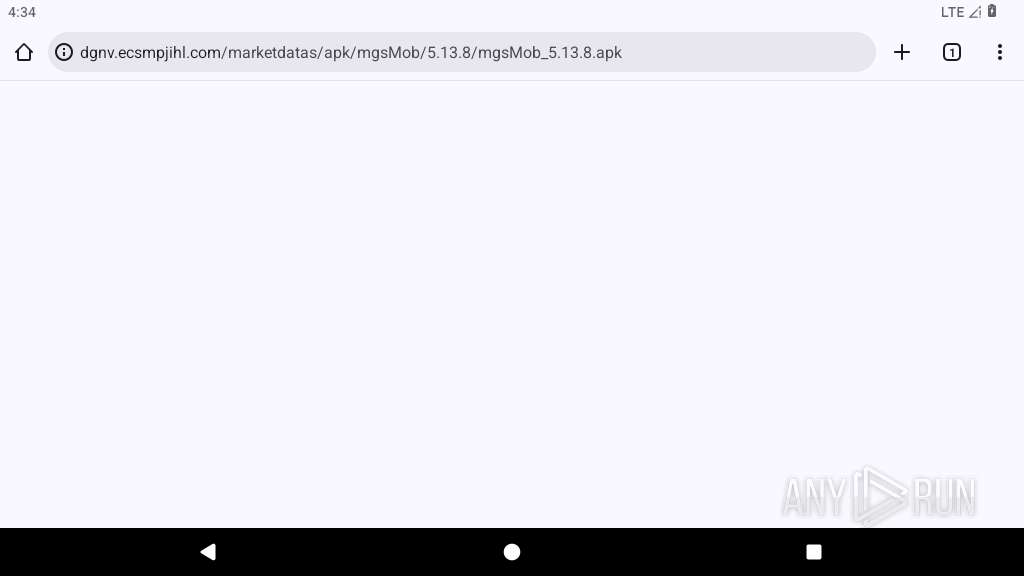
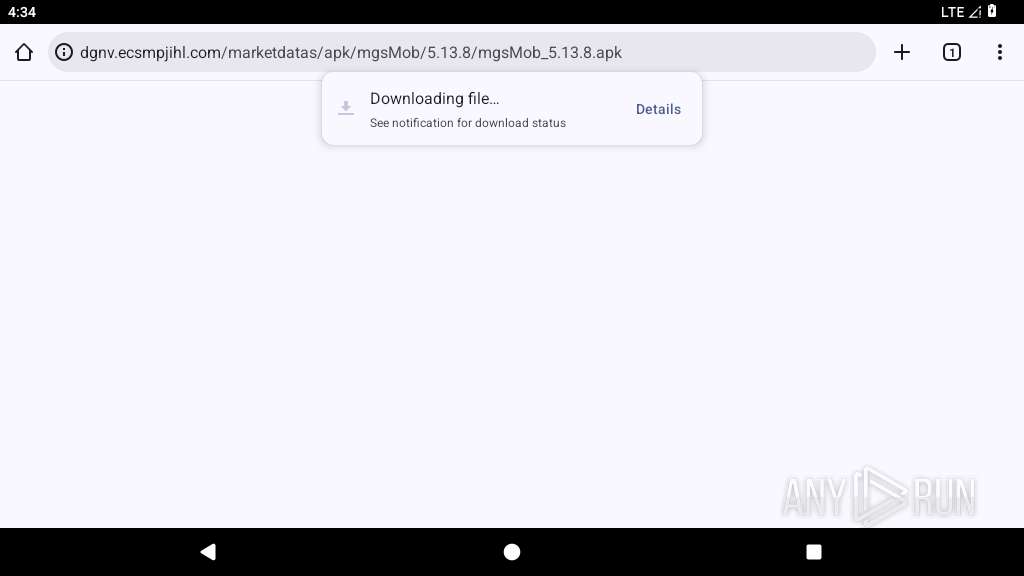
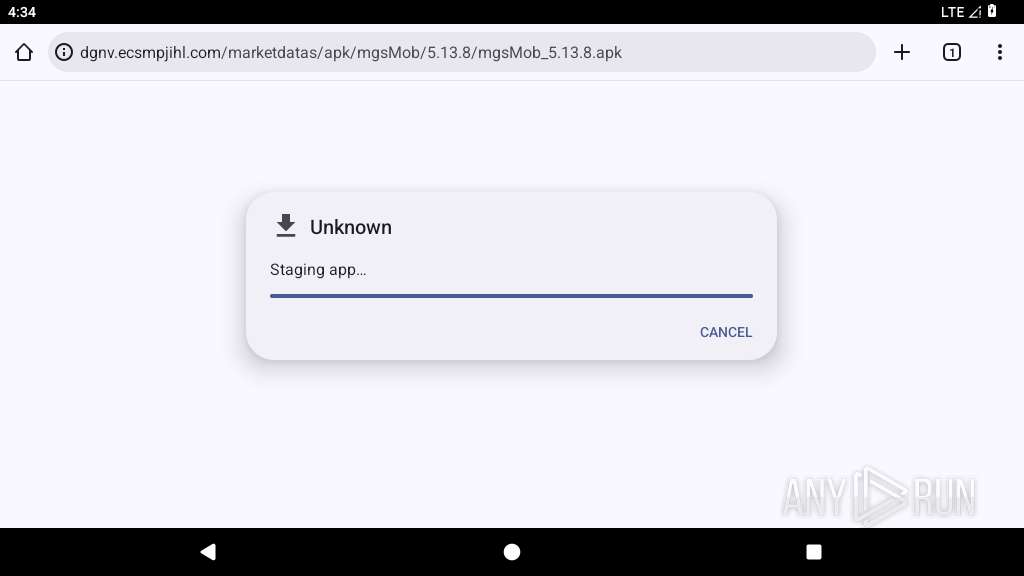
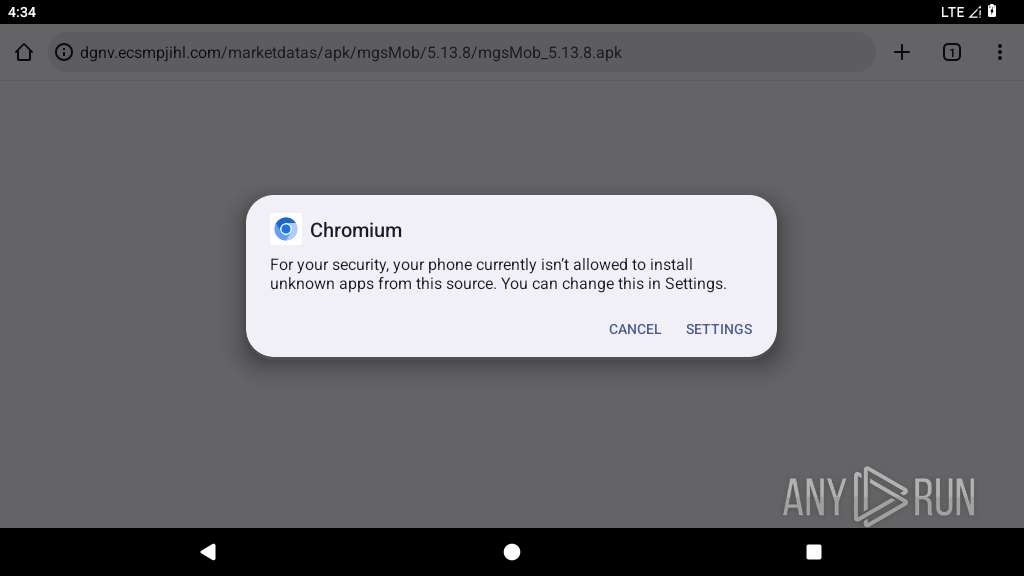
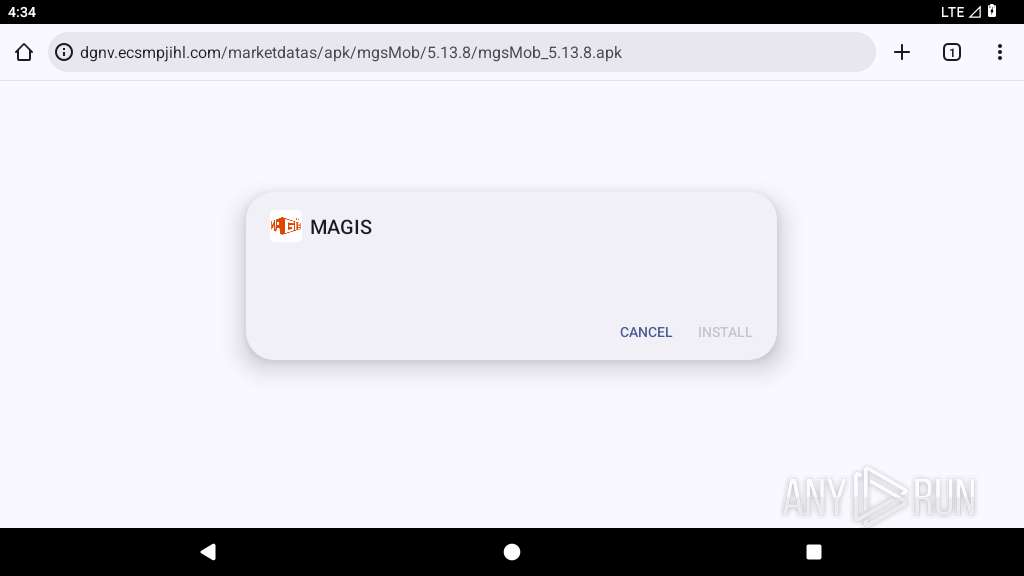
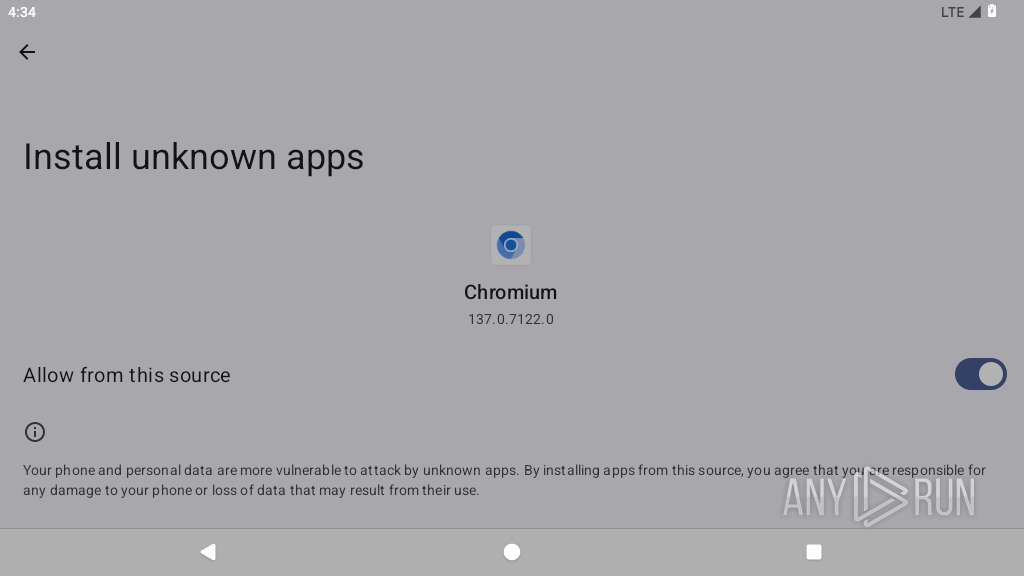
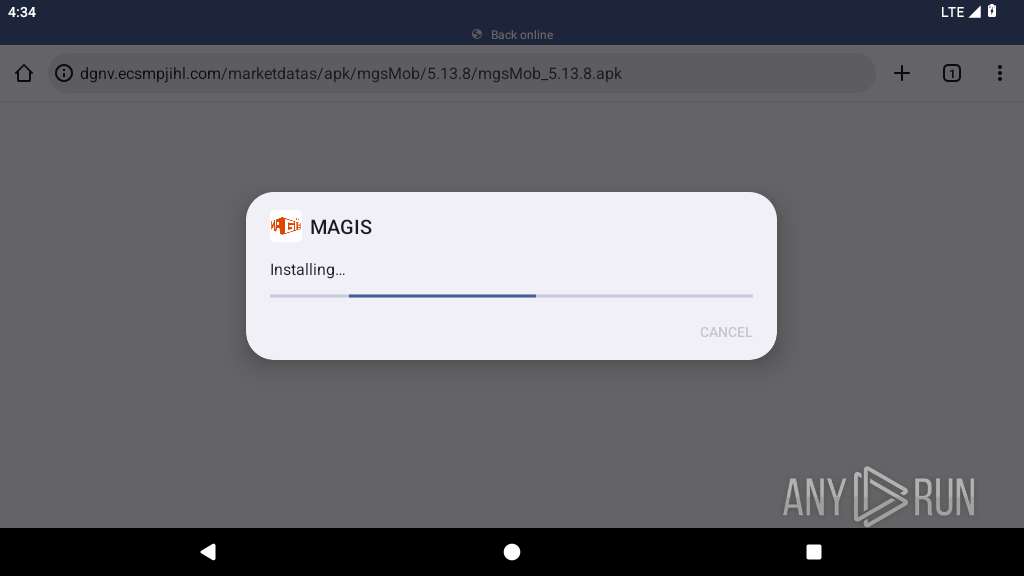
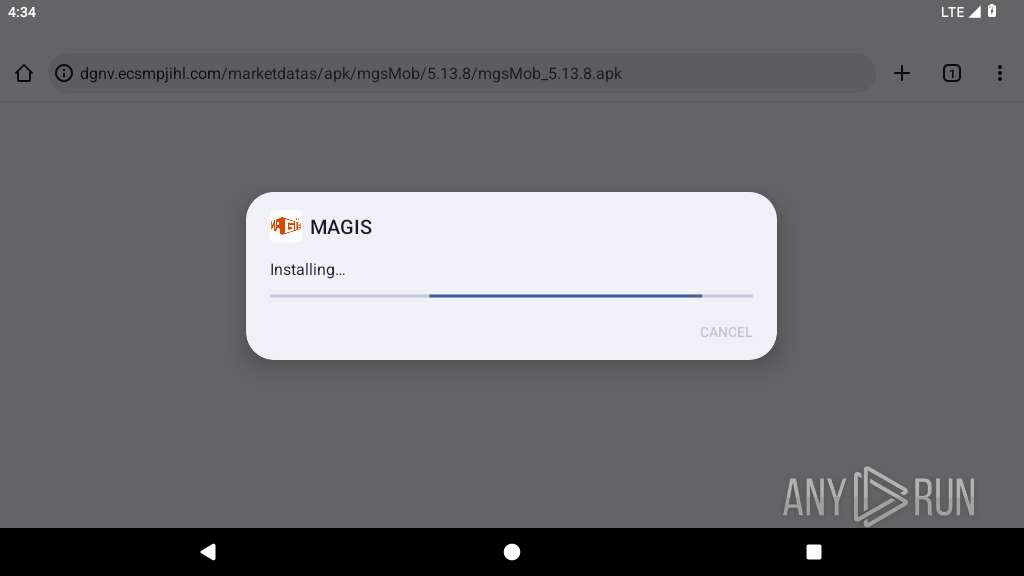
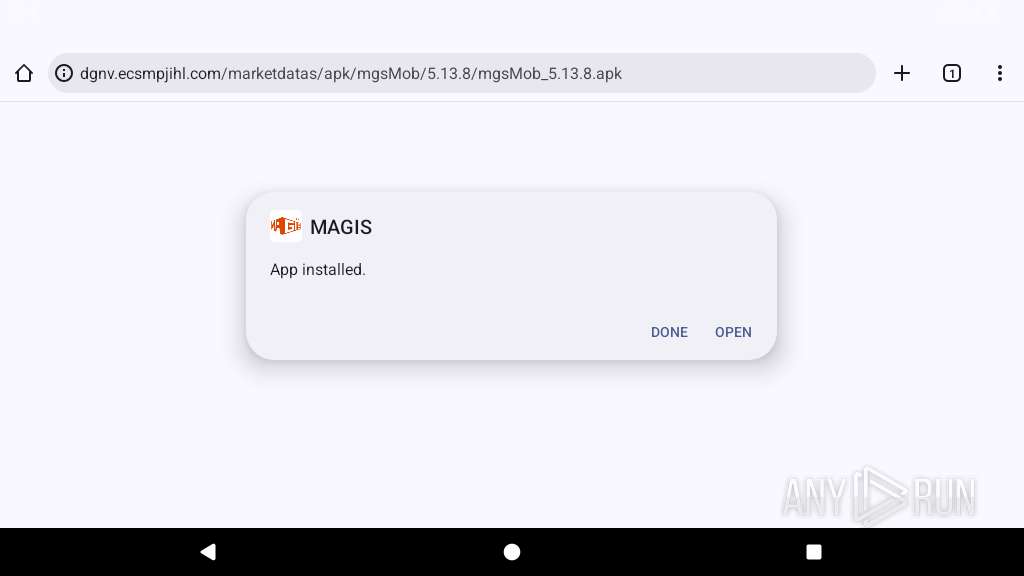
| URL: | http://dgnv.ecsmpjihl.com/marketdatas/apk/mgsMob/5.13.8/mgsMob_5.13.8.apk |
| Full analysis: | https://app.any.run/tasks/123a4fa3-54e3-42b4-9b22-47e1a5b8e9fc |
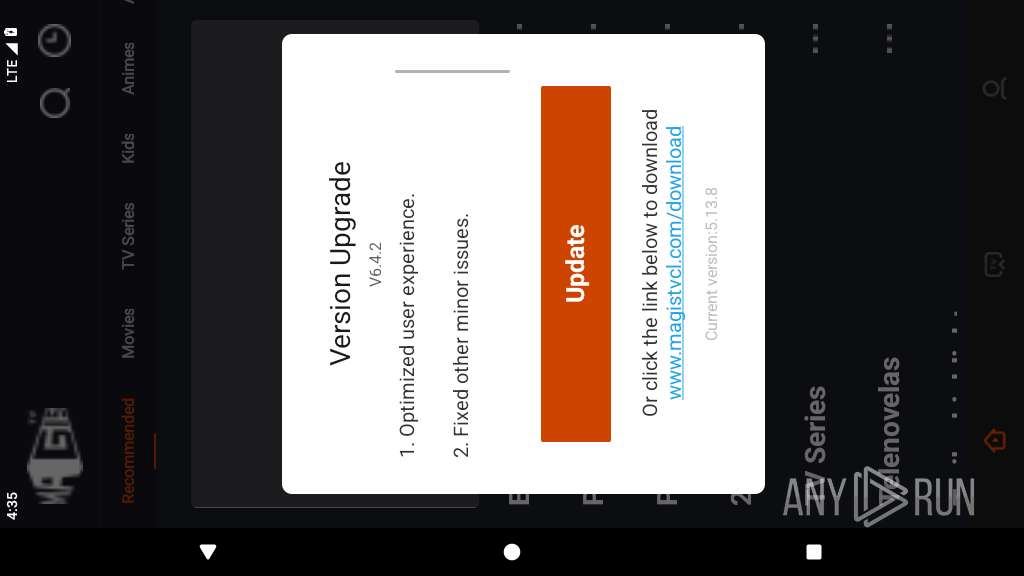
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2025, 16:34:04 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MD5: | 0AFDA6CE362CFA925C1BE383E345EF45 |
| SHA1: | 0A8019690ECB36ADA58A38BAFF7FB6542F0F861B |
| SHA256: | AB1D3CBC0AD65DFF2892B373C727839A6B35FD1C4AF3498C1D69D359D47BA1A9 |
| SSDEEP: | 3:N1KaCneFJLKTxsVC7QLUcK/WoKXpLfn:CauCLuxMELDWoGlfn |
MALICIOUS
Executes system commands or scripts
- app_process64 (PID: 4303)
SUSPICIOUS
Collects data about the device's environment (JVM version)
- app_process64 (PID: 4303)
Retrieves a list of running application processes
- app_process64 (PID: 4303)
Detects Xposed framework for modifications
- app_process64 (PID: 4303)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 4303)
Retrieves Android OS build information
- app_process64 (PID: 4303)
Accesses system-level resources
- app_process64 (PID: 4303)
Uses encryption API functions
- app_process64 (PID: 4303)
Accesses memory information
- app_process64 (PID: 4303)
Establishing a connection
- app_process64 (PID: 4303)
Detects when screen powers off
- app_process64 (PID: 4303)
Launches a new activity
- app_process64 (PID: 4303)
Returns the name of the current network operator
- app_process64 (PID: 4303)
Starts a service
- app_process64 (PID: 4303)
Accesses external device storage files
- app_process64 (PID: 4303)
INFO
Loads a native library into the application
- app_process64 (PID: 4303)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 4303)
Stores data using SQLite database
- app_process64 (PID: 4303)
Dynamically registers broadcast event listeners
- app_process64 (PID: 4303)
Verifies whether the device is connected to the internet
- app_process64 (PID: 4303)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 4303)
Returns elapsed time since boot
- app_process64 (PID: 4303)
Dynamically loads a class in Java
- app_process64 (PID: 4303)
Gets file name without full path
- app_process64 (PID: 4303)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 4303)
Listens for connection changes
- app_process64 (PID: 4303)
Retrieves the value of a secure system setting
- app_process64 (PID: 4303)
Detects device power status
- app_process64 (PID: 4303)
Retrieves the value of a system setting
- app_process64 (PID: 4303)
Attempting to connect via WebSocket
- app_process64 (PID: 4303)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
28
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3970 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4019 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4042 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4064 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4082 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4134 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4288 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4291 | /apex/com.android.art/bin/dex2oat32 --zip-fd=6 --zip-location=/data/app/~~IOlrRMQomAj9dU7QQ5NtdA==/com.msandroid.mobile-8pWrZVcMxYA9hm0_dzEvMg==/base.apk --oat-fd=7 --oat-location=/data/app/~~IOlrRMQomAj9dU7QQ5NtdA==/com.msandroid.mobile-8pWrZVcMxYA9hm0_dzEvMg==/oat/arm64/base.odex --output-vdex-fd=8 --swap-fd=9 --class-loader-context=PCL[] --classpath-dir=/data/app/~~IOlrRMQomAj9dU7QQ5NtdA==/com.msandroid.mobile-8pWrZVcMxYA9hm0_dzEvMg== --instruction-set=arm64 --instruction-set-features=default --instruction-set-variant=cortex-a53 --compiler-filter=verify --compilation-reason=install --compact-dex-level=none --max-image-block-size=524288 --resolve-startup-const-strings=true --generate-mini-debug-info --runtime-arg -Xtarget-sdk-version:33 --runtime-arg -Xhidden-api-policy:enabled --runtime-arg -Xms64m --runtime-arg -Xmx512m --comments=app-version-name:5.13.8,app-version-code:51308,art-version:340090000 | /apex/com.android.art/bin/dex2oat32 | — | artd |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4303 | com.msandroid.mobile | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4388 | getprop ro.build.version.emui | /system/bin/toolbox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
166
Text files
151
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4303 | app_process64 | /data/data/com.msandroid.mobile/files/PersistedInstallation8420681893549592910tmp | binary | |
MD5:— | SHA256:— | |||
| 4303 | app_process64 | /data/data/com.msandroid.mobile/files/PersistedInstallation.W0RFRkFVTFRd+MToxODc2NzUyNDY3NTphbmRyb2lkOmM3NGYwM2Y4YTg2ODE1YzUzNWY1ZjY.json | binary | |
MD5:— | SHA256:— | |||
| 4303 | app_process64 | /data/data/com.msandroid.mobile/files/.com.google.firebase.crashlytics.files.v2:com.msandroid.mobile/open-sessions/68DFFB180105000110CF60951B79DA32/native/session.json | binary | |
MD5:— | SHA256:— | |||
| 4303 | app_process64 | /data/data/com.msandroid.mobile/shared_prefs/com.google.android.gms.measurement.prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 4303 | app_process64 | /data/data/com.msandroid.mobile/shared_prefs/com.google.firebase.crashlytics.xml | xml | |
MD5:— | SHA256:— | |||
| 4303 | app_process64 | /data/data/com.msandroid.mobile/shared_prefs/com.google.firebase.inappmessaging.xml | xml | |
MD5:— | SHA256:— | |||
| 4303 | app_process64 | /data/data/com.msandroid.mobile/files/.com.google.firebase.crashlytics.files.v2:com.msandroid.mobile/open-sessions/68DFFB180105000110CF60951B79DA32/native/app.json | binary | |
MD5:— | SHA256:— | |||
| 4303 | app_process64 | /data/data/com.msandroid.mobile/files/.com.google.firebase.crashlytics.files.v2:com.msandroid.mobile/open-sessions/68DFFB180105000110CF60951B79DA32/native/os.json | binary | |
MD5:— | SHA256:— | |||
| 4303 | app_process64 | /data/data/com.msandroid.mobile/files/.com.google.firebase.crashlytics.files.v2:com.msandroid.mobile/open-sessions/68DFFB180105000110CF60951B79DA32/native/device.json | binary | |
MD5:— | SHA256:— | |||
| 4303 | app_process64 | /data/data/com.msandroid.mobile/shared_prefs/FirebaseHeartBeatW0RFRkFVTFRd+MToxODc2NzUyNDY3NTphbmRyb2lkOmM3NGYwM2Y4YTg2ODE1YzUzNWY1ZjY.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
57
DNS requests
59
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.185.100:80 | http://www.google.com/gen_204 | US | — | — | whitelisted |
1939 | app_process64 | GET | 204 | 142.250.186.163:80 | http://connectivitycheck.gstatic.com/generate_204 | US | — | — | whitelisted |
3970 | app_process64 | GET | 200 | 142.250.185.142:80 | http://clients2.google.com/time/1/current?cup2key=9:IaE34rplTB8NHb_MlSmpOeFyPT7NnuY5nfImL70AE7U&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
4303 | app_process64 | GET | 200 | 188.114.97.3:80 | http://jktgr.ludgwoxhe.com/MarketServer/update?action=checkUpdate&packagenamesAndVersioncodes=com.msandroid.mobile%2C51308&language=en&sn=vDedjnhT2IA%3D&userId=unknown | NL | xml | 565 b | whitelisted |
4303 | app_process64 | POST | 200 | 104.21.12.105:80 | http://skc2r.plracsimf.com/api/adserver/v2/get_content | unknown | binary | 558 b | unknown |
4303 | app_process64 | GET | 200 | 188.114.96.3:80 | http://miqe.sdxpkgyaq.com/media/adsys/504f35f9-acd1-4d06-9548-12cd6bfcb076.jpg | NL | image | 872 Kb | whitelisted |
4303 | app_process64 | GET | 200 | 188.114.96.3:80 | http://miqe.sdxpkgyaq.com/media/adsys/55fc3fe0-7633-4878-b798-03da14a06a44.png | NL | image | 380 Kb | whitelisted |
4303 | app_process64 | GET | 200 | 188.114.96.3:80 | http://miqe.sdxpkgyaq.com/media/adsys/89082139-f360-4031-92b1-55f678b8f3a9.jpg | NL | image | 538 Kb | whitelisted |
4303 | app_process64 | GET | 101 | 104.18.53.63:80 | http://bjac.mdj1kgdcv.com:80/v1/imagine | unknown | — | — | unknown |
4303 | app_process64 | GET | 200 | 188.114.97.3:80 | http://g4tc2.irlapchbd.com/notice/api/get_notice?pkg=com.msandroid.mobile&v=51308&language=en&sn=809992392&userId=809992392 | NL | binary | 117 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
450 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.250.185.100:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.35:80 | — | GOOGLE | US | whitelisted |
— | — | 142.250.185.100:443 | www.google.com | GOOGLE | US | whitelisted |
3970 | app_process64 | 142.250.185.142:80 | clients2.google.com | GOOGLE | US | whitelisted |
3970 | app_process64 | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3970 | app_process64 | 172.67.165.181:443 | dgnv.ecsmpjihl.com | CLOUDFLARENET | US | unknown |
3970 | app_process64 | 142.250.185.100:443 | www.google.com | GOOGLE | US | whitelisted |
3970 | app_process64 | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE | US | whitelisted |
3970 | app_process64 | 142.250.184.234:443 | androidchromeprotect.pa.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
dgnv.ecsmpjihl.com |
| unknown |
accounts.google.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
androidchromeprotect.pa.googleapis.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| unknown |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3970 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3970 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1939 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
4303 | app_process64 | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google in TLS SNI) |
4303 | app_process64 | Misc activity | ET INFO Google DNS Over HTTPS Certificate Inbound |
4303 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
4303 | app_process64 | Generic Protocol Command Decode | SURICATA HTTP request field missing colon |
4303 | app_process64 | Generic Protocol Command Decode | SURICATA HTTP request header invalid |
4303 | app_process64 | Generic Protocol Command Decode | SURICATA HTTP METHOD terminated by non-compliant character |