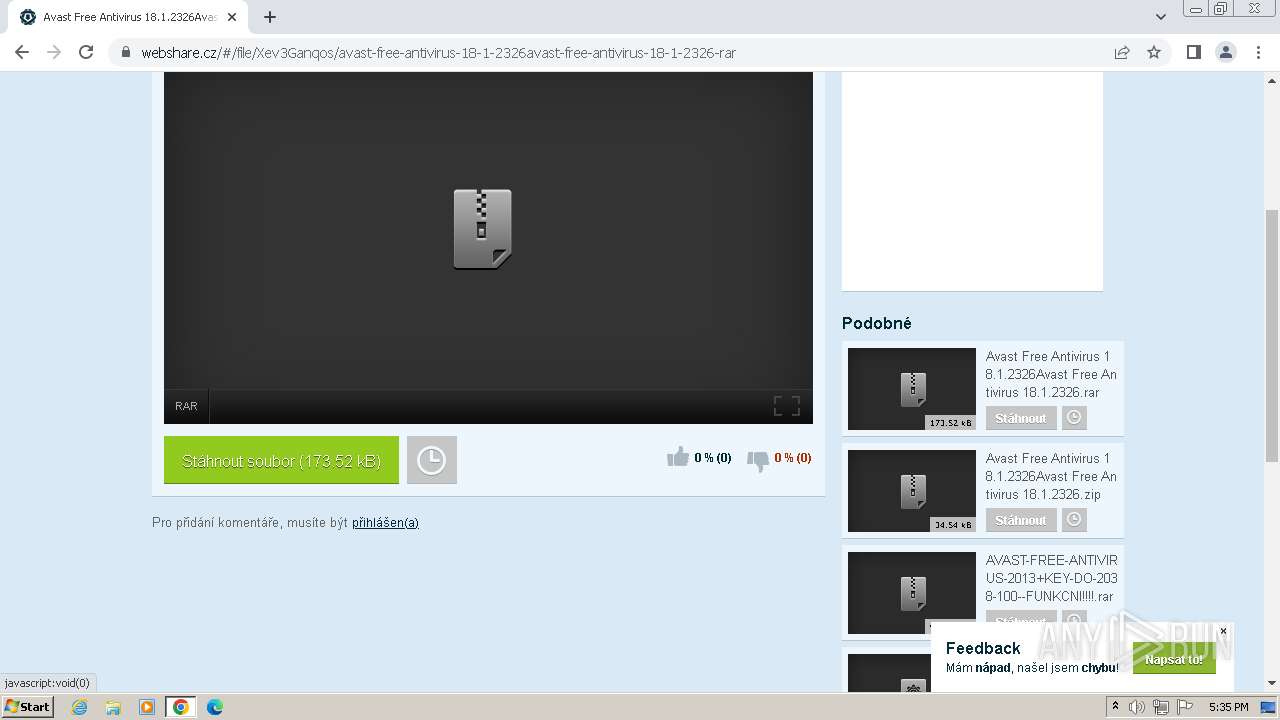
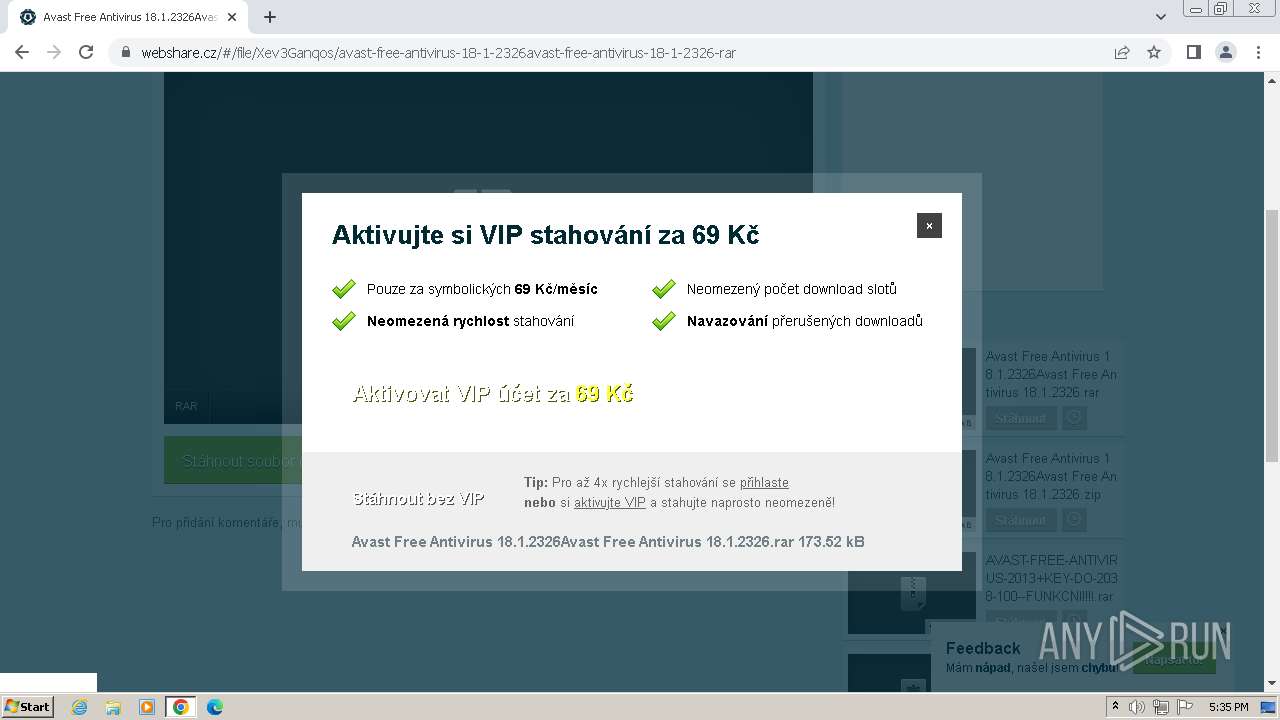
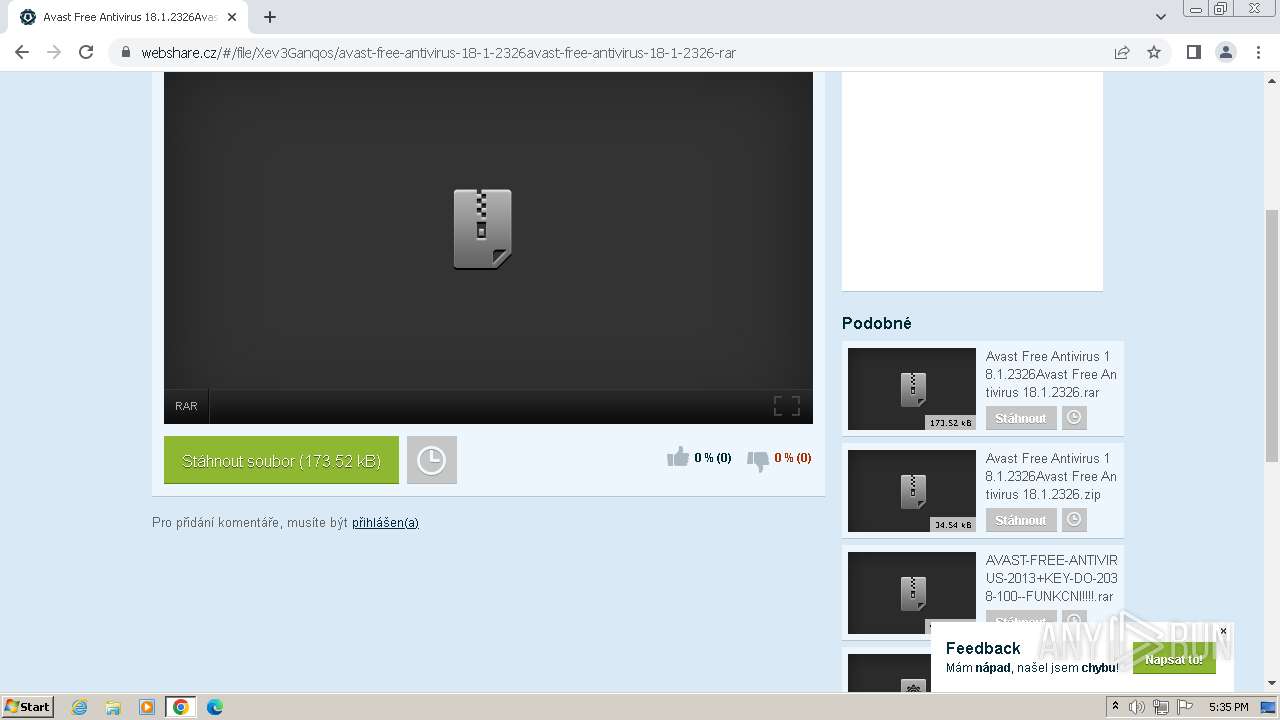
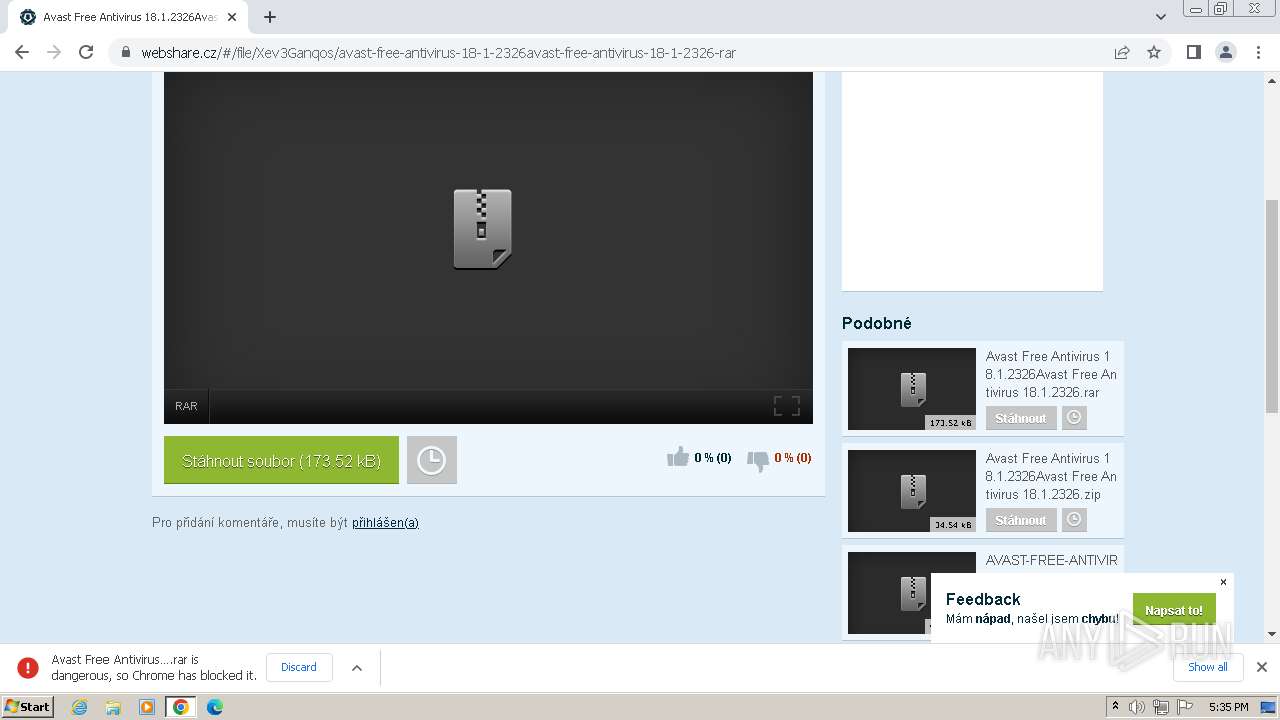
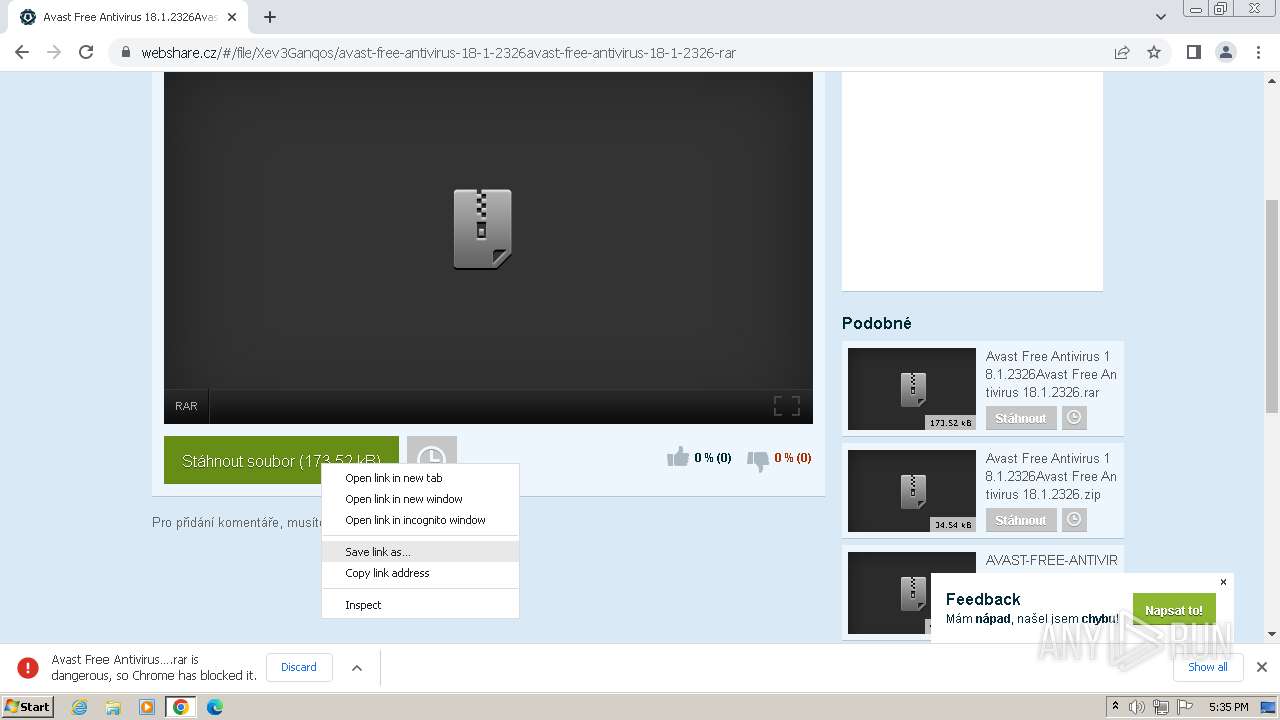
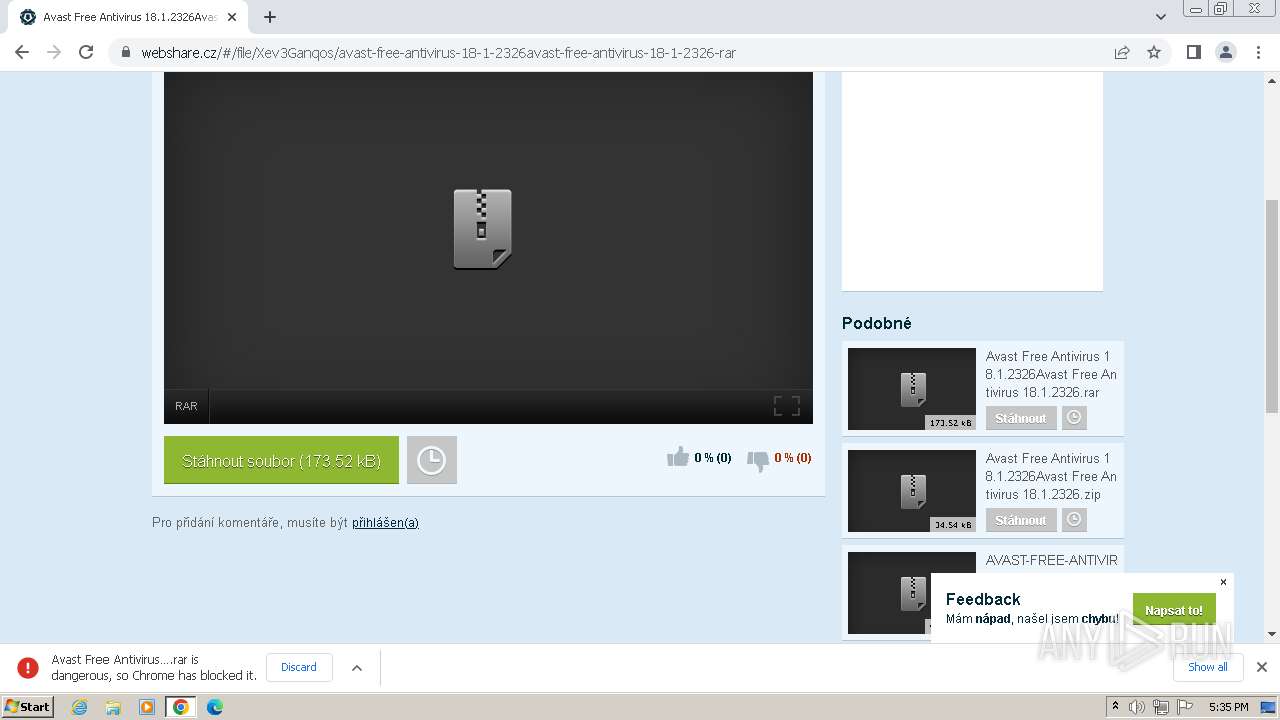
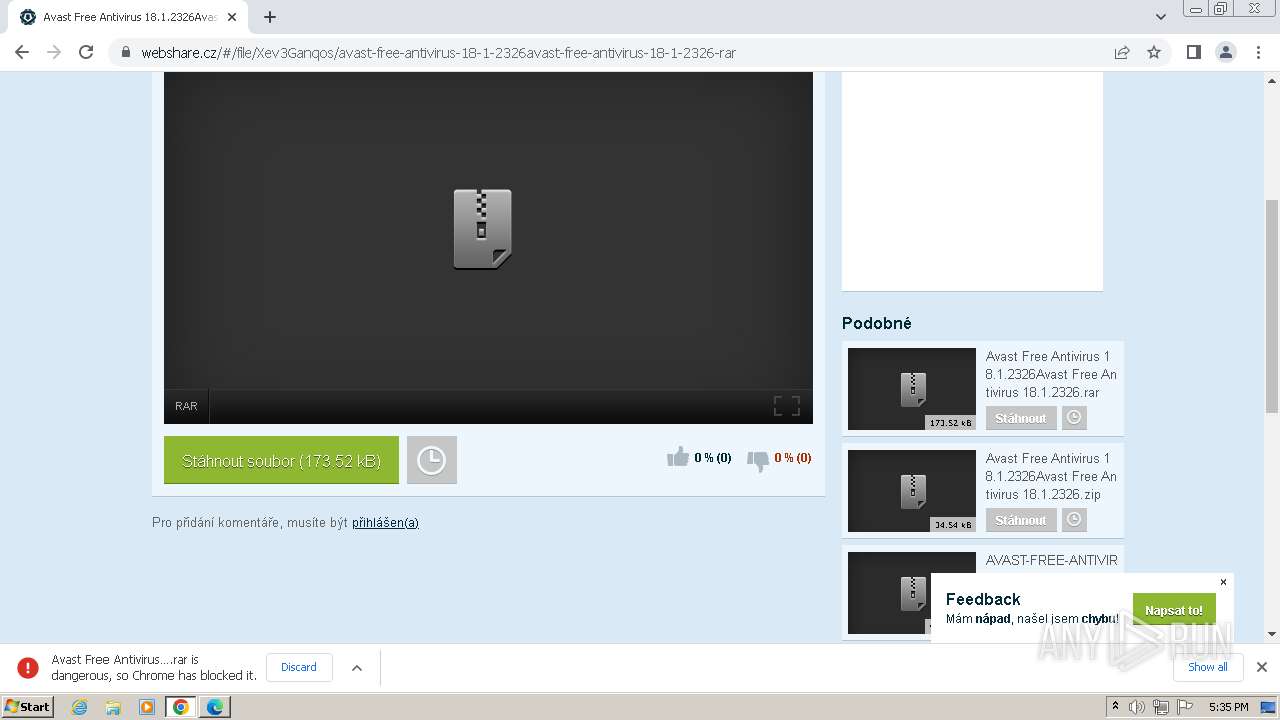
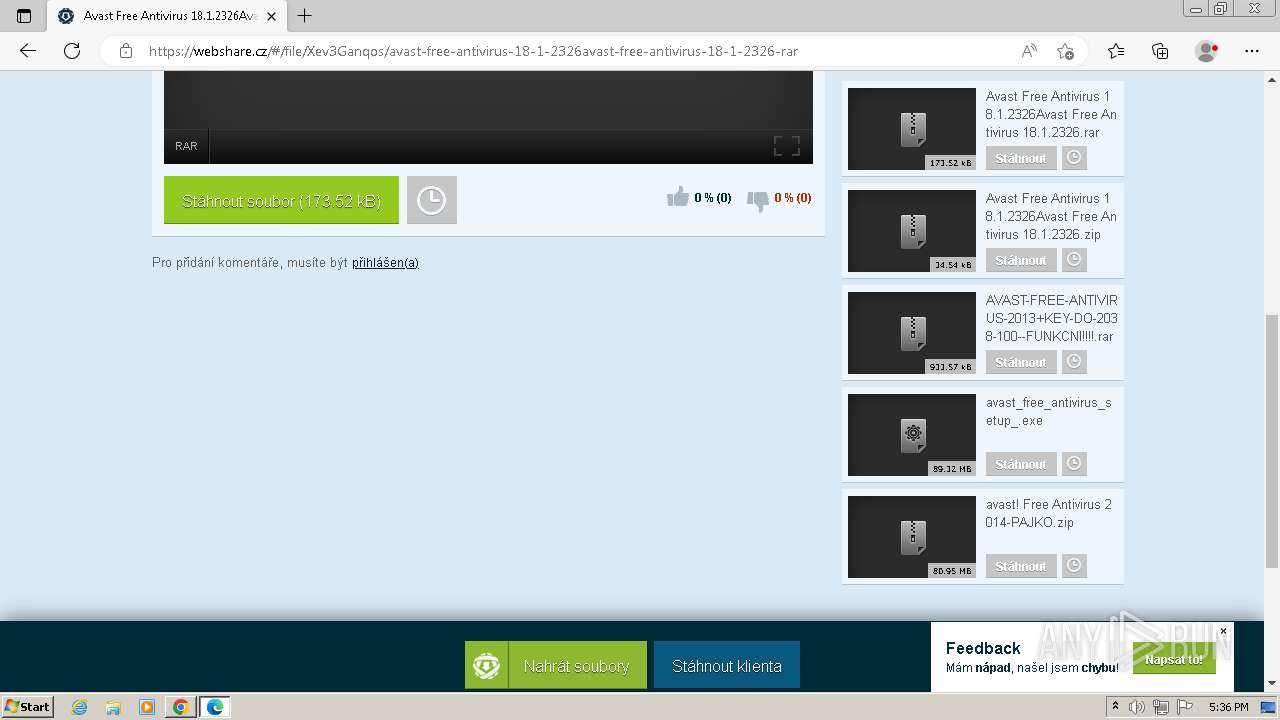
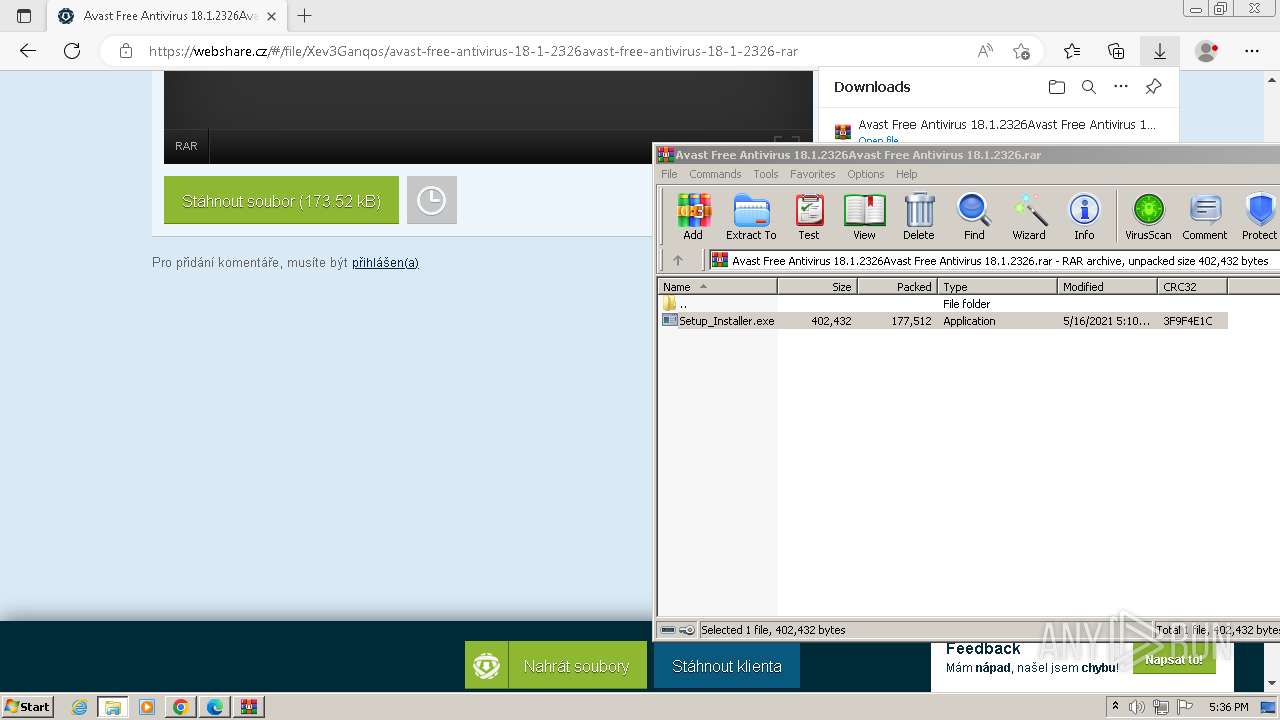
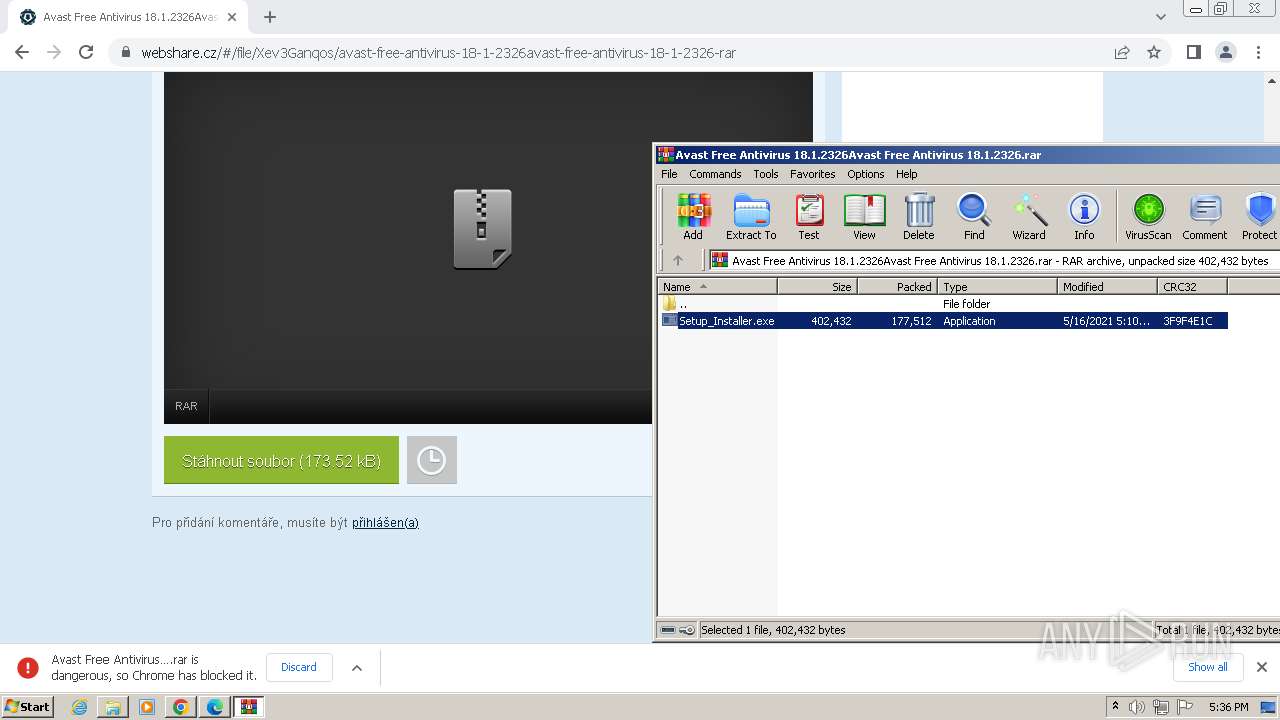
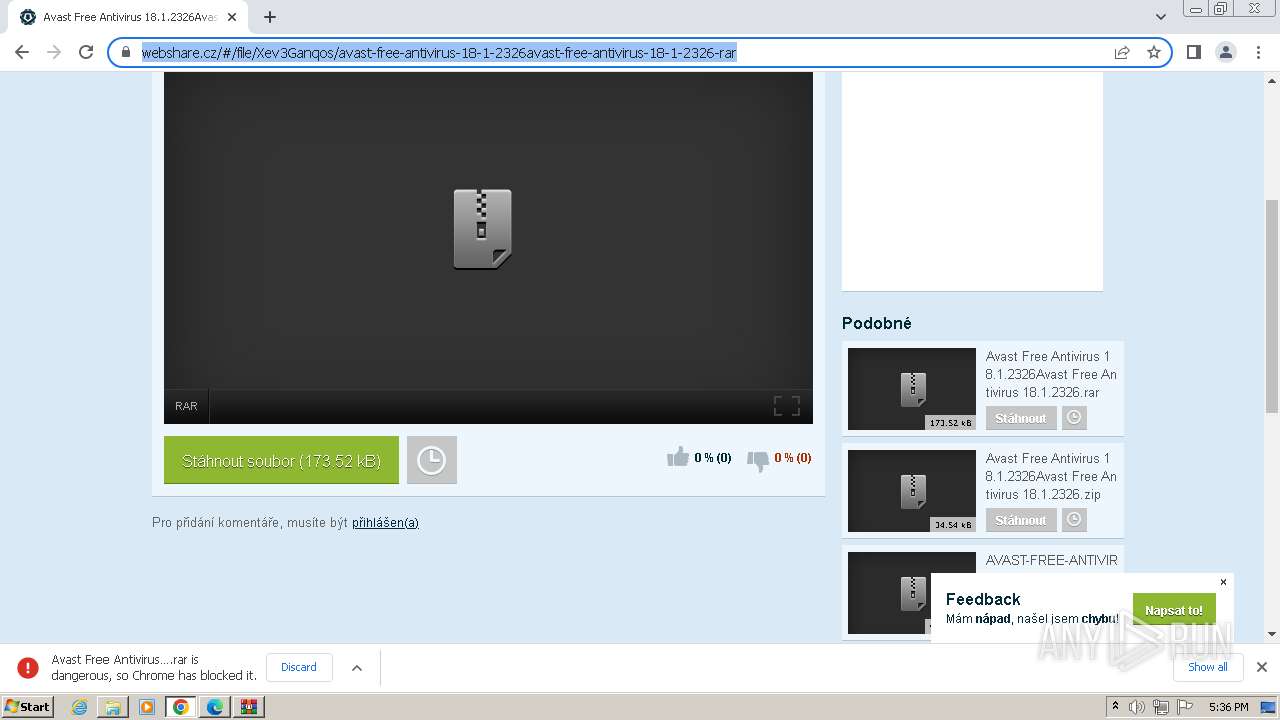
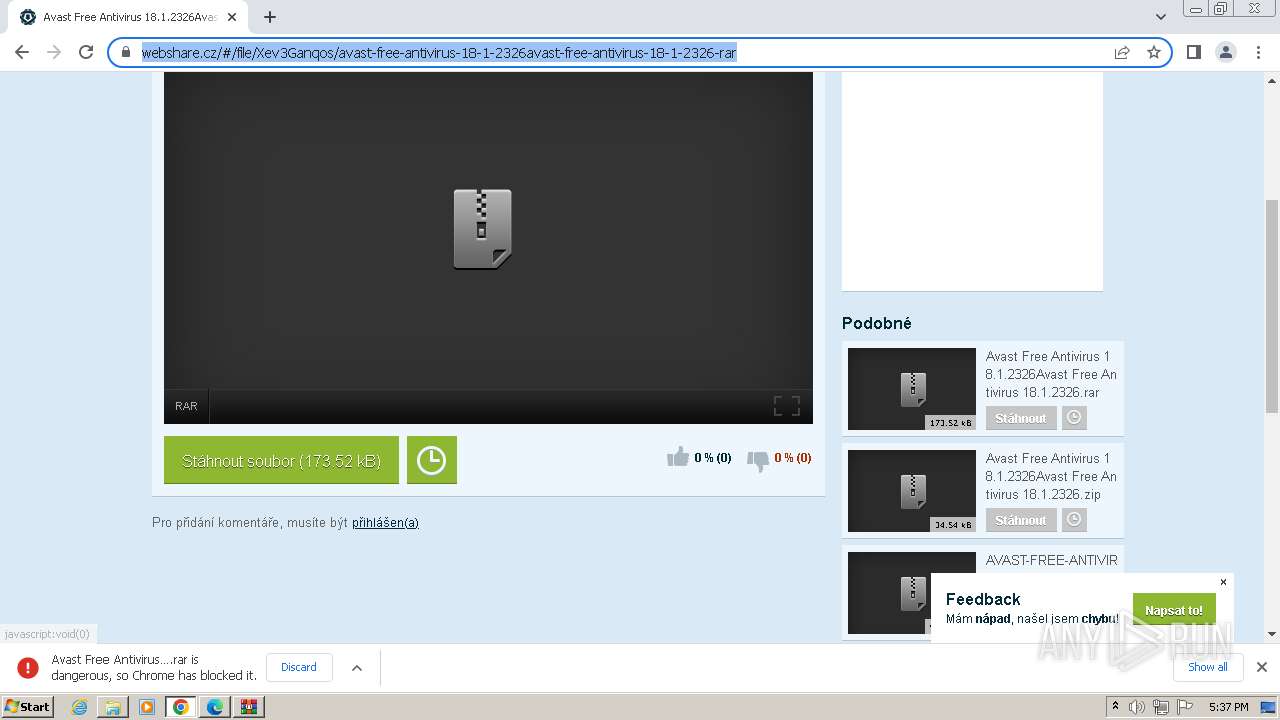
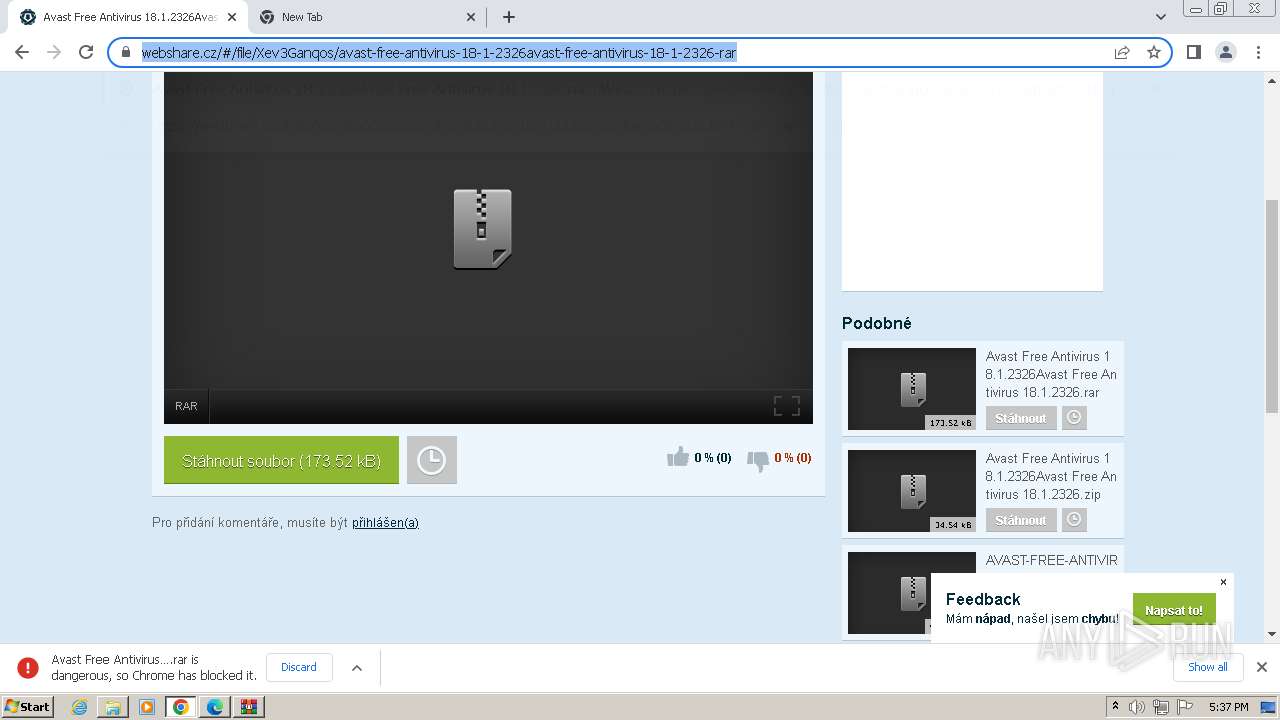
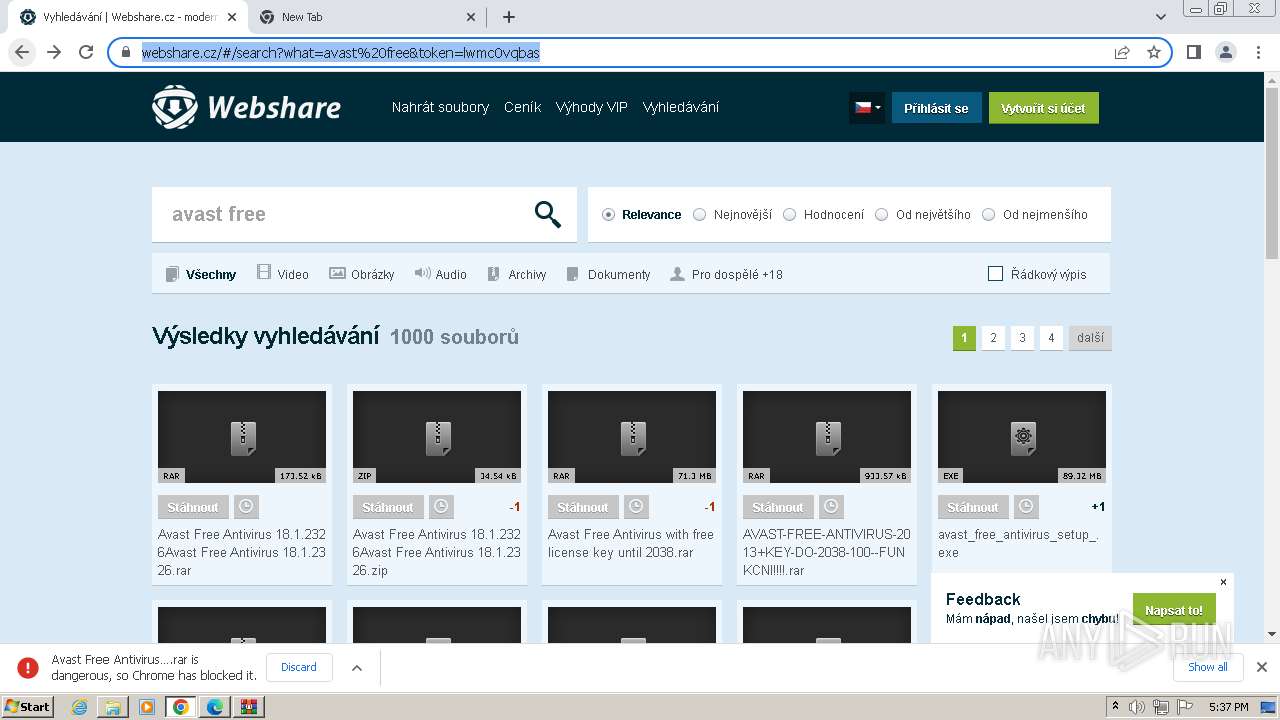
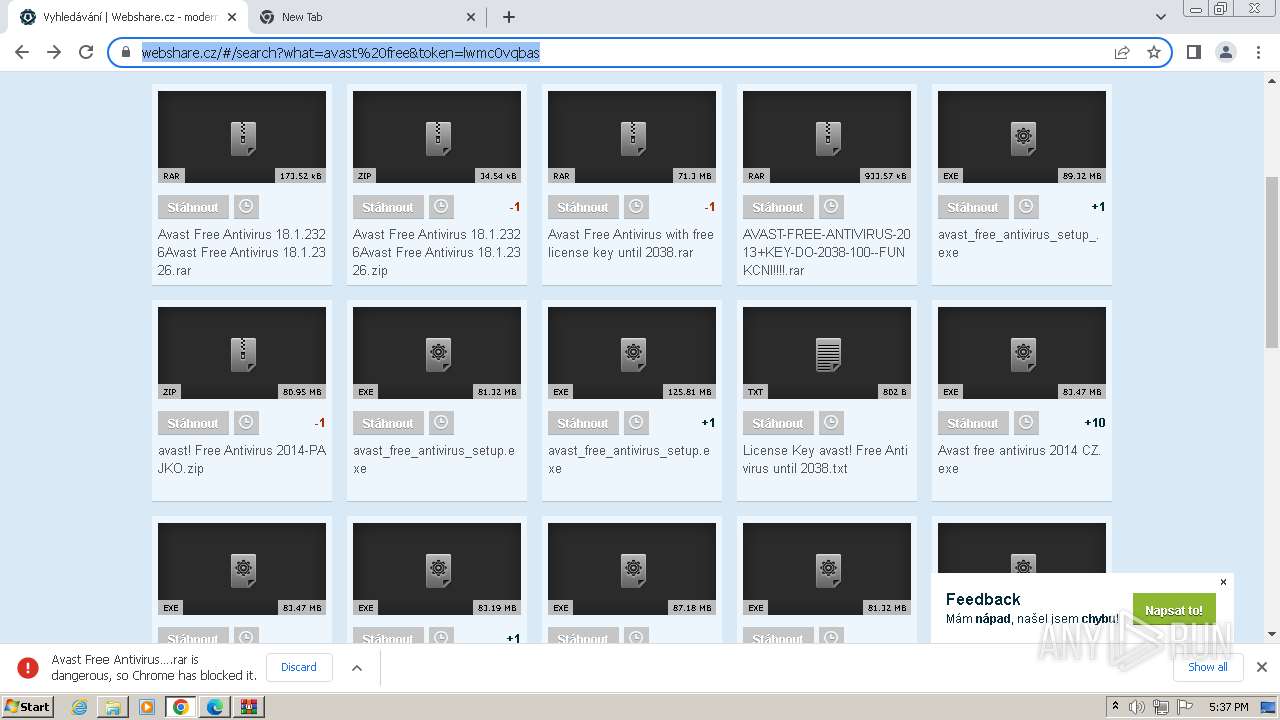
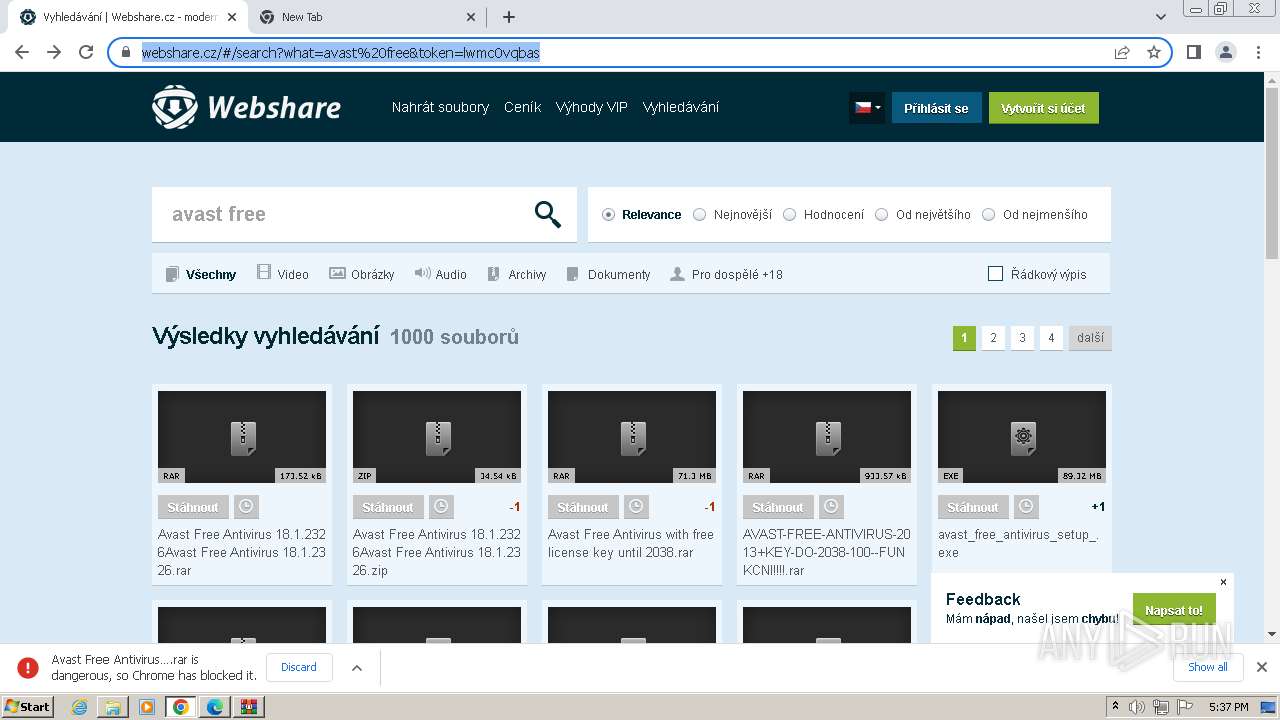
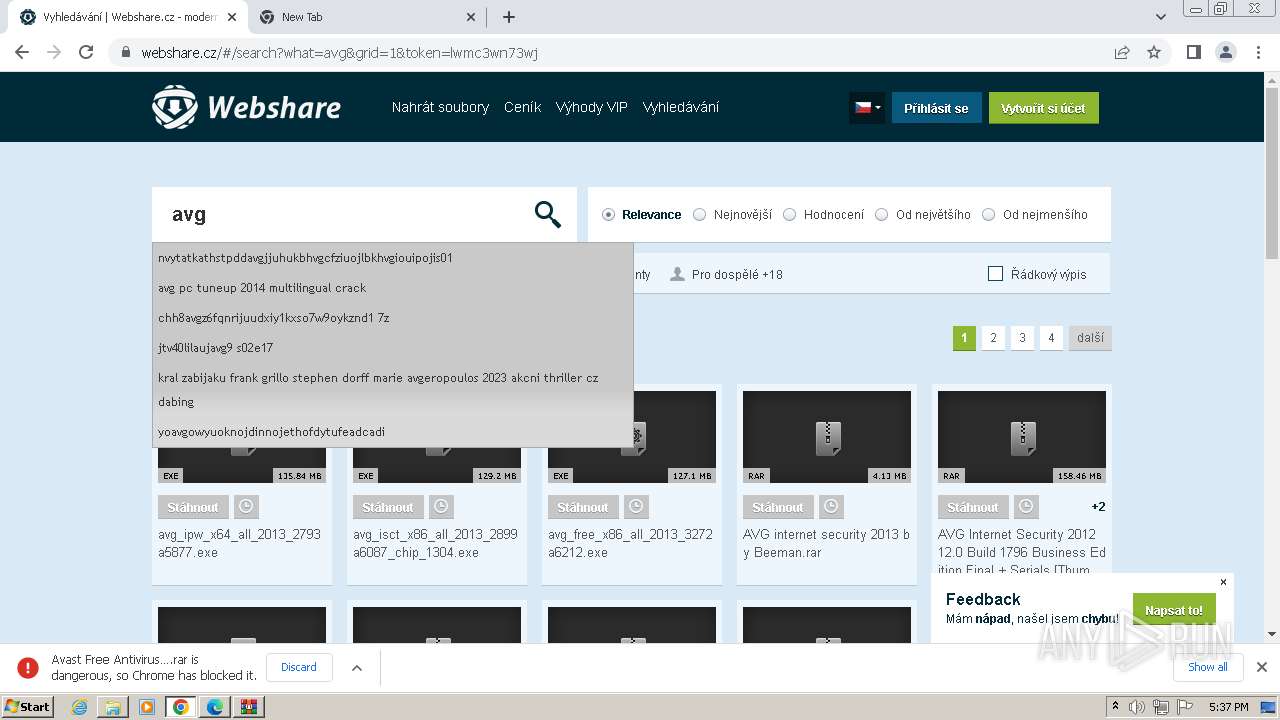
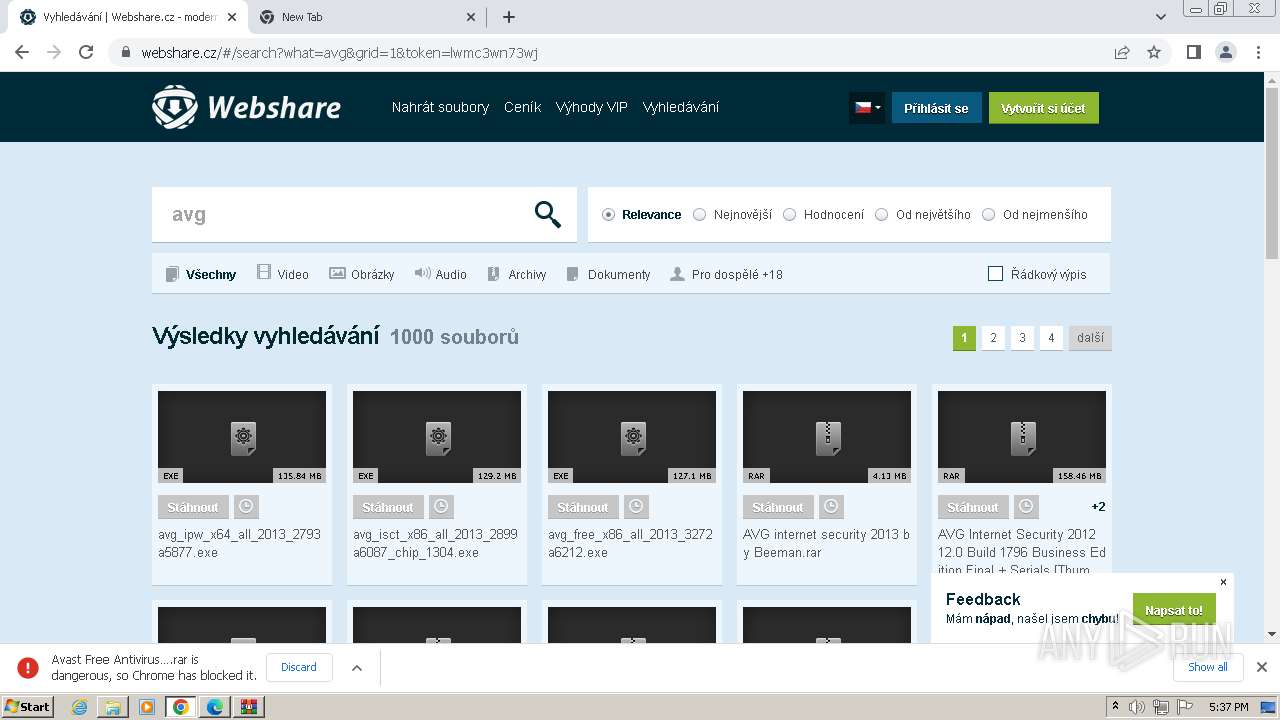
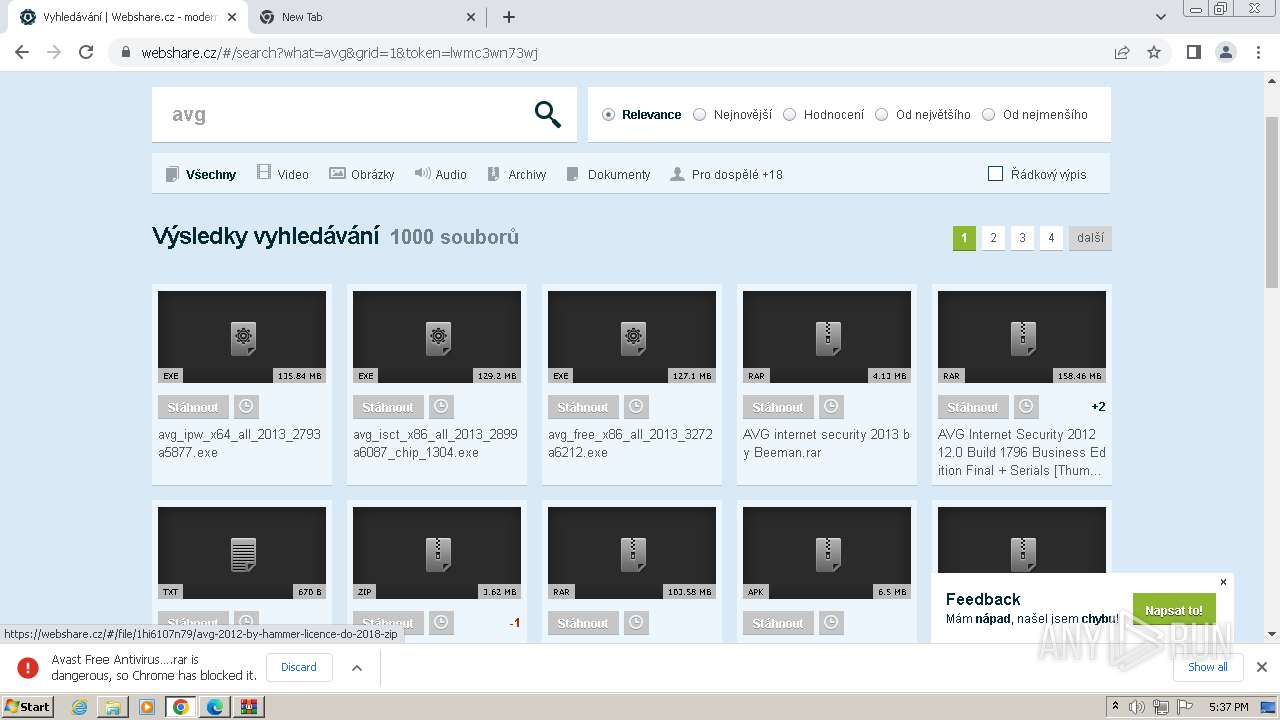
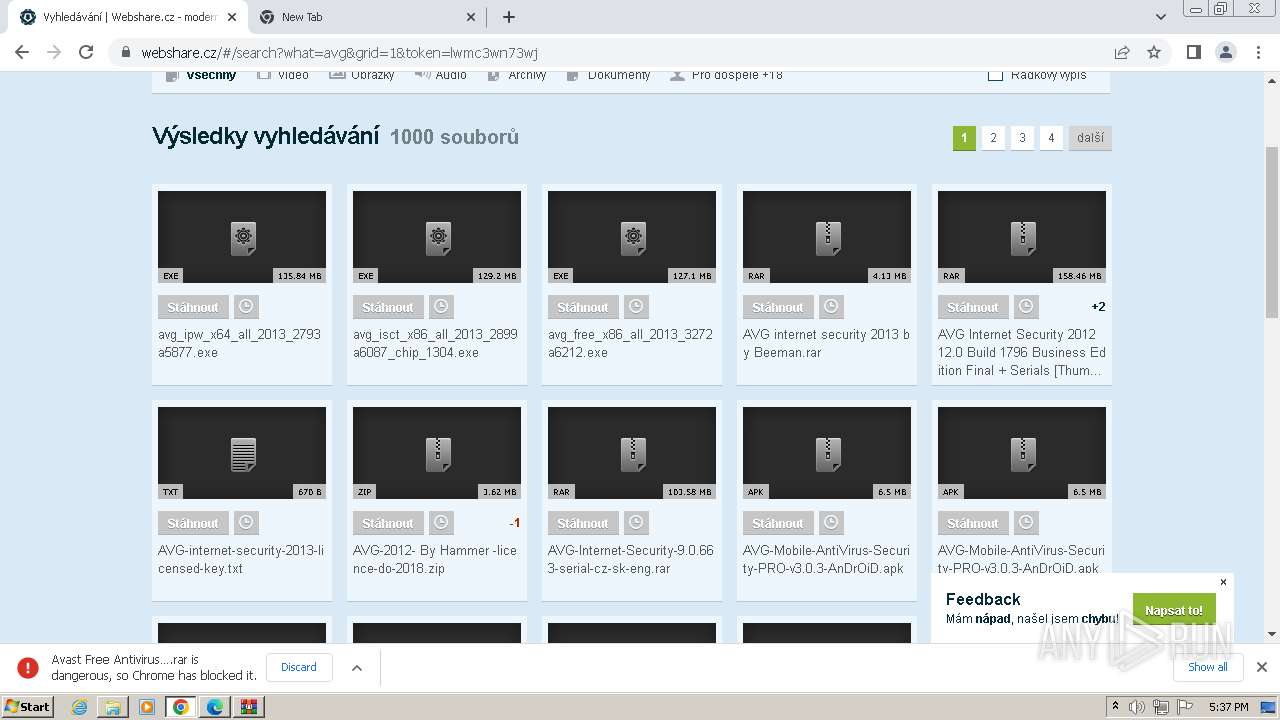
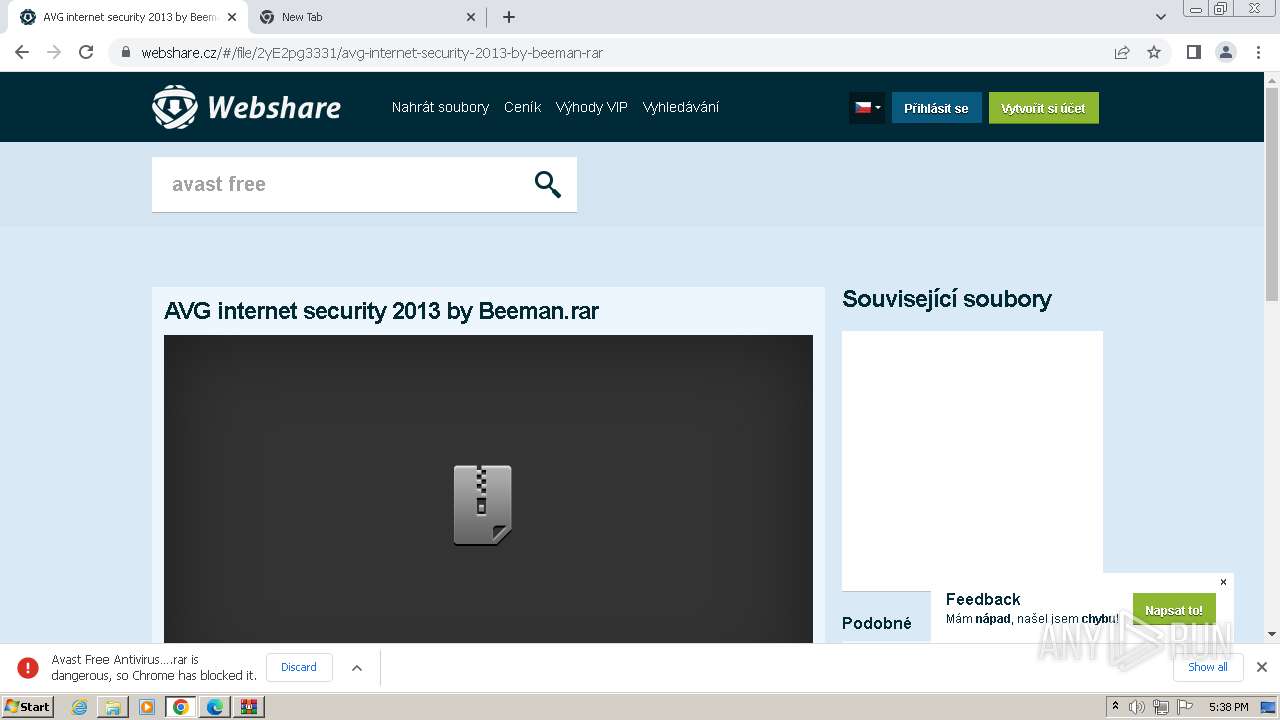
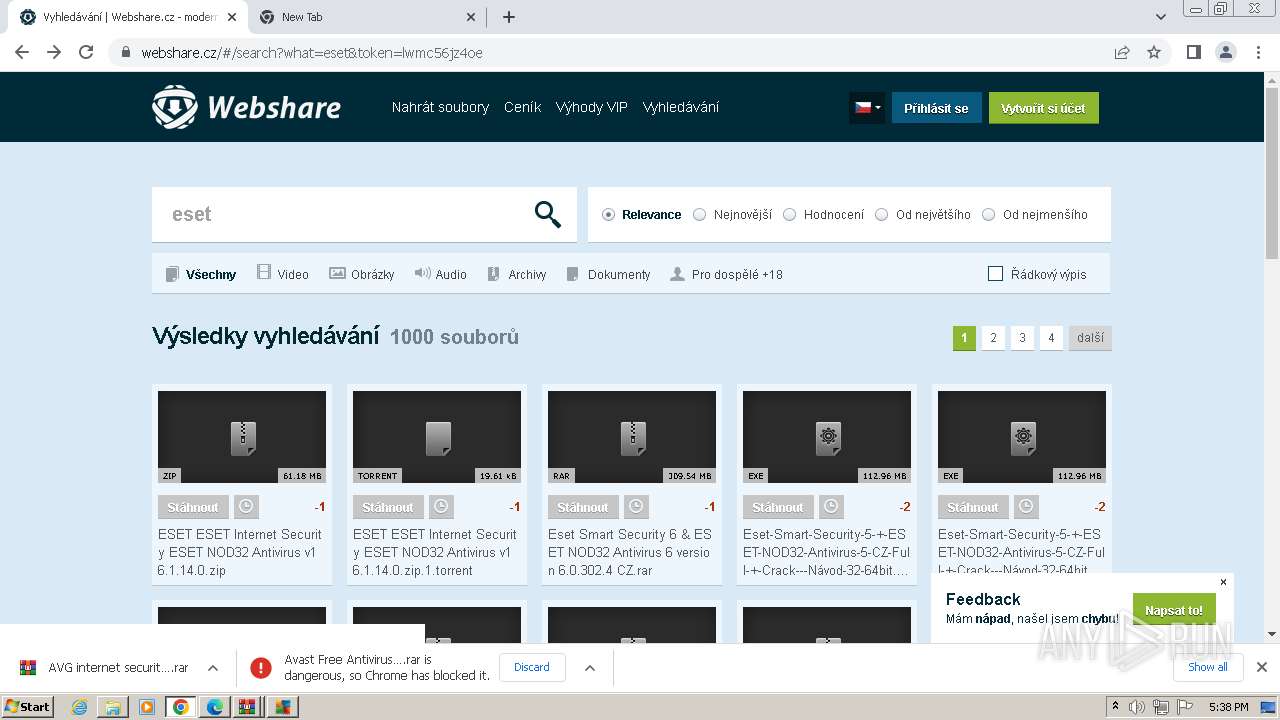
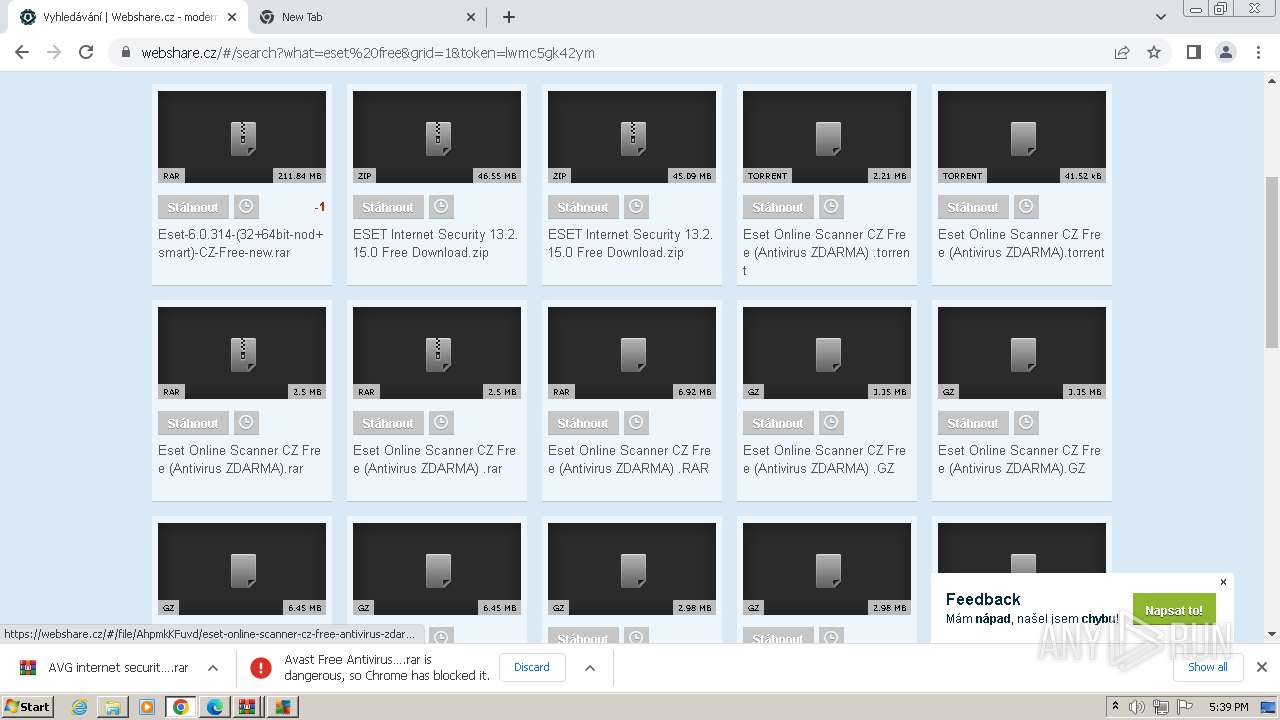
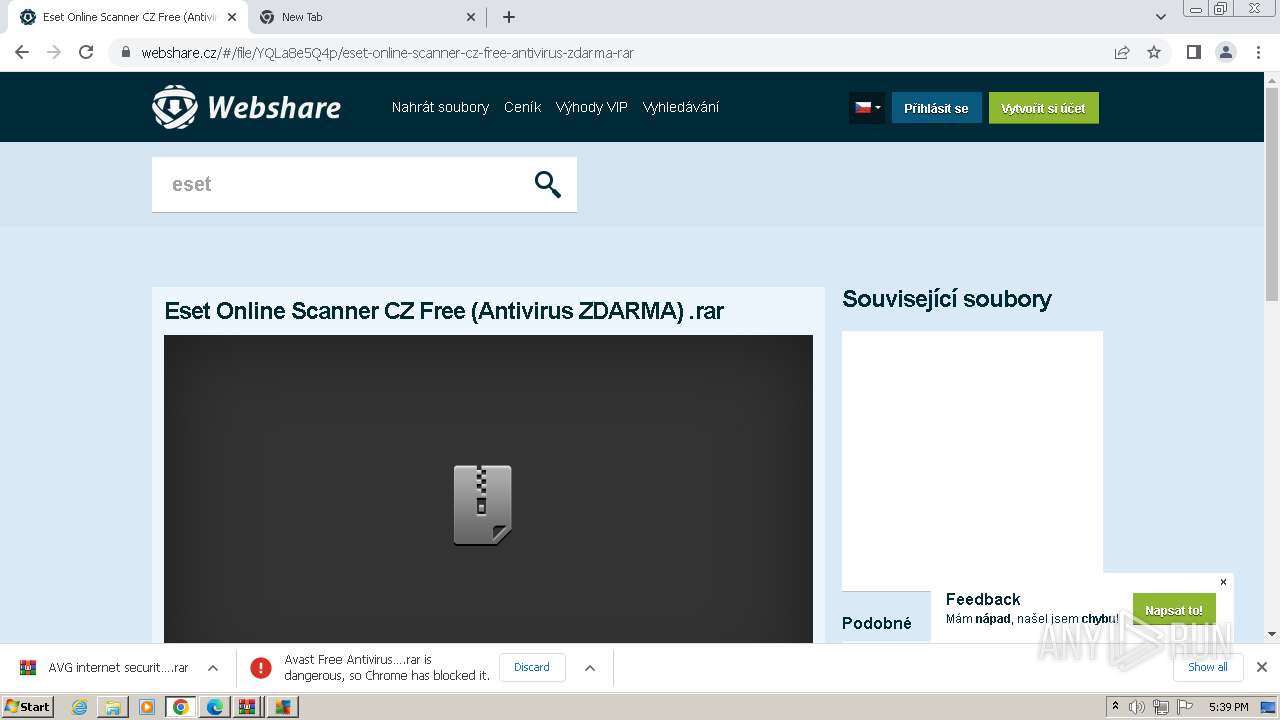
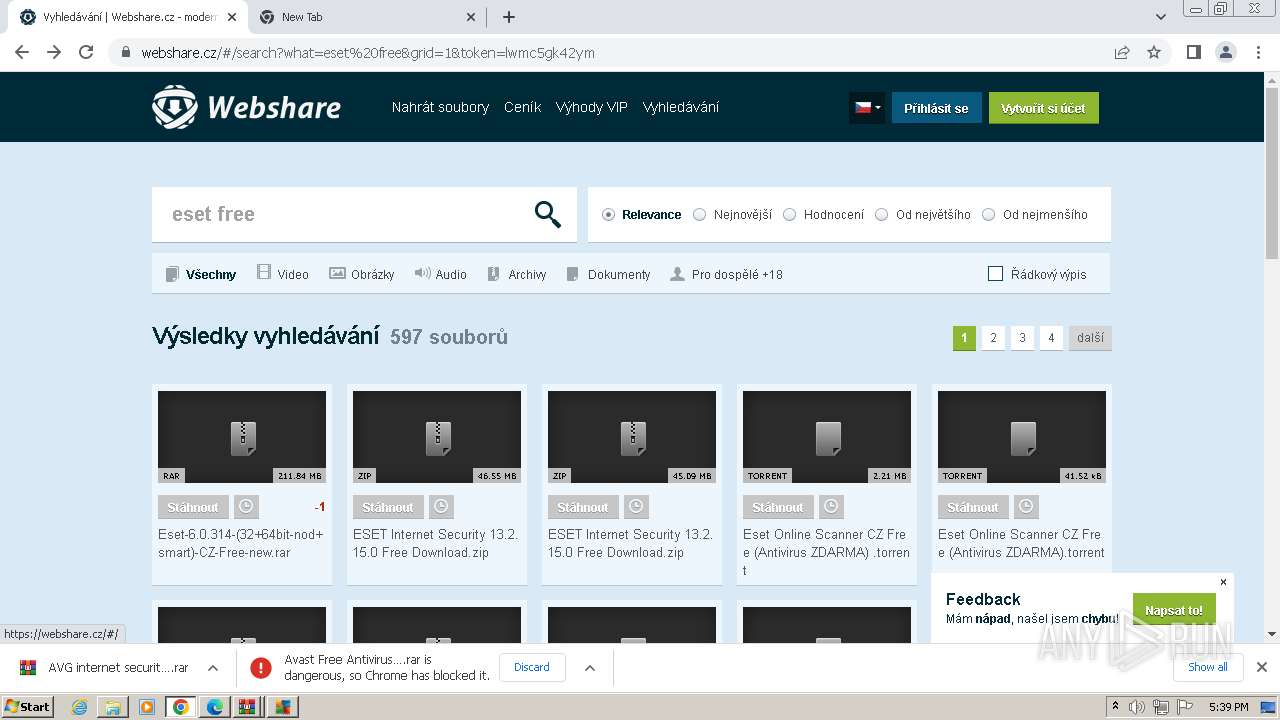
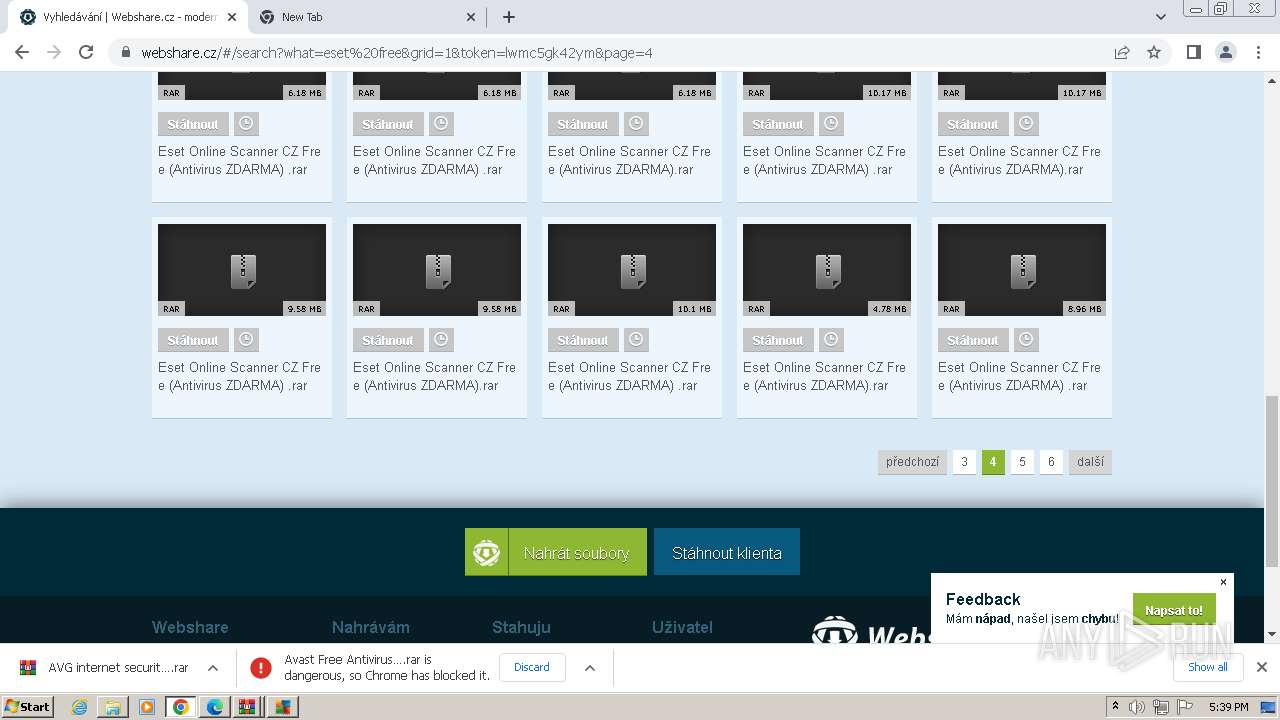
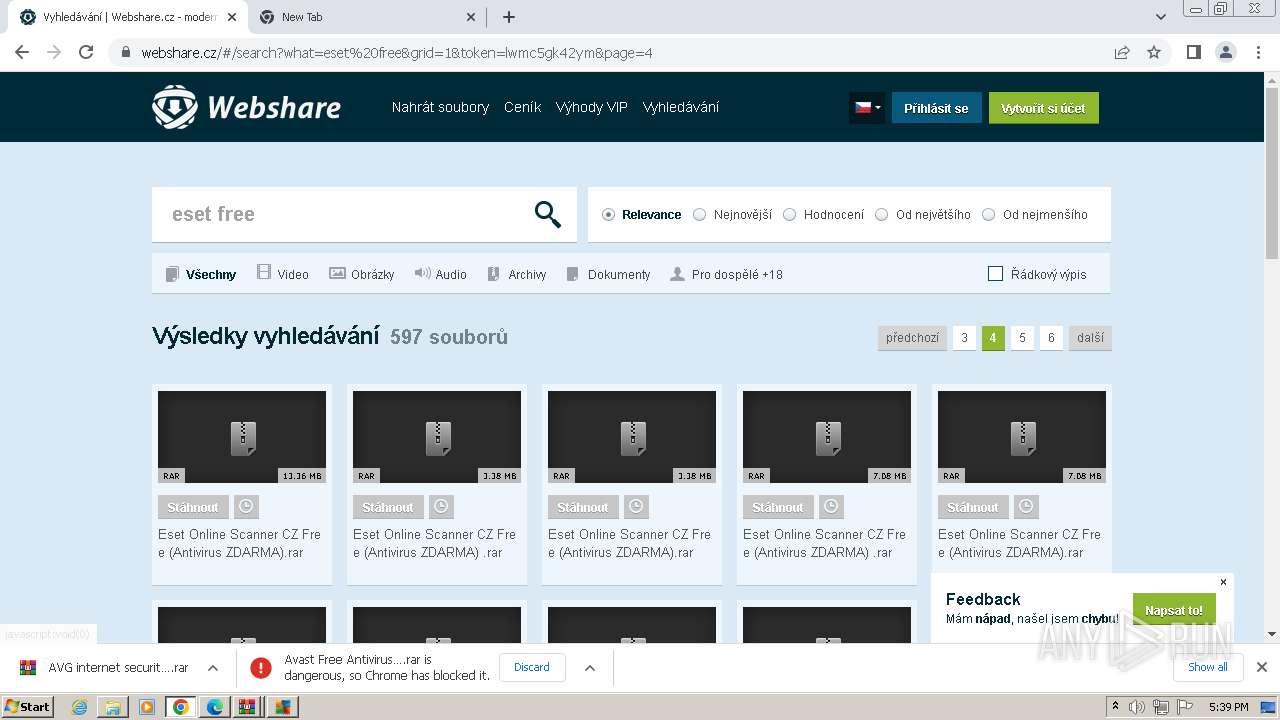
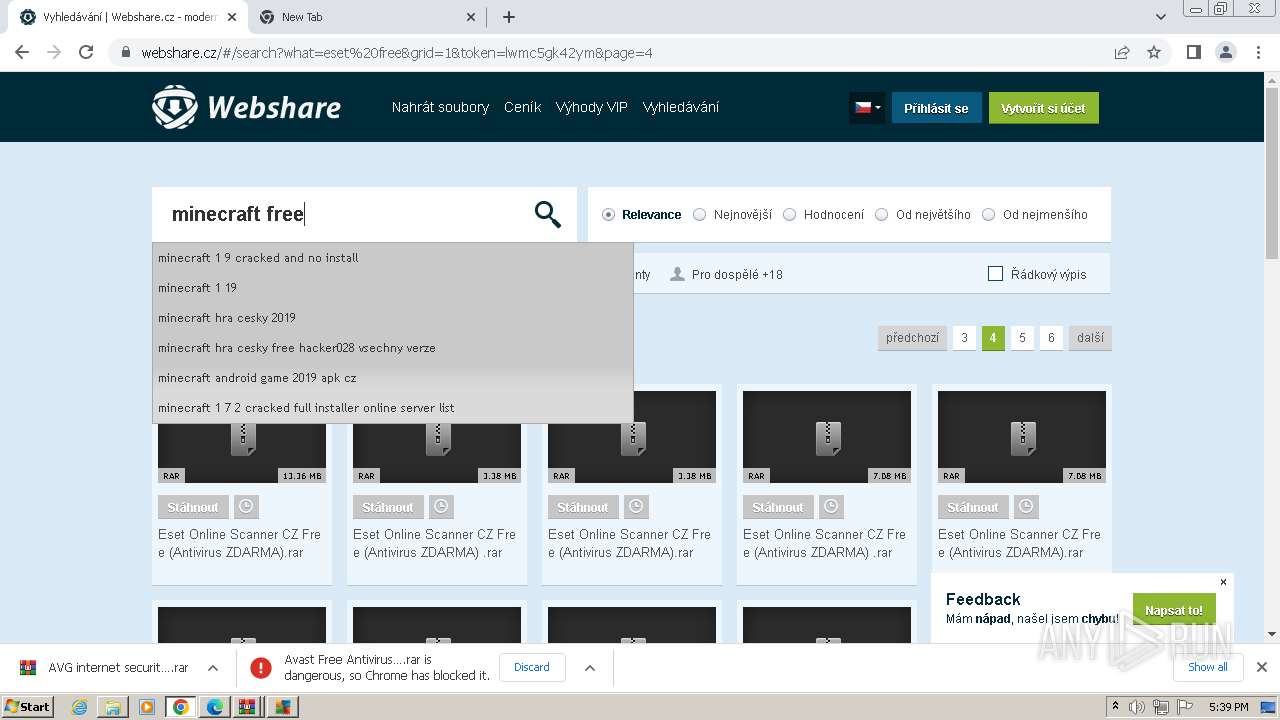
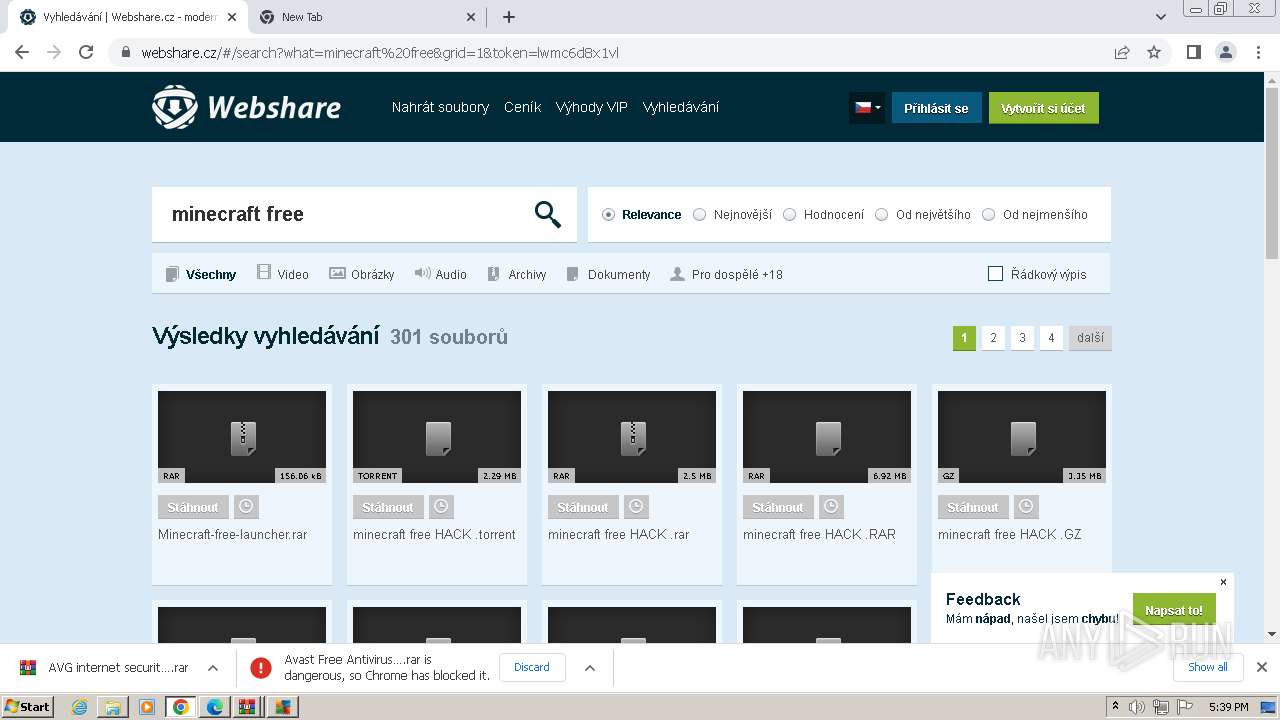
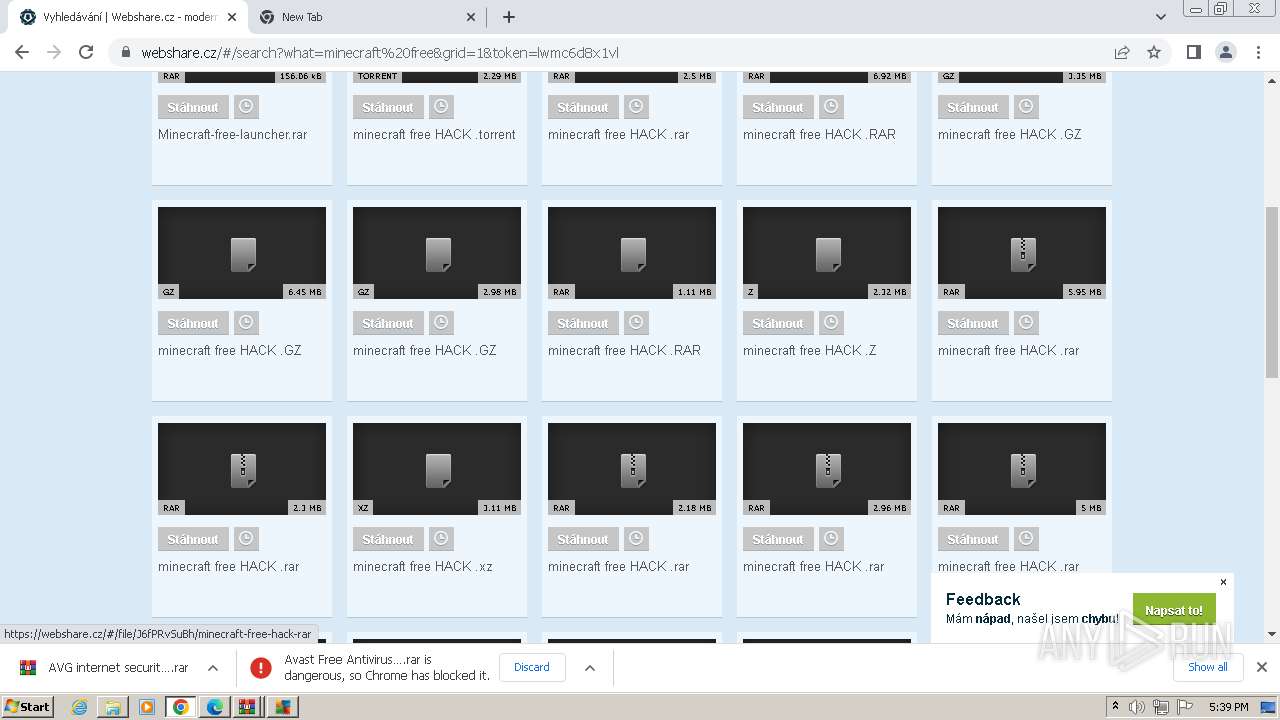
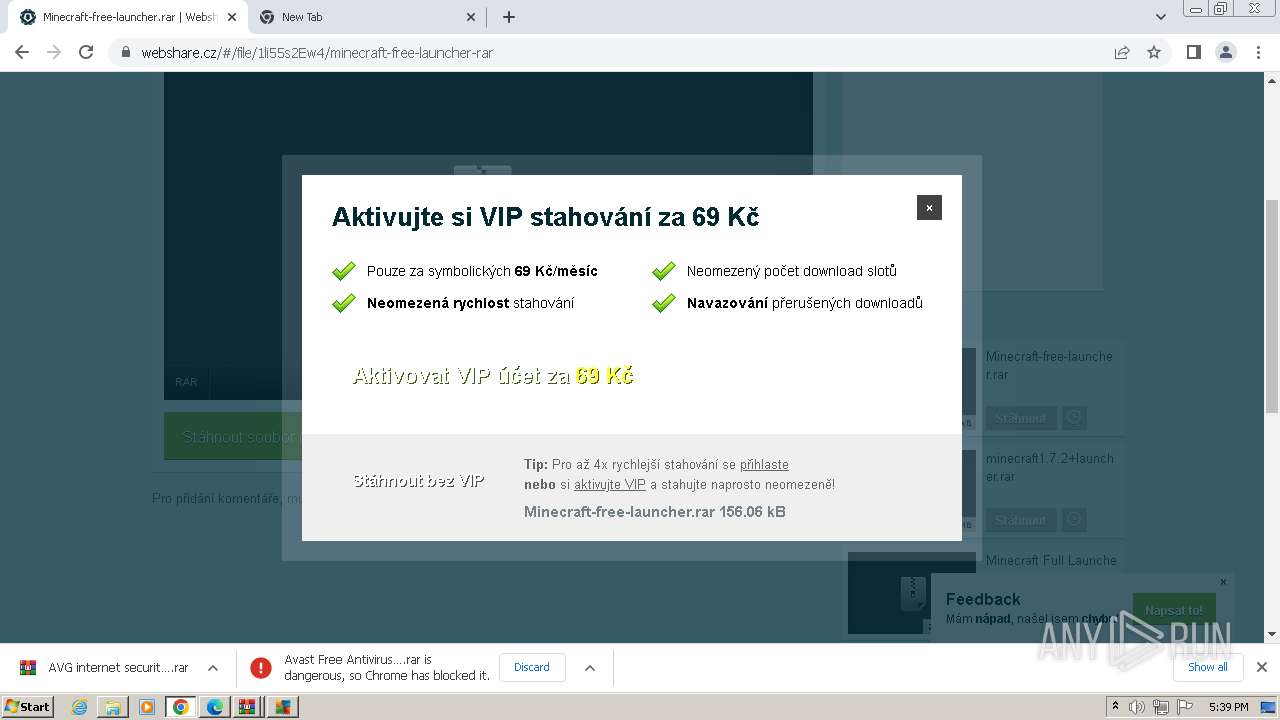
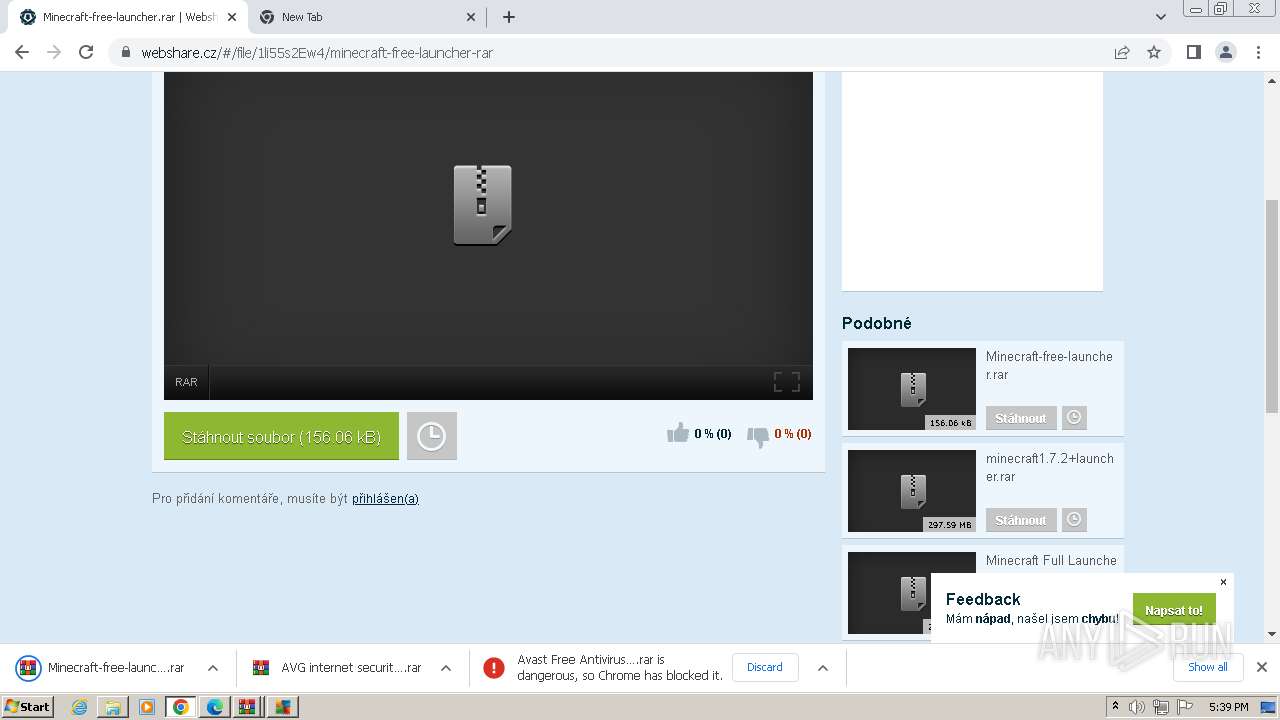
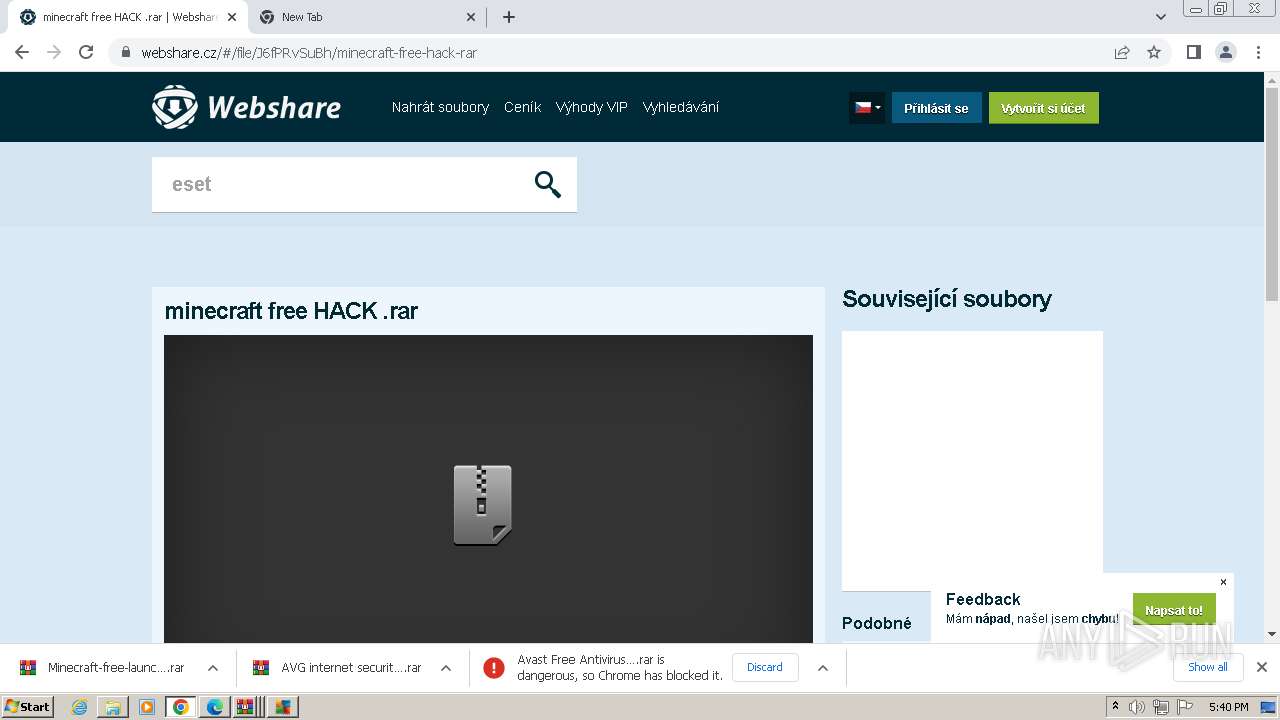
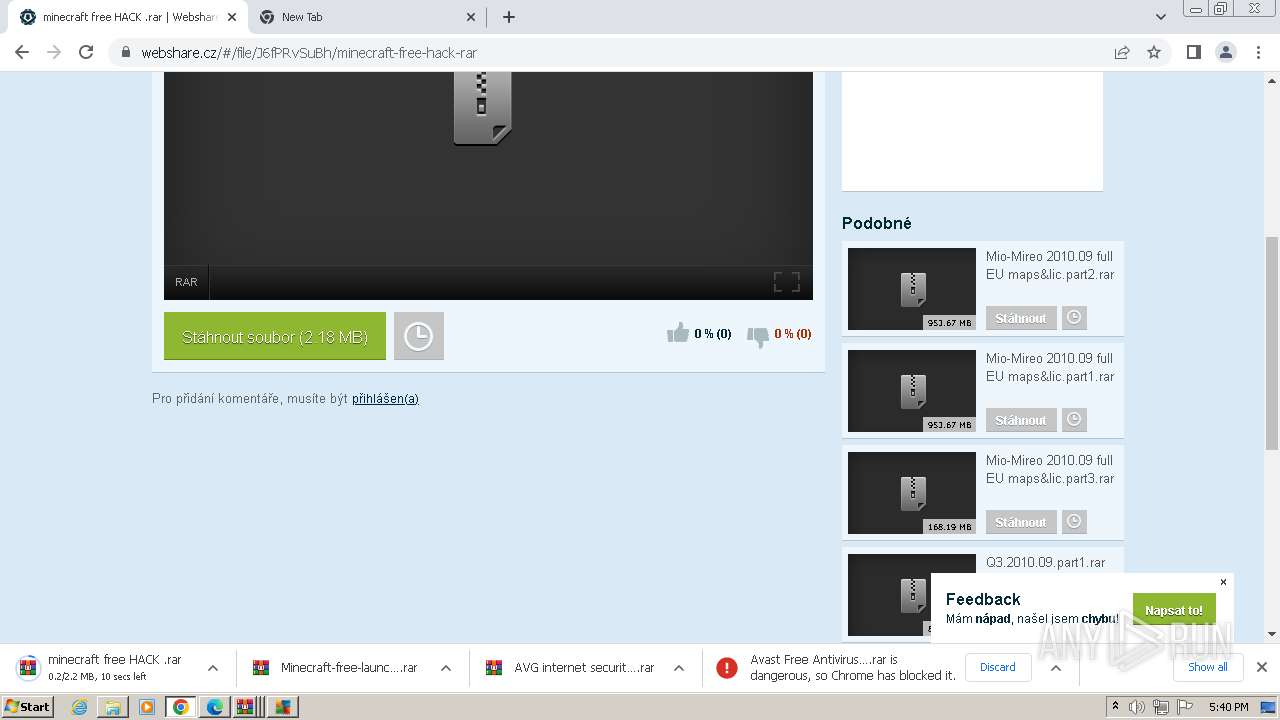
| URL: | https://webshare.cz/#/file/3142VS6bb4/minecraft-cracked-launcher-1-7-4-exe |
| Full analysis: | https://app.any.run/tasks/f1c486c6-4dad-4c20-912b-0ef7aa319f35 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2024, 16:35:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6F29950228D4CB601784E7855CDEB60B |
| SHA1: | 428CACD05798EF6738012E359DF3598A1B36E4C0 |
| SHA256: | ABC262D6F3D26F1E723852E0AD7F6D4F84423C7F9AA42454BB66B388DE64097D |
| SSDEEP: | 3:N8R2WZf+IANIsRuAGUr9zAbAdA:2AQf+IS7+N |
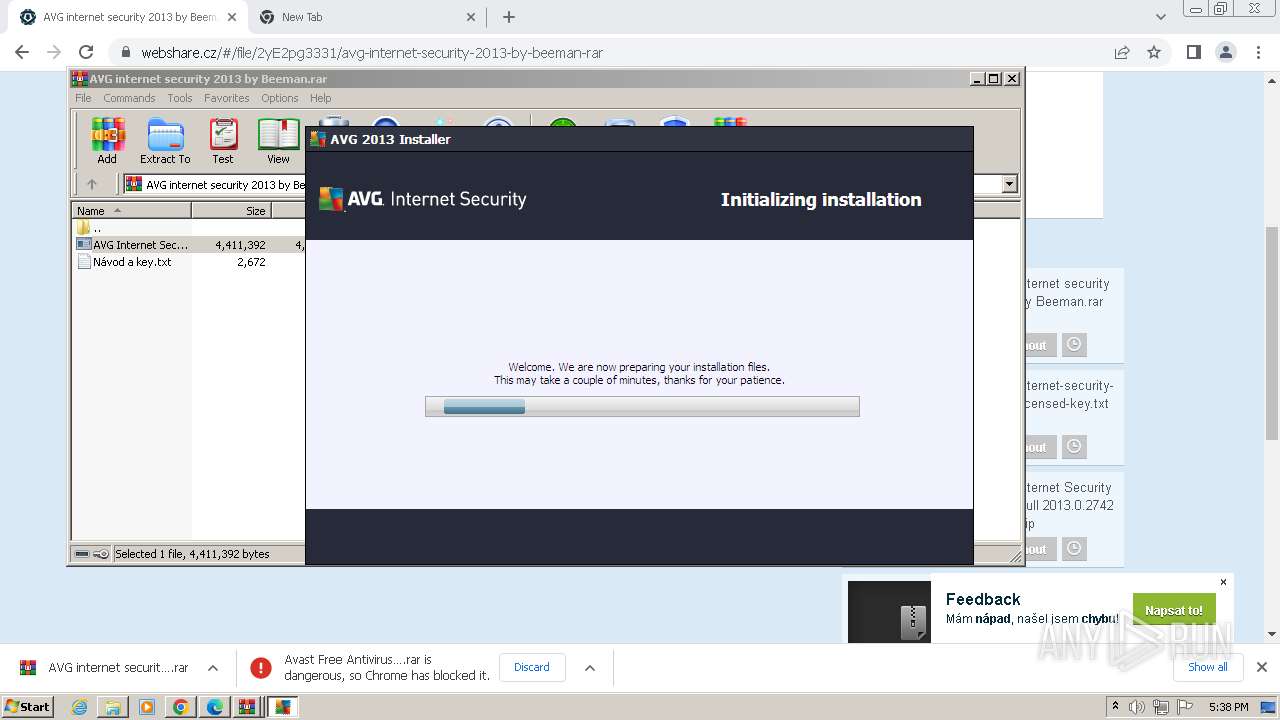
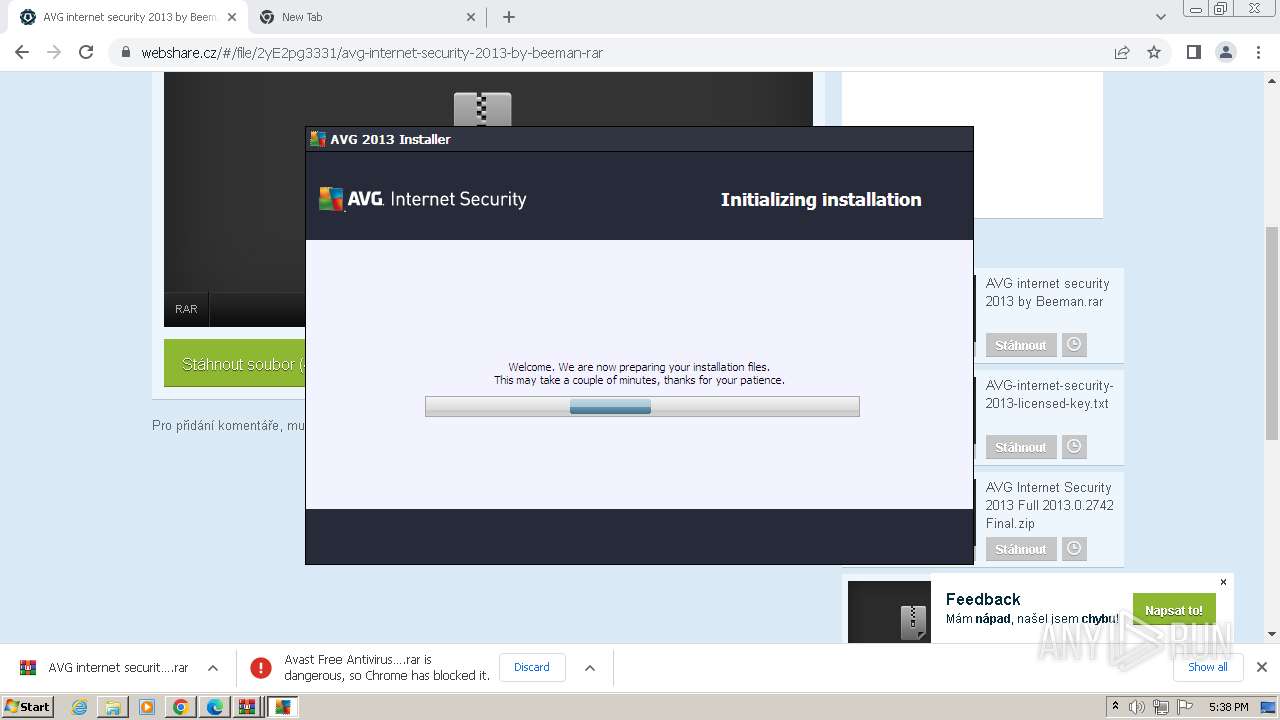
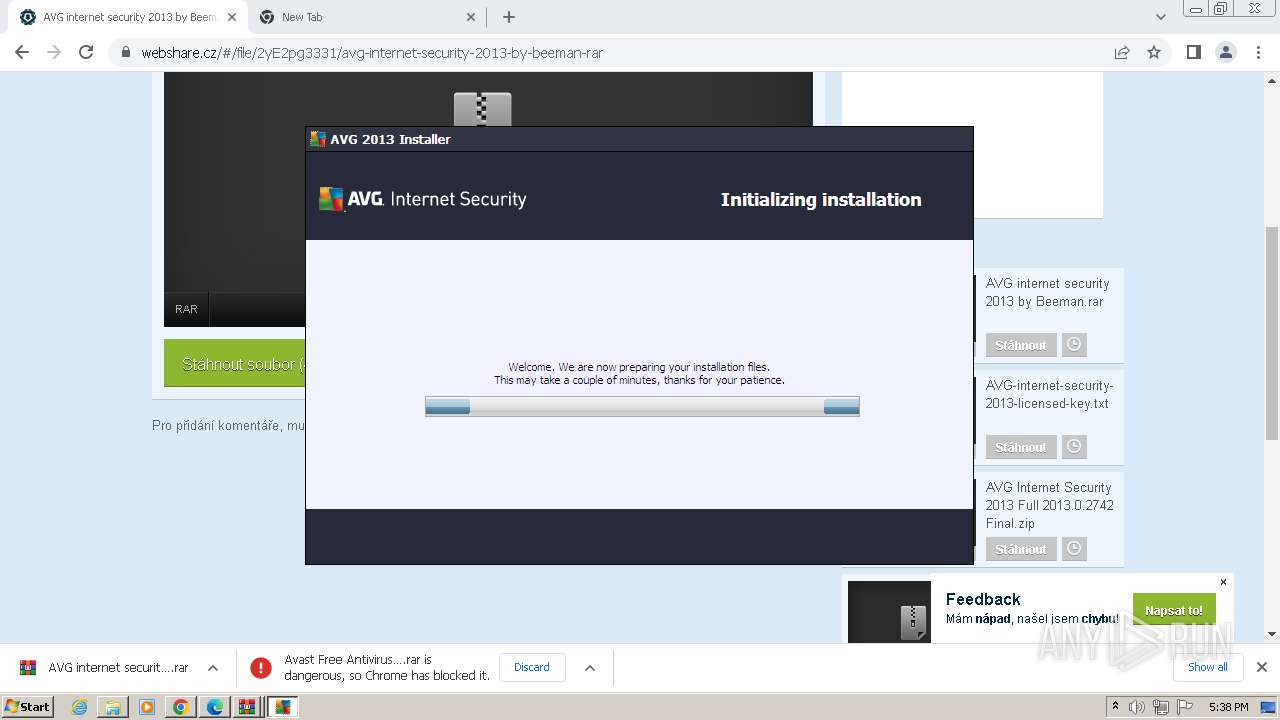
MALICIOUS
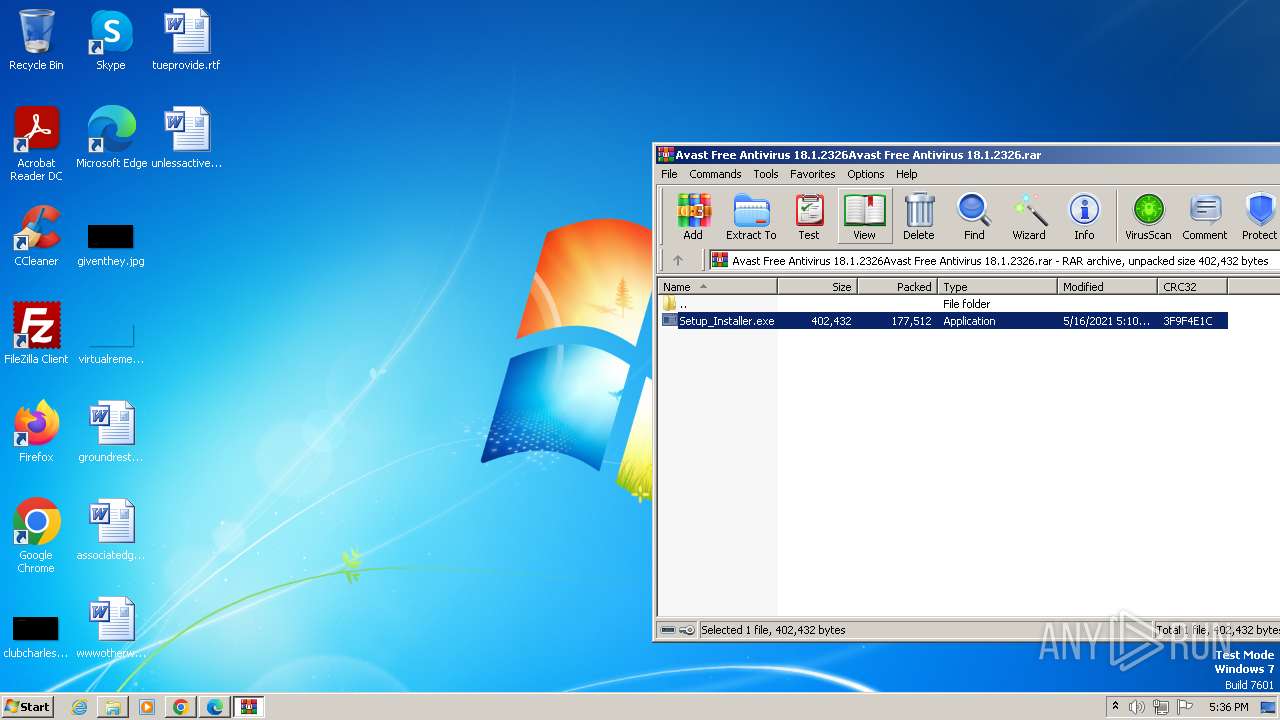
Creates a writable file in the system directory
- Setup_Installer.exe (PID: 2920)
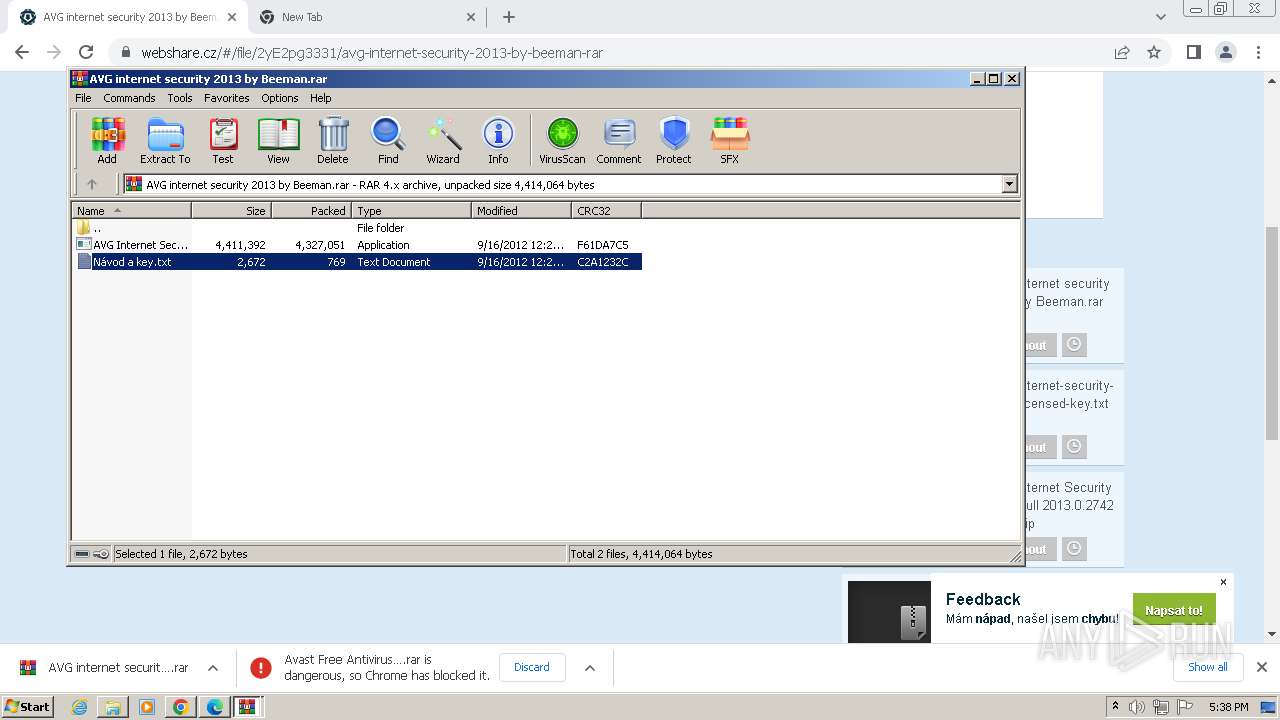
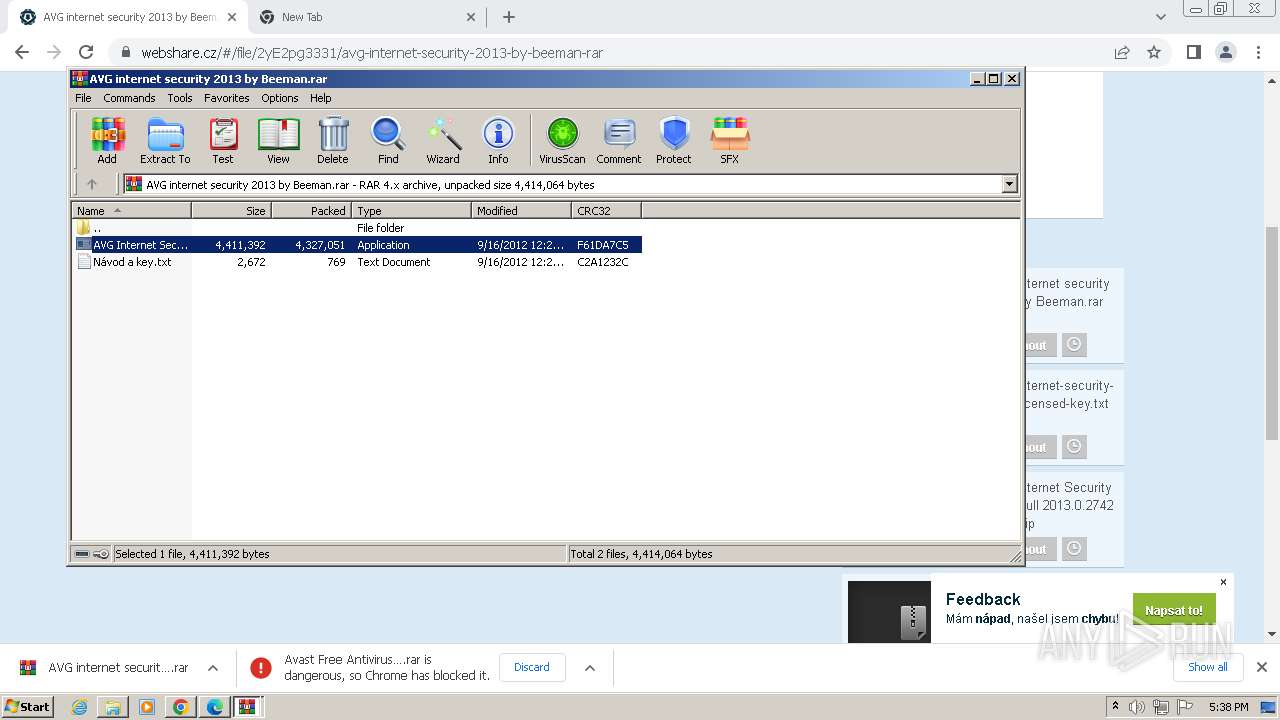
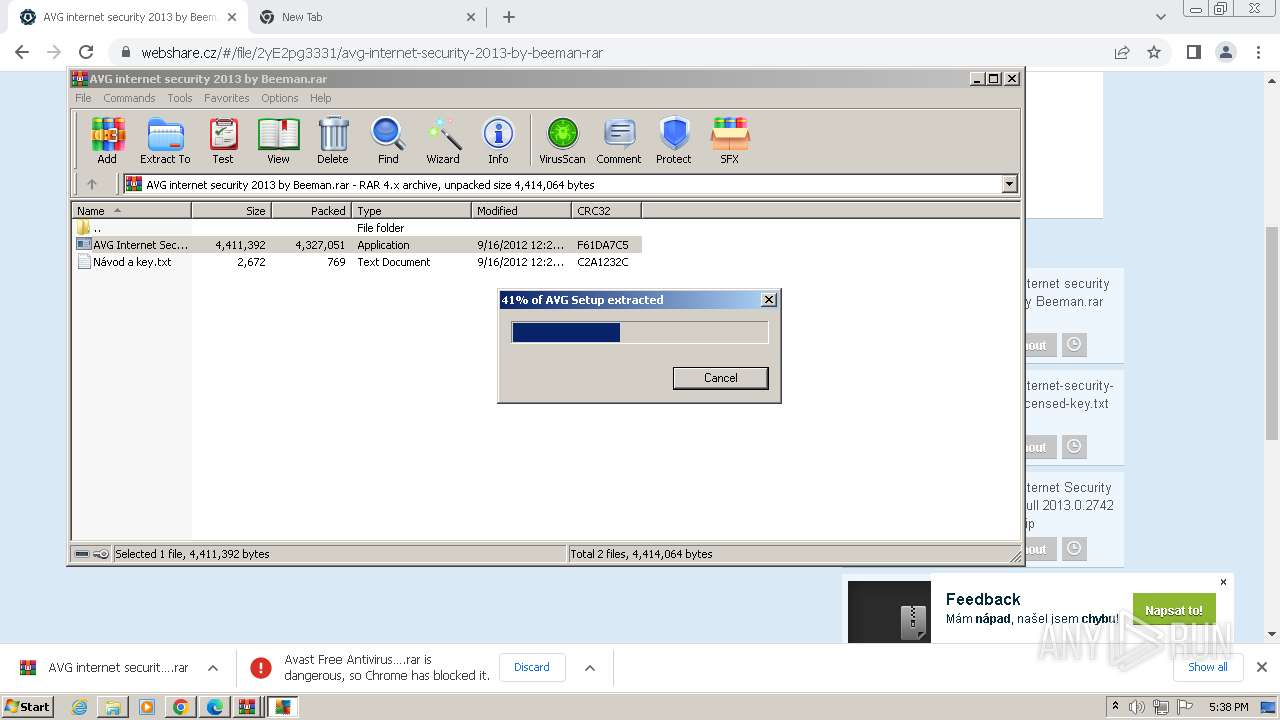
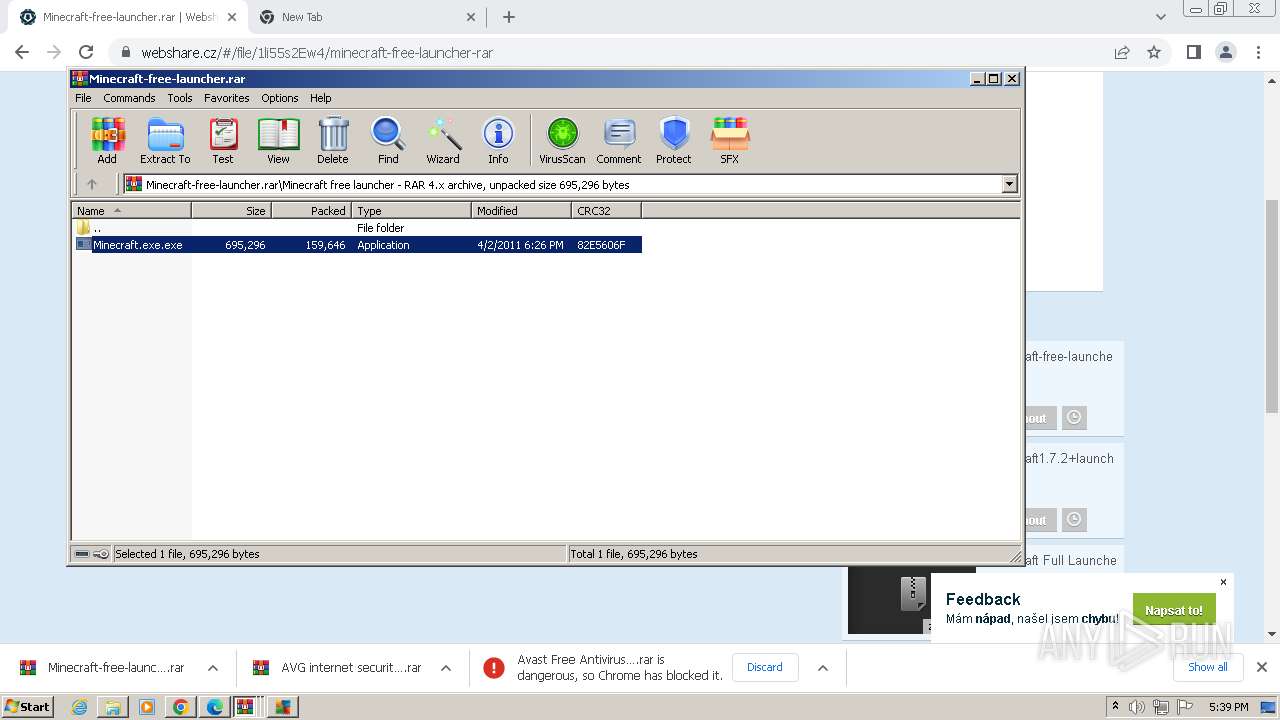
Drops the executable file immediately after the start
- Setup_Installer.exe (PID: 2920)
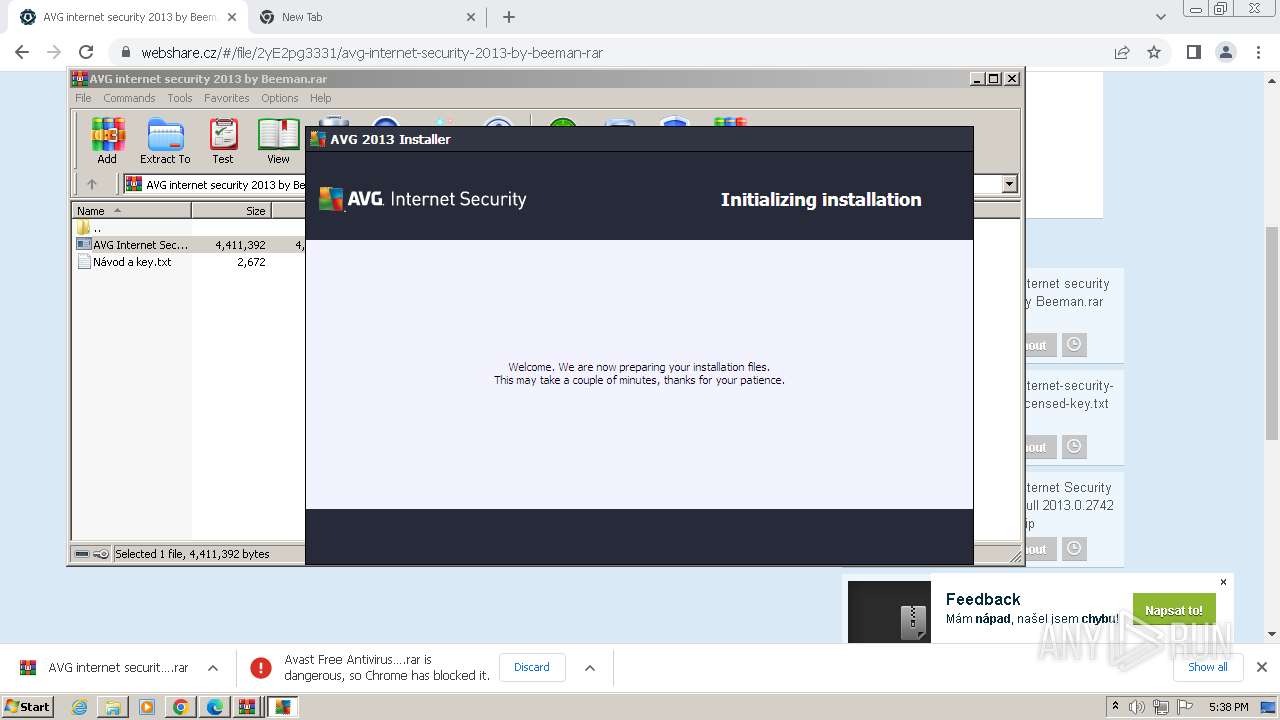
- AVG Internet Security 2013.exe (PID: 3172)
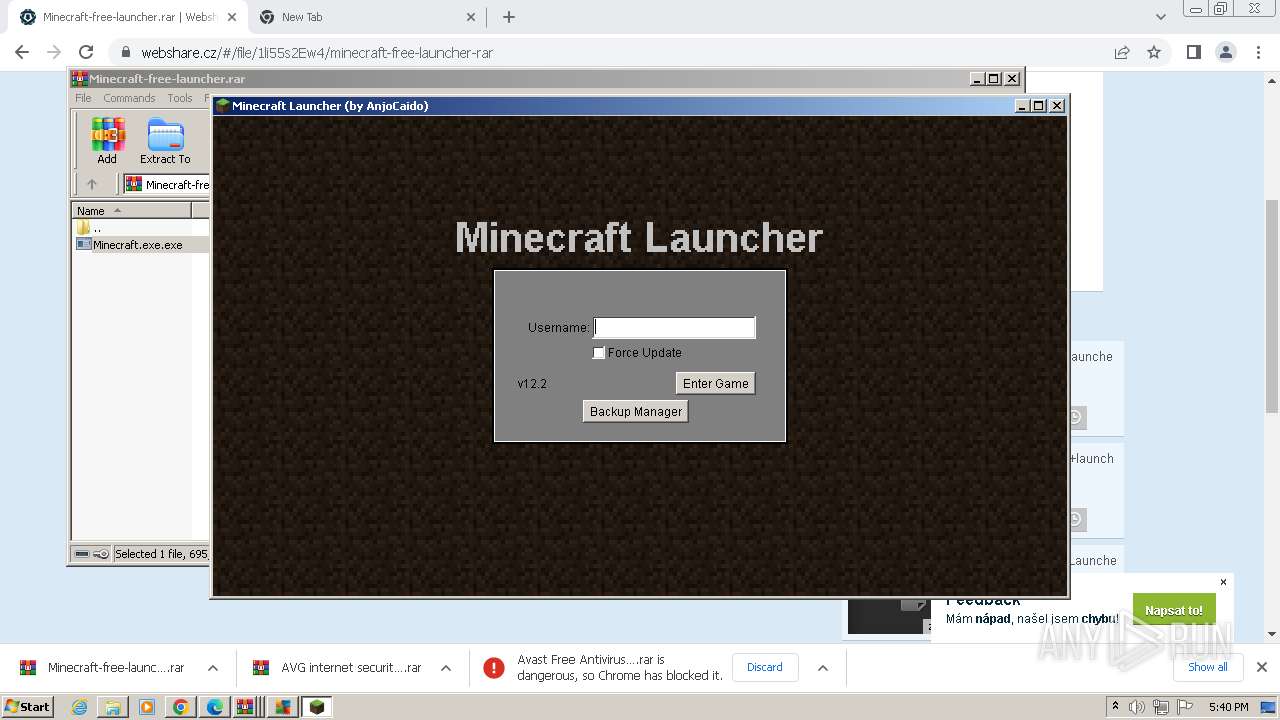
- Minecraft.exe.exe (PID: 3748)
REVENGERAT has been detected (YARA)
- svchost.exe (PID: 368)
Steals credentials from Web Browsers
- avgmfapx.exe (PID: 3792)
Actions looks like stealing of personal data
- avgmfapx.exe (PID: 3792)
SUSPICIOUS
The process creates files with name similar to system file names
- Setup_Installer.exe (PID: 2920)
Executable content was dropped or overwritten
- Setup_Installer.exe (PID: 2920)
- AVG Internet Security 2013.exe (PID: 3172)
- Minecraft.exe.exe (PID: 3748)
The process executes via Task Scheduler
- svchost.exe (PID: 368)
Connects to unusual port
- svchost.exe (PID: 368)
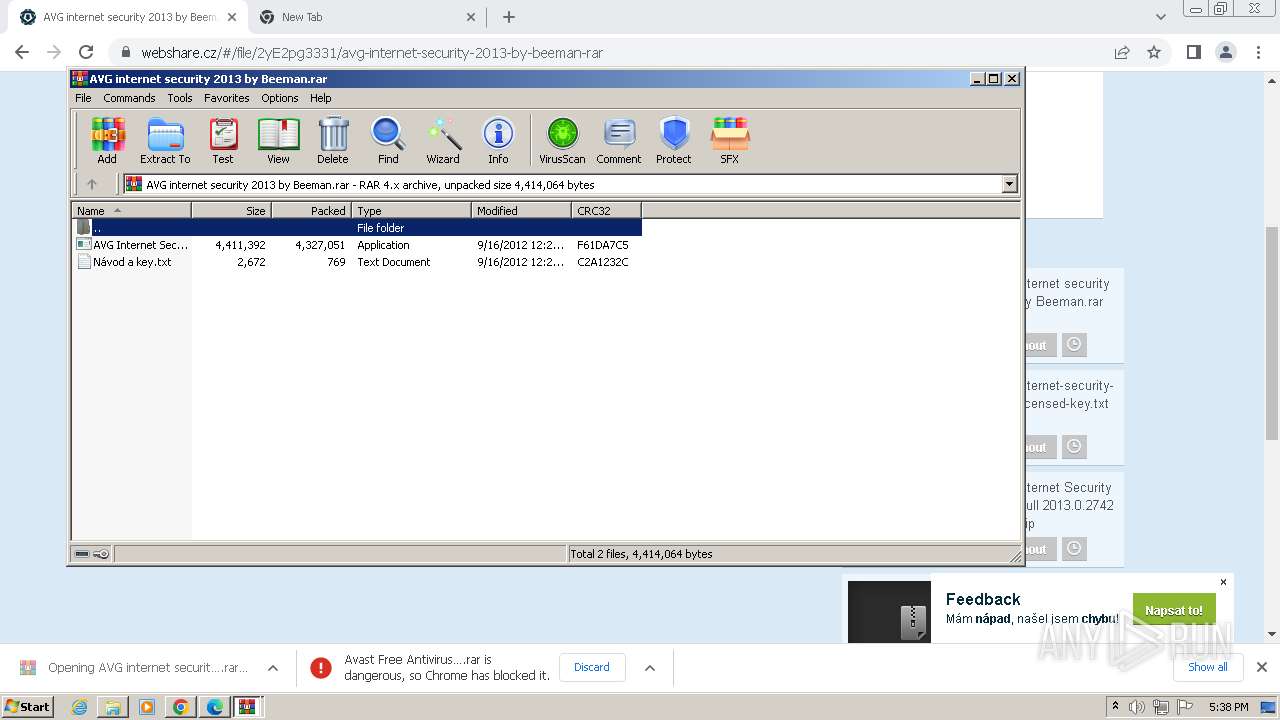
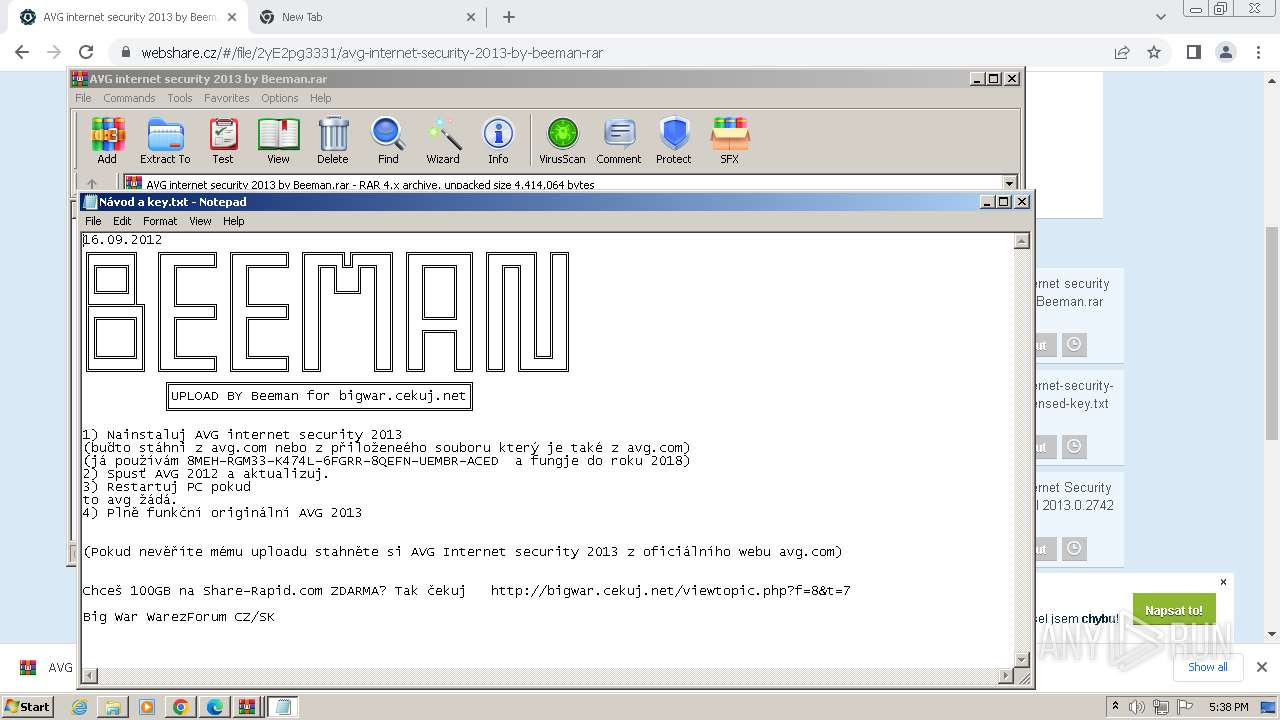
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 3028)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3028)
- WinRAR.exe (PID: 736)
Reads the date of Windows installation
- avgmfapx.exe (PID: 3792)
Reads the Internet Settings
- avgmfapx.exe (PID: 3792)
Checks for Java to be installed
- Minecraft.exe.exe (PID: 3748)
- javaw.exe (PID: 988)
INFO
Application launched itself
- chrome.exe (PID: 3960)
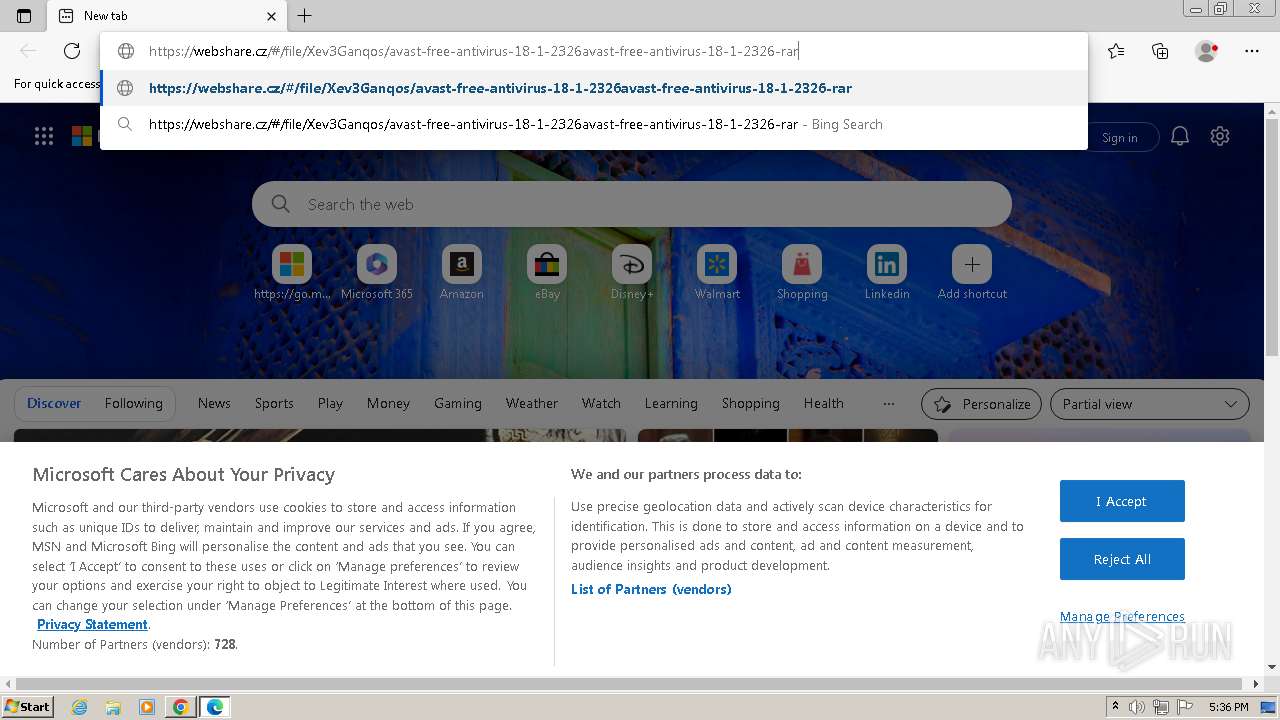
- msedge.exe (PID: 2460)
Reads the computer name
- wmpnscfg.exe (PID: 2272)
- Setup_Installer.exe (PID: 2920)
- svchost.exe (PID: 368)
- avgmfapx.exe (PID: 3792)
- javaw.exe (PID: 988)
- Minecraft.exe.exe (PID: 3748)
Checks supported languages
- wmpnscfg.exe (PID: 2272)
- Setup_Installer.exe (PID: 2920)
- svchost.exe (PID: 368)
- AVG Internet Security 2013.exe (PID: 3172)
- avgmfapx.exe (PID: 3792)
- Minecraft.exe.exe (PID: 3748)
- javaw.exe (PID: 988)
- i4jdel0.exe (PID: 3160)
- java.exe (PID: 4048)
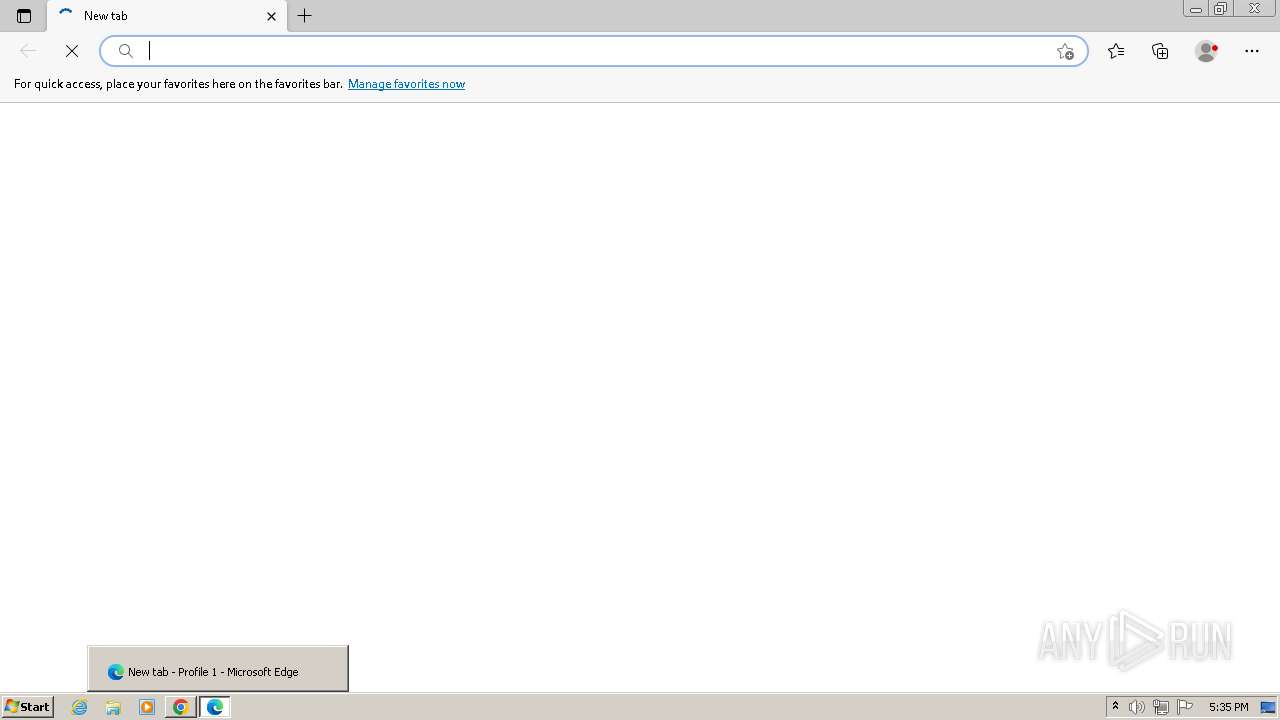
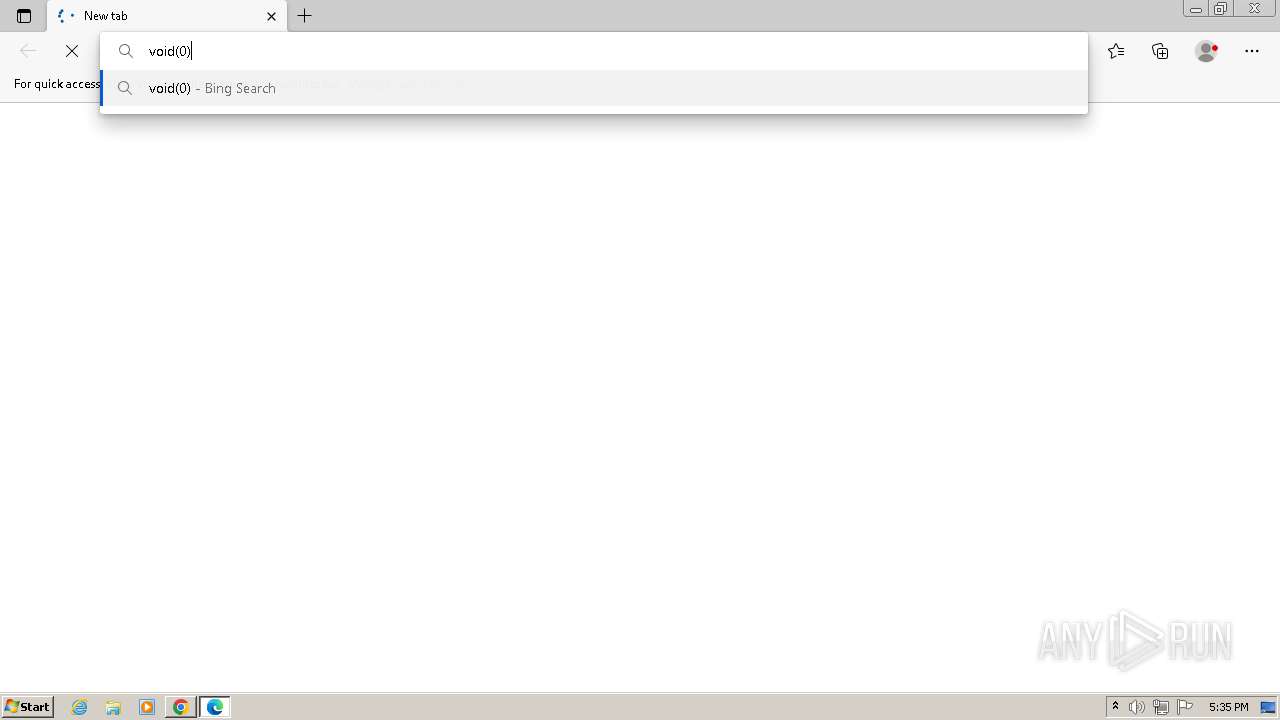
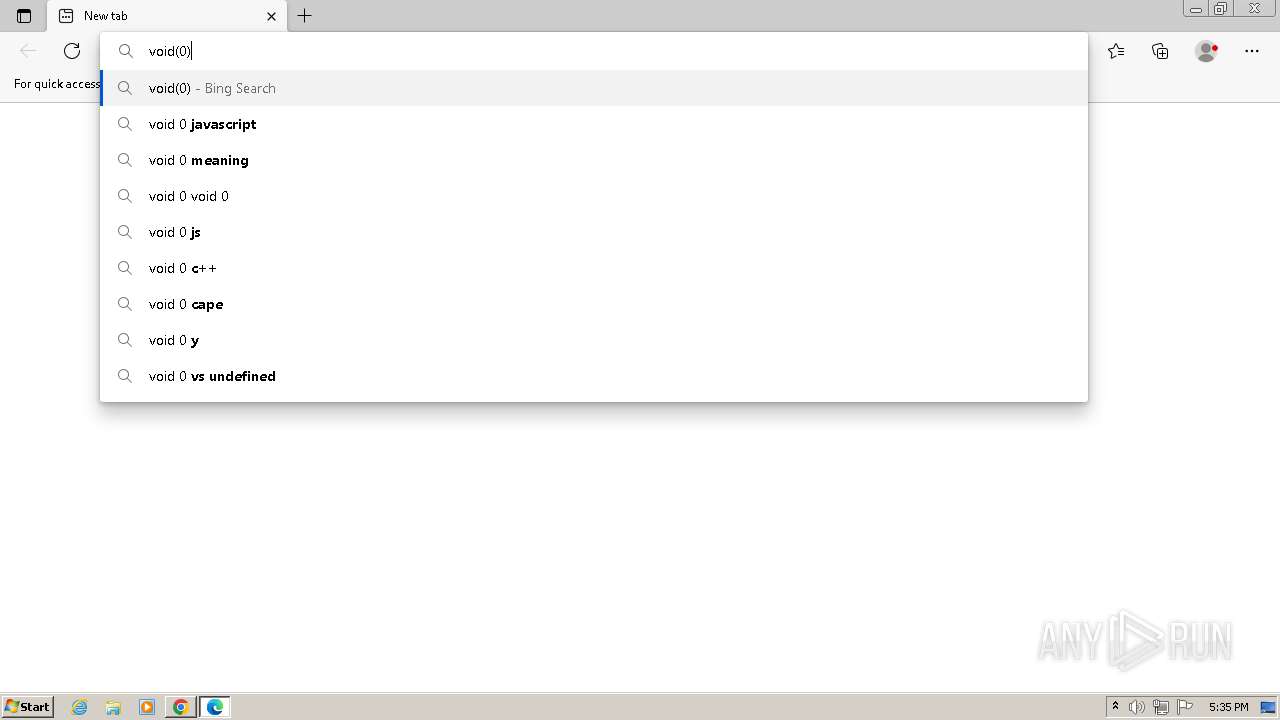
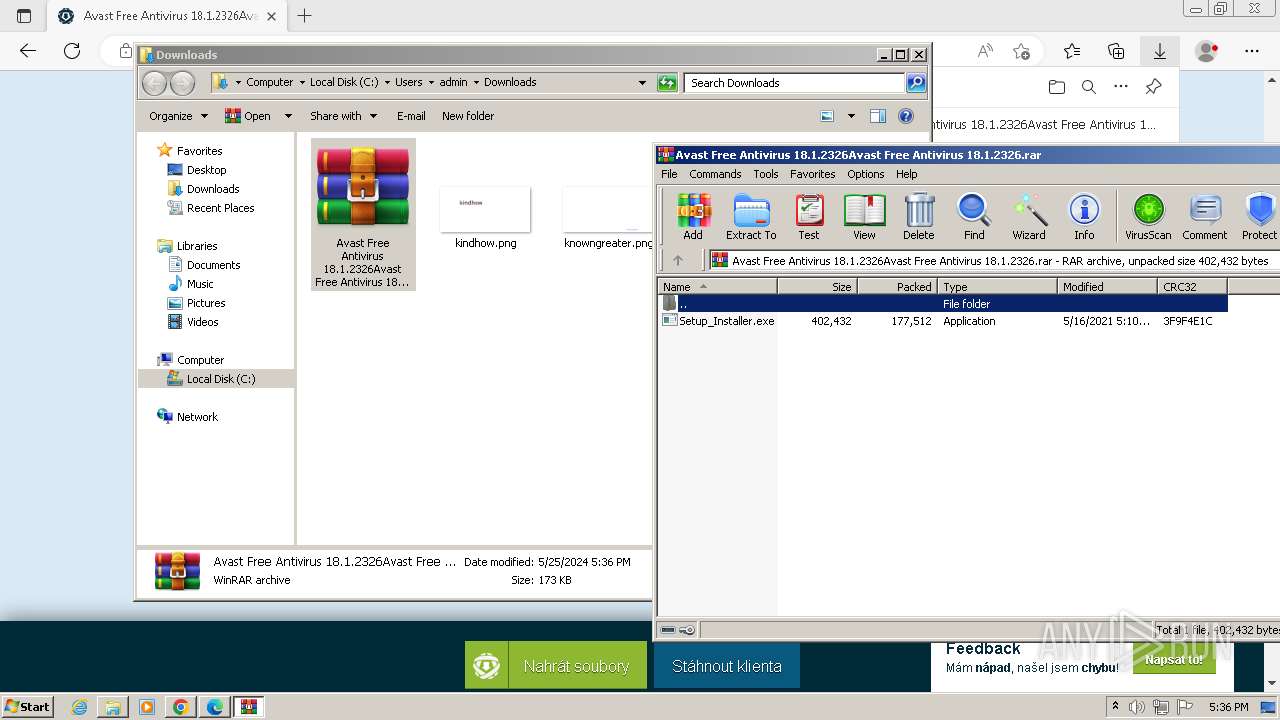
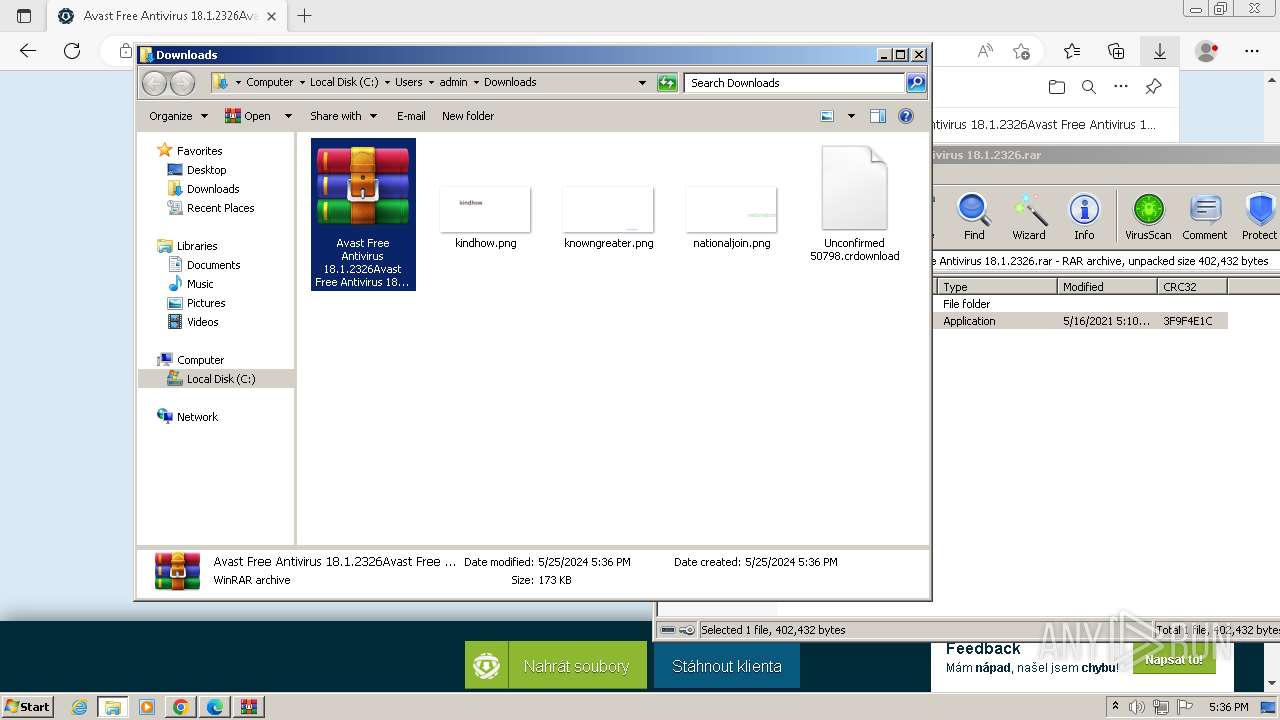
Manual execution by a user
- msedge.exe (PID: 2460)
- Setup_Installer.exe (PID: 1280)
- wmpnscfg.exe (PID: 2272)
- Setup_Installer.exe (PID: 2920)
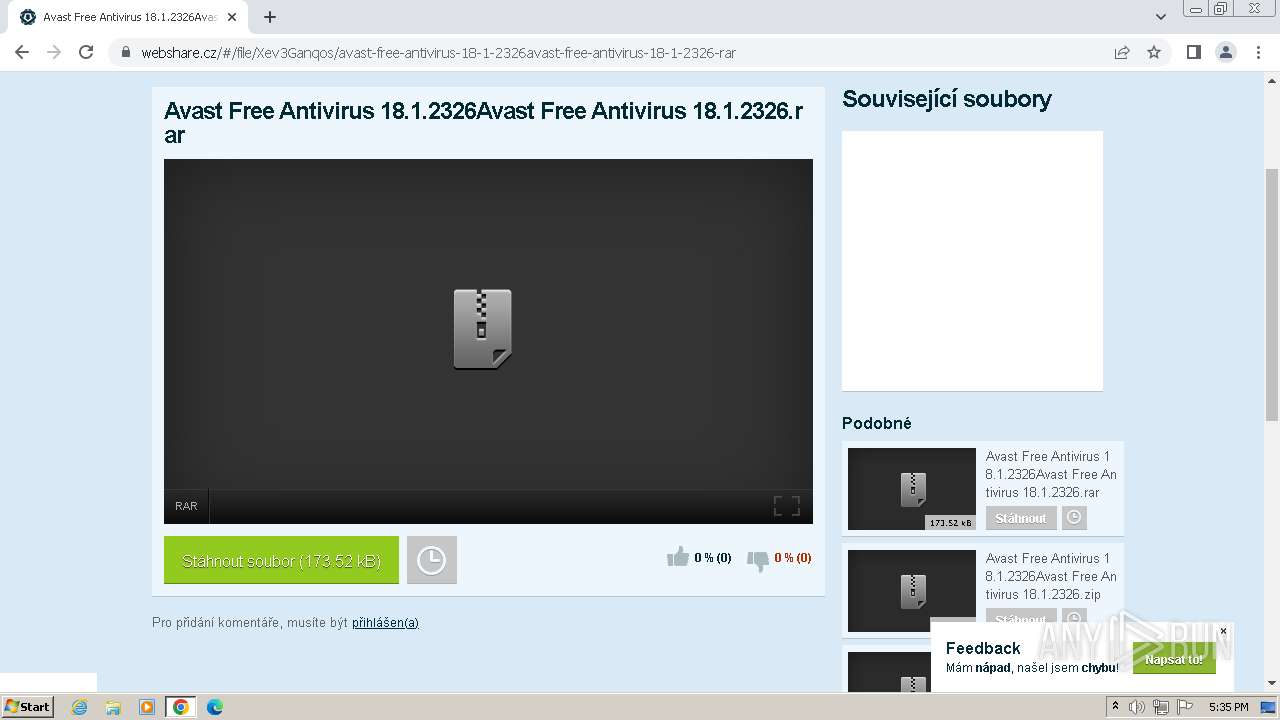
- WinRAR.exe (PID: 2104)
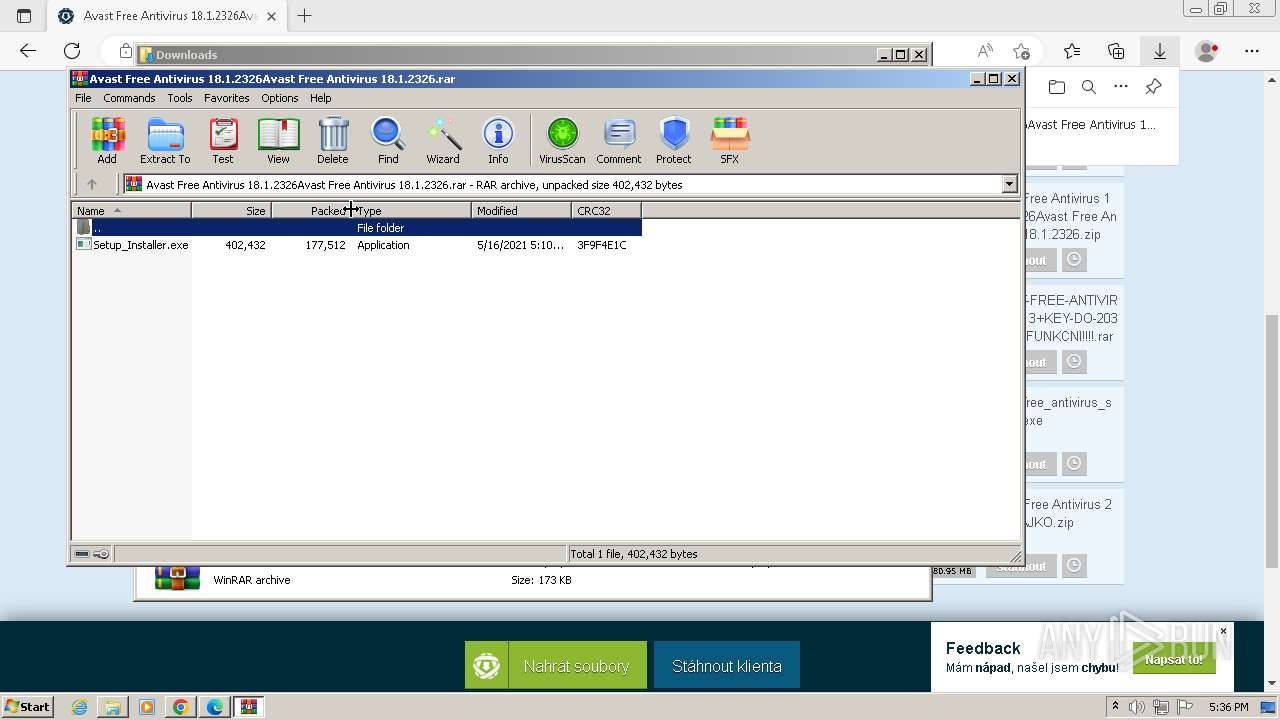
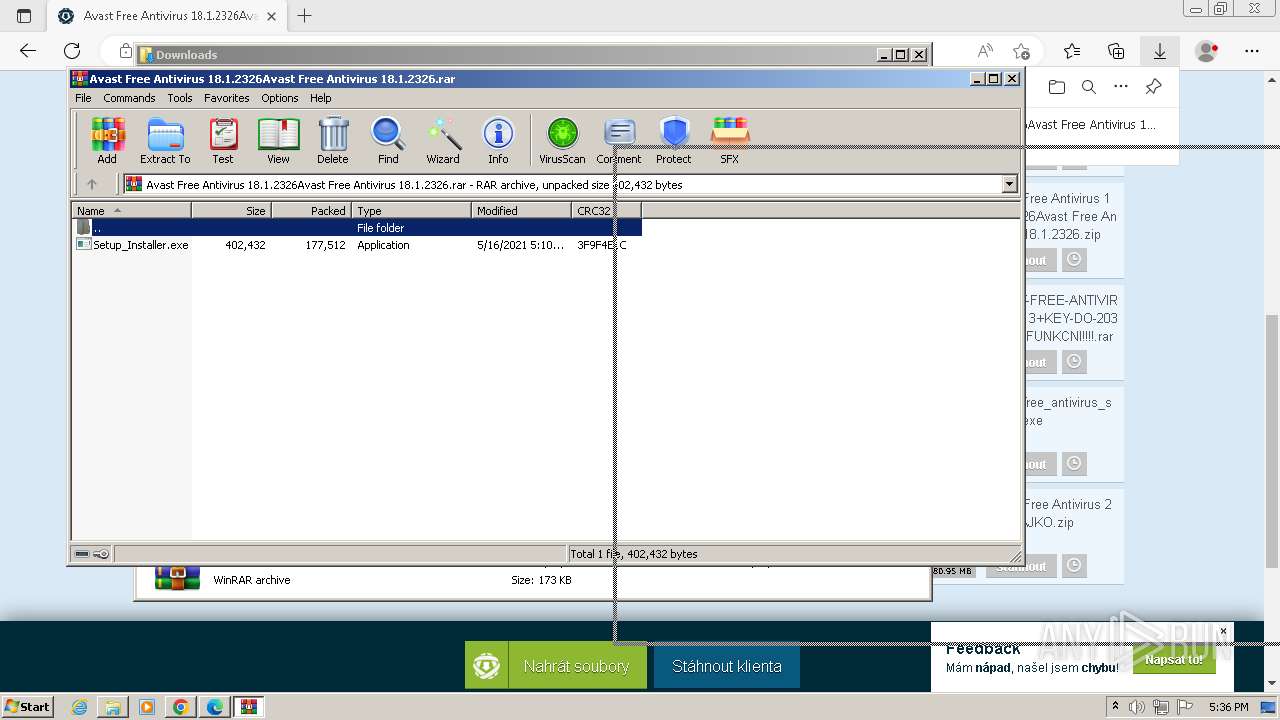
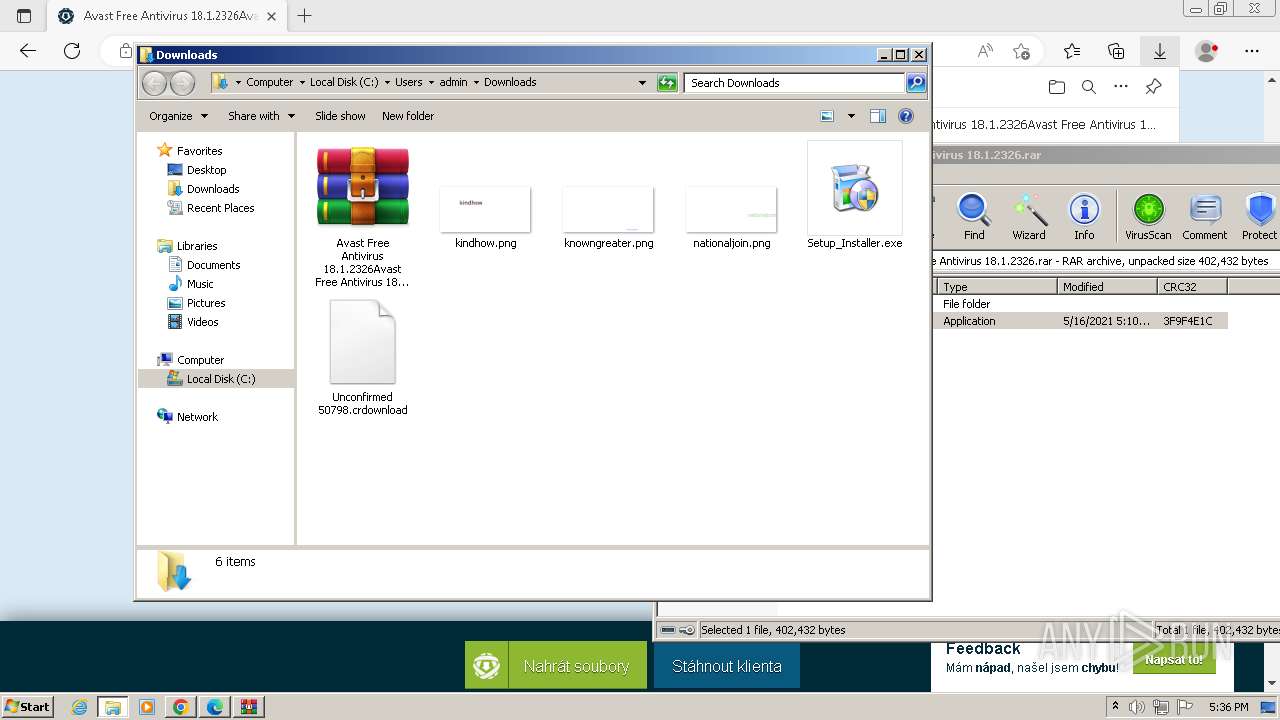
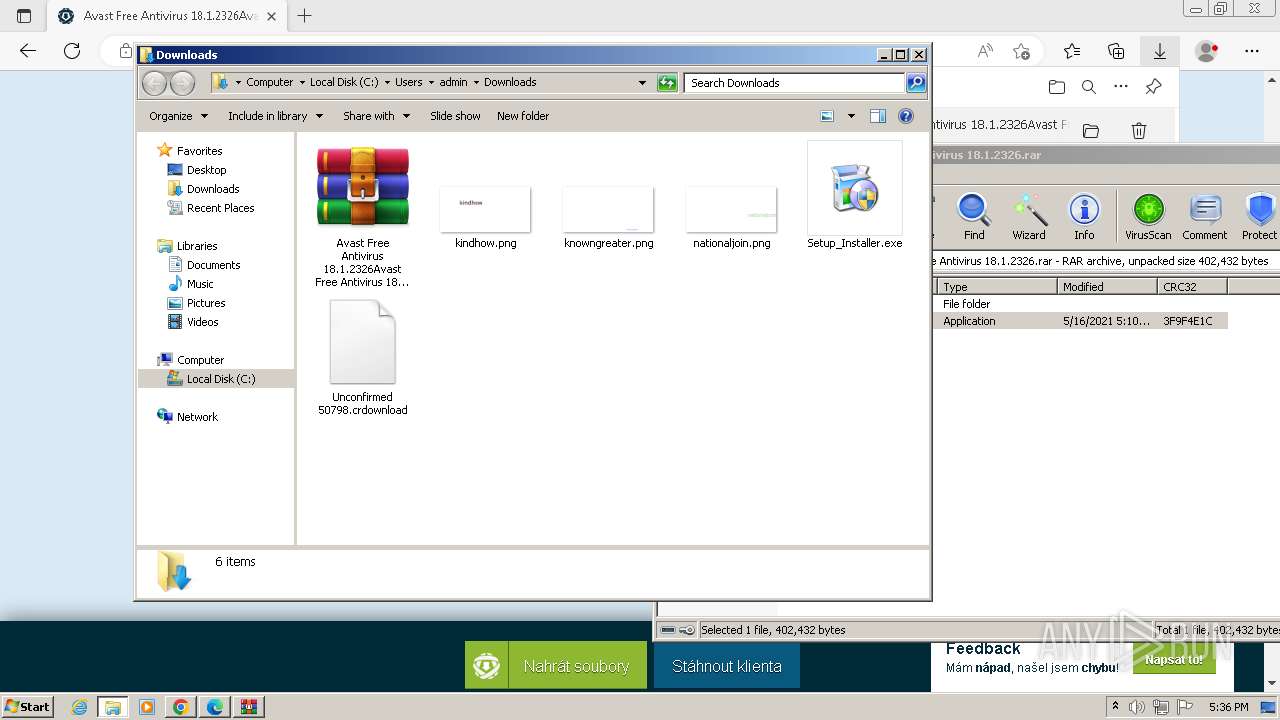
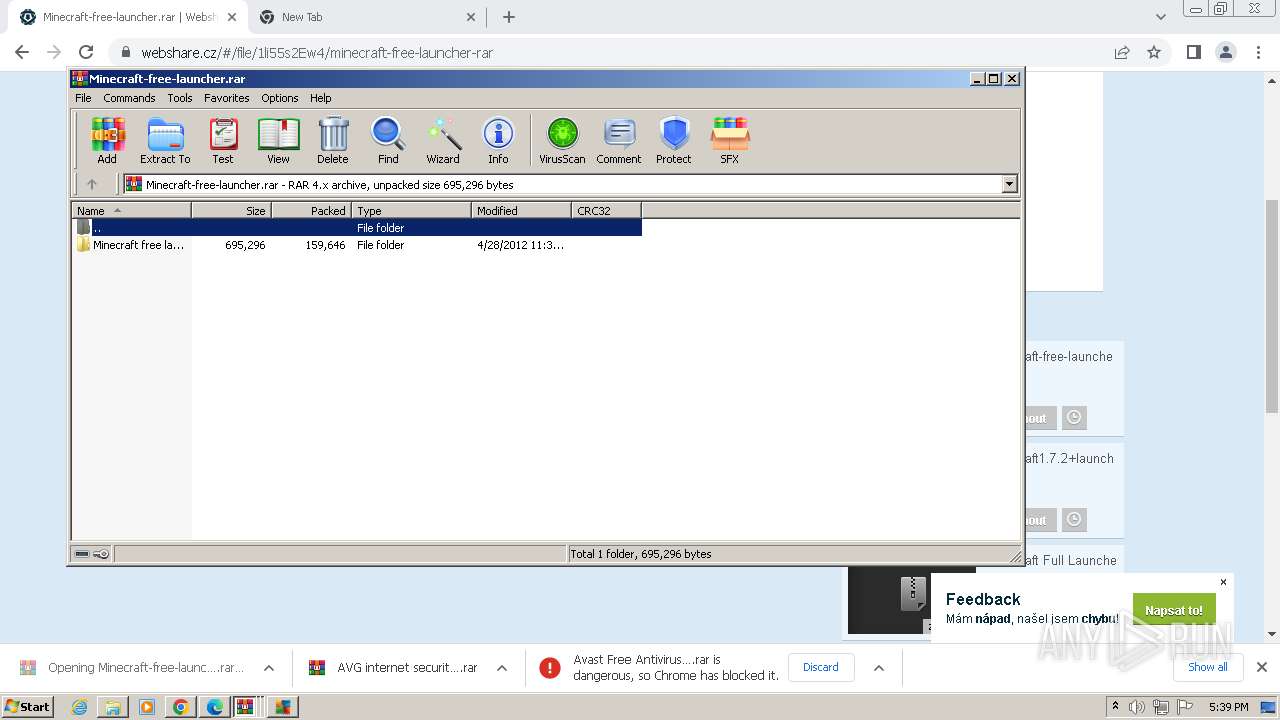
The process uses the downloaded file
- msedge.exe (PID: 3608)
- WinRAR.exe (PID: 2104)
- chrome.exe (PID: 2028)
- WinRAR.exe (PID: 3028)
- chrome.exe (PID: 3180)
- WinRAR.exe (PID: 736)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2104)
- chrome.exe (PID: 3828)
- WinRAR.exe (PID: 3028)
- WinRAR.exe (PID: 736)
Drops the executable file immediately after the start
- chrome.exe (PID: 3960)
- msedge.exe (PID: 956)
- msedge.exe (PID: 2460)
- WinRAR.exe (PID: 2104)
- chrome.exe (PID: 3828)
- WinRAR.exe (PID: 3028)
- WinRAR.exe (PID: 736)
Reads Environment values
- svchost.exe (PID: 368)
Reads the machine GUID from the registry
- Setup_Installer.exe (PID: 2920)
- svchost.exe (PID: 368)
- Minecraft.exe.exe (PID: 3748)
- javaw.exe (PID: 988)
Create files in a temporary directory
- AVG Internet Security 2013.exe (PID: 3172)
- Minecraft.exe.exe (PID: 3748)
- java.exe (PID: 4048)
- javaw.exe (PID: 988)
Creates files in the program directory
- avgmfapx.exe (PID: 3792)
- java.exe (PID: 4048)
Creates files or folders in the user directory
- avgmfapx.exe (PID: 3792)
Process checks computer location settings
- avgmfapx.exe (PID: 3792)
Checks proxy server information
- avgmfapx.exe (PID: 3792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RevengeRat
(PID) Process(368) svchost.exe
C2 (1)systemmicrosoft.linkpc.net
Ports (1)5005
BotnetGuest
Options
MutexRV_MUTEX
Splitter*-]NK[-*
KeyRevenge-RAT
Total processes
115
Monitored processes
64
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | C:\Windows\System32\svchost.exe | C:\Windows\System32\svchost.exe | taskeng.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
RevengeRat(PID) Process(368) svchost.exe C2 (1)systemmicrosoft.linkpc.net Ports (1)5005 BotnetGuest Options MutexRV_MUTEX Splitter*-]NK[-* KeyRevenge-RAT | |||||||||||||||
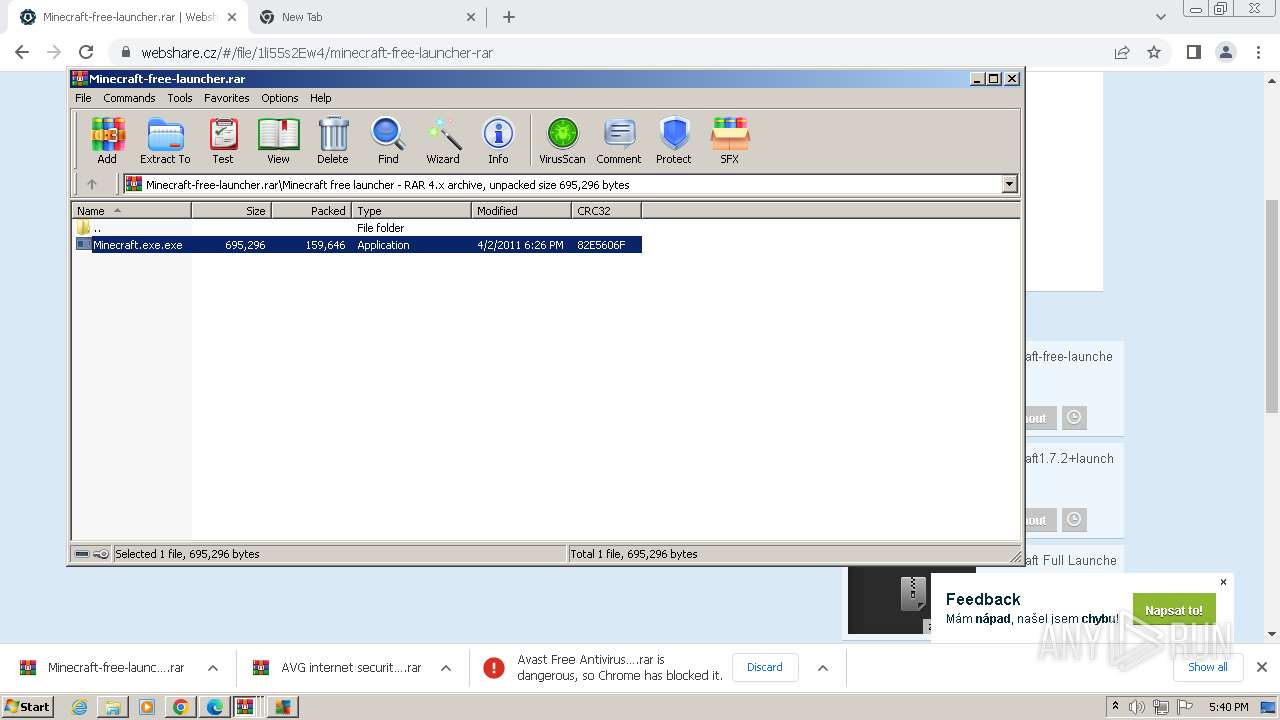
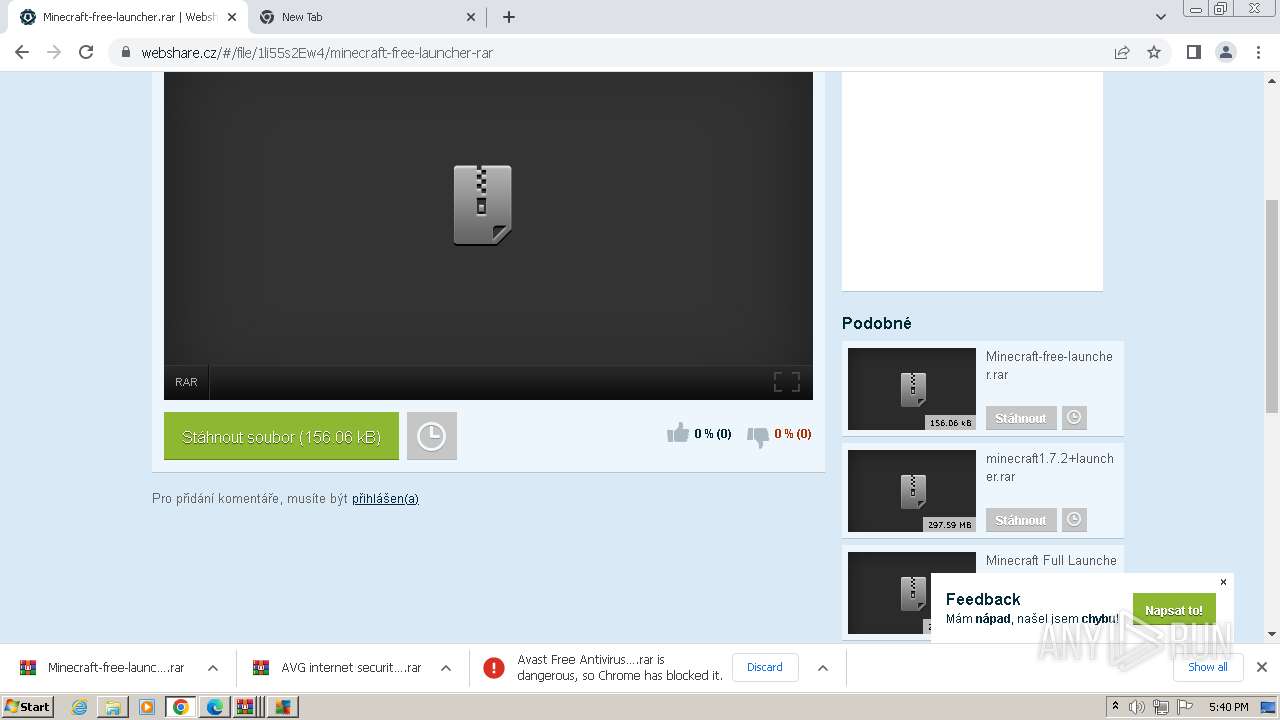
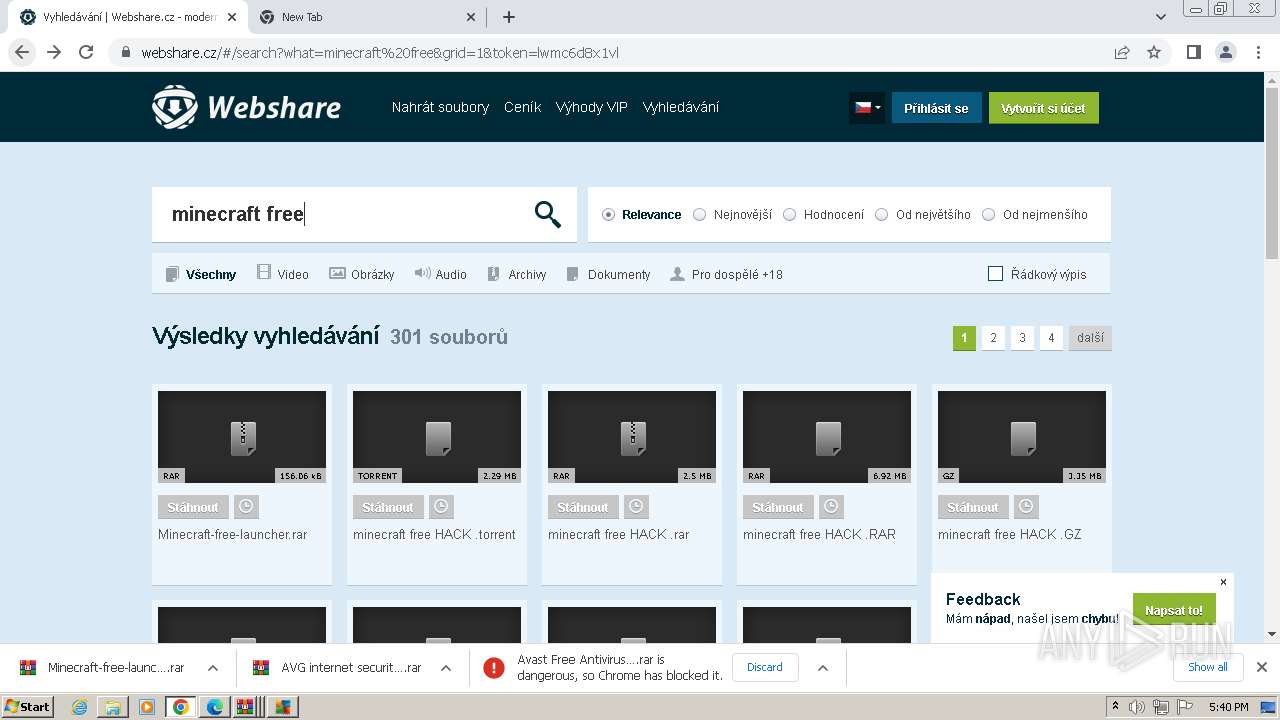
| 736 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Minecraft-free-launcher.rar" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1144 --field-trial-handle=1108,i,3060898099398275338,4935241113391441075,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1708 --field-trial-handle=1108,i,3060898099398275338,4935241113391441075,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1400 --field-trial-handle=1300,i,4944479896953255007,8055322137917271118,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 988 | javaw -Xms512m -Xmx1024m -Dsun.java2d.noddraw=true -Dsun.java2d.d3d=false -Dsun.java2d.opengl=false -Dsun.java2d.pmoffscreen=false -classpath /C:/Users/admin/AppData/Local/Temp/e4j72AE.tmp_dir/MinecraftSP.jar net.minecraft.LauncherFrame | C:\Program Files\Common Files\Oracle\Java\javapath_target_52116515\javaw.exe | — | Minecraft.exe.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1504 --field-trial-handle=1108,i,3060898099398275338,4935241113391441075,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1264 --field-trial-handle=1108,i,3060898099398275338,4935241113391441075,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1280 | "C:\Users\admin\Downloads\Setup_Installer.exe" | C:\Users\admin\Downloads\Setup_Installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsApplication62 Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --instant-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2228 --field-trial-handle=1300,i,4944479896953255007,8055322137917271118,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
36 064
Read events
35 836
Write events
207
Delete events
21
Modification events
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
32
Suspicious files
562
Text files
175
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10426a.TMP | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\65482728-f01a-4ebd-9f34-1e561e58e309.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF104ce9.TMP | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF104299.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF105eac.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
220
DNS requests
139
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1120 | chrome.exe | 142.250.145.84:443 | accounts.google.com | GOOGLE | US | unknown |
3960 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
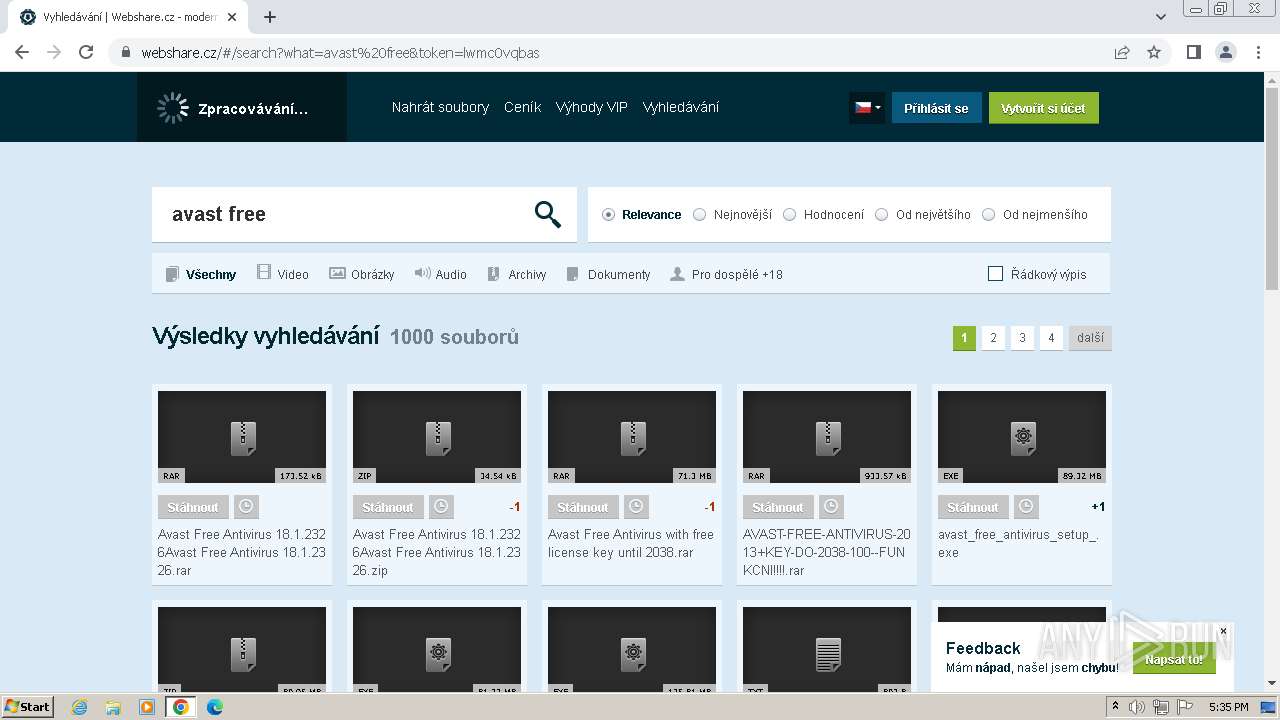
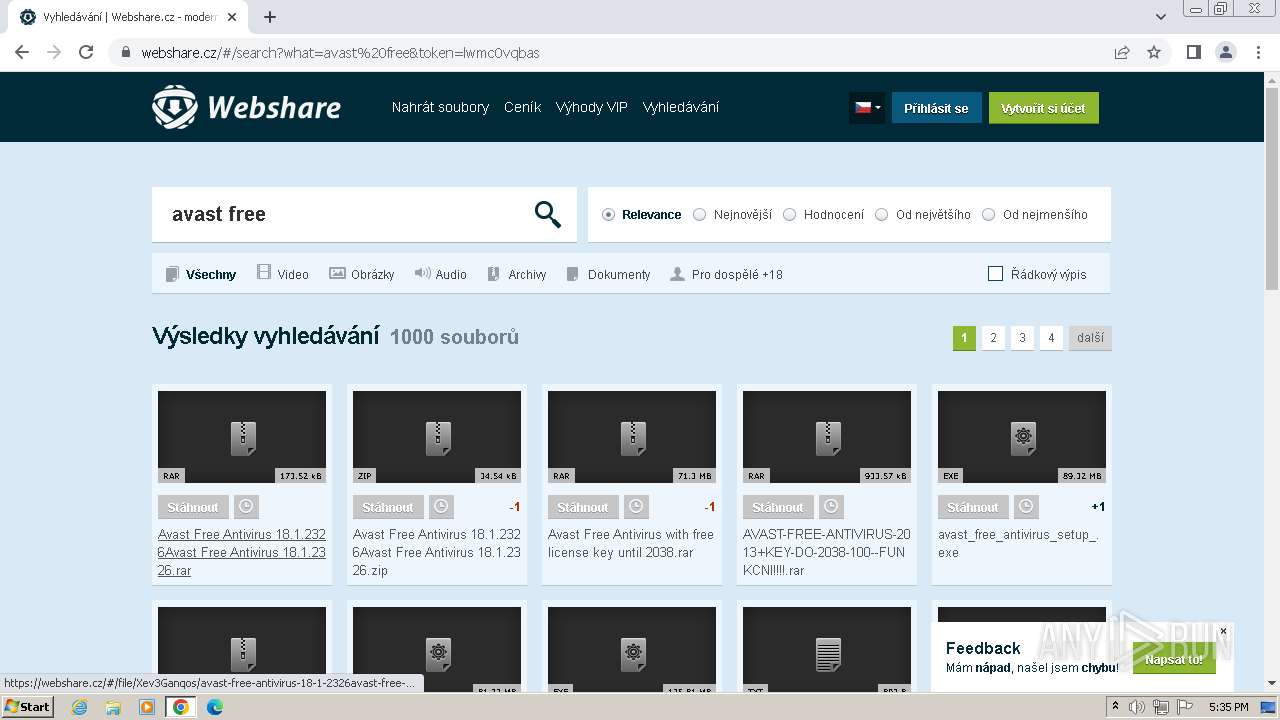
1120 | chrome.exe | 185.201.232.19:443 | webshare.cz | Tlap s.r.o. | CZ | unknown |
1120 | chrome.exe | 77.75.77.163:443 | c.imedia.cz | Seznam.cz, a.s. | CZ | unknown |
1120 | chrome.exe | 172.217.16.194:443 | www.googleadservices.com | GOOGLE | US | whitelisted |
1120 | chrome.exe | 77.75.79.172:443 | c.seznam.cz | Seznam.cz, a.s. | CZ | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
webshare.cz |
| whitelisted |
www.googleadservices.com |
| whitelisted |
c.imedia.cz |
| whitelisted |
c.seznam.cz |
| unknown |
googleads.g.doubleclick.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
www.google-analytics.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to DynDNS Domain (linkpc .net) |
1088 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to DynDNS Domain (linkpc .net) |