| File name: | x64_x32_installer__v4.2.2.msi |
| Full analysis: | https://app.any.run/tasks/b08d6d0f-21d1-45ae-a8f7-5bb79db95f47 |
| Verdict: | Malicious activity |
| Analysis date: | August 23, 2024, 16:47:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
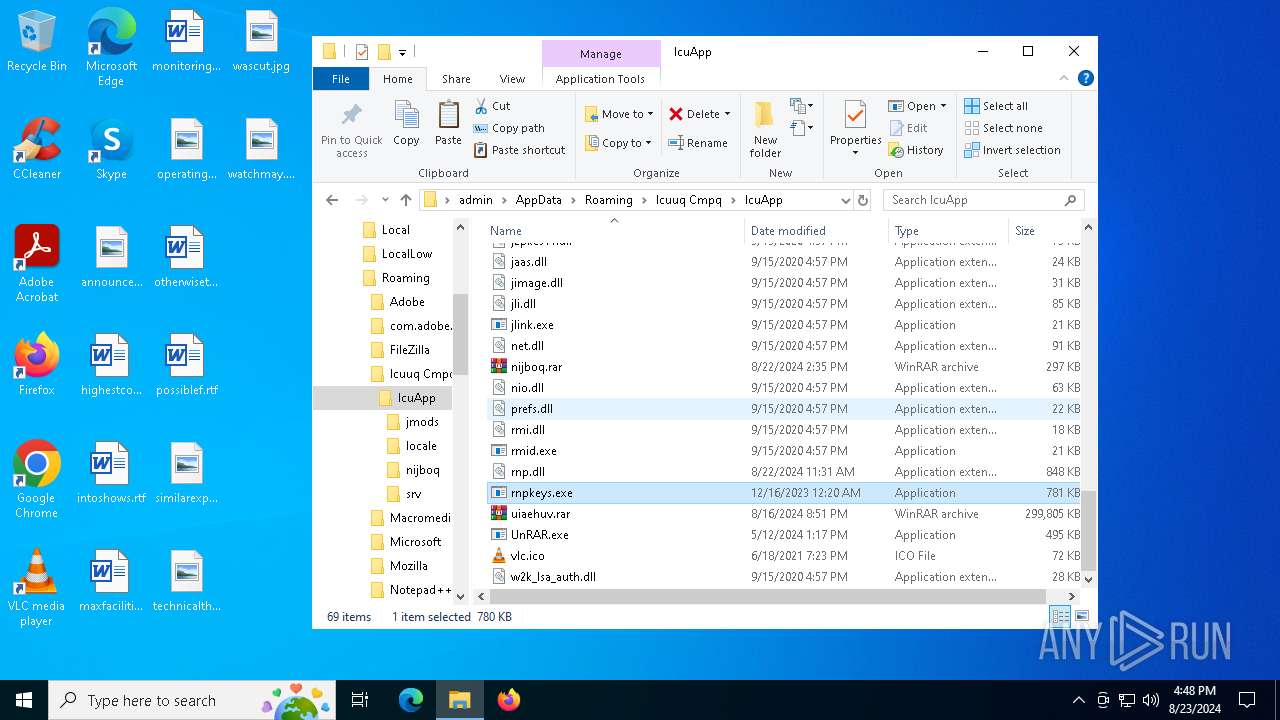
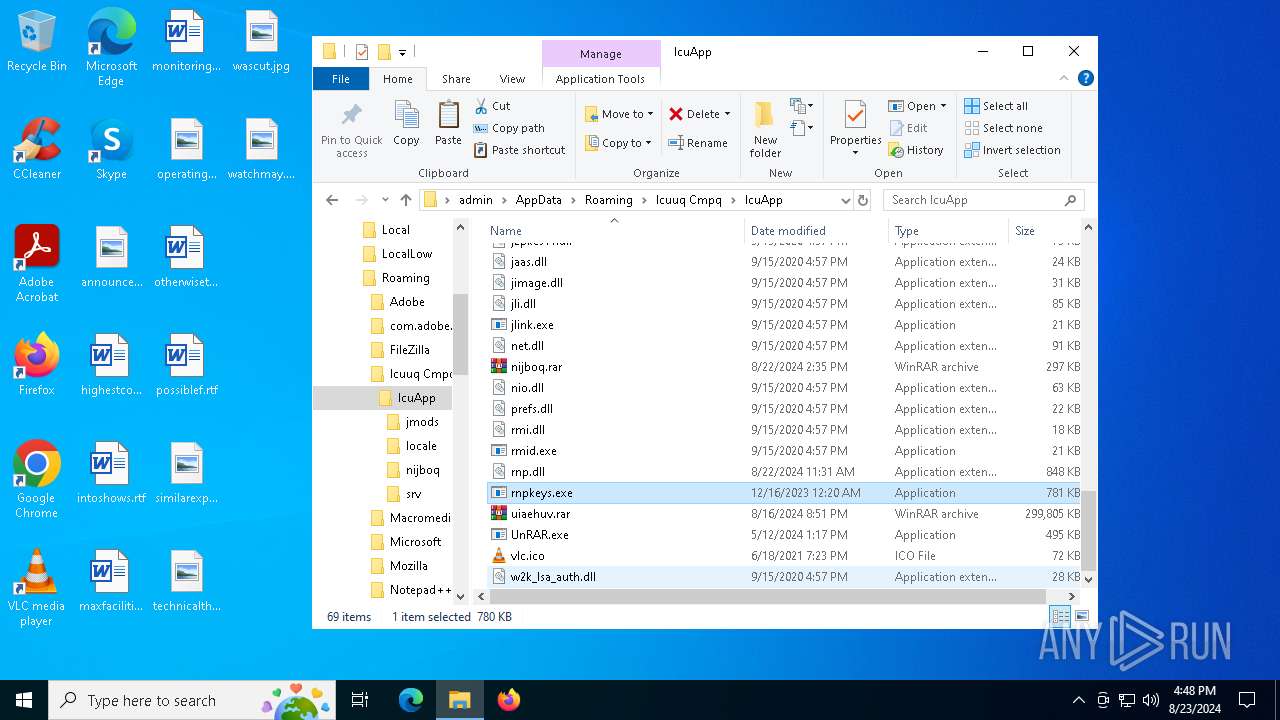
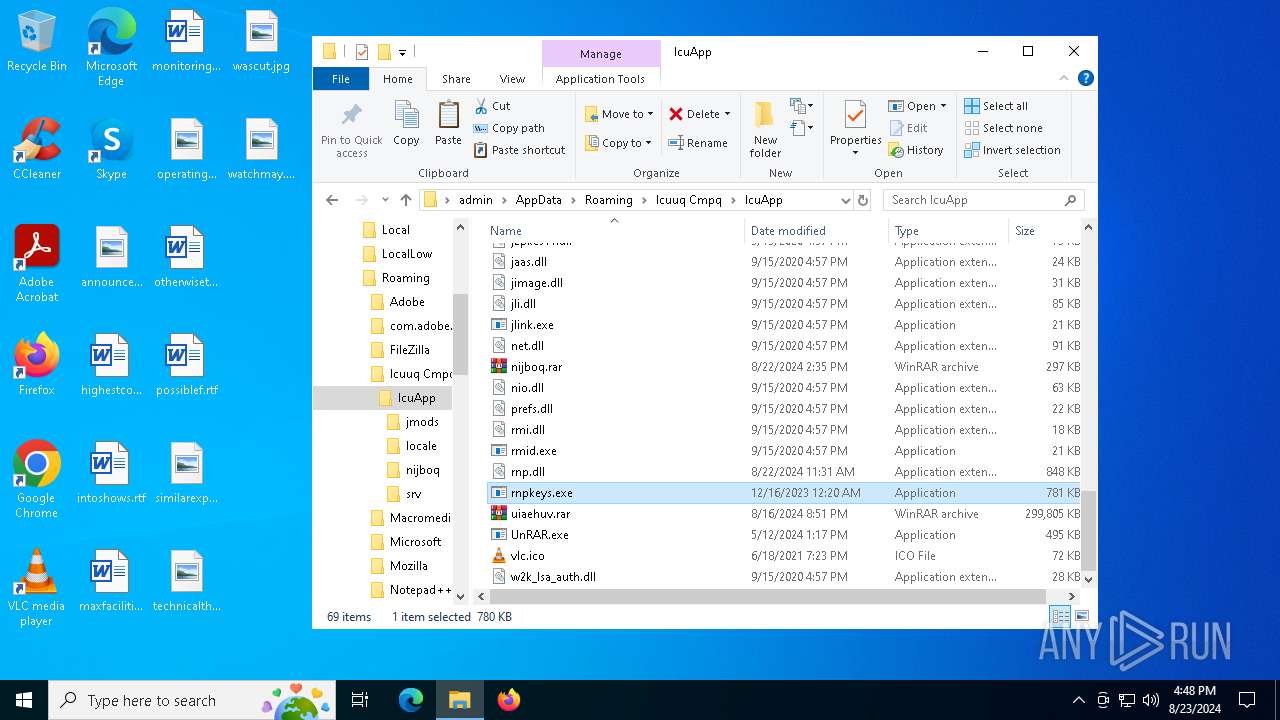
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {A06E125F-2A1D-4491-AE35-1E59BECF7A5D}, Number of Words: 10, Subject: IcuApp, Author: Icuuq Cmpq, Name of Creating Application: IcuApp, Template: x64;2057, Comments: This installer database contains the logic and data required to install IcuApp., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Thu Aug 22 11:36:04 2024, Last Saved Time/Date: Thu Aug 22 11:36:04 2024, Last Printed: Thu Aug 22 11:36:04 2024, Number of Pages: 450 |
| MD5: | B8DA67923E70736F23F50E188B9B12A9 |
| SHA1: | C695C02AD88616D21F730C1248E885E1849C9671 |
| SHA256: | AB31AF0388712C0DC00D974B15EE40888D3D65207FD81FA5148A832186C60504 |
| SSDEEP: | 196608:rnKDHPKOFfXWZQHvOJgdbOIkVBqjgnMn86M0WFd5ljUaWR261zVzg:2rJZm7xBJnM86Q/BUaW/Jpg |
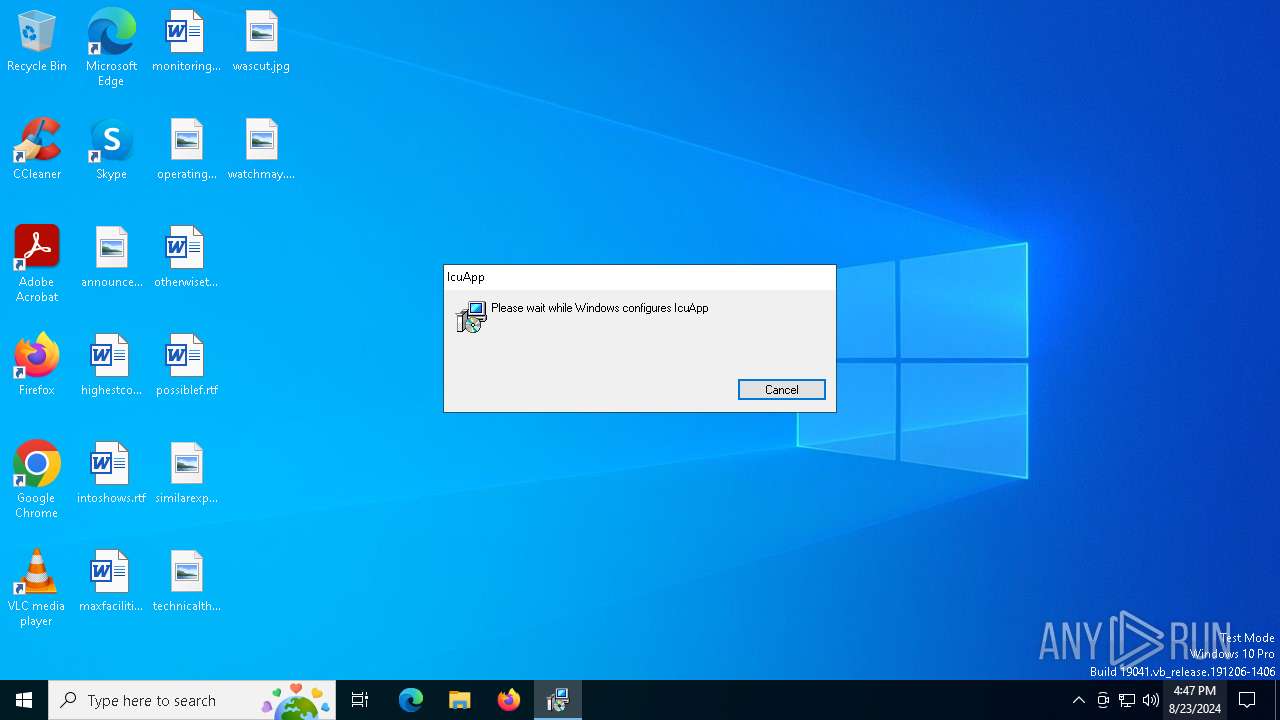
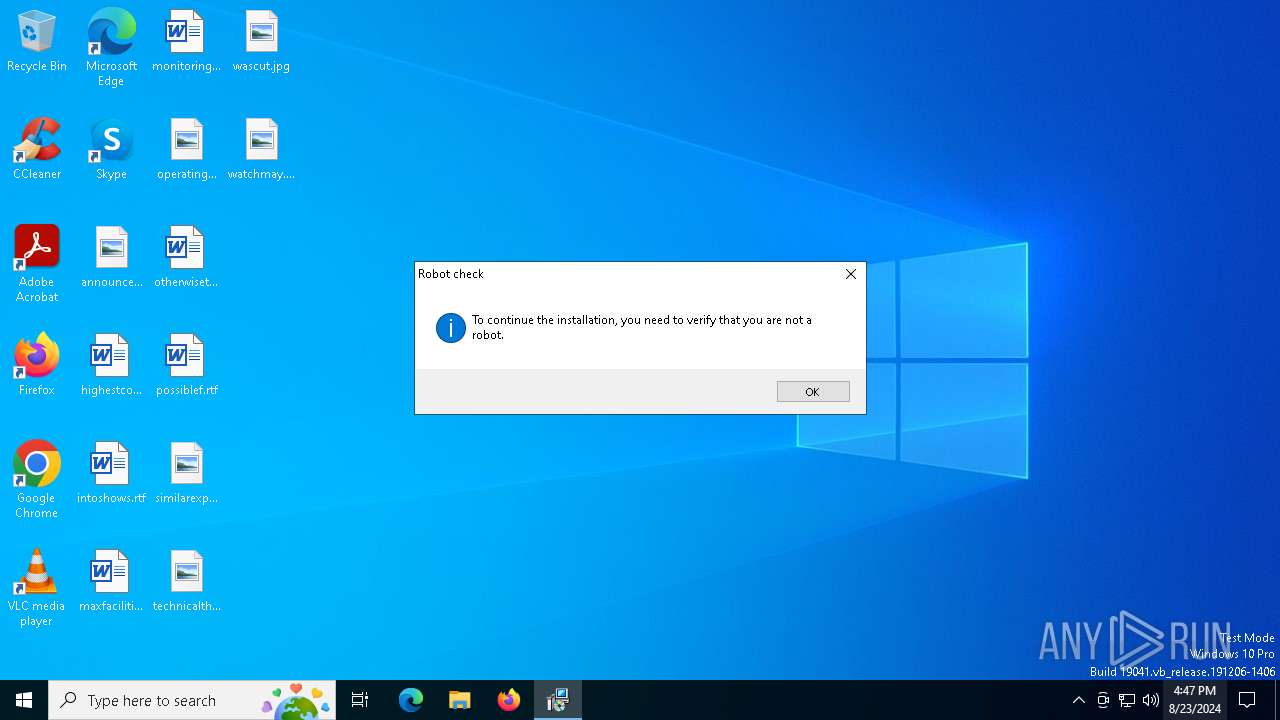
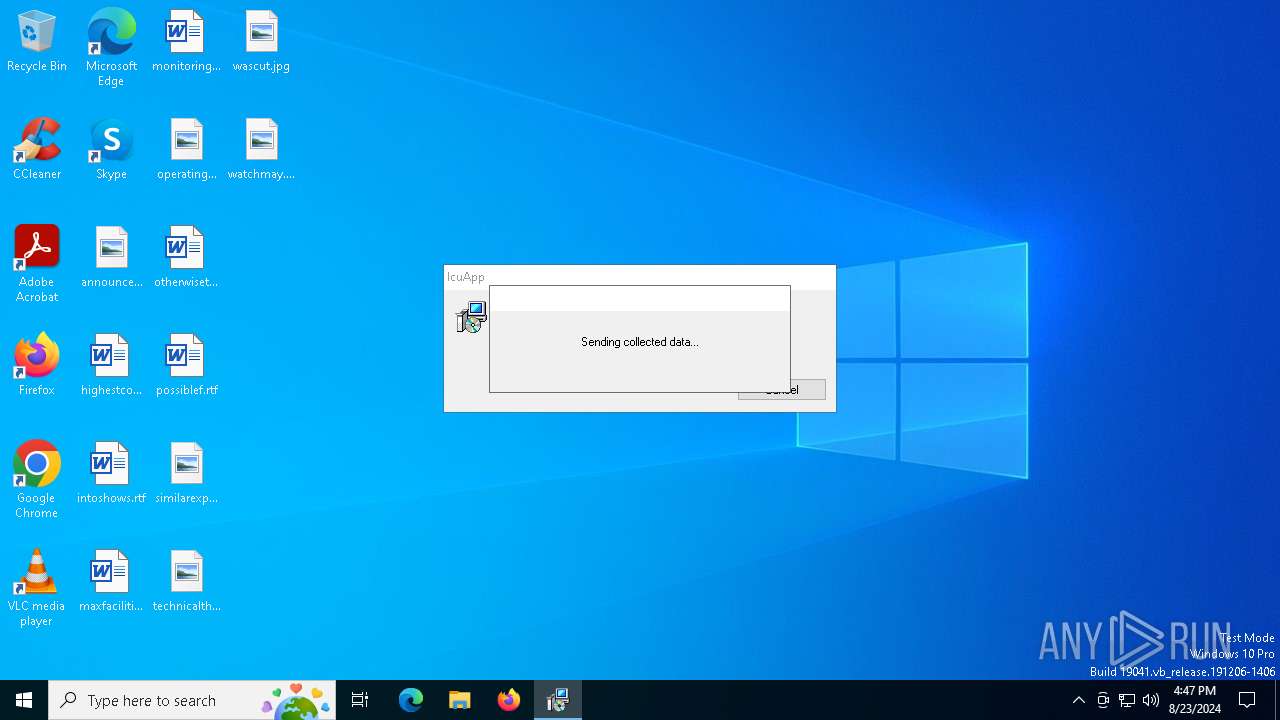
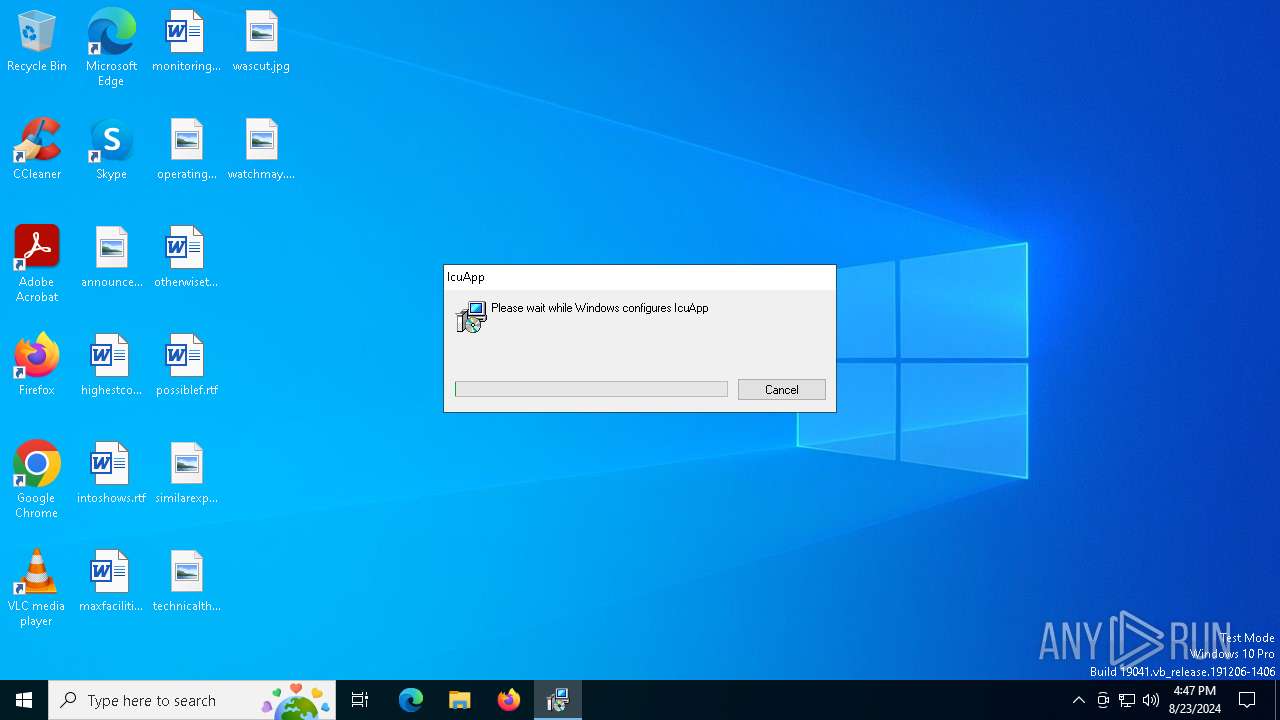
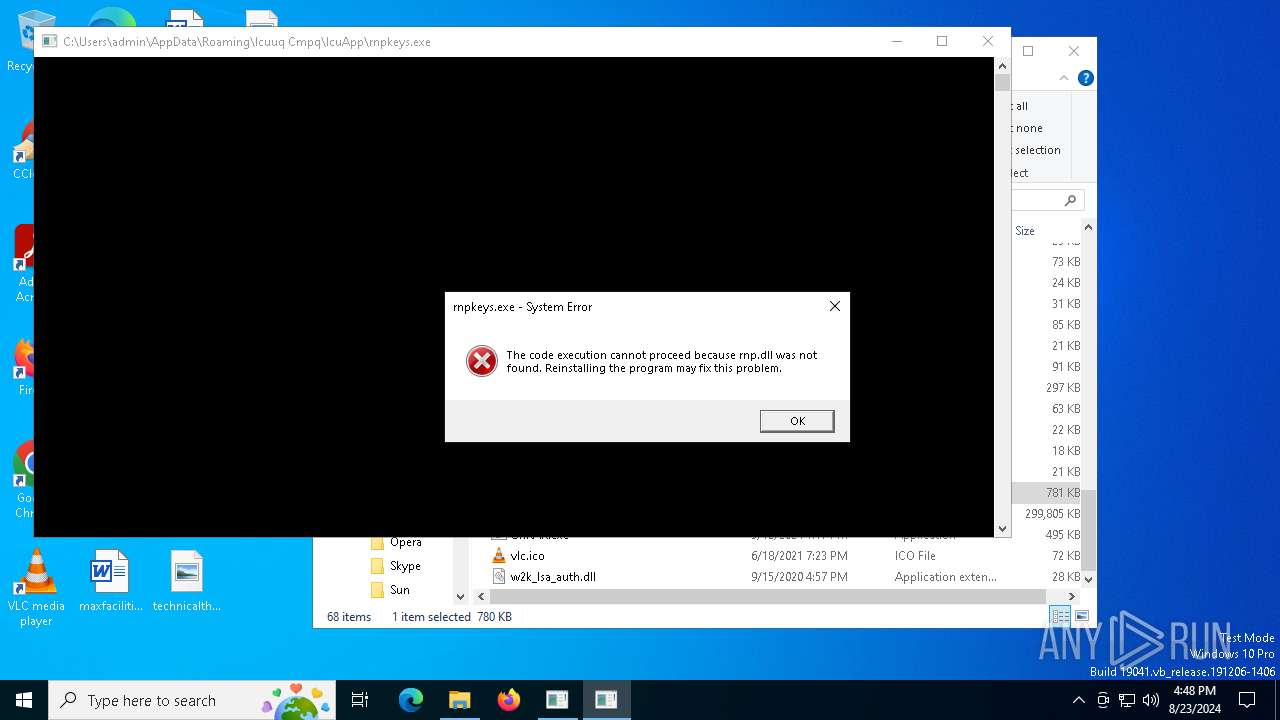
MALICIOUS
ROBOTDROPPER has been detected
- msiexec.exe (PID: 6936)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6936)
Drops the executable file immediately after the start
- msiexec.exe (PID: 6936)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6988)
Checks Windows Trust Settings
- msiexec.exe (PID: 6988)
Process drops legitimate windows executable
- msiexec.exe (PID: 6936)
The process executes via Task Scheduler
- default-browser-agent.exe (PID: 4248)
Loads DLL from Mozilla Firefox
- default-browser-agent.exe (PID: 4248)
INFO
Reads the computer name
- msiexec.exe (PID: 6936)
- msiexec.exe (PID: 6988)
Checks supported languages
- msiexec.exe (PID: 6988)
- msiexec.exe (PID: 6936)
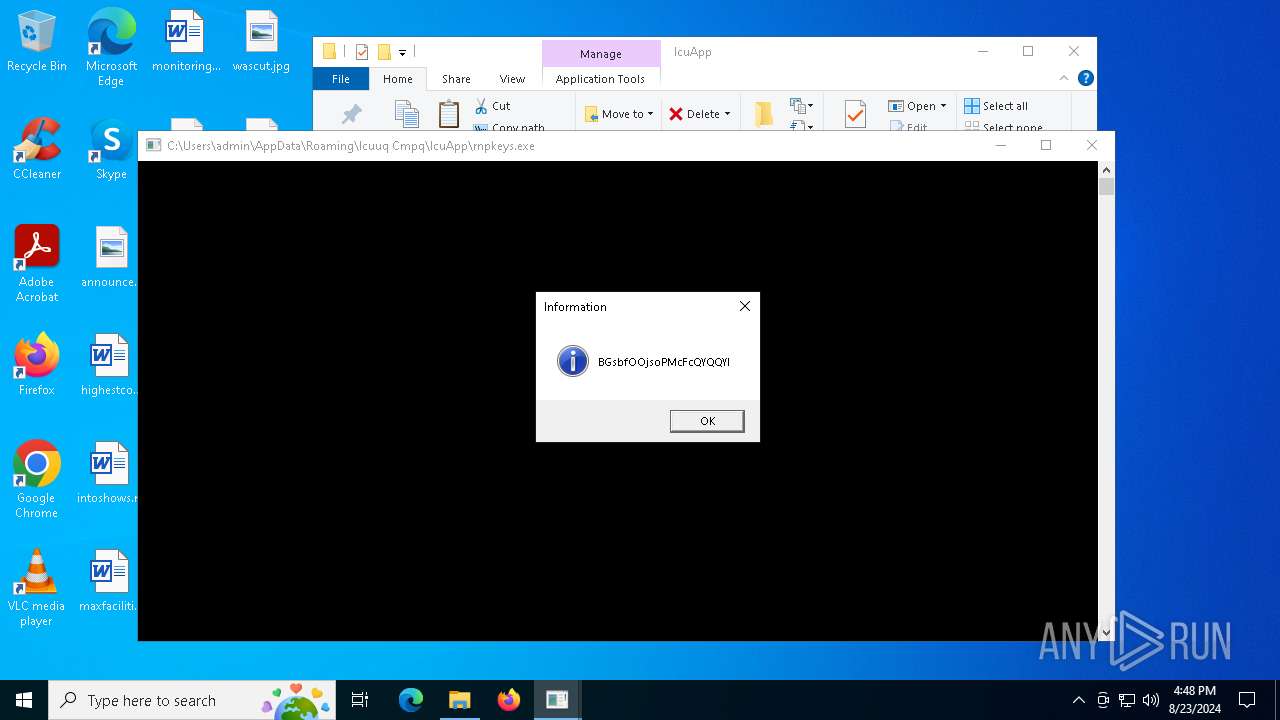
- rnpkeys.exe (PID: 1684)
- rnpkeys.exe (PID: 4068)
- rnpkeys.exe (PID: 4976)
- default-browser-agent.exe (PID: 4248)
An automatically generated document
- msiexec.exe (PID: 6824)
Reads Environment values
- msiexec.exe (PID: 6988)
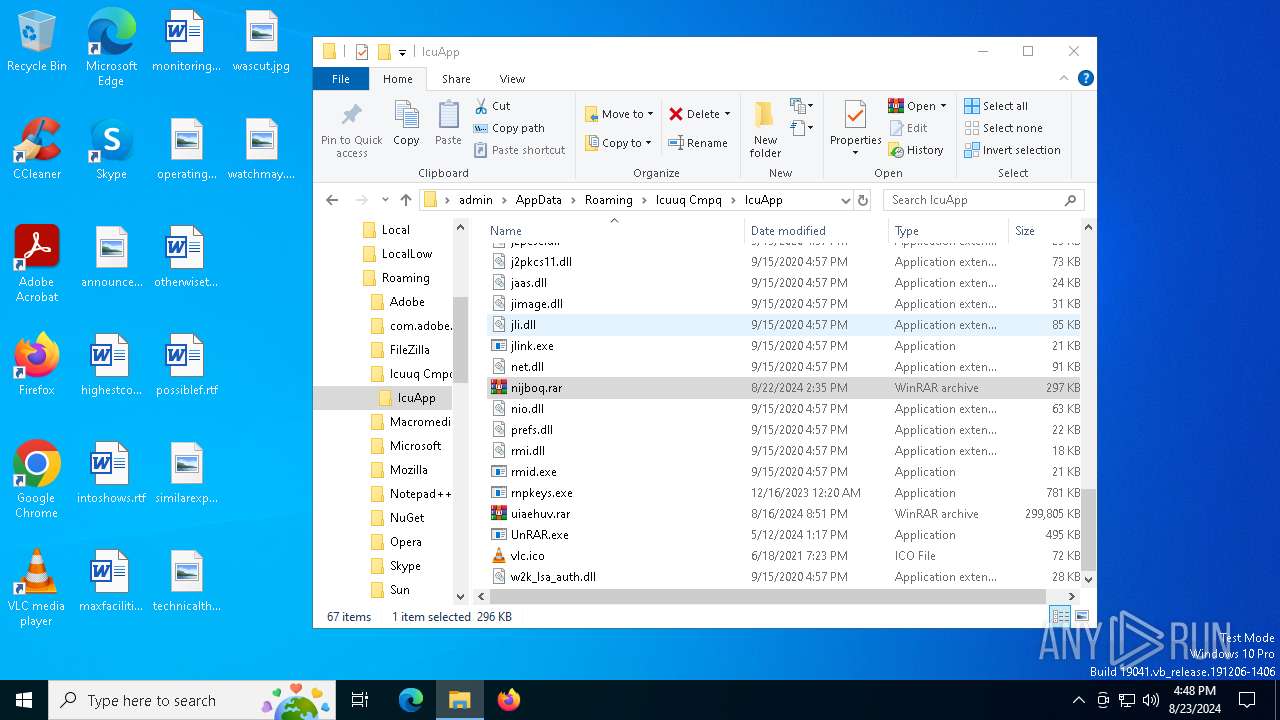
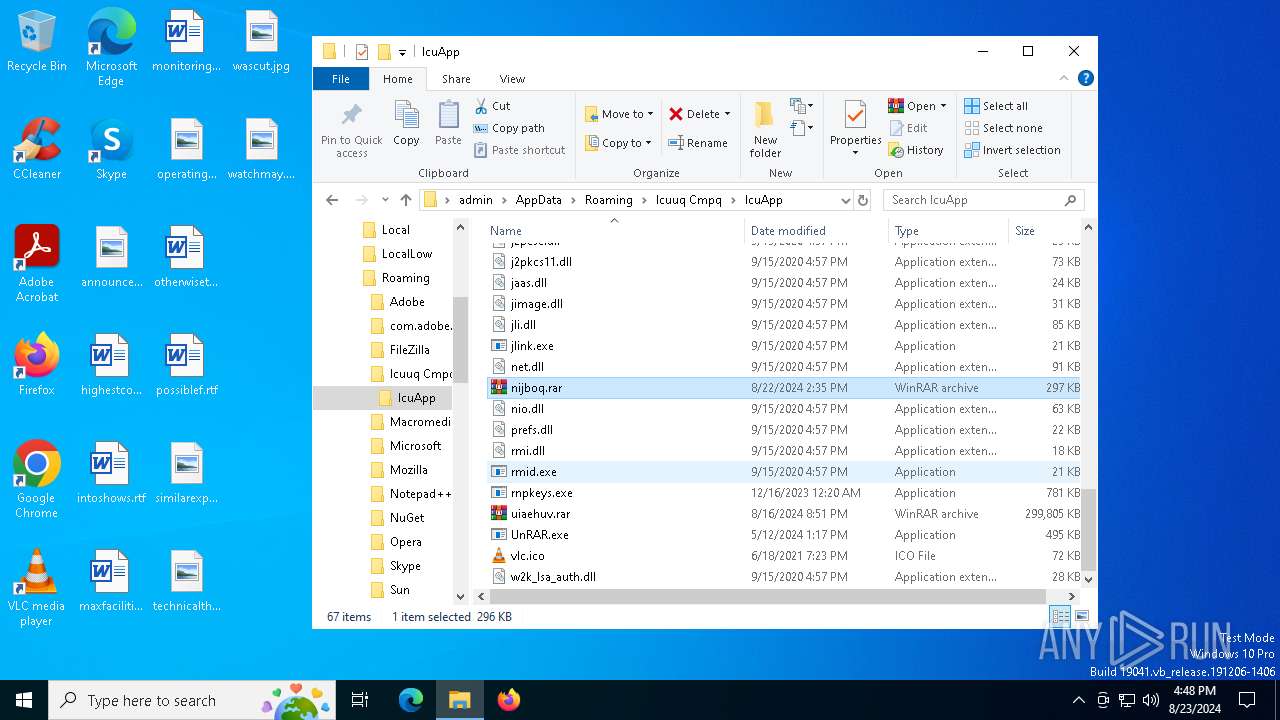
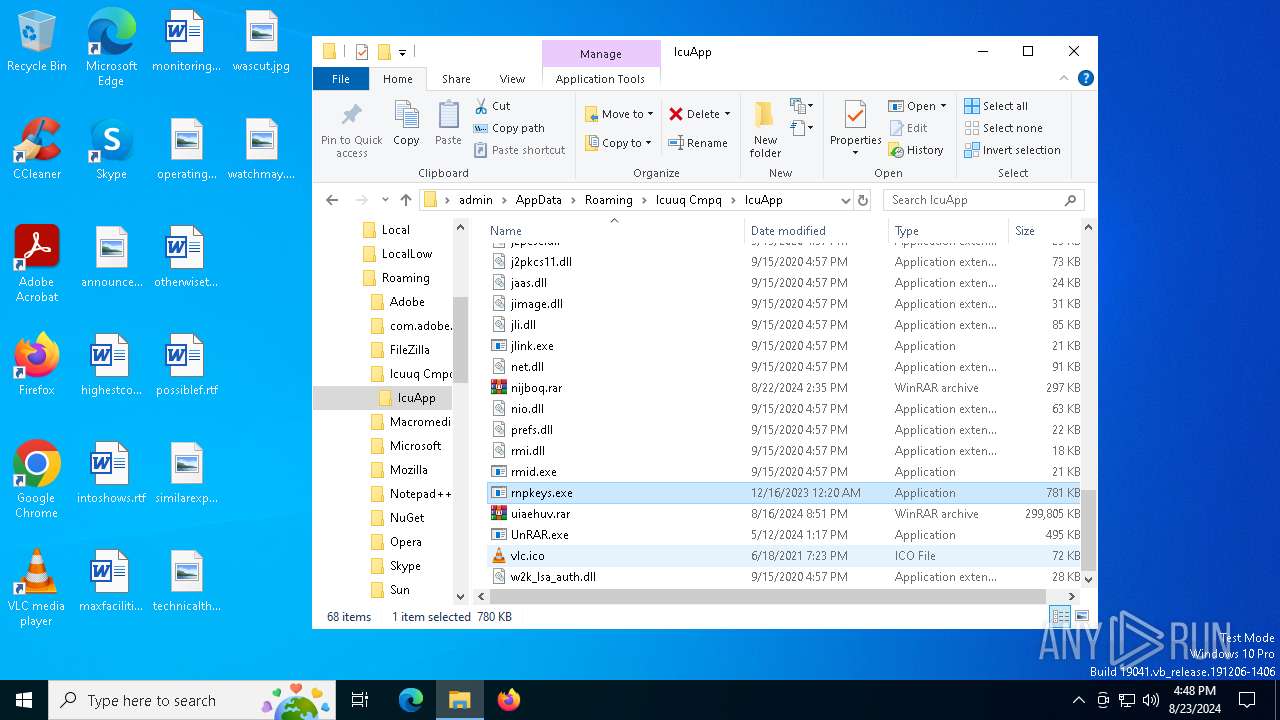
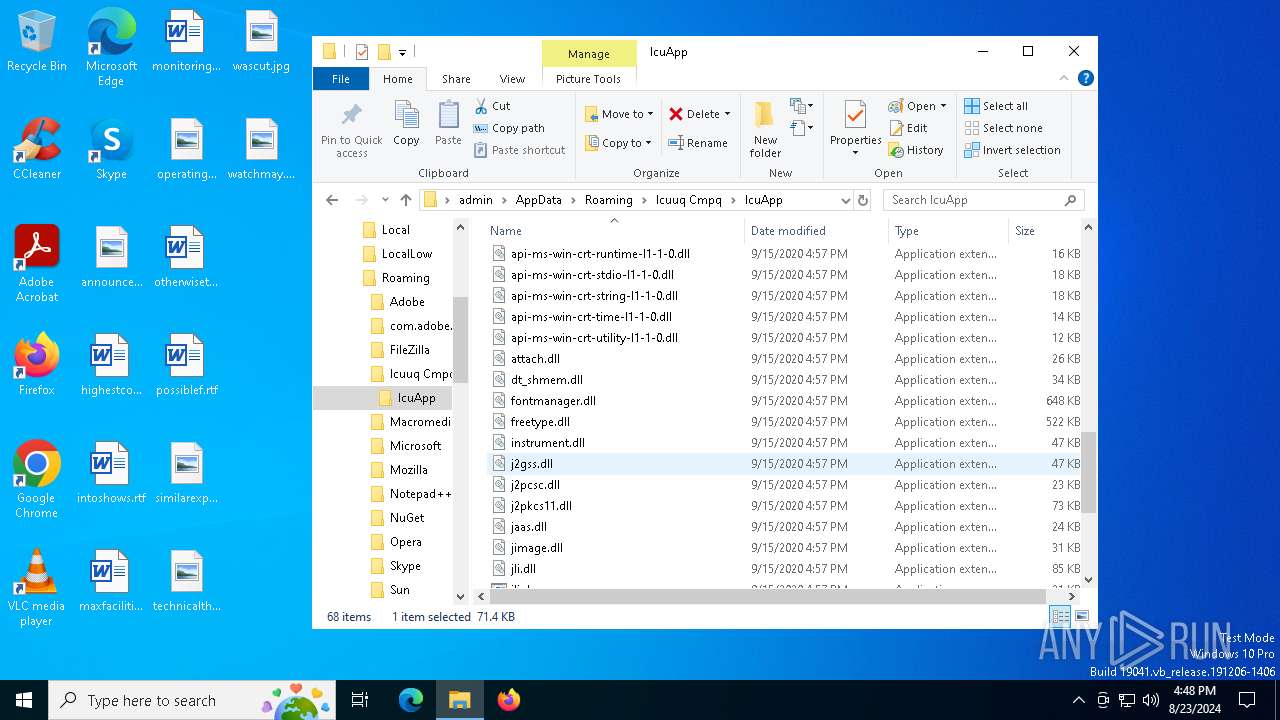
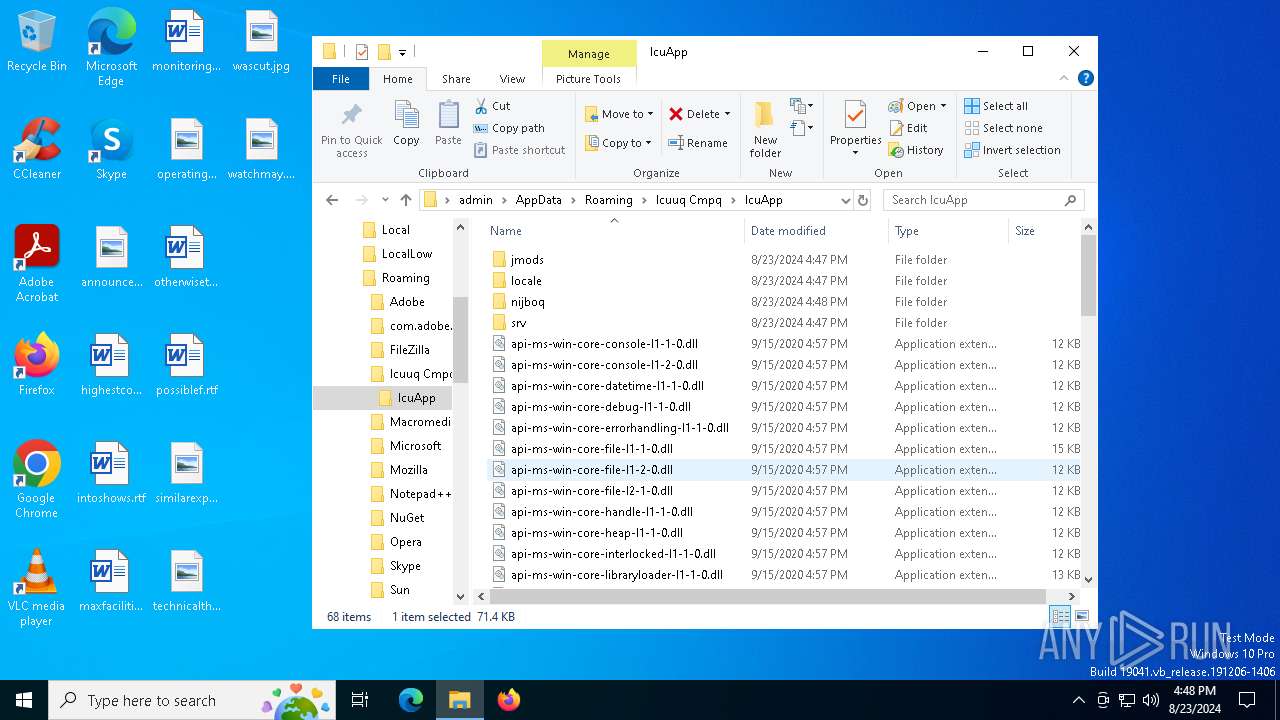
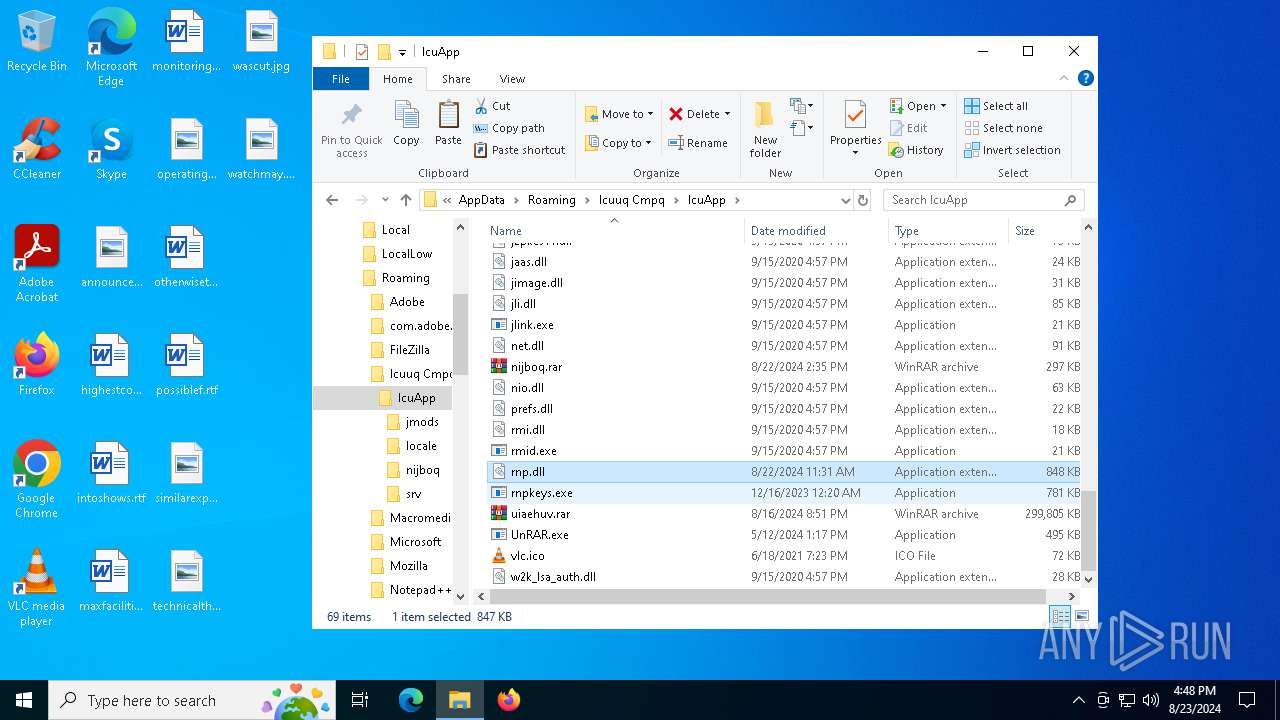
Executable content was dropped or overwritten
- msiexec.exe (PID: 6936)
- WinRAR.exe (PID: 6712)
Checks proxy server information
- msiexec.exe (PID: 6988)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6988)
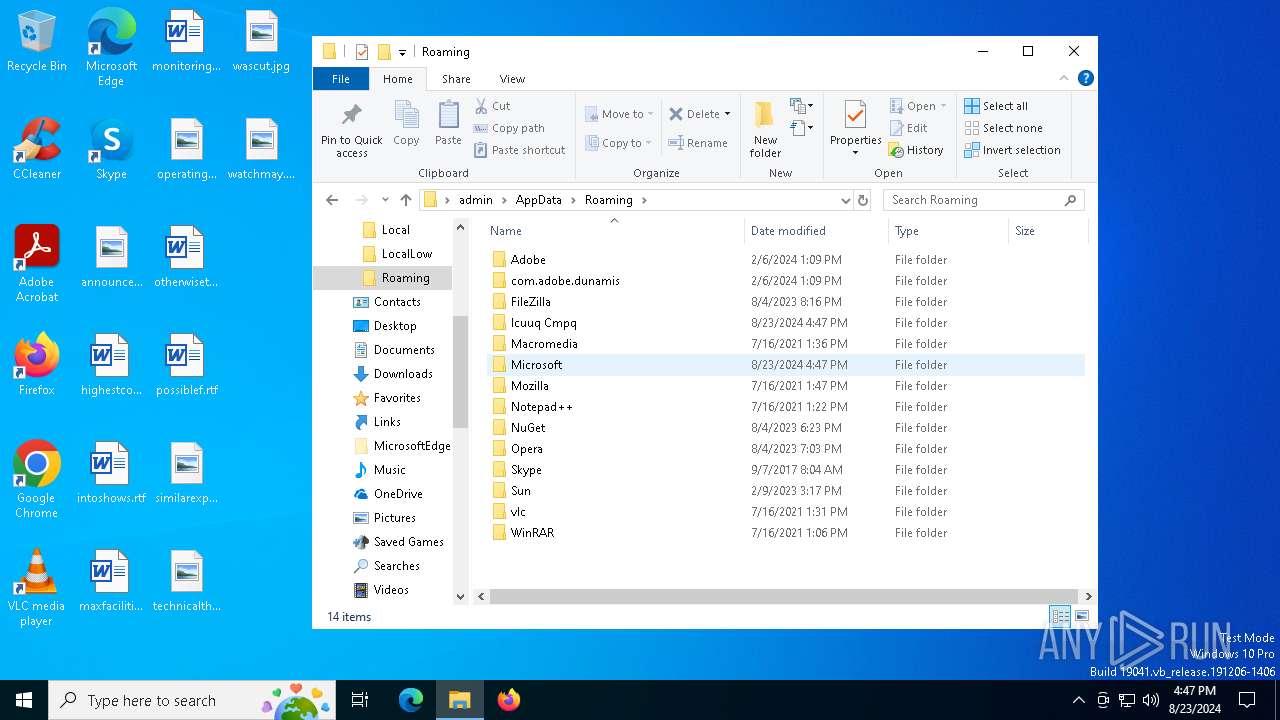
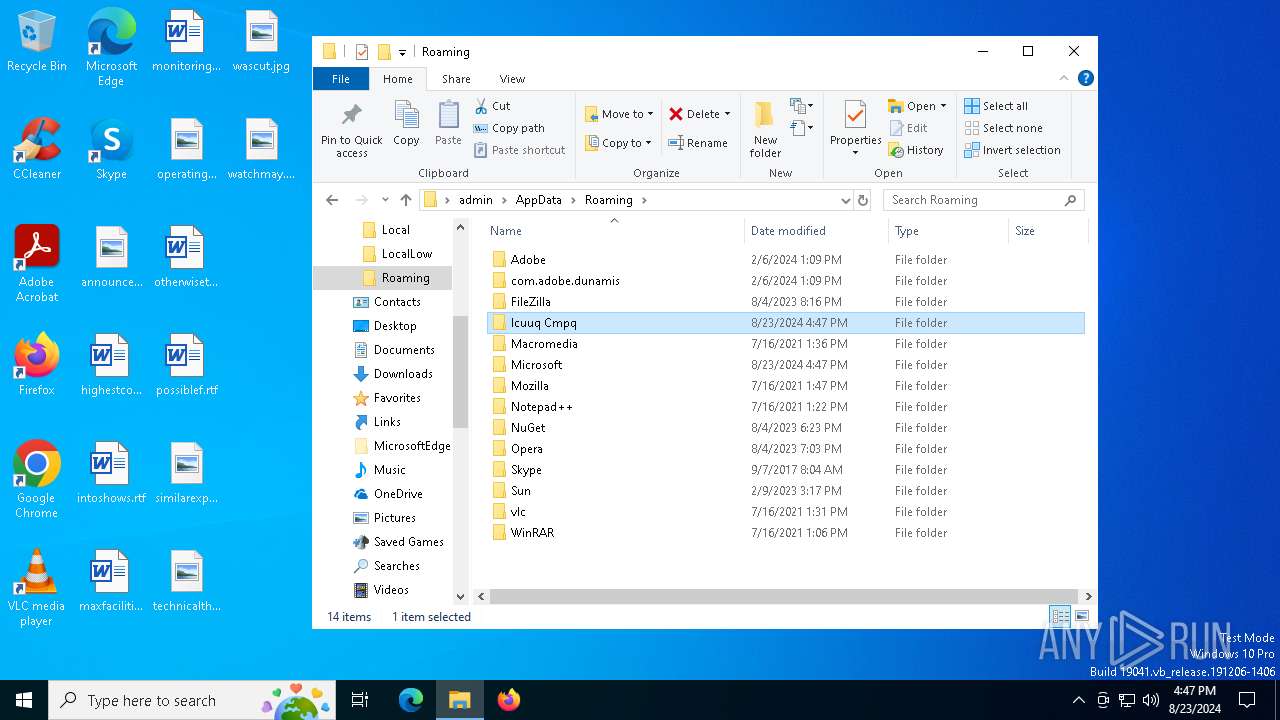
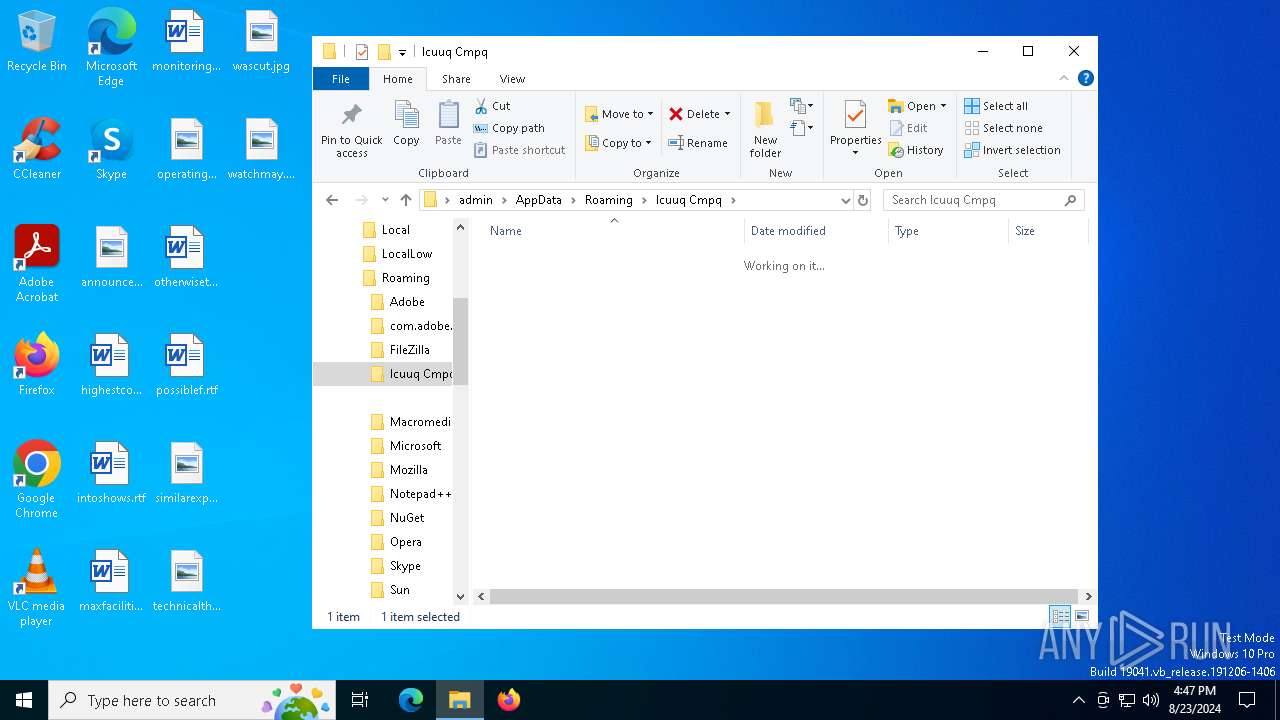
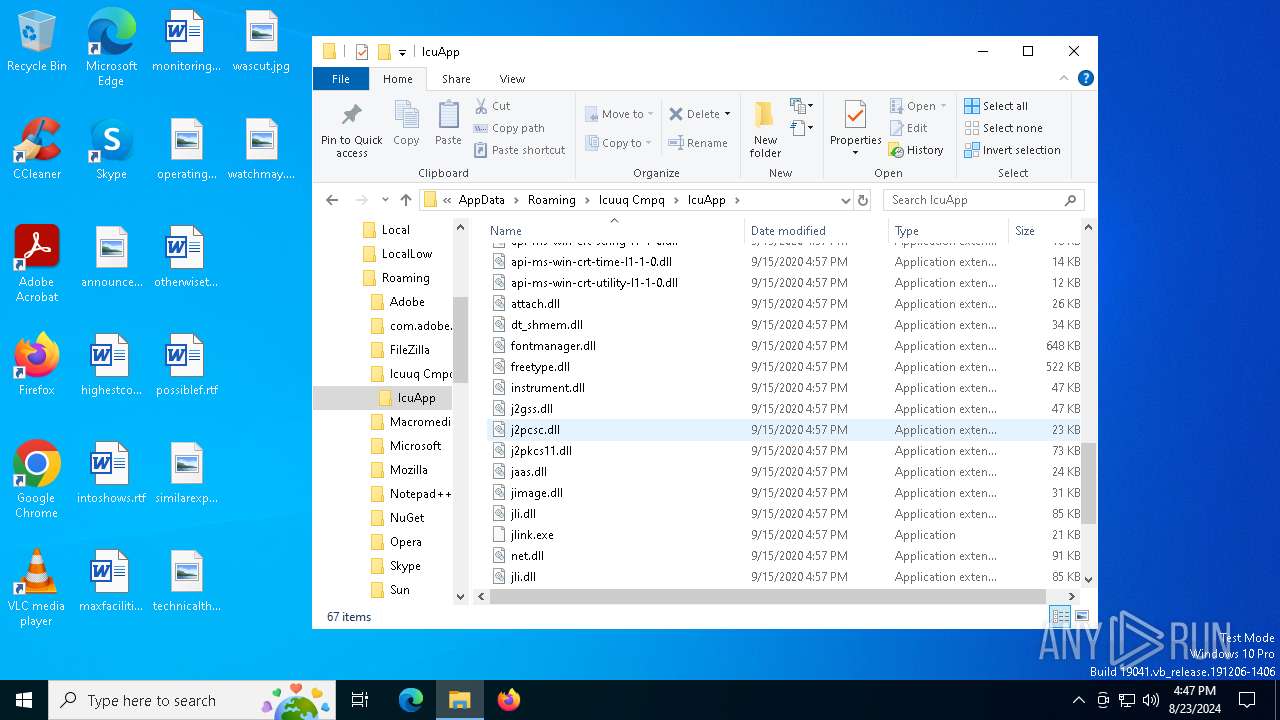
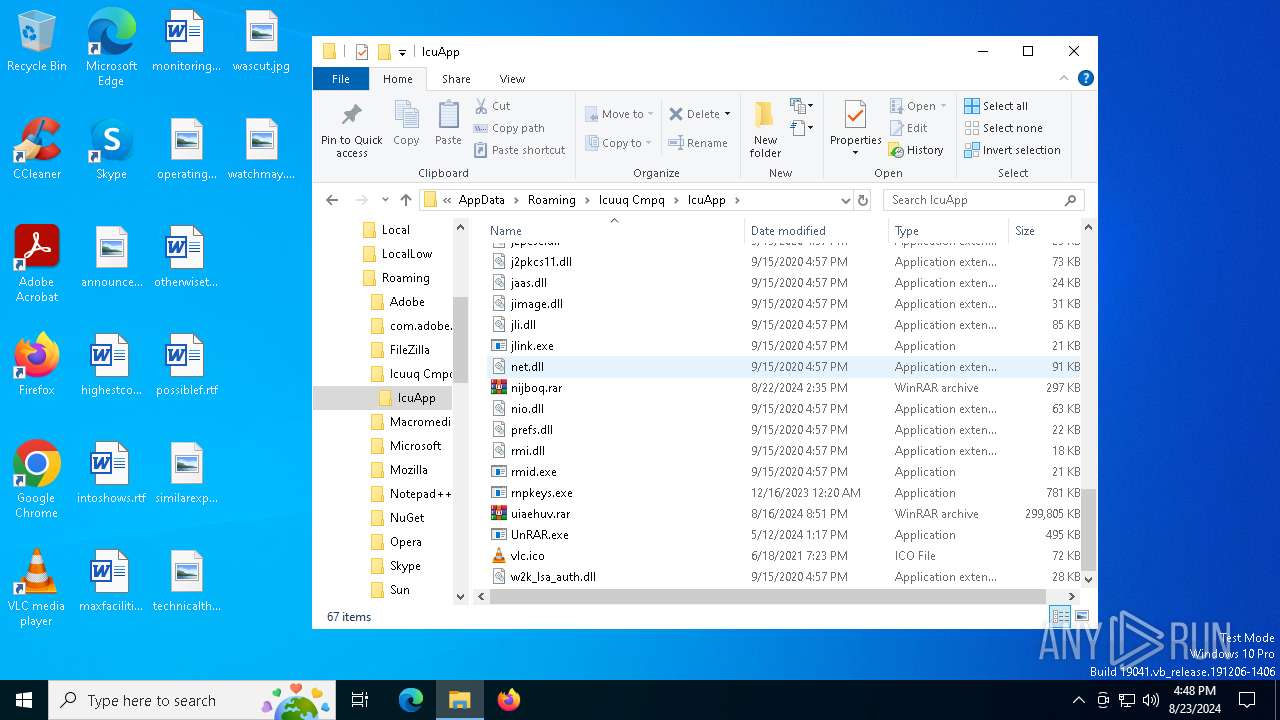
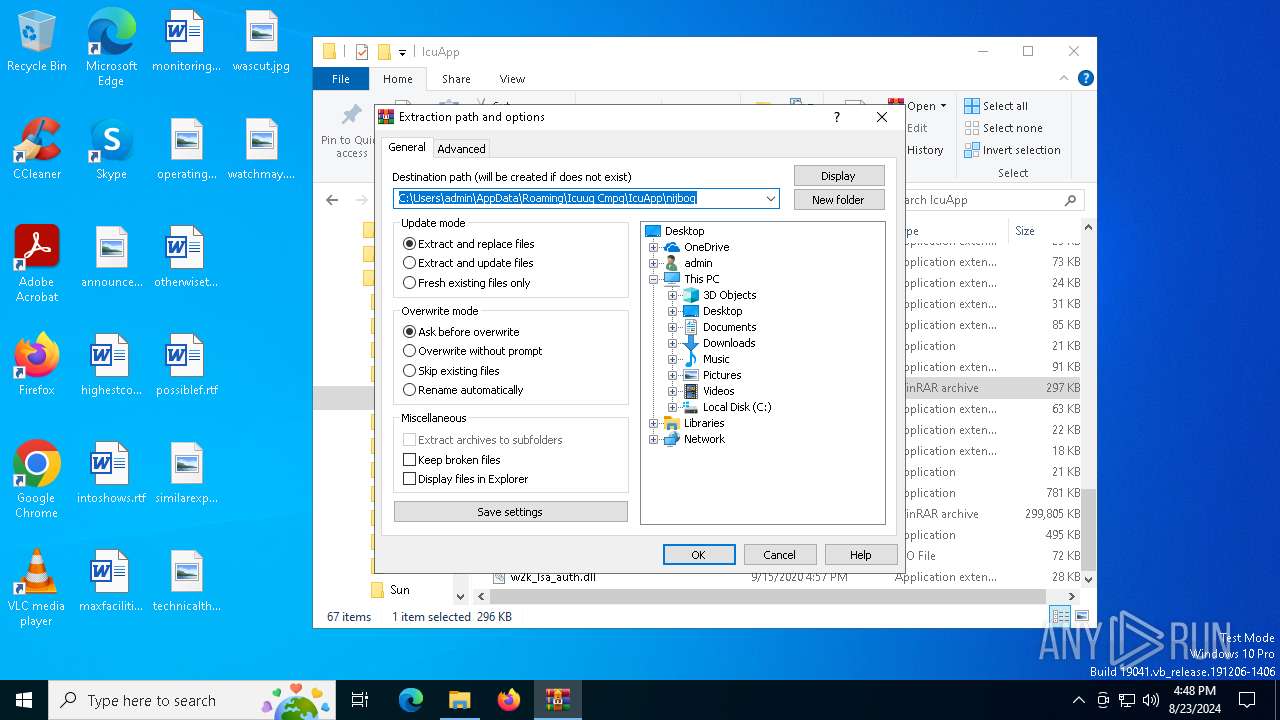
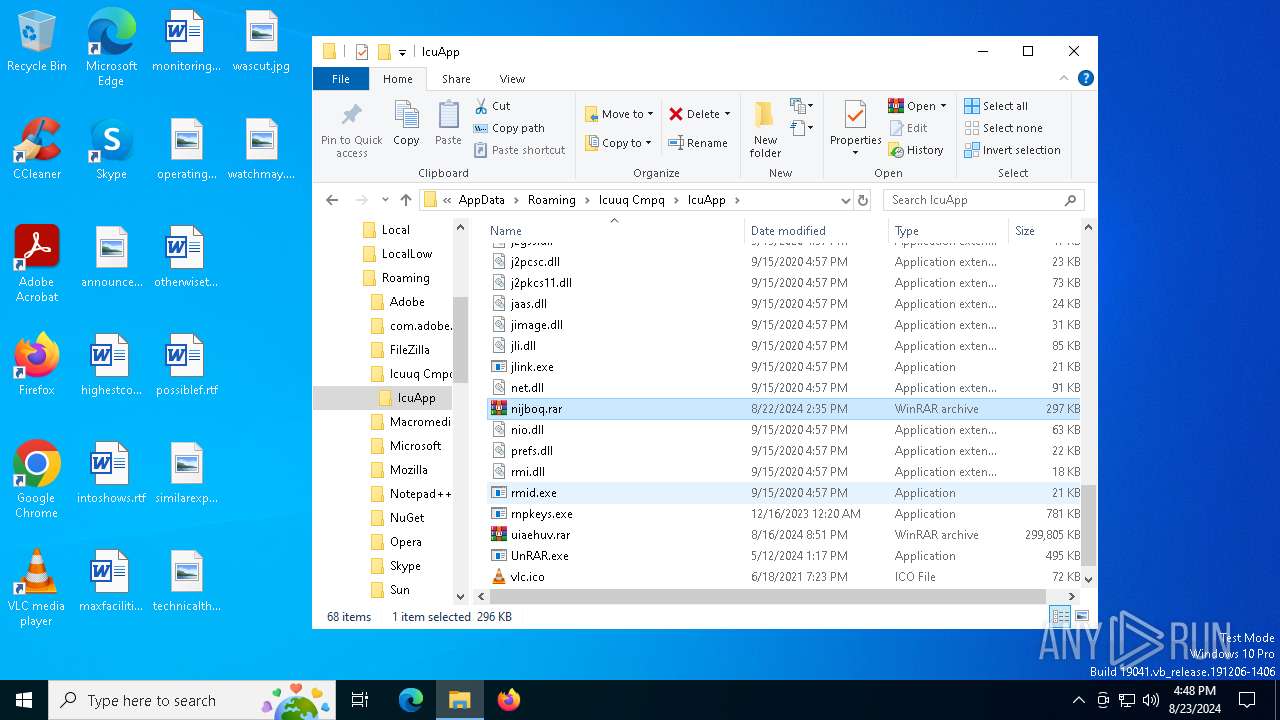
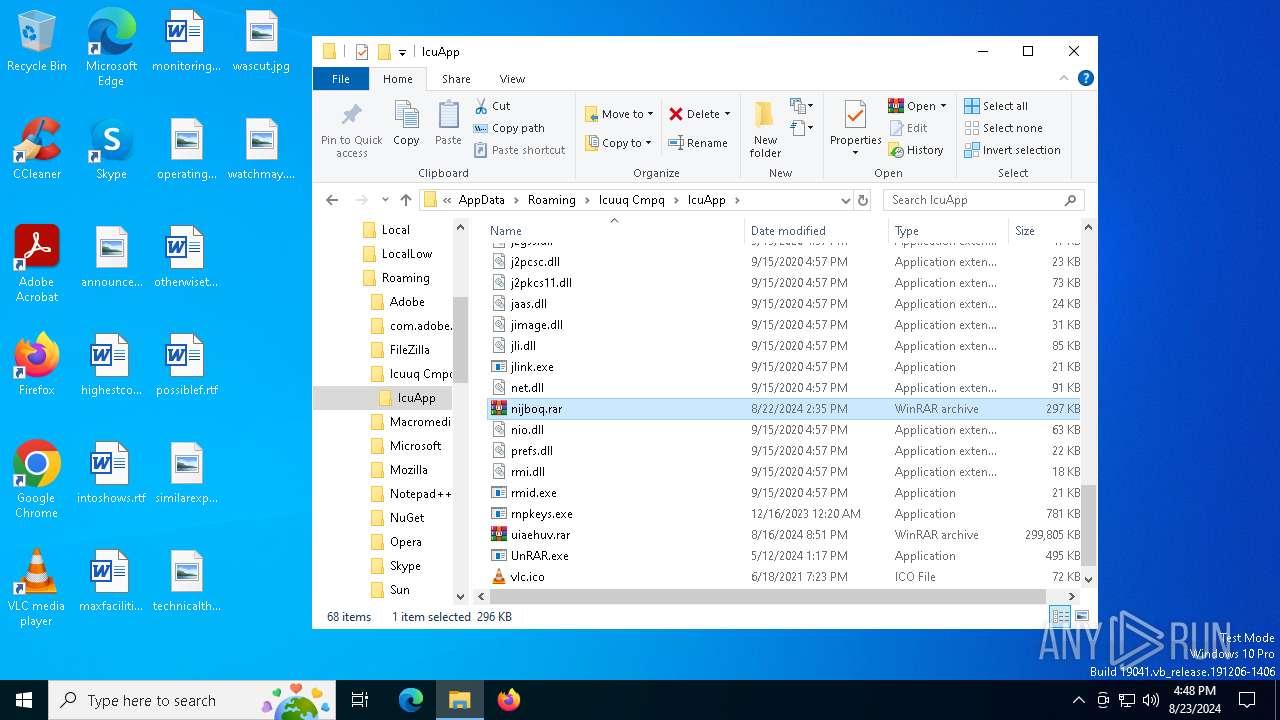
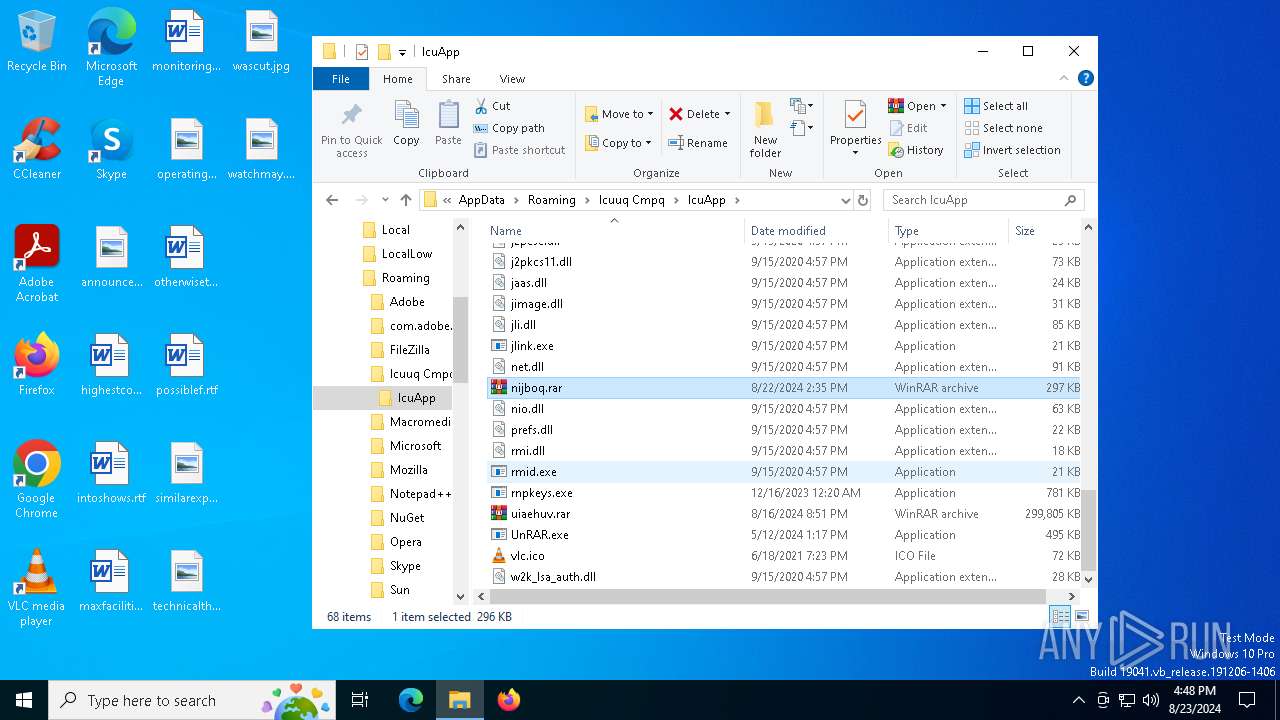
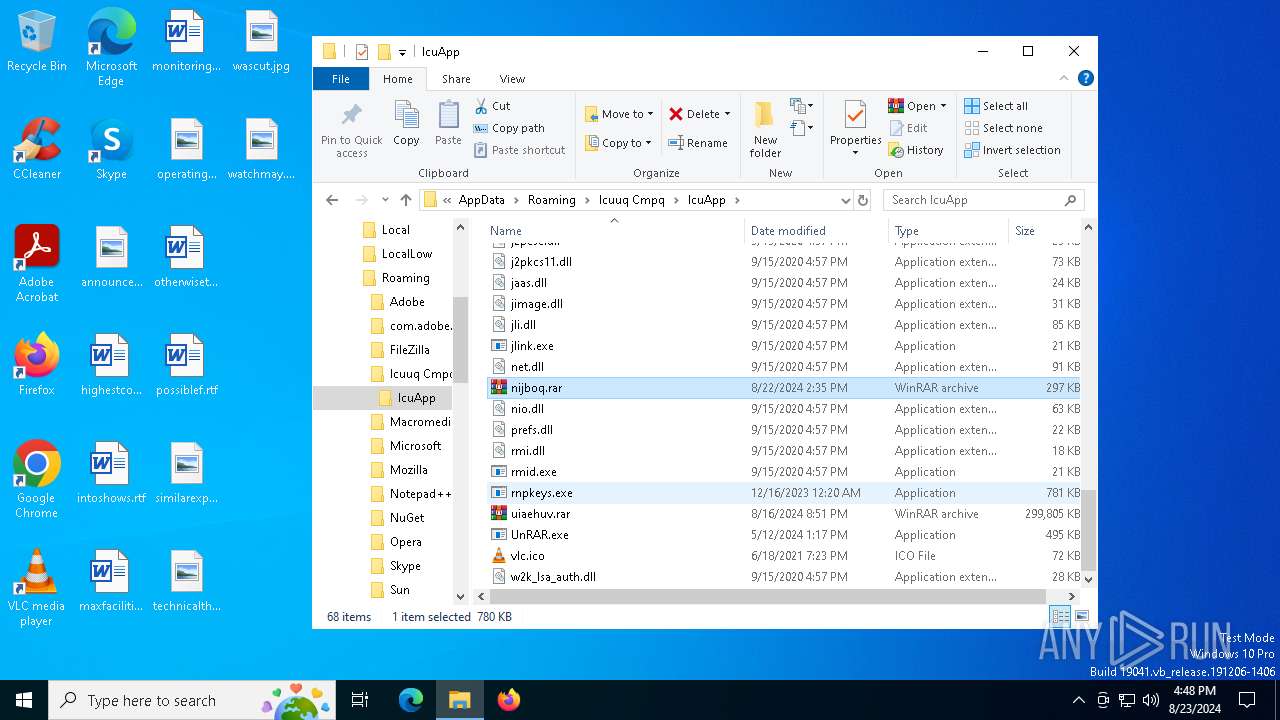
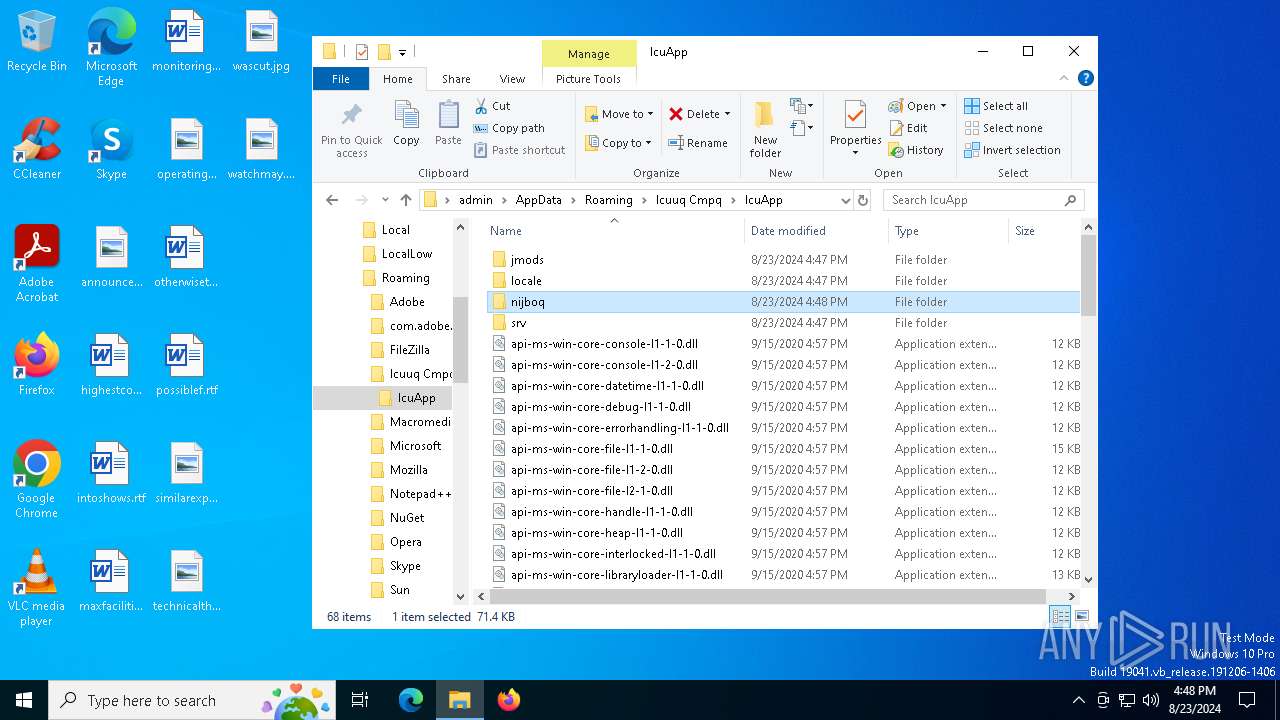
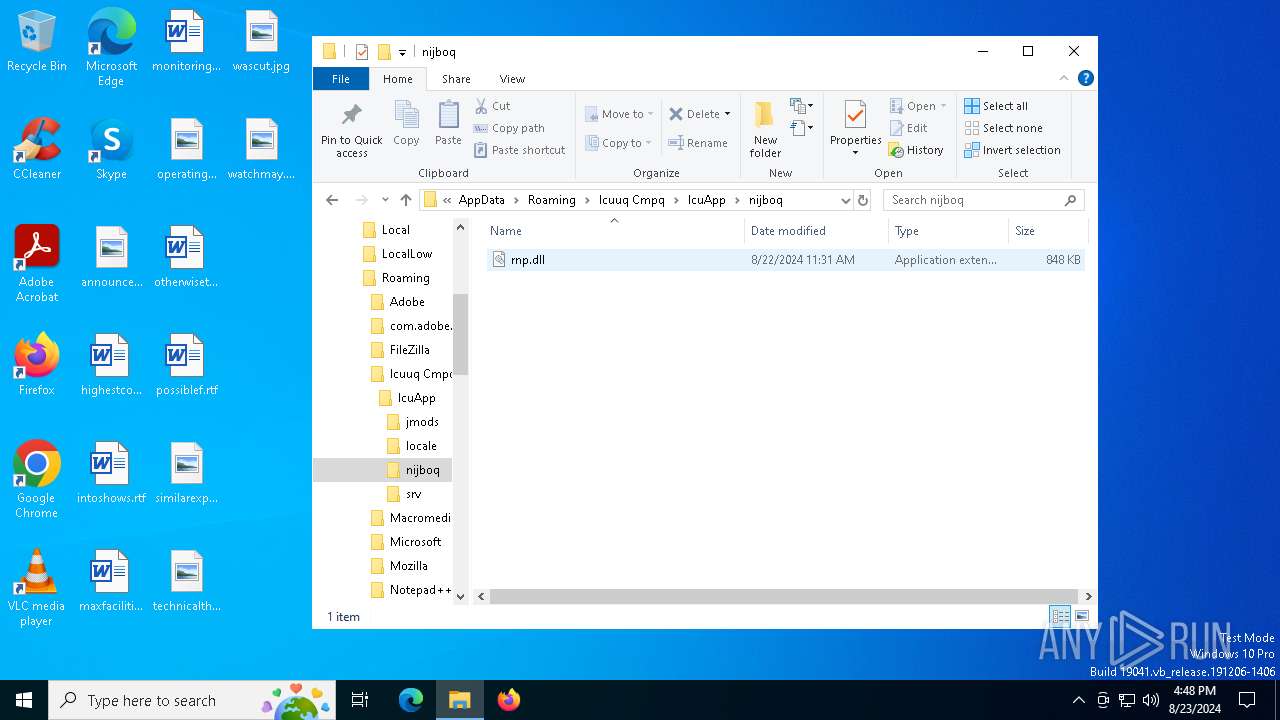
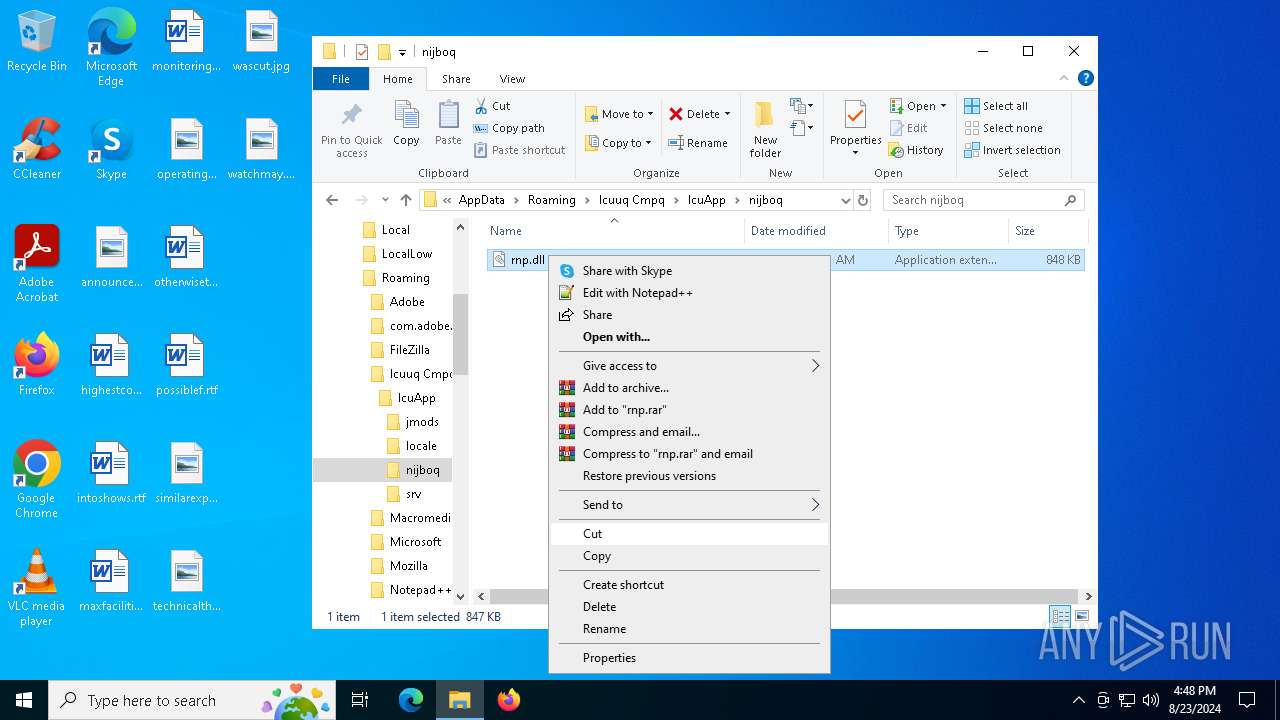
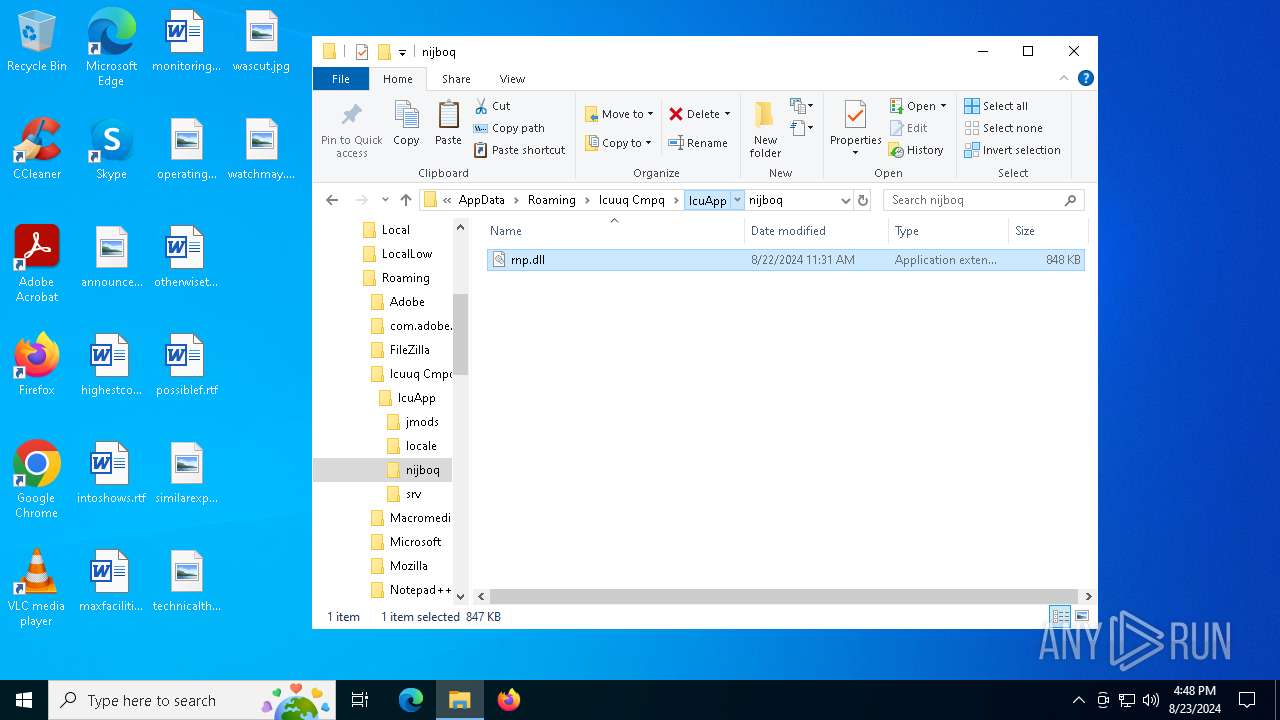
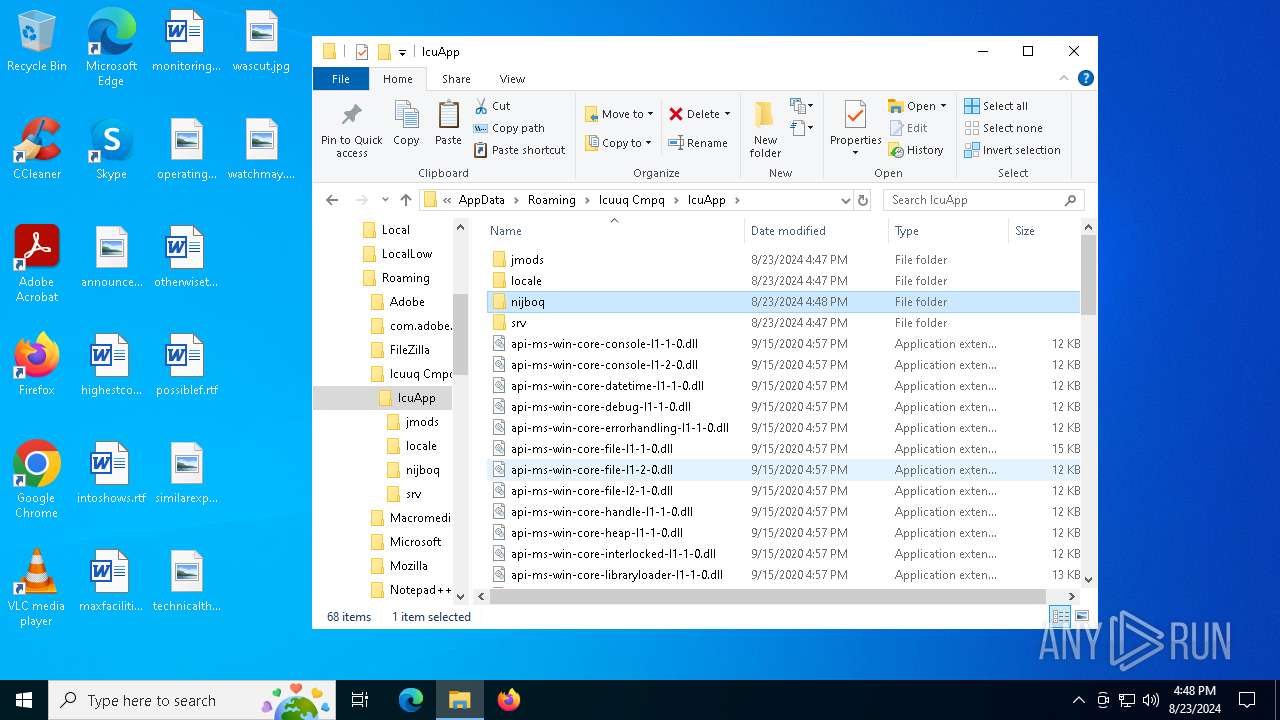
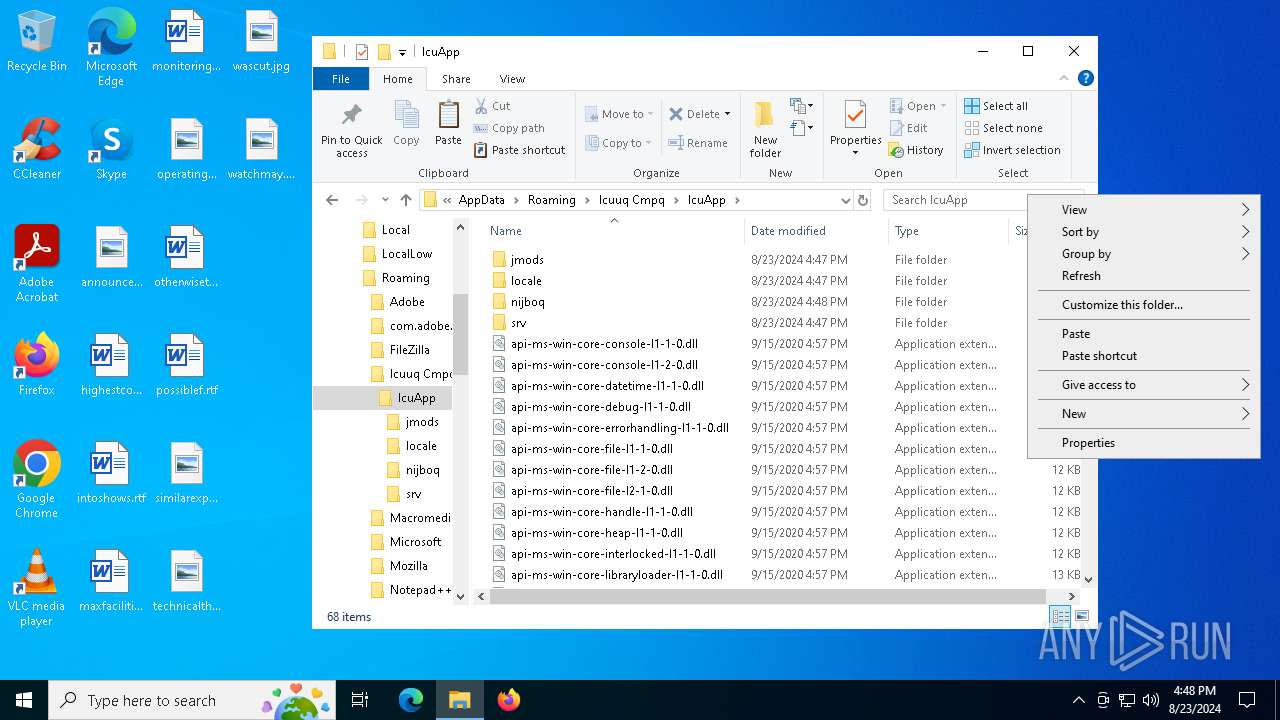
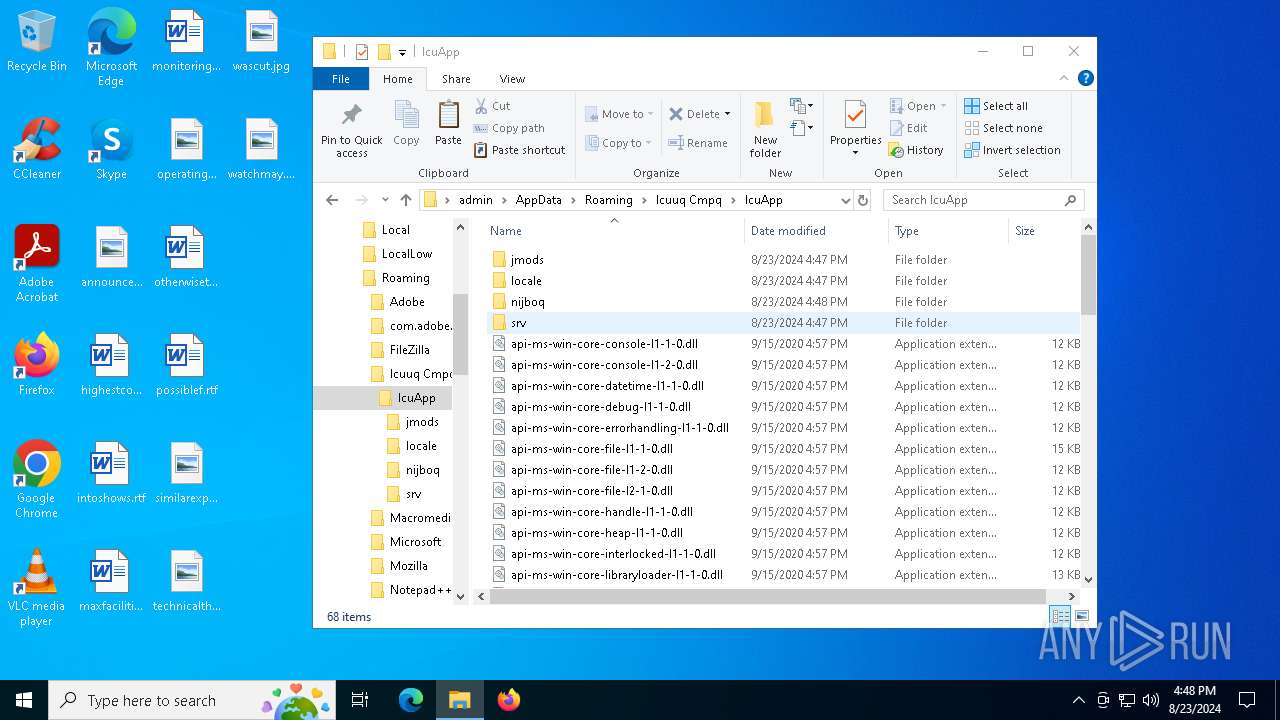
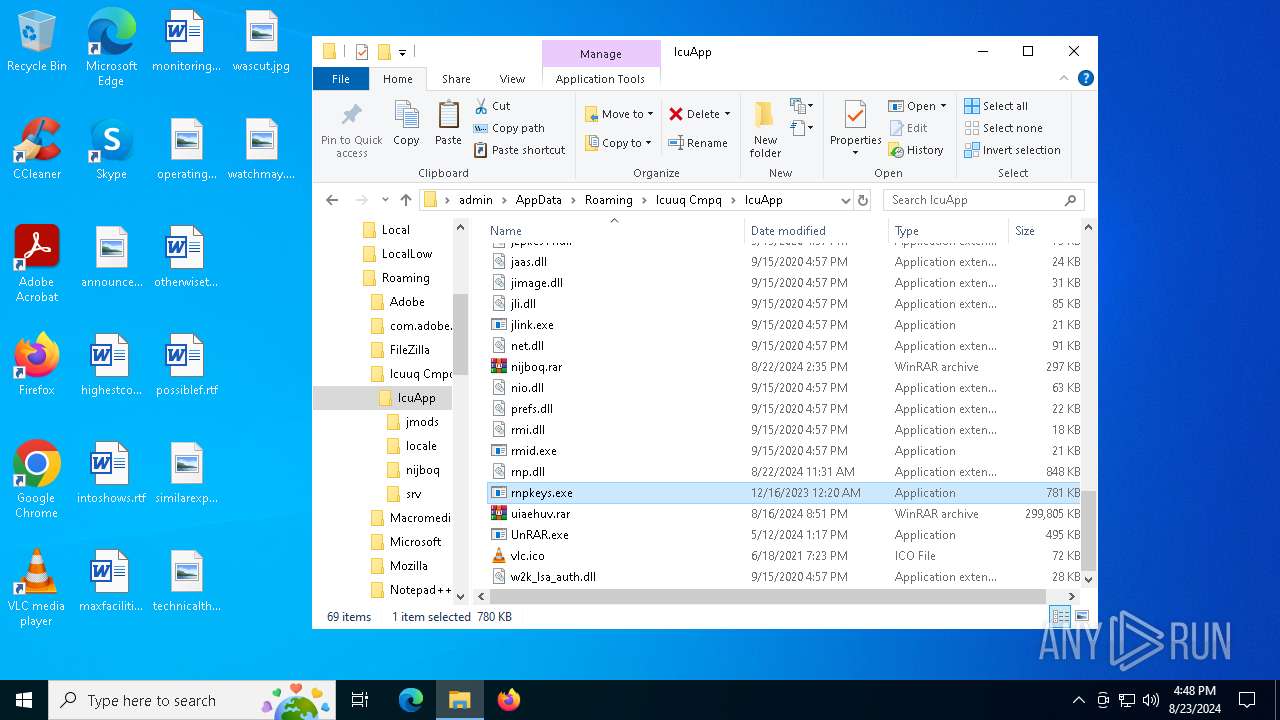
Creates files or folders in the user directory
- msiexec.exe (PID: 6988)
- msiexec.exe (PID: 6936)
Reads the software policy settings
- msiexec.exe (PID: 6988)
Creates a software uninstall entry
- msiexec.exe (PID: 6936)
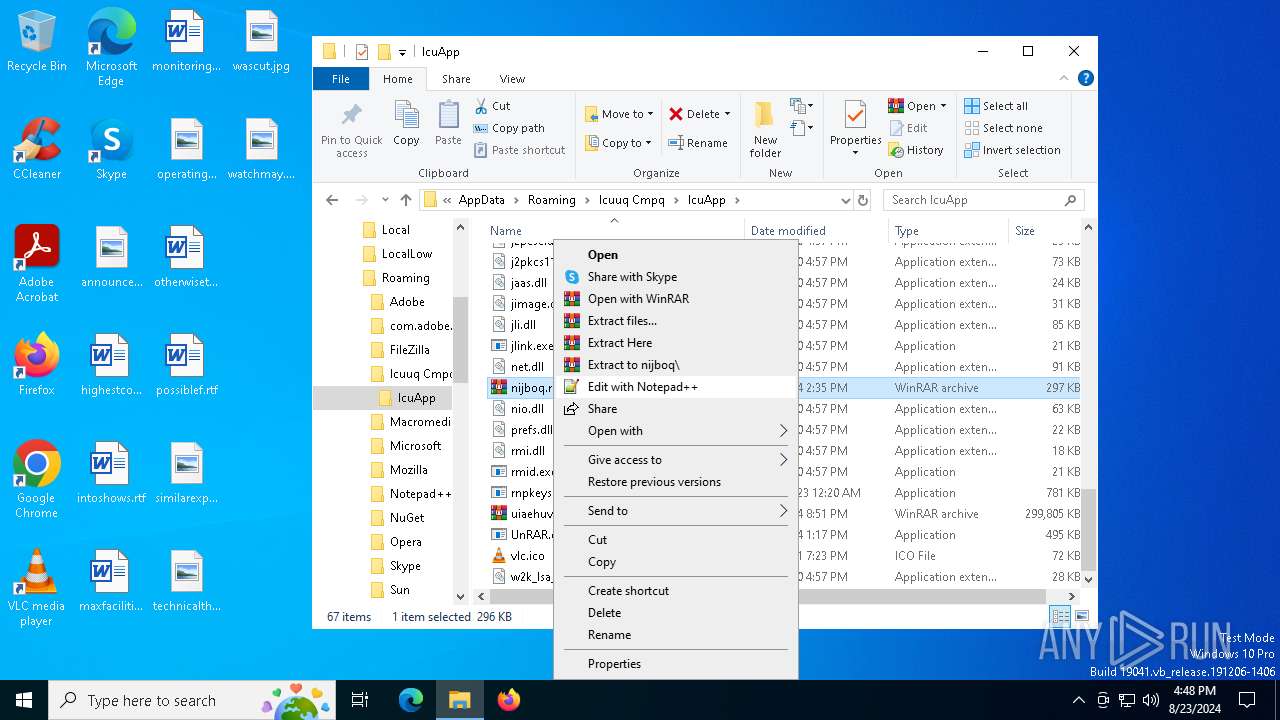
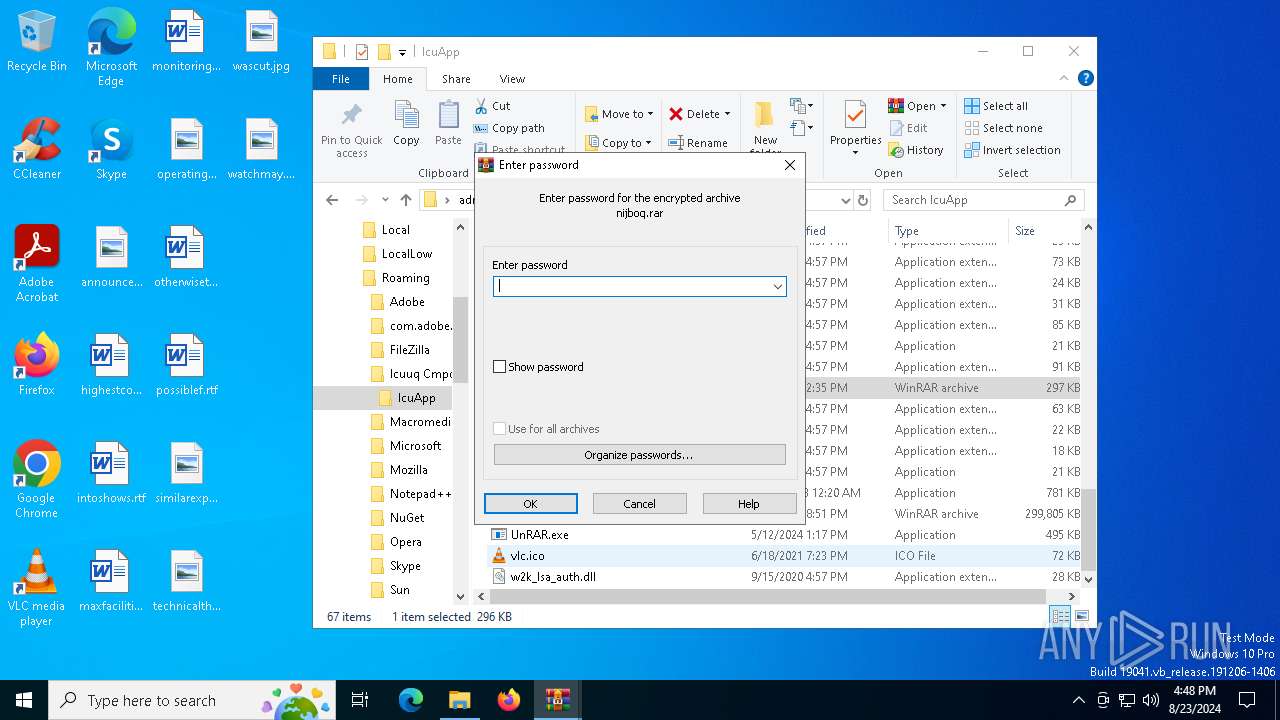
Manual execution by a user
- WinRAR.exe (PID: 6712)
- rnpkeys.exe (PID: 3852)
- rnpkeys.exe (PID: 1684)
- rnpkeys.exe (PID: 4068)
- rnpkeys.exe (PID: 4976)
Application launched itself
- firefox.exe (PID: 5264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {A06E125F-2A1D-4491-AE35-1E59BECF7A5D} |
| Words: | 10 |
| Subject: | IcuApp |
| Author: | Icuuq Cmpq |
| LastModifiedBy: | - |
| Software: | IcuApp |
| Template: | x64;2057 |
| Comments: | This installer database contains the logic and data required to install IcuApp. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:08:22 11:36:04 |
| ModifyDate: | 2024:08:22 11:36:04 |
| LastPrinted: | 2024:08:22 11:36:04 |
| Pages: | 450 |
Total processes
146
Monitored processes
16
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rnpkeys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1684 | "C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\rnpkeys.exe" | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\rnpkeys.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 115.6.0 Modules
| |||||||||||||||
| 1944 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rnpkeys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3840 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rnpkeys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3852 | "C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\rnpkeys.exe" | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\rnpkeys.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 3221225781 Version: 115.6.0 Modules
| |||||||||||||||
| 4068 | "C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\rnpkeys.exe" | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\rnpkeys.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 115.6.0 Modules
| |||||||||||||||
| 4248 | "C:\Program Files\Mozilla Firefox\default-browser-agent.exe" do-task "308046B0AF4A39CB" | C:\Program Files\Mozilla Firefox\default-browser-agent.exe | — | svchost.exe | |||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 2147500037 Version: 123.0 Modules
| |||||||||||||||
| 4976 | "C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\rnpkeys.exe" | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\rnpkeys.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 115.6.0 Modules
| |||||||||||||||
| 5264 | "C:\Program Files\Mozilla Firefox\firefox.exe" --backgroundtask defaultagent do-task 308046B0AF4A39CB | C:\Program Files\Mozilla Firefox\firefox.exe | — | default-browser-agent.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 3 Version: 123.0 Modules
| |||||||||||||||
| 5532 | "C:\Program Files\Mozilla Firefox\firefox.exe" --backgroundtask defaultagent do-task 308046B0AF4A39CB | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 3 Version: 123.0 Modules
| |||||||||||||||
Total events
10 399
Read events
10 168
Write events
222
Delete events
9
Modification events
| (PID) Process: | (6936) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 181B00000FFF4D297CF5DA01 | |||
| (PID) Process: | (6936) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 7A599F3E2387DA9871A31E16FF6D8DF8079B660F267845C502DA5E242450B788 | |||
| (PID) Process: | (6936) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6988) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6988) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6988) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6988) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6988) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6988) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6988) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
70
Suspicious files
38
Text files
5
Unknown types
1
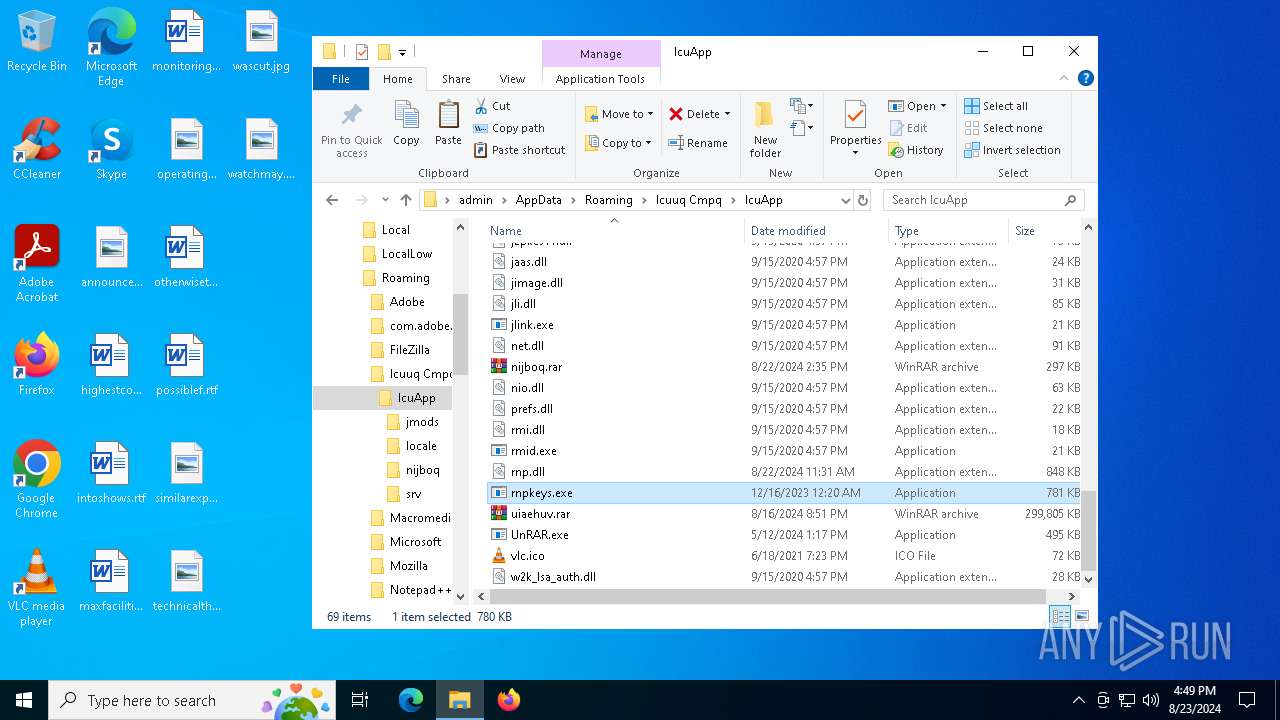
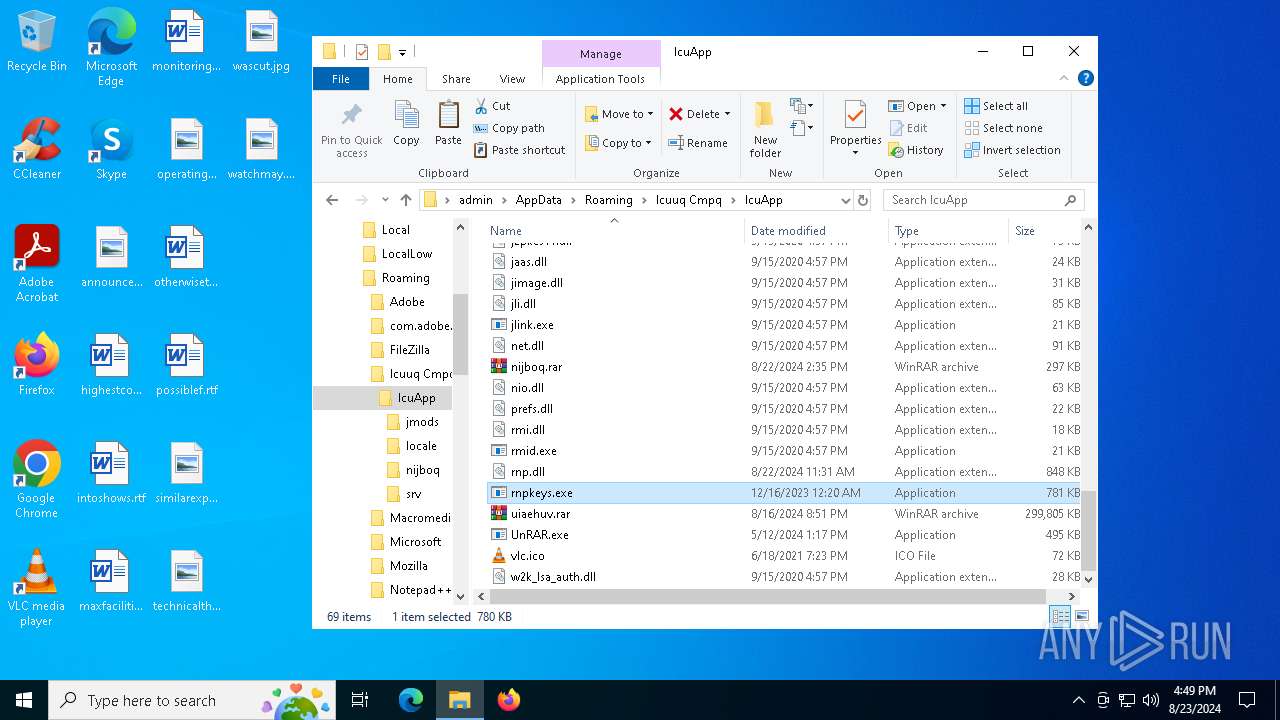
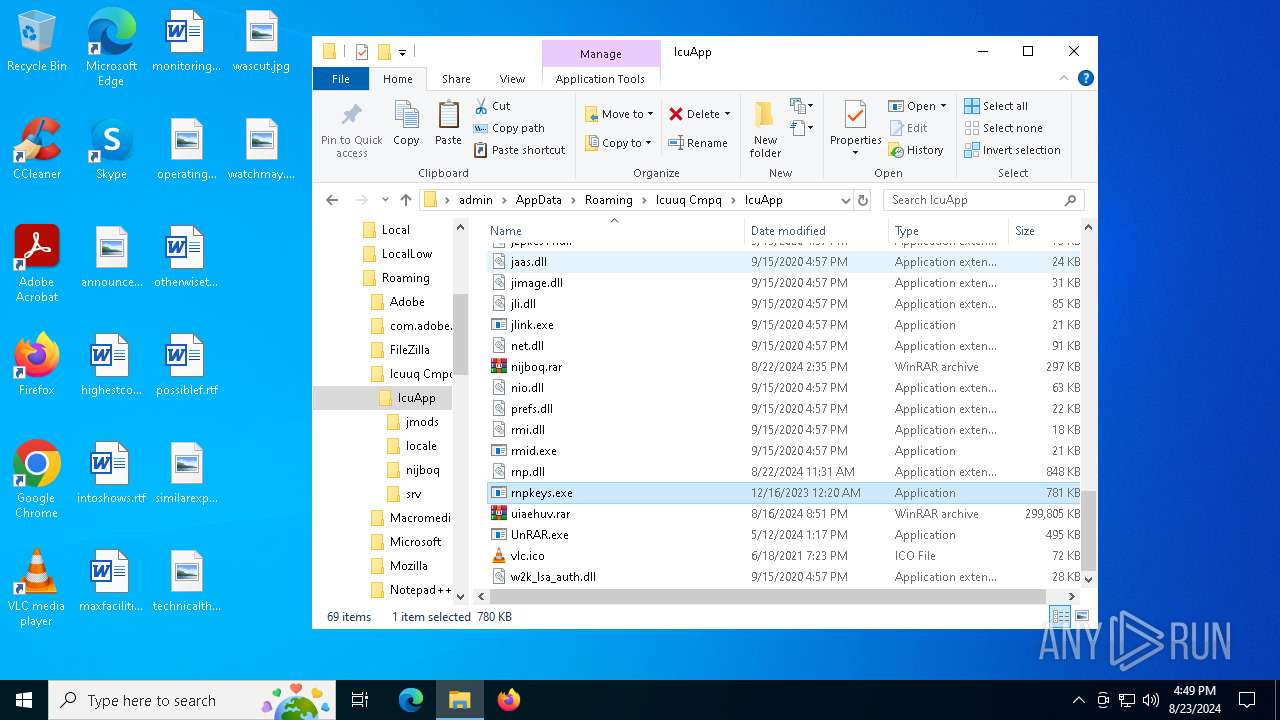
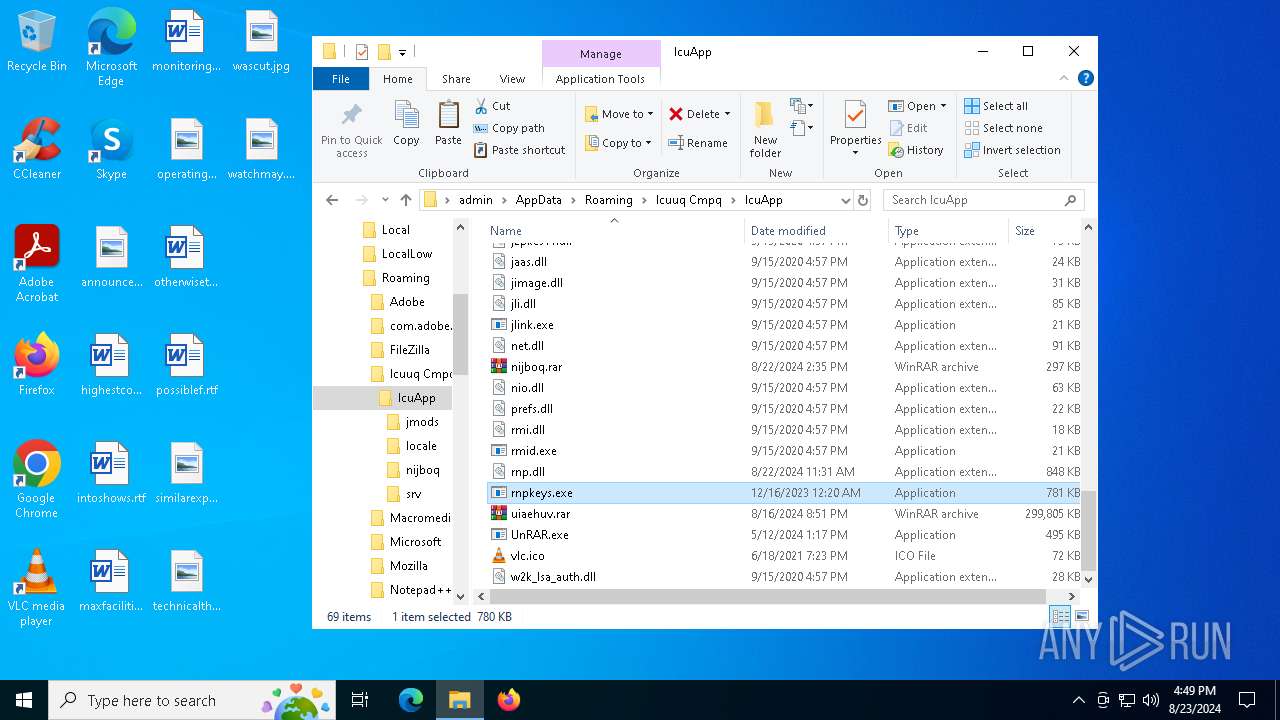
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6936 | msiexec.exe | C:\Windows\Installer\11ea2e.msi | — | |
MD5:— | SHA256:— | |||
| 6936 | msiexec.exe | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\jmods\java.base.jmod | — | |
MD5:— | SHA256:— | |||
| 6936 | msiexec.exe | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\srv\classes.jsa | — | |
MD5:— | SHA256:— | |||
| 6936 | msiexec.exe | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\srv\classes_nocoops.jsa | — | |
MD5:— | SHA256:— | |||
| 6936 | msiexec.exe | C:\Windows\Installer\MSIECA1.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 6936 | msiexec.exe | C:\Windows\Installer\MSIF704.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 6936 | msiexec.exe | C:\Windows\Installer\MSIECF0.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 6936 | msiexec.exe | C:\Windows\Installer\MSIED9D.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 6988 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:7FB5FA1534DCF77F2125B2403B30A0EE | SHA256:33A39E9EC2133230533A686EC43760026E014A3828C703707ACBC150FE40FD6F | |||
| 6936 | msiexec.exe | C:\Windows\Installer\MSIEC33.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
33
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6988 | msiexec.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
6988 | msiexec.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1076 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6560 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2720 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1432 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6988 | msiexec.exe | 188.114.97.3:443 | get-license4.com | CLOUDFLARENET | NL | unknown |
6988 | msiexec.exe | 142.250.184.195:80 | c.pki.goog | GOOGLE | US | whitelisted |
1076 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1076 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1432 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
get-license4.com |
| malicious |
c.pki.goog |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
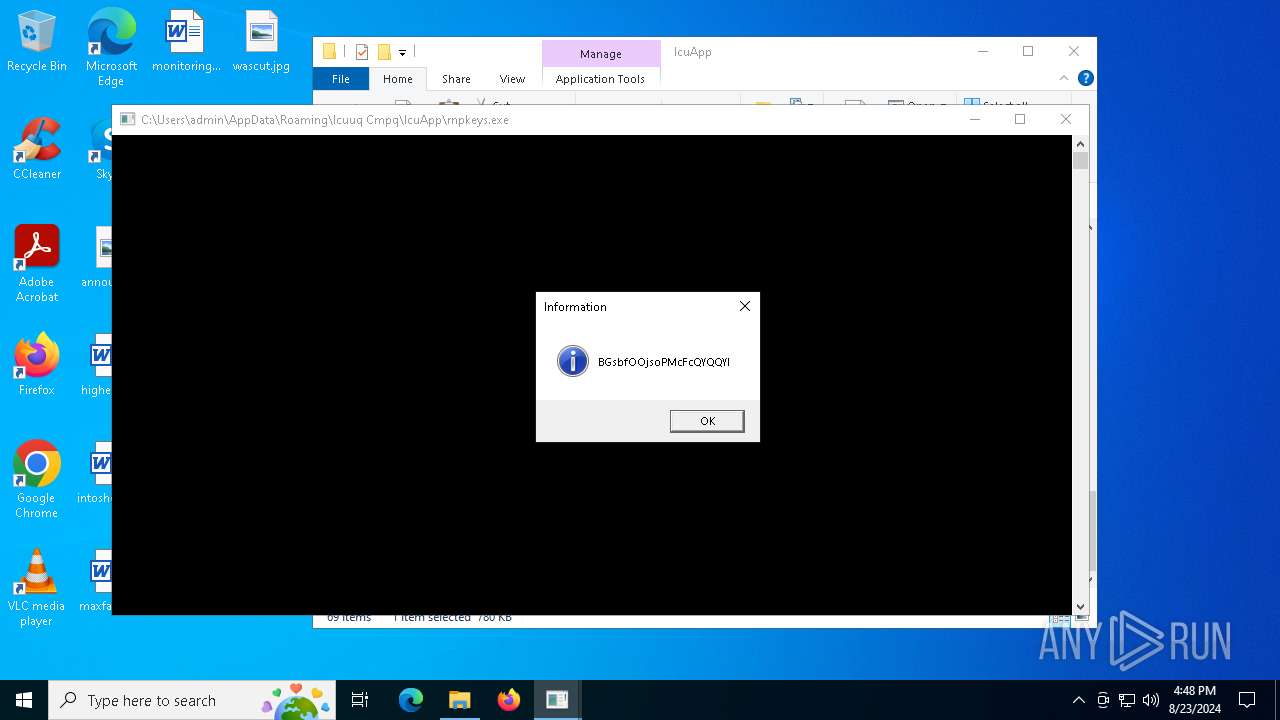
Threats
Process | Message |
|---|---|
rnpkeys.exe | Folder has been created! |