| File name: | ryujinx-canary-1.2.68-win_x64.zip |
| Full analysis: | https://app.any.run/tasks/7dd28baa-9653-4f1b-a027-7d269eacbddf |
| Verdict: | Malicious activity |
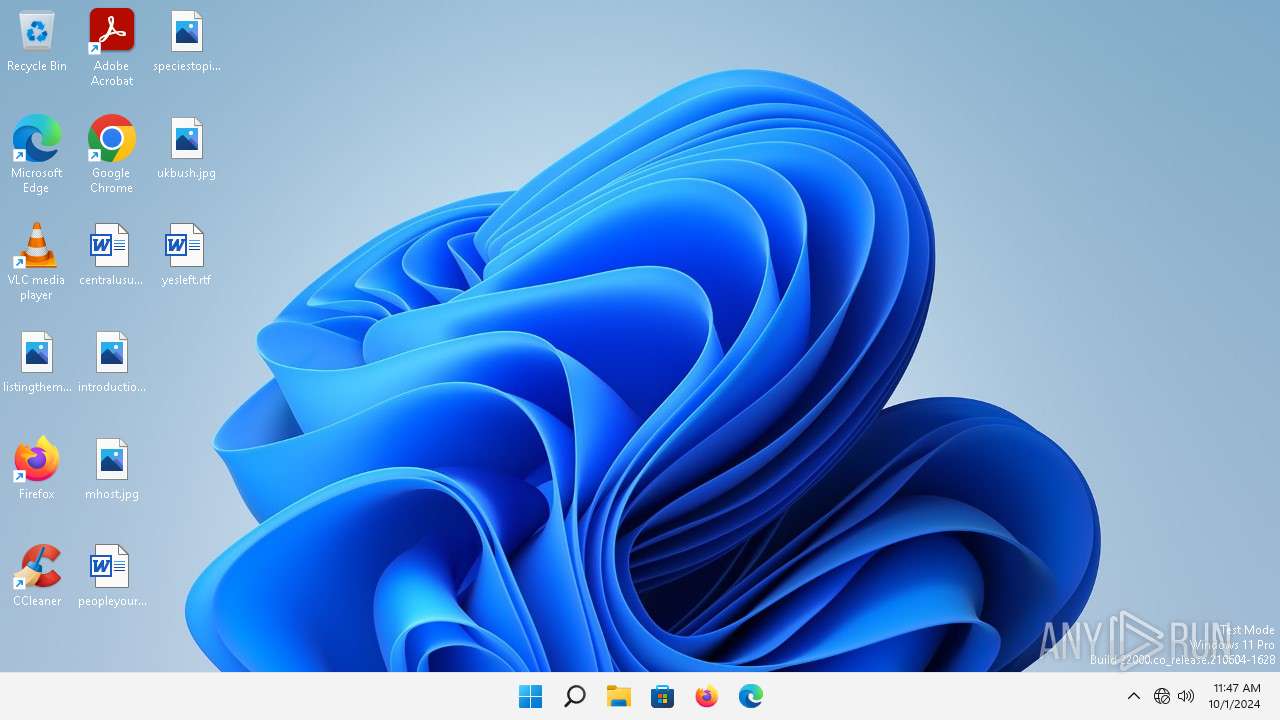
| Analysis date: | November 30, 2024, 13:19:06 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
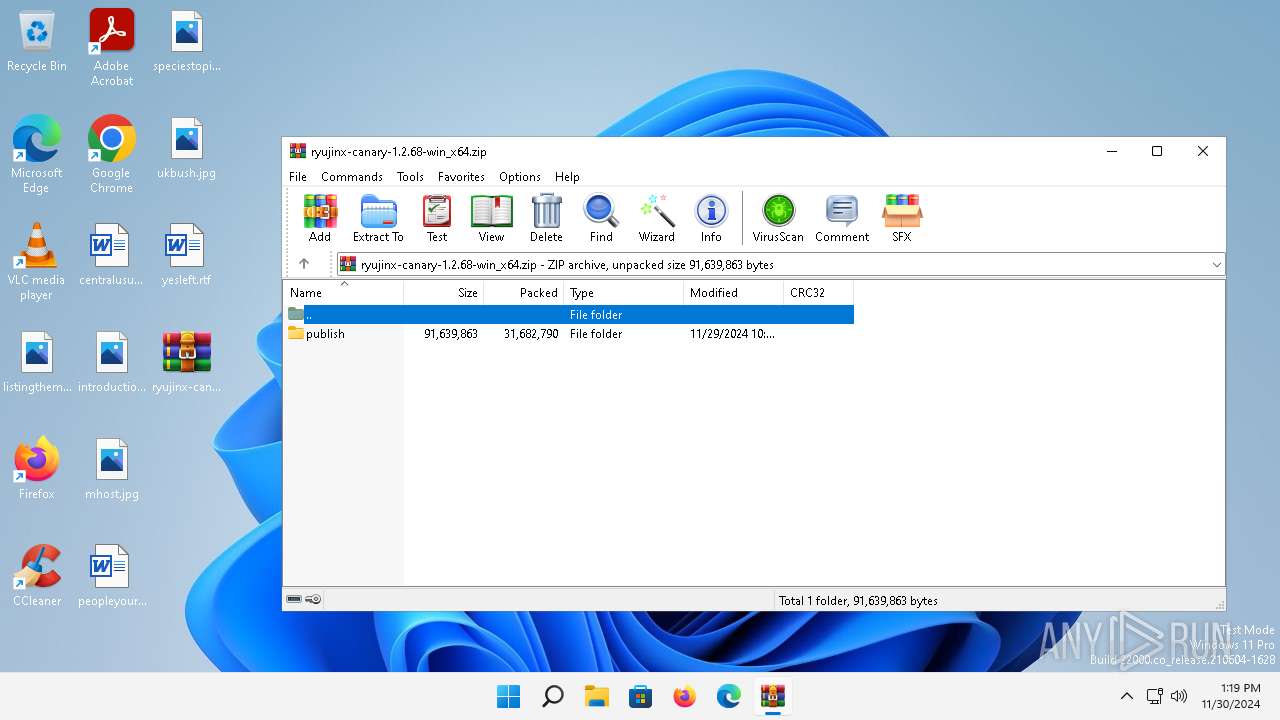
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 1381198C6F1F9CB3475EB97EE41B1792 |
| SHA1: | 1B91567639AD82E261FC4CBD65309E1FFA8DB1D2 |
| SHA256: | AB4A25D503678CBE5BE8A9E8FD158E7B29C964AA1757BF53FF197AE2F0906E2F |
| SSDEEP: | 196608:mWyChlCvAjQO7dncjRqtSaofVV07pE8MF/huI27hOiUIOZeTKIdUErf:mWFHCo15c4tMP0pExuv7hOiUIIeFdUc |
MALICIOUS
No malicious indicators.SUSPICIOUS
Generic archive extractor
- WinRAR.exe (PID: 1564)
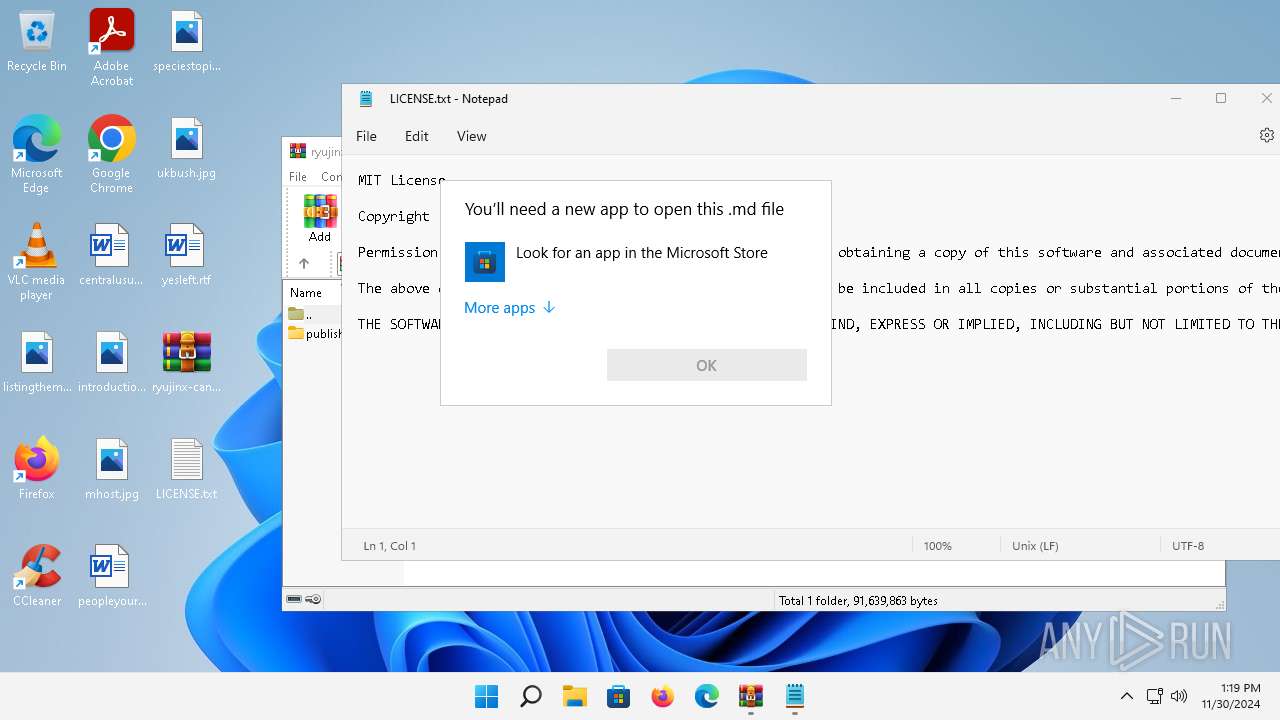
Reads the Internet Settings
- Notepad.exe (PID: 6772)
- OpenWith.exe (PID: 4316)
- OpenWith.exe (PID: 5776)
- OpenWith.exe (PID: 6596)
- WerFault.exe (PID: 3712)
Reads security settings of Internet Explorer
- Notepad.exe (PID: 6772)
Executes application which crashes
- rundll32.exe (PID: 1220)
The process creates files with name similar to system file names
- WerFault.exe (PID: 3712)
INFO
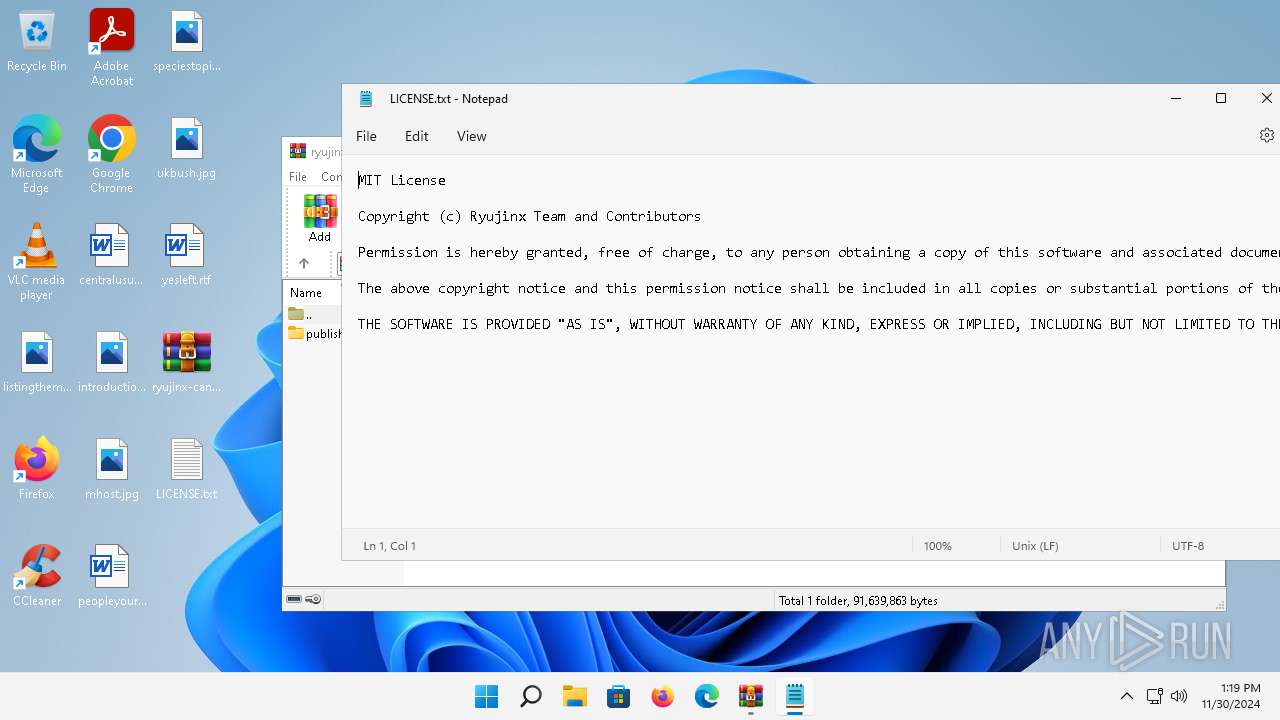
Manual execution by a user
- Notepad.exe (PID: 6772)
- OpenWith.exe (PID: 4316)
- OpenWith.exe (PID: 5776)
- rundll32.exe (PID: 1288)
- OpenWith.exe (PID: 6596)
- rundll32.exe (PID: 1220)
- rundll32.exe (PID: 6236)
Checks supported languages
- Notepad.exe (PID: 6772)
Reads the computer name
- Notepad.exe (PID: 6772)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 4316)
- OpenWith.exe (PID: 6596)
- OpenWith.exe (PID: 5776)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4316)
- OpenWith.exe (PID: 6596)
- OpenWith.exe (PID: 5776)
Checks proxy server information
- WerFault.exe (PID: 3712)
Reads the software policy settings
- WerFault.exe (PID: 3712)
Creates files or folders in the user directory
- WerFault.exe (PID: 3712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:11:29 22:35:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | publish/ |
Total processes
123
Monitored processes
9
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1220 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\Desktop\avutil-57.dll, #1 | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225477 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1288 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\Desktop\libsoundio.dll, #1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1564 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\ryujinx-canary-1.2.68-win_x64.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3712 | C:\Windows\system32\WerFault.exe -u -p 1220 -s 352 | C:\Windows\System32\WerFault.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.22000.348 (WinBuild.160101.0800) Modules
| |||||||||||||||
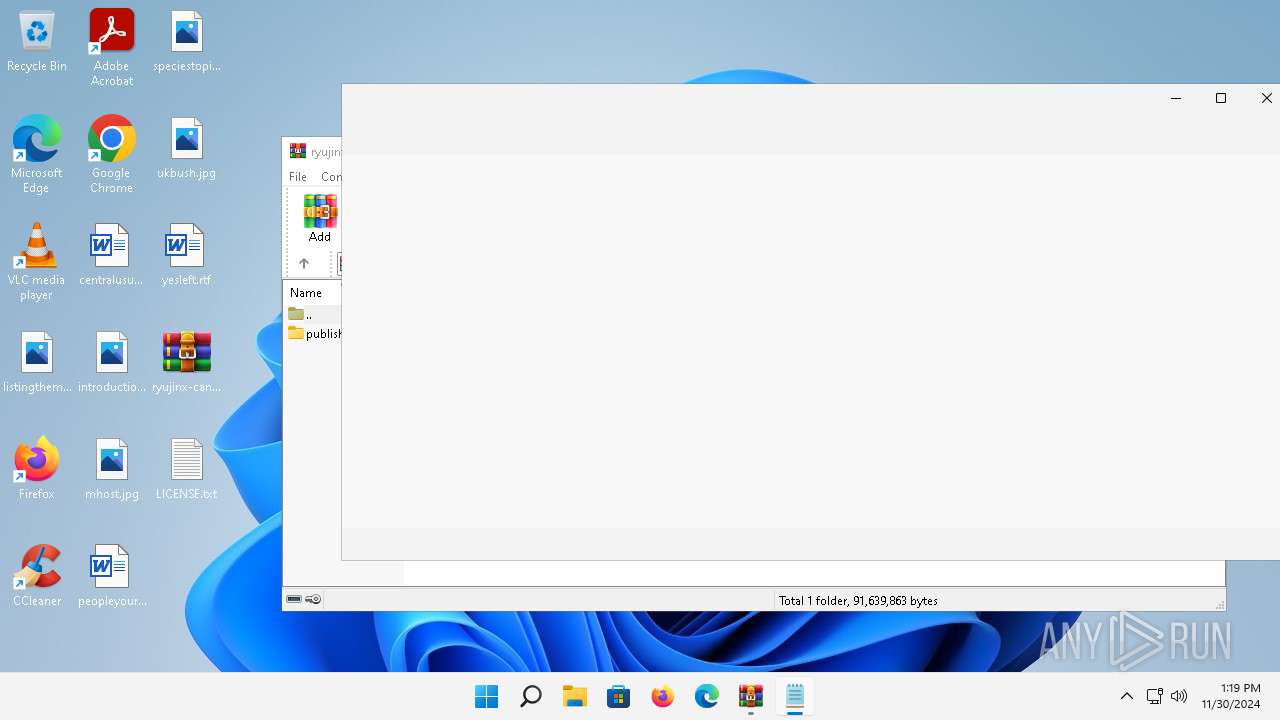
| 4316 | "C:\Windows\System32\OpenWith.exe" C:\Users\admin\Desktop\THIRDPARTY.md | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
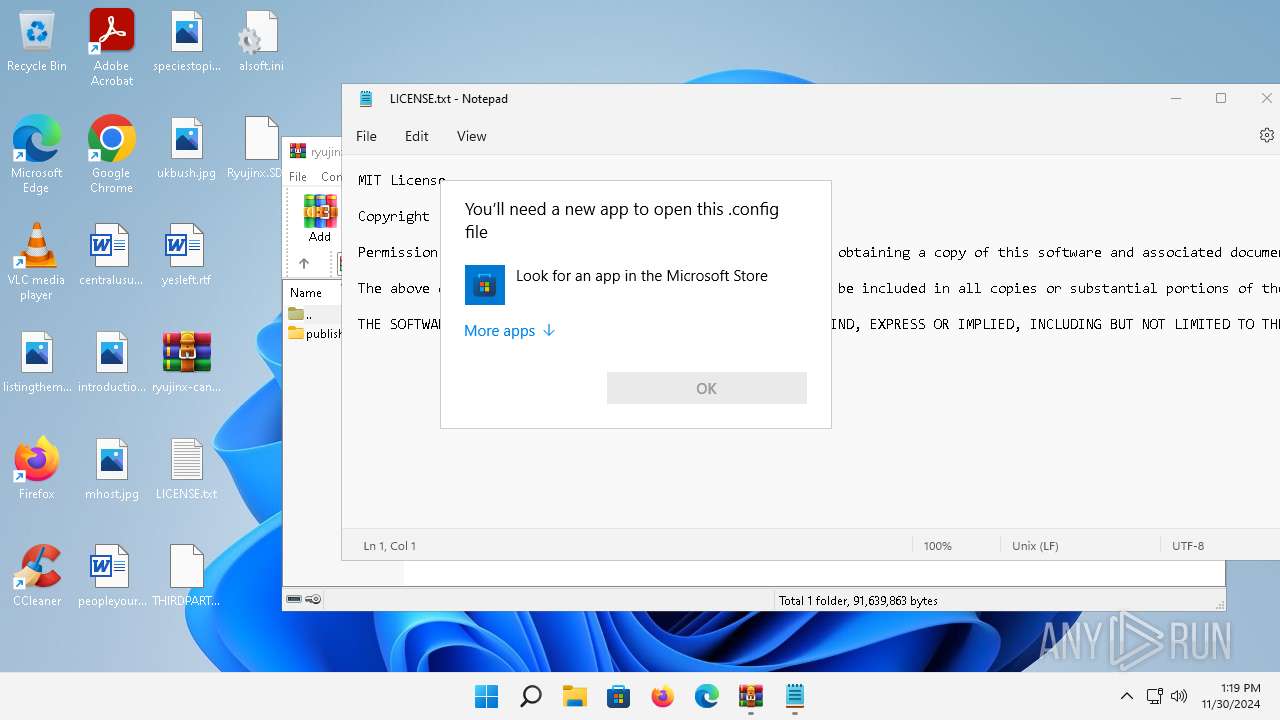
| 5776 | "C:\Windows\System32\OpenWith.exe" C:\Users\admin\Desktop\Ryujinx.SDL2.Common.dll.config | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6236 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\Desktop\glfw3.dll, #1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6596 | "C:\Windows\System32\OpenWith.exe" C:\Users\admin\Desktop\alsoft.ini | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6772 | "C:\Windows\system32\notepad.exe" C:\Users\admin\Desktop\LICENSE.txt | C:\Program Files\WindowsApps\Microsoft.WindowsNotepad_11.2205.11.0_x64__8wekyb3d8bbwe\Notepad\Notepad.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
12 586
Read events
12 577
Write events
9
Delete events
0
Modification events
| (PID) Process: | (1564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ryujinx-canary-1.2.68-win_x64.zip | |||
| (PID) Process: | (1564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3712 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_avu_1748365b281afdbec44c4fafcdec392fe368e43_3599c531_8bbf62e6-9fc5-4687-a864-0ec4a14fffc5\Report.wer | — | |
MD5:— | SHA256:— | |||
| 3712 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER.5bc26eb4-9574-4008-a513-2073e3b87a43.tmp.dmp | binary | |
MD5:98F21DE301ED255C443EC661DE68E370 | SHA256:71963D308AD7B10FA62F219AFB720B770416A05F1561A35C6BF22619E3D2F55E | |||
| 3712 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER.f26a554f-3ed4-45d0-b65b-925bcc05ad53.tmp.xml | xml | |
MD5:A4296CE5C53CF3D7C2034812B6304926 | SHA256:BFAE64E8B440A8F4DE2353C9CF7D2DEDFB0C9D2AD1192B7B47EE443D896D6D10 | |||
| 3712 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER.32d555ec-dc52-4341-9b3f-47f27eecdde7.tmp.WERInternalMetadata.xml | xml | |
MD5:33508C9443EB3D1F01CEA6D6FBBC3DD3 | SHA256:106B38AF26C70B752B19F7FD2D8693B148F5801AC66761EFE29A4A7DD601D882 | |||
| 3712 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\rundll32.exe.1220.dmp | binary | |
MD5:5A0F6308CC1299D8ADB8B5F1EB6CF64A | SHA256:76E8D85B4DC6DC3B927F5A342CD548908AE128494FD745E18E564D3FCA833117 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
43
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1600 | MoUsoCoreWorker.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c2349bb04ba7ddf3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.18.64.212:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.213.164.137:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
2860 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?ca35b9155f2b6b6f | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.67:443 | https://login.live.com/RST2.srf | unknown | xml | 10.7 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.69:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.75:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | GET | 200 | 52.113.194.132:443 | https://ecs.office.com/config/v2/Office/officeclicktorun/16.0.16626.20134/Production/CC?&Clientid=%7b80C2A92B-EDEE-479E-8470-DBC6C547F2FB%7d&Application=officeclicktorun&Platform=win32&Version=16.0.16626.20134&MsoVersion=16.0.16626.20134&ProcessName=officec2rclient.exe&Audience=Production&Build=ship&Architecture=x64&OsVersion=10.0&OsBuild=22000&Channel=CC&InstallType=C2R&SessionId=%7bE4048F24-6552-49EE-944D-9B6F70179389%7d&LabMachine=false | unknown | binary | 79.1 Kb | whitelisted |
— | — | POST | 400 | 20.190.159.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 210 b | whitelisted |
— | — | POST | 200 | 20.190.159.23:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5668 | rundll32.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1948 | OfficeC2RClient.exe | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
— | — | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
— | — | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
— | — | 2.18.64.212:80 | — | Administracion Nacional de Telecomunicaciones | UY | unknown |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1600 | MoUsoCoreWorker.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
5056 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
login.live.com |
| whitelisted |
ecs.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |