| URL: | http://anglerola.msk.ru |
| Full analysis: | https://app.any.run/tasks/61b0a575-90e2-4980-86da-5eaba4f4d0a6 |
| Verdict: | No threats detected |
| Analysis date: | September 17, 2020, 19:09:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 388B60DB9197E46A92B302E6C7F8DB82 |
| SHA1: | AB82917C58940792852138832D3D539330210D26 |
| SHA256: | AB63EF6012D379AED106D8F5C17241E3898AC8269DD2F688CDE88B5FA13312F9 |
| SSDEEP: | 3:N1Kf243EAn:CX3EAn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3948)
INFO
Application launched itself
- chrome.exe (PID: 3948)
Reads the hosts file
- chrome.exe (PID: 3948)
- chrome.exe (PID: 668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7834812376780964548 --mojo-platform-channel-handle=1556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3932 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9407275140710359597 --mojo-platform-channel-handle=1928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8582750043209771493 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2800 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9327821896845659759 --mojo-platform-channel-handle=2804 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5118170735284456090 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5038278863904307350 --mojo-platform-channel-handle=2724 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4353552913985042074 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13163249468381893621 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12790279909056753458 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3324 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
649
Read events
574
Write events
71
Delete events
4
Modification events
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3948-13244843356757125 |
Value: 259 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3948-13244843356757125 |
Value: 259 | |||
Executable files
0
Suspicious files
33
Text files
171
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8933c4c9-2127-4a5f-b8cf-66237d63e270.tmp | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFed6b4.TMP | text | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFed695.TMP | text | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFed85a.TMP | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFed712.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
64
DNS requests
32
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
668 | chrome.exe | GET | 304 | 67.27.158.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
668 | chrome.exe | GET | 302 | 217.174.105.4:80 | http://anglerola.msk.ru/ | RU | html | 654 b | suspicious |
668 | chrome.exe | GET | 200 | 50.28.0.84:80 | http://cpxtri.com/redirect?sid=76104 | US | html | 21.3 Kb | suspicious |
668 | chrome.exe | GET | 302 | 50.28.0.84:80 | http://cpxtri.com/redirect?cid=oOWmuwVInH&http_referer=&sid=76104&subid=&s3=&10f37c88406fdf6fcba17a39f864a856=1&rr=1&id=&t=1600369765&hrf=05GldGACjtJLMA09ZYfxgsyQNRzyJ%2Ffud%2B8SkvN4sunO77UBcfY%3D&iwx=1280&iwy=572&owx=1280&owy=692&isph=0&pbc=0&fp=null&hf=1&op=1&pd=24&tp=%3F&xd=%3F&yd=%3F&pl=3&mt=4&sw=1280&sh=692&fw=1280&fh=720&pw=0&ph=0&ow=1280x692&iw=1280x572&sd=24&ifr=0&coo=1&m=0&hr=1&ab=1&ua=%257B%2522ef%2522%253A%25223g%2522%252C%2522rtt%2522%253A650%252C%2522down%2522%253A1.35%252C%2522save%2522%253Afalse%257D&npl=Win32&ncpu=%3F&nhc=4>z=-60&nba=1&nbt=0&nve=Google+Inc.&vapp=Netscape&napv=5.0+%28Windows+NT+6.1%29+AppleWebKit%2F537.36+%28KHTML%2C+like+Gecko%29+Chrome%2F75.0.3770.100+Safari%2F537.36&ss=1&ls=1&bl=en-US&sl=undefined&dr=Google%2520Inc.%257CGoogle%2520SwiftShader%257CWebGL%25201.0%2520%28OpenGL%2520ES%25202.0%2520Chromium%29&is=1972814972&wc=object&msy=undefined&ddm=undefined&ps=20030107&st=0&sp=undefined&mob=0&ifp1=0&ifp2=0&wn=&nap=0&ind=1&opd=1&dab=0&nsb=1&chk1=0&chk2=1&chk3=0&chk4=0 | US | html | 21.3 Kb | suspicious |
668 | chrome.exe | GET | 200 | 185.180.12.141:80 | http://r2---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=185.183.107.236&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1600369695&mv=m&mvi=2&pl=24&shardbypass=yes | AT | crx | 834 Kb | whitelisted |
668 | chrome.exe | GET | 200 | 50.28.0.84:80 | http://adskpak.com/redirect?sid=76104 | US | html | 21.3 Kb | whitelisted |
668 | chrome.exe | GET | 200 | 67.27.158.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
668 | chrome.exe | GET | 303 | 54.210.16.35:80 | http://p.zetadeo.com/ad/ad?p=282033&w=579134&t=09a059f2d88de094&r=aHR0cHMlM0EvL25wb3JuLnRvcC9pbmRleA==&vw=1280&vh=572 | US | html | 79 b | suspicious |
668 | chrome.exe | GET | 200 | 54.210.16.35:80 | http://p.zetadeo.com/go/282033/579134/aHR0cHMlM0EvL25wb3JuLnRvcC9pbmRleA==?cb= | US | html | 305 b | suspicious |
668 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 545 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
668 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
668 | chrome.exe | 217.174.105.4:80 | anglerola.msk.ru | e-Style ISP LLC | RU | unknown |
668 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 217.174.105.4:80 | anglerola.msk.ru | e-Style ISP LLC | RU | unknown |
668 | chrome.exe | 195.64.185.10:443 | nporn.top | delta-x Ltd | UA | suspicious |
668 | chrome.exe | 50.28.0.84:80 | adskpak.com | Liquid Web, L.L.C | US | suspicious |
668 | chrome.exe | 54.210.16.35:80 | p.zetadeo.com | Amazon.com, Inc. | US | suspicious |
668 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
668 | chrome.exe | 172.217.18.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
668 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
anglerola.msk.ru |
| suspicious |
adskpak.com |
| whitelisted |
www.google.com |
| malicious |
cpxtri.com |
| suspicious |
nporn.top |
| suspicious |
ssl.gstatic.com |
| whitelisted |
p.zetadeo.com |
| suspicious |
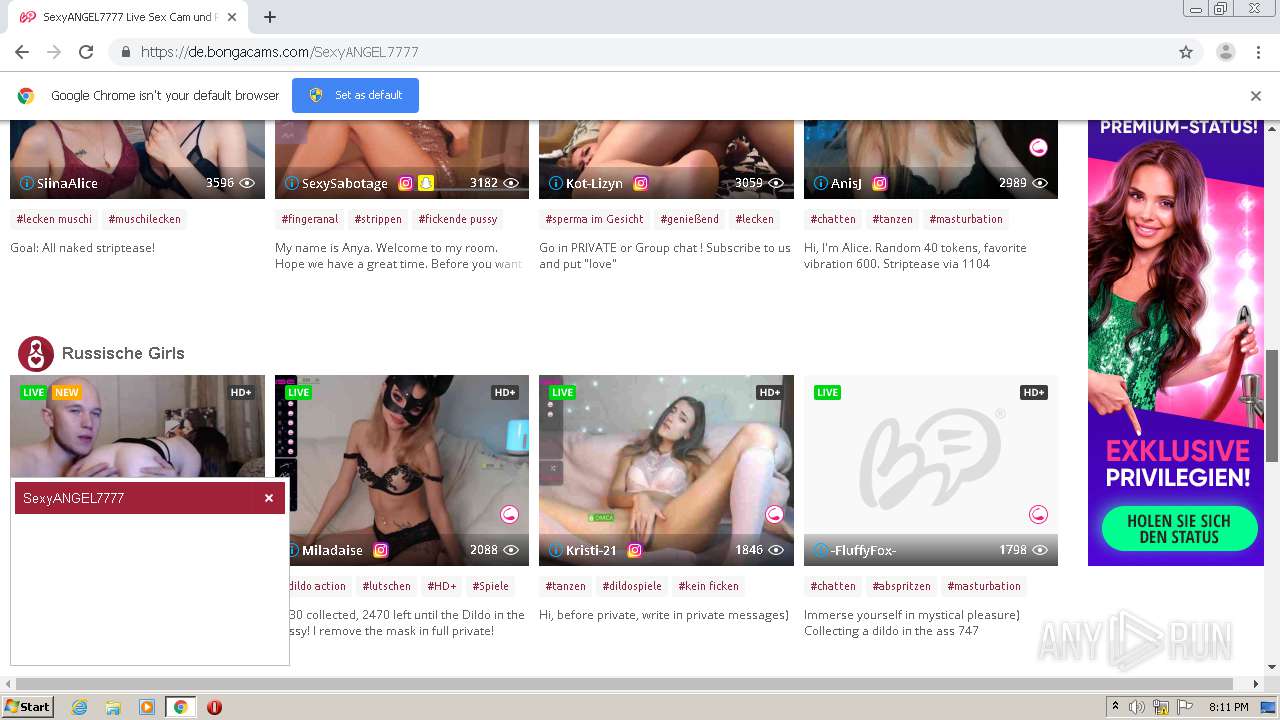
bongacams.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
668 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
668 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |