| File name: | http://www.ctrip.com/ |
| Full analysis: | https://app.any.run/tasks/ee24923e-0d38-45b4-a900-485712260f29 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 09:47:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 9C3F80CF3EBBB495B1AAFE7AF3A34993 |
| SHA1: | D96C86B6C73462C204556C201AAD237B73558588 |
| SHA256: | AB24AE3D2F6E8A85F3C16C15E4556238C8FACC04C29C6FD1FE3878F3E38358B1 |
| SSDEEP: | 6144:PYOow5oMghG80hUlPKD1gqvUKM1py1J141E19UIEFFa1L6D+S2VdB8Y2lOoOGeO5:Ppow5oMghG80hUlPKD1gqvUKM1py1J1u |
MALICIOUS
No malicious indicators.SUSPICIOUS
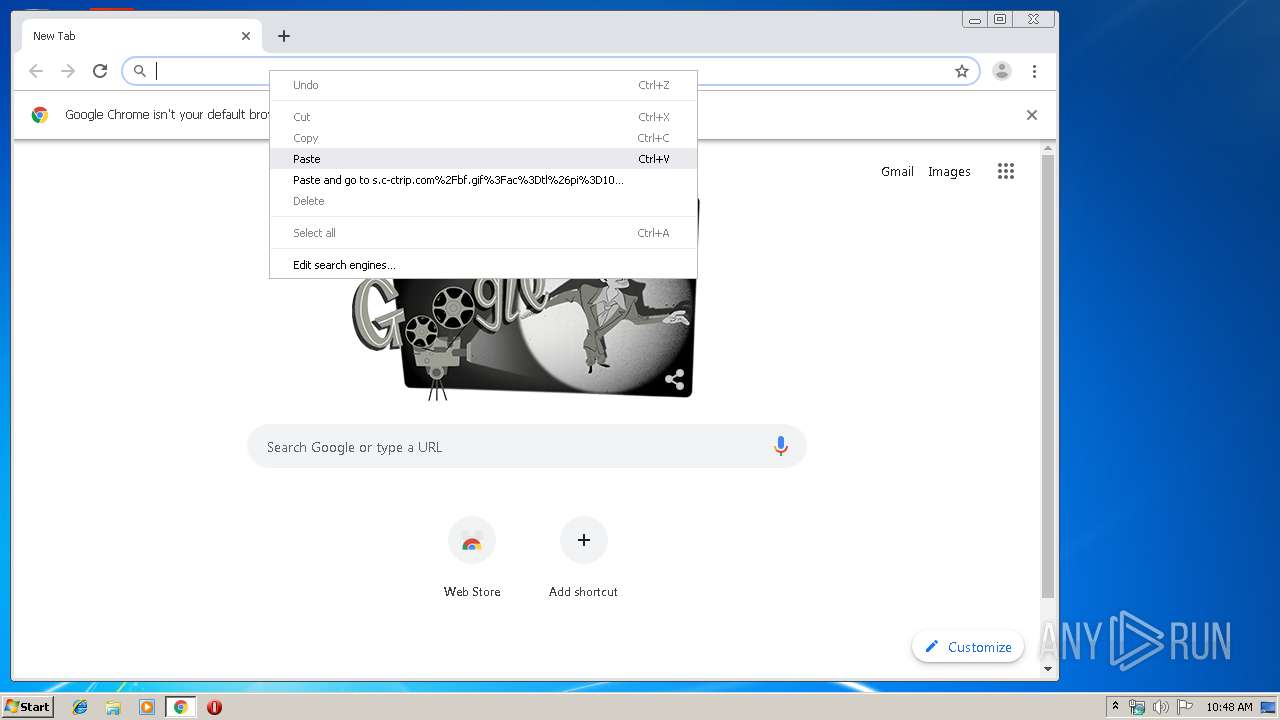
Modifies files in Chrome extension folder
- chrome.exe (PID: 3784)
INFO
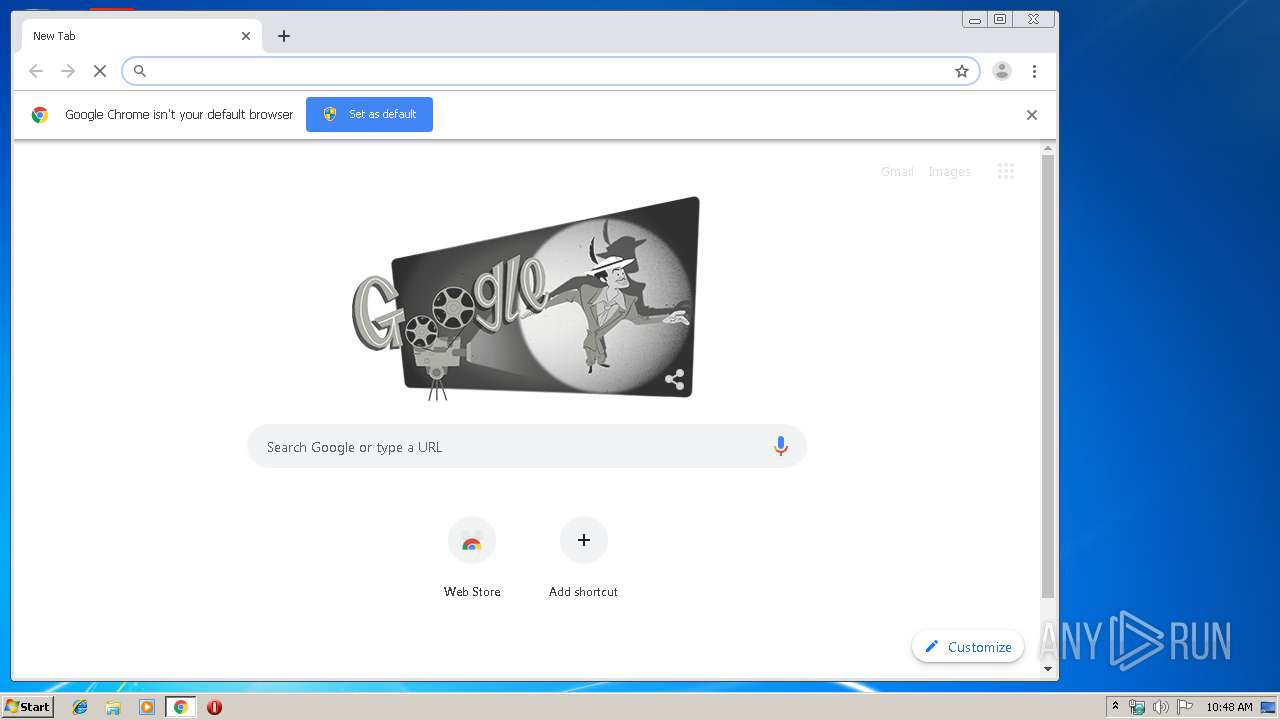
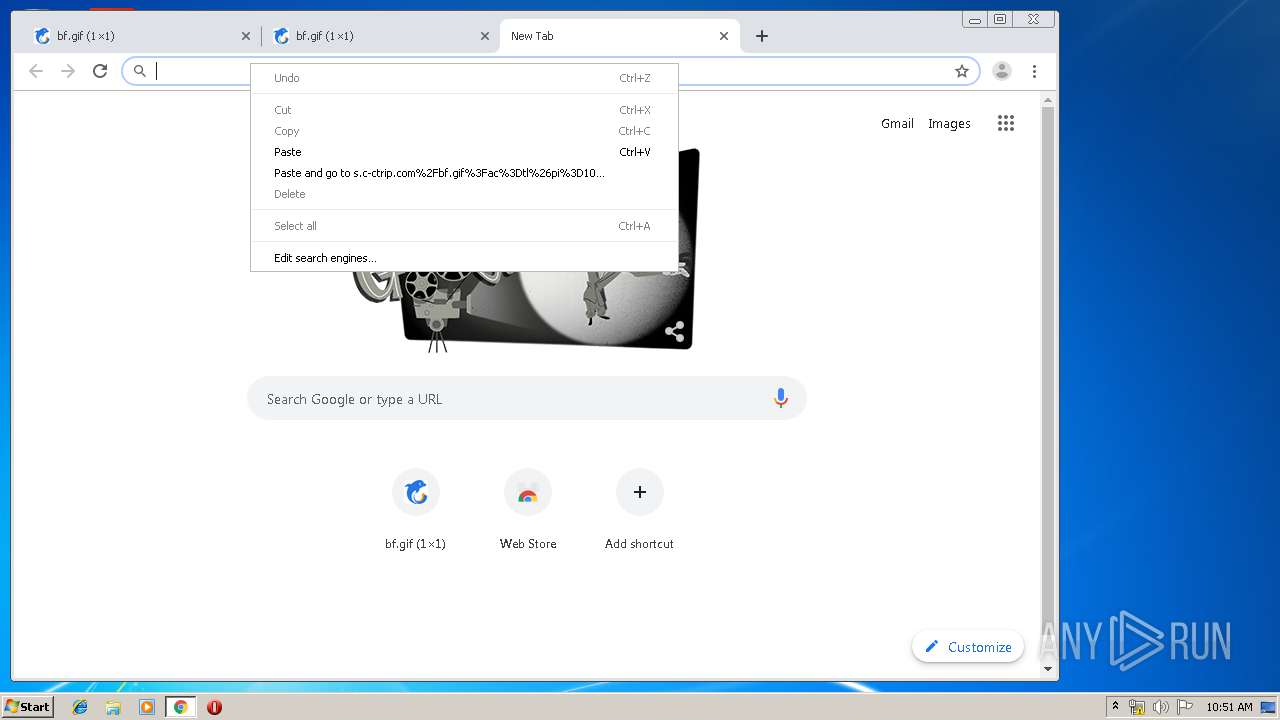
Manual execution by user
- chrome.exe (PID: 3784)
Reads the hosts file
- chrome.exe (PID: 3784)
- chrome.exe (PID: 3116)
Application launched itself
- chrome.exe (PID: 3784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| HTTPEquivXUACompatible: | IE=edge |
|---|---|
| ContentType: | text/html; charset=gb2312 |
| Description: | Я???????????й????ȵ????????з?????˾????9000????Ա?ṩ?Ƶ?Ԥ?????Ƶ????????ؼ۾Ƶ???ѯ????ƱԤ?????ɻ?Ʊ??ѯ??ʱ?̱�Ʊ?۲?ѯ????????ѯ???ȼ?Ԥ???????ù??�Ϊ???ij????ṩȫ??λ???з????? |
| Keywords: | ?Ƶ?Ԥ??,?ؼ۾Ƶ?, ??Ʊ,??ƱԤ??,?ɻ?Ʊ??ѯ,??????ѯ,?Ƶ??Ź?,???ζȼ?,????,???ù??? |
| Title: | Я????????????:?Ƶ?Ԥ??,??ƱԤ????ѯ,???ζȼ?,???ù??? |
Total processes
81
Monitored processes
46
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,4815314004157936351,225816199678238817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15787209085259401205 --mojo-platform-channel-handle=3360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,4815314004157936351,225816199678238817,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9152702176168496010 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,4815314004157936351,225816199678238817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5619123878733180602 --mojo-platform-channel-handle=3924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fd9a9d0,0x6fd9a9e0,0x6fd9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,4815314004157936351,225816199678238817,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9955123522096471390 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,4815314004157936351,225816199678238817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11897645243071286258 --mojo-platform-channel-handle=3668 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,4815314004157936351,225816199678238817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13097671710920541998 --mojo-platform-channel-handle=3400 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,4815314004157936351,225816199678238817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7099073712876127296 --mojo-platform-channel-handle=3948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,4815314004157936351,225816199678238817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6925486898688947236 --mojo-platform-channel-handle=3488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,4815314004157936351,225816199678238817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13010800894362292252 --mojo-platform-channel-handle=3428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
631
Read events
531
Write events
95
Delete events
5
Modification events
| (PID) Process: | (3784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3784-13213360127955250 |
Value: 259 | |||
| (PID) Process: | (3784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3784) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
73
Text files
164
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3120 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs8B1E.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs8B1F.tmp | — | |
MD5:— | SHA256:— | |||
| 3784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\15bdf402-c626-4c94-865c-f7d3872b2444.tmp | — | |
MD5:— | SHA256:— | |||
| 3784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF171a6d.TMP | text | |
MD5:— | SHA256:— | |||
| 3784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF171a6d.TMP | text | |
MD5:— | SHA256:— | |||
| 3784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
73
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
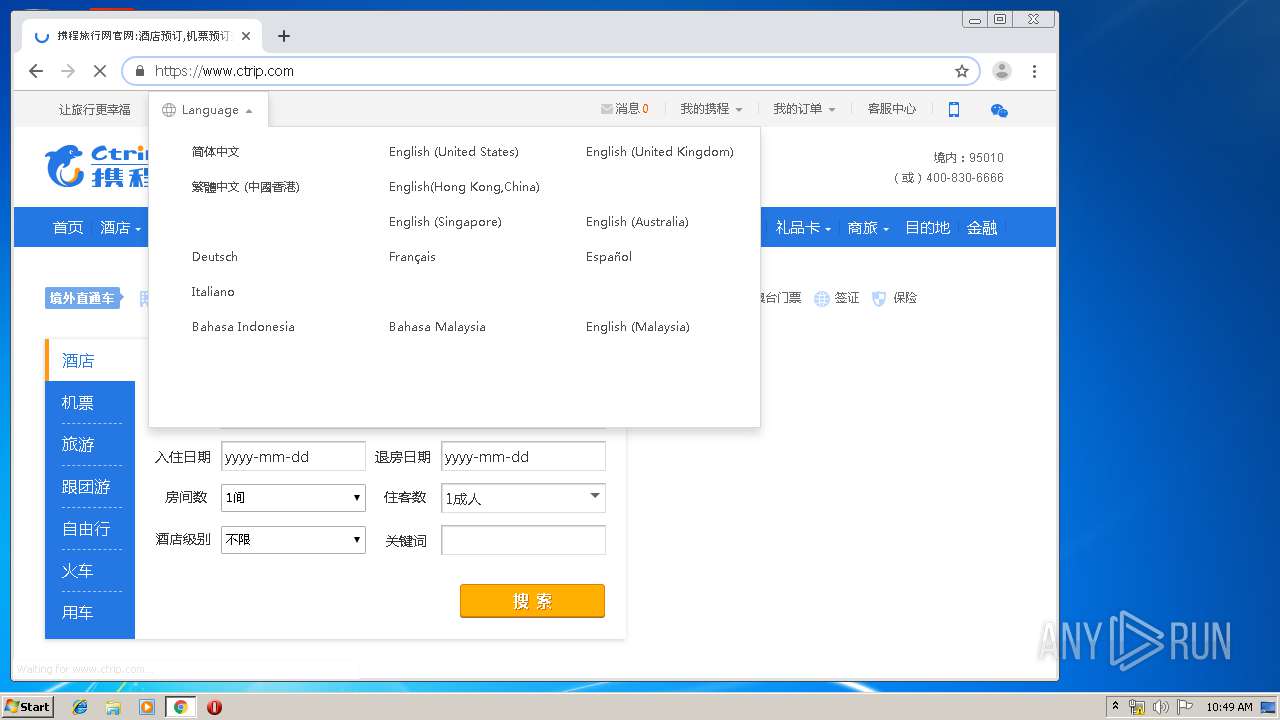
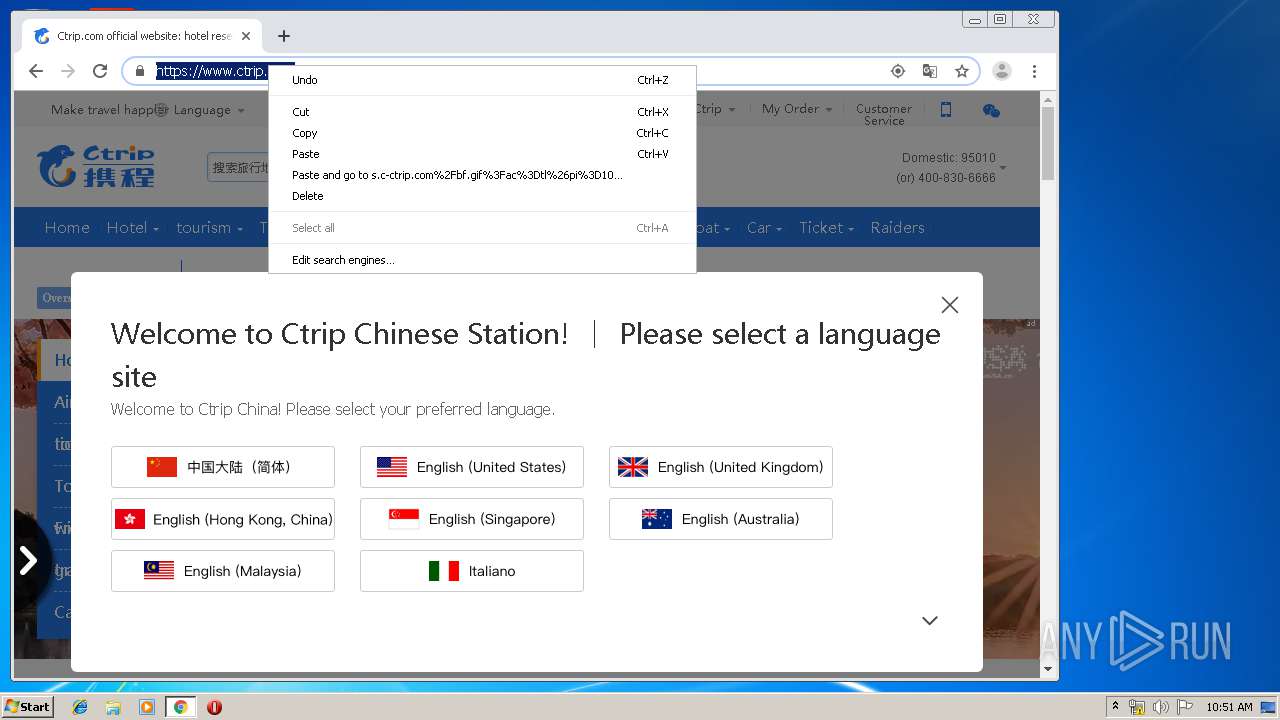
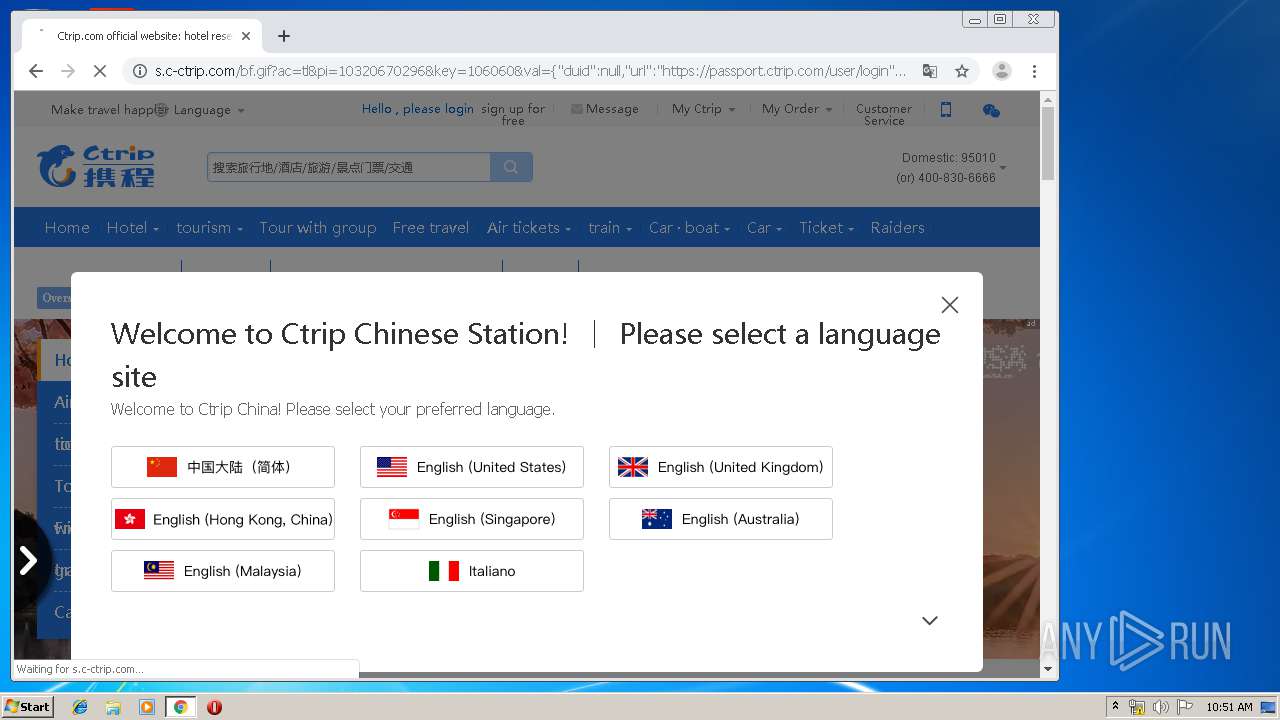
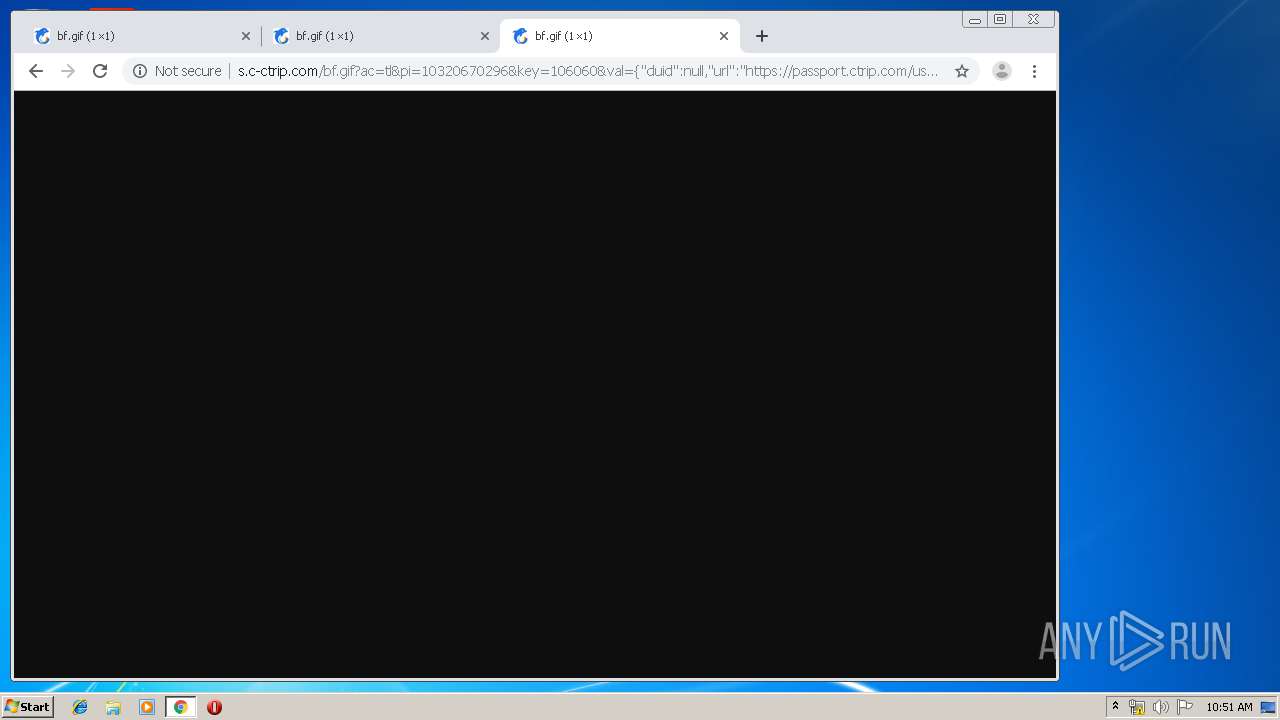
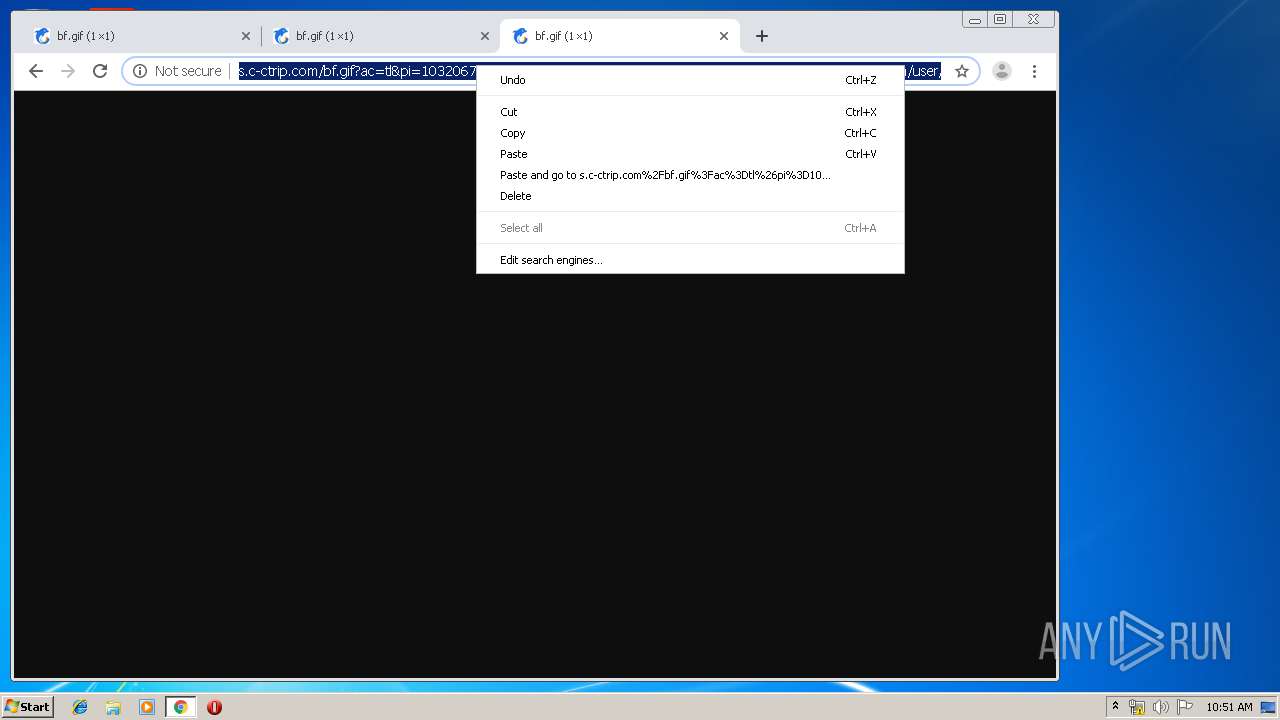
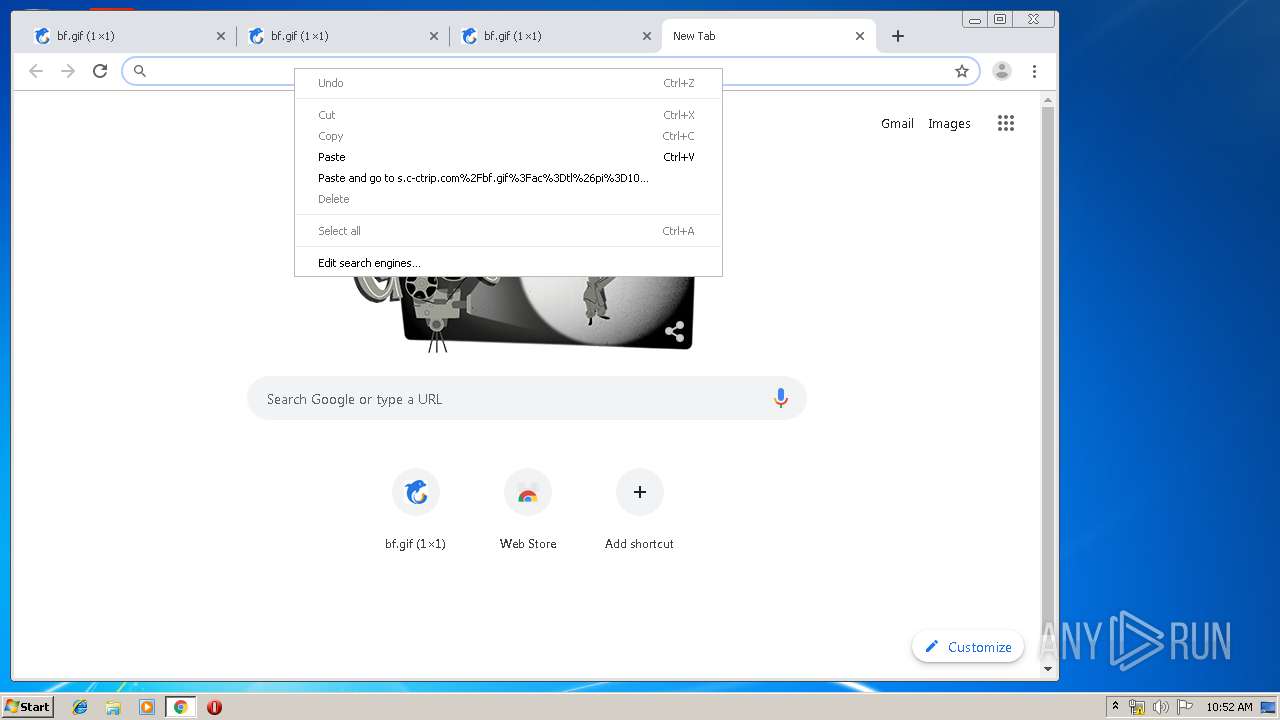
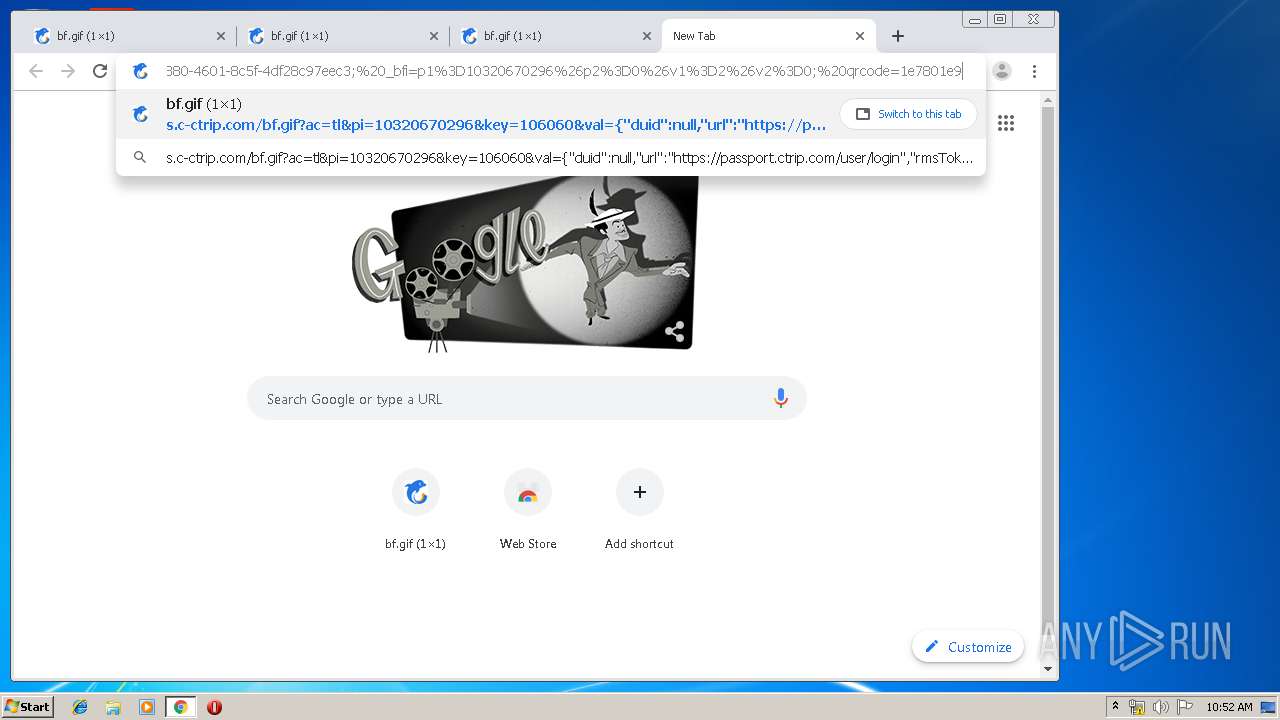
3116 | chrome.exe | GET | 200 | 23.45.108.46:80 | http://s.c-ctrip.com/bf.gif?ac=tl&pi=10320670296&key=106060&val={%22duid%22:null,%22url%22:%22https://passport.ctrip.com/user/login%22,%22rmsToken%22:%22fp=1cpfrcd-44fuwi-bsebf9&vid=1568872048825.4f08u3&pageId=10320670296&r=437c63f7388046018c5f4df28c97eec3&ip=221.122.91.78&rg=undefined&kpData=0_0_0&kpControl=0_0_0-0_0_0&kpEmp=0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0&screen=1600x900&tz=+8&blang=zh-CN&oslang=zh-CN&ua=Mozilla%2F5.0%20(Windows%20NT%2010.0%3B%20WOW64%3B%20Trident%2F7.0%3B%20.NET4.0C%3B%20.NET4.0E%3B%20.NET%20CLR%202.0.50727%3B%20.NET%20CLR%203.0.30729%3B%20.NET%20CLR%203.5.30729%3B%20rv%3A11.0)%20like%20Gecko&d=passport.ctrip.com&v=22%22,%22cookie%22:%22_bfs=1.2;%20_bfa=1.1568872048825.4f08u3.1.1568872048825.1568872048825.1.2;%20_sm_au_c=iHVr2WTr6ttLQ57P0a;%20gad_city=96617ee7af8aedd02bbece8583e0066e;%20_RF1=221.122.91.78;%20_RSG=1O4WuS_OyD43x.bCAVJVn8;%20_RDG=282c3cd622cc452c241c23ad45957020e4;%20_RGUID=437c63f7-3880-4601-8c5f-4df28c97eec3;%20_bfi=p1%3D10320670296%26p2%3D0%26v1%3D2%26v2%3D0;%20qrcode=1e7801e9 | NL | — | 43 b | malicious |
3116 | chrome.exe | GET | 200 | 23.45.108.46:80 | http://s.c-ctrip.com/bf.gif?ac=tl&pi=10320670296&key=106060&val={%22duid%22:null,%22url%22:%22https://passport.ctrip.com/user/login%22,%22rmsToken%22:%22fp=1cpfrcd-44fuwi-bsebf9&vid=1568872048825.4f08u3&pageId=10320670296&r=437c63f7388046018c5f4df28c97eec3&ip=221.122.91.78&rg=undefined&kpData=0_0_0&kpControl=0_0_0-0_0_0&kpEmp=0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0&screen=1600x900&tz=+8&blang=zh-CN&oslang=zh-CN&ua=Mozilla%2F5.0%20(Windows%20NT%2010.0%3B%20WOW64%3B%20Trident%2F7.0%3B%20.NET4.0C%3B%20.NET4.0E%3B%20.NET%20CLR%202.0.50727%3B%20.NET%20CLR%203.0.30729%3B%20.NET%20CLR%203.5.30729%3B%20rv%3A11.0)%20like%20Gecko&d=passport.ctrip.com&v=22%22,%22cookie%22:%22_bfs=1.2;%20_bfa=1.1568872048825.4f08u3.1.1568872048825.1568872048825.1.2;%20_sm_au_c=iHVr2WTr6ttLQ57P0a;%20gad_city=96617ee7af8aedd02bbece8583e0066e;%20_RF1=221.122.91.78;%20_RSG=1O4WuS_OyD43x.bCAVJVn8;%20_RDG=282c3cd622cc452c241c23ad45957020e4;%20_RGUID=437c63f7-3880-4601-8c5f-4df28c97eec3;%20_bfi=p1%3D10320670296%26p2%3D0%26v1%3D2%26v2%3D0;%20qrcode=1e7801e9 | NL | — | 43 b | malicious |
3116 | chrome.exe | GET | 200 | 23.45.108.46:80 | http://s.c-ctrip.com/bf.gif?ac=tl&pi=10320670296&key=106060&val={%22duid%22:null,%22url%22:%22https://passport.ctrip.com/user/login%22,%22rmsToken%22:%22fp=1cpfrcd-44fuwi-bsebf9&vid=1568872048825.4f08u3&pageId=10320670296&r=437c63f7388046018c5f4df28c97eec3&ip=221.122.91.78&rg=undefined&kpData=0_0_0&kpControl=0_0_0-0_0_0&kpEmp=0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0&screen=1600x900&tz=+8&blang=zh-CN&oslang=zh-CN&ua=Mozilla%2F5.0%20(Windows%20NT%2010.0%3B%20WOW64%3B%20Trident%2F7.0%3B%20.NET4.0C%3B%20.NET4.0E%3B%20.NET%20CLR%202.0.50727%3B%20.NET%20CLR%203.0.30729%3B%20.NET%20CLR%203.5.30729%3B%20rv%3A11.0)%20like%20Gecko&d=passport.ctrip.com&v=22%22,%22cookie%22:%22_bfs=1.2;%20_bfa=1.1568872048825.4f08u3.1.1568872048825.1568872048825.1.2;%20_sm_au_c=iHVr2WTr6ttLQ57P0a;%20gad_city=96617ee7af8aedd02bbece8583e0066e;%20_RF1=221.122.91.78;%20_RSG=1O4WuS_OyD43x.bCAVJVn8;%20_RDG=282c3cd622cc452c241c23ad45957020e4;%20_RGUID=437c63f7-3880-4601-8c5f-4df28c97eec3;%20_bfi=p1%3D10320670296%26p2%3D0%26v1%3D2%26v2%3D0;%20qrcode=1e7801e9 | NL | — | 43 b | malicious |
3116 | chrome.exe | GET | 200 | 23.45.108.46:80 | http://s.c-ctrip.com/bf.gif?ac=tl&pi=10320670296&key=106060&val={%22duid%22:null,%22url%22:%22https://passport.ctrip.com/user/login%22,%22rmsToken%22:%22fp=1cpfrcd-44fuwi-bsebf9&vid=1568872048825.4f08u3&pageId=10320670296&r=437c63f7388046018c5f4df28c97eec3&ip=221.122.91.78&rg=undefined&kpData=0_0_0&kpControl=0_0_0-0_0_0&kpEmp=0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0&screen=1600x900&tz=+8&blang=zh-CN&oslang=zh-CN&ua=Mozilla%2F5.0%20(Windows%20NT%2010.0%3B%20WOW64%3B%20Trident%2F7.0%3B%20.NET4.0C%3B%20.NET4.0E%3B%20.NET%20CLR%202.0.50727%3B%20.NET%20CLR%203.0.30729%3B%20.NET%20CLR%203.5.30729%3B%20rv%3A11.0)%20like%20Gecko&d=passport.ctrip.com&v=22%22,%22cookie%22:%22_bfs=1.2;%20_bfa=1.1568872048825.4f08u3.1.1568872048825.1568872048825.1.2;%20_sm_au_c=iHVr2WTr6ttLQ57P0a;%20gad_city=96617ee7af8aedd02bbece8583e0066e;%20_RF1=221.122.91.78;%20_RSG=1O4WuS_OyD43x.bCAVJVn8;%20_RDG=282c3cd622cc452c241c23ad45957020e4;%20_RGUID=437c63f7-3880-4601-8c5f-4df28c97eec3;%20_bfi=p1%3D10320670296%26p2%3D0%26v1%3D2%26v2%3D0;%20qrcode=1e7801e9 | NL | — | 43 b | malicious |
3116 | chrome.exe | GET | 200 | 23.45.108.46:80 | http://s.c-ctrip.com/bf.gif?ac=tl&pi=10320670296&key=106060&val={%22duid%22:null,%22url%22:%22https://passport.ctrip.com/user/login%22,%22rmsToken%22:%22fp=1cpfrcd-44fuwi-bsebf9&vid=1568872048825.4f08u3&pageId=10320670296&r=437c63f7388046018c5f4df28c97eec3&ip=221.122.91.78&rg=undefined&kpData=0_0_0&kpControl=0_0_0-0_0_0&kpEmp=0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0-0_0_0_0_0_0_0_0_0_0&screen=1600x900&tz=+8&blang=zh-CN&oslang=zh-CN&ua=Mozilla%2F5.0%20(Windows%20NT%2010.0%3B%20WOW64%3B%20Trident%2F7.0%3B%20.NET4.0C%3B%20.NET4.0E%3B%20.NET%20CLR%202.0.50727%3B%20.NET%20CLR%203.0.30729%3B%20.NET%20CLR%203.5.30729%3B%20rv%3A11.0)%20like%20Gecko&d=passport.ctrip.com&v=22%22,%22cookie%22:%22_bfs=1.2;%20_bfa=1.1568872048825.4f08u3.1.1568872048825.1568872048825.1.2;%20_sm_au_c=iHVr2WTr6ttLQ57P0a;%20gad_city=96617ee7af8aedd02bbece8583e0066e;%20_RF1=221.122.91.78;%20_RSG=1O4WuS_OyD43x.bCAVJVn8;%20_RDG=282c3cd622cc452c241c23ad45957020e4;%20_RGUID=437c63f7-3880-4601-8c5f-4df28c97eec3;%20_bfi=p1%3D10320670296%26p2%3D0%26v1%3D2%26v2%3D0;%20qrcode=1e7801e9 | NL | — | 43 b | malicious |
3116 | chrome.exe | GET | 200 | 23.45.108.52:80 | http://pic.c-ctrip.com/common/beam.png | NL | image | 13.6 Kb | whitelisted |
3116 | chrome.exe | GET | 200 | 23.45.108.52:80 | http://pic.c-ctrip.com/common/bl.png | NL | image | 29.5 Kb | whitelisted |
3116 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3116 | chrome.exe | GET | 200 | 23.45.108.52:80 | http://webresource.c-ctrip.com/code/ubt/_bfa.min.js?v=20198_19 | NL | text | 19.2 Kb | whitelisted |
3116 | chrome.exe | GET | 200 | 23.45.108.52:80 | http://pic.c-ctrip.com/common/404_bg.jpg | NL | image | 44.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 23.45.108.46:80 | s.c-ctrip.com | Akamai International B.V. | NL | whitelisted |
3116 | chrome.exe | 172.217.16.142:443 | ogs.google.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
s.c-ctrip.com |
| malicious |
www.google.com |
| malicious |