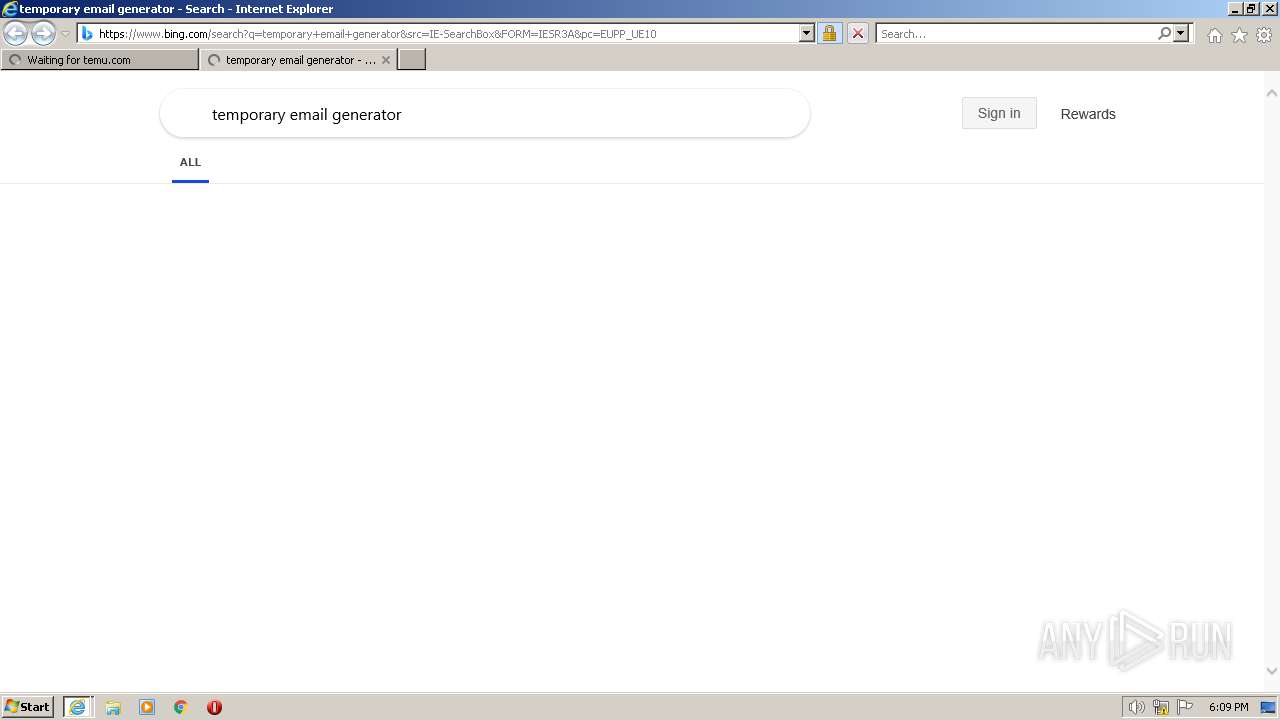
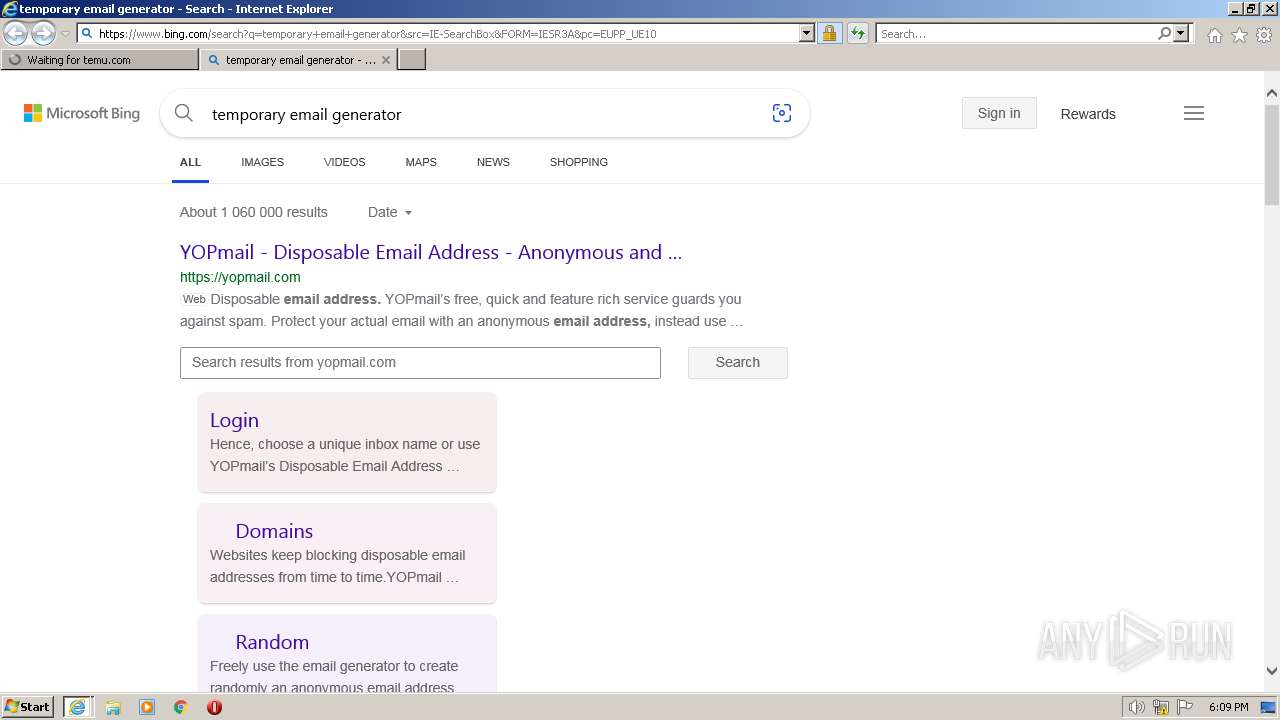
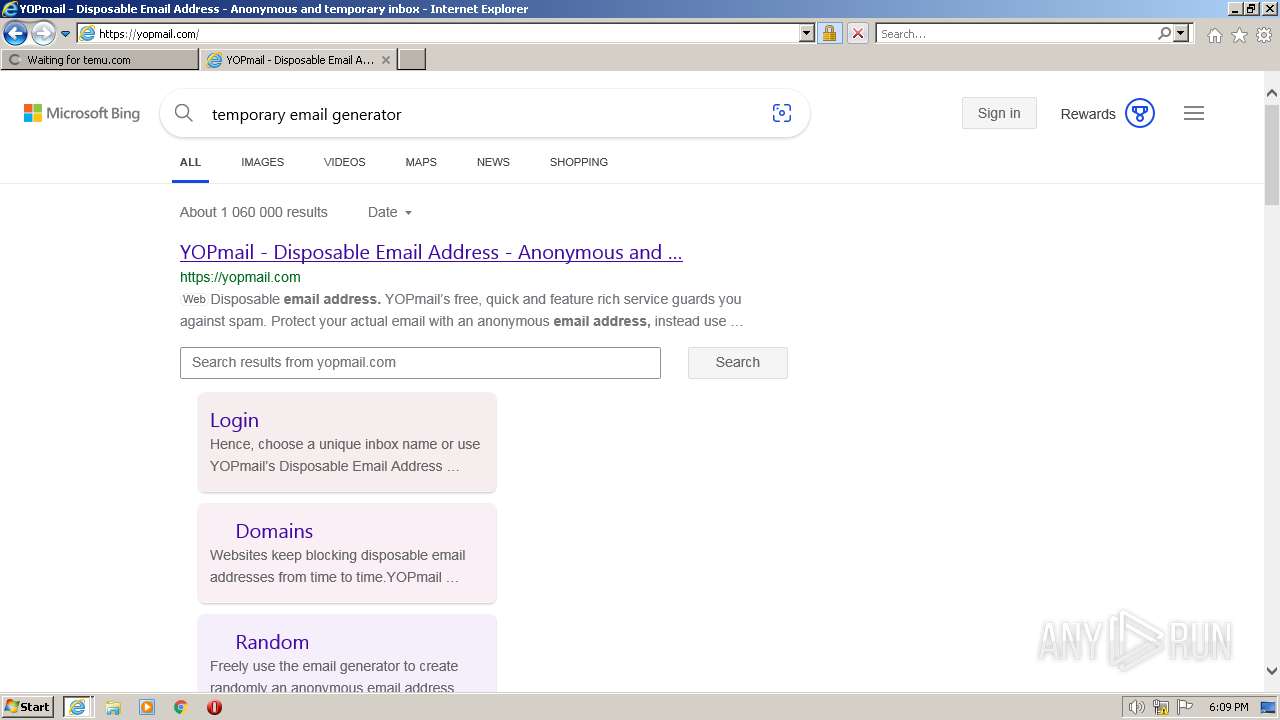
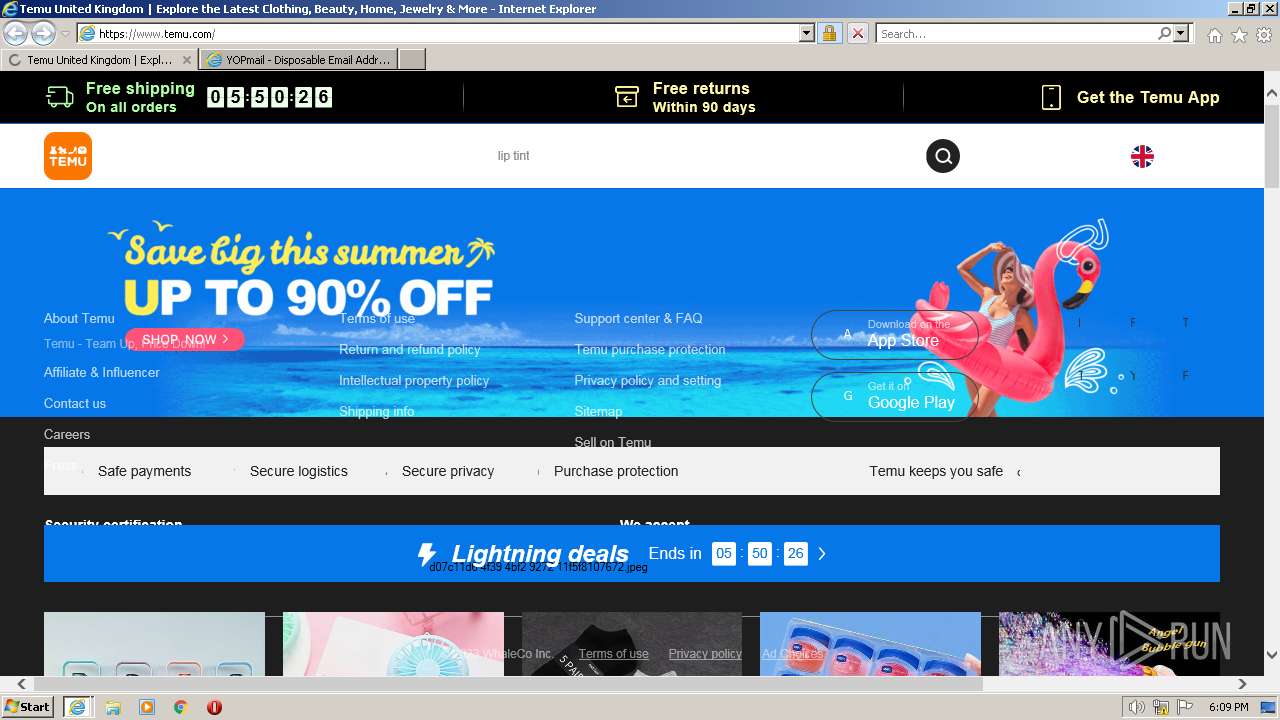
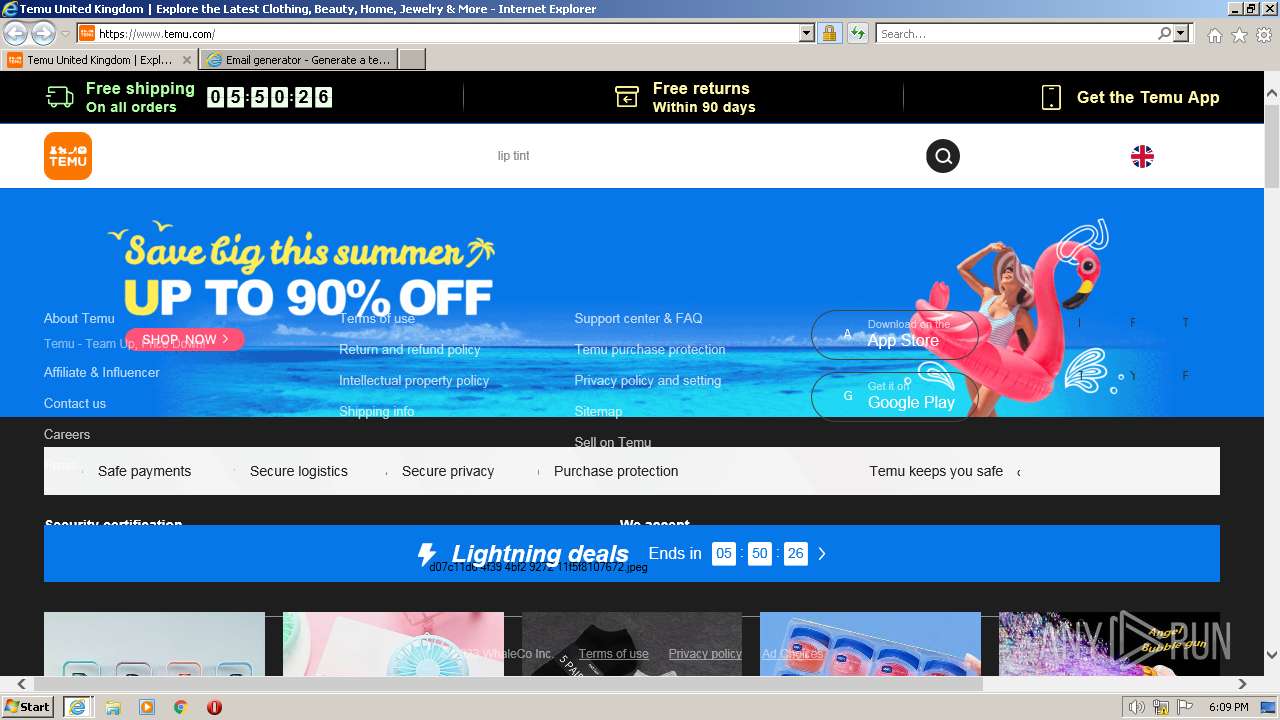
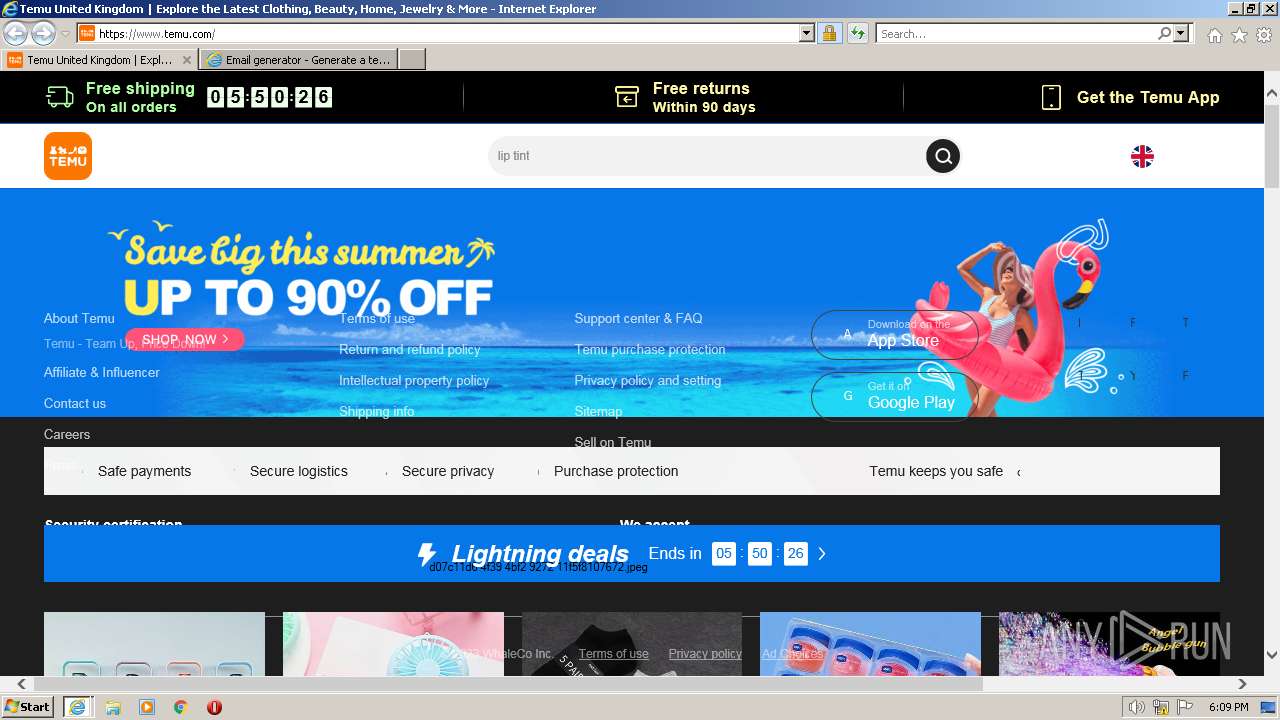
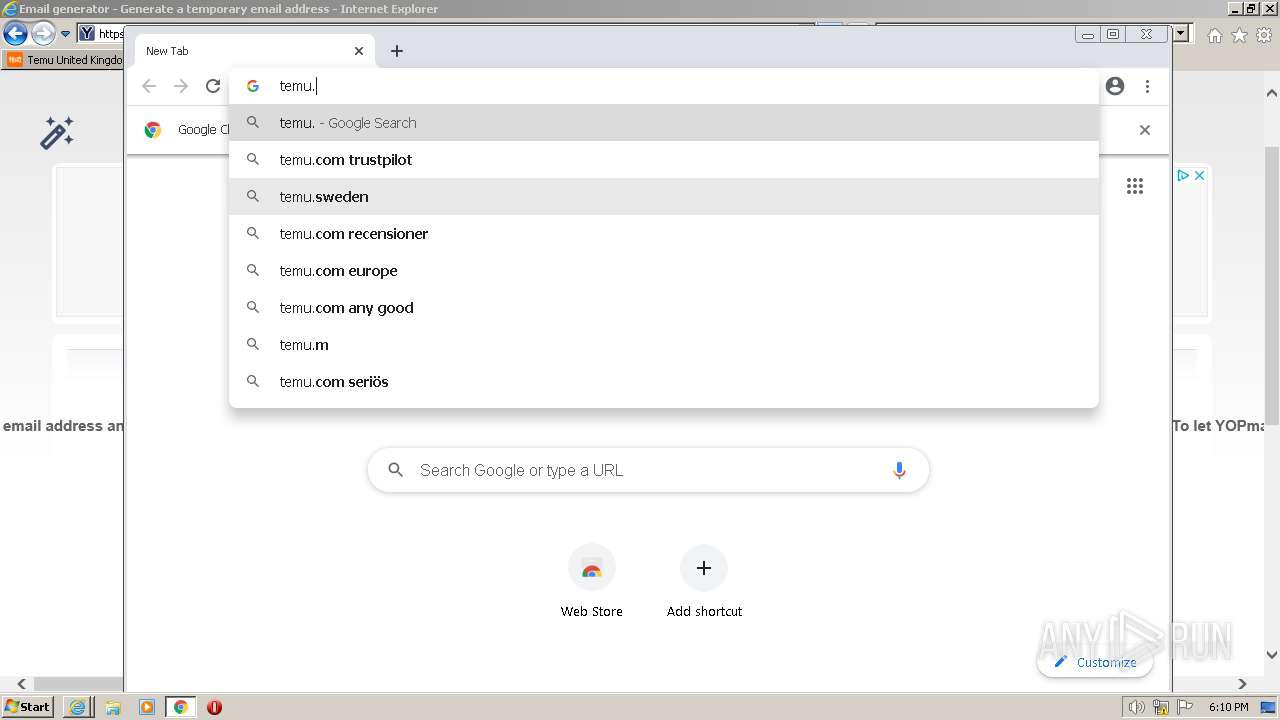
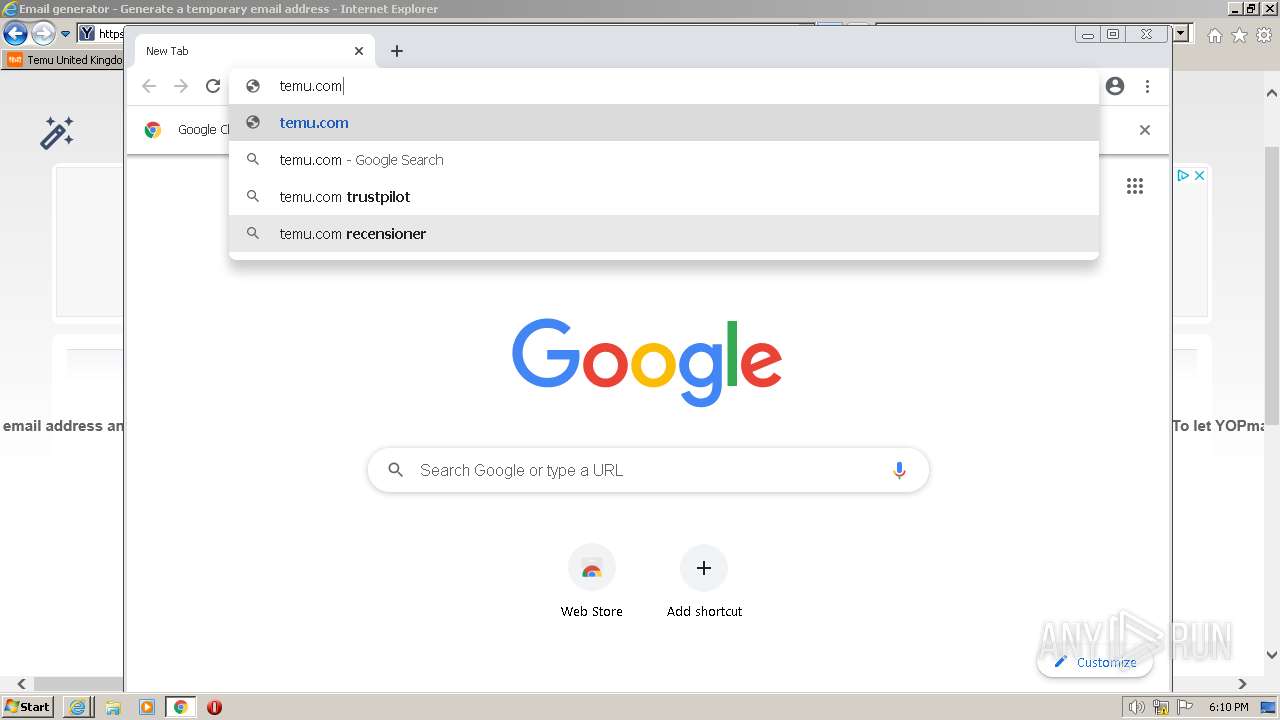
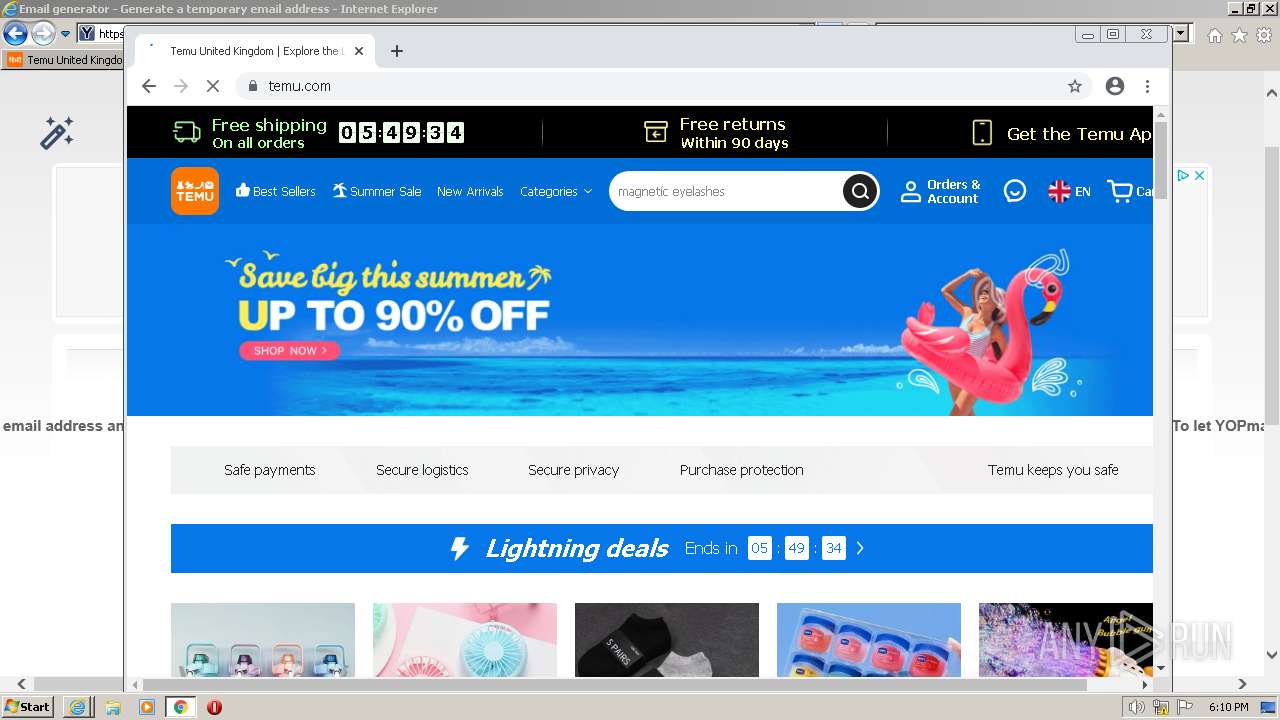
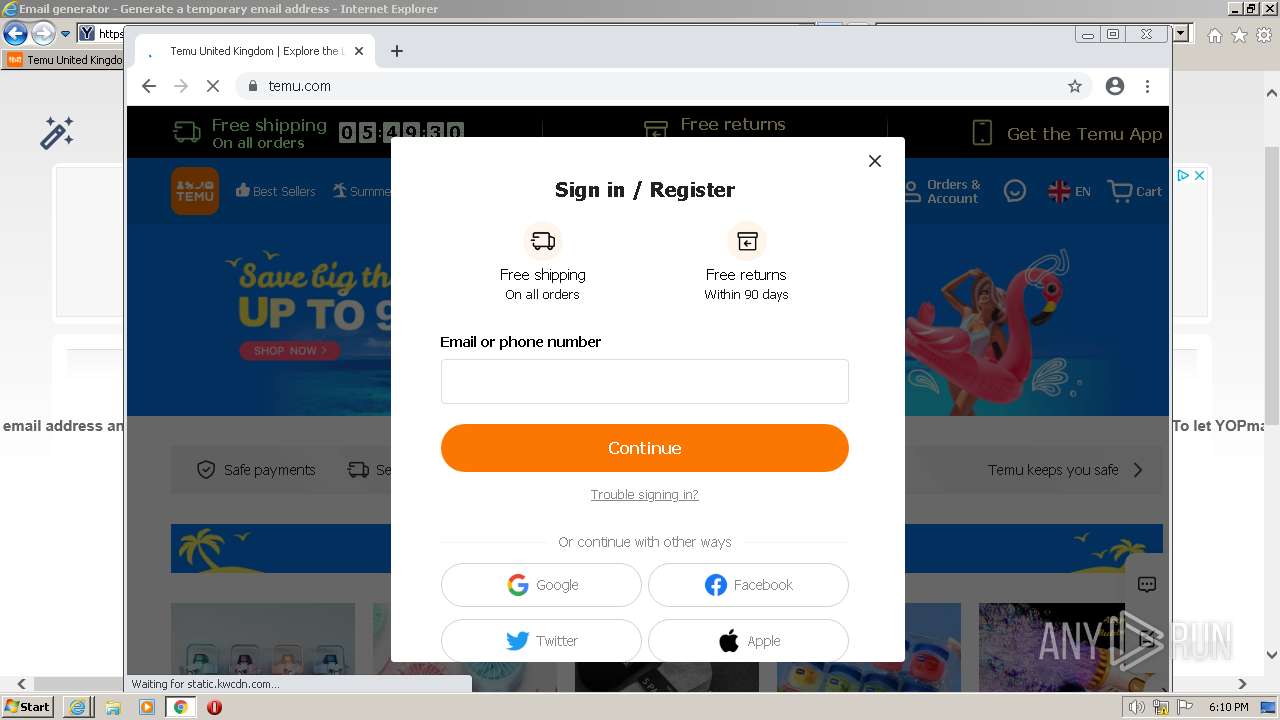
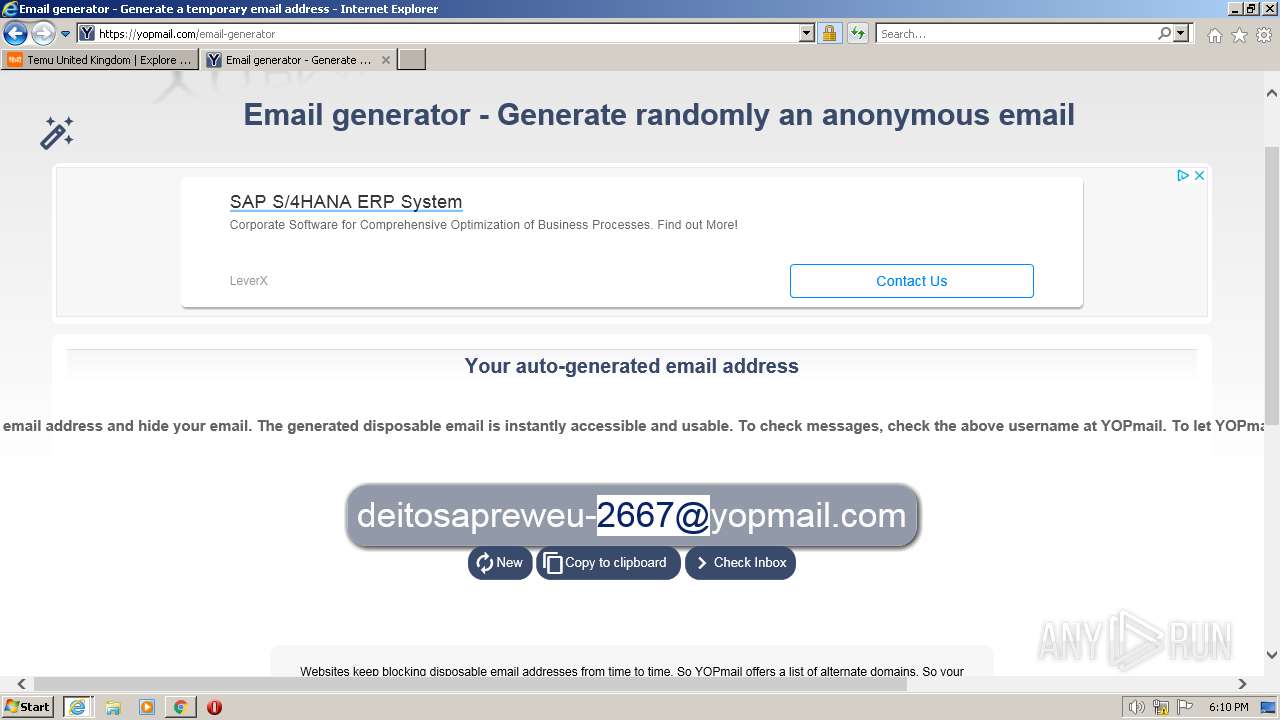
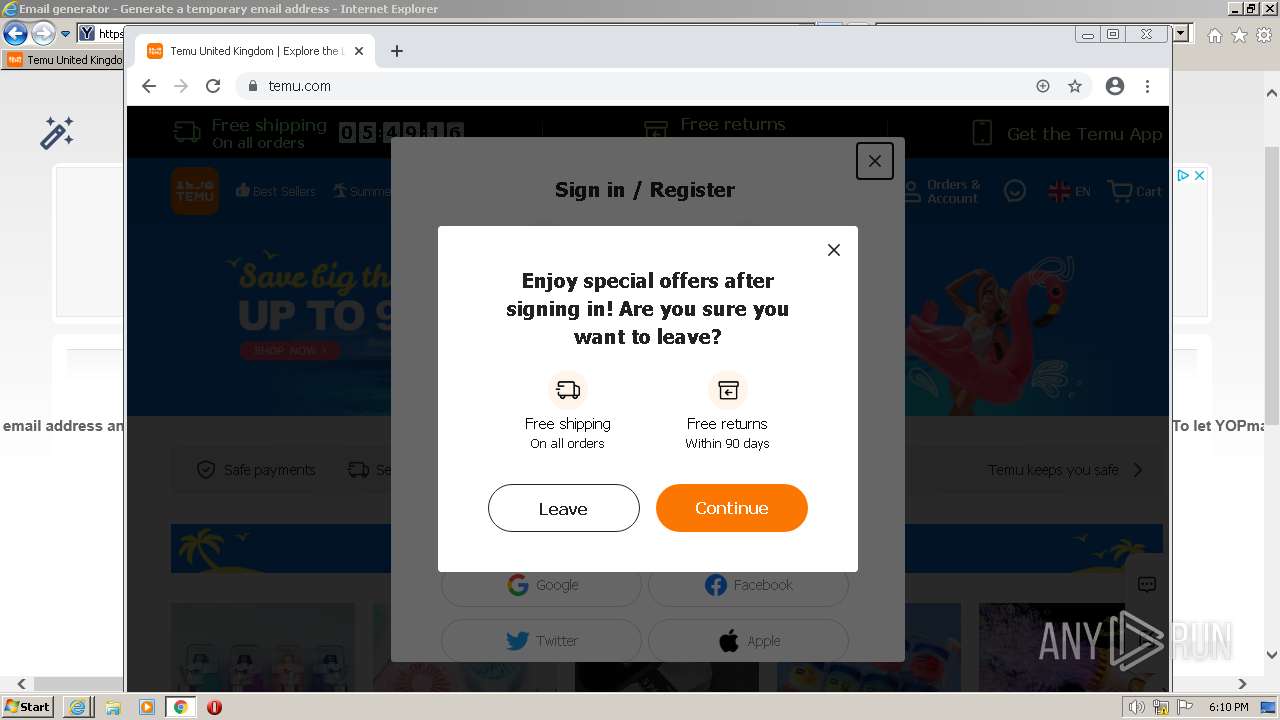
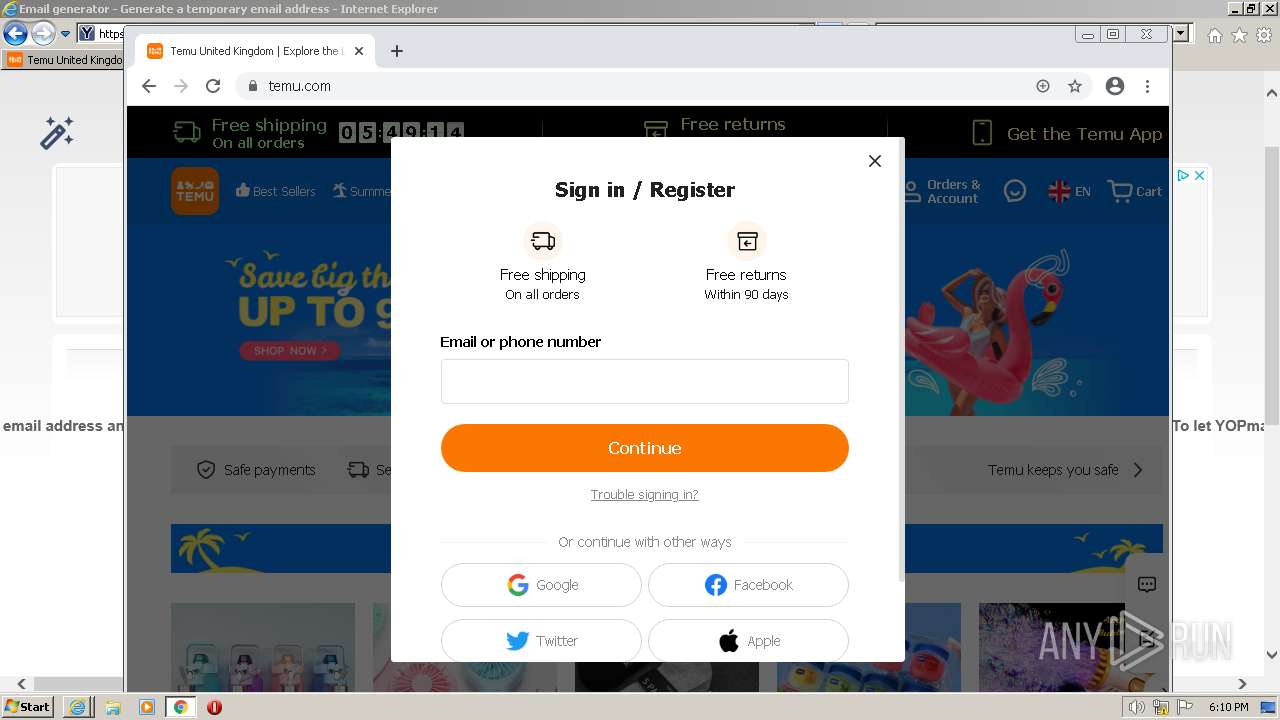
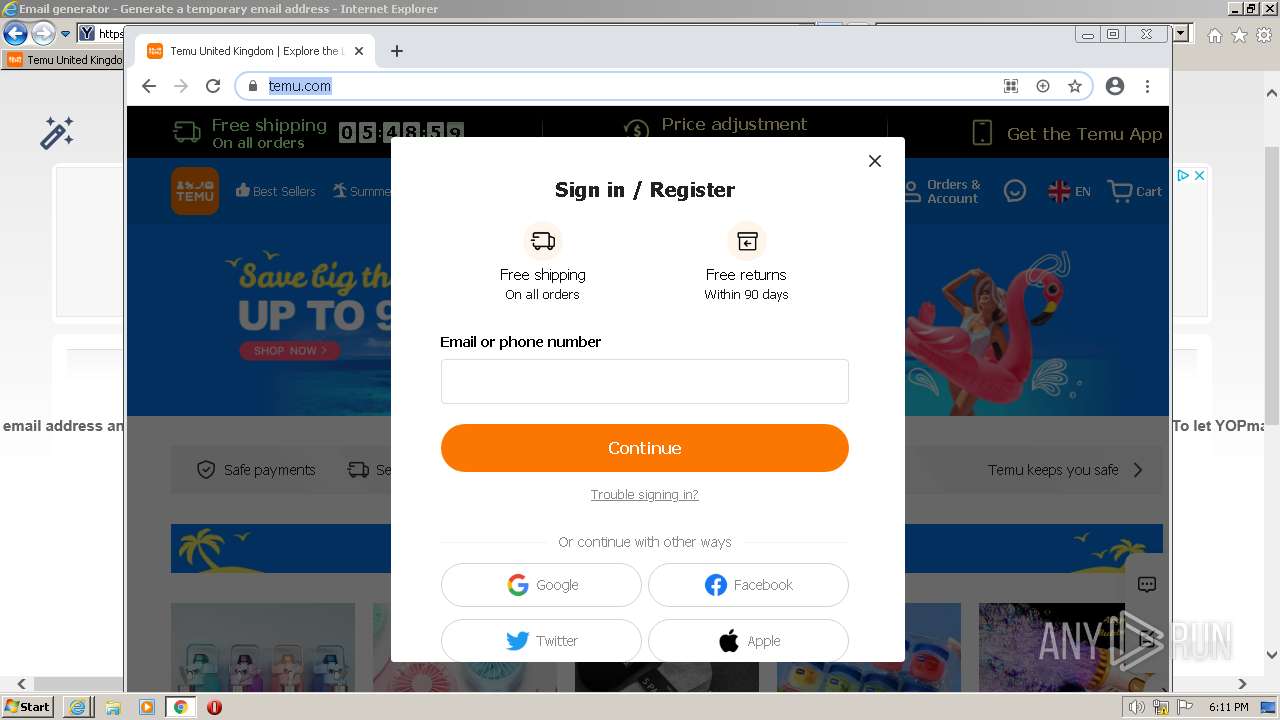
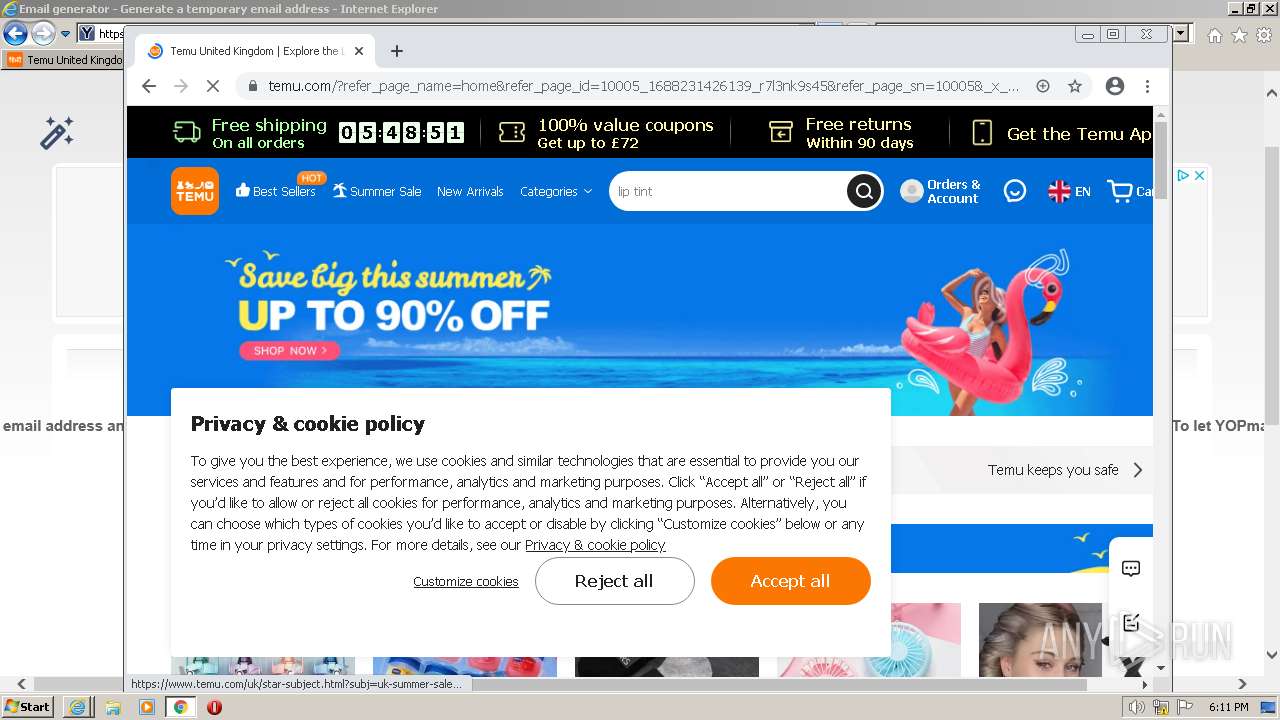
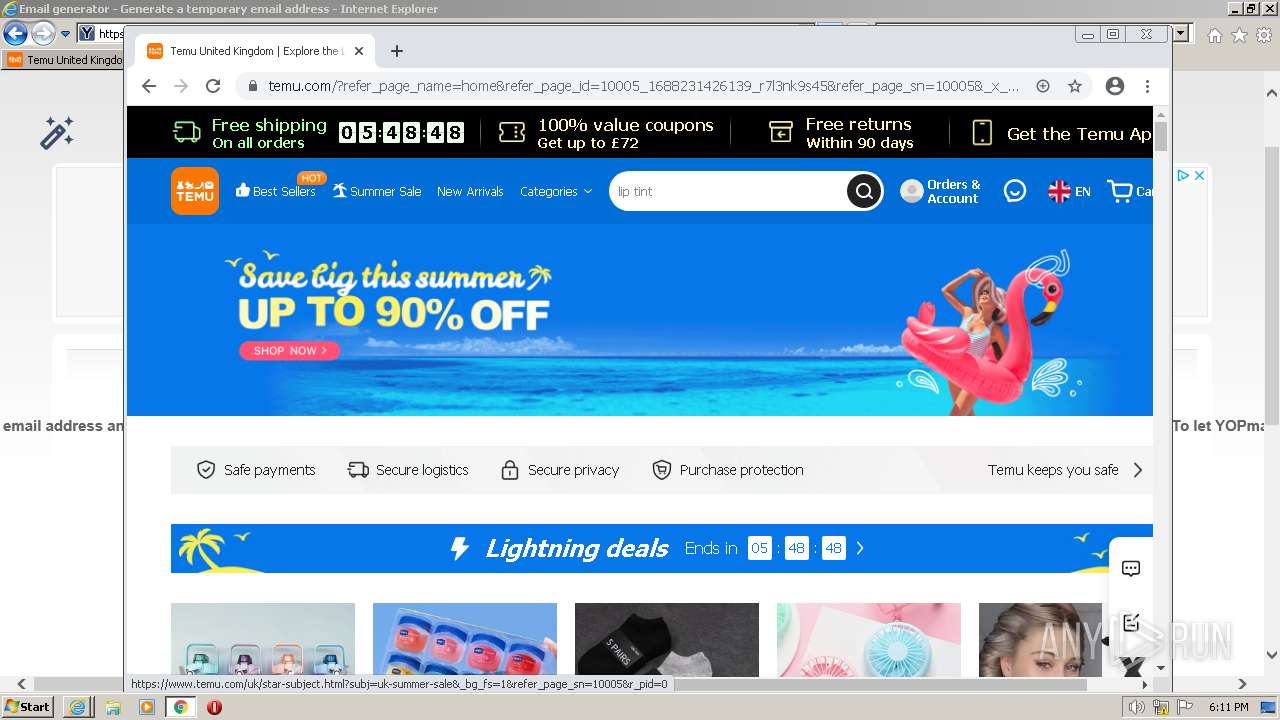
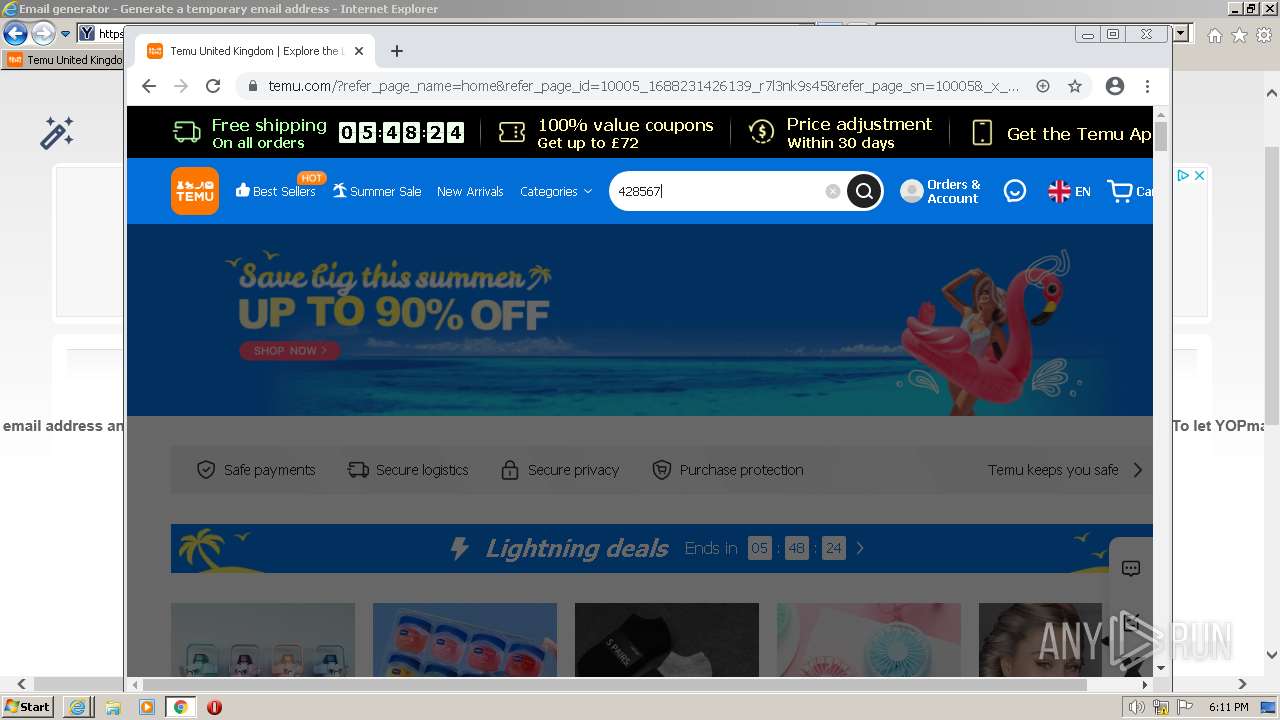
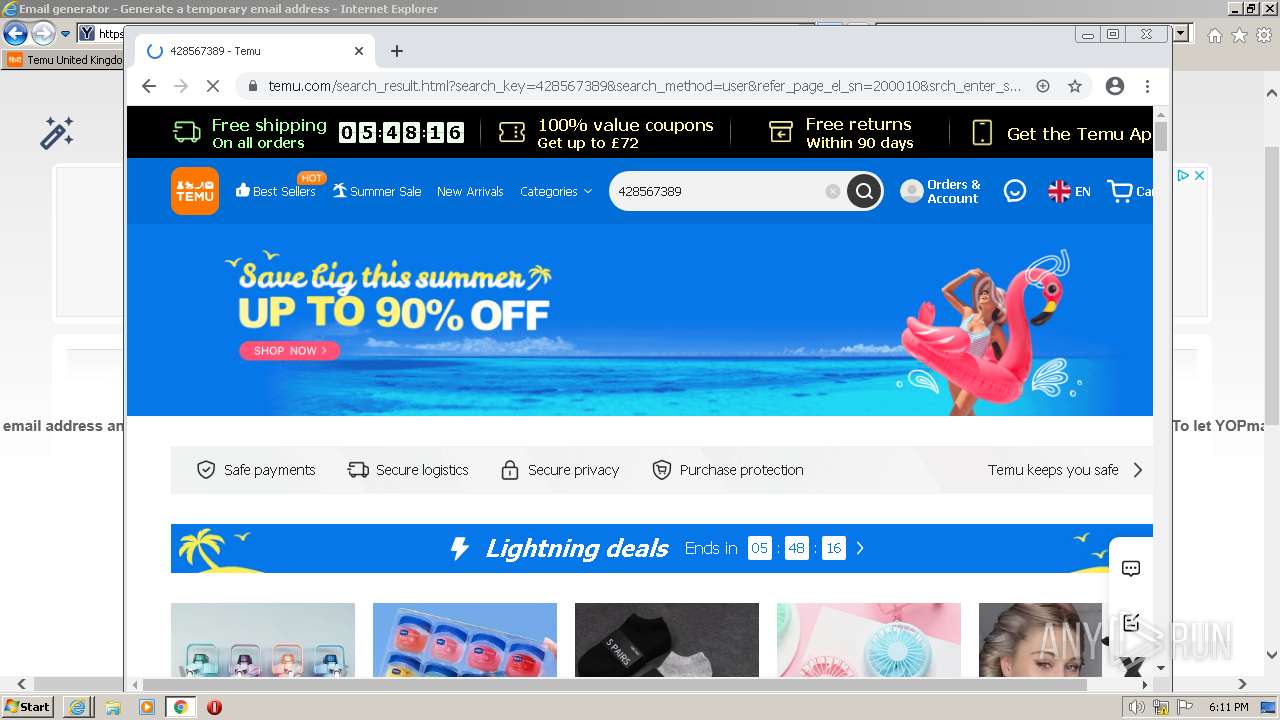
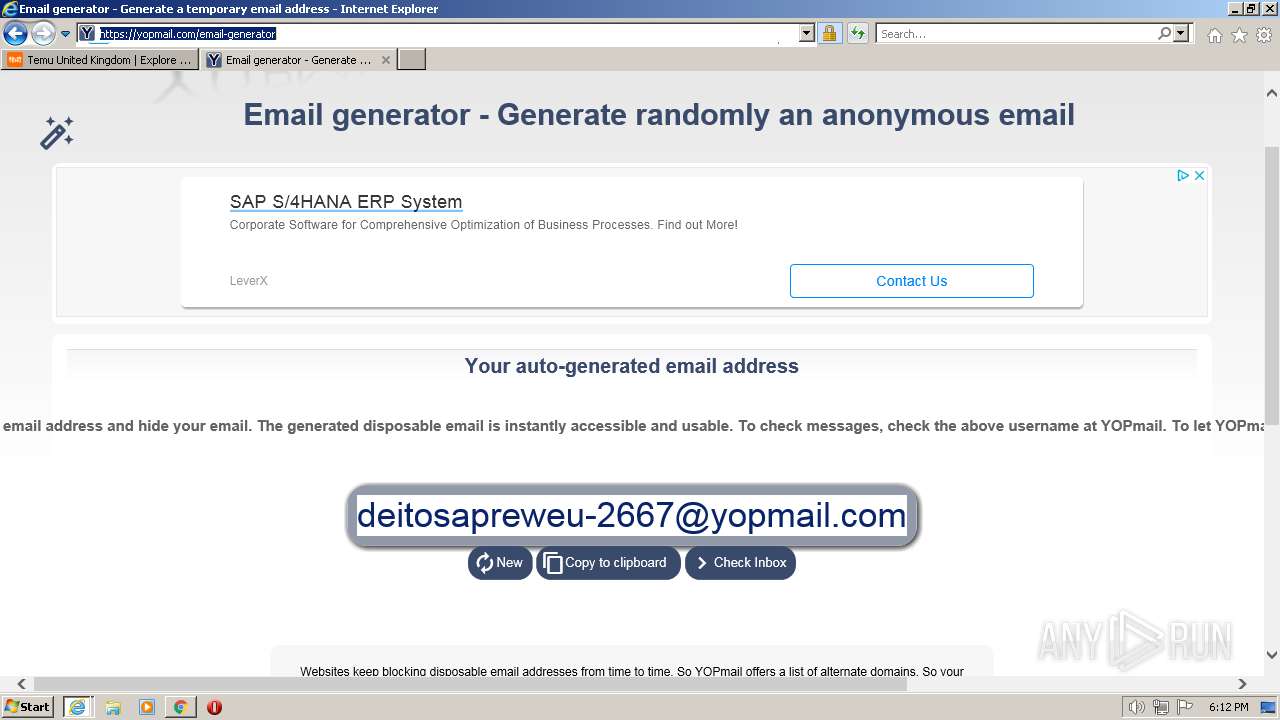
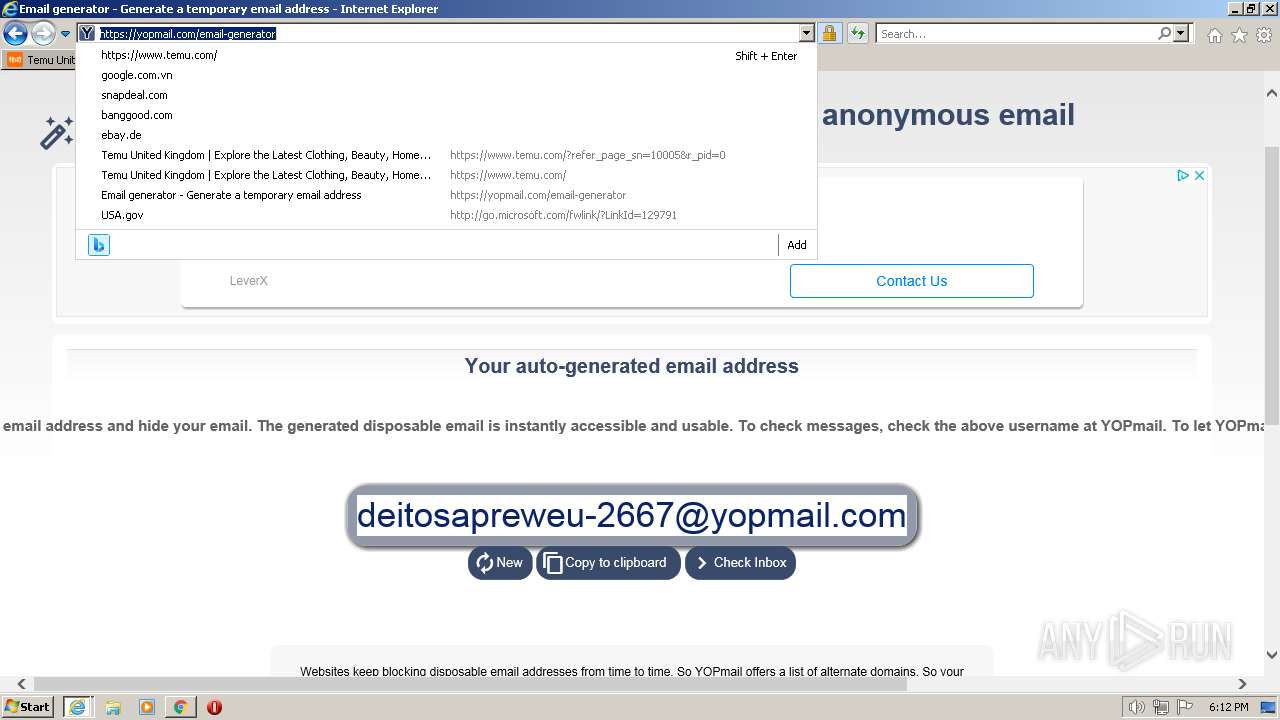
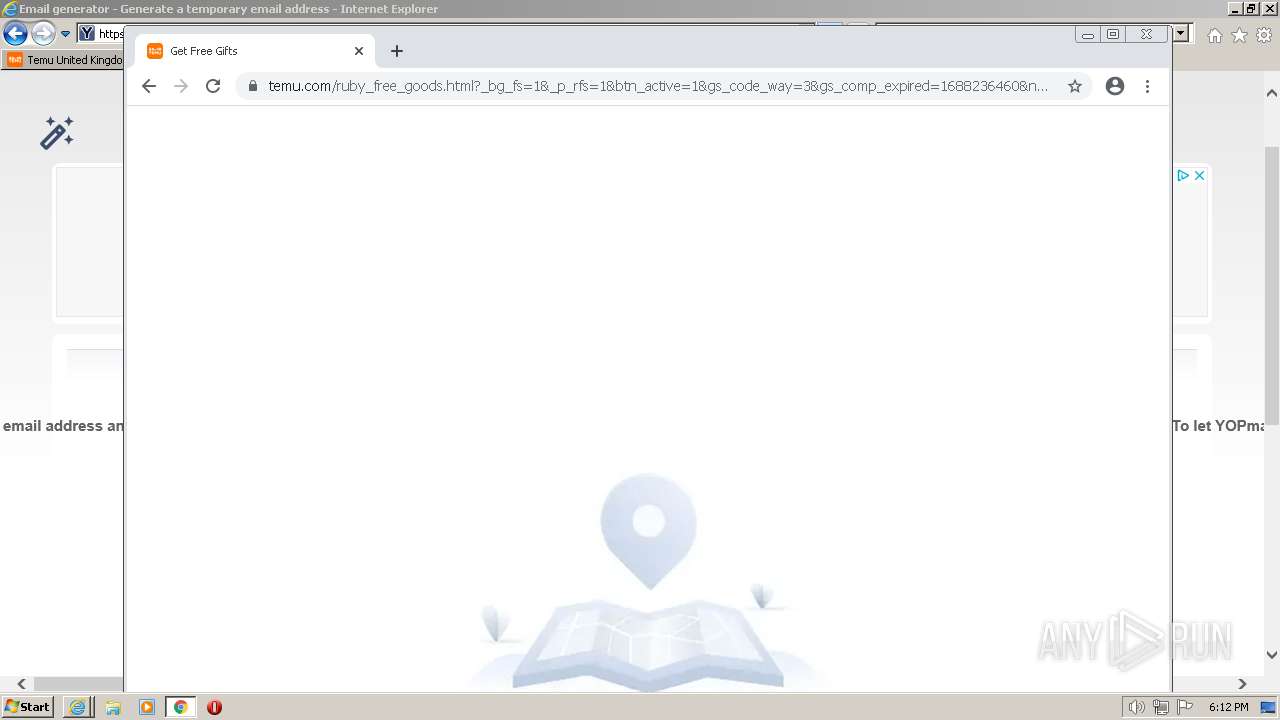
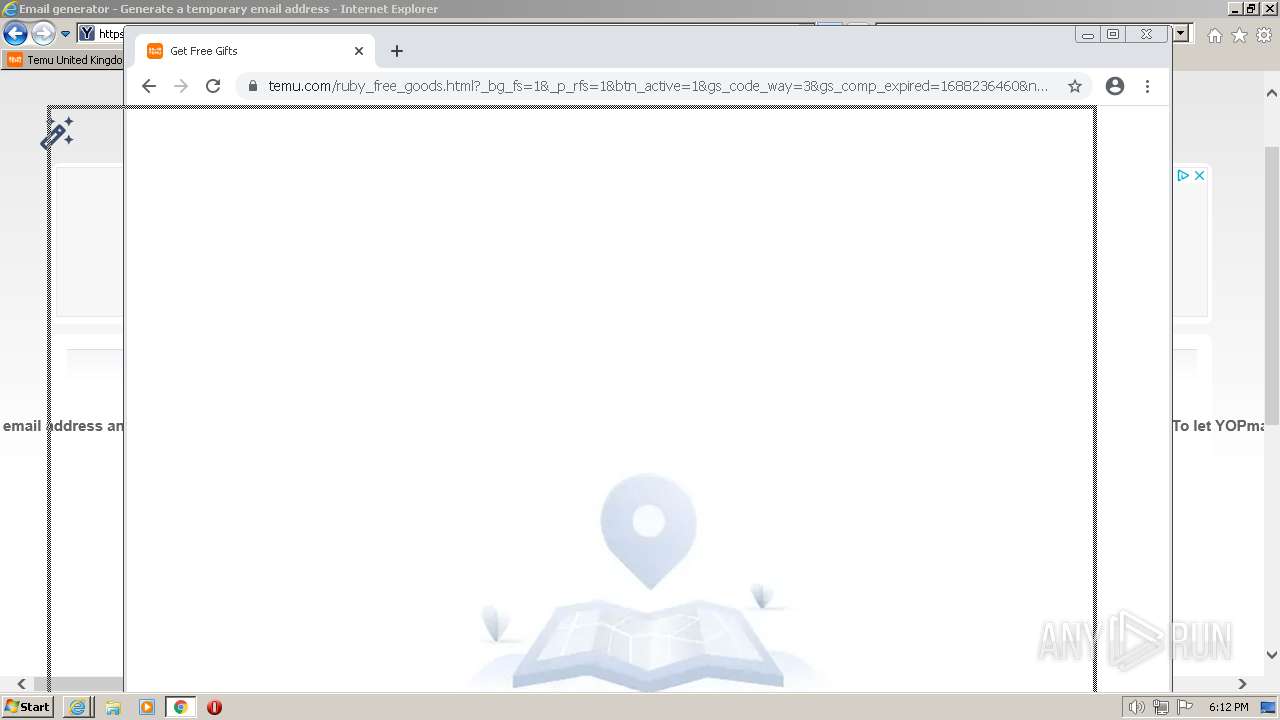
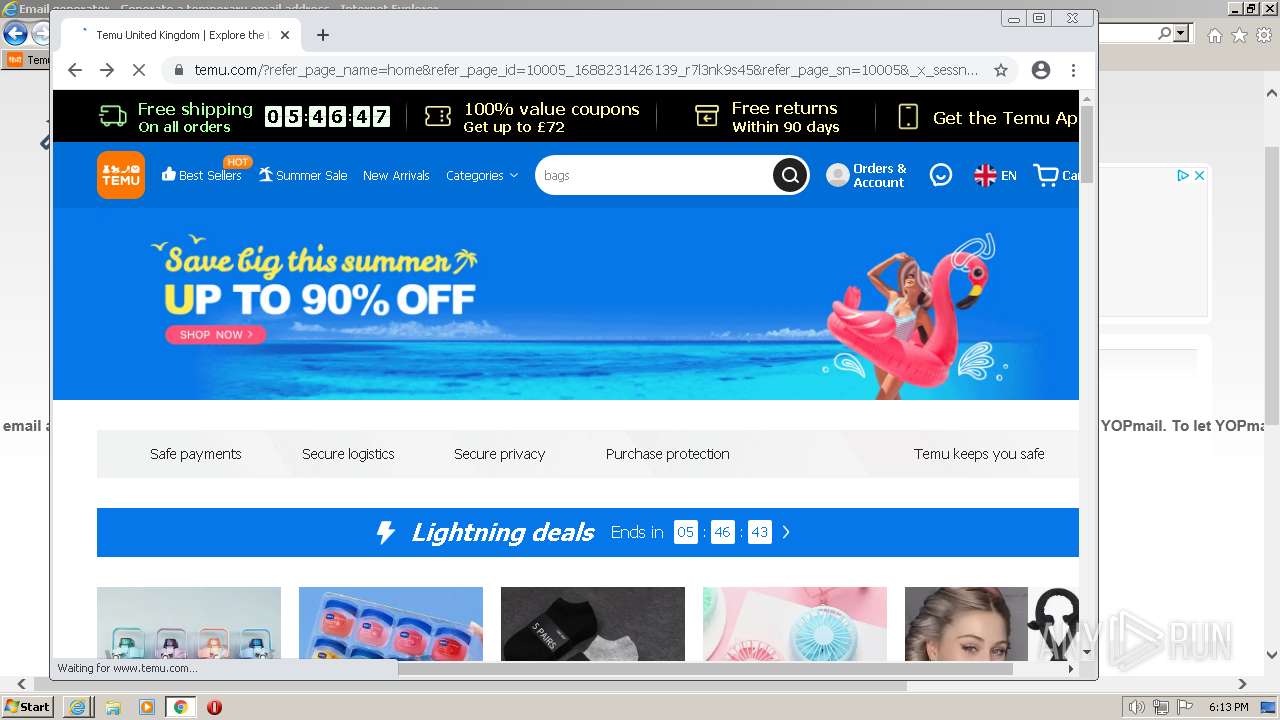
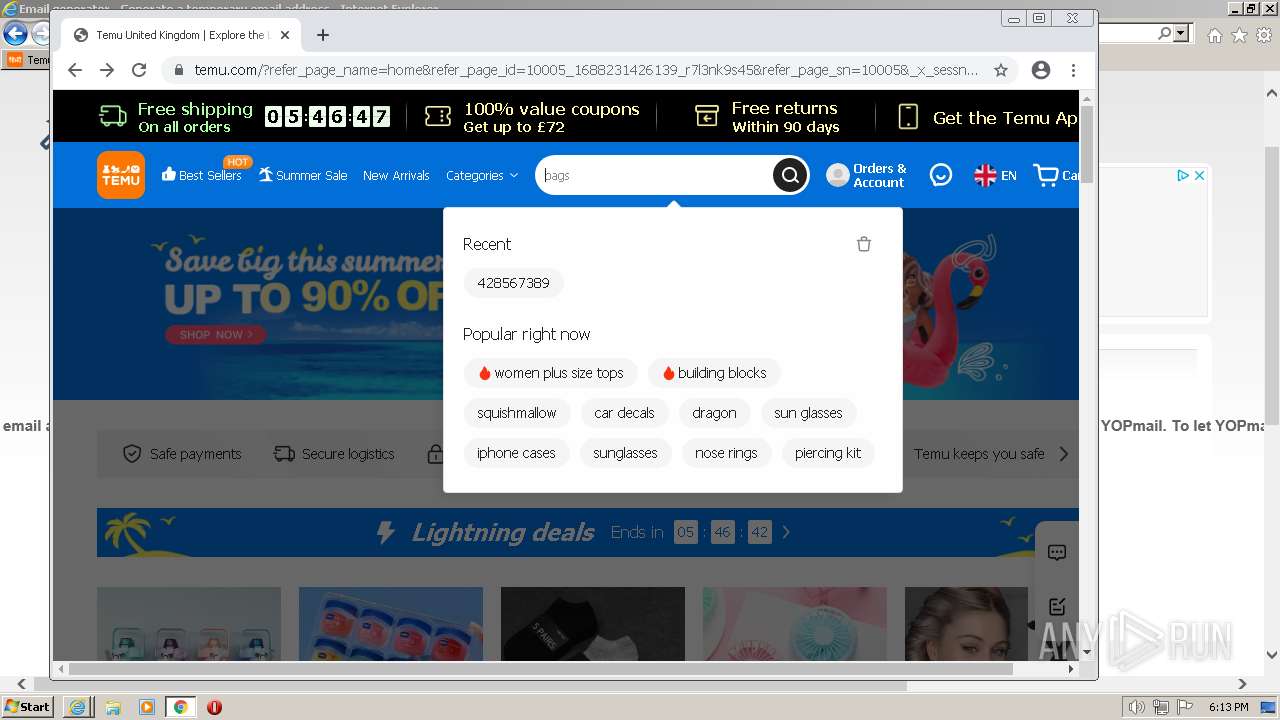
| URL: | https://temu.com |
| Full analysis: | https://app.any.run/tasks/d1ea8b79-8067-4135-b7b3-15931a092d5b |
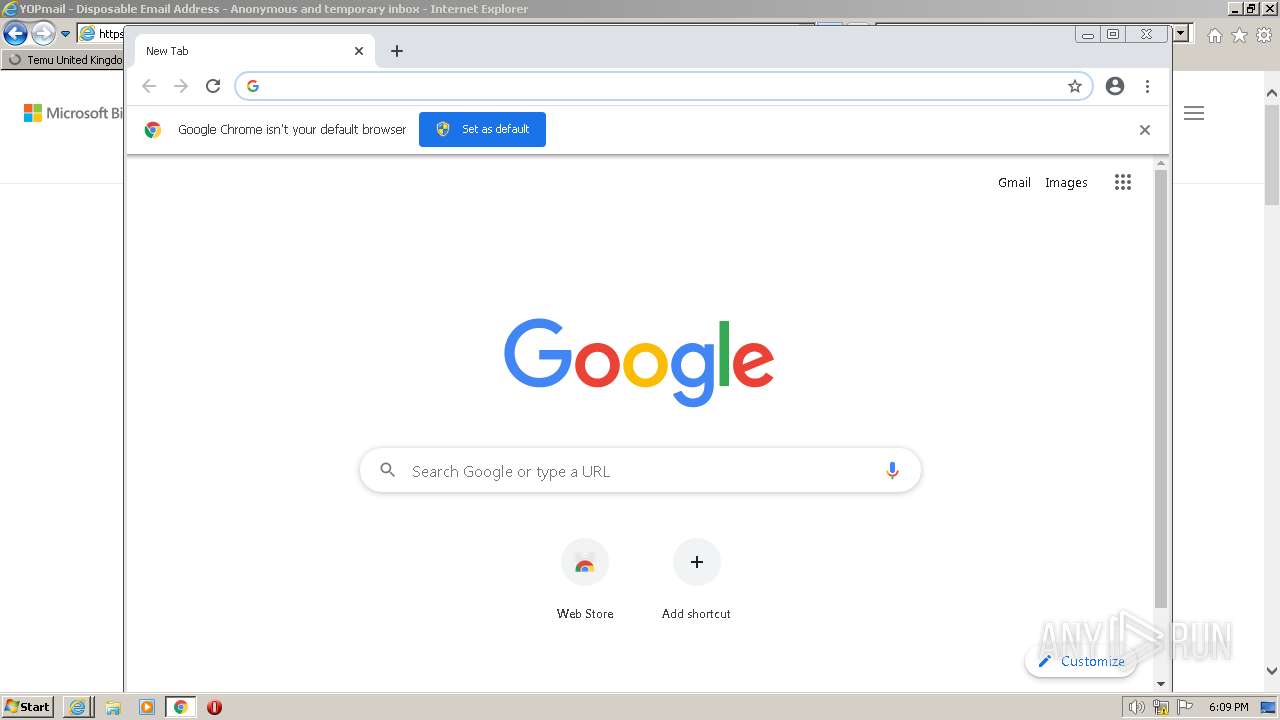
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2023, 17:08:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BF606A96F1BD848C04EA4120AF70971A |
| SHA1: | 17A3E9201A2C298E47CECFE9EC142050FA4E2266 |
| SHA256: | ABB55E8DFE4273038FCFC695F82FC2CD34B4D1D10C97F35437D8A63CE3A49E1C |
| SSDEEP: | 3:N8II:2II |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
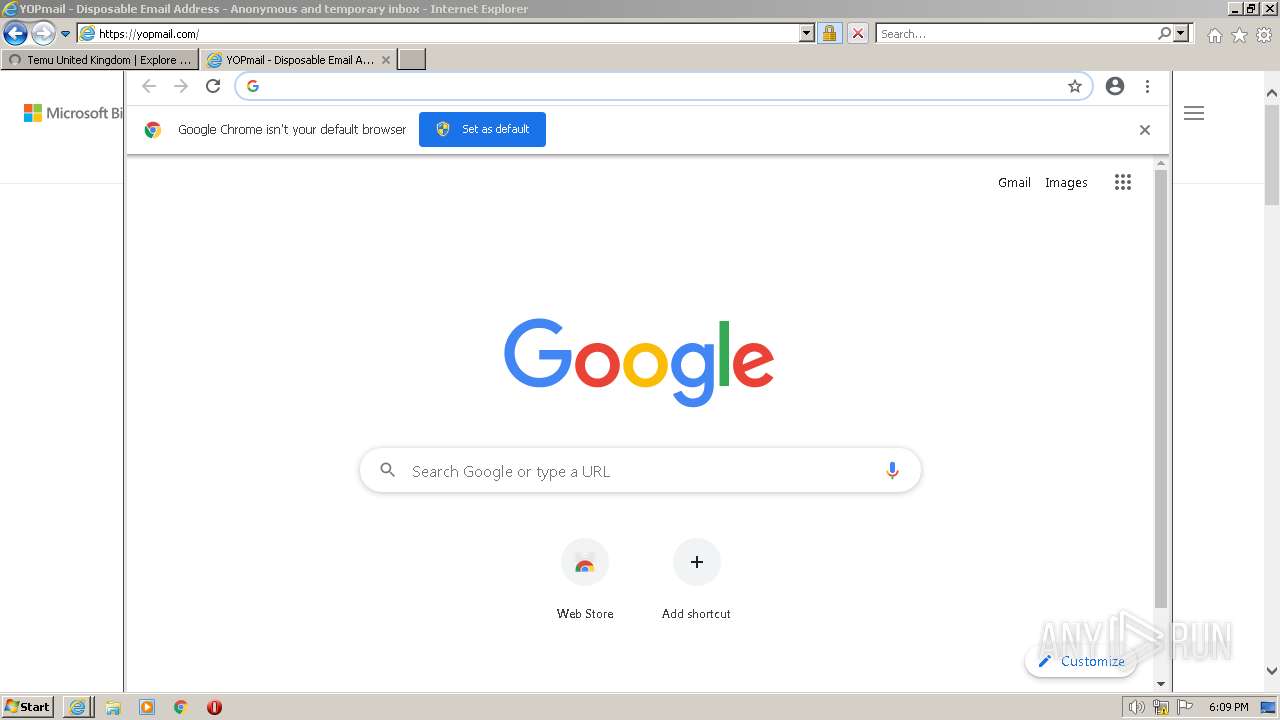
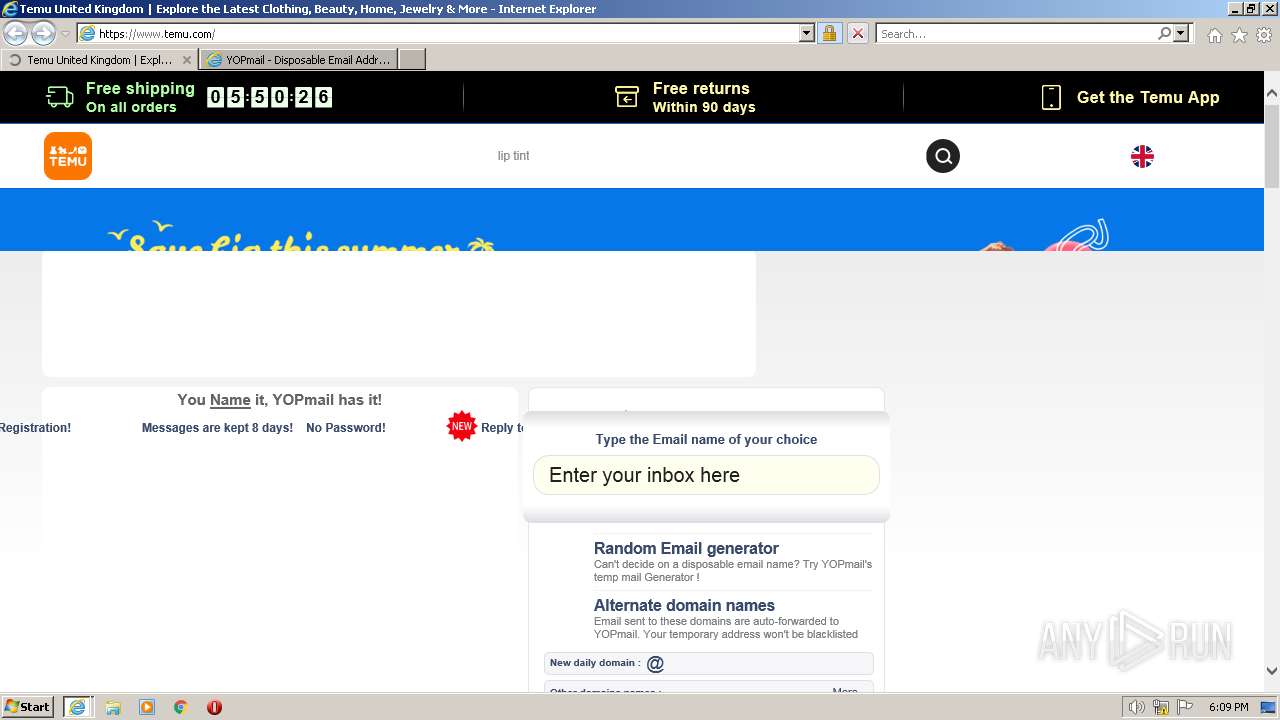
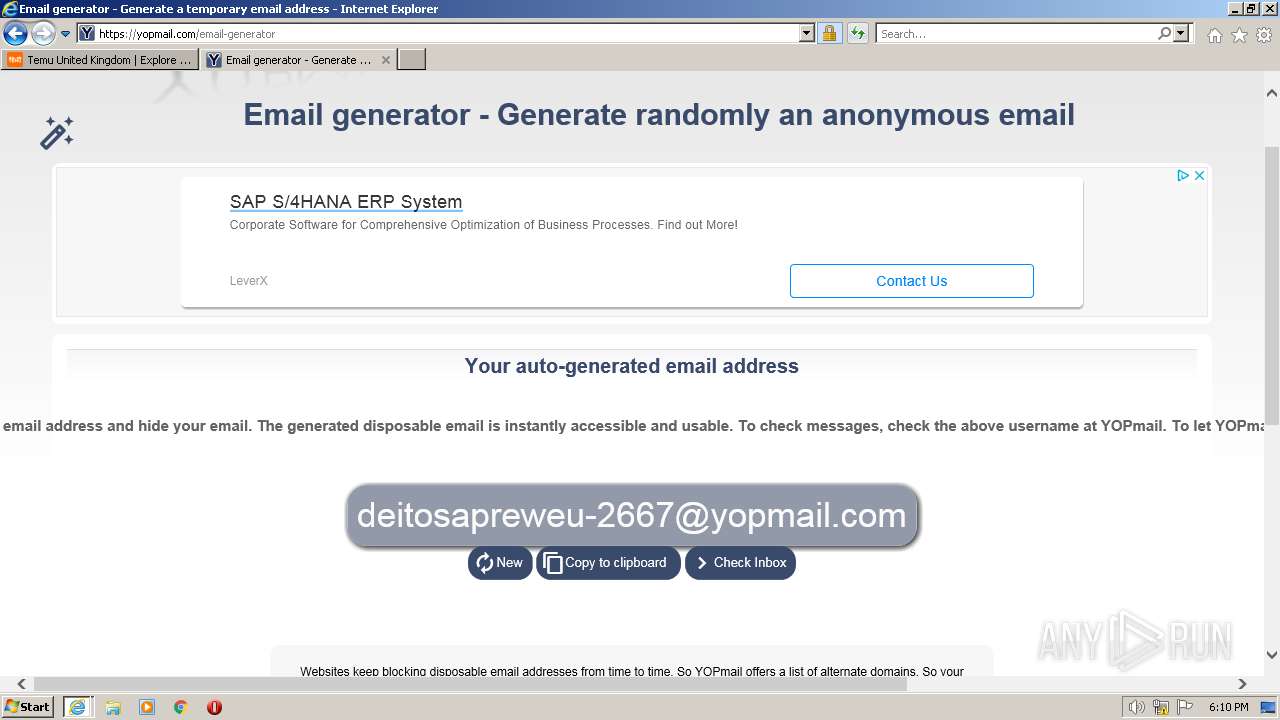
Application launched itself
- iexplore.exe (PID: 3412)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 2536)
Manual execution by a user
- wmpnscfg.exe (PID: 116)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 2892)
Reads the computer name
- wmpnscfg.exe (PID: 116)
The process checks LSA protection
- wmpnscfg.exe (PID: 116)
Checks supported languages
- wmpnscfg.exe (PID: 116)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 116)
Executable content was dropped or overwritten
- chrome.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
99
Monitored processes
60
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1012,393269115991737611,15509244588512101534,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2336 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17941125879834321791,16156503024701485633,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1012,393269115991737611,15509244588512101534,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17941125879834321791,16156503024701485633,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,393269115991737611,15509244588512101534,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17941125879834321791,16156503024701485633,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1012,393269115991737611,15509244588512101534,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1012,393269115991737611,15509244588512101534,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3692 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x69aed988,0x69aed998,0x69aed9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
33 229
Read events
32 828
Write events
386
Delete events
15
Modification events
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
12
Suspicious files
416
Text files
566
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
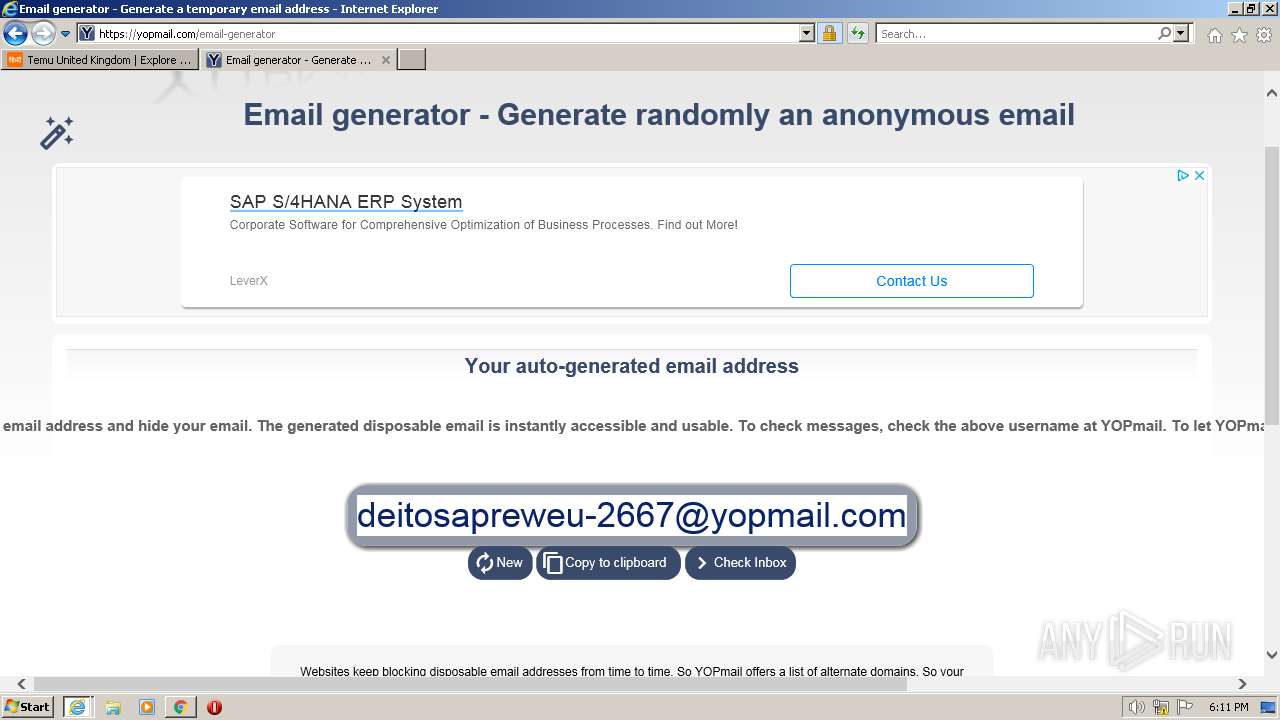
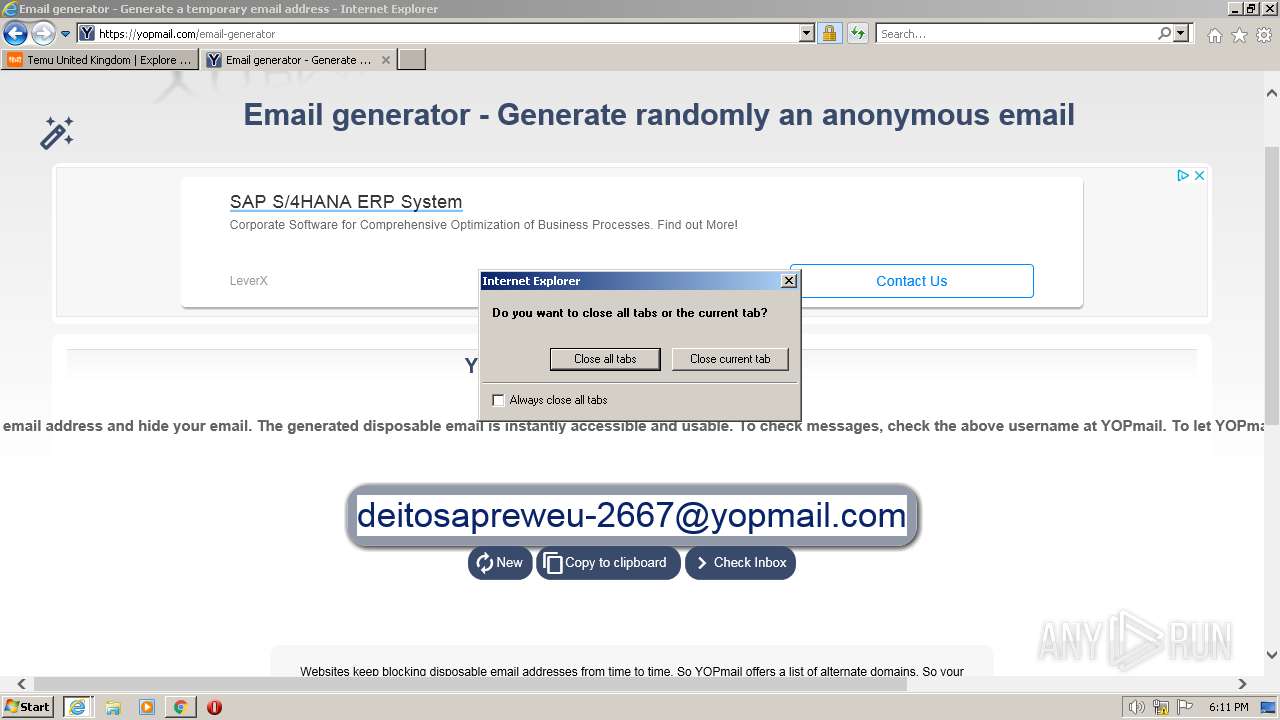
| 2872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\S6B804TD.txt | text | |
MD5:383B007E9720DC9B4BE9A71ABBC27B55 | SHA256:77C1F246E852238F1F006694EBD8F81A1144590C60AADD9A81A71E4D65F064E3 | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3BCCB80F6B1913069C8A715C062775EB | SHA256:3967D9E08882751366252E512F00D22BEA7541C0C01B7380CFC1498EEBA02999 | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].xml | xml | |
MD5:58DD6C3AB71512637C5AA43B1F345481 | SHA256:061B34A712A9B6156E0A5A2EE0E6D08BFCCD5E81E70383AB269C956061282483 | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:DEDC2749F4C0CC7912D2BC2880479332 | SHA256:5B2B8E28AFF36E863C1C959623B31D37E49FD2C956800F220F273D7DD45778E7 | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[1].htm | xml | |
MD5:B696CF195418DDEEBCEF0ED4363E2FF4 | SHA256:9755CB916CA70556500D09FD041DCEC472427868358BA2CF22E6569F82EA2443 | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:3A6DECBA1623A47B78FF1AD7EAF5C837 | SHA256:98DD7FAA8E84D6803E40492942288472463DEB81A5E99ECA9E7B1F4F12A8EFFA | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\qsml[1].xml | xml | |
MD5:B696CF195418DDEEBCEF0ED4363E2FF4 | SHA256:9755CB916CA70556500D09FD041DCEC472427868358BA2CF22E6569F82EA2443 | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6Q0H1CH3.txt | text | |
MD5:0902531601AFCC06556537F6F9698CB8 | SHA256:0D0D9EB11806AEB1DCFB91A05525C83933CBB04E4DC71110E127DBCC7B7B7D4A | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\VWQCO6AG.txt | text | |
MD5:B874B228AB066720C16876F4EF66BCC6 | SHA256:1F3B3EB474F17CA149F00626EC12BBE134284961BC01E32020E8CF787A16082D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
328
DNS requests
108
Threats
506
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3412 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2872 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://crl.godaddy.com/gdig2s1-4377.crl | US | binary | 65.2 Kb | whitelisted |
3412 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
2780 | iexplore.exe | GET | 200 | 23.201.254.55:80 | http://x1.c.lencr.org/ | CH | der | 717 b | whitelisted |
2780 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECyP1HvZSJrzEIqeU6yEBFk%3D | US | der | 471 b | whitelisted |
2780 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC7ovYBEye4sBKjzD2eimWd | US | der | 472 b | whitelisted |
2780 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHFqGvcZW4luEC%2Bj74dtJbY%3D | US | der | 471 b | whitelisted |
2872 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 2.01 Kb | whitelisted |
2780 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2780 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2872 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | SUCURI-SEC | US | suspicious |
2872 | iexplore.exe | 13.107.5.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2872 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2872 | iexplore.exe | 20.223.39.110:443 | www.temu.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2872 | iexplore.exe | 20.15.0.25:443 | temu.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2872 | iexplore.exe | 192.124.249.36:80 | ocsp.godaddy.com | SUCURI-SEC | US | suspicious |
2780 | iexplore.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
2780 | iexplore.exe | 20.190.160.22:443 | login.microsoftonline.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2780 | iexplore.exe | 2.23.209.187:443 | r.bing.com | Akamai International B.V. | GB | suspicious |
2780 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.godaddy.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
www.temu.com |
| unknown |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
744 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |