| File name: | http://cd.huoying666.com/hysetup/litescr/2704/hy_B1918L2Z.exe |
| Full analysis: | https://app.any.run/tasks/d69d1b00-2b2d-4378-8bd2-a7347b183fb2 |
| Verdict: | Malicious activity |
| Analysis date: | January 08, 2021, 07:40:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A0265039BC7687135A9E1A2704368A87 |
| SHA1: | 600E0F5DF809374E5C0D9E5462A76145126BE1C6 |
| SHA256: | AB9919567F58F88AFDF1F83FFEE1368968ADB848E349F016620B743B89C83424 |
| SSDEEP: | 1572864:1+C54JpiqXsRSjzvDjXmmMFCjxZdM35c/L0mVGpYcMXIXTe:1+gqX/fp7jxZmi/g6cMn |
MALICIOUS
Drops executable file immediately after starts
- hy_B1918L2Z.exe (PID: 2708)
Application was dropped or rewritten from another process
- HYst.exe (PID: 3132)
- HYst.exe (PID: 1560)
- HYFastSide.exe (PID: 2004)
- winhost.exe (PID: 2124)
- winhost.exe (PID: 4036)
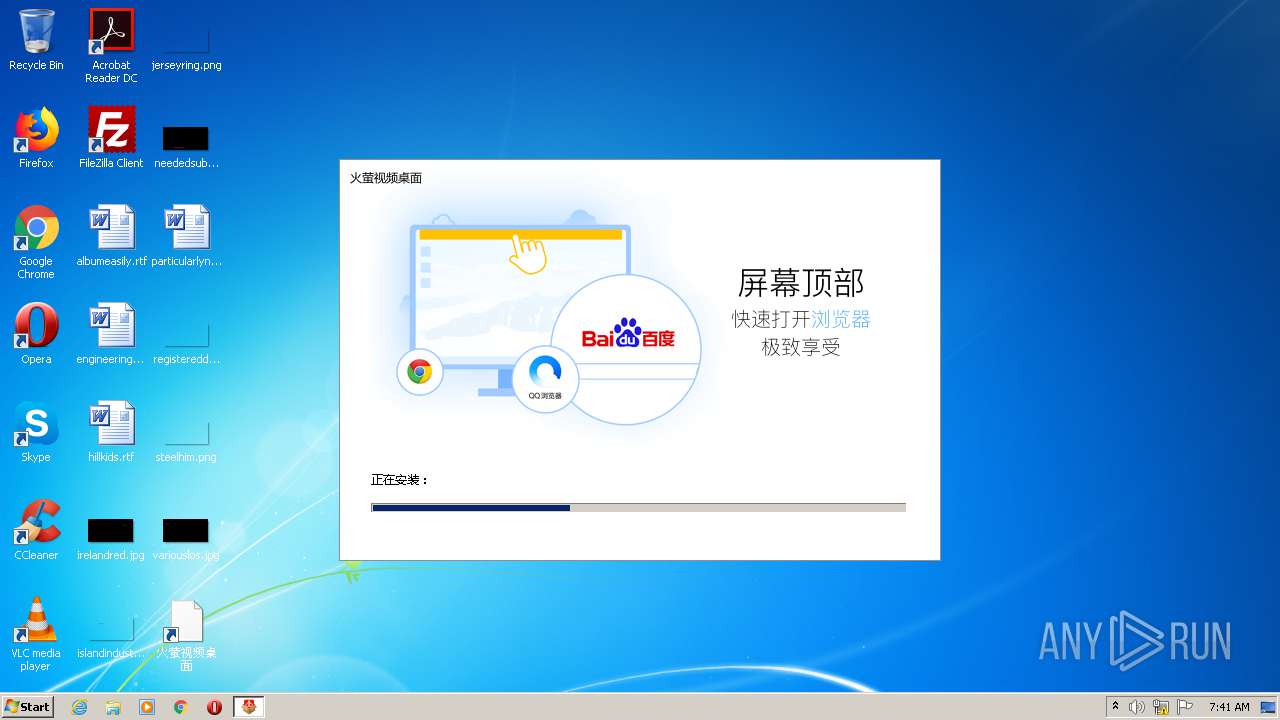
- HYVideoDesktop.exe (PID: 672)
- HYFastSide.exe (PID: 1740)
- HYFM.exe (PID: 3576)
- HYVideoDesktopCore.exe (PID: 2132)
- HYVideoDesktopCore.exe (PID: 2896)
- HYVideoDesktopCore.exe (PID: 3840)
Changes settings of System certificates
- HYst.exe (PID: 3132)
Registers / Runs the DLL via REGSVR32.EXE
- HYst.exe (PID: 3132)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3016)
- regsvr32.exe (PID: 3572)
- HYVideoDesktop.exe (PID: 672)
- HYFM.exe (PID: 3576)
Changes the autorun value in the registry
- HYst.exe (PID: 3132)
Steals credentials from Web Browsers
- winhost.exe (PID: 4036)
- winhost.exe (PID: 2124)
- HYFastSide.exe (PID: 1740)
Actions looks like stealing of personal data
- winhost.exe (PID: 2124)
- winhost.exe (PID: 4036)
- HYFastSide.exe (PID: 1740)
SUSPICIOUS
Creates a software uninstall entry
- hy_B1918L2Z.exe (PID: 2708)
- HYst.exe (PID: 3132)
- HYVideoDesktop.exe (PID: 672)
- HYFastSide.exe (PID: 1740)
Drops a file that was compiled in debug mode
- hy_B1918L2Z.exe (PID: 2708)
- HYst.exe (PID: 1560)
- HYst.exe (PID: 3132)
Executable content was dropped or overwritten
- hy_B1918L2Z.exe (PID: 2708)
- HYst.exe (PID: 1560)
- HYst.exe (PID: 3132)
Low-level read access rights to disk partition
- HYst.exe (PID: 3132)
Adds / modifies Windows certificates
- HYst.exe (PID: 3132)
Application launched itself
- HYst.exe (PID: 3132)
- winhost.exe (PID: 2124)
Drops a file with too old compile date
- HYst.exe (PID: 1560)
- HYst.exe (PID: 3132)
Creates a directory in Program Files
- HYst.exe (PID: 3132)
Creates files in the program directory
- HYst.exe (PID: 3132)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3016)
- regsvr32.exe (PID: 3572)
Creates files in the user directory
- HYst.exe (PID: 3132)
Uses RUNDLL32.EXE to load library
- HYVideoDesktop.exe (PID: 672)
- HYst.exe (PID: 3132)
INFO
Dropped object may contain Bitcoin addresses
- HYst.exe (PID: 1560)
- HYst.exe (PID: 3132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:01 13:57:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 237568 |
| InitializedDataSize: | 55435264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1aeed |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.2.1.6 |
| ProductVersionNumber: | 5.2.1.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0004) |
| CharacterSet: | Unicode |
| CompanyName: | 北京众纳鑫海网络技术有限公司 |
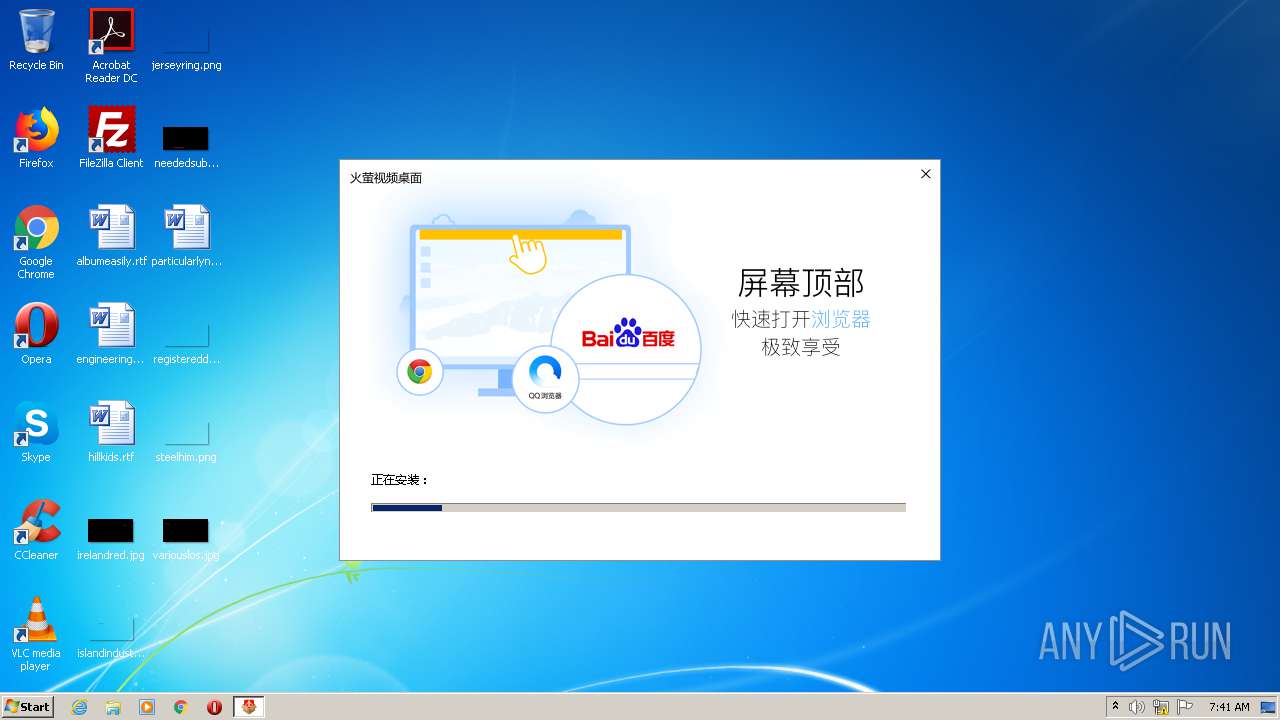
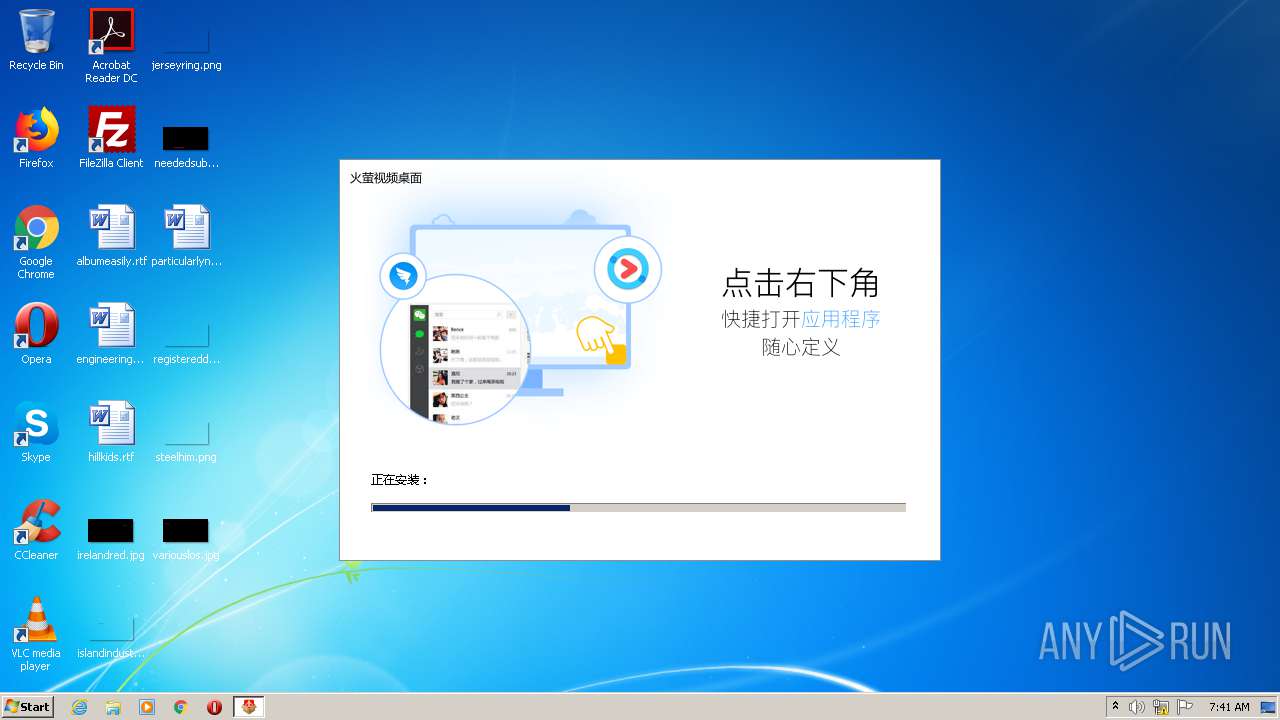
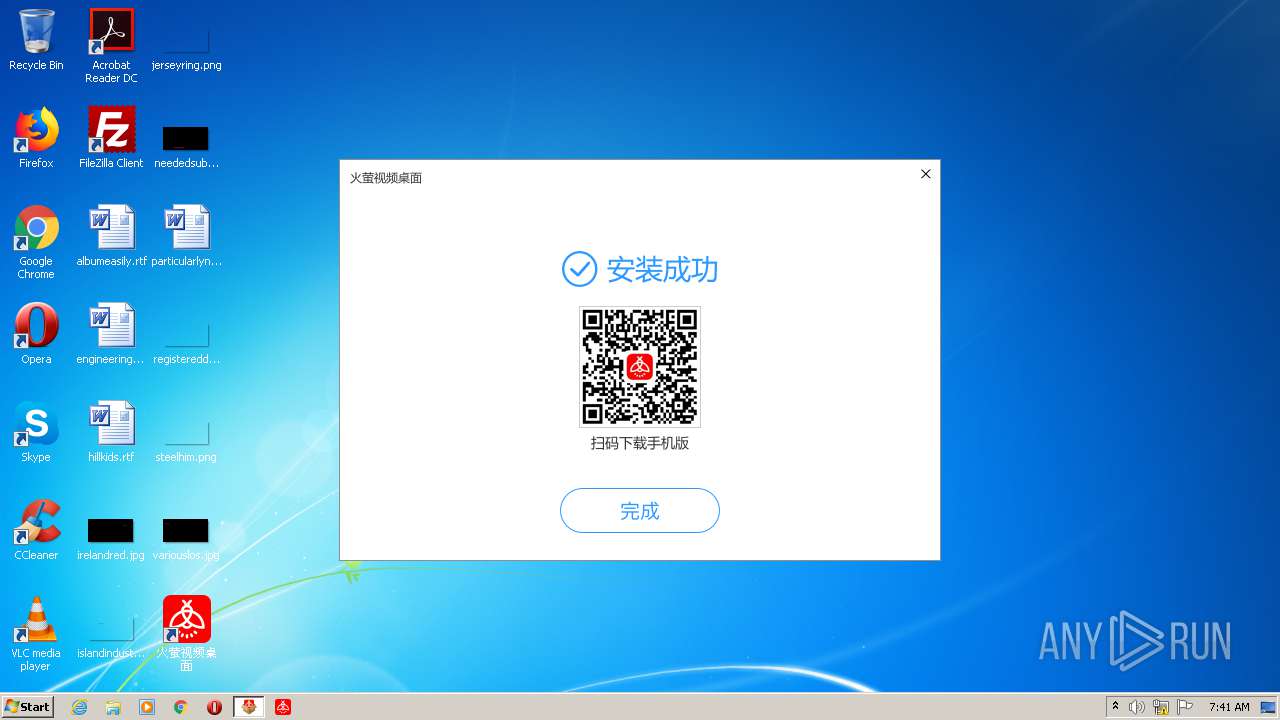
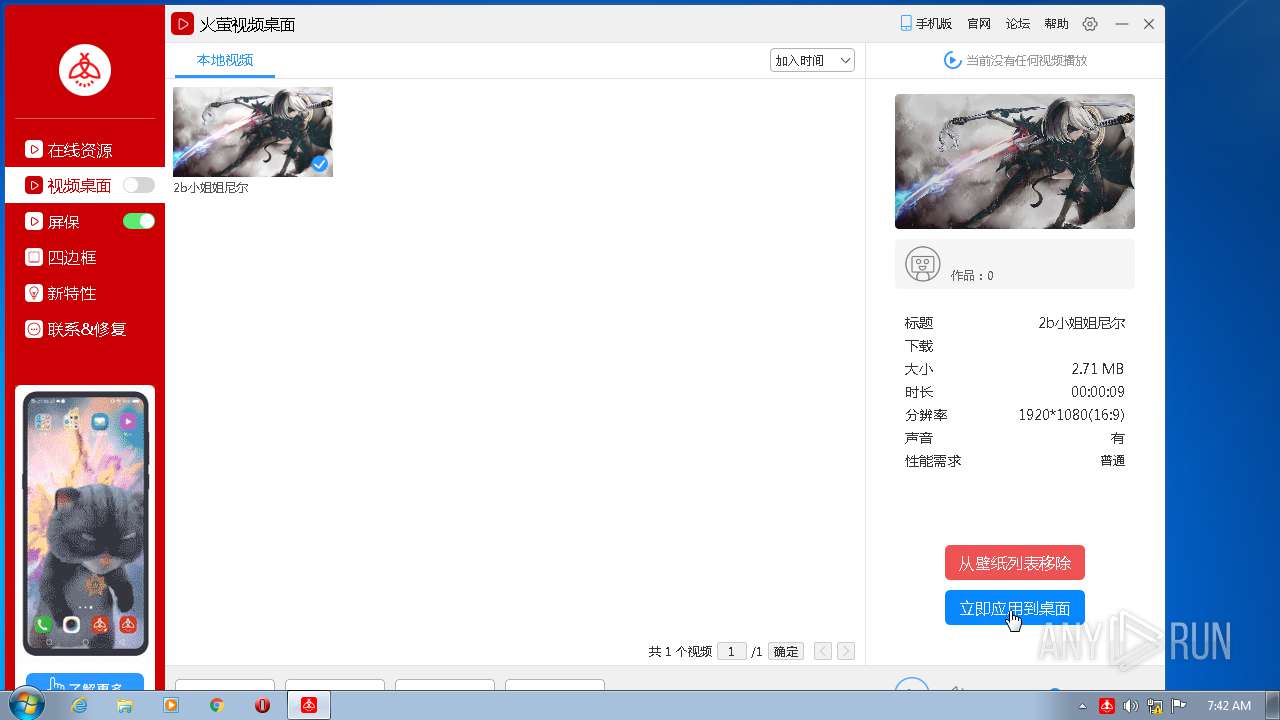
| FileDescription: | 火萤视频桌面 |
| FileVersion: | 5.2.1.6 |
| LegalCopyright: | 北京众纳鑫海网络技术有限公司 |
