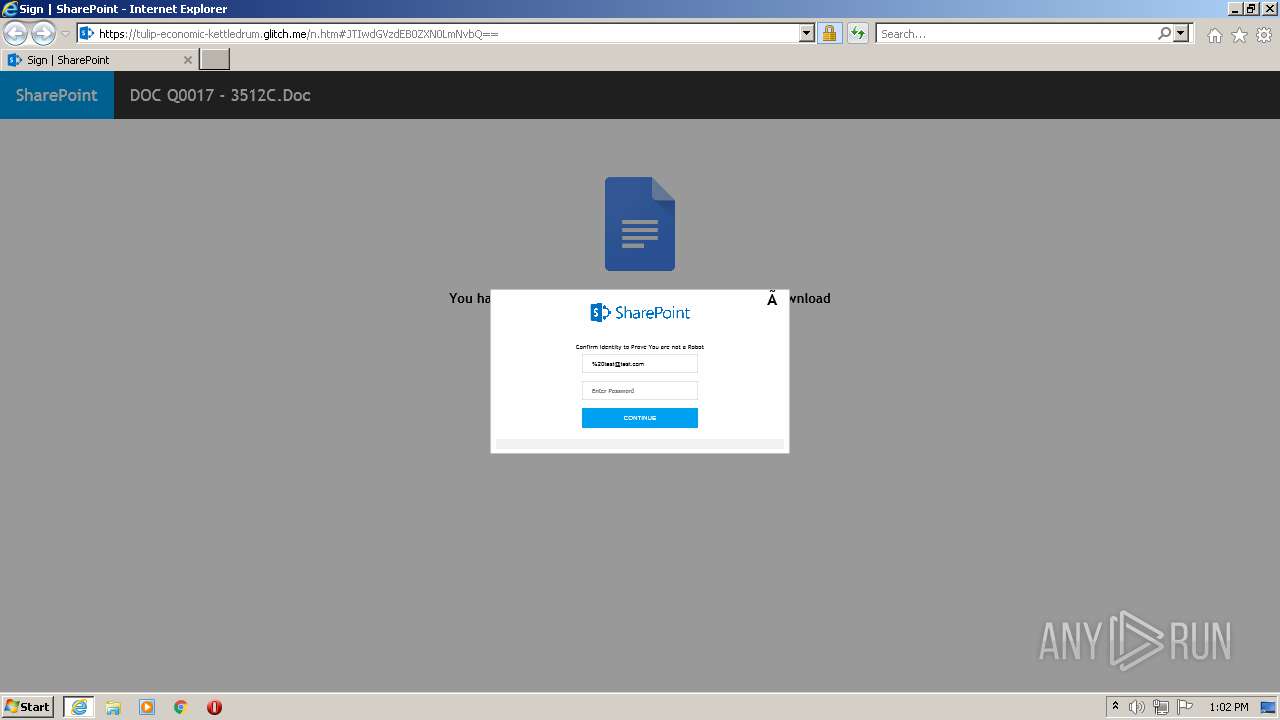
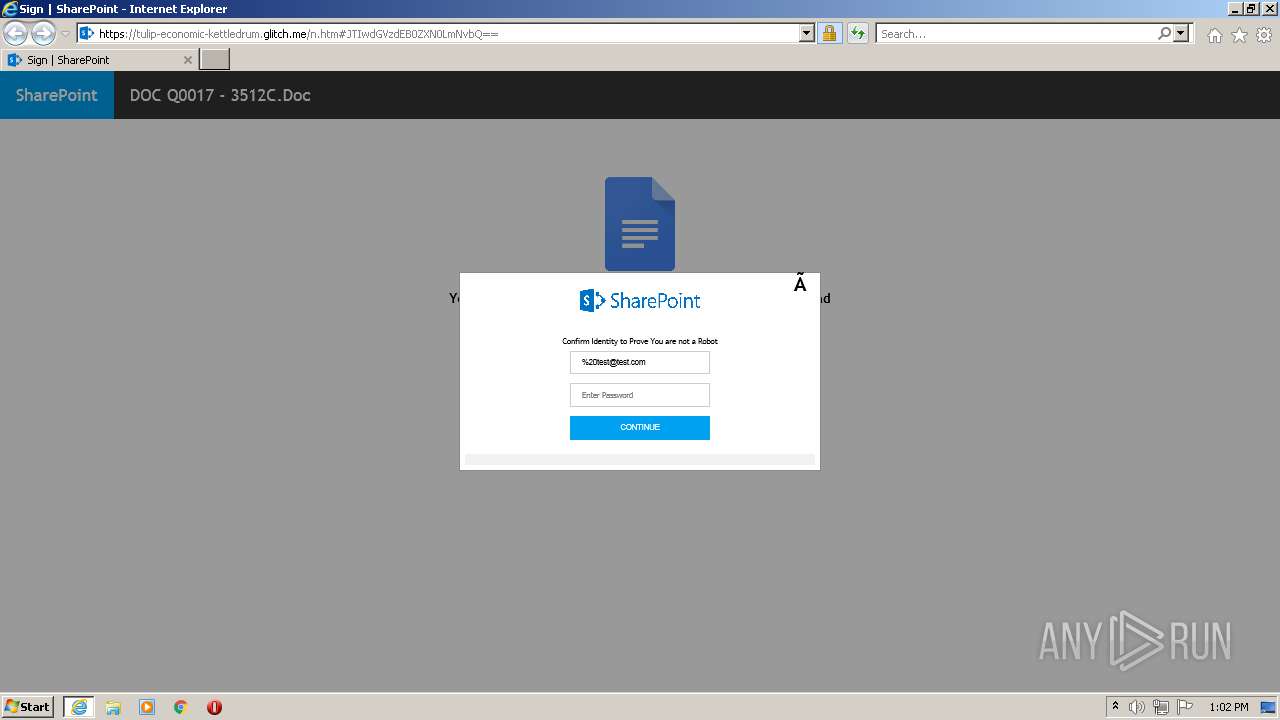
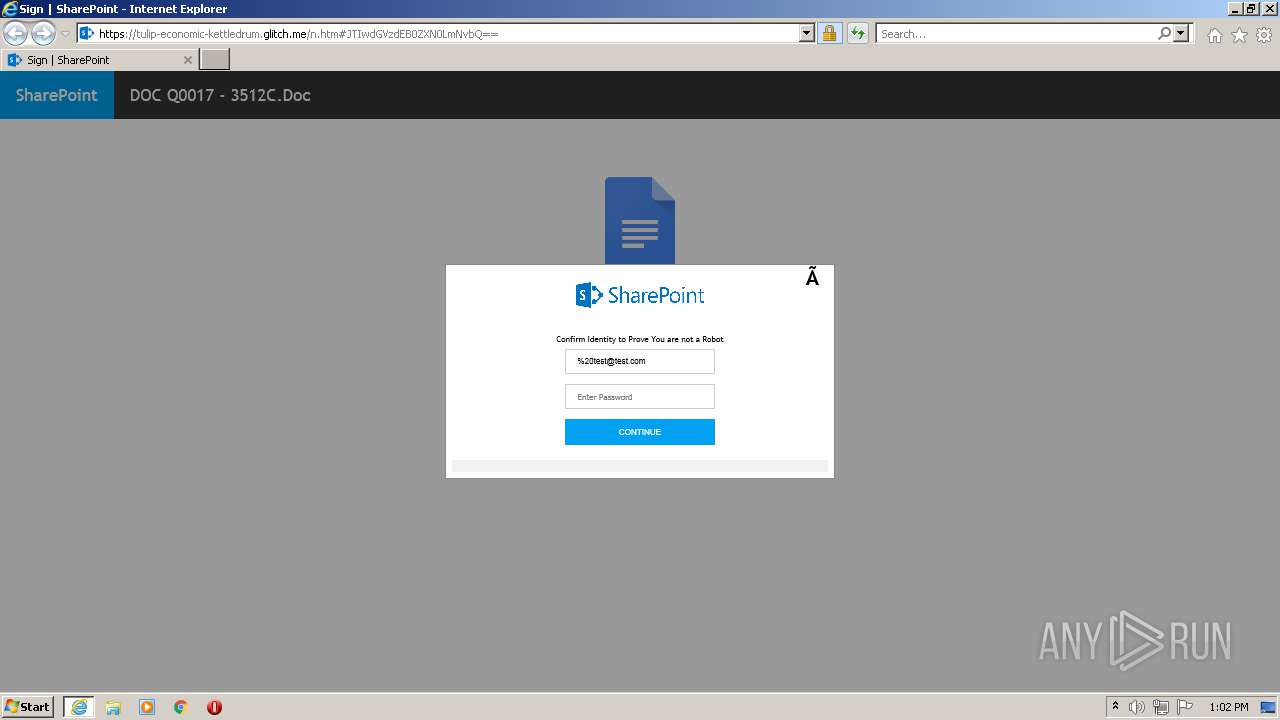
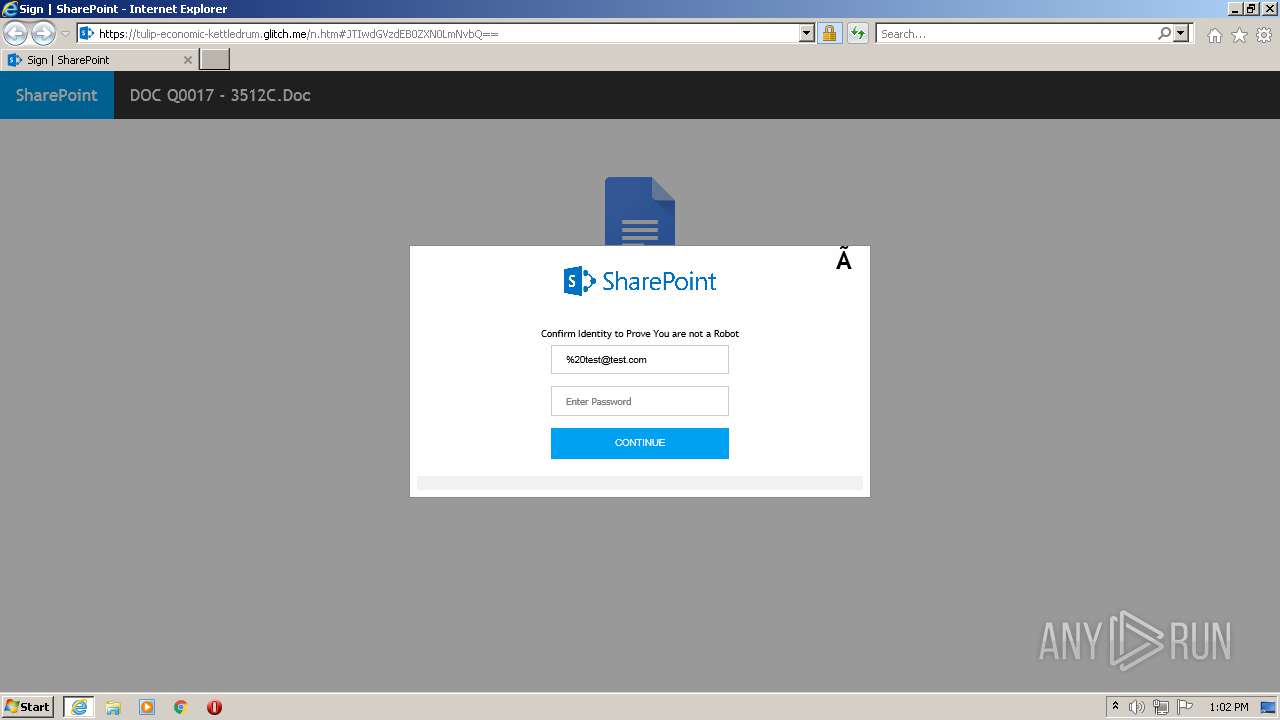
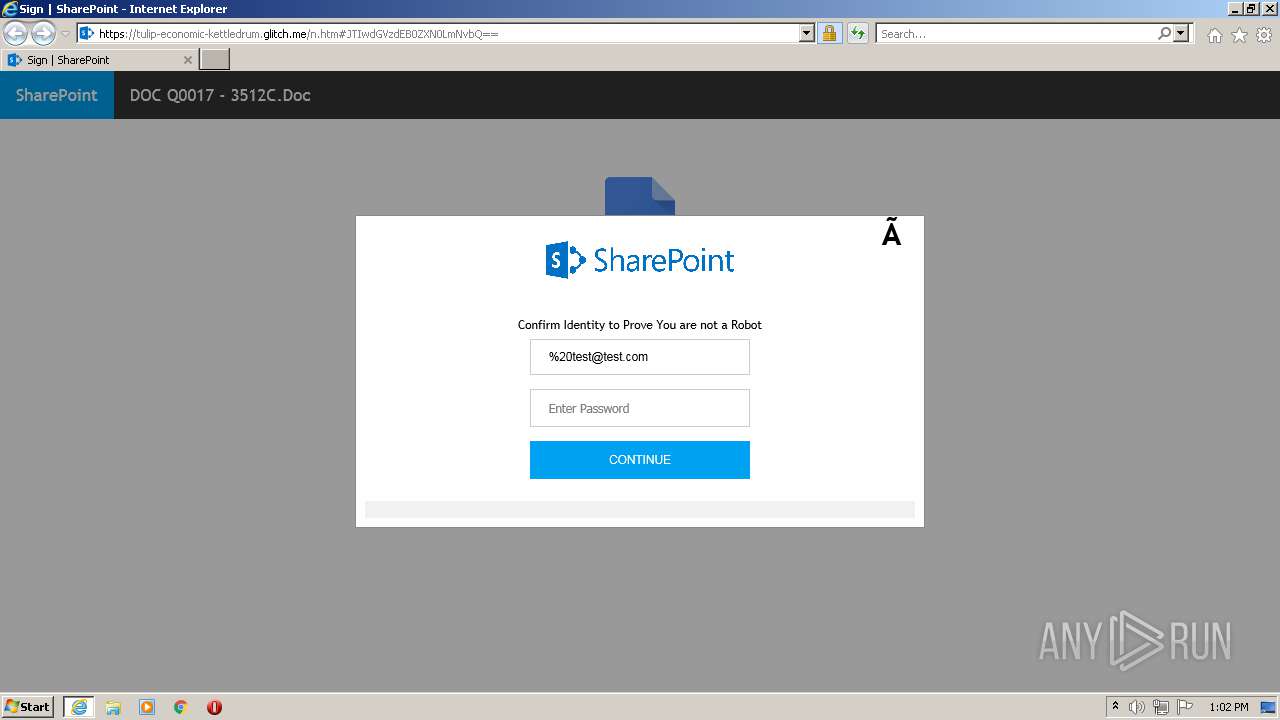
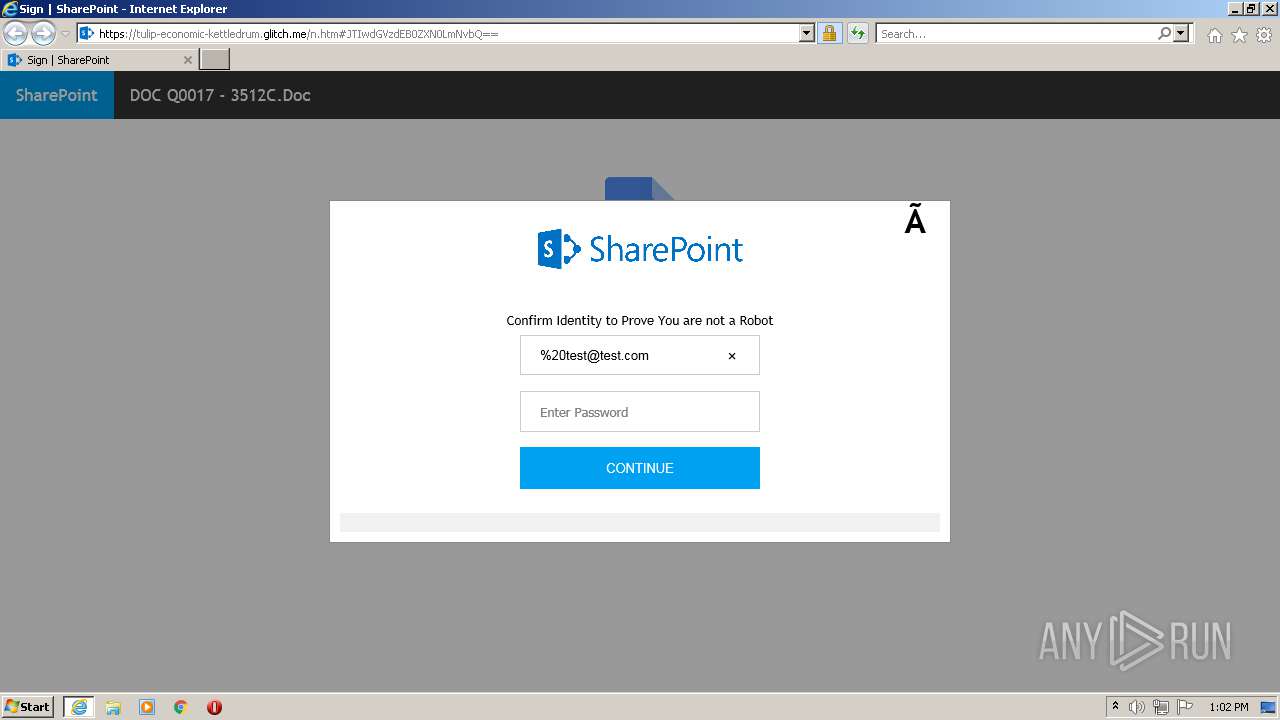
| URL: | https://spot-truthful-patio.glitch.me/red.htm#%20test@test.com |
| Full analysis: | https://app.any.run/tasks/cd14898d-94a7-4d99-bcc1-3dc688d1146d |
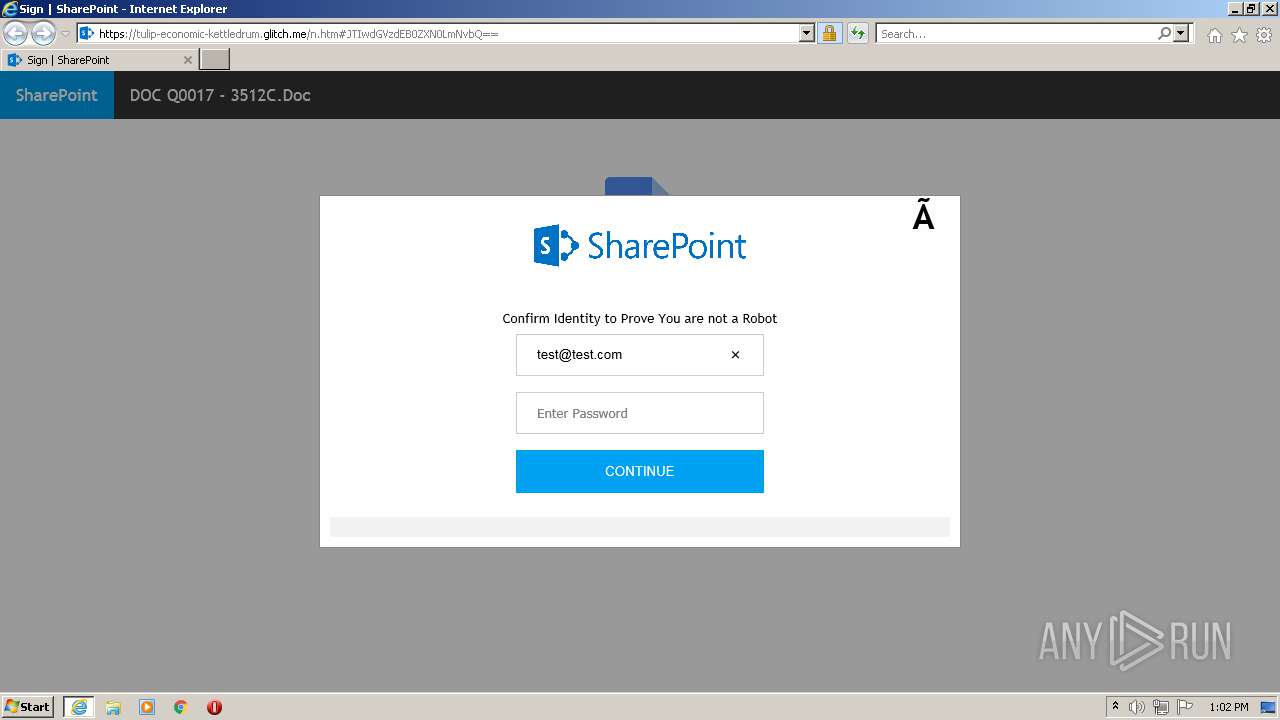
| Verdict: | Malicious activity |
| Analysis date: | August 23, 2021, 12:01:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 14BBE6C8146E23CDD73B6CE678C8C4B3 |
| SHA1: | 2D68F2606E8F60AE0C1E1B068B58C25C79805F82 |
| SHA256: | AB3000D2B9D496111A29EDF0FB8B6C64D369F822A0C4DA61C93C0B0B1FBDBDD7 |
| SSDEEP: | 3:N8Y6R2C4L2JQAoXAJqhlzIn:2Y6R2xKSZVhlzIn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1508)
