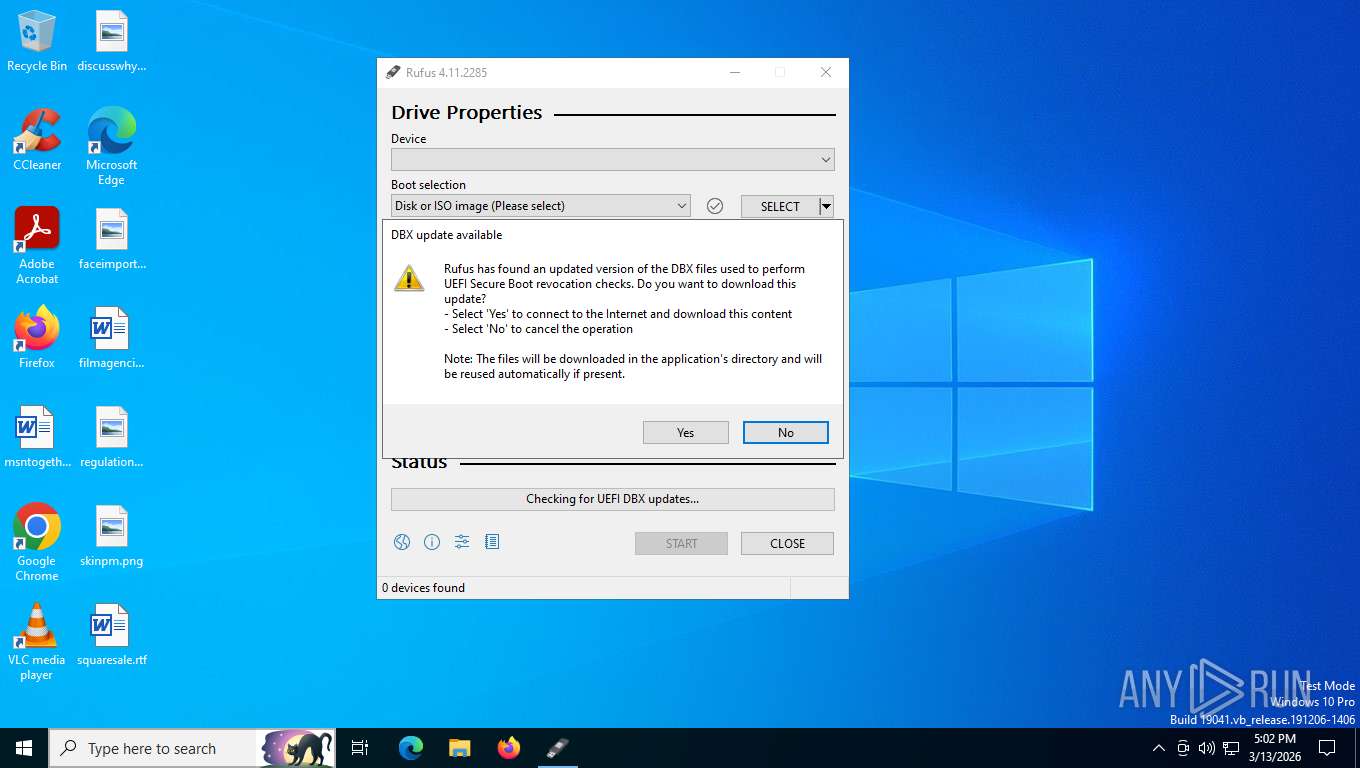
| File name: | rufus-4.11.exe |
| Full analysis: | https://app.any.run/tasks/c4152e38-fcac-4235-9e35-d38ddc3e5062 |
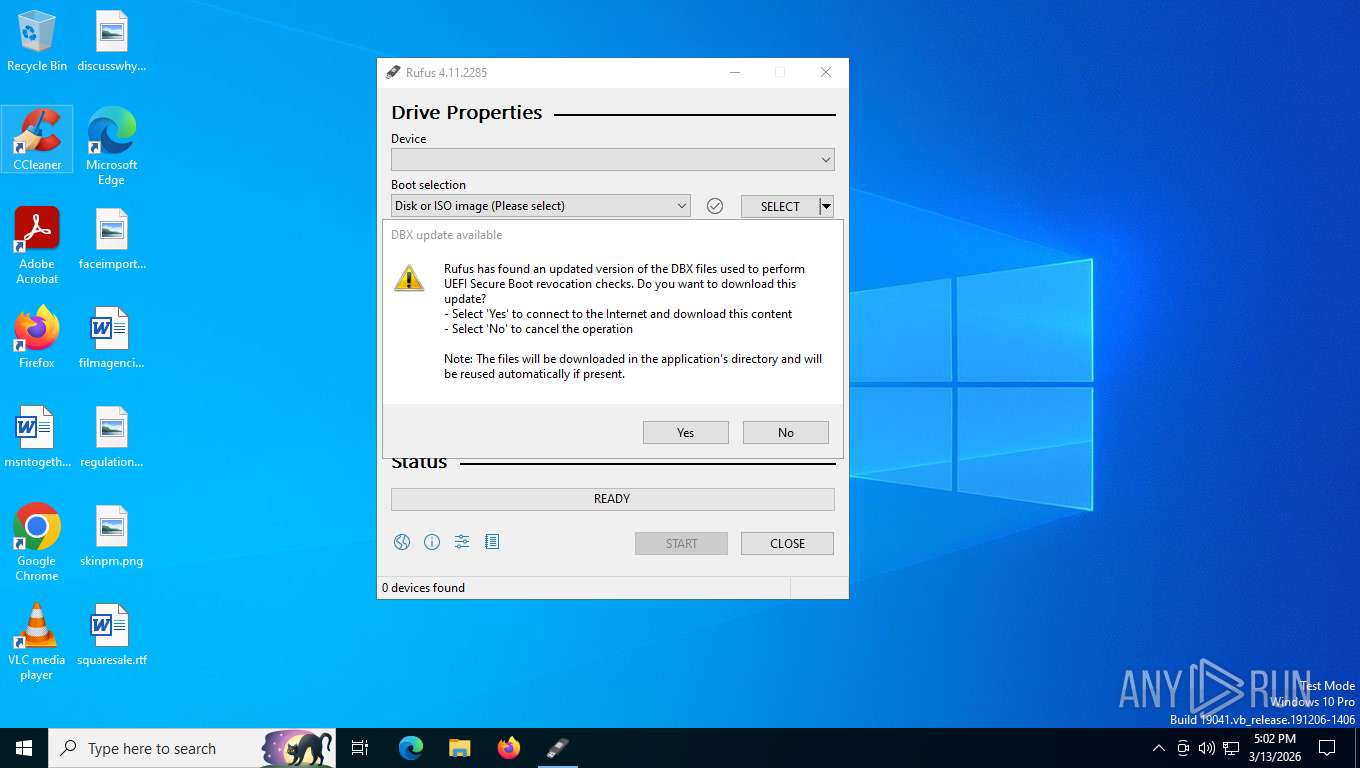
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2026, 21:01:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 3 sections |
| MD5: | 5B86D4F2CE7D2AB212914C634D20F714 |
| SHA1: | FD96FD51231E449678D71C7A5F8A2308B1C88375 |
| SHA256: | ABBF04D50A44A9612C027FC8072F6DA67F5BCDA2B826F1F852C9C24D7A1FCDFF |
| SSDEEP: | 98304:/tLadtyVqWVX1+JhThc5lBH9IR3/kxjcLjhs4ArFt/a6M7dMI9IDi6pBYcyXnoA2:Fg4Cly |
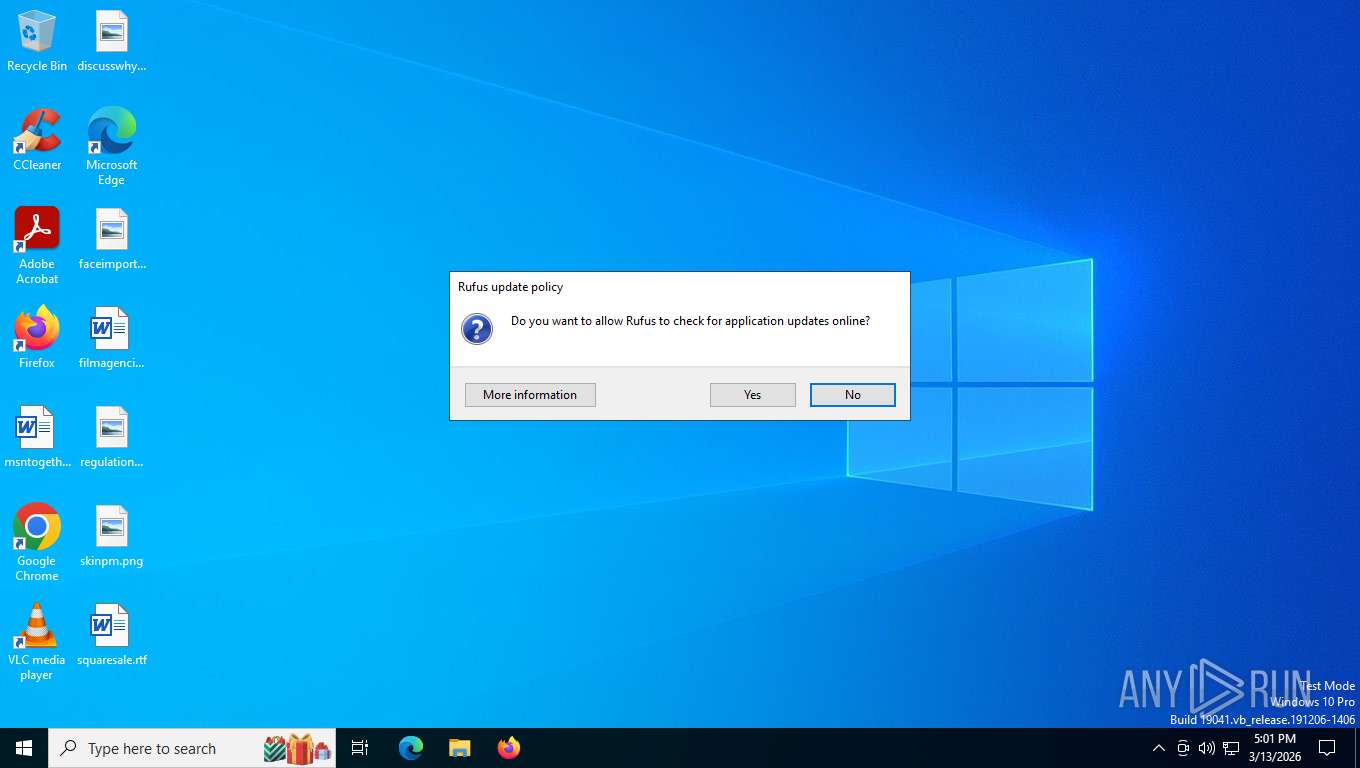
MALICIOUS
Changes the Windows auto-update feature
- rufus-4.11.exe (PID: 9208)
SUSPICIOUS
Executes as Windows Service
- vds.exe (PID: 7944)
INFO
Reads the machine GUID from the registry
- rufus-4.11.exe (PID: 9208)
Reads the computer name
- rufus-4.11.exe (PID: 9208)
Create files in a temporary directory
- rufus-4.11.exe (PID: 9208)
Process checks whether UAC notifications are on
- rufus-4.11.exe (PID: 9208)
Creates files or folders in the user directory
- rufus-4.11.exe (PID: 9208)
Checks supported languages
- rufus-4.11.exe (PID: 9208)
UPX packer has been detected
- rufus-4.11.exe (PID: 9208)
Reads security settings of Internet Explorer
- rufus-4.11.exe (PID: 9208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2095:05:10 17:21:16+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 1884160 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | 3776512 |
| EntryPoint: | 0x5658c0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.11.2285.0 |
| ProductVersionNumber: | 4.11.2285.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | https://rufus.ie |
| CompanyName: | Akeo Consulting |
| FileDescription: | Rufus |
| FileVersion: | 4.11.2285 |
| InternalName: | Rufus |
| LegalCopyright: | © 2011-2025 Pete Batard (GPL v3) |
| LegalTrademarks: | https://www.gnu.org/licenses/gpl-3.0.html |
| OriginalFileName: | rufus-4.11.exe |
| ProductName: | Rufus |
| ProductVersion: | 4.11.2285 |
Total processes
158
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 224 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
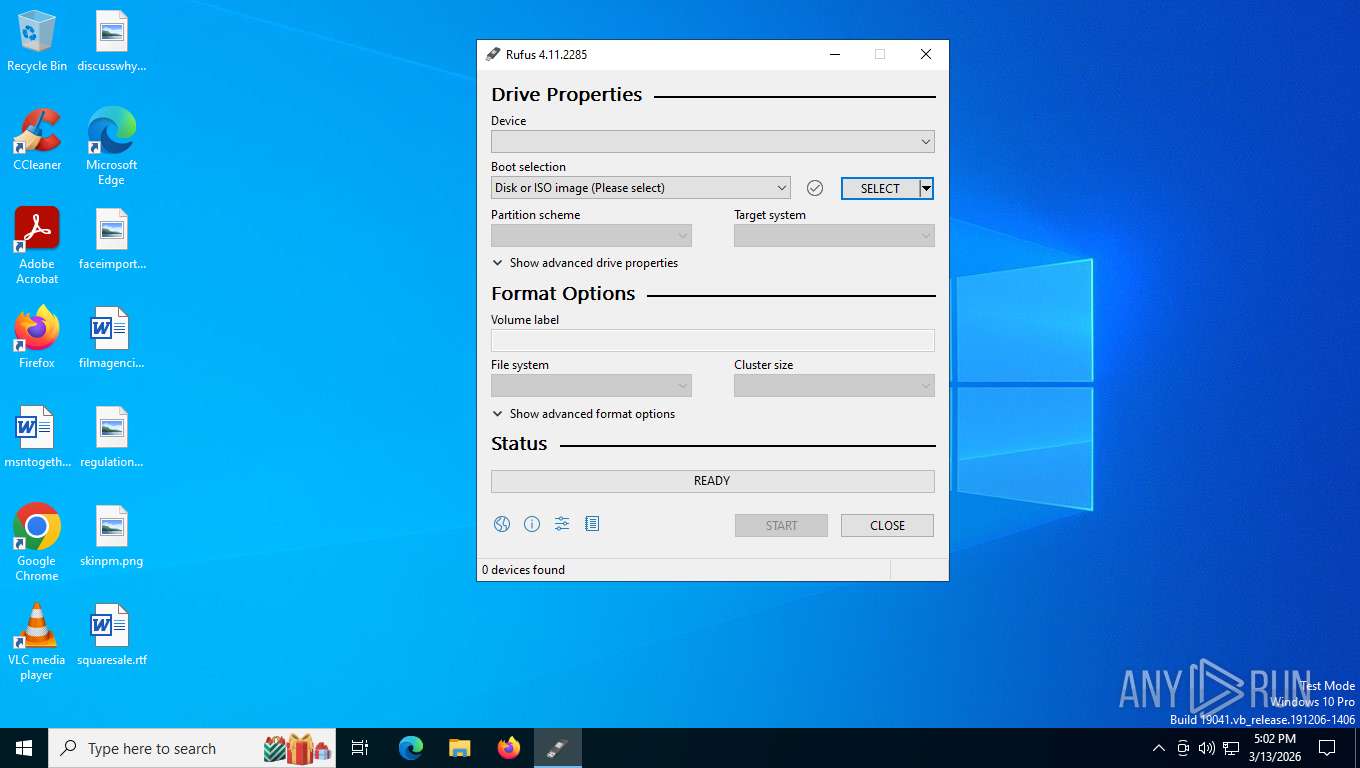
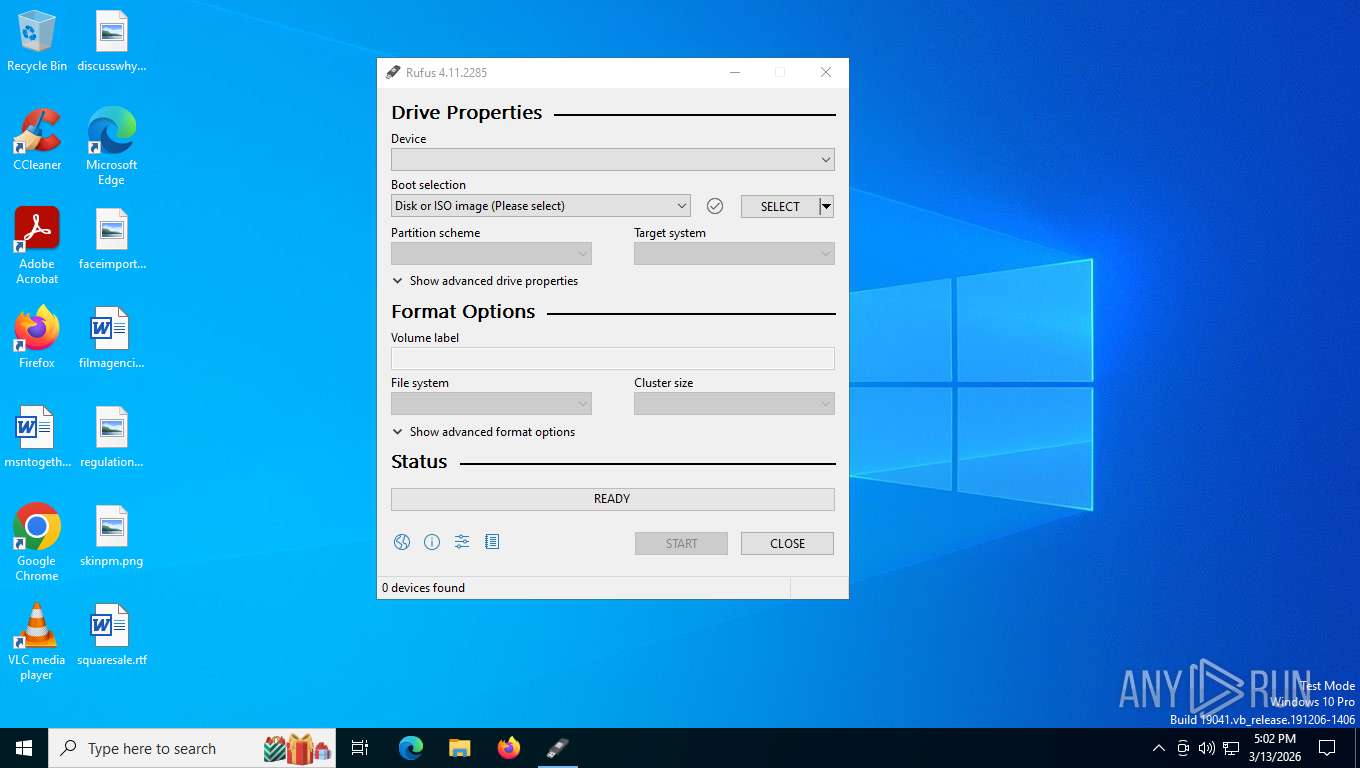
| 4304 | "C:\Users\admin\AppData\Local\Temp\rufus-4.11.exe" | C:\Users\admin\AppData\Local\Temp\rufus-4.11.exe | — | explorer.exe | |||||||||||
User: admin Company: Akeo Consulting Integrity Level: MEDIUM Description: Rufus Exit code: 3221226540 Version: 4.11.2285 Modules
| |||||||||||||||
| 7636 | C:\WINDOWS\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Virtual Disk Service Loader Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7944 | C:\WINDOWS\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 9208 | "C:\Users\admin\AppData\Local\Temp\rufus-4.11.exe" | C:\Users\admin\AppData\Local\Temp\rufus-4.11.exe | explorer.exe | ||||||||||||
