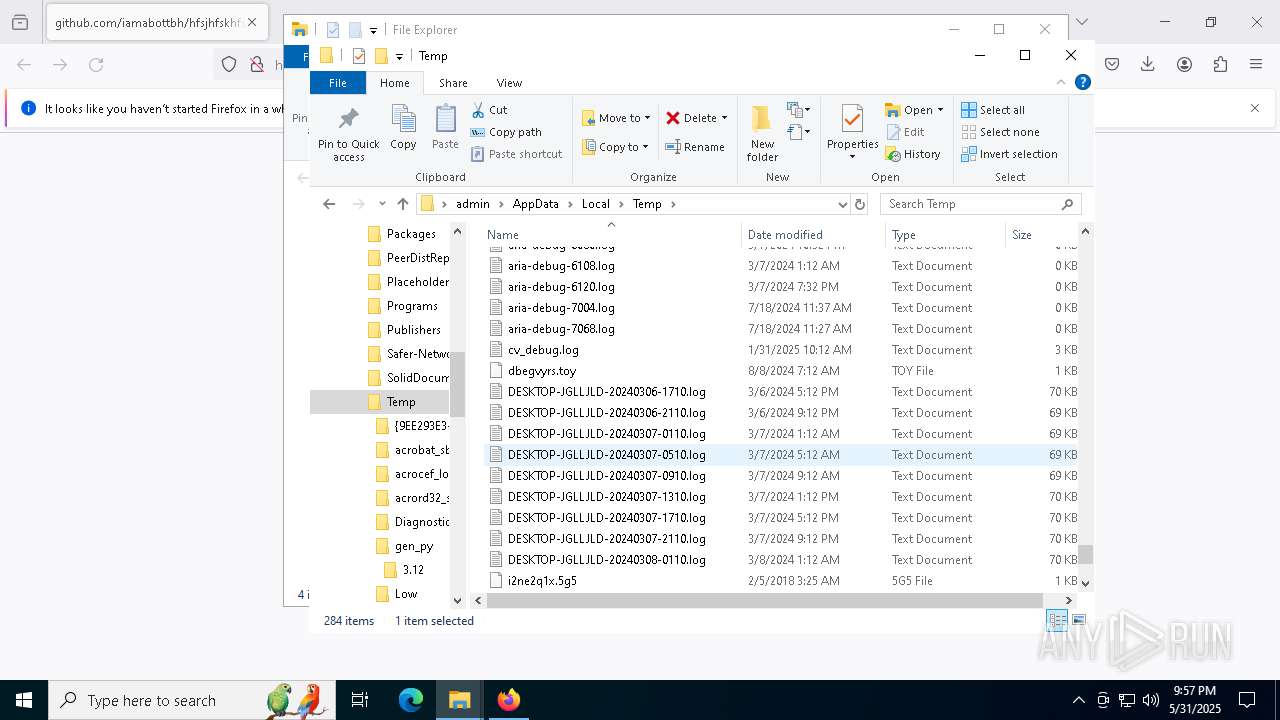
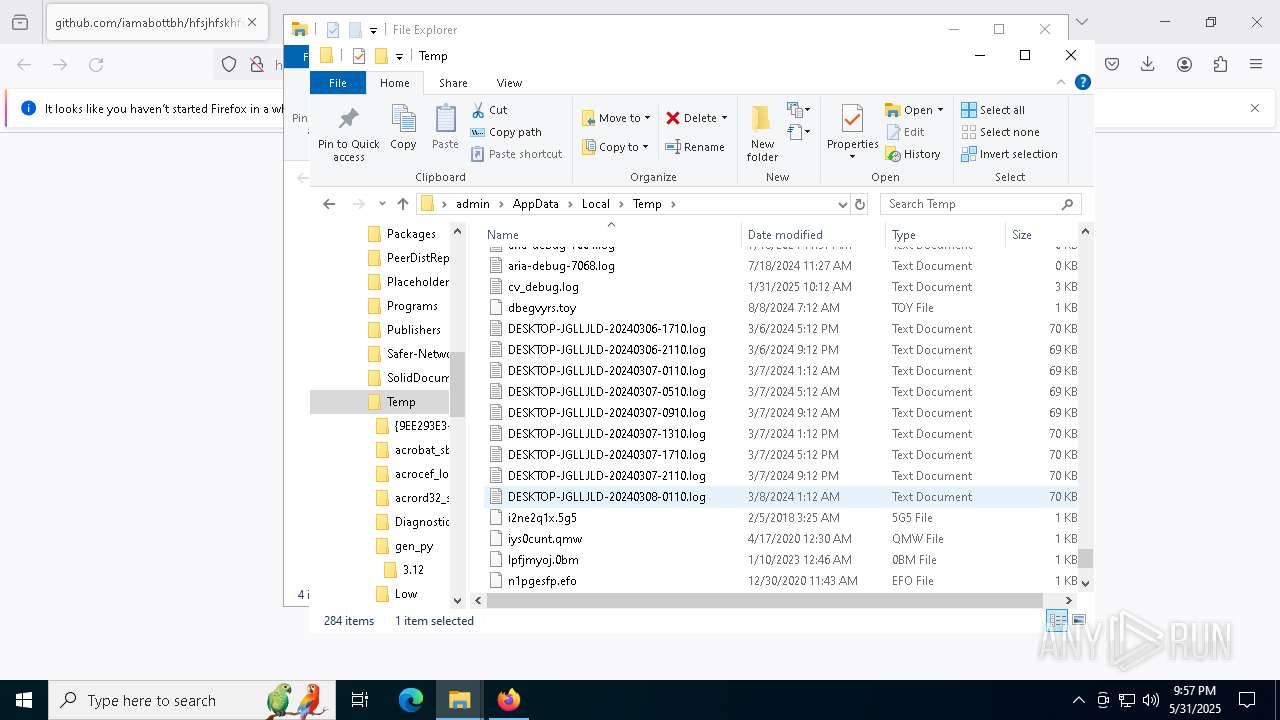
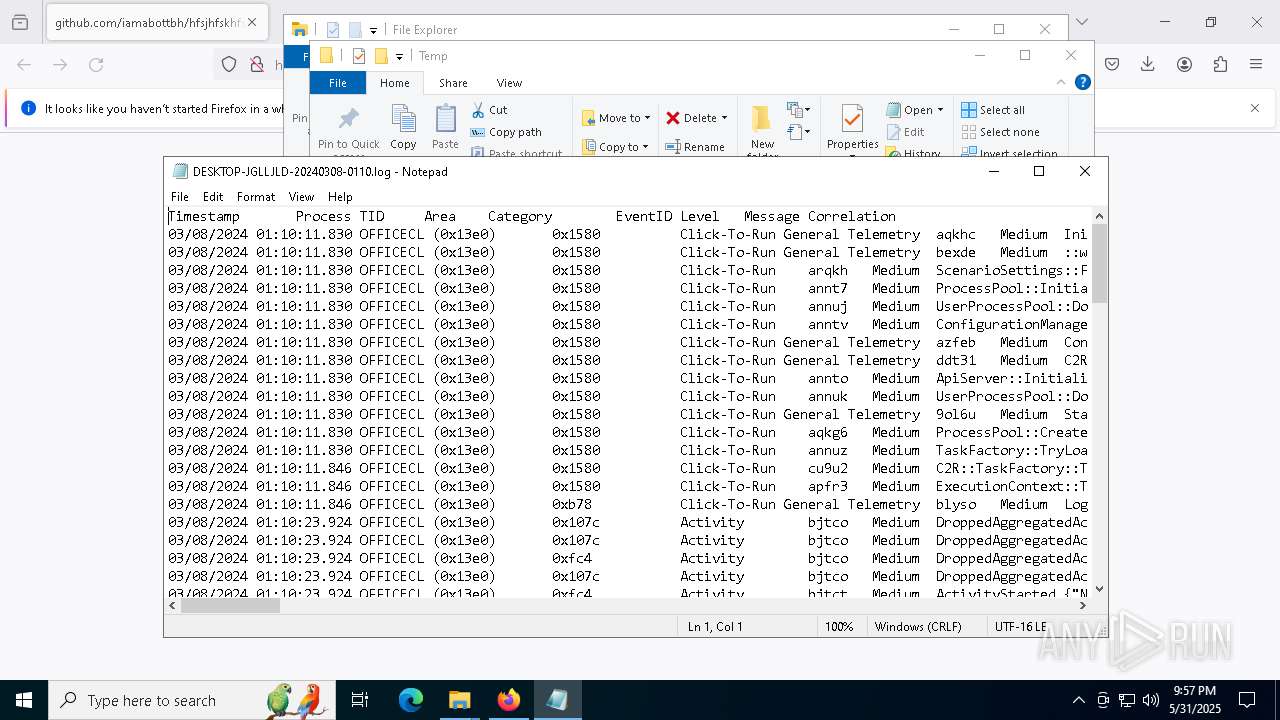
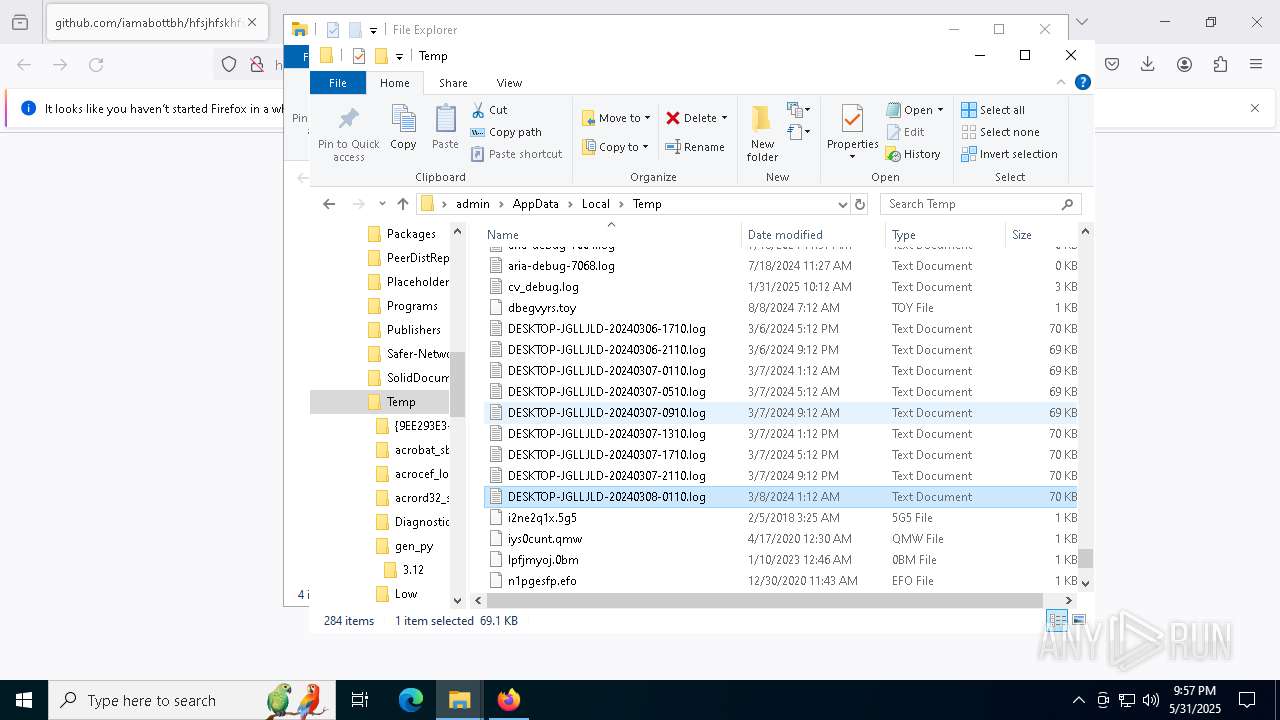
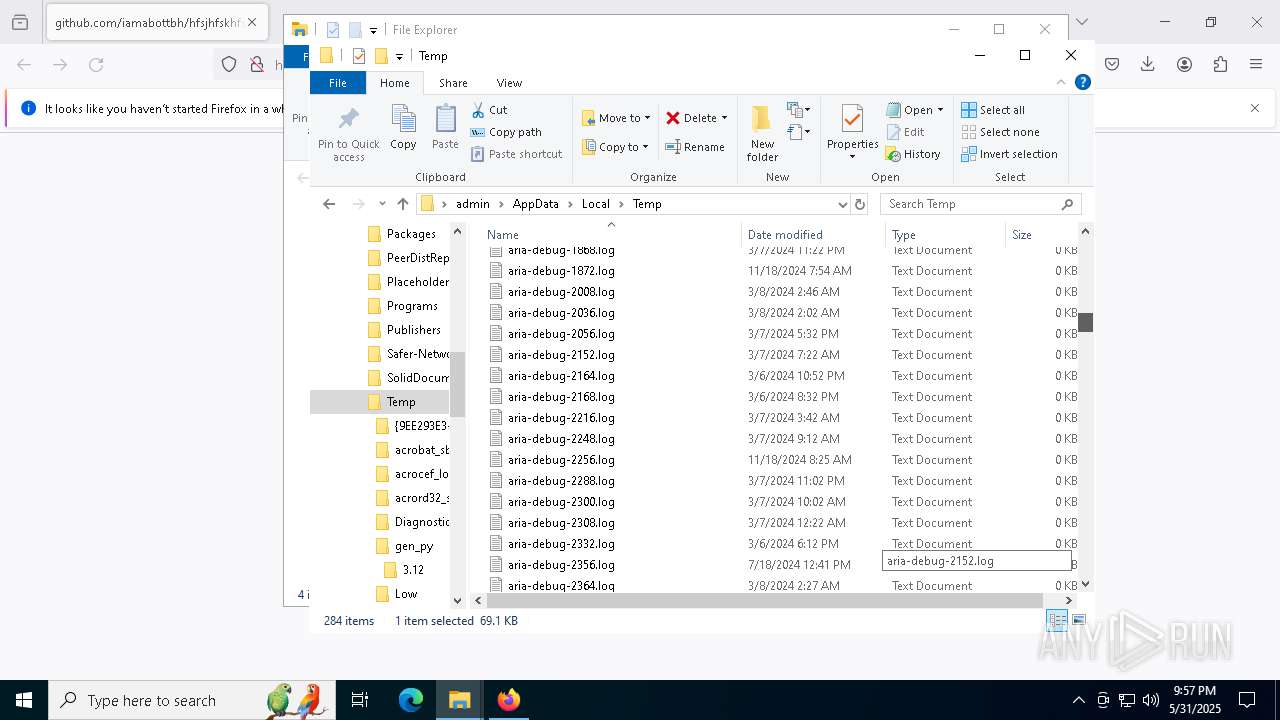
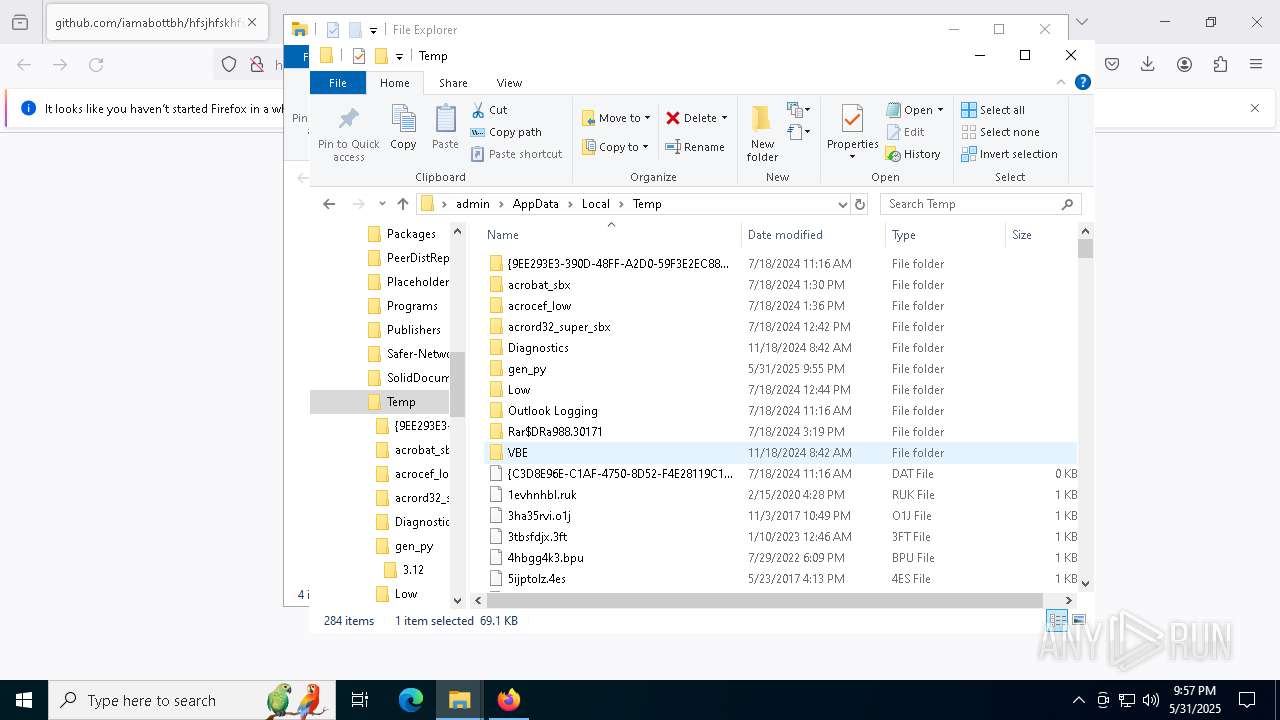
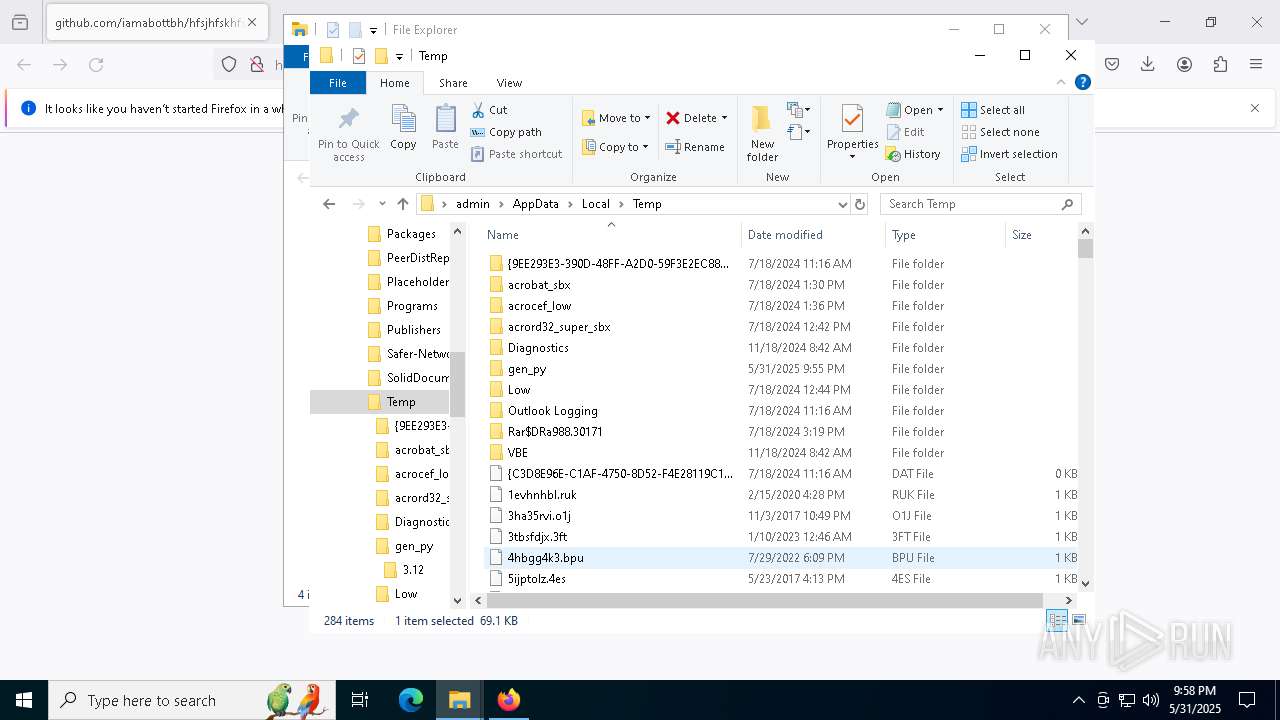
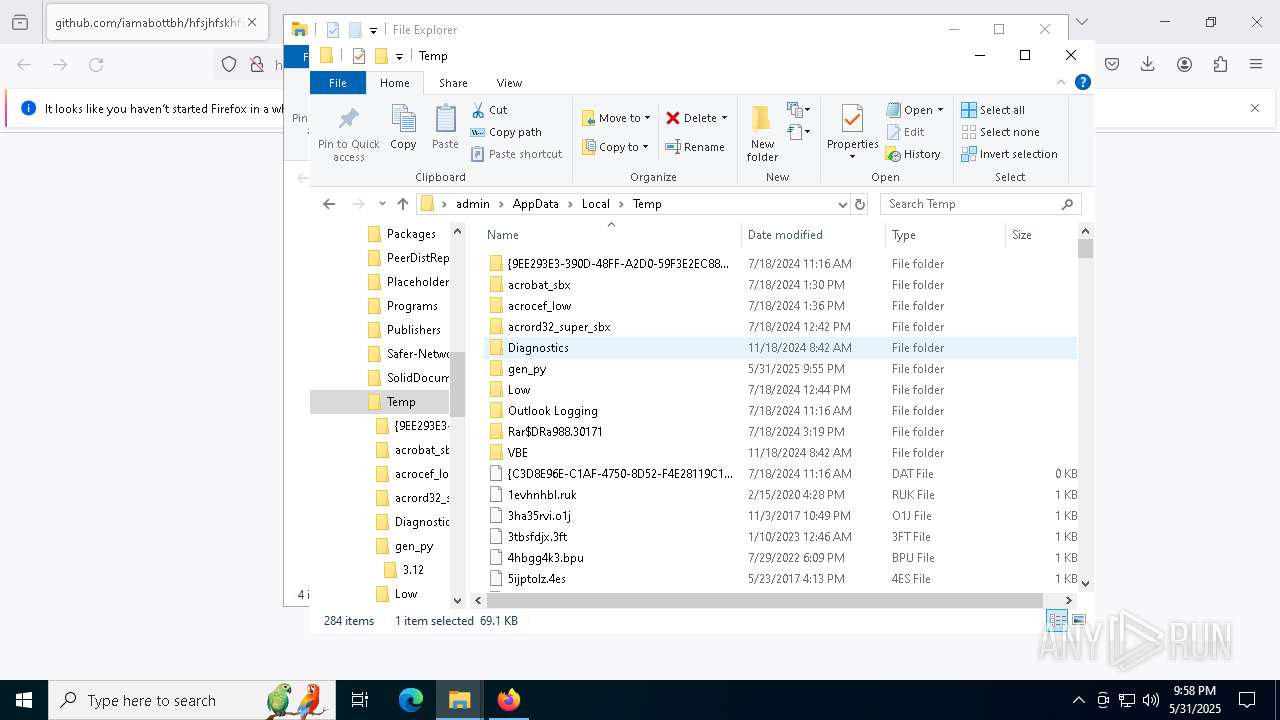
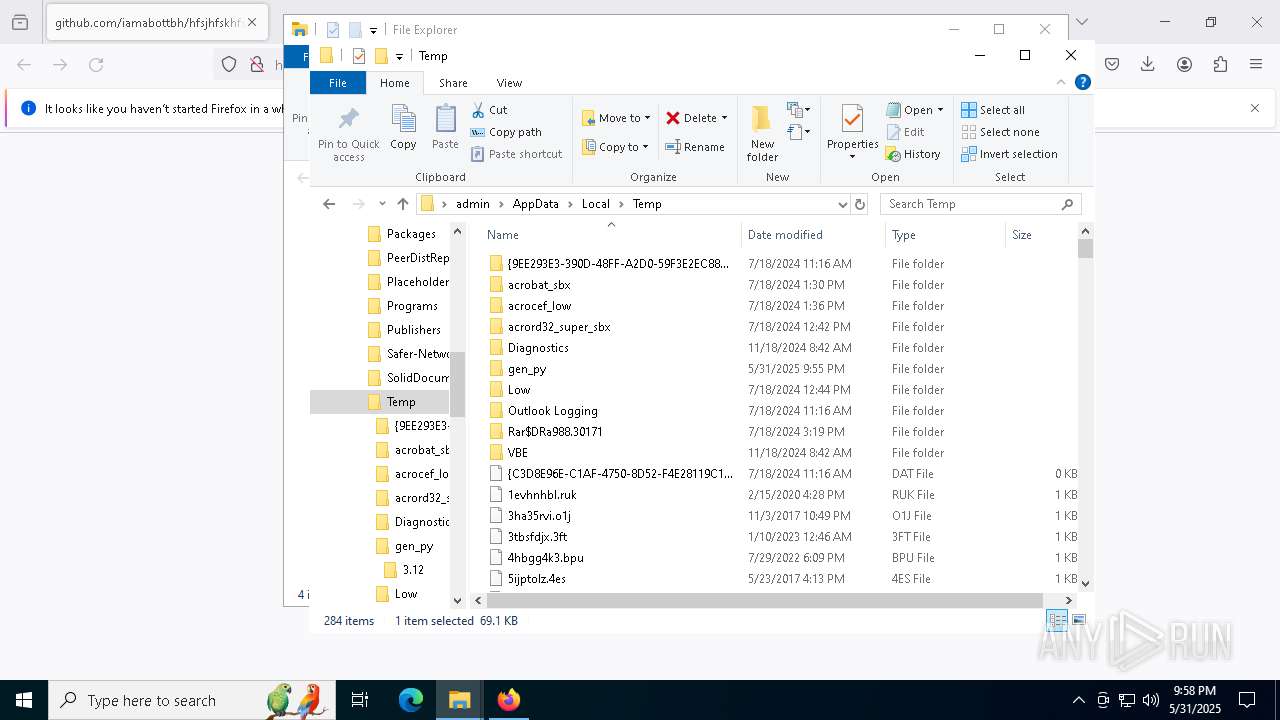
Create files in a temporary directory
- system_service.exe (PID: 472)
- system_service.exe (PID: 7788)
The sample compiled with english language support
- system_service.exe (PID: 472)
- system_service.exe (PID: 668)
Reads the computer name
- system_service.exe (PID: 7788)
Drops encrypted JS script (Microsoft Script Encoder)
- system_service.exe (PID: 7788)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 132)
- WMIC.exe (PID: 7228)
- WMIC.exe (PID: 7500)
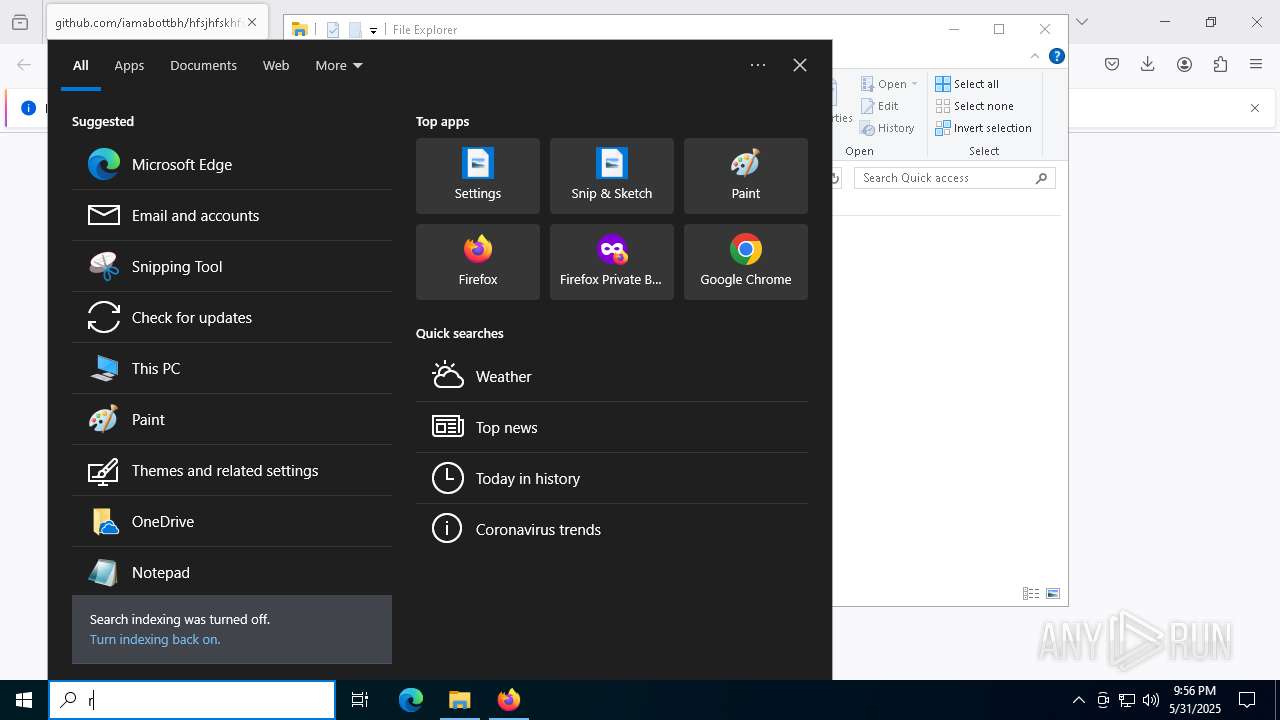
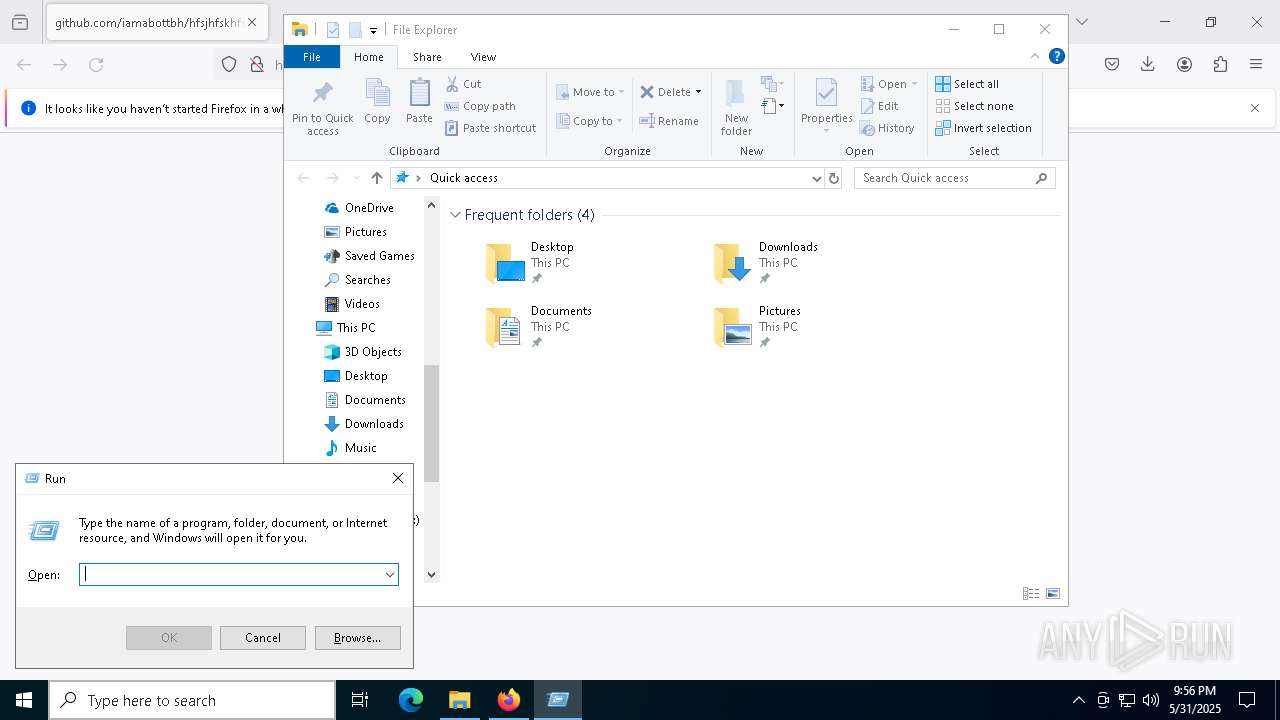
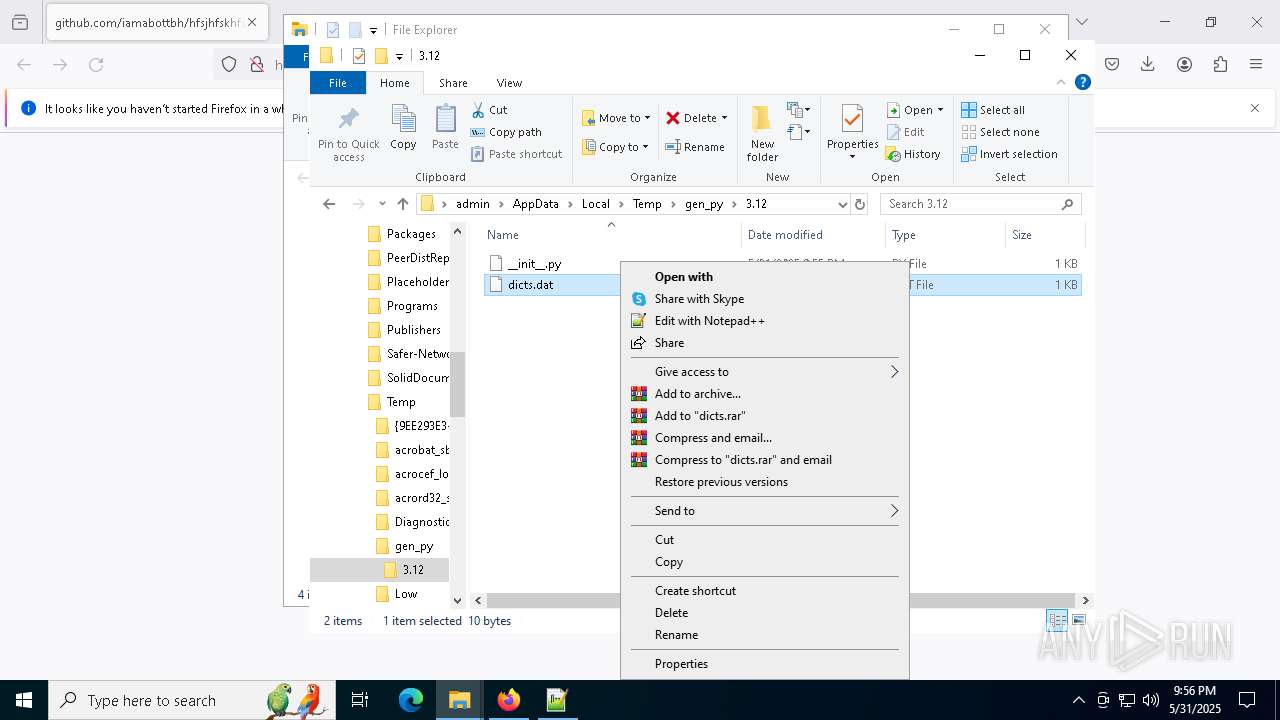
Manual execution by a user
- notepad.exe (PID: 536)
- notepad++.exe (PID: 2284)
- system_service.exe (PID: 668)
- notepad++.exe (PID: 456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
306
Monitored processes
170
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | wmic diskdrive get model | C:\Windows\System32\wbem\WMIC.exe | — | system_service.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | taskkill /F /IM windasm.exe | C:\Windows\System32\taskkill.exe | — | system_service.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | taskkill /F /IM process.exe | C:\Windows\System32\taskkill.exe | — | system_service.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | C:\WINDOWS\system32\cmd.exe /c "wmic path win32_VideoController get name" | C:\Windows\System32\cmd.exe | — | system_service.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
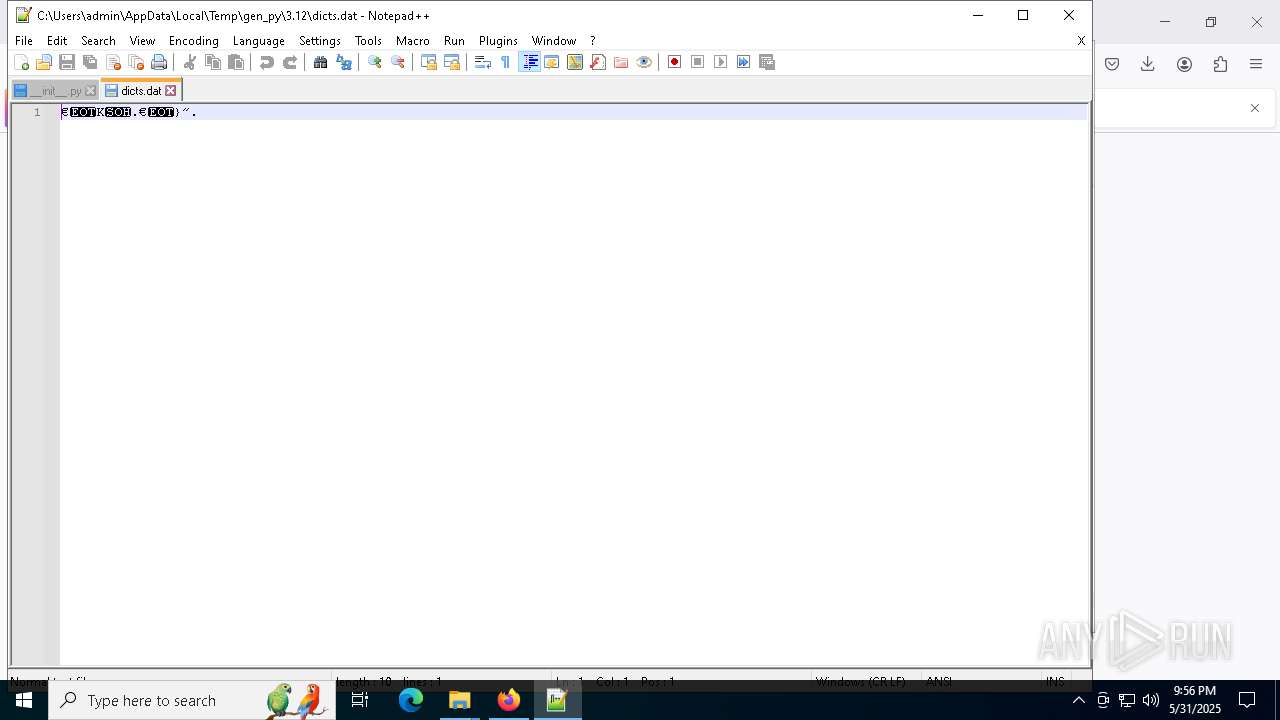
| 456 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\gen_py\3.12\dicts.dat" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 472 | "C:\Users\admin\Downloads\system_service.exe" | C:\Users\admin\Downloads\system_service.exe | firefox.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\DESKTOP-JGLLJLD-20240308-0110.log | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 656 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 387
Read events
33 385
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2600) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (2600) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
Executable files
567
Suspicious files
174
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2600 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2600 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2600 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:C09FF302D57C404B61E6A89B0B9F36E7 | SHA256:6A5B4F82595799346D0E501FE6CC8629E0FD6ED27B74D0E6CB5073DDB2E3C40B | |||
| 2600 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2600 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:22DA36CA5BA1D055ADE237F52DC825A7 | SHA256:7438A5D5298BFA0ABAB51E6B35EAC0F26B830BCEFBDBEB5F07721DBA34F89E0D | |||
| 2600 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2600 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2600 | firefox.exe | C:\Users\admin\Downloads\system_service.srtUWfPB.exe.part | — | |
MD5:— | SHA256:— | |||
| 2600 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:3B237642D43F89E82BAB831746DEA95A | SHA256:566B542CFF0CF40FF4798E600B5D13AB354CD3BADAC0534E9F746427A6BCBA2E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
92
DNS requests
129
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2600 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2600 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
2600 | firefox.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
2600 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
2600 | firefox.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
2600 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2600 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
2600 | firefox.exe | POST | 200 | 2.16.206.143:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2600 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://o.pki.goog/s/wr3/3H4 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7188 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2600 | firefox.exe | 34.36.137.203:443 | spocs.getpocket.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
2600 | firefox.exe | 185.199.108.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
2600 | firefox.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
2600 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
github.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
mc.prod.ads.prod.webservices.mozgcp.net |
| whitelisted |