| File name: | C:\Users\admin\AppData\Roaming\Eclipse Media Inc\Installer Assistant\prerequisites\BESetup_EmuWC.msi |
| Full analysis: | https://app.any.run/tasks/72677c5f-b403-4a38-a546-ed80d867857b |
| Verdict: | Malicious activity |
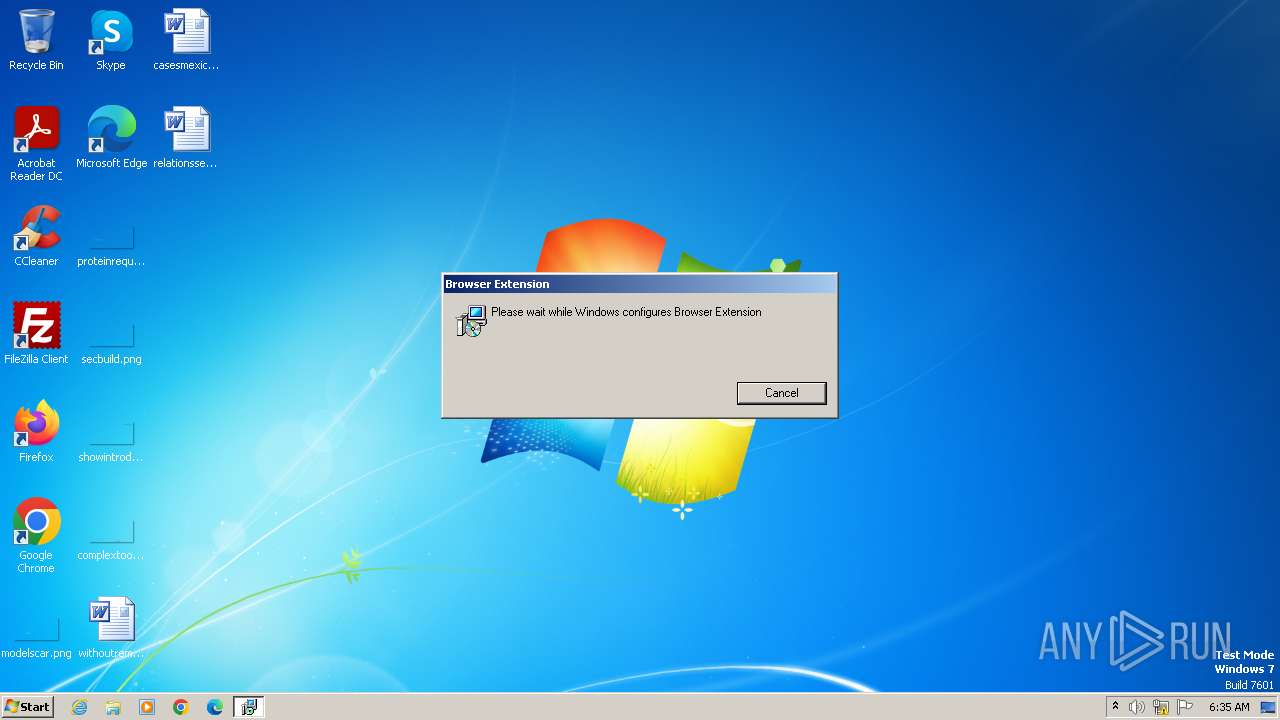
| Analysis date: | November 14, 2023, 06:35:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Security: 0, Code page: 1252, Revision Number: {347DDFE7-D4C1-434B-B9D7-54F76B22C03B}, Number of Words: 10, Subject: Browser Extension, Author: Blaze Media, Name of Creating Application: Advanced Installer 15.8 build b14c769f44, Template: ;1033, Comments: This installer database contains the logic and data required to install Browser Extension., Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | 2D9E93D7EFDD29091807122268863BAB |
| SHA1: | 79620E2CB35232C0E50D6A94FF02655F2DEA696B |
| SHA256: | AB6B3A30D643BD1A807D4415E554A7E005C9320D1ADBD0BFB4666CF1509C3078 |
| SSDEEP: | 49152:Cu4YW5T68otYLN4TFvr/7RaZADXGQt56YK1JeXl2ajKMIoDqc1lodL41YsxBMAd/:AY/NsAuewMInSlodL++36qlsljn6jNO |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 3484)
Bypass execution policy to execute commands
- powershell.exe (PID: 3768)
- powershell.exe (PID: 3676)
- powershell.exe (PID: 756)
- powershell.exe (PID: 1608)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 1592)
- powershell.exe (PID: 2644)
- powershell.exe (PID: 3824)
- powershell.exe (PID: 556)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 3912)
- MSIDD61.tmp (PID: 1936)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 2932)
Checks Windows Trust Settings
- msiexec.exe (PID: 3484)
The process executes Powershell scripts
- msiexec.exe (PID: 3912)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 3912)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 3912)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 3912)
- MSIDD61.tmp (PID: 1936)
Powershell version downgrade attack
- powershell.exe (PID: 3768)
- powershell.exe (PID: 1608)
- powershell.exe (PID: 3676)
- powershell.exe (PID: 756)
- powershell.exe (PID: 1592)
- powershell.exe (PID: 2644)
- powershell.exe (PID: 556)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 3824)
Reads the Internet Settings
- powershell.exe (PID: 3768)
- powershell.exe (PID: 1608)
- powershell.exe (PID: 1812)
- MSIDD61.tmp (PID: 1936)
- powershell.exe (PID: 556)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 3484)
Probably obfuscated PowerShell command line is found
- MSIDD61.tmp (PID: 1936)
Unusual connection from system programs
- powershell.exe (PID: 3768)
- powershell.exe (PID: 556)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 1608)
INFO
Checks supported languages
- msiexec.exe (PID: 3484)
- msiexec.exe (PID: 3912)
- wmpnscfg.exe (PID: 4072)
- 7za.exe (PID: 1208)
- MSIDD61.tmp (PID: 1936)
Reads the computer name
- msiexec.exe (PID: 3484)
- msiexec.exe (PID: 3912)
- wmpnscfg.exe (PID: 4072)
- 7za.exe (PID: 1208)
- MSIDD61.tmp (PID: 1936)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3440)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3484)
- msiexec.exe (PID: 3912)
- wmpnscfg.exe (PID: 4072)
Application launched itself
- msiexec.exe (PID: 3484)
Reads Environment values
- msiexec.exe (PID: 3912)
- MSIDD61.tmp (PID: 1936)
Create files in a temporary directory
- msiexec.exe (PID: 3912)
- msiexec.exe (PID: 3484)
Manual execution by a user
- wmpnscfg.exe (PID: 4072)
Creates files or folders in the user directory
- msiexec.exe (PID: 3484)
- 7za.exe (PID: 1208)
Starts application with an unusual extension
- msiexec.exe (PID: 3484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2009:12:11 11:47:44 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {347DDFE7-D4C1-434B-B9D7-54F76B22C03B} |
| Words: | 10 |
| Subject: | Browser Extension |
| Author: | Blaze Media |
| LastModifiedBy: | - |
| Software: | Advanced Installer 15.8 build b14c769f44 |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install Browser Extension. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Pages: | 200 |
Total processes
62
Monitored processes
16
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssD028.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssC003.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1208 | "C:\Users\admin\AppData\Roaming/Browser Extension/7za.exe" x Data.7z -y -p1.20.154.17755 | C:\Users\admin\AppData\Roaming\Browser Extension\7za.exe | — | powershell.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 1592 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy bypass -c "$w="$env:APPDATA"+'/Browser Extension/BE.txt';$h=Get-Content -Path $w -Raw;[byte[]]$bytes=($h -split '(.{2})' -ne '' -replace '^','0X');[Reflection.Assembly]::Load($bytes);[WebCompanion.BrowserExtension.S]::Start()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | MSIDD61.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssC816.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1812 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssD4EF.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | "C:\Windows\Installer\MSIDD61.tmp" /DontWait /HideWindow /dir "C:\Users\admin\AppData\Roaming\Browser Extension\" C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -ExecutionPolicy bypass -c "$w="$env:APPDATA"+'/Browser Extension/BE.txt';$h=Get-Content -Path $w -Raw;[byte[]]$bytes=($h -split '(.{2})' -ne '' -replace '^','0X');[Reflection.Assembly]::Load($bytes);[WebCompanion.BrowserExtension.S]::Start()" | C:\Windows\Installer\MSIDD61.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 15.8.0.0 Modules
| |||||||||||||||
| 2644 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssDE0B.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 574 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3440 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\BESetup_EmuWC.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
21 758
Read events
21 213
Write events
532
Delete events
13
Modification events
| (PID) Process: | (3440) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000F2B487BA16B0D901C80700002C0A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000F2B487BA16B0D901C80700002C0A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 72 | |||
| (PID) Process: | (3484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000008C62D6BA16B0D901C80700002C0A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Leave) |
Value: 400000000000000064514ABC16B0D901C80700002C0A0000D3070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Enter) |
Value: 400000000000000064514ABC16B0D901C80700002C0A0000D4070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Leave) |
Value: 400000000000000034645DBC16B0D901C80700002C0A0000D4070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Leave) |
Value: 4000000000000000781D5ABD16B0D901C80700002C0A0000D0070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Leave) |
Value: 4000000000000000781D5ABD16B0D901C80700002C0A0000D5070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
16
Suspicious files
39
Text files
37
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3912 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msiB124.tmp.txt | — | |
MD5:— | SHA256:— | |||
| 3912 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssB125.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 3912 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssB126.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 3912 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msiBAEC.tmp.txt | — | |
MD5:— | SHA256:— | |||
| 3912 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssBAED.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 3912 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssBAFE.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 3912 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msiBFF1.tmp.txt | — | |
MD5:— | SHA256:— | |||
| 3912 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssBFF2.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 3912 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssC003.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
8
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
556 | powershell.exe | POST | 200 | 52.222.206.199:80 | http://d3cv8ymwoql87l.cloudfront.net/ | unknown | binary | 19 b | unknown |
1812 | powershell.exe | POST | 200 | 52.222.206.199:80 | http://d3cv8ymwoql87l.cloudfront.net/ | unknown | binary | 19 b | unknown |
3768 | powershell.exe | POST | 200 | 52.222.206.199:80 | http://d3cv8ymwoql87l.cloudfront.net/ | unknown | binary | 19 b | unknown |
1608 | powershell.exe | POST | 200 | 52.222.206.199:80 | http://d3cv8ymwoql87l.cloudfront.net/ | unknown | binary | 19 b | unknown |
1812 | powershell.exe | POST | 200 | 52.222.206.199:80 | http://d3cv8ymwoql87l.cloudfront.net/ | unknown | binary | 19 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
868 | svchost.exe | 95.101.148.135:80 | — | Akamai International B.V. | NL | unknown |
3768 | powershell.exe | 52.222.206.199:80 | d3cv8ymwoql87l.cloudfront.net | AMAZON-02 | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 184.30.20.134:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1608 | powershell.exe | 52.222.206.199:80 | d3cv8ymwoql87l.cloudfront.net | AMAZON-02 | US | unknown |
556 | powershell.exe | 52.222.206.199:80 | d3cv8ymwoql87l.cloudfront.net | AMAZON-02 | US | unknown |
1812 | powershell.exe | 52.222.206.199:80 | d3cv8ymwoql87l.cloudfront.net | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d3cv8ymwoql87l.cloudfront.net |
| unknown |
armmf.adobe.com |
| whitelisted |