User: admin Company: Akeo Consulting Integrity Level: HIGH Description: Rufus Version: 4.11.2285 Modules
| |||||||||||||||
Total events
1 403
Read events
1 336
Write events
34
Delete events
33
Modification events
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Akeo Consulting\Rufus |
| Operation: | write | Name: | CommCheck64 |
Value: 3C561E0000000000 | |||
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{D4A218D3-4466-468F-BDF7-A756B2942EFC}Machine\Software\Policies\Microsoft\AppHVSI |
| Operation: | write | Name: | AllowAppHVSI_ProviderSet |
Value: 0 | |||
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{D4A218D3-4466-468F-BDF7-A756B2942EFC}Machine\Software\Policies\Microsoft\EdgeUpdate |
| Operation: | write | Name: | UpdateDefault |
Value: 0 | |||
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{D4A218D3-4466-468F-BDF7-A756B2942EFC}Machine\Software\Policies\Microsoft\Windows\Network Connections |
| Operation: | write | Name: | NC_DoNotShowLocalOnlyIcon |
Value: 1 | |||
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{D4A218D3-4466-468F-BDF7-A756B2942EFC}Machine\Software\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | EnableSmartScreen |
Value: 0 | |||
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{D4A218D3-4466-468F-BDF7-A756B2942EFC}Machine\Software\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | **del.ShellSmartScreenLevel |
Value: | |||
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{D4A218D3-4466-468F-BDF7-A756B2942EFC}Machine\Software\Policies\Microsoft\Windows\Windows Feeds |
| Operation: | write | Name: | EnableFeeds |
Value: 0 | |||
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{D4A218D3-4466-468F-BDF7-A756B2942EFC}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{D4A218D3-4466-468F-BDF7-A756B2942EFC}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUStatusServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (9208) rufus-4.11.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{D4A218D3-4466-468F-BDF7-A756B2942EFC}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | UpdateServiceUrlAlternate |
Value: http://neverupdatewindows10.com | |||
Executable files
0
Suspicious files
14
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9208 | rufus-4.11.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\sbat_level[1].txt | text | |
MD5:56DE005EB20181CDD68ED3032AF86F60 | SHA256:87E6B80F7E1DFD4C76FE0D5A0B4671265FC59BB4D25BFAC08DEA489927B58A87 | |||
| 9208 | rufus-4.11.exe | C:\Windows\System32\GroupPolicy\Machine\Registry.pol | binary | |
MD5:39E5BE35CC598F9086924A39E1105BF8 | SHA256:1C26BCB05CA50C85751D3023494D2E4D35F56D74451AC47880FD239F3B54F171 | |||
| 9208 | rufus-4.11.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:7F924EAEA21BB91214FF7B4525F3BD29 | SHA256:E718475014C8F51A8F2746FBE90A7BFF516B65BEF36EE6340A5FC746BC5DFC32 | |||
| 9208 | rufus-4.11.exe | C:\Users\admin\AppData\Local\Temp\Ruf5590.tmp | text | |
MD5:727ED48003879D07D5CC9D0EE5F41ECF | SHA256:F63525DEE1D721CF2C766E964AA85A6C156B3EE5B434AAD01C8AADB40BB6AFB9 | |||
| 9208 | rufus-4.11.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7DACE55039CA6999268859156FBC55EF | binary | |
MD5:1C876C6C00FD7D5DA020229B131C7A90 | SHA256:866226FBB758C4678CB3AE40556B0DCB27DBE6EF089DC175AF10F14E7A212D45 | |||
| 9208 | rufus-4.11.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:1C2D4956F25997CEA7C091A6A4F8BEDF | SHA256:EA889DF210FF232993BD7791C23372E0F4AE0A9CD43DD27A1D91103BE40591C6 | |||
| 9208 | rufus-4.11.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0DBF8FDF4477DDB1046881C52784692A | binary | |
MD5:A833DA36D6B3A97C777E01AF8C4D4EAC | SHA256:1878178A9A6603913340890B40562B2DEEF02D1EC8965CD67E4A1CE502CB7580 | |||
| 9208 | rufus-4.11.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\10C8BDB0D7E5729D576C30C7920D43C5 | binary | |
MD5:4AA6BA1D2B3FB57418927307881C8744 | SHA256:CA64A61BF5527EC853D8AD8E7F2BF203F467BC17F41B7693017CC09D61A63D64 | |||
| 9208 | rufus-4.11.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\10C8BDB0D7E5729D576C30C7920D43C5 | binary | |
MD5:C45451F6EEE8D51DB2017194593E39E1 | SHA256:E9C79A034132A6242C9D159B25F6F87ED6328644111DAF504DF299F77FC4E4C1 | |||
| 9208 | rufus-4.11.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0DBF8FDF4477DDB1046881C52784692A | binary | |
MD5:62D94FBE7307CB95786DE812F08830DB | SHA256:A1F6F92457EFA2AF9ADD01A08DC67AE0E39A877D2FAC546B66B127B5213D8B77 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
129
TCP/UDP connections
44
DNS requests
27
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
9208 | rufus-4.11.exe | GET | 302 | 140.82.121.3:443 | https://github.com/pbatard/Fido/releases/download/v1.69/Fido.ps1.lzma | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 200 | 20.190.159.23:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
356 | svchost.exe | GET | 200 | 23.11.40.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
9208 | rufus-4.11.exe | GET | 200 | 104.18.20.213:80 | http://r12.c.lencr.org/72.crl | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 400 | 20.190.159.23:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
9208 | rufus-4.11.exe | GET | 200 | 185.199.108.153:443 | https://rufus.ie/sbat_level.txt | unknown | text | 290 b | unknown |
9208 | rufus-4.11.exe | GET | 200 | 185.199.108.153:443 | https://rufus.ie/sb_active.txt | unknown | text | 163 b | unknown |
9208 | rufus-4.11.exe | GET | 200 | 185.199.108.153:443 | https://rufus.ie/sb_revoked.txt | unknown | text | 40 b | unknown |
9208 | rufus-4.11.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEBqer%2Bxt6OGbXBkxQbaNkN0%3D | unknown | — | — | whitelisted |
9208 | rufus-4.11.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQzZq5DY2RqjBUGCjtK3%2FEujBgJrwQU0SLaTFnxS18mOKqd1u7rDcP7qWECEDbgWe2IjdV67dVwtnJ%2Fm9o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8400 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3348 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2292 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2292 | svchost.exe | 224.0.0.251:5353 | — | — | — | whitelisted |
356 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 23.11.40.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
rufus.ie |
| whitelisted |
r12.c.lencr.org |
| whitelisted |
github.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
8400 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
rufus-4.11.exe | *** Rufus init ***
|
rufus-4.11.exe | Dat dir: 'C:\Users\admin\AppData\Local'
|
rufus-4.11.exe | Sys dir: 'C:\WINDOWS\system32'
|
rufus-4.11.exe | Cur dir: 'C:\Users\admin\AppData\Local\Temp\'
|
rufus-4.11.exe | App dir: 'C:\Users\admin\AppData\Local\Temp\'
|
rufus-4.11.exe | Usr dir: 'C:\Users\admin'
|
rufus-4.11.exe | Tmp dir: 'C:\Users\admin\AppData\Local\Temp\'
|
rufus-4.11.exe | Will use settings from registry
|
rufus-4.11.exe | Binary executable is signed by 'Akeo Consulting'
|
rufus-4.11.exe | localization: extracted data to 'C:\Users\admin\AppData\Local\Temp\Ruf5590.tmp'
|