analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
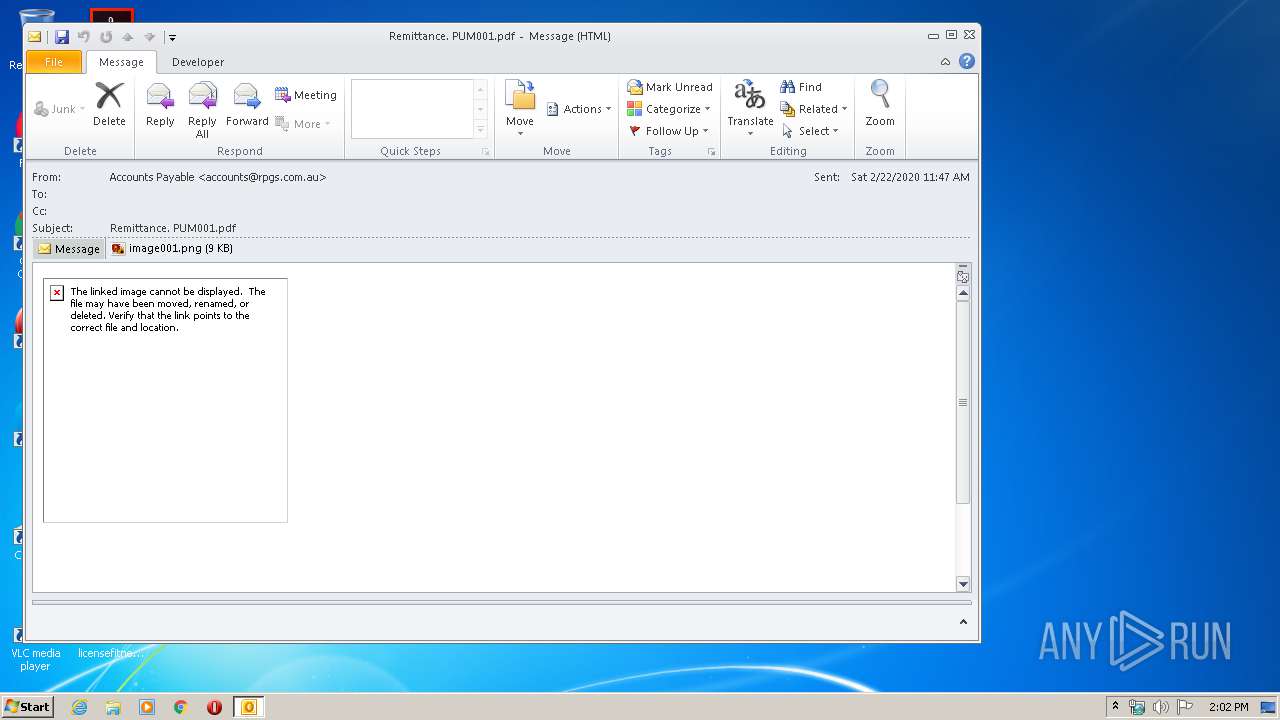
| File name: | 48PnYT01q4z4kBlB.eml |
| Full analysis: | https://app.any.run/tasks/a8d074b7-6863-45f6-b54f-23f128f47fd9 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 14:01:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines |
| MD5: | 4642C639E64B2118E75C3908A1C4D293 |
| SHA1: | 21B777873157F2F90204040E39AA7AA8436F7F94 |
| SHA256: | AB274563BD4C99D1E4C531DB4FF33C466E938EA26C5DB86EC888B1A2A9557643 |
| SSDEEP: | 384:Uzfd4hlBd1iu9SCMH6/S+6Qc0j90aB8/IRvgyF4dMQwZuO70MP7WjZw96L:W61dTrk6/P63mB5LhZh7j7CZt |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 304)
Creates files in the user directory
- OUTLOOK.EXE (PID: 304)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 304)
Executed via COM
- DllHost.exe (PID: 952)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 3588)
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 1948)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 304)
Changes internet zones settings
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 3020)
Application launched itself
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 3020)
Reads internet explorer settings
- iexplore.exe (PID: 3588)
- iexplore.exe (PID: 1948)
Reads settings of System Certificates
- iexplore.exe (PID: 3588)
- iexplore.exe (PID: 1948)
- iexplore.exe (PID: 3020)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3020)
Changes settings of System certificates
- iexplore.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
41
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 304 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\48PnYT01q4z4kBlB.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 14.0.6025.1000 | ||||
| 952 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
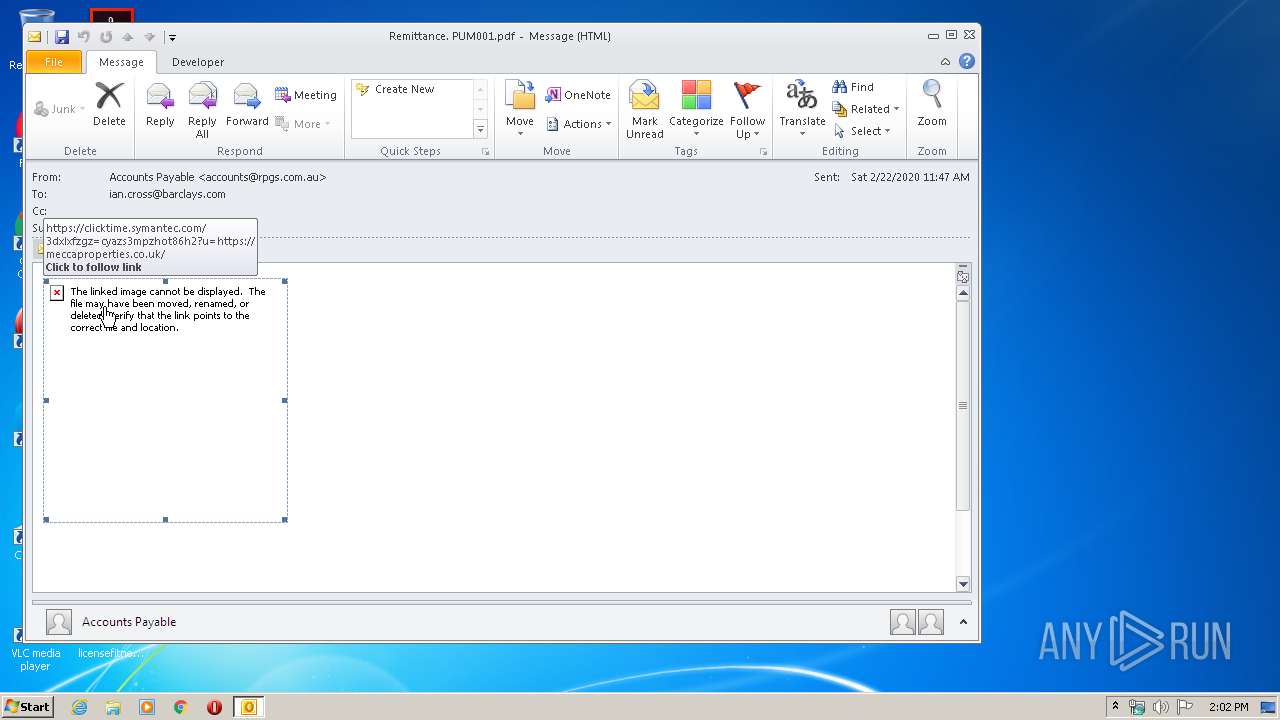
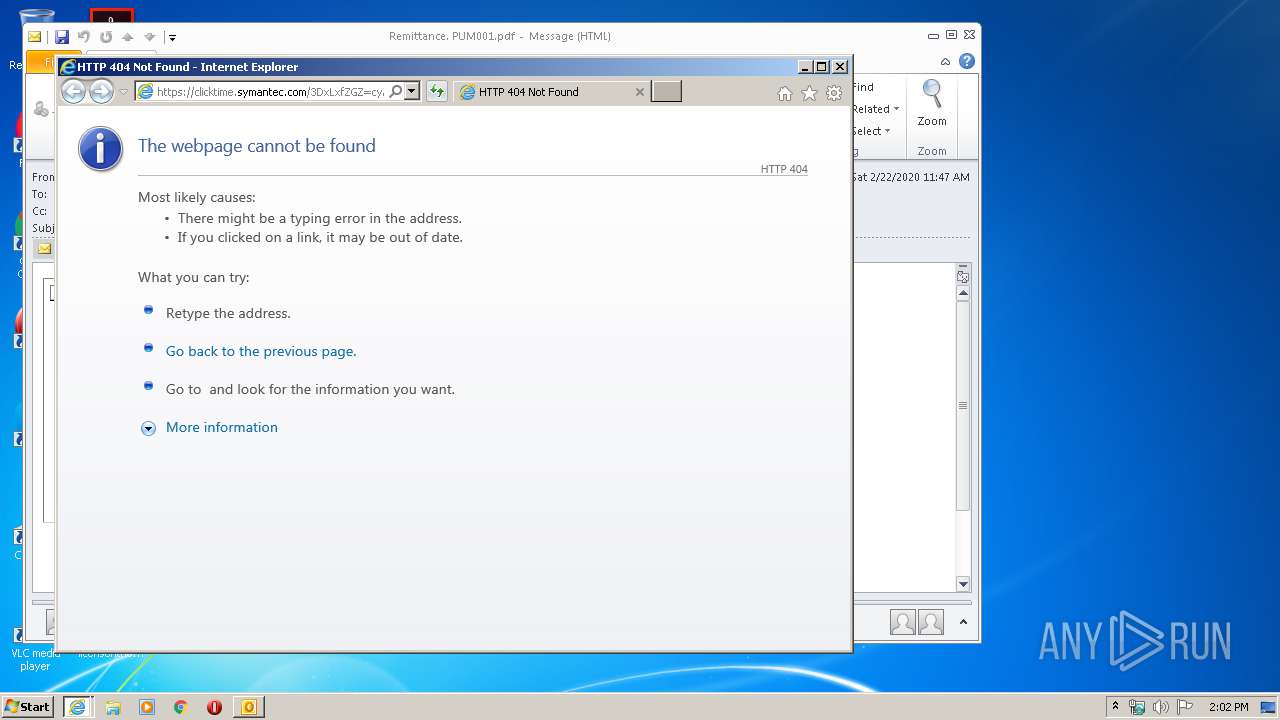
| 3316 | "C:\Program Files\Internet Explorer\iexplore.exe" https://clicktime.symantec.com/3DxLxfZGZ=cyAzS3MpZHoT86H2?u=https%3A%2F%2Fmeccaproperties.co.uk%2F | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 3020 | "C:\Program Files\Internet Explorer\iexplore.exe" https://clicktime.symantec.com/3DxLxfZGZ=cyAzS3MpZHoT86H2?u=https%3A%2F%2Fmeccaproperties.co.uk%2F | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 3588 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3316 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 1948 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3020 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
Total events
5 103
Read events
2 814
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
7
Text files
46
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C01.tmp.cvr | — | |
MD5:— | SHA256:— | |||
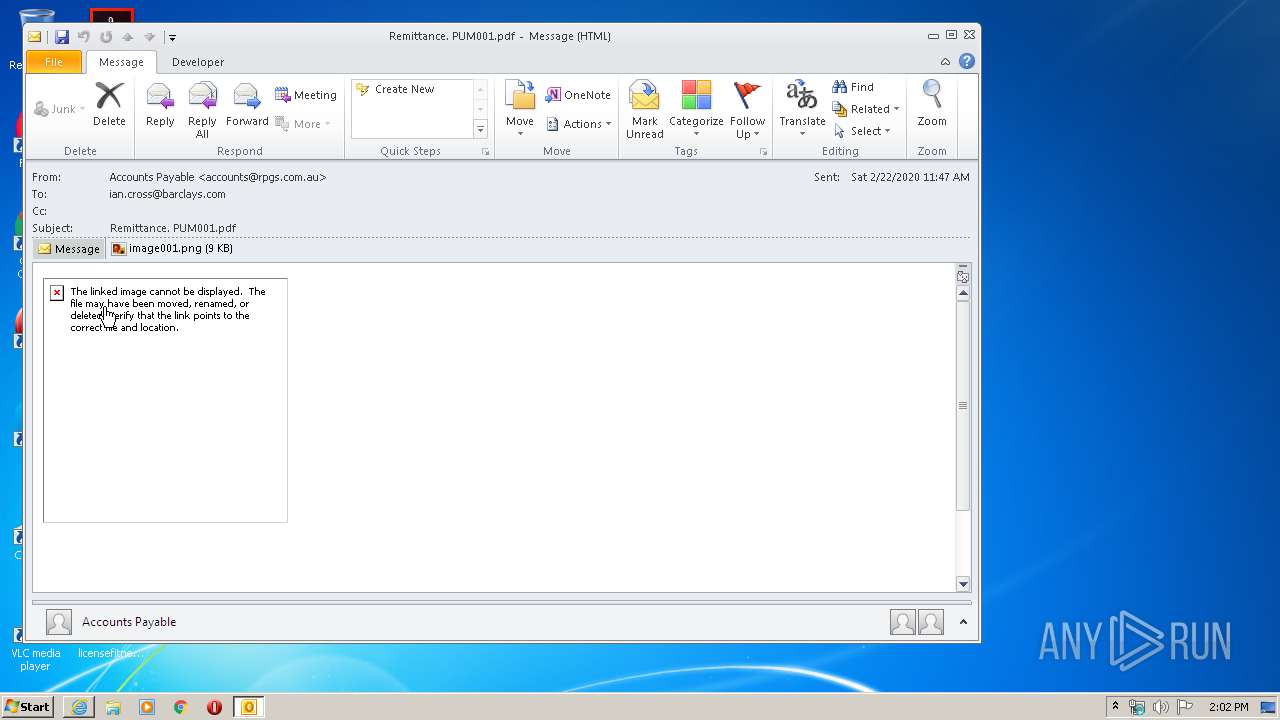
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\BO18V50Q\image001 (2).png\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabD01A.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD01B.tmp | — | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:4D6E4DE7D29E949D8534579E3D12CC70 | SHA256:F1B8B22F38D8245B581778AC5C2A58EEA2D4C0B99FA1936DF2F7EB84230EFC72 | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:A4A443C99C0BFC6E2353B242D1A96971 | SHA256:943066562FE26954EBDAC0CF0DA3894499366C8C87CA8B3D47BBCD1B4A95E4A0 | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\BO18V50Q\image001.png | image | |
MD5:C61846DBEC6002F40E6E502F2AEB9F40 | SHA256:FA2D6211EF9904EC8070DBF784B28DD731A971A70C60498BFCED0EF28EFCCFF4 | |||
| 3588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4F21952A714049709706EC223B44B03A_8D12746EFE073D92CFA4EC4B200698F2 | binary | |
MD5:436DB93AC8B129286162944B2266342C | SHA256:C4C83971A6EA4762E1BBA05213A8327A289CCC67CCB2FA38593DD17533649F17 | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_C699D67F7AE48642A500B100DEE48253.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_C71056DEF74B014BA1351B690B4A89AD.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
13
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
304 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3588 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSofjAxBuTohWXP6VJZj6bafABTLwQUJG4rLdBqklFRJWkBqppHponnQCACEARVgvu5%2FjcXZSNqWxpEG%2Bw%3D | US | der | 471 b | whitelisted |
3588 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAyO4MkNaokViAQGHuJB%2Ba8%3D | US | der | 471 b | whitelisted |
3588 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAyO4MkNaokViAQGHuJB%2Ba8%3D | US | der | 471 b | whitelisted |
3588 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSofjAxBuTohWXP6VJZj6bafABTLwQUJG4rLdBqklFRJWkBqppHponnQCACEARVgvu5%2FjcXZSNqWxpEG%2Bw%3D | US | der | 471 b | whitelisted |
3316 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
304 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3020 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3316 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1948 | iexplore.exe | 18.195.27.17:443 | clicktime.symantec.com | Amazon.com, Inc. | DE | unknown |
3588 | iexplore.exe | 18.195.27.17:443 | clicktime.symantec.com | Amazon.com, Inc. | DE | unknown |
3588 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3316 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
clicktime.symantec.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |