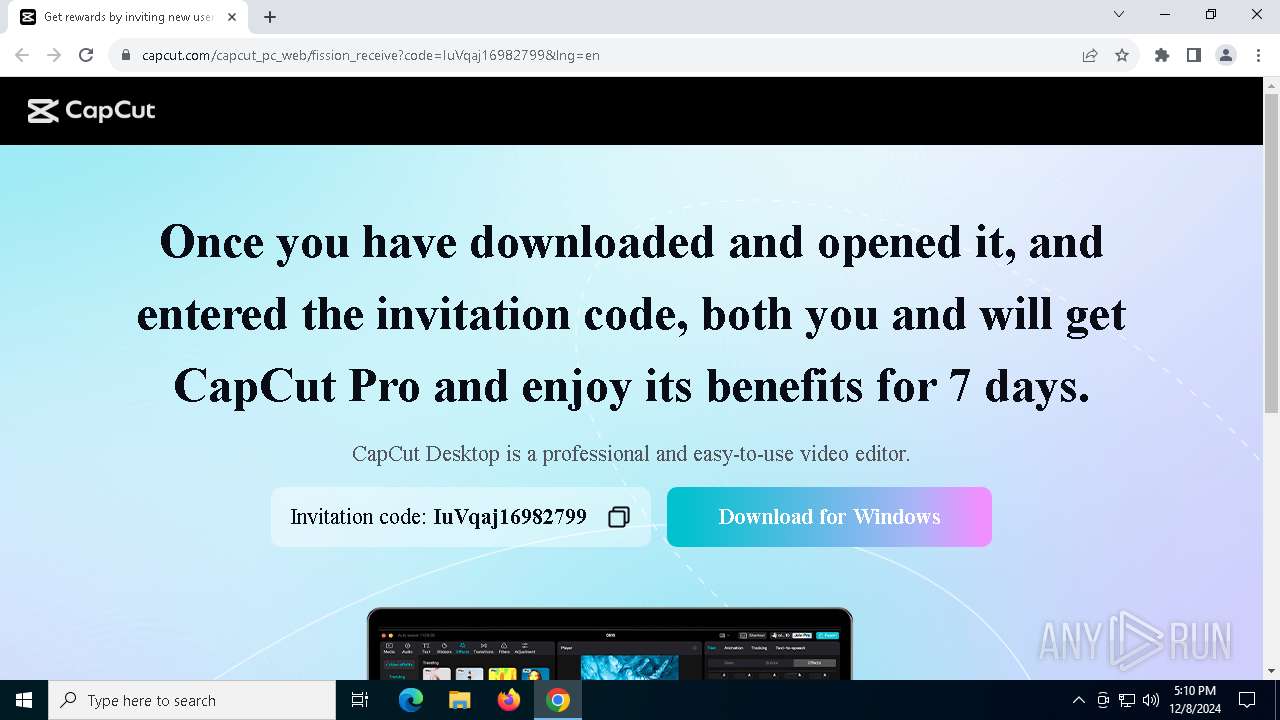
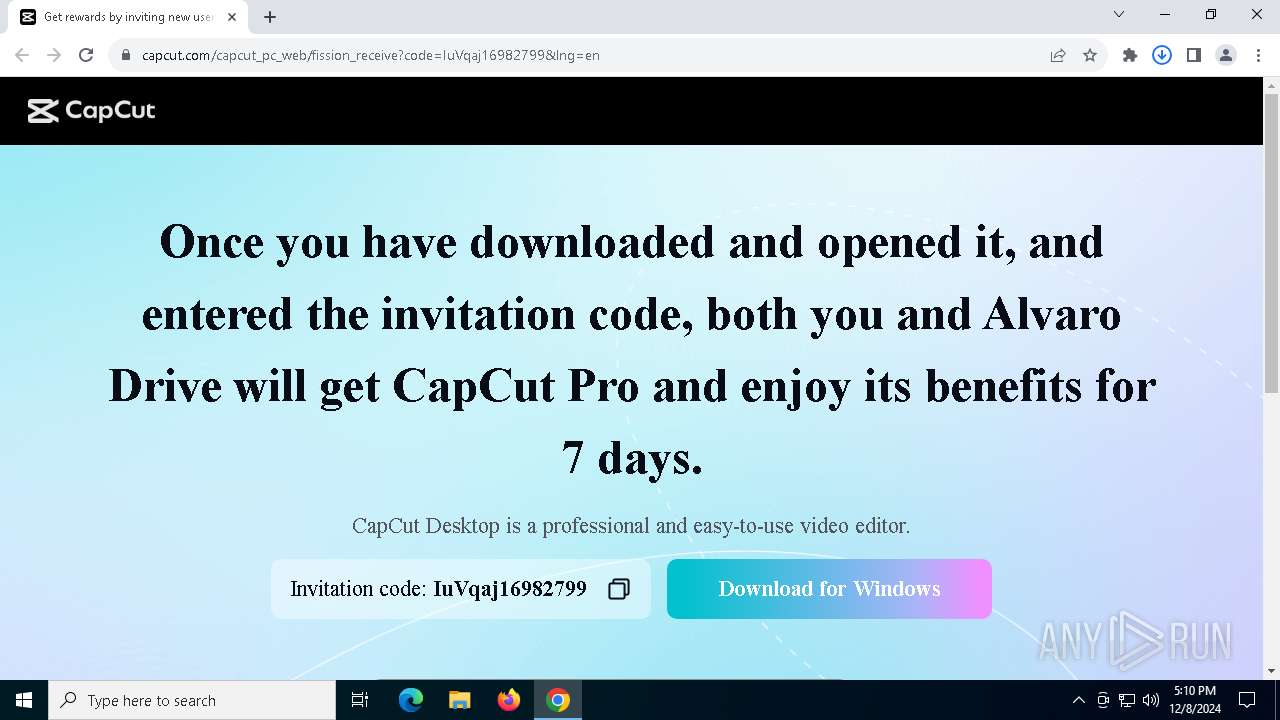
| URL: | https://www.capcut.com/capcut_pc_web/fission_receive?code=IuVqaj16982799&lng=en |
| Full analysis: | https://app.any.run/tasks/5f6e5406-2d2a-4191-8b9d-290e98193795 |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2024, 17:09:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 65A7CA915F30B97A4CBA70B1D4A9D2B6 |
| SHA1: | 07AC25F87B3336C24A840DE233A7E09E2255D081 |
| SHA256: | ABC1F3FE2AA788D2B5307411D106CA84FC0B212F2992C6C6A03E1ADF6EBC9388 |
| SSDEEP: | 3:N8DSLZUKIGeA/p4EycdfchkL:2OL9I300s |
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- capcut_capcutpc_invitefission_1.2.4_installer.exe (PID: 968)
The process creates files with name similar to system file names
- capcut_capcutpc_invitefission_1.2.4_installer.exe (PID: 968)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5836)
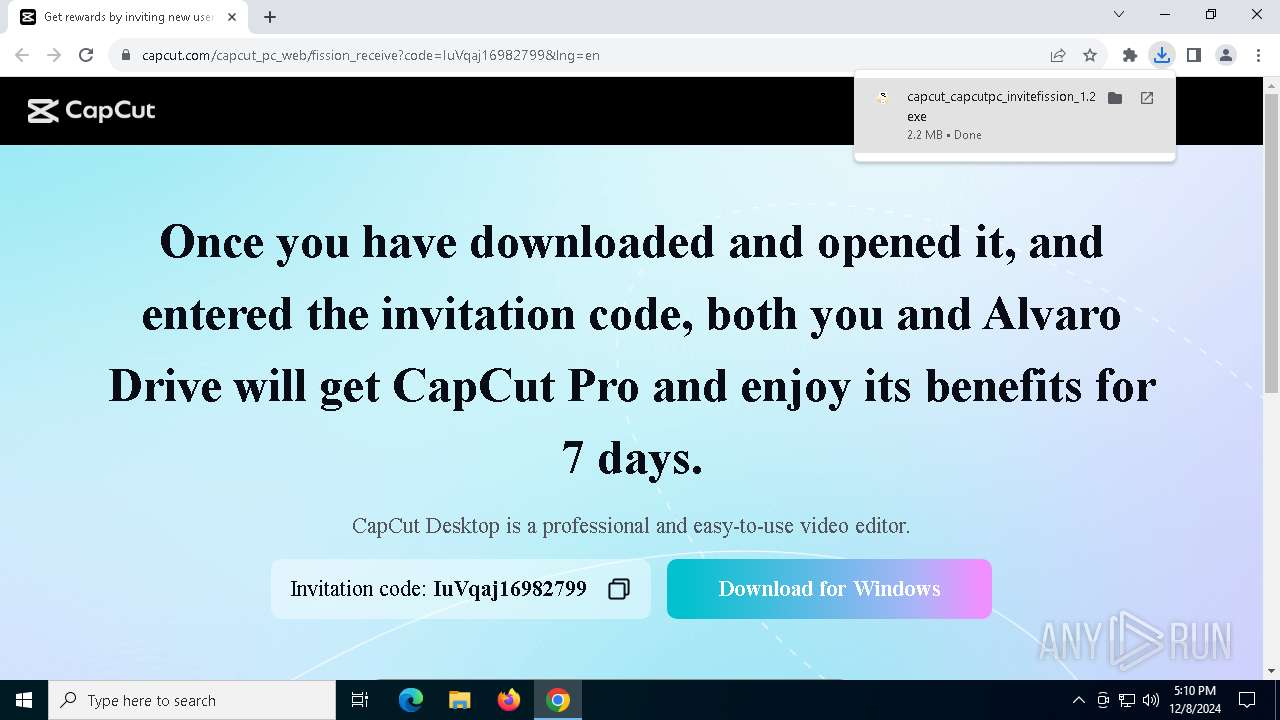
Executable content was dropped or overwritten
- capcut_capcutpc_invitefission_1.2.4_installer.exe (PID: 968)
- app_package_245f698fc8.exe (PID: 648)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7108)
Starts CMD.EXE for commands execution
- capcut_capcutpc_invitefission_1.2.4_installer.exe (PID: 968)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 4556)
Uses WMIC.EXE to obtain information about the network interface controller
- cmd.exe (PID: 6872)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 5604)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2192)
Process drops legitimate windows executable
- app_package_245f698fc8.exe (PID: 648)
Drops 7-zip archiver for unpacking
- app_package_245f698fc8.exe (PID: 648)
The process drops C-runtime libraries
- app_package_245f698fc8.exe (PID: 648)
INFO
Application launched itself
- chrome.exe (PID: 5564)
Reads the computer name
- capcut_capcutpc_invitefission_1.2.4_installer.exe (PID: 968)
- app_package_245f698fc8.exe (PID: 648)
Executable content was dropped or overwritten
- chrome.exe (PID: 5564)
- chrome.exe (PID: 1220)
Creates files or folders in the user directory
- capcut_capcutpc_invitefission_1.2.4_installer.exe (PID: 968)
- app_package_245f698fc8.exe (PID: 648)
Checks supported languages
- capcut_capcutpc_invitefission_1.2.4_installer.exe (PID: 968)
- app_package_245f698fc8.exe (PID: 648)
The process uses the downloaded file
- chrome.exe (PID: 6840)
- chrome.exe (PID: 5564)
- chrome.exe (PID: 6372)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6096)
- WMIC.exe (PID: 5720)
- WMIC.exe (PID: 6004)
- WMIC.exe (PID: 7000)
- WMIC.exe (PID: 2164)
Create files in a temporary directory
- capcut_capcutpc_invitefission_1.2.4_installer.exe (PID: 968)
- app_package_245f698fc8.exe (PID: 648)
Sends debugging messages
- capcut_capcutpc_invitefission_1.2.4_installer.exe (PID: 968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
47
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3588 --field-trial-handle=1876,i,12848580618723118229,16317848393340988398,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 648 | "C:\Users\admin\AppData\Local\app_shell_cache_359289\app_package_245f698fc8.exe" /s /create_desktop=1 /install_path="C:\Users\admin\AppData\Local\CapCut" | C:\Users\admin\AppData\Local\app_shell_cache_359289\app_package_245f698fc8.exe | capcut_capcutpc_invitefission_1.2.4_installer.exe | ||||||||||||
User: admin Company: Bytedance Pte. Ltd. Integrity Level: HIGH Description: CapCut Version: 3.3.0.1161 Modules
| |||||||||||||||
| 968 | "C:\Users\admin\Downloads\capcut_capcutpc_invitefission_1.2.4_installer.exe" | C:\Users\admin\Downloads\capcut_capcutpc_invitefission_1.2.4_installer.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2212 --field-trial-handle=1876,i,12848580618723118229,16317848393340988398,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2164 | "C:\Users\admin\Downloads\capcut_capcutpc_invitefission_1.2.4_installer.exe" | C:\Users\admin\Downloads\capcut_capcutpc_invitefission_1.2.4_installer.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2164 | wmic nicconfig get DefaultIPGateway,macaddress | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3564 --field-trial-handle=1876,i,12848580618723118229,16317848393340988398,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3952 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 913
Read events
13 879
Write events
27
Delete events
7
Modification events
| (PID) Process: | (5564) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5564) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5564) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5564) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5564) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6372) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000747BD70B9449DB01 | |||
| (PID) Process: | (968) capcut_capcutpc_invitefission_1.2.4_installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\DeviceInfo\MacAddr |
| Operation: | write | Name: | mac |
Value: 35323A35343A30303A42383A32363A3038 | |||
| (PID) Process: | (968) capcut_capcutpc_invitefission_1.2.4_installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ByteDance\CapCut\Common |
| Operation: | write | Name: | Info |
Value: 74630510000020F544A0A771E5BE827B36C5C6E7874EF443026E1E68ECE84B4F28A01D26FD53E6B9A8AADE7A7BD683151B77E528B54A3BBBEC0B4226729074D023462B8A955938F1FFB28C46130E8CB9A3DB2D0B06D4CD3D1127BC26D30B60A5466873C485B8A37D9738419709A49649C4659915397E6DF1EA5D85CE374A84DC6D066785EF92FF9BAC2728D82C120F777C0BAADD36CB9418D05E4FF3ECA9609AF5DE768FABEB26EAA9EACE7ED39169DD067FCC81B3EB82C8BB6A0510562723F63F4DBFA32F34F97B14E056DF5DD69E34C44035DE17FA6062F0F4F6563B4E7036E84B80C3F96A2D1FD6B24DC286A54D71F8F4602DD616 | |||
| (PID) Process: | (5564) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | ahfgeienlihckogmohjhadlkjgocpleb |
Value: 3B08F722C14555E595AF269F140EE426CE8DEBAD90D03EE9FF33B95CB34233F6 | |||
| (PID) Process: | (5564) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | bjbddleefiddlmdfdfbgodgacjjldihj |
Value: 5CFE6AD362B9AABBD07085580BC6C063CF1C79A0B22ECB6BCBA21EECA68BA07F | |||
Executable files
474
Suspicious files
1 234
Text files
1 041
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF136351.TMP | — | |
MD5:— | SHA256:— | |||
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF136351.TMP | — | |
MD5:— | SHA256:— | |||
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF136361.TMP | — | |
MD5:— | SHA256:— | |||
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF136361.TMP | — | |
MD5:— | SHA256:— | |||
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF136361.TMP | — | |
MD5:— | SHA256:— | |||
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
109
DNS requests
58
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3040 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3040 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6016 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6300 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5588 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwxtpuzdppbkpvqnjipwx43gshq_2024.12.7.1/jflhchccmppkfebkiaminageehmchikm_2024.12.07.01_all_aduya2fcdcdr7baewmt2slm7nyoq.crx3 | unknown | — | — | whitelisted |
6016 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3040 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3040 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2380 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1076 | svchost.exe | 23.32.186.57:443 | go.microsoft.com | AKAMAI-AS | BR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.capcut.com |
| unknown |
accounts.google.com |
| whitelisted |
lf16-web-buz.capcut.com |
| unknown |
starling-va.capcutapi.com |
| unknown |
Threats
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
capcut_capcutpc_invitefission_1.2.4_installer.exe | checkBoxCreateShortcut status:1
|