| File name: | e88dc637081ff17bf215018595faa974a1cab72e |
| Full analysis: | https://app.any.run/tasks/a900b8c4-a5ba-4068-9d84-984054275cda |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 03:05:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Author: 1, Template: Normal, Last Saved By: 1, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Jul 28 13:30:00 2015, Last Saved Time/Date: Tue Jul 28 13:30:00 2015, Number of Pages: 1, Number of Words: 0, Number of Characters: 0, Security: 0 |
| MD5: | E14B93846E305BC9A52C31198B67E721 |
| SHA1: | E88DC637081FF17BF215018595FAA974A1CAB72E |
| SHA256: | ABB83C8DD0E62919946DE688FD81051162791DB1FEC1184B3217A14606D83F4C |
| SSDEEP: | 768:V2xuV67cqupXxwcRpQ4HzfHUgwDfH781mzcyE7dz:UxWGSew+0zfH4b7eb7l |
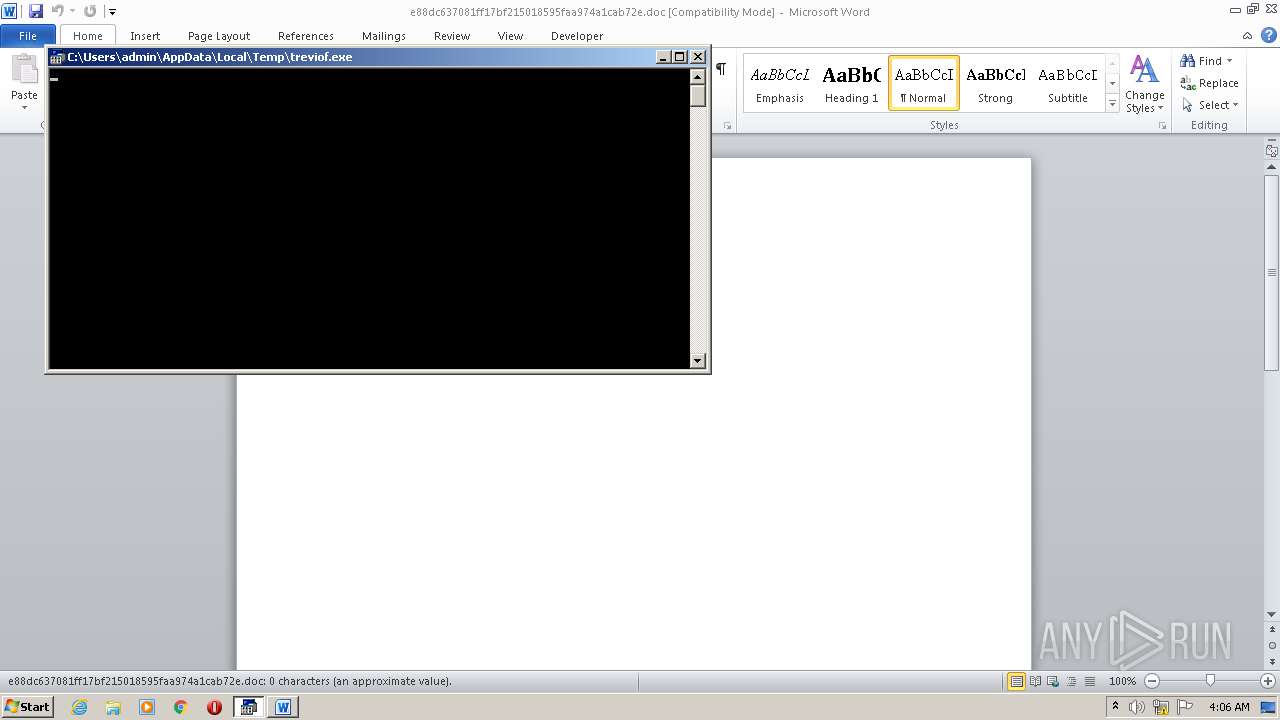
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2084)
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2084)
SUSPICIOUS
Executes application which crashes
- WINWORD.EXE (PID: 2084)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2084)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 2084)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | 1 |
| Keywords: | - |
| Template: | Normal |
| LastModifiedBy: | 1 |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2015:07:28 12:30:00 |
| ModifyDate: | 2015:07:28 12:30:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | Home |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | - |
| AppVersion: | 11.9999 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | ???????? Microsoft Office Word |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2084 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\e88dc637081ff17bf215018595faa974a1cab72e.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3208 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 553
Read events
895
Write events
533
Delete events
125
Modification events
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %97 |
Value: 2539370024080000010000000000000000000000 | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4105.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3208 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs4A8B.tmp | — | |
MD5:— | SHA256:— | |||
| 3208 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs4A8C.tmp | — | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$8dc637081ff17bf215018595faa974a1cab72e.doc | pgc | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\treviof.exe | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2084 | WINWORD.EXE | GET | 404 | 178.32.213.120:80 | http://laperleblanche.fr/345/wrw.exe | FR | html | 963 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2084 | WINWORD.EXE | 178.32.213.120:80 | laperleblanche.fr | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
laperleblanche.fr |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2084 | WINWORD.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |