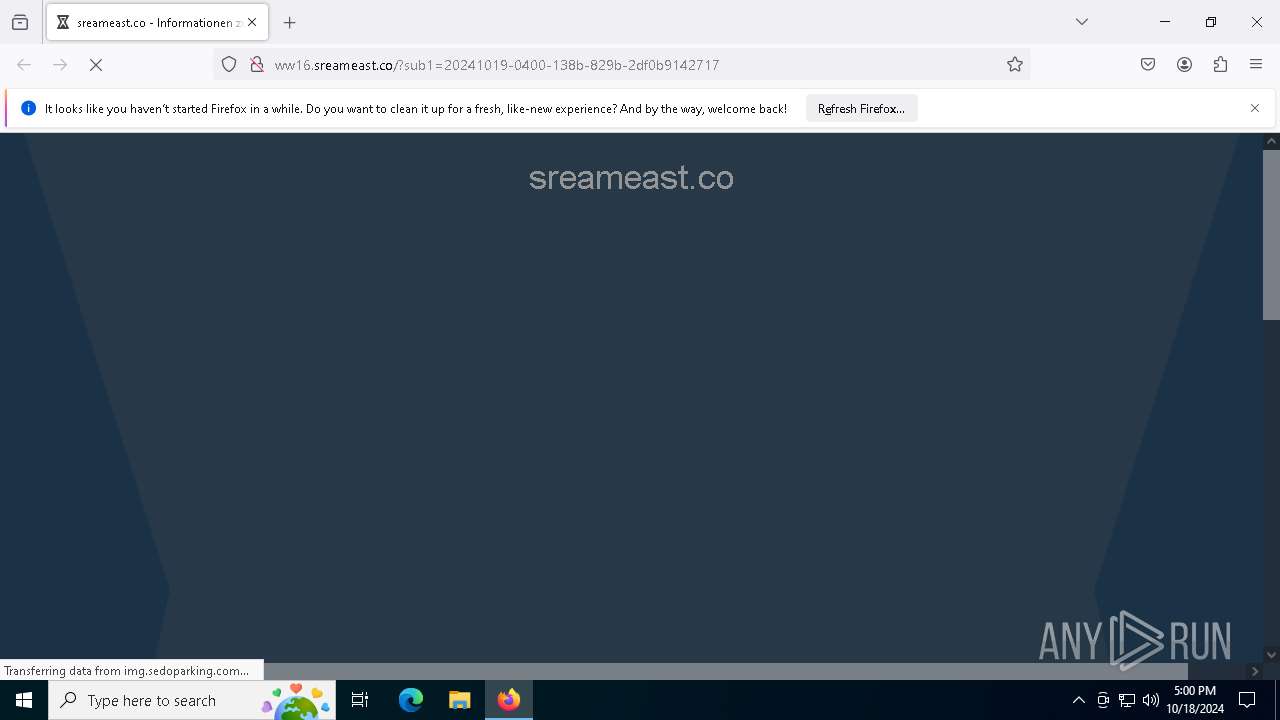
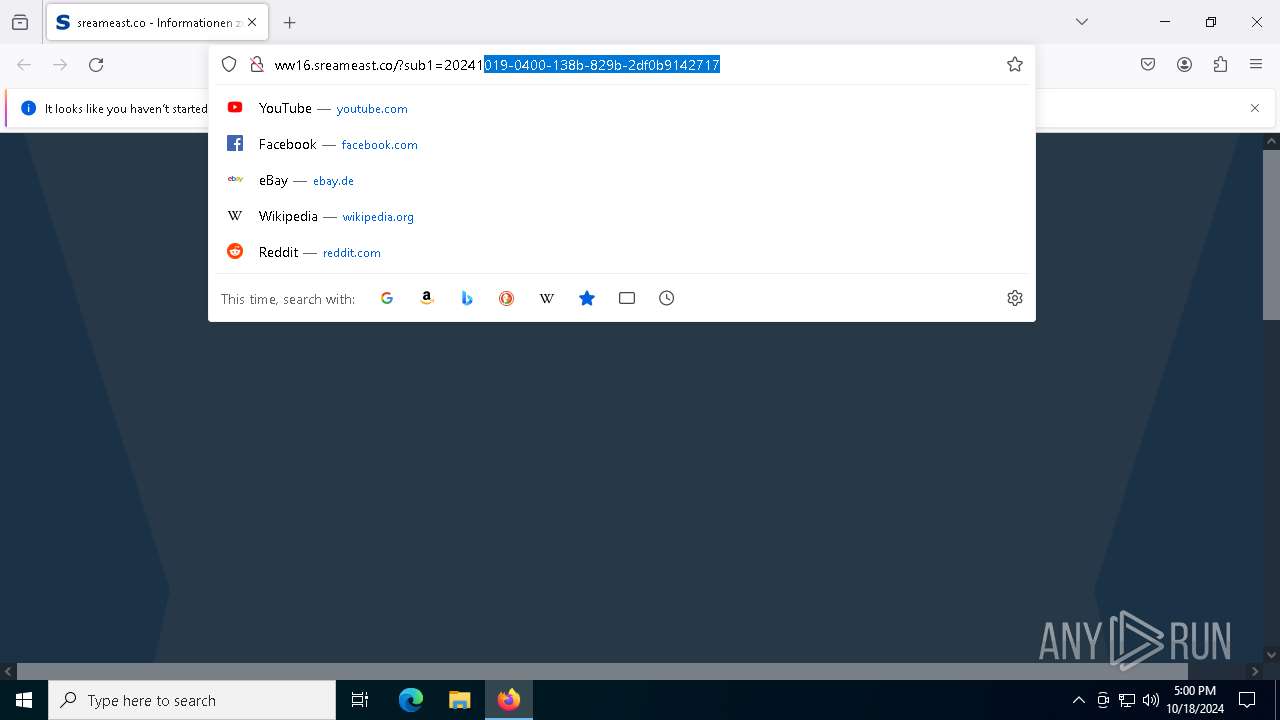