| ProductName: | 火萤视频桌面 |
| ProductVersion: | 5.2.1.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jun-2020 11:57:50 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | 北京众纳鑫海网络技术有限公司 |
| FileDescription: | 火萤视频桌面 |
| FileVersion: | 5.2.1.6 |
| LegalCopyright: | 北京众纳鑫海网络技术有限公司 |
| ProductName: | 火萤视频桌面 |
| ProductVersion: | 5.2.1.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 01-Jun-2020 11:57:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00039F81 | 0x0003A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59698 |
.rdata | 0x0003B000 | 0x00012F22 | 0x00013000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.41644 |
.data | 0x0004E000 | 0x00004464 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.52057 |
.gfids | 0x00053000 | 0x000001BC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.29789 |
.tls | 0x00054000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00055000 | 0x034C1E80 | 0x034C2000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99803 |
.reloc | 0x03517000 | 0x00004460 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.57303 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.77117 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 4.49804 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 4.29572 | 16936 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 7.98465 | 41148 | UNKNOWN | Chinese - PRC | RT_ICON |
HYLITE.7Z | 7.99999 | 53864391 | UNKNOWN | English - United States | FNV |
HYST.EXE | 7.31184 | 1215824 | UNKNOWN | English - United States | FNV |
ZLIB.DLL | 6.65761 | 164864 | UNKNOWN | English - United States | FNV |
IDD_DIALOG1 | 3.70711 | 108 | UNKNOWN | Chinese - PRC | RT_DIALOG |
IDI_ICON1 | 2.64638 | 76 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
Imports
KERNEL32.dll |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
60
Monitored processes
19
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Program Files\HYLite\HYVideoDesktop.exe" | C:\Program Files\HYLite\HYVideoDesktop.exe | HYst.exe | ||||||||||||
User: admin Company: 北京众纳鑫海网络技术有限公司 Integrity Level: MEDIUM Description: 火萤视频桌面主程序 Exit code: 0 Version: 5.2.1.6 Modules
| |||||||||||||||
| 688 | xcopy "C:\Users\admin\AppData\Local\Temp\HYLite\HYLiteResources" "C:\HYLiteResources\" /E /C /Y | C:\Windows\system32\xcopy.exe | — | HYst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | C:\Windows\System32\rundll32.exe | C:\Windows\System32\rundll32.exe | — | HYst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | C:\Windows\System32\rundll32.exe | C:\Windows\System32\rundll32.exe | — | HYst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\Temp\HYst.exe" --unzip | C:\Users\admin\AppData\Local\Temp\HYst.exe | HYst.exe | ||||||||||||
User: admin Company: 北京众纳鑫海网络技术有限公司 Integrity Level: HIGH Description: 火萤视频桌面安装程序 Exit code: 0 Version: 5.2.1.6 Modules
| |||||||||||||||
| 1740 | "C:\Users\admin\AppData\Local\HYFastSide\HYFastSide.exe" | C:\Users\admin\AppData\Local\HYFastSide\HYFastSide.exe | HYVideoDesktop.exe | ||||||||||||
User: admin Company: 北京众纳鑫海网络技术有限公司 Integrity Level: MEDIUM Description: 火萤视频桌面组件 Exit code: 0 Version: 5.1.1.15 Modules
| |||||||||||||||
| 2004 | "C:\Users\admin\AppData\Local\HYFastSide\HYFastSide.exe" --install-silent | C:\Users\admin\AppData\Local\HYFastSide\HYFastSide.exe | — | HYst.exe | |||||||||||
User: admin Company: 北京众纳鑫海网络技术有限公司 Integrity Level: HIGH Description: 火萤视频桌面组件 Exit code: 0 Version: 5.1.1.15 Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\FLYSVR\winhost.exe" -q | C:\Users\admin\AppData\Local\FLYSVR\winhost.exe | HYVideoDesktop.exe | ||||||||||||
User: admin Company: winhost Integrity Level: MEDIUM Description: winhost Exit code: 0 Version: 5.2.1.6 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\HYLite\HYVideoDesktopCore.exe" 131456 | C:\Program Files\HYLite\HYVideoDesktopCore.exe | — | HYVideoDesktop.exe | |||||||||||
User: admin Company: 火萤 Integrity Level: MEDIUM Description: 火萤视频桌面核心程序 Exit code: 0 Version: 6.1.0.0 Modules
| |||||||||||||||
| 2708 | "C:\Users\admin\AppData\Local\Temp\hy_B1918L2Z.exe" | C:\Users\admin\AppData\Local\Temp\hy_B1918L2Z.exe | explorer.exe | ||||||||||||
User: admin Company: 北京众纳鑫海网络技术有限公司 Integrity Level: HIGH Description: 火萤视频桌面 Exit code: 0 Version: 5.2.1.6 Modules
| |||||||||||||||
Total events
1 923
Read events
1 540
Write events
380
Delete events
3
Modification events
| (PID) Process: | (3132) HYst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\HYLite |
| Operation: | write | Name: | mid |
Value: 4a6a7d30deeada78d1e2de4a31347fc5 | |||
| (PID) Process: | (3132) HYst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3132) HYst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3132) HYst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2708) hy_B1918L2Z.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\FLYSVR |
| Operation: | write | Name: | NString |
Value: B191 | |||
| (PID) Process: | (2708) hy_B1918L2Z.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\HYLite |
| Operation: | write | Name: | och |
Value: D+ZWrqMFnrSFm0VWxSRD1Q== | |||
| (PID) Process: | (2708) hy_B1918L2Z.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\HYLite |
| Operation: | write | Name: | ch |
Value: 8C4lYO6RcOsBVjR2kwpI3TxyIr7xsMhkJVYHGi1S+RXZbKLRRpVF2MaZLEpjW24bTQReSFN1b2dpUWDitIjGOA== | |||
| (PID) Process: | (3132) HYst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3132) HYst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3132) HYst.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
252
Suspicious files
405
Text files
61
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2708 | hy_B1918L2Z.exe | C:\Users\admin\AppData\Local\Temp\HYLite.7z | — | |
MD5:— | SHA256:— | |||
| 2708 | hy_B1918L2Z.exe | C:\Users\admin\AppData\Local\Temp\zlib.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | HYst.exe | C:\Users\admin\AppData\Local\Temp\HYLite\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | HYst.exe | C:\Users\admin\AppData\Local\Temp\HYLite\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | HYst.exe | C:\Users\admin\AppData\Local\Temp\HYLite\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | HYst.exe | C:\Users\admin\AppData\Local\Temp\HYLite\api-ms-win-core-interlocked-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | HYst.exe | C:\Users\admin\AppData\Local\Temp\HYLite\api-ms-win-core-libraryloader-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | HYst.exe | C:\Users\admin\AppData\Local\Temp\HYLite\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | HYst.exe | C:\Users\admin\AppData\Local\Temp\HYLite\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | HYst.exe | C:\Users\admin\AppData\Local\Temp\HYLite\api-ms-win-core-processthreads-l1-1-1.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
24
DNS requests
8
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
672 | HYVideoDesktop.exe | POST | 200 | 47.93.165.92:80 | http://cp3.huoying666.com/1100.gif | CN | — | — | suspicious |
672 | HYVideoDesktop.exe | POST | 200 | 47.93.165.92:80 | http://cp3.huoying666.com/1100.gif | CN | — | — | suspicious |
1740 | HYFastSide.exe | GET | 200 | 60.222.11.31:80 | http://cd.huoying666.com/static/profiles.pro | CN | text | 5.90 Kb | malicious |
672 | HYVideoDesktop.exe | POST | 200 | 47.93.165.92:80 | http://cp3.huoying666.com/1100.gif | CN | — | — | suspicious |
1740 | HYFastSide.exe | GET | 200 | 180.163.121.240:80 | http://s7.huoying666.com/uploads/files/game_pro_wl.ini | CN | text | 204 b | malicious |
672 | HYVideoDesktop.exe | POST | 200 | 47.93.165.92:80 | http://cp3.huoying666.com/1100.gif | CN | — | — | suspicious |
672 | HYVideoDesktop.exe | POST | 200 | 47.93.165.92:80 | http://cp3.huoying666.com/1100.gif | CN | — | — | suspicious |
672 | HYVideoDesktop.exe | POST | 200 | 47.93.165.92:80 | http://cp3.huoying666.com/1100.gif | CN | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 180.163.121.240:80 | s7.huoying666.com | China Telecom (Group) | CN | suspicious |
672 | HYVideoDesktop.exe | 47.93.165.92:443 | cp3.huoying666.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
3132 | HYst.exe | 47.93.165.92:443 | cp3.huoying666.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
3132 | HYst.exe | 120.55.156.0:443 | cp5.huoying666.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
4036 | winhost.exe | 47.111.207.82:443 | picssl.xunmzone.com | — | CN | unknown |
1740 | HYFastSide.exe | 60.222.11.31:80 | cd.huoying666.com | CHINA UNICOM China169 Backbone | CN | suspicious |
672 | HYVideoDesktop.exe | 116.211.224.246:443 | s2.huoying666.com | CHINANET Hubei province network | CN | unknown |
672 | HYVideoDesktop.exe | 47.93.165.92:80 | cp3.huoying666.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
4036 | winhost.exe | 47.111.207.85:443 | static.scp.btoo3.com | — | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cp3.huoying666.com |
| suspicious |
cp5.huoying666.com |
| unknown |
static.scp.btoo3.com |
| unknown |
picssl.xunmzone.com |
| unknown |
cd.huoying666.com |
| malicious |
s7.huoying666.com |
| malicious |
s2.huoying666.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
672 | HYVideoDesktop.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
672 | HYVideoDesktop.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
672 | HYVideoDesktop.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
672 | HYVideoDesktop.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
672 | HYVideoDesktop.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
672 | HYVideoDesktop.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
8 ETPRO signatures available at the full report
Process | Message |
|---|---|
HYst.exe | unzip done
|
HYst.exe | xcopy "C:\Users\admin\AppData\Local\Temp\HYLite\HYLiteResources" "C:\HYLiteResources\" /E /C /Y |
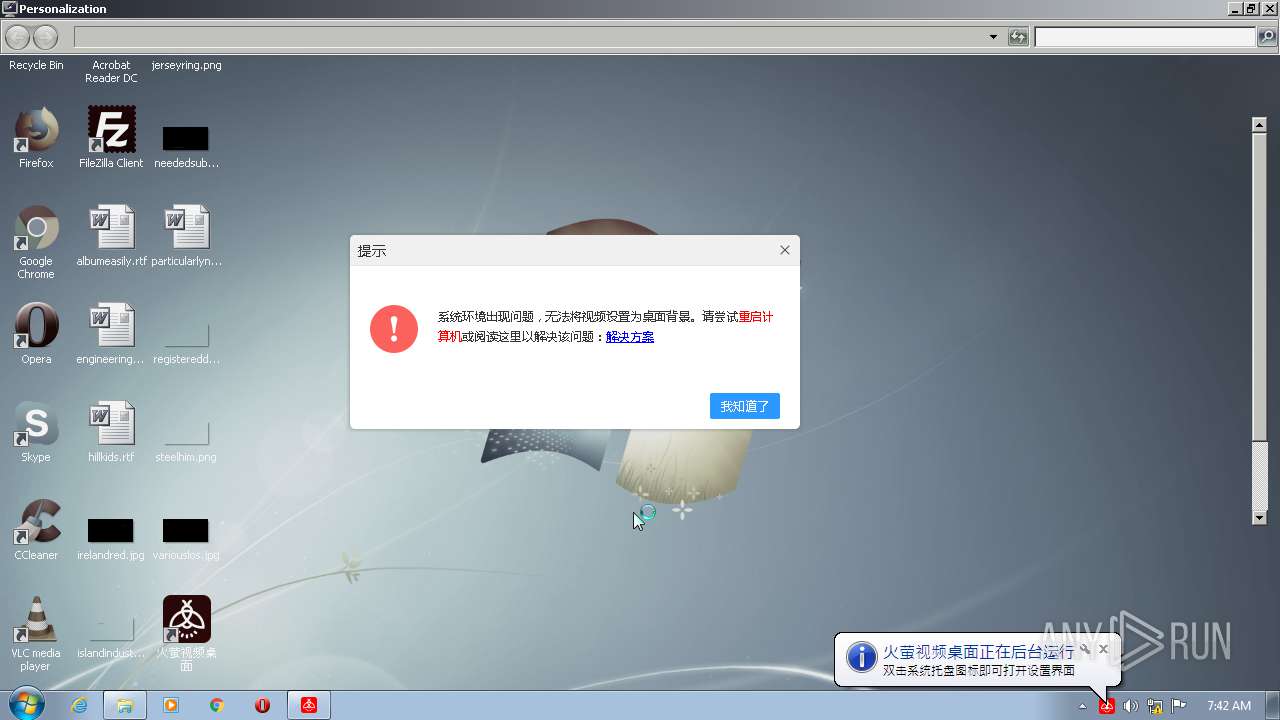
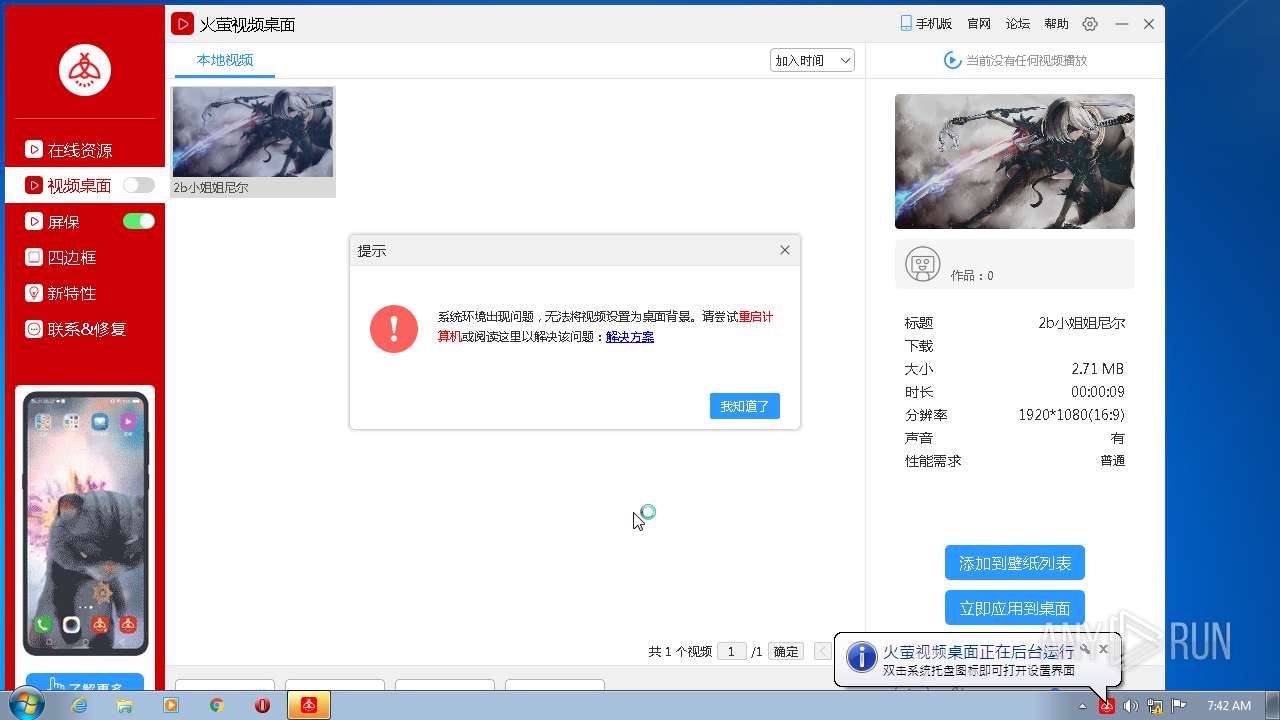
HYVideoDesktop.exe | QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
HYVideoDesktop.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
HYVideoDesktop.exe | content-type missing in HTTP POST, defaulting to application/x-www-form-urlencoded. Use QNetworkRequest::setHeader() to fix this problem.
|
HYVideoDesktop.exe | content-type missing in HTTP POST, defaulting to application/x-www-form-urlencoded. Use QNetworkRequest::setHeader() to fix this problem.
|
HYst.exe | sleep again
|
HYst.exe | sleep again
|
HYst.exe | sleep again
|
HYst.exe | sleep again
|