| File name: | twkey.exe |
| Full analysis: | https://app.any.run/tasks/c4d89361-d80c-41d0-b138-895496e84dc3 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 08:17:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 865D5559D03C80992AE680381539DE6C |
| SHA1: | FB3C4FBD3F46274B944972D0795A4F75B9E05742 |
| SHA256: | ABB06D4DCB2B4887065613FBB09F23A9D6AE47E4513C5501582B83A4B3DE562C |
| SSDEEP: | 98304:dFUm0aO3Dbz/zgaP5jzUpw9gCpodFd/8WEwBYPDt10UpgrE:dGH3Dbz/8elUS9fp+v/kDQUpyE |
MALICIOUS
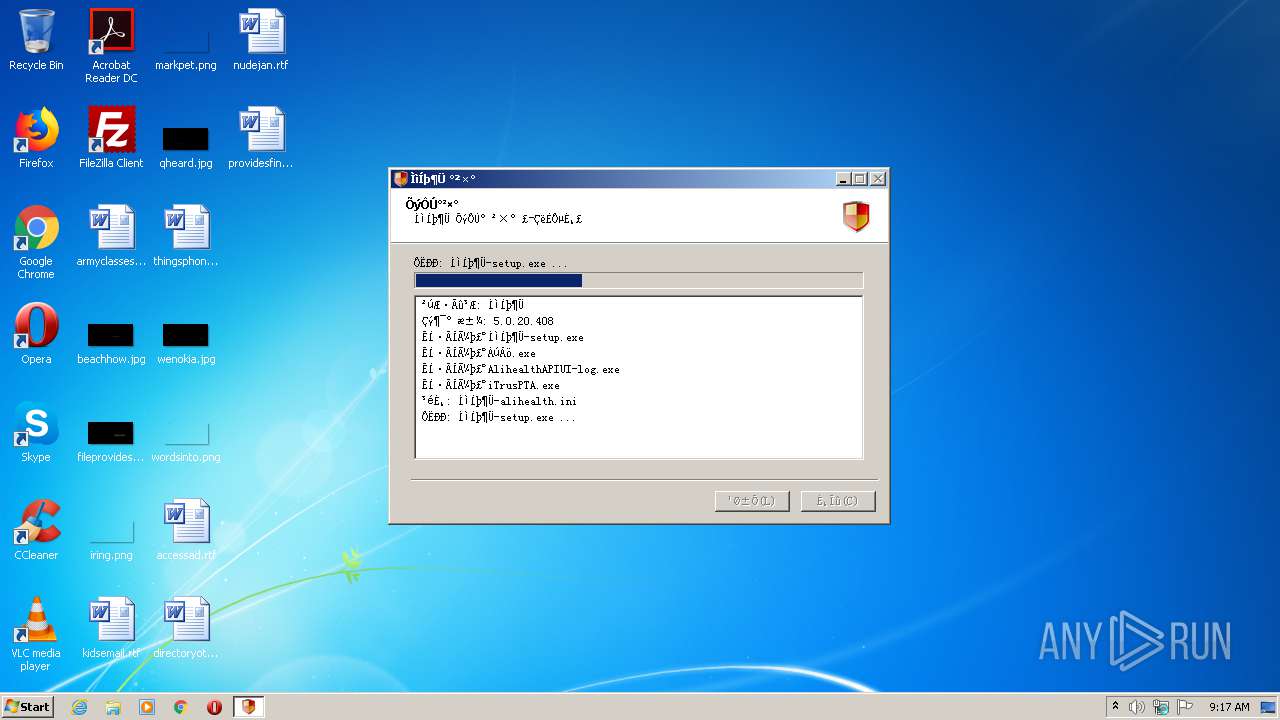
Loads dropped or rewritten executable
- twkey.exe (PID: 3468)
- ÌìÍþ¶Ü-setup.exe (PID: 2660)
- AlihealthAPIUI-log.exe (PID: 1492)
- ÁúÂö.exe (PID: 3484)
- iTrusPTA.exe (PID: 3764)
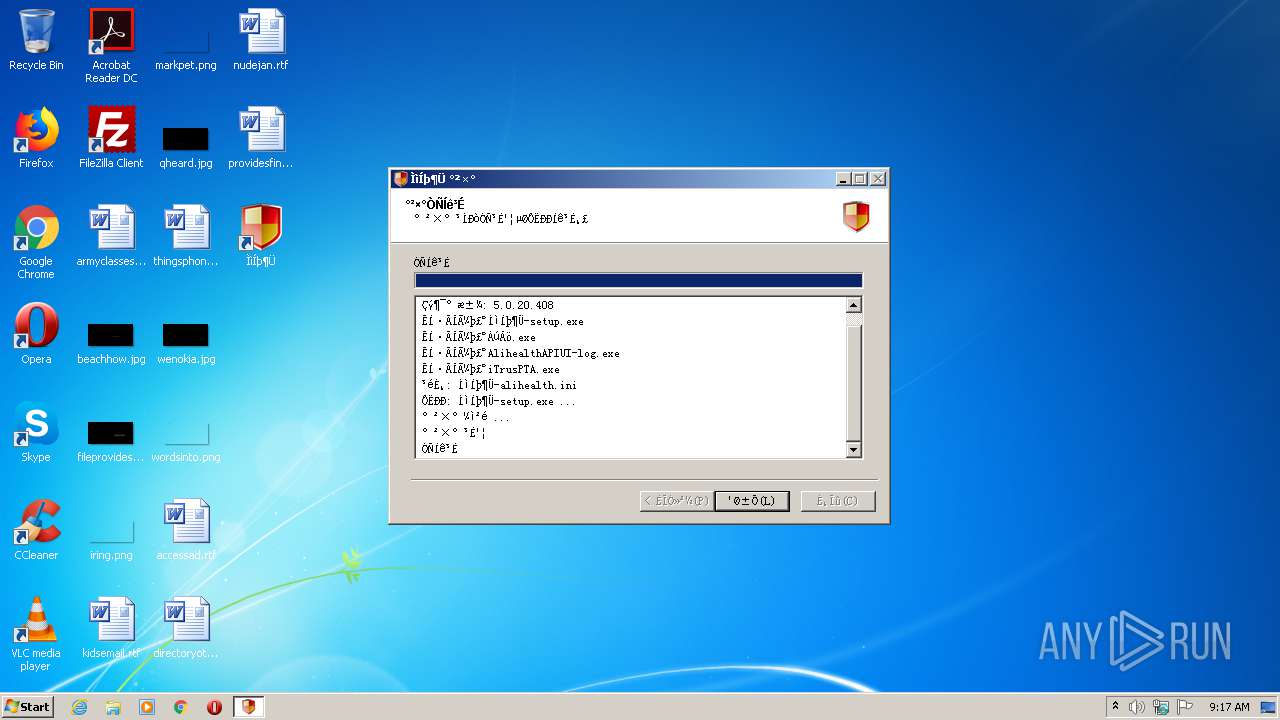
Application was dropped or rewritten from another process
- ÌìÍþ¶Ü-setup.exe (PID: 2660)
- AlihealthAPIUI-log.exe (PID: 1492)
- ÁúÂö.exe (PID: 3484)
- iTrus.exe (PID: 3720)
- nsDEC4.tmp (PID: 1576)
- nsDFBF.tmp (PID: 1468)
- nsE09B.tmp (PID: 2732)
- mtoken_iosvr.exe (PID: 2420)
- mtoken_iosvr.exe (PID: 2280)
- iTrusPTA.exe (PID: 3764)
- iTrus.exe (PID: 3860)
Changes the autorun value in the registry
- ÌìÍþ¶Ü-setup.exe (PID: 2660)
Starts NET.EXE for service management
- nsDEC4.tmp (PID: 1576)
- nsE09B.tmp (PID: 2732)
Changes settings of System certificates
- ÌìÍþ¶Ü-setup.exe (PID: 2660)
- iTrusPTA.exe (PID: 3764)
Changes internet zones settings
- iTrusPTA.exe (PID: 3764)
SUSPICIOUS
Executable content was dropped or overwritten
- ÌìÍþ¶Ü-setup.exe (PID: 2660)
- AlihealthAPIUI-log.exe (PID: 1492)
- twkey.exe (PID: 3468)
- ÁúÂö.exe (PID: 3484)
- iTrusPTA.exe (PID: 3764)
Creates files in the Windows directory
- ÌìÍþ¶Ü-setup.exe (PID: 2660)
- ÁúÂö.exe (PID: 3484)
- iTrusPTA.exe (PID: 3764)
- twkey.exe (PID: 3468)
Modifies the open verb of a shell class
- ÌìÍþ¶Ü-setup.exe (PID: 2660)
Creates files in the program directory
- ÌìÍþ¶Ü-setup.exe (PID: 2660)
- AlihealthAPIUI-log.exe (PID: 1492)
- ÁúÂö.exe (PID: 3484)
- iTrusPTA.exe (PID: 3764)
- twkey.exe (PID: 3468)
Starts application with an unusual extension
- ÁúÂö.exe (PID: 3484)
Creates a software uninstall entry
- ÌìÍþ¶Ü-setup.exe (PID: 2660)
Executed as Windows Service
- mtoken_iosvr.exe (PID: 2280)
Creates COM task schedule object
- iTrusPTA.exe (PID: 3764)
Creates files in the user directory
- iTrusPTA.exe (PID: 3764)
Reads Internet Cache Settings
- iTrus.exe (PID: 3860)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:16 01:50:50+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3384 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.20.408 |
| ProductVersionNumber: | 5.0.20.408 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | 北京天威诚信电子商务服务有限公司 |
| CompanyWebsite: | https://www.itrus.com.cn/ |
| FileDescription: | - |
| FileVersion: | 5.0.20.408 |
| LegalCopyright: | - |
| ProductName: | 天威盾-alihealth |
| ProductVersion: | 5.0.20.408 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Dec-2019 00:50:50 |
| Detected languages: |
|
| CompanyName: | 北京天威诚信电子商务服务有限公司 |
| CompanyWebsite: | https://www.itrus.com.cn/ |
| FileDescription: | - |
| FileVersion: | 5.0.20.408 |
| LegalCopyright: | - |
| ProductName: | 天威盾-alihealth |
| ProductVersion: | 5.0.20.408 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Dec-2019 00:50:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000060E4 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41884 |
.rdata | 0x00008000 | 0x0000123E | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03406 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21839 |
.ndata | 0x00025000 | 0x00014000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x00004788 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.75542 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28847 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.45081 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 6.70709 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.45849 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
56
Monitored processes
17
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | net.exe stop "Longmai mToken IOSVR" | C:\Windows\system32\net.exe | — | nsDEC4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 628 | C:\Windows\system32\net1 start "Longmai mToken IOSVR" | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\AppData\Local\Temp\twkey.exe" | C:\Users\admin\AppData\Local\Temp\twkey.exe | — | explorer.exe | |||||||||||
User: admin Company: 北京天威诚信电子商务服务有限公司 Integrity Level: MEDIUM Exit code: 3221226540 Version: 5.0.20.408 Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\AppData\Local\Temp\nspDEB3.tmp\nsDFBF.tmp" mtoken_iosvr.exe /Service | C:\Users\admin\AppData\Local\Temp\nspDEB3.tmp\nsDFBF.tmp | — | ÁúÂö.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1492 | C:\Users\admin\AppData\Local\Temp\AlihealthAPIUI-log.exe /S | C:\Users\admin\AppData\Local\Temp\AlihealthAPIUI-log.exe | ÌìÍþ¶Ü-setup.exe | ||||||||||||
User: admin Company: 北京天威诚信电子商务服务有限公司 Integrity Level: HIGH Description: i信 Exit code: 0 Version: 11.3.19.1028 Modules
| |||||||||||||||
| 1576 | "C:\Users\admin\AppData\Local\Temp\nspDEB3.tmp\nsDEC4.tmp" net.exe stop "Longmai mToken IOSVR" | C:\Users\admin\AppData\Local\Temp\nspDEB3.tmp\nsDEC4.tmp | — | ÁúÂö.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 2280 | "C:\Windows\system32\mtoken_iosvr.exe" | C:\Windows\system32\mtoken_iosvr.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Longmai Technology Integrity Level: SYSTEM Description: mToken IO Deamon Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2420 | mtoken_iosvr.exe /Service | C:\Windows\system32\mtoken_iosvr.exe | — | nsDFBF.tmp | |||||||||||
User: admin Company: Longmai Technology Integrity Level: HIGH Description: mToken IO Deamon Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2660 | C:\Users\admin\AppData\Local\Temp\ÌìÍþ¶Ü-setup.exe | C:\Users\admin\AppData\Local\Temp\ÌìÍþ¶Ü-setup.exe | twkey.exe | ||||||||||||
User: admin Company: 北京天威诚信电子商务服务有限公司 Integrity Level: HIGH Exit code: 0 Version: 5.0.20.408 Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\AppData\Local\Temp\nspDEB3.tmp\nsE09B.tmp" net.exe start "Longmai mToken IOSVR" | C:\Users\admin\AppData\Local\Temp\nspDEB3.tmp\nsE09B.tmp | — | ÁúÂö.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 292
Read events
882
Write events
398
Delete events
12
Modification events
| (PID) Process: | (3468) twkey.exe | Key: | HKEY_CURRENT_USER\Software\iTruschina\iTrusUKEY |
| Operation: | write | Name: | AutoInstall |
Value: 1 | |||
| (PID) Process: | (3468) twkey.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\iTruschina\iTrusUKEY\98.WinVer |
| Operation: | write | Name: | ProductId |
Value: WinVer | |||
| (PID) Process: | (3468) twkey.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\iTruschina\iTrusUKEY\98.WinVer |
| Operation: | write | Name: | ProductVersion |
Value: 6.1.7601.17932_11.0.9600.17843 | |||
| (PID) Process: | (3468) twkey.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\iTruschina\iTrusUKEY\99.HostId |
| Operation: | write | Name: | ProductId |
Value: HostId | |||
| (PID) Process: | (3468) twkey.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\iTruschina\iTrusUKEY\99.HostId |
| Operation: | write | Name: | ProductVersion |
Value: {3276AAEB-4469-4C24-B14D-E04826836738} | |||
| (PID) Process: | (3468) twkey.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\iTruschina\iTrusUKEY |
| Operation: | write | Name: | InstallId |
Value: {DC73AC76-5B2E-4417-B77B-7D5018935A57} | |||
| (PID) Process: | (3468) twkey.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\iTruschina\iTrusUKEY\Setup |
| Operation: | write | Name: | CurKeyName |
Value: ÌìÍþ¶Ü | |||
| (PID) Process: | (3468) twkey.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\iTruschina\iTrusUKEY\Shortcut |
| Operation: | write | Name: | ÌìÍþ¶Ü |
Value: 1 | |||
| (PID) Process: | (3468) twkey.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\iTruschina\iTrusUKEY\Setup |
| Operation: | write | Name: | NoShortcut |
Value: 1 | |||
| (PID) Process: | (2660) ÌìÍþ¶Ü-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\iTruschina\iTrusUKEY\98.WinVer |
| Operation: | write | Name: | ProductId |
Value: WinVer | |||
Executable files
40
Suspicious files
4
Text files
20
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | twkey.exe | C:\Users\admin\AppData\Local\Temp\ÌìÍþ¶Ü-setup.exe | executable | |
MD5:— | SHA256:— | |||
| 3468 | twkey.exe | C:\Users\admin\AppData\Local\Temp\nsqD50E.tmp\System.dll | executable | |
MD5:0063D48AFE5A0CDC02833145667B6641 | SHA256:AC9DFE3B35EA4B8932536ED7406C29A432976B685CC5322F94EF93DF920FEDE7 | |||
| 1492 | AlihealthAPIUI-log.exe | C:\Users\admin\AppData\Local\Temp\nszDD6A.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | ÌìÍþ¶Ü-setup.exe | C:\Program Files\iTrus\iTrus.exe | executable | |
MD5:— | SHA256:— | |||
| 2660 | ÌìÍþ¶Ü-setup.exe | C:\Windows\system32\iTrusUI.dll | executable | |
MD5:— | SHA256:— | |||
| 2660 | ÌìÍþ¶Ü-setup.exe | C:\Program Files\iTrus\uninstall-itrusukey.exe | executable | |
MD5:— | SHA256:— | |||
| 1492 | AlihealthAPIUI-log.exe | C:\Program Files\iTrus\AlihealthAPIUI\AlihealthAPIUI.cdat | binary | |
MD5:— | SHA256:— | |||
| 1492 | AlihealthAPIUI-log.exe | C:\Program Files\iTrus\AlihealthAPIUI\uninst.exe | executable | |
MD5:— | SHA256:— | |||
| 3468 | twkey.exe | C:\Users\admin\AppData\Local\Temp\nsqD50E.tmp\FindProcDLL.dll | executable | |
MD5:8614C450637267AFACAD1645E23BA24A | SHA256:0FA04F06A6DE18D316832086891E9C23AE606D7784D5D5676385839B21CA2758 | |||
| 3468 | twkey.exe | C:\Users\admin\AppData\Local\Temp\ÁúÂö.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3860 | iTrus.exe | GET | 200 | 139.129.105.201:80 | http://ukey.itrus.com.cn/itrusca/setupservice.html%05%05%05%05%05?host=S-1-5-5-0-67014&uuid=e10e12dc-f2d3-4ebf-82a8-f35183726443&component=iTrusUKEY,5.0.20.408&component=Longmai,1.0.19.906&component=iTrusPTA,1.0.18.426&component=AlihealthAPIUI,11.3.19.1028&component=WinVer,6.1.7601.17932_11.0.9600.17843&component=HostId,{3276AAEB-4469-4C24-B14D-E04826836738}&component=OSVERSIONINFO,6_1_Service%20Pack%201_2_7601 | CN | html | 4.37 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | iTrus.exe | 139.129.105.201:80 | ukey.itrus.com.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ukey.itrus.com.cn |
| unknown |
dns.msftncsi.com |
| shared |