| File name: | rufus-4.11p.exe |
| Full analysis: | https://app.any.run/tasks/249c16a4-732a-4c1e-8dc3-5caa0faed001 |
| Verdict: | Malicious activity |
| Analysis date: | October 21, 2025, 03:33:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 3 sections |
| MD5: | 5B86D4F2CE7D2AB212914C634D20F714 |
| SHA1: | FD96FD51231E449678D71C7A5F8A2308B1C88375 |
| SHA256: | ABBF04D50A44A9612C027FC8072F6DA67F5BCDA2B826F1F852C9C24D7A1FCDFF |
| SSDEEP: | 98304:/tLadtyVqWVX1+JhThc5lBH9IR3/kxjcLjhs4ArFt/a6M7dMI9IDi6pBYcyXnoA2:Fg4Cly |
MALICIOUS
Changes the Windows auto-update feature
- rufus-4.11p.exe (PID: 7728)
SUSPICIOUS
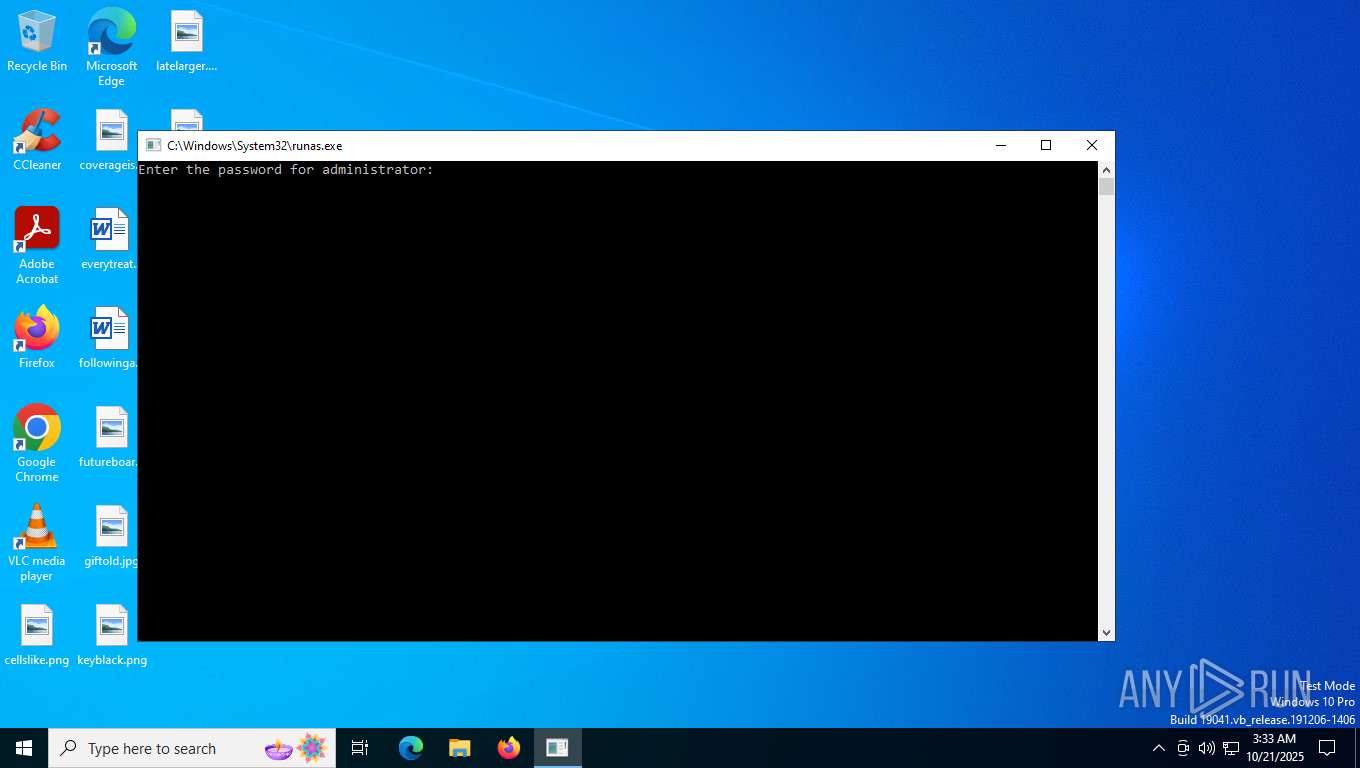
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 7464)
Executes as Windows Service
- vds.exe (PID: 7816)
Creates file in the systems drive root
- rufus-4.11p.exe (PID: 7728)
Reads security settings of Internet Explorer
- rufus-4.11p.exe (PID: 7728)
INFO
Reads the computer name
- rufus-4.11p.exe (PID: 7728)
Checks supported languages
- rufus-4.11p.exe (PID: 7728)
Reads the machine GUID from the registry
- rufus-4.11p.exe (PID: 7728)
Process checks whether UAC notifications are on
- rufus-4.11p.exe (PID: 7728)
UPX packer has been detected
- rufus-4.11p.exe (PID: 7728)
Checks proxy server information
- rufus-4.11p.exe (PID: 7728)
Create files in a temporary directory
- rufus-4.11p.exe (PID: 7728)
Reads the software policy settings
- rufus-4.11p.exe (PID: 7728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2095:05:10 17:21:16+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 1884160 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | 3776512 |
| EntryPoint: | 0x5658c0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
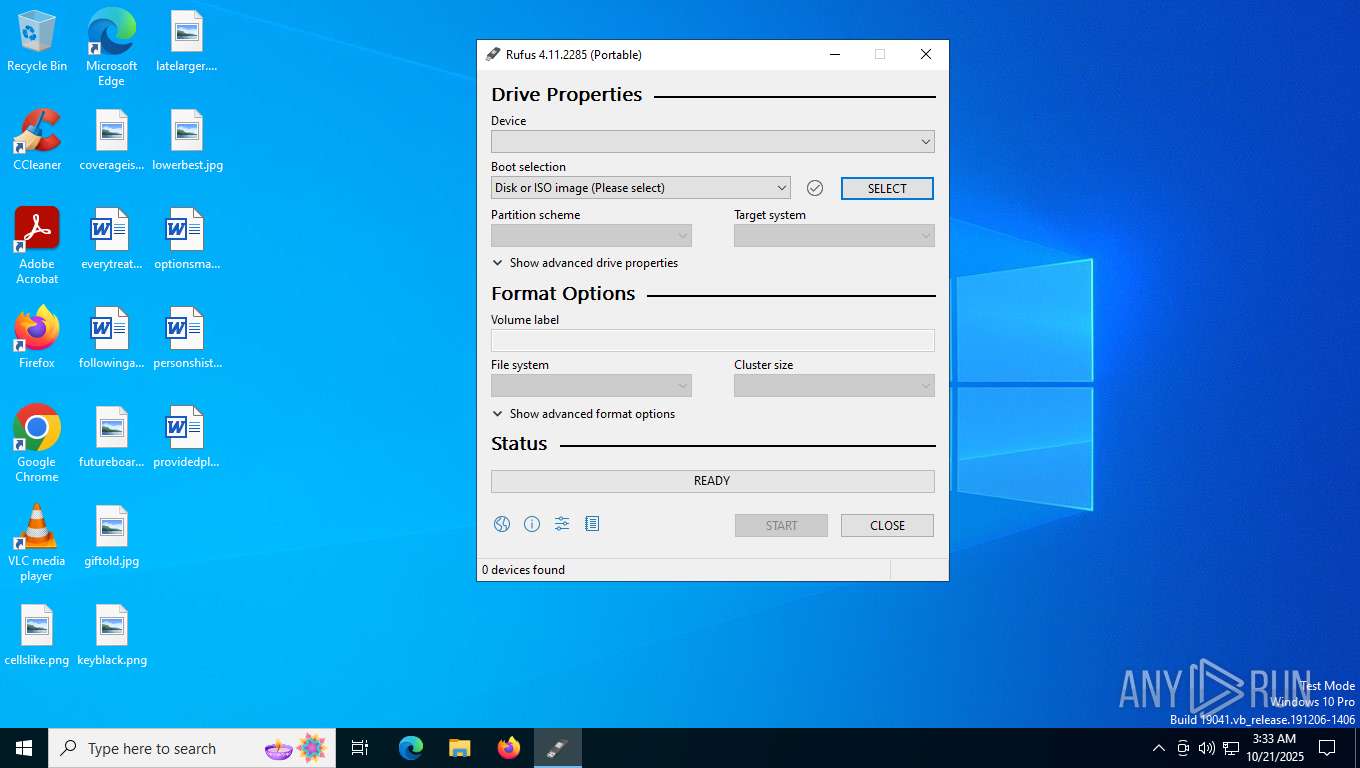
| FileVersionNumber: | 4.11.2285.0 |
| ProductVersionNumber: | 4.11.2285.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | https://rufus.ie |
| CompanyName: | Akeo Consulting |
| FileDescription: | Rufus |
| FileVersion: | 4.11.2285 |
| InternalName: | Rufus |
| LegalCopyright: | © 2011-2025 Pete Batard (GPL v3) |
| LegalTrademarks: | https://www.gnu.org/licenses/gpl-3.0.html |
| OriginalFileName: | rufus-4.11.exe |
| ProductName: | Rufus |
| ProductVersion: | 4.11.2285 |
Total processes
152
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7176 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
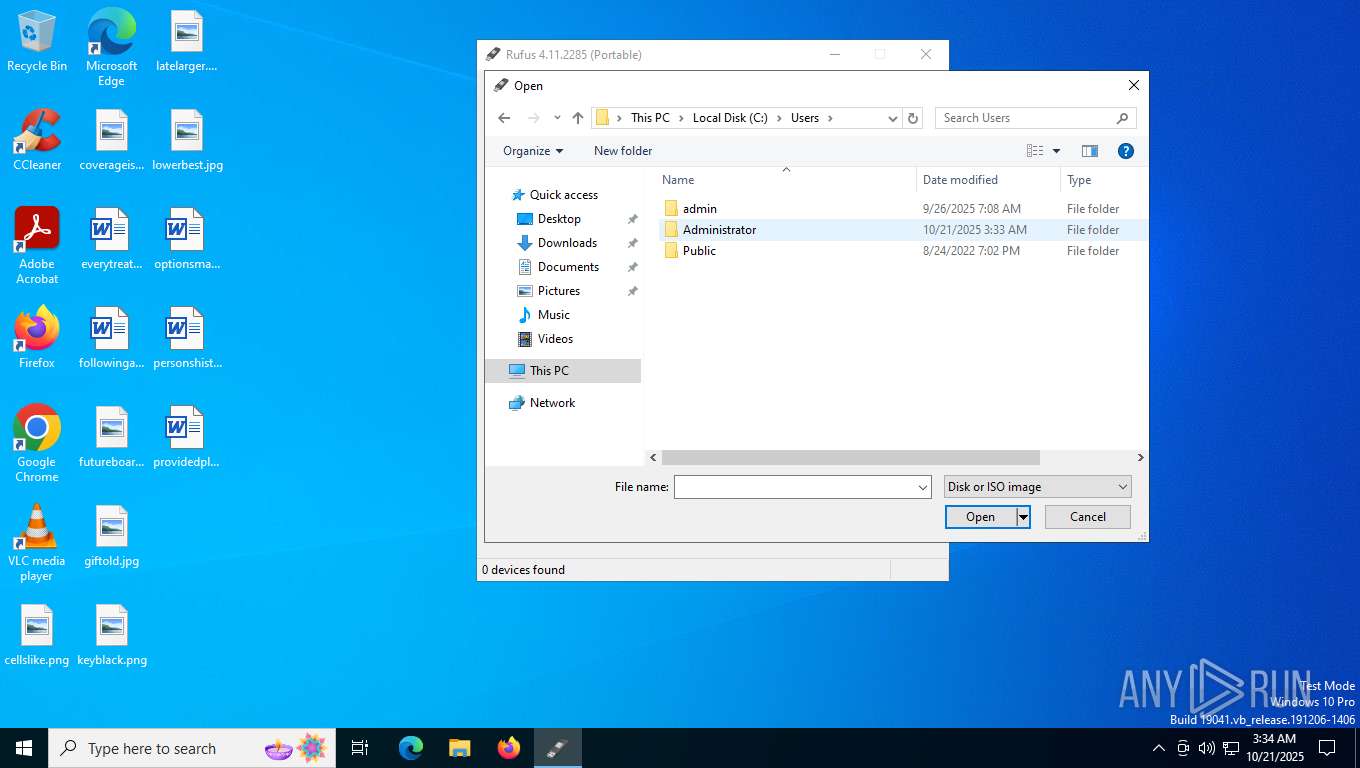
| 7464 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\AppData\Local\Temp\rufus-4.11p.exe | C:\Windows\System32\runas.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runas.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
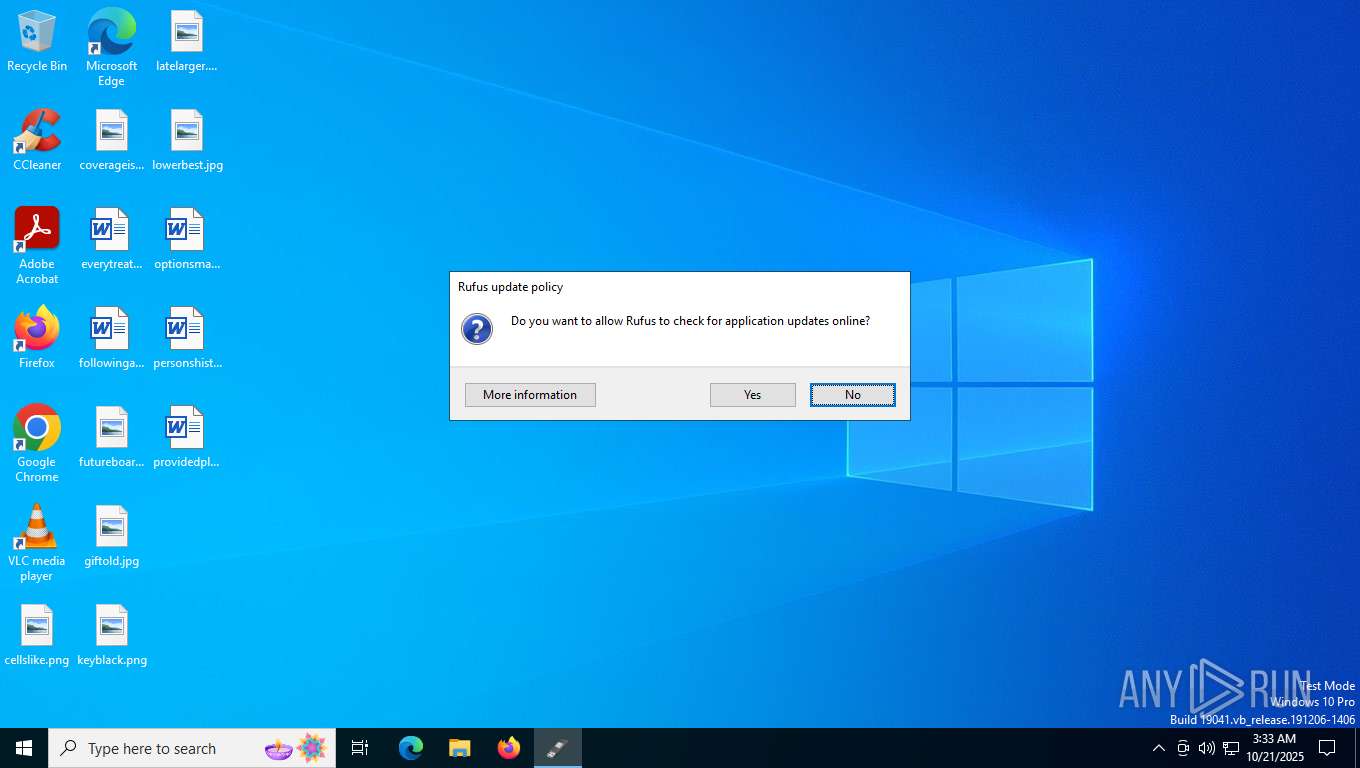
| 7728 | C:\Users\admin\AppData\Local\Temp\rufus-4.11p.exe | C:\Users\admin\AppData\Local\Temp\rufus-4.11p.exe | runas.exe | ||||||||||||
User: Administrator Company: Akeo Consulting Integrity Level: HIGH Description: Rufus Version: 4.11.2285 Modules
| |||||||||||||||
| 7780 | C:\WINDOWS\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Virtual Disk Service Loader Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7816 | C:\WINDOWS\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 289
Read events
6 047
Write events
200
Delete events
42
Modification events
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\AppHVSI |
| Operation: | write | Name: | AllowAppHVSI_ProviderSet |
Value: 0 | |||
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\EdgeUpdate |
| Operation: | write | Name: | UpdateDefault |
Value: 0 | |||
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\Windows\Network Connections |
| Operation: | write | Name: | NC_DoNotShowLocalOnlyIcon |
Value: 1 | |||
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | EnableSmartScreen |
Value: 0 | |||
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | **del.ShellSmartScreenLevel |
Value: | |||
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\Windows\Windows Feeds |
| Operation: | write | Name: | EnableFeeds |
Value: 0 | |||
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUStatusServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | UpdateServiceUrlAlternate |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (7728) rufus-4.11p.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{0EC4B7B6-1852-43FE-B291-F76C36876276}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | **del.FillEmptyContentUrls |
Value: | |||
Executable files
3
Suspicious files
18
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7728 | rufus-4.11p.exe | C:\Users\admin\AppData\Local\Temp\rufus.ini~ | text | |
MD5:25F951ACCB182500A1A135F7556724C3 | SHA256:DEE26225B0313E2A75B3A5B75C615E67C6C20617D50C5A0C17B2A425EAD98609 | |||
| 7728 | rufus-4.11p.exe | C:\Users\Administrator\AppData\Local\Temp\RufD028.tmp | text | |
MD5:727ED48003879D07D5CC9D0EE5F41ECF | SHA256:F63525DEE1D721CF2C766E964AA85A6C156B3EE5B434AAD01C8AADB40BB6AFB9 | |||
| 7728 | rufus-4.11p.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:1C2D4956F25997CEA7C091A6A4F8BEDF | SHA256:EA889DF210FF232993BD7791C23372E0F4AE0A9CD43DD27A1D91103BE40591C6 | |||
| 7728 | rufus-4.11p.exe | C:\Users\admin\AppData\Local\Temp\rufus.ini | text | |
MD5:25F951ACCB182500A1A135F7556724C3 | SHA256:DEE26225B0313E2A75B3A5B75C615E67C6C20617D50C5A0C17B2A425EAD98609 | |||
| 7728 | rufus-4.11p.exe | C:\Windows\System32\GroupPolicy\Machine\Registry.pol | binary | |
MD5:39E5BE35CC598F9086924A39E1105BF8 | SHA256:1C26BCB05CA50C85751D3023494D2E4D35F56D74451AC47880FD239F3B54F171 | |||
| 7728 | rufus-4.11p.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8CFF94A6502E24DC82E1FBEB7044EEA | binary | |
MD5:EB7D61D9C241E34B849716ADAD3C36AA | SHA256:8055F3D78D1A85186E586AC579414968CCBCB085F1416C656187D6FAE103D4ED | |||
| 7728 | rufus-4.11p.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D0E1C4B6144E7ECAB3F020E4A19EFC29_B5F77004C894173A10E3A199871D2D90 | binary | |
MD5:8DA3DB5060BFF432E607C133B6FF5CCC | SHA256:107875E453D4175E22C936173ACA0405DA1726A4855335461C7F94339B575844 | |||
| 7728 | rufus-4.11p.exe | C:\Users\admin\AppData\Local\Temp\Rufus\dbx_x64.bin | binary | |
MD5:C612F3405FE89A07062007D7B01D4186 | SHA256:74DF077175DCA7FF8BCD27CE8285656E38097803F803E2D124467273699E4B17 | |||
| 7728 | rufus-4.11p.exe | C:\Users\admin\AppData\Local\Temp\Rufus\dbx_ia32.bin | binary | |
MD5:A49C6C49A19FD0627348936CA324E2AD | SHA256:DFE6C4EEF0473C8972C0C88DFEB723867CEBDEF081B8A1CF34289F885293A9CB | |||
| 7728 | rufus-4.11p.exe | C:\Users\Administrator\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:417E1515ABB2C4C688717634BF70377C | SHA256:2787067D45E7D1BFD4C464584BF72760DBE43CB8CB2D19A64B5045FBA69679D1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
43
DNS requests
25
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7088 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7728 | rufus-4.11p.exe | GET | 200 | 104.18.21.213:80 | http://r13.c.lencr.org/19.crl | unknown | — | — | whitelisted |
7728 | rufus-4.11p.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7728 | rufus-4.11p.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
3616 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3616 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7352 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5256 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7728 | rufus-4.11p.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
7728 | rufus-4.11p.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CECoW9cIBGAf3CpJj3Tw5qfI%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5488 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7016 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2276 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2276 | svchost.exe | 224.0.0.251:5353 | — | — | — | whitelisted |
5488 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7088 | SearchApp.exe | 92.123.104.34:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7088 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
api.github.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
rufus-4.11p.exe | *** Rufus init ***
|
rufus-4.11p.exe | Usr dir: 'C:\Users\Administrator'
|
rufus-4.11p.exe | Tmp dir: 'C:\Users\ADMINI~1\AppData\Local\Temp\'
|
rufus-4.11p.exe | App dir: 'C:\Users\admin\AppData\Local\Temp\'
|
rufus-4.11p.exe | Sys dir: 'C:\WINDOWS\system32'
|
rufus-4.11p.exe | Dat dir: 'C:\Users\Administrator\AppData\Local'
|
rufus-4.11p.exe | Cur dir: 'C:\Windows\System32\'
|
rufus-4.11p.exe | Will use settings from INI file
|
rufus-4.11p.exe | Binary executable is signed by 'Akeo Consulting'
|
rufus-4.11p.exe | localization: extracted data to 'C:\Users\ADMINI~1\AppData\Local\Temp\RufD028.tmp'
|