INFO
Reads the computer name
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 1508)
Checks supported languages
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 1508)
Application launched itself
- iexplore.exe (PID: 3644)
Changes internet zones settings
- iexplore.exe (PID: 3644)
Checks Windows Trust Settings
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 1508)
Reads settings of System Certificates
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 1508)
Reads internet explorer settings
- iexplore.exe (PID: 1508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1508 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3644 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3644 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://spot-truthful-patio.glitch.me/red.htm#%20test@test.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
9 331
Read events
9 216
Write events
115
Delete events
0
Modification events
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30906390 | |||
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30906390 | |||
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
16
Text files
17
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:38D98D59269E239338B32B0DE903F97A | SHA256:3A7FAB2E8F6C972BE2F32200A4640282E249A4656160A9BC437866D6D8D702D4 | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:0B9BD55749A1DB65A17210B5B822839D | SHA256:08D52A4238A9273C98BD40D77EB2A0B92907A1F609D8A9CAC34F32A582208B73 | |||
| 1508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:DE7F52480022A7F8DEBA99332A5D29C5 | SHA256:47AAB9EFC5C36C512AAB2E6BF40D317817D5422A21F8FE13C5B57257102FAA8C | |||
| 1508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:42CE92A75C123698CA833BB953127098 | SHA256:3E49EBF4E6372D46D61F20B12B2541BE858368CC9443D9D59565F7F05C762721 | |||
| 1508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FC5A820A001B41D68902E051F36A5282_30F701A5D3F3E340D2DF9758F7784007 | der | |
MD5:F32A86C47ABD8CF200B7122A2327DAC0 | SHA256:A4DD414AACF111FD9815DFBC30CF549B590BE0481E0E17F1C27CA8C5C60B3C6C | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:60D1F6464A53AAEE7680932962AA12A9 | SHA256:A5ED22A753FBF3A86EA699186A3A99CCDAE71631BFBDE467BFAABB864B4E132F | |||
| 1508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\620BEF1064BD8E252C599957B3C91896 | der | |
MD5:743A25B75F830C0754C9E362C7454ACB | SHA256:606794203748F6653D098D54493F5F560CF6C69A63A2F736EBD0E0DA3F3F40BD | |||
| 1508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\620BEF1064BD8E252C599957B3C91896 | binary | |
MD5:43D9C572CC5792AC70D35444FB58EC88 | SHA256:5B59A390A069C751EED87731A0548C1D1AE5D072B44CDD8B8D48499CA4CD8220 | |||
| 1508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:916586F695C39CBF4C99D2678D43DD9B | SHA256:9D12C66B161C8F9AF0587AF56165BD34403C98E29AEC77E170CB710C720E903E | |||
| 1508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\n[1].htm | html | |
MD5:0E5E564A0CB1FD462DFB9EB532C2FD6E | SHA256:91F3518482DEE194BEE220DA2A8FAAFCC19C6D7AFB09C10A91029F25004EE9EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
34
DNS requests
24
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1508 | iexplore.exe | GET | 200 | 205.185.216.10:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cc400e3b380bef51 | US | compressed | 4.70 Kb | whitelisted |
1672 | svchost.exe | GET | 304 | 205.185.216.10:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e8d904dbd20b039b | US | — | — | whitelisted |
3644 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1508 | iexplore.exe | GET | 200 | 13.225.84.145:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
1508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEATMDKI2BYEZlA6LK6Vxj74%3D | US | der | 471 b | whitelisted |
1508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
1508 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1508 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
3644 | iexplore.exe | GET | 200 | 205.185.216.10:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?161ece0b70517f48 | US | compressed | 4.70 Kb | whitelisted |
1508 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCeFMaRQ3SNqAUAAAAAiBGe | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1508 | iexplore.exe | 13.225.84.42:80 | o.ss2.us | — | US | unknown |
1508 | iexplore.exe | 13.225.84.145:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
3644 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3644 | iexplore.exe | 205.185.216.10:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1508 | iexplore.exe | 13.225.84.120:80 | crl.rootca1.amazontrust.com | — | US | whitelisted |
3644 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1508 | iexplore.exe | 13.225.84.104:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
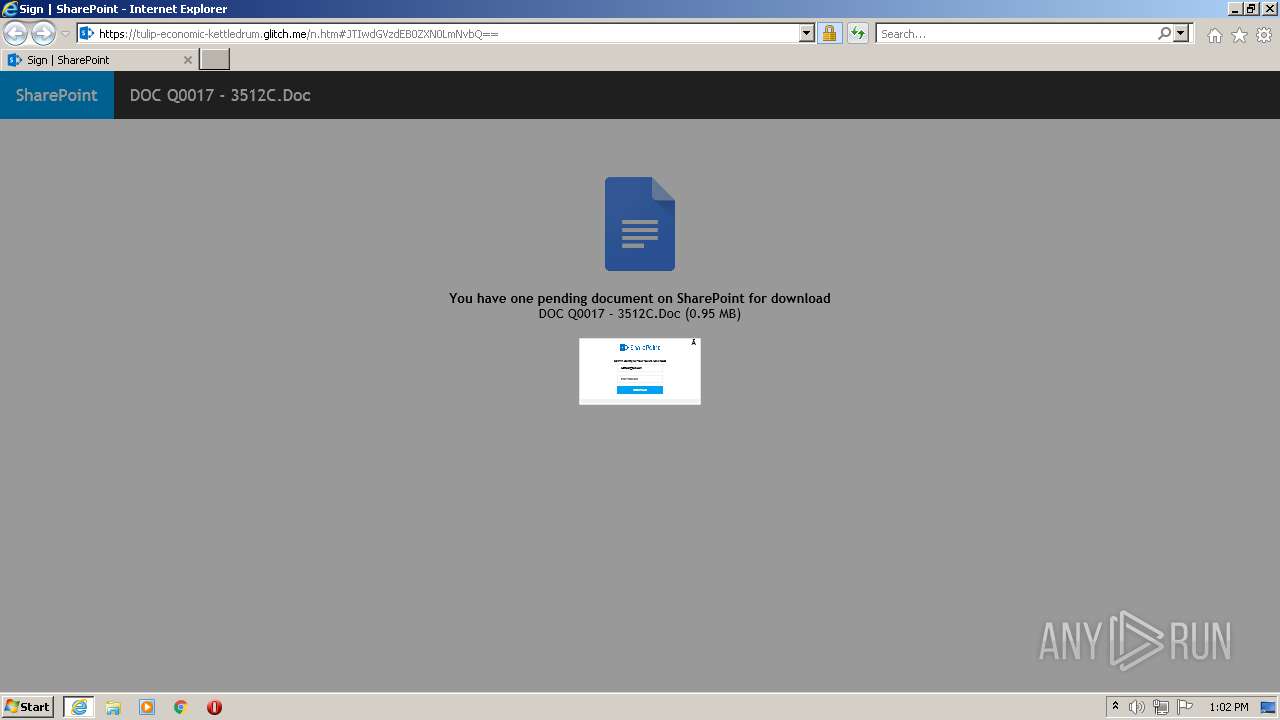
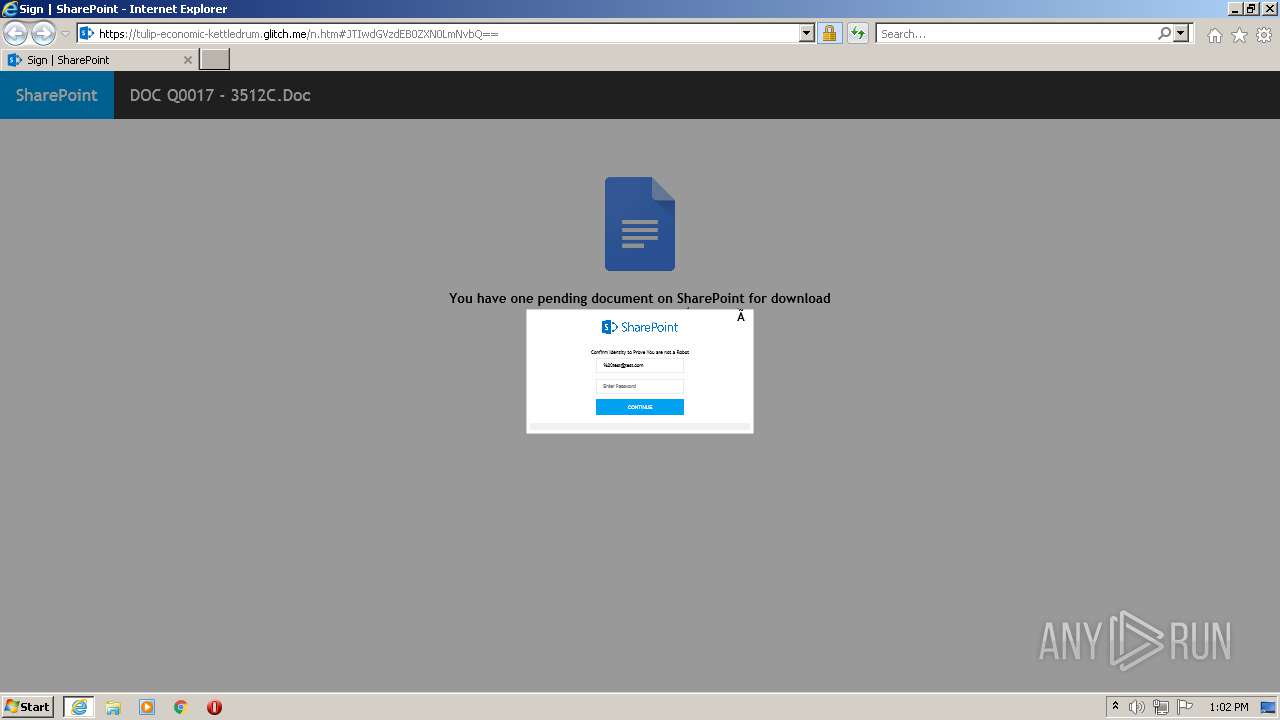
1508 | iexplore.exe | 162.125.66.15:443 | dl.dropbox.com | Dropbox, Inc. | DE | malicious |
1508 | iexplore.exe | 34.197.3.188:443 | spot-truthful-patio.glitch.me | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
spot-truthful-patio.glitch.me |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.rootca1.amazontrust.com |
| whitelisted |
ocsp.sca1b.amazontrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Suspicious Glitch Hosted DNS Request - Possible Phishing Landing |
1508 | iexplore.exe | Misc activity | ET INFO Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
— | — | A Network Trojan was detected | ET CURRENT_EVENTS Possible Glitch.me Phishing Domain |
— | — | Misc activity | ET INFO Suspicious Glitch Hosted DNS Request - Possible Phishing Landing |
1508 | iexplore.exe | Misc activity | ET INFO Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |