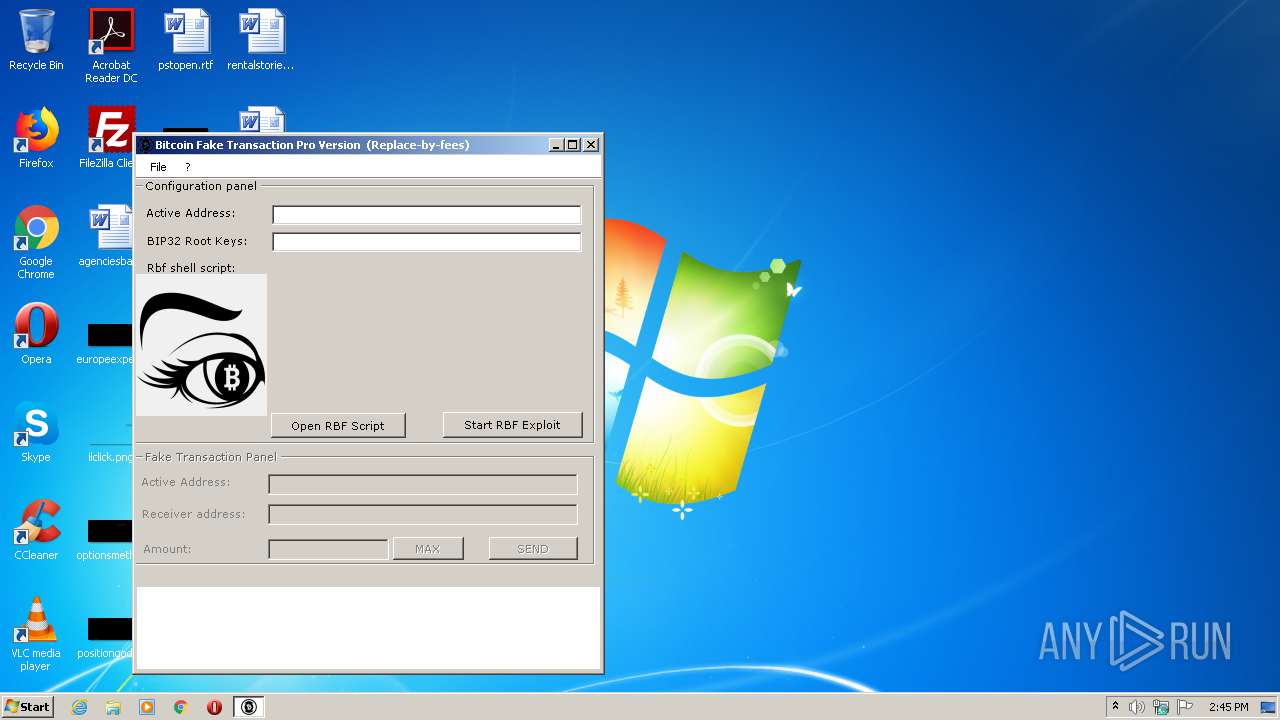
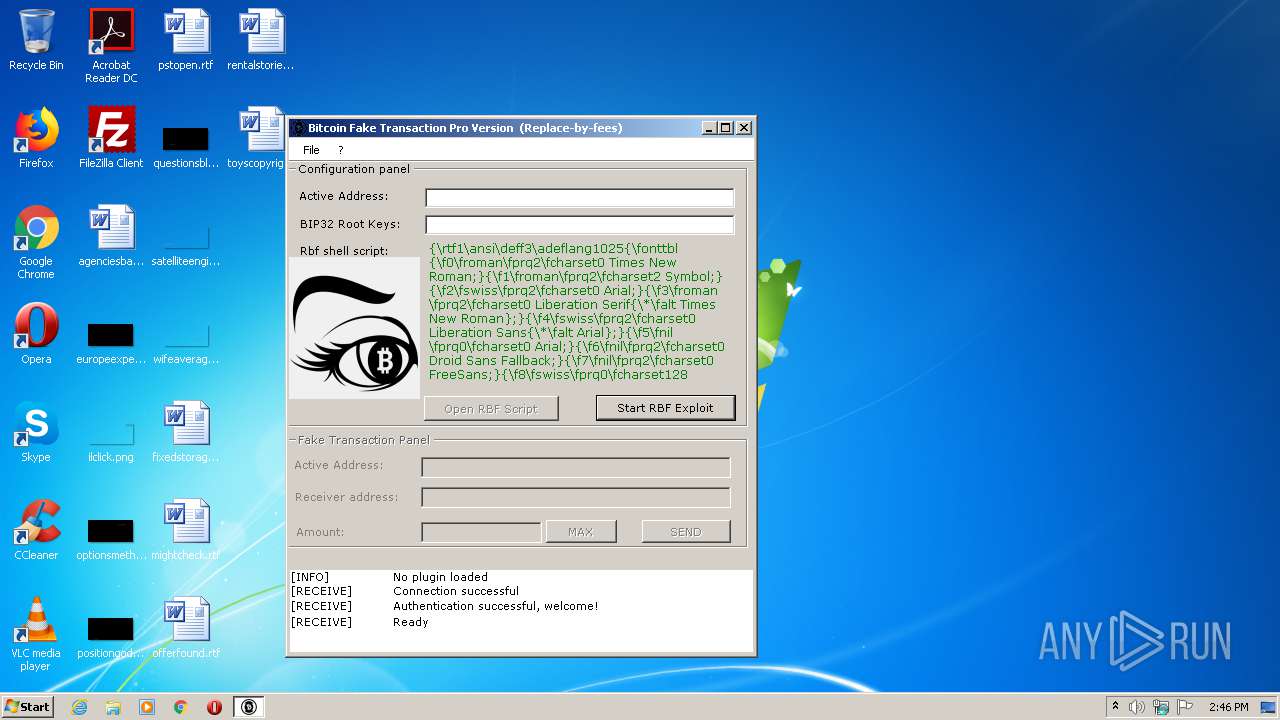
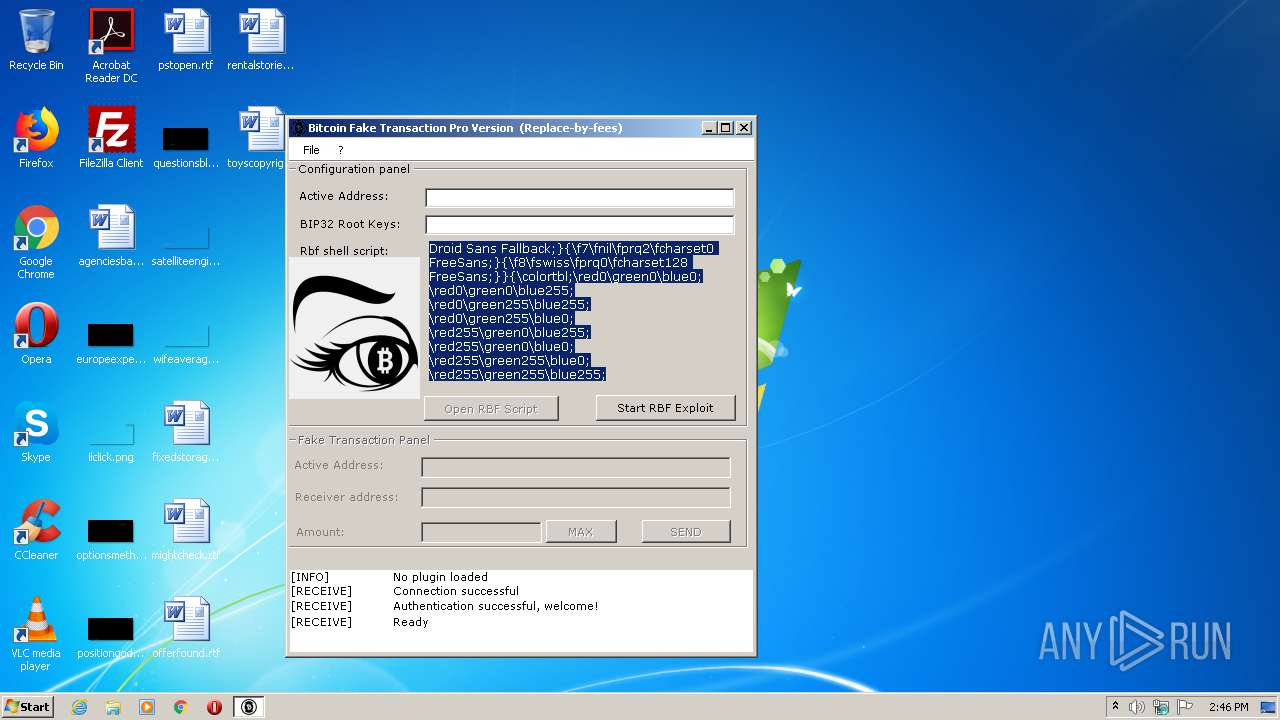
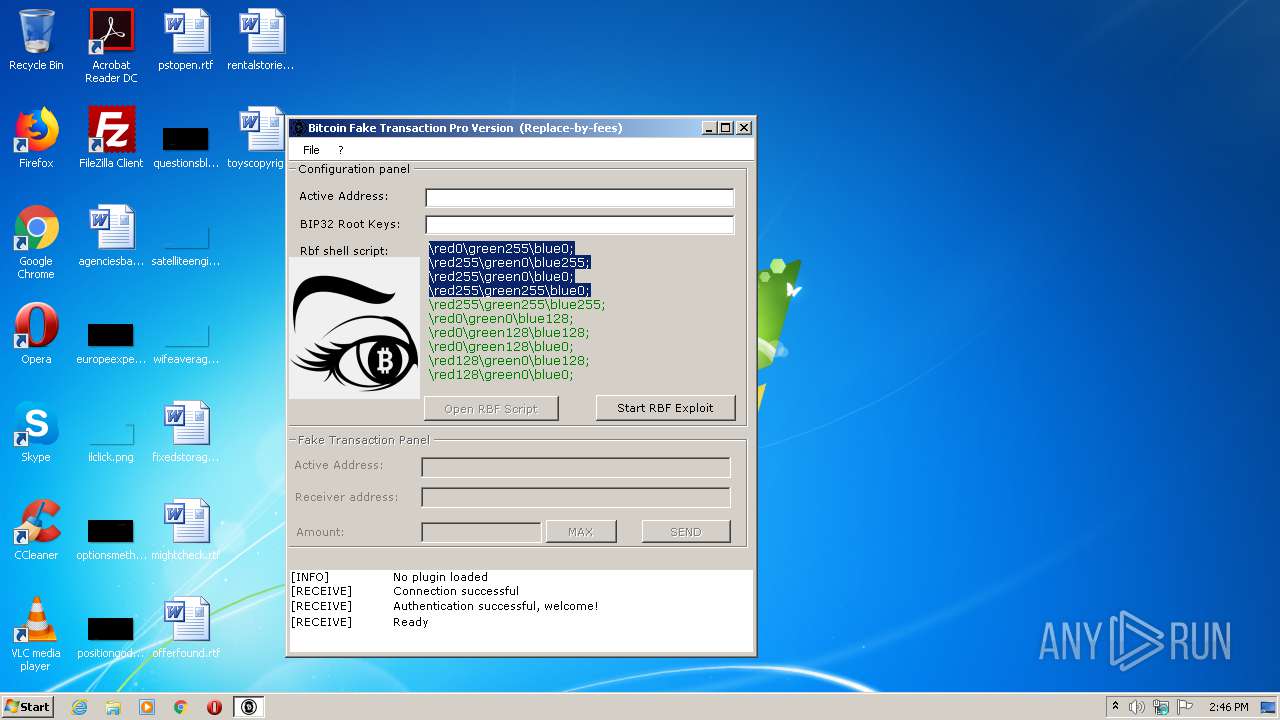
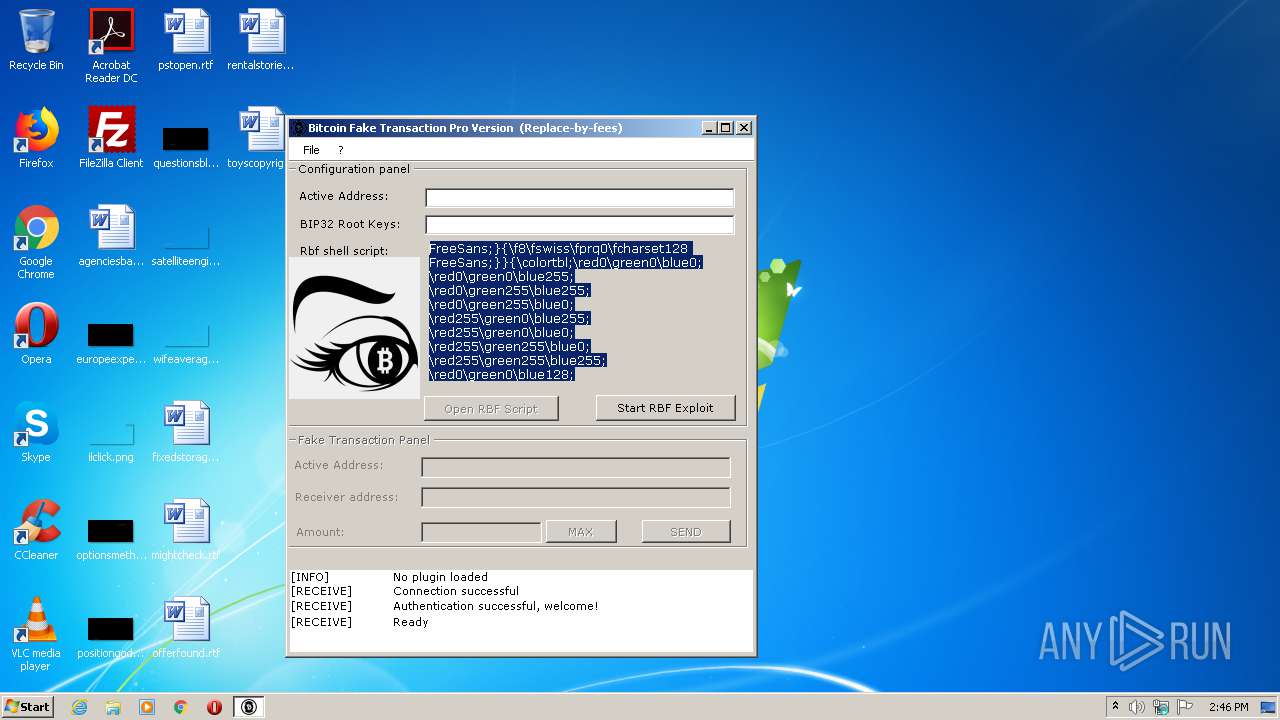
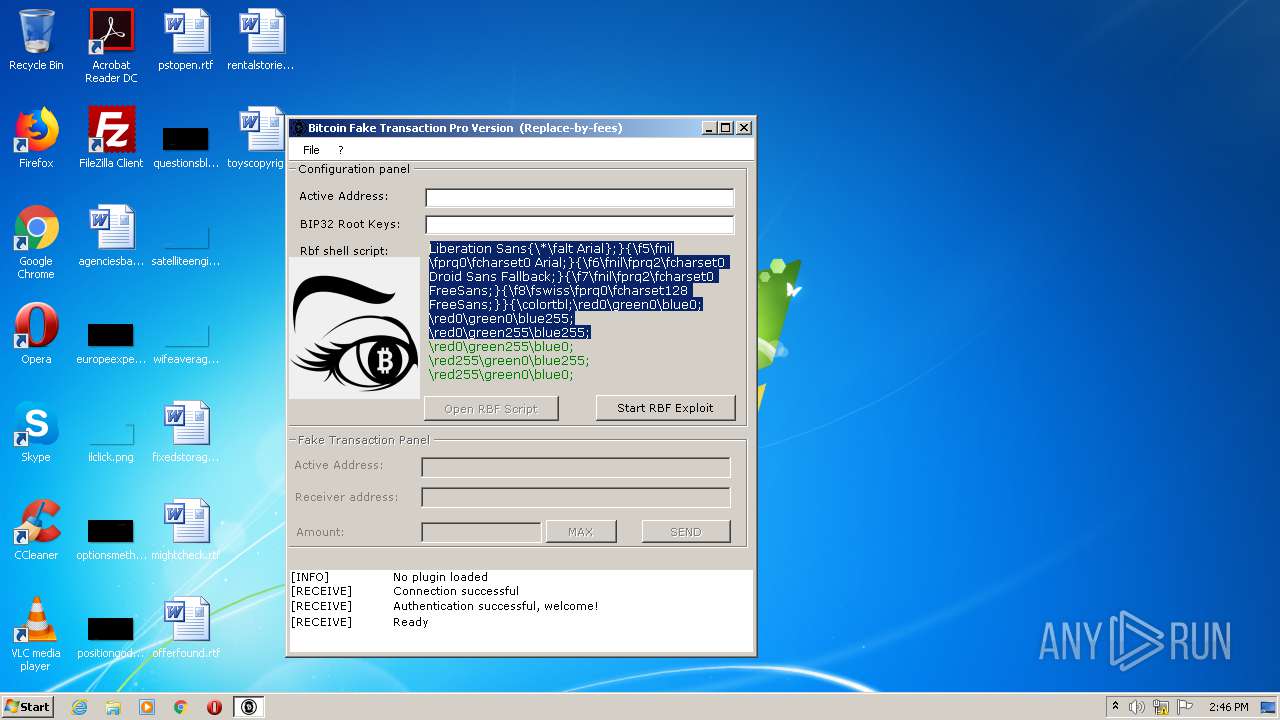
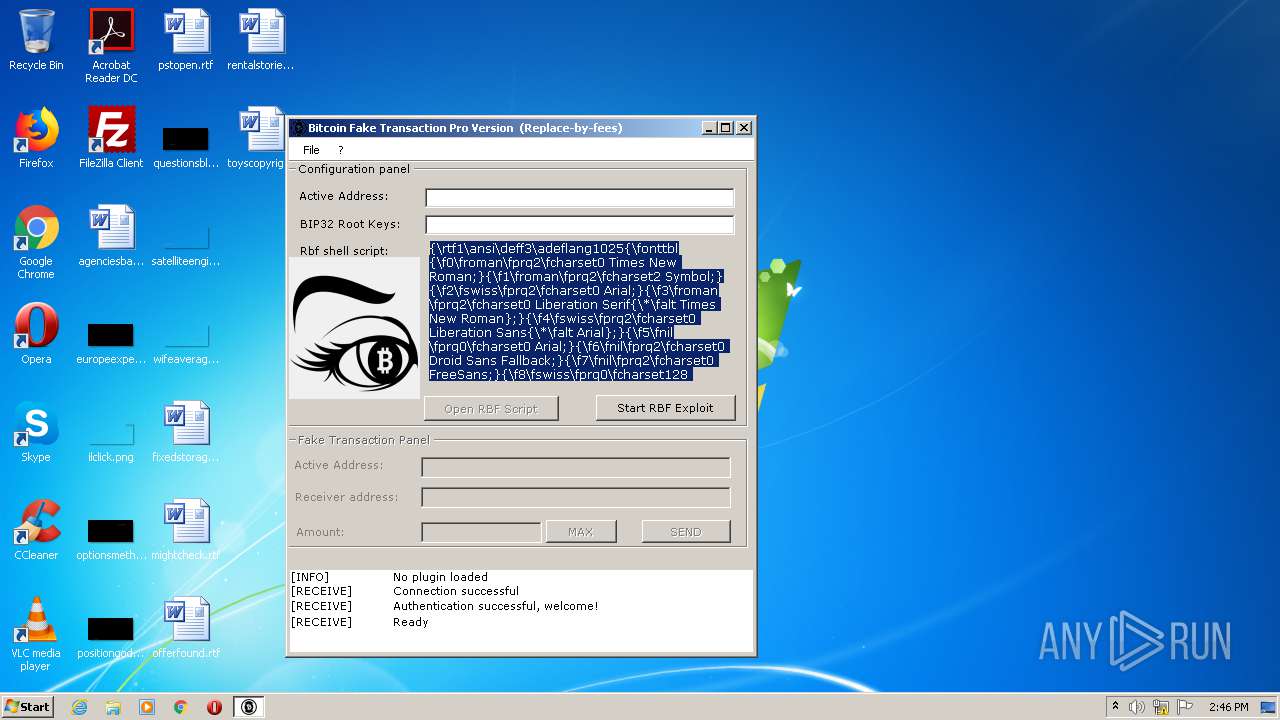
| File name: | Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe |
| Full analysis: | https://app.any.run/tasks/00e10107-17f7-4cff-ba03-2d0cdb214102 |
| Verdict: | No threats detected |
| Analysis date: | July 27, 2020, 13:45:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | CEC612877B2643E72BAC75B27DF255CF |
| SHA1: | 9038C3623F6465D7CECD71AE1AB203E82A259274 |
| SHA256: | AB82562C0C288DB769DD3BAA19917885EAA853532FA5D8F4BB40D6D436D532CD |
| SSDEEP: | 3072:sFCuomKEZEs32GhNvihpEU9Si4k2gHdG094qSPqzm3eKFCuoml:1QKEZES2GhN6/EIBHA0SP3IQl |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:29 00:05:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 196096 |
| InitializedDataSize: | 96768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31d9e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | BitCoine |
| FileVersion: | 1.0.0.0 |
| InternalName: | Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe |
| LegalCopyright: | Copyright © 2019 |
| OriginalFileName: | Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe |
| ProductName: | BitCoine |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Jun-2019 22:05:05 |
| Debug artifacts: |
|
| FileDescription: | BitCoine |
| FileVersion: | 1.0.0.0 |
| InternalName: | Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe |
| LegalCopyright: | Copyright © 2019 |
| OriginalFilename: | Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe |
| ProductName: | BitCoine |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 28-Jun-2019 22:05:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0002FDA4 | 0x0002FE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.90887 |
.sdata | 0x00032000 | 0x00000138 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.45707 |
.rsrc | 0x00034000 | 0x00017600 | 0x00017600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.34169 |
.reloc | 0x0004C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89697 | 1498 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.26832 | 93040 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.16096 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
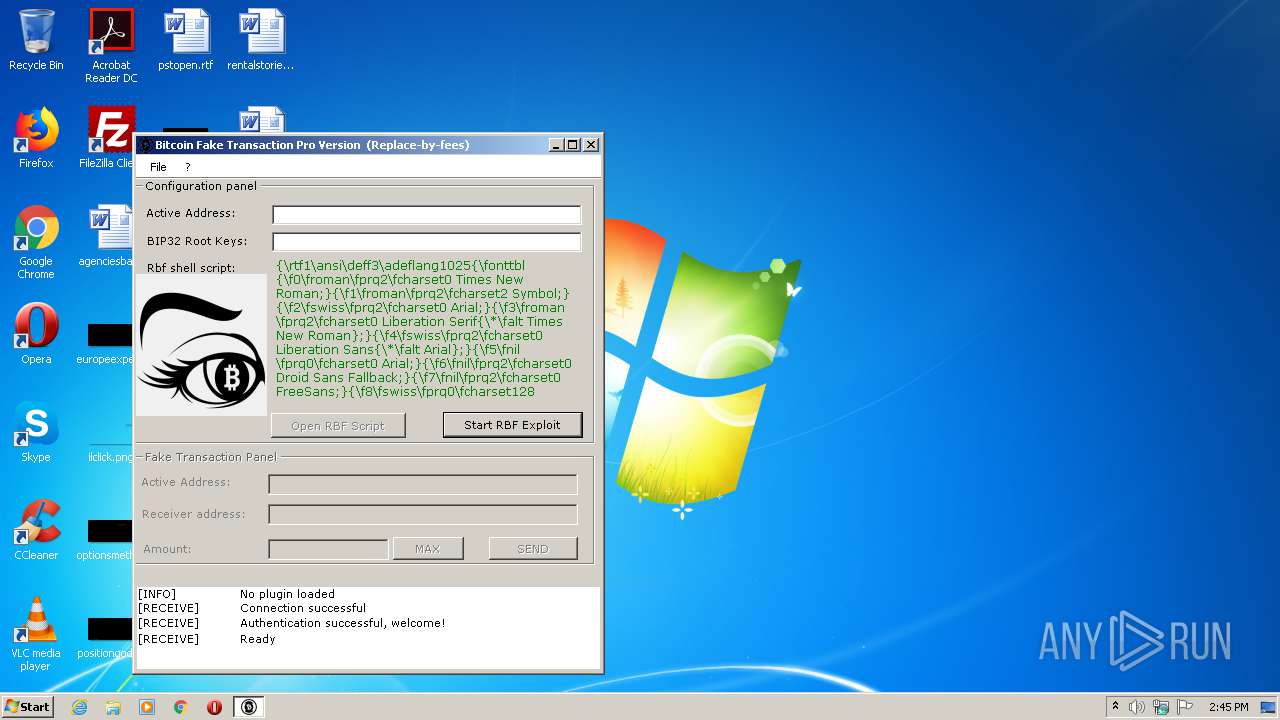
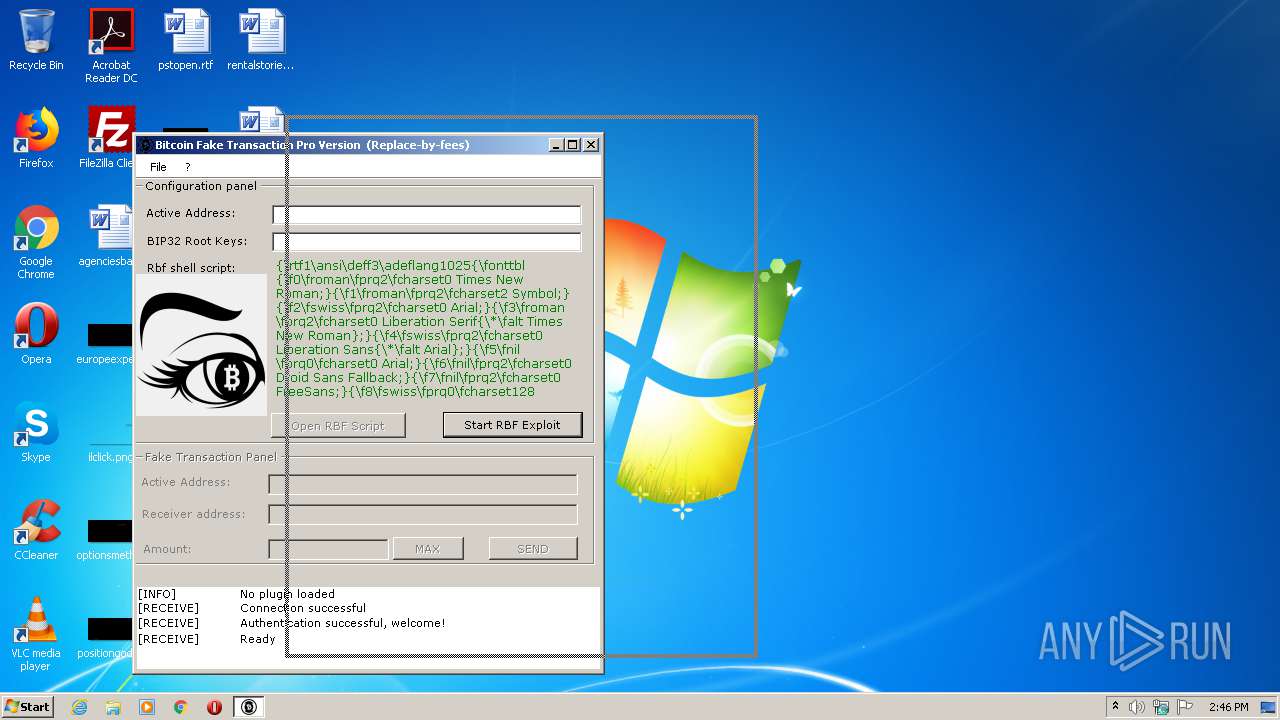
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
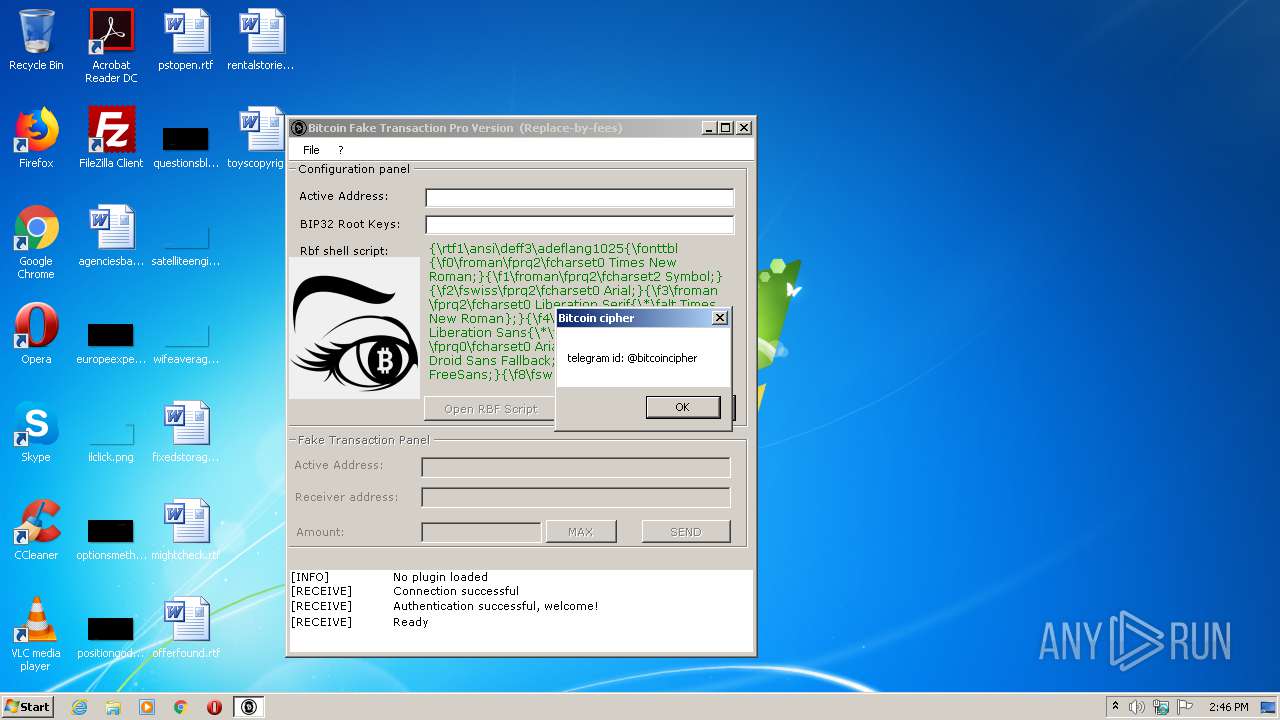
Behavior graph
Click at the process to see the details
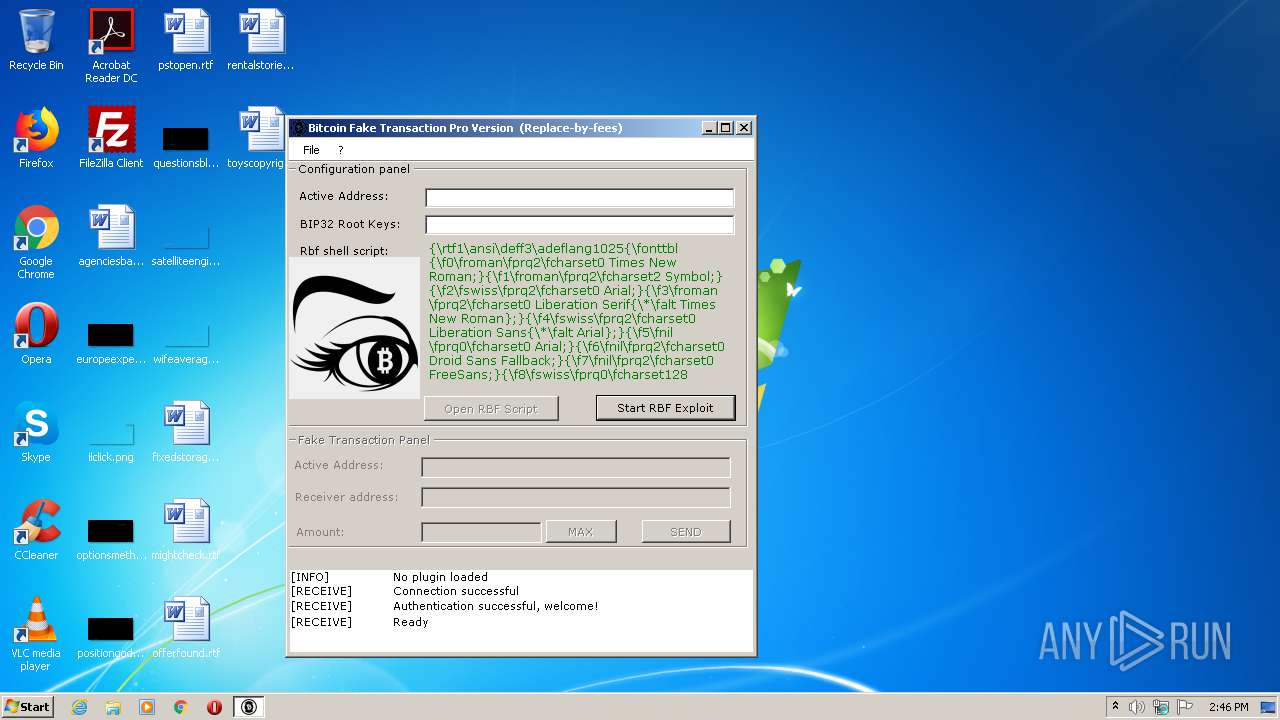
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2124 | "C:\Users\admin\AppData\Local\Temp\Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe" | C:\Users\admin\AppData\Local\Temp\Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: BitCoine Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
537
Read events
500
Write events
36
Delete events
1
Modification events
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000B0000000100000000000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | 2 |
Value: 42006900740063006F0069006E002000460061006B00650020005400720061006E00730061006300740069006F006E00200028005200650070006C006100630065002D00620079002D00660065006500730029002000500072006F002000560065007200730069006F006E002E00650078006500000014001F4225481E03947BC34DB131E946B44C8DD5740000001A00EEBBFE23000010007DB10D7BD29C934A973346CC89022E7C00002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000001900EFBE7E47B3FBE4C93B4BA2BAD3F5D3CD46F98207BA827A5B6945B5D7EC83085F08CC20000000 | |||
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000100000000000000FFFFFFFF | |||
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\rtf |
| Operation: | write | Name: | 0 |
Value: 14001F4225481E03947BC34DB131E946B44C8DD5740000001A00EEBBFE23000010007DB10D7BD29C934A973346CC89022E7C00002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000001900EFBE7E47B3FBE4C93B4BA2BAD3F5D3CD46F98207BA827A5B6945B5D7EC83085F08CC200008040000020481191410D80320000000404000000000000000000000000000000000000000000000000000010000B40000003153505330F125B7EF471A10A5F102608C9EEBAC390000000A000000001F000000130000007300700065006300690065007300730074006F0072006900650073002E00720074006600000000003500000004000000001F00000011000000520069006300680020005400650078007400200046006F0072006D006100740000000000150000000C0000000015000000ED0B000000000000150000000E000000004000000000876D3CA168D201000000003100000031535053B1166D44AD8D7048A748402EA43D788C1500000064000000001500000067867F4B3D5C9786000000003801000031535053A66A63283D95D211B5D600C04FD918D01100000019000000001300000077014040B5000000200000000011100000A400000014001F44471A0359723FA74489C55595FE6B30EE200000001A00EEBBFE2300001000D09AD3FD8F23AF46ADB46C85480369C700006E003200ED0B0000274A032620005350454349457E312E5254460000520008000400EFBE274A0326FB50B76D2A00000059C000000000020000000000000000000000000000007300700065006300690065007300730074006F0072006900650073002E0072007400660000001C0000003900000018000000001F000000130000007300700065006300690065007300730074006F0072006900650073002E00720074006600000000001D0000000B000000001F000000050000002E0072007400660000000000000000002D00000031535053901C6949177E1A10A91C08002B2ECDA9110000000300000000030000000000000000000000340100003153505340E83E1E2BBC6C4782372ACD1A839B226900000008000000001F0000002C00000043003A005C00550073006500720073005C00610064006D0069006E005C0044006F00630075006D0065006E00740073005C007300700065006300690065007300730074006F0072006900650073002E0072007400660000002900000003000000001F100000010000000900000064006F00630075006D0065006E0074000000000011000000140000000003000000010000007500000011000000001F000000310000007B00310036003800350044003400410042002D0041003500310042002D0034004100460031002D0041003400450035002D004300450045003800370030003000320034003300310044007D002E004D006500720067006500200041006E00790000000000000000002900000031535053FCB3B4B9512B424AB5D8324146AFCF250D000000080000000001000000000000002D00000031535053C0E85BCF6C23D34ABACECD608A2748D71100000064000000000B000000FFFF0000000000000000000000000000 | |||
| (PID) Process: | (2124) Bitcoin Fake Transaction (Replace-by-fees) Pro Version.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\rtf |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report