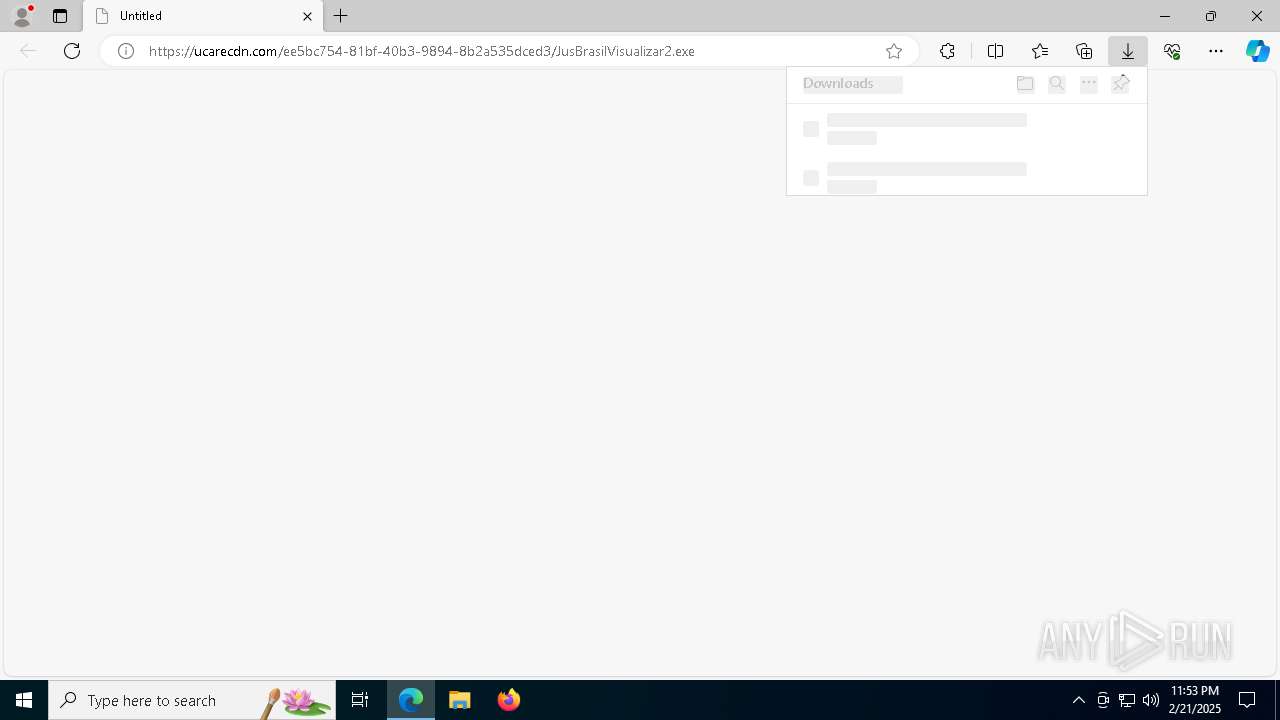
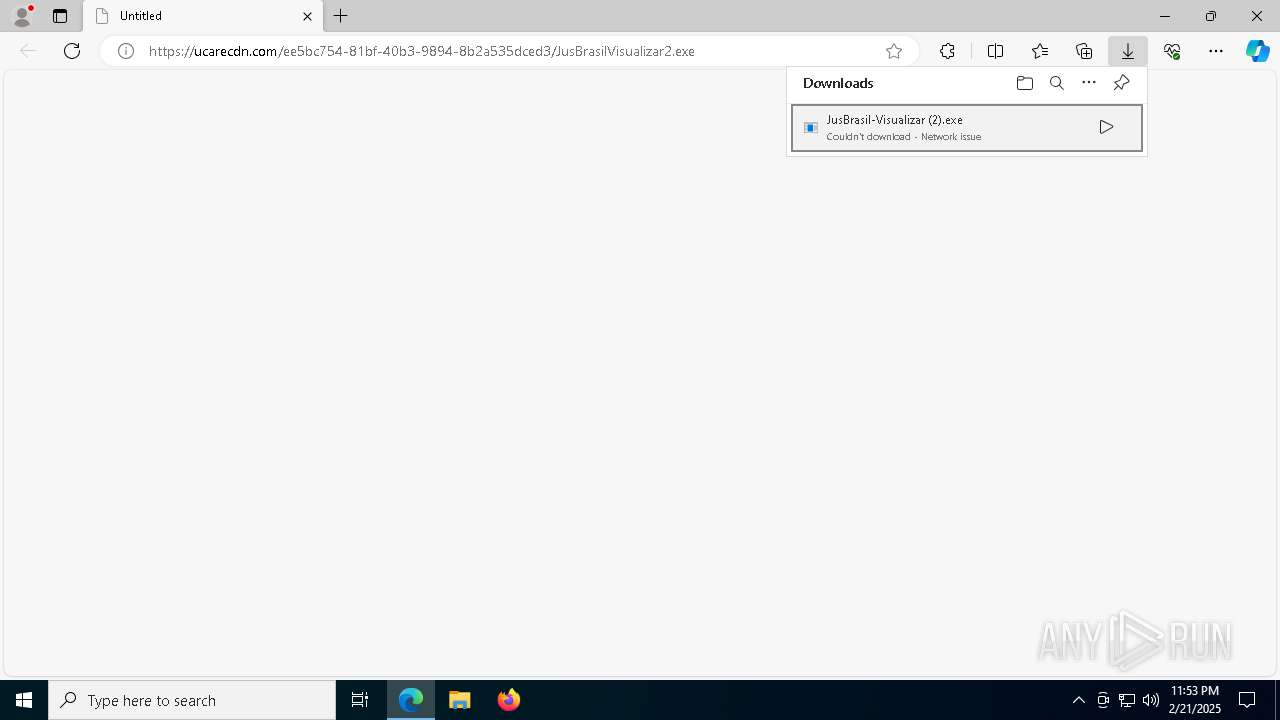
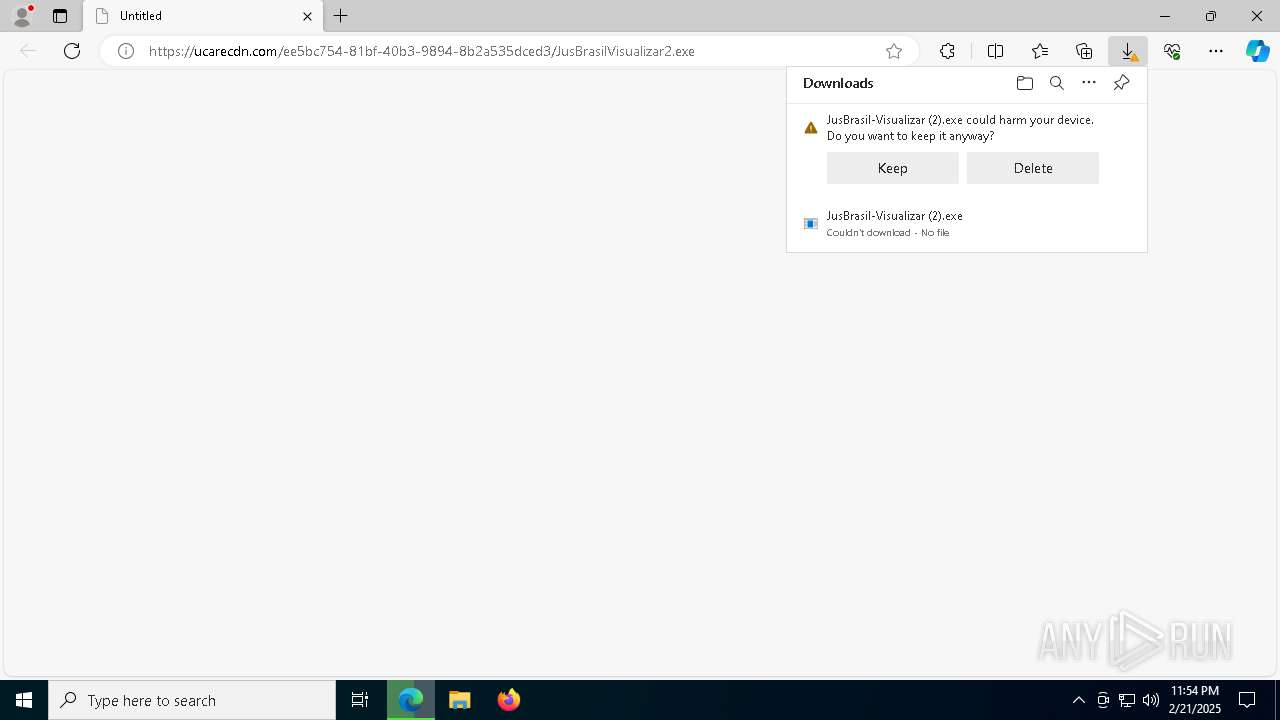
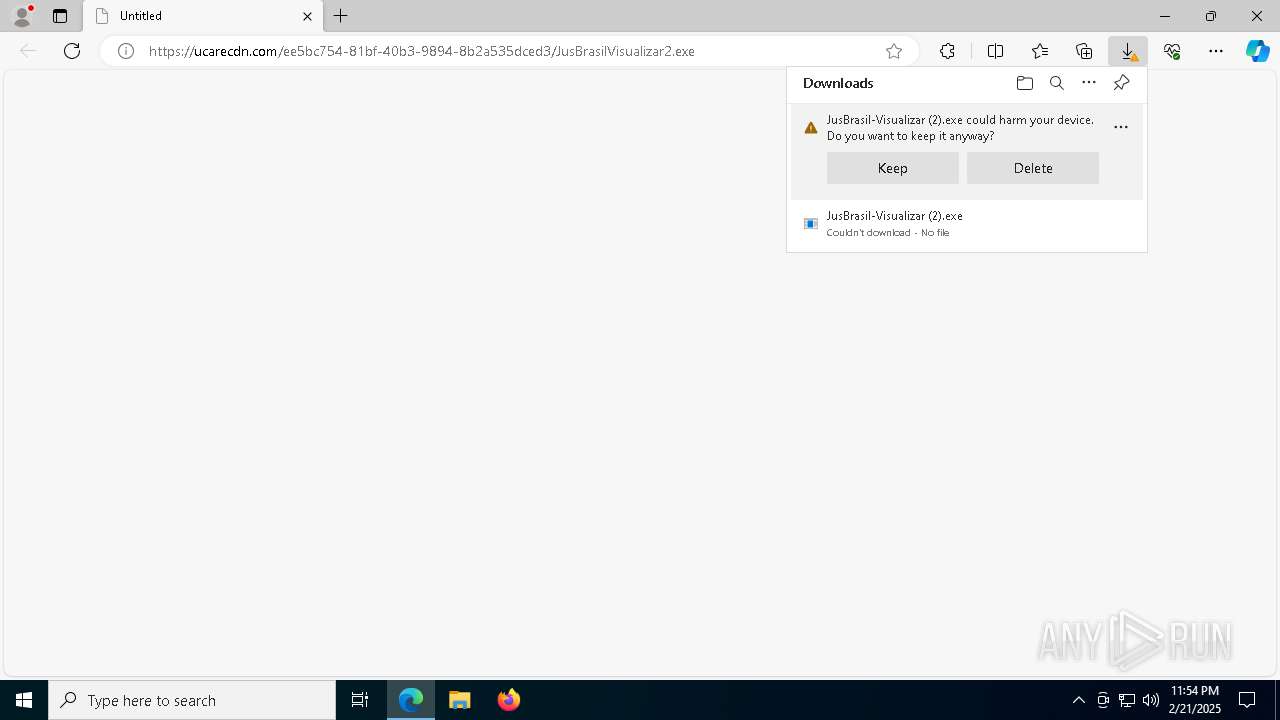
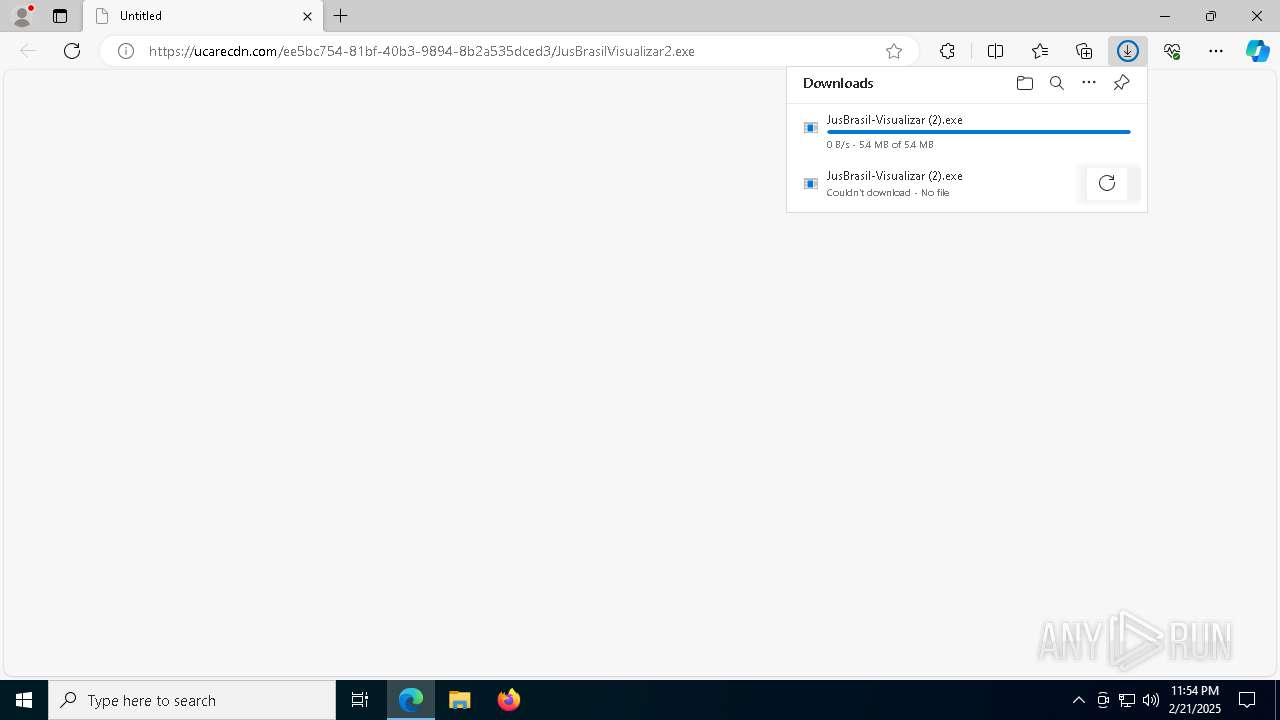
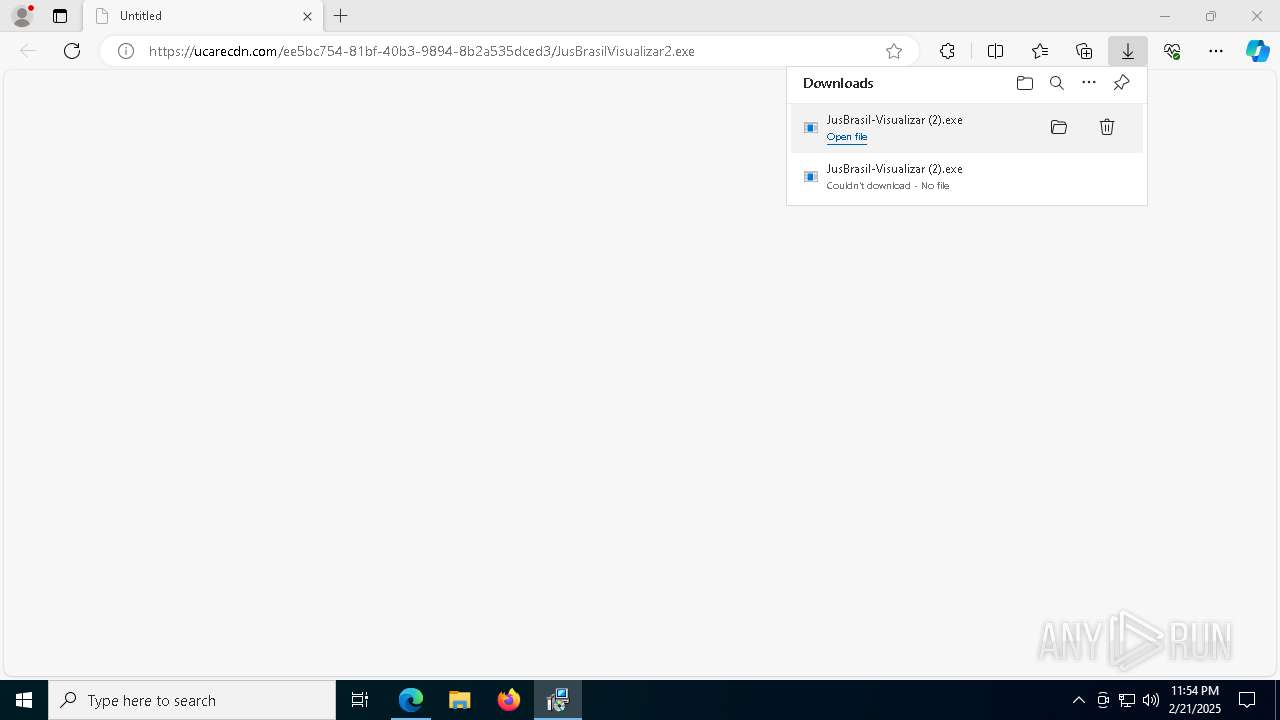
| URL: | https://ucarecdn.com/ee5bc754-81bf-40b3-9894-8b2a535dced3/JusBrasilVisualizar2.exe |
| Full analysis: | https://app.any.run/tasks/b0eef195-ade0-4071-9184-054596de7412 |
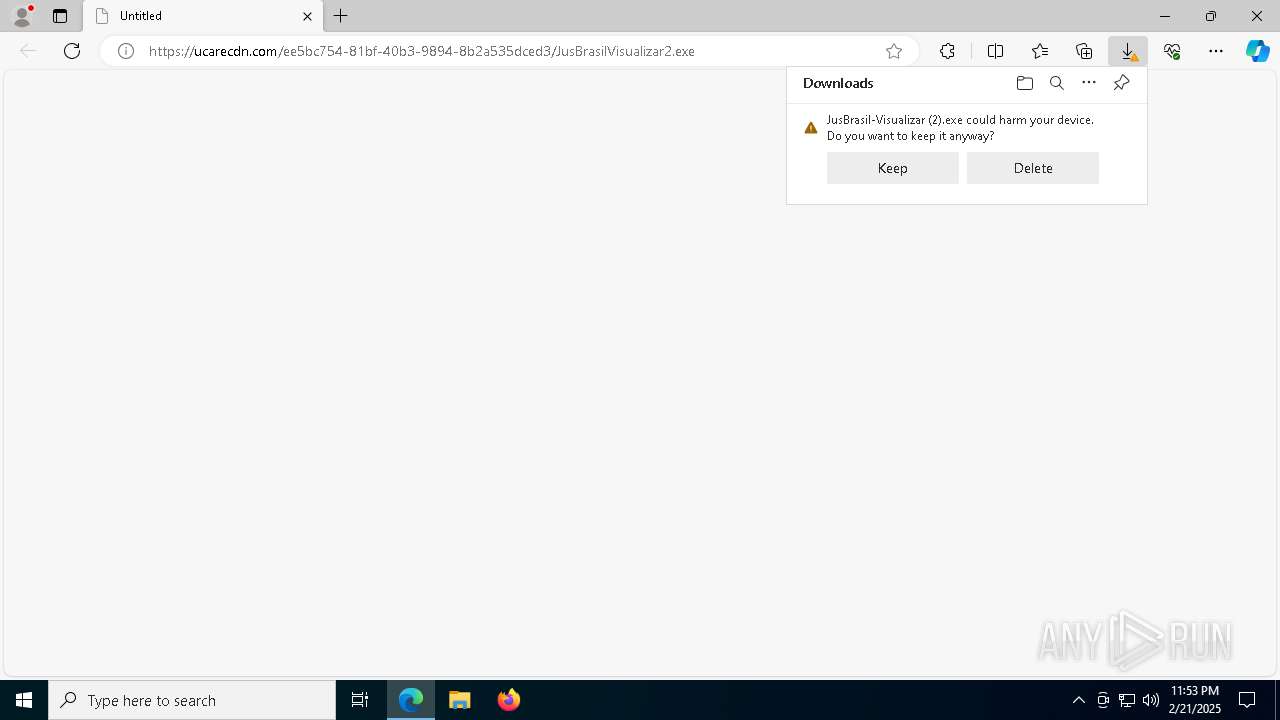
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2025, 23:53:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 73545440D2D16C144FC8DDC2A39FC5FF |
| SHA1: | B9C3A0620FE569E689F39B2D243D3F40E8081ECE |
| SHA256: | AB7107E649073F5A280DB87790AF0DE55A5077E6845D6710FC300E54615DA787 |
| SSDEEP: | 3:N8IGTbNqSeDsmcfli0bN:2ImNqSeIM0Z |
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 8144)
SUSPICIOUS
Reads security settings of Internet Explorer
- JusBrasil-Visualizar (2).exe (PID: 7064)
- ScreenConnect.ClientService.exe (PID: 8144)
- ScreenConnect.WindowsClient.exe (PID: 6932)
- ScreenConnect.WindowsClient.exe (PID: 7232)
Executable content was dropped or overwritten
- rundll32.exe (PID: 5040)
Executes as Windows Service
- VSSVC.exe (PID: 4540)
- ScreenConnect.ClientService.exe (PID: 8144)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4052)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 8144)
- ScreenConnect.ClientService.exe (PID: 8144)
- msiexec.exe (PID: 4052)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 8144)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 8144)
The process creates files with name similar to system file names
- msiexec.exe (PID: 4052)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 4052)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 8144)
INFO
Reads the computer name
- identity_helper.exe (PID: 7348)
- JusBrasil-Visualizar (2).exe (PID: 7064)
- msiexec.exe (PID: 4052)
- msiexec.exe (PID: 1804)
- msiexec.exe (PID: 5092)
- ScreenConnect.ClientService.exe (PID: 8144)
- ScreenConnect.WindowsClient.exe (PID: 6932)
- msiexec.exe (PID: 2796)
- ScreenConnect.WindowsClient.exe (PID: 7232)
Checks supported languages
- identity_helper.exe (PID: 7348)
- JusBrasil-Visualizar (2).exe (PID: 7064)
- msiexec.exe (PID: 5092)
- msiexec.exe (PID: 4052)
- msiexec.exe (PID: 1804)
- ScreenConnect.ClientService.exe (PID: 8144)
- ScreenConnect.WindowsClient.exe (PID: 6932)
- msiexec.exe (PID: 2796)
- ScreenConnect.WindowsClient.exe (PID: 7232)
Executable content was dropped or overwritten
- msedge.exe (PID: 6656)
- msedge.exe (PID: 6344)
- msiexec.exe (PID: 4052)
- msiexec.exe (PID: 628)
Reads the machine GUID from the registry
- JusBrasil-Visualizar (2).exe (PID: 7064)
- ScreenConnect.ClientService.exe (PID: 8144)
- ScreenConnect.WindowsClient.exe (PID: 6932)
- ScreenConnect.WindowsClient.exe (PID: 7232)
Reads Environment values
- identity_helper.exe (PID: 7348)
Create files in a temporary directory
- JusBrasil-Visualizar (2).exe (PID: 7064)
- rundll32.exe (PID: 5040)
Process checks computer location settings
- JusBrasil-Visualizar (2).exe (PID: 7064)
Application launched itself
- msedge.exe (PID: 6344)
Manages system restore points
- SrTasks.exe (PID: 1412)
Creates a software uninstall entry
- msiexec.exe (PID: 4052)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 7232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
174
Monitored processes
43
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.3.7.9067\7439252f0b2ba94f\ScreenConnect.ClientSetup.msi" | C:\Windows\SysWOW64\msiexec.exe | JusBrasil-Visualizar (2).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | C:\Windows\syswow64\MsiExec.exe -Embedding BBBC2415B3EFCBF12698E51CEFF6FA20 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2796 | C:\Windows\syswow64\MsiExec.exe -Embedding C8E746F9A5E44E673B7A88581F0D3D5B E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4052 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4704 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5780 --field-trial-handle=2064,i,6469184109215218599,16313114966758268864,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5040 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSIB2B9.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1291031 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5092 | C:\Windows\syswow64\MsiExec.exe -Embedding 95174D5D12913AB43C96A4B7FC9BAA2E | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 998
Read events
10 707
Write events
274
Delete events
17
Modification events
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CC2446FC458D2F00 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0DE54CFC458D2F00 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328418 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AD411BE7-4447-40A0-A2F7-1255237E2E5D} | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328418 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {56C1DB84-2308-43A4-93B3-341C1FFC178F} | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D6B45FFC458D2F00 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
32
Suspicious files
73
Text files
38
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF134e42.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF134e42.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF134e81.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF134e42.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF134e81.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
53
DNS requests
45
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6076 | svchost.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6076 | svchost.exe | GET | 200 | 95.101.54.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7300 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5740 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5740 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1224 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6076 | svchost.exe | 95.101.54.122:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6076 | svchost.exe | 104.79.89.142:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6076 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6656 | msedge.exe | 151.101.194.132:443 | ucarecdn.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ucarecdn.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
8144 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |