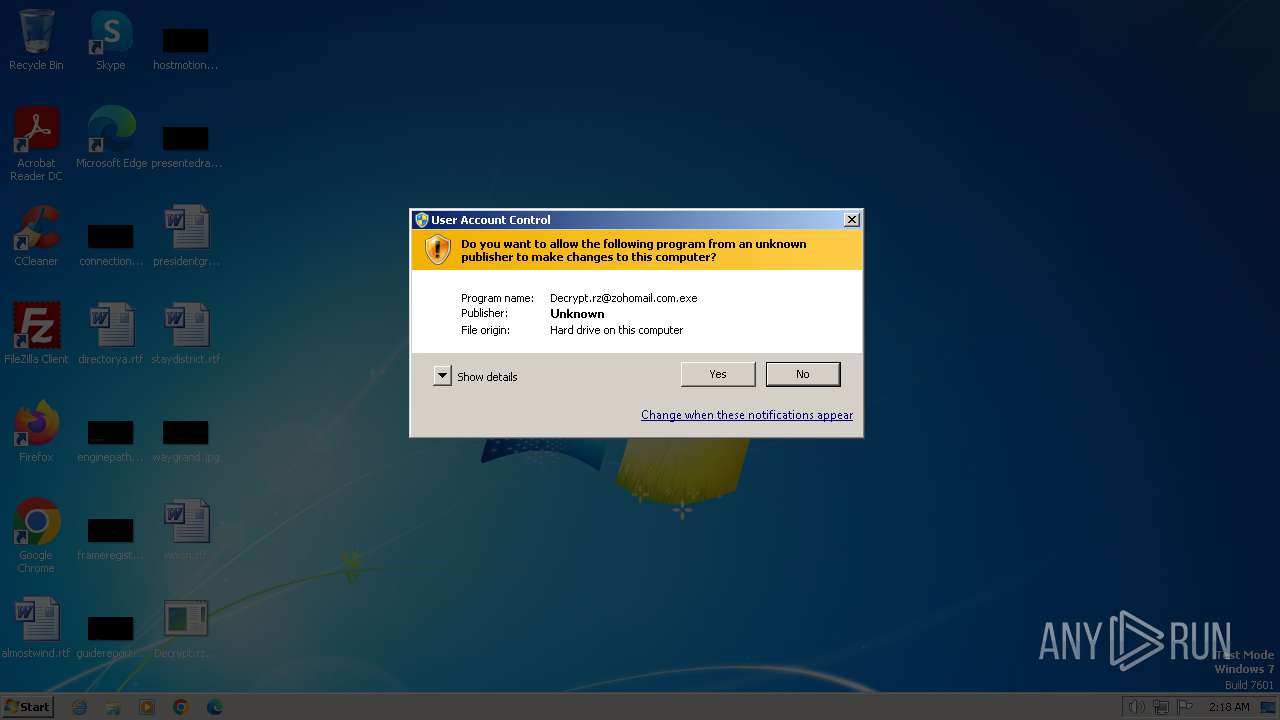
| File name: | Decrypt.rz@zohomail.com.exe |
| Full analysis: | https://app.any.run/tasks/d0de3fb4-464c-4b0c-a87f-aadf8862a862 |
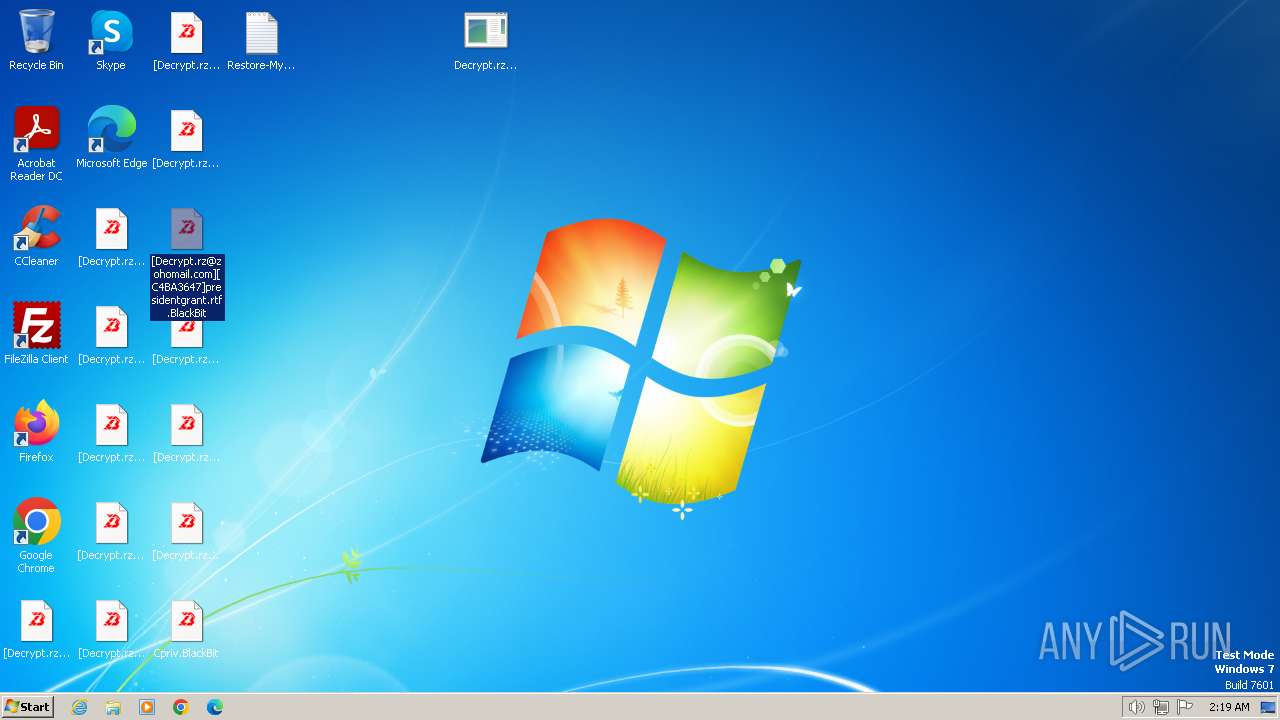
| Verdict: | Malicious activity |
| Analysis date: | March 19, 2024, 02:17:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 40F71B66A8A337082C2D8FD98D326312 |
| SHA1: | 2D8B734656B0A010748DB5D14910A5C99E753571 |
| SHA256: | ABC1974D0186AC3307AB509601C8BCE9F50ACD2AADA725F90D35D066C5603B31 |
| SSDEEP: | 24576:BAh1CA2UEiIwCEzDaamePkN/9qr5IvbpW9Xj:BAh1CA2UEiDCEzDaalPkN/9qr5ipW9Xj |
MALICIOUS
Drops the executable file immediately after the start
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- csc.exe (PID: 3516)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
- csc.exe (PID: 3824)
Starts Visual C# compiler
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
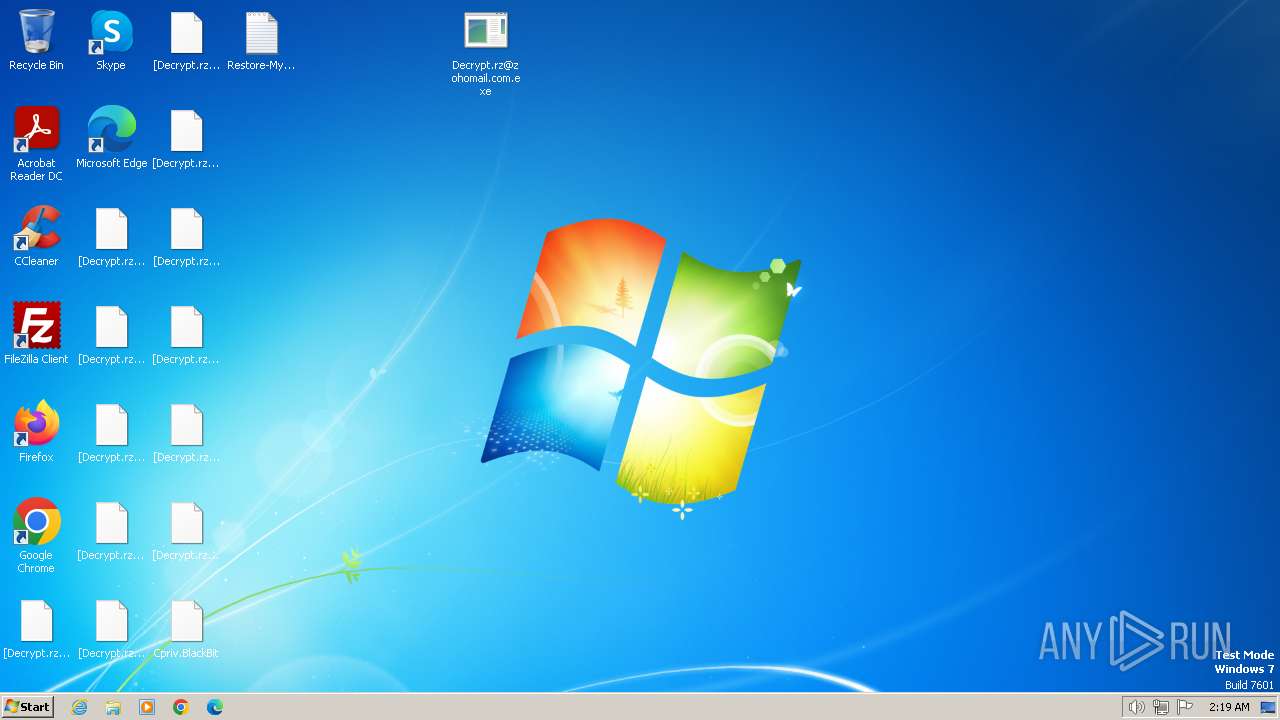
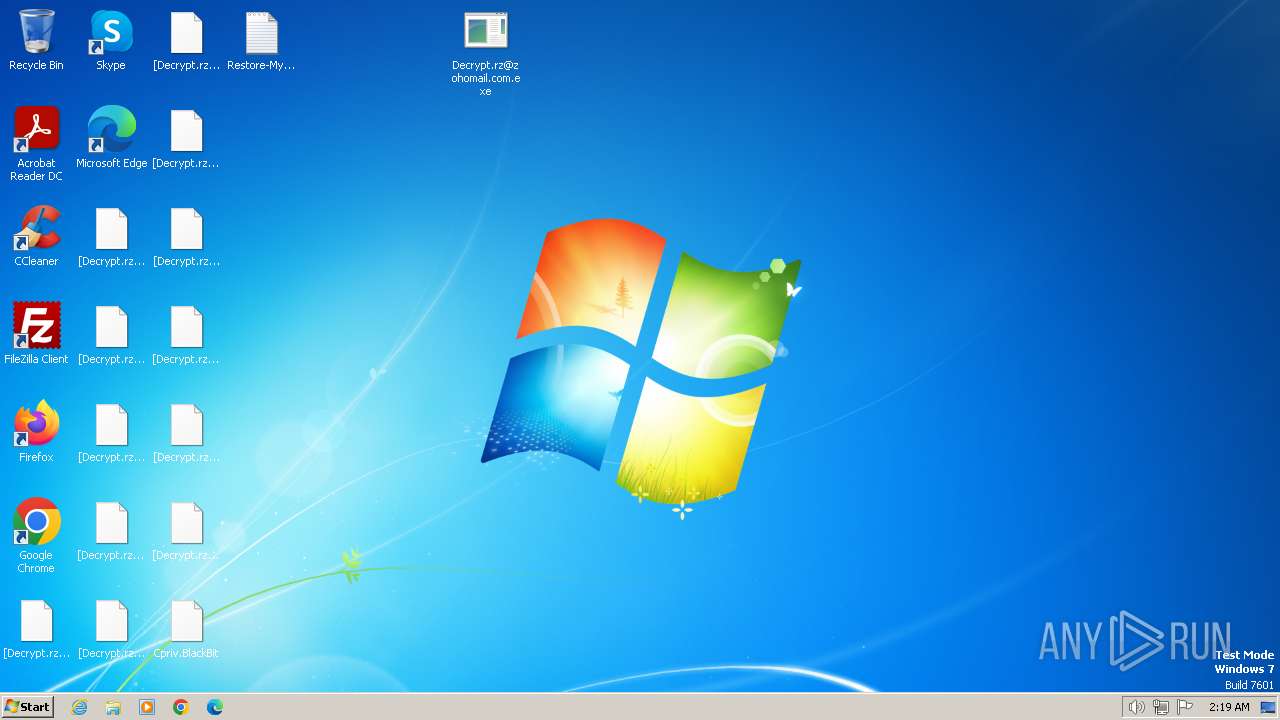
Create files in the Startup directory
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
Deletes shadow copies
- cmd.exe (PID: 2844)
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 3688)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 2924)
- cmd.exe (PID: 2536)
Disables Windows Defender
- Decrypt.rz@zohomail.com.exe (PID: 2136)
SUSPICIOUS
Executable content was dropped or overwritten
- csc.exe (PID: 3516)
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
- csc.exe (PID: 3824)
Reads the Internet Settings
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
- WMIC.exe (PID: 3920)
Creates file in the systems drive root
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
Application launched itself
- Decrypt.rz@zohomail.com.exe (PID: 2124)
Uses pipe srvsvc via SMB (transferring data)
- Decrypt.rz@zohomail.com.exe (PID: 2124)
Write to the desktop.ini file (may be used to cloak folders)
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
Uses .NET C# to load dll
- Decrypt.rz@zohomail.com.exe (PID: 2136)
- Decrypt.rz@zohomail.com.exe (PID: 2124)
Starts CMD.EXE for commands execution
- Decrypt.rz@zohomail.com.exe (PID: 2136)
Reads security settings of Internet Explorer
- Decrypt.rz@zohomail.com.exe (PID: 2136)
- Decrypt.rz@zohomail.com.exe (PID: 2124)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 2916)
- cmd.exe (PID: 3836)
Executes as Windows Service
- VSSVC.exe (PID: 2804)
- wbengine.exe (PID: 1608)
- vds.exe (PID: 3504)
INFO
Reads the machine GUID from the registry
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- cvtres.exe (PID: 2072)
- Decrypt.rz@zohomail.com.exe (PID: 2036)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
- csc.exe (PID: 3824)
- cvtres.exe (PID: 3604)
- csc.exe (PID: 3516)
Checks supported languages
- cvtres.exe (PID: 2072)
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- Decrypt.rz@zohomail.com.exe (PID: 2036)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
- csc.exe (PID: 3824)
- cvtres.exe (PID: 3604)
- csc.exe (PID: 3516)
Creates files in the program directory
- csc.exe (PID: 3516)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
- csc.exe (PID: 3824)
- Decrypt.rz@zohomail.com.exe (PID: 2124)
Create files in a temporary directory
- cvtres.exe (PID: 2072)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
- cvtres.exe (PID: 3604)
- Decrypt.rz@zohomail.com.exe (PID: 2124)
Reads the computer name
- Decrypt.rz@zohomail.com.exe (PID: 2124)
- Decrypt.rz@zohomail.com.exe (PID: 2036)
- Decrypt.rz@zohomail.com.exe (PID: 2136)
Creates files or folders in the user directory
- Decrypt.rz@zohomail.com.exe (PID: 2124)
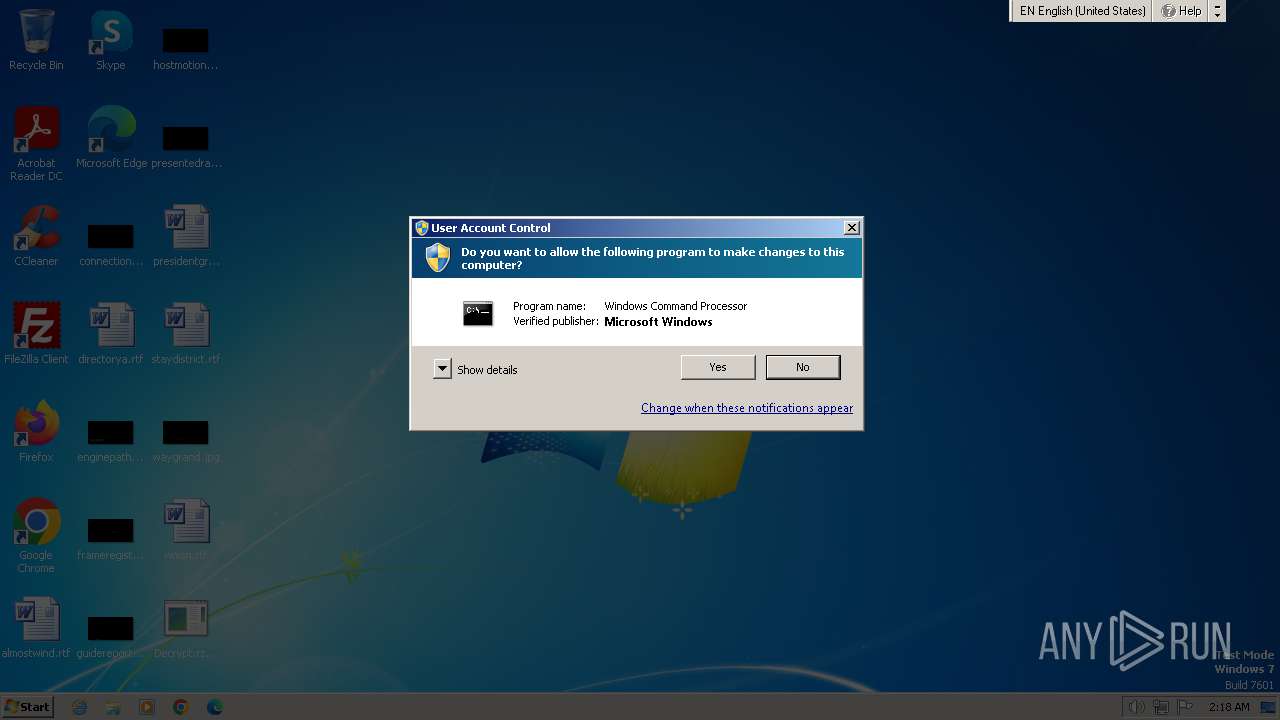
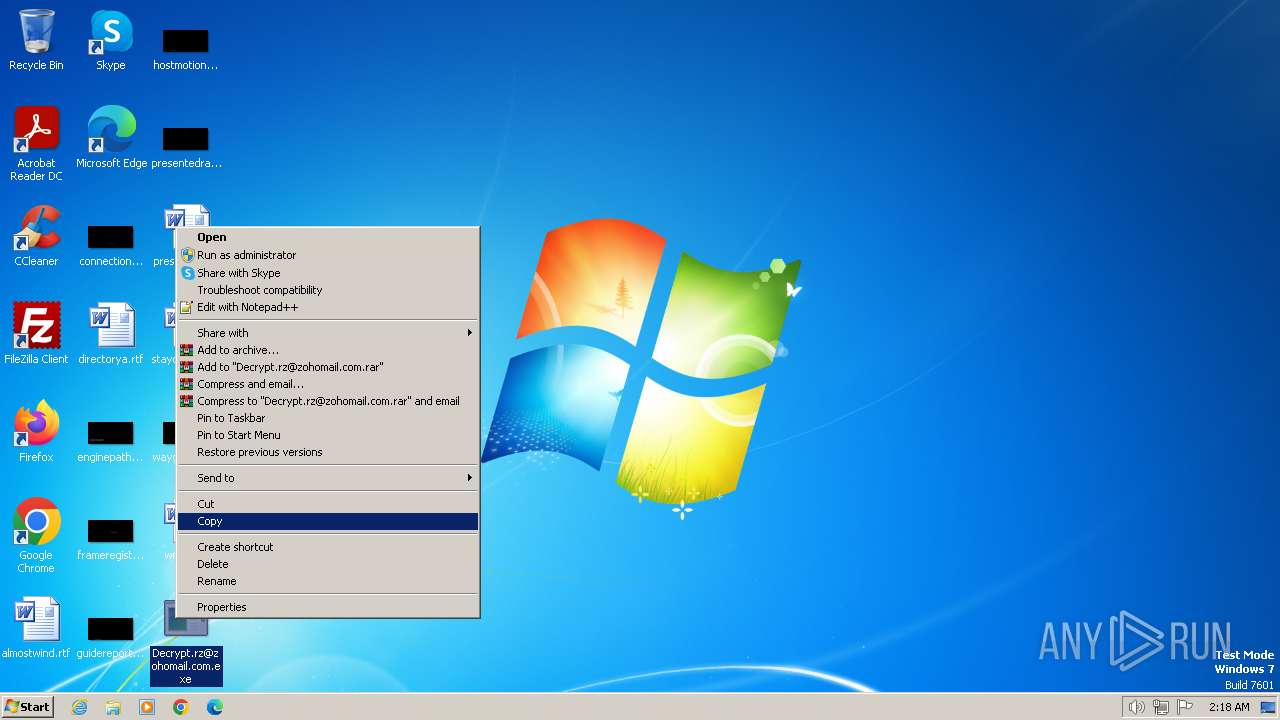
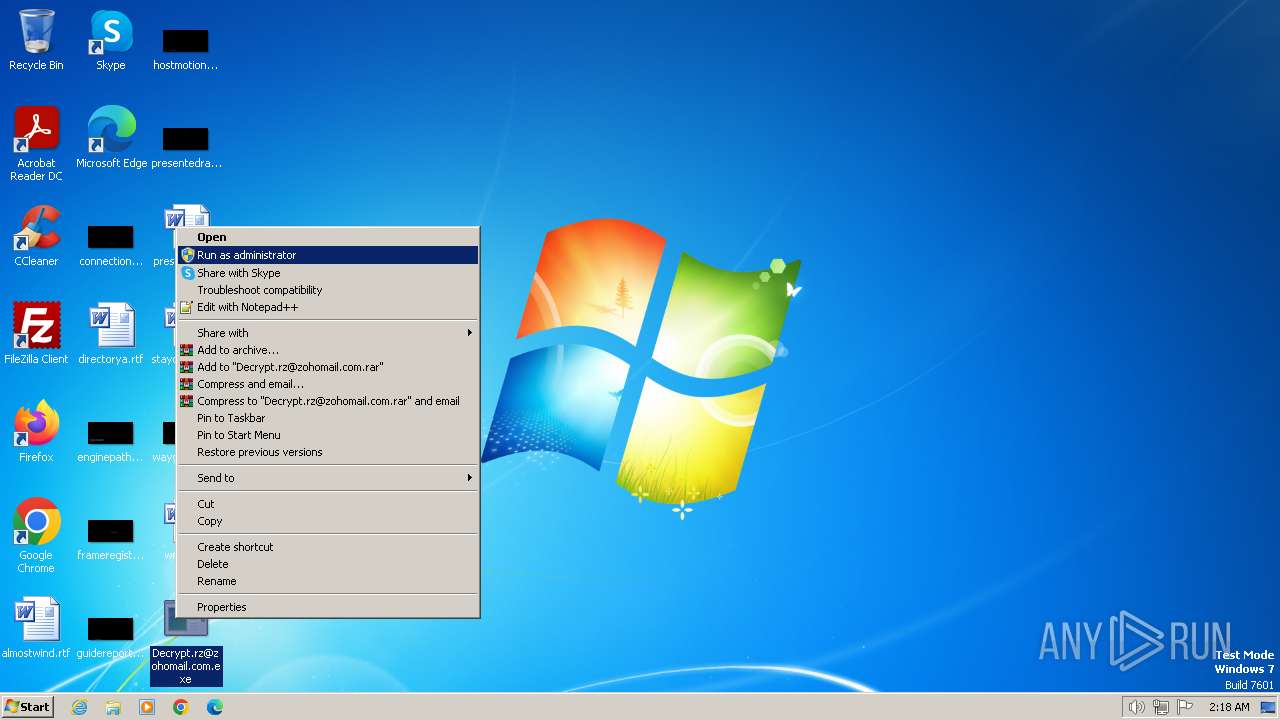
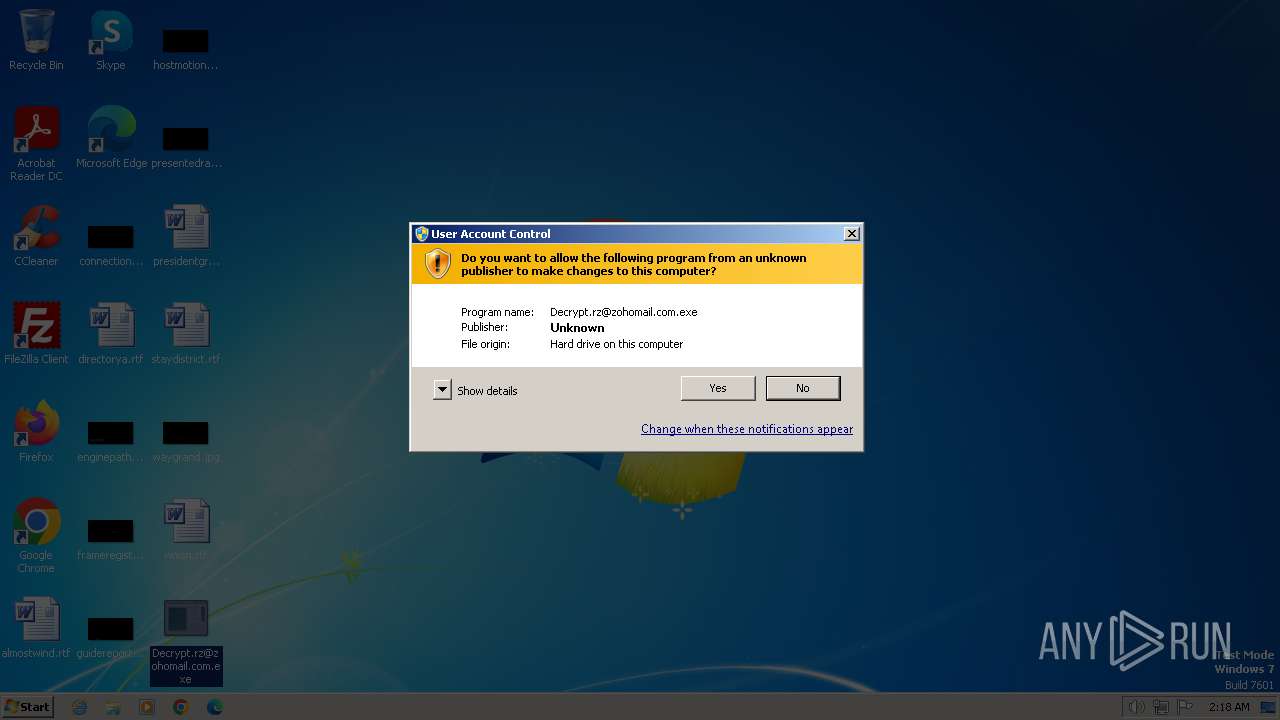
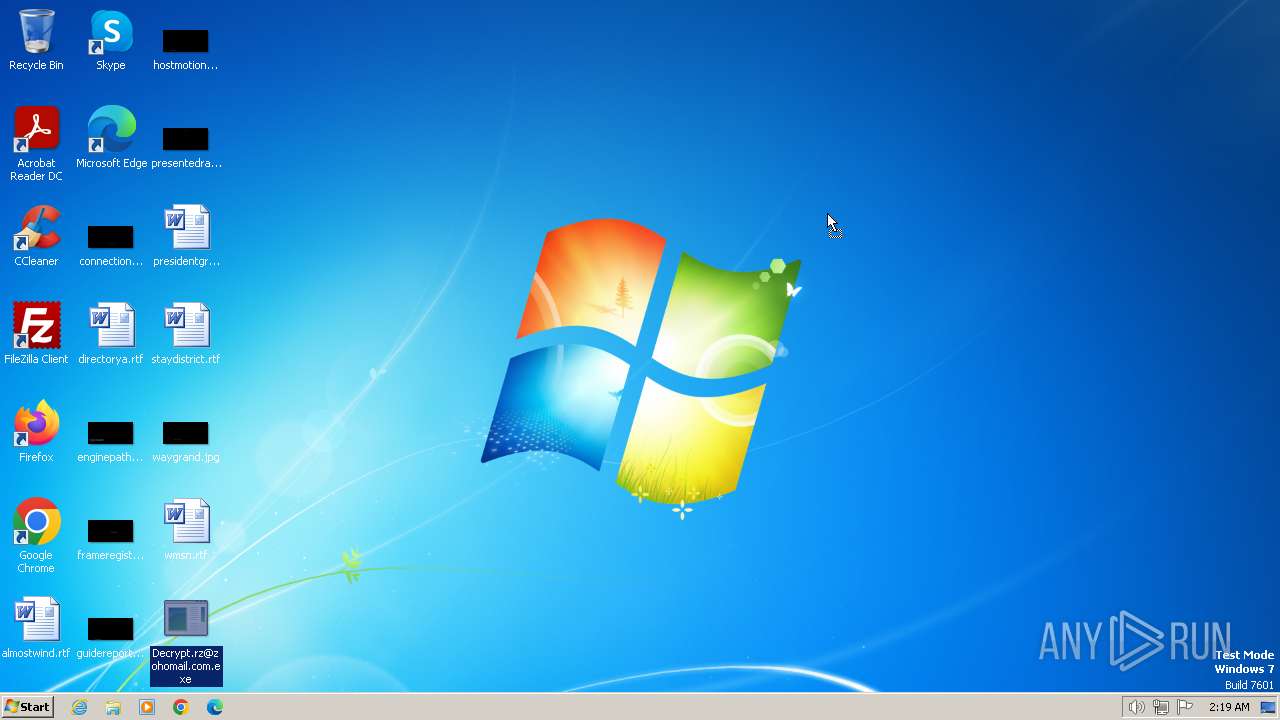
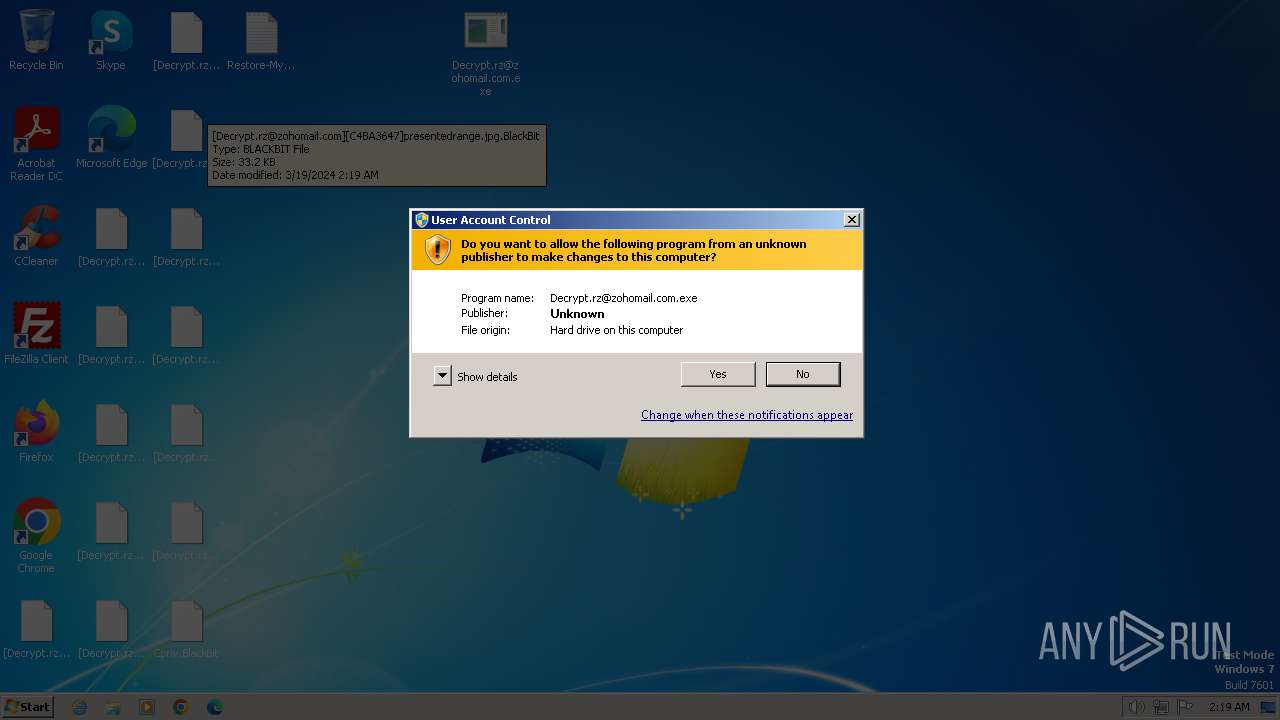
Manual execution by a user
- Decrypt.rz@zohomail.com.exe (PID: 2036)
Reads Environment values
- Decrypt.rz@zohomail.com.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:07:13 22:47:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 451072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcd2f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft |
| FileDescription: | svchost |
| FileVersion: | 1.0.0.0 |
| InternalName: | svchost.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFileName: | svchost.exe |
| ProductName: | svchost |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.2.0.0 |
Total processes
88
Monitored processes
28
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1336 | wbadmin delete catalog -quiet | C:\Windows\System32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | "C:\Windows\system32\wbengine.exe" | C:\Windows\System32\wbengine.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Block Level Backup Engine Service EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | wbadmin DELETE SYSTEMSTATEBACKUP | C:\Windows\System32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 4294967293 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2036 | "C:\Users\admin\Desktop\Decrypt.rz@zohomail.com.exe" | C:\Users\admin\Desktop\Decrypt.rz@zohomail.com.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: svchost Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2072 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES4735.tmp" "c:\ProgramData\CSC7BF95240584649E6BD65124F94C7A877.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\Desktop\Decrypt.rz@zohomail.com.exe" | C:\Users\admin\Desktop\Decrypt.rz@zohomail.com.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: svchost Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\Desktop\Decrypt.rz@zohomail.com.exe" | C:\Users\admin\Desktop\Decrypt.rz@zohomail.com.exe | Decrypt.rz@zohomail.com.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: svchost Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2176 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | netsh firewall set opmode mode=disable | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 481
Read events
10 246
Write events
235
Delete events
0
Modification events
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Invoke |
| Operation: | write | Name: | Michael Gillespie |
Value: C:\ProgramData\winlogon.exe | |||
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Decrypt_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Decrypt_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Decrypt_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Decrypt_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2124) Decrypt.rz@zohomail.com.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Decrypt_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
27
Suspicious files
93
Text files
538
Unknown types
2 756
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | Decrypt.rz@zohomail.com.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\winlogon.exe | executable | |
MD5:40F71B66A8A337082C2D8FD98D326312 | SHA256:ABC1974D0186AC3307AB509601C8BCE9F50ACD2AADA725F90D35D066C5603B31 | |||
| 2124 | Decrypt.rz@zohomail.com.exe | C:\Users\admin\AppData\Local\Temp\hijymhmg.ico | image | |
MD5:305C2042777E67710483E58ACC04AC2C | SHA256:F9DDF619CA0266055744C2BECA77673AA41702104B459A0F55DE3945196B6C50 | |||
| 3516 | csc.exe | C:\ProgramData\CSC7BF95240584649E6BD65124F94C7A877.TMP | binary | |
MD5:CAB93F5755F91A42DDA69ADE378B6450 | SHA256:0078DA646396DFCD75E13387C3382F04119D24B76417E86E5C5AB88F7F4CEF8C | |||
| 2124 | Decrypt.rz@zohomail.com.exe | C:\ProgramData\winlogon.exe | executable | |
MD5:40F71B66A8A337082C2D8FD98D326312 | SHA256:ABC1974D0186AC3307AB509601C8BCE9F50ACD2AADA725F90D35D066C5603B31 | |||
| 2124 | Decrypt.rz@zohomail.com.exe | C:\Users\admin\AppData\Roaming\winlogon.exe | executable | |
MD5:40F71B66A8A337082C2D8FD98D326312 | SHA256:ABC1974D0186AC3307AB509601C8BCE9F50ACD2AADA725F90D35D066C5603B31 | |||
| 2124 | Decrypt.rz@zohomail.com.exe | C:\Users\admin\AppData\Local\Temp\spd5emco.0.cs | text | |
MD5:94B9B21922ACD93345556A6E6864B8DC | SHA256:CE6B730C181CC081042A62FC27CFA946624E6C7A2B864336FDAA262CF3ABA39A | |||
| 2124 | Decrypt.rz@zohomail.com.exe | C:\Users\admin\Documents\Cpriv.BlackBit | text | |
MD5:BABE95A250D4939AF2961B88176779A6 | SHA256:783680586BC6564EC76E56F50D4216A8400CDF3A918E607DB7733EC6AEA97E91 | |||
| 2124 | Decrypt.rz@zohomail.com.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Cpriv.BlackBit | text | |
MD5:BABE95A250D4939AF2961B88176779A6 | SHA256:783680586BC6564EC76E56F50D4216A8400CDF3A918E607DB7733EC6AEA97E91 | |||
| 2124 | Decrypt.rz@zohomail.com.exe | C:\Users\admin\Music\Cpriv.BlackBit | text | |
MD5:BABE95A250D4939AF2961B88176779A6 | SHA256:783680586BC6564EC76E56F50D4216A8400CDF3A918E607DB7733EC6AEA97E91 | |||
| 2124 | Decrypt.rz@zohomail.com.exe | C:\Users\admin\Videos\Cpriv.BlackBit | text | |
MD5:BABE95A250D4939AF2961B88176779A6 | SHA256:783680586BC6564EC76E56F50D4216A8400CDF3A918E607DB7733EC6AEA97E91 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
20
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.2:445 | — | — | — | whitelisted |
4 | System | 192.168.100.1:445 | — | — | — | unknown |
4 | System | 192.168.100.2:139 | — | — | — | whitelisted |
4 | System | 192.168.100.1:139 | — | — | — | unknown |
4 | System | 192.168.100.2:137 | — | — | — | whitelisted |
4 | System | 192.168.100.1:137 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
dns.msftncsi.com |
| shared |