| File name: | dq.exe |
| Full analysis: | https://app.any.run/tasks/6b3a076b-828c-4f44-aed8-78e638cac01e |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 16:26:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | BAF28D5C01E8735F31C20FED5D484710 |
| SHA1: | DA56737AF59045C092FD60AEF15F70386580354C |
| SHA256: | ABAE3D4A2D7A4E7307279E6C92DA5565E7F54916F487E2BF9E2A5E987D6E5C66 |
| SSDEEP: | 24576:XK+4tbSI+YKqB17A98REKlhShlMGFhvKP/711V3:34IEBtWCGFdKP/711V3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- dq.exe (PID: 2188)
Creates files in the program directory
- dq.exe (PID: 2188)
INFO
Reads the computer name
- runas.exe (PID: 3184)
Checks supported languages
- runas.exe (PID: 3184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x9654a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 380416 |
| CodeSize: | 723456 |
| LinkerVersion: | 14.29 |
| PEType: | PE32 |
| TimeStamp: | 2022:08:12 18:26:45+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 12-Aug-2022 16:26:45 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Aug-2022 16:26:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B09C4 | 0x000B0A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6163 |
.rdata | 0x000B2000 | 0x0004ACE2 | 0x0004AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.19957 |
.data | 0x000FD000 | 0x00007E34 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88548 |
.rsrc | 0x00105000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7123 |
.reloc | 0x00106000 | 0x00009C2C | 0x00009E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58317 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
40
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
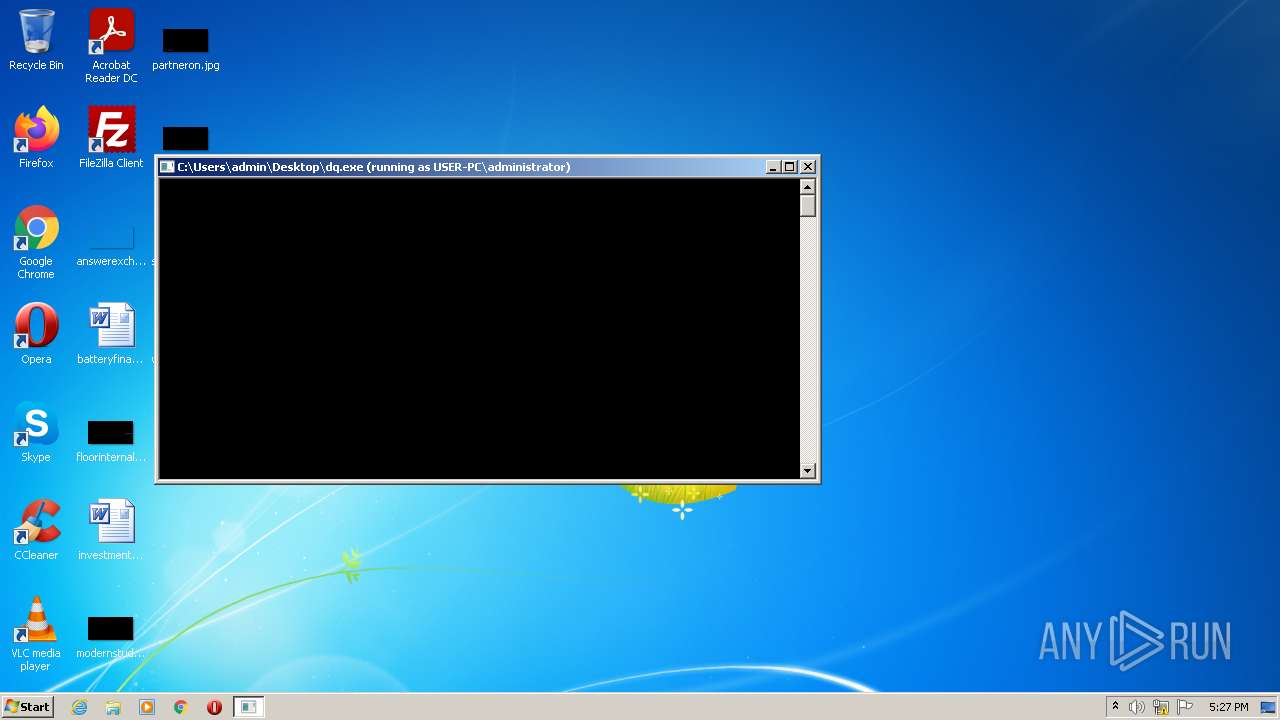
| 2188 | C:\Users\admin\Desktop\dq.exe | C:\Users\admin\Desktop\dq.exe | runas.exe | ||||||||||||
User: Administrator Integrity Level: HIGH Exit code: 3221226505 Modules
| |||||||||||||||
| 3184 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\Desktop\dq.exe | C:\Windows\System32\runas.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
31
Read events
31
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
95
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2188 | dq.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi.protected | — | |
MD5:— | SHA256:— | |||
| 2188 | dq.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab.protected | — | |
MD5:— | SHA256:— | |||
| 2188 | dq.exe | C:\config.sys.protected | text | |
MD5:— | SHA256:— | |||
| 2188 | dq.exe | C:\ProgramData\Adobe\Setup\{AC76BA86-7AD7-1033-7B44-AC0F074E4100}\AcroRdrDCUpd2001320064.msp.protected | — | |
MD5:— | SHA256:— | |||
| 2188 | dq.exe | C:\ProgramData\Adobe\ARM\Reader_15.007.20033\ReaderDCManifest.msi.protected | text | |
MD5:— | SHA256:— | |||
| 2188 | dq.exe | C:\Users\admin\AppData\Local\Adobe\A0A2C719-B8B1-4DC7-B33B-C50E709F20B0\96458326-0F6E-4F95-88EE-ED9F0B2D5401.protected | text | |
MD5:— | SHA256:— | |||
| 2188 | dq.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini.protected | text | |
MD5:— | SHA256:— | |||
| 2188 | dq.exe | C:\autoexec.bat.protected | text | |
MD5:— | SHA256:— | |||
| 2188 | dq.exe | C:\Windows\AppCompat\Programs\AEINV_PREVIOUS.xml.protected | text | |
MD5:— | SHA256:— | |||
| 2188 | dq.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\ACE.dll.protected | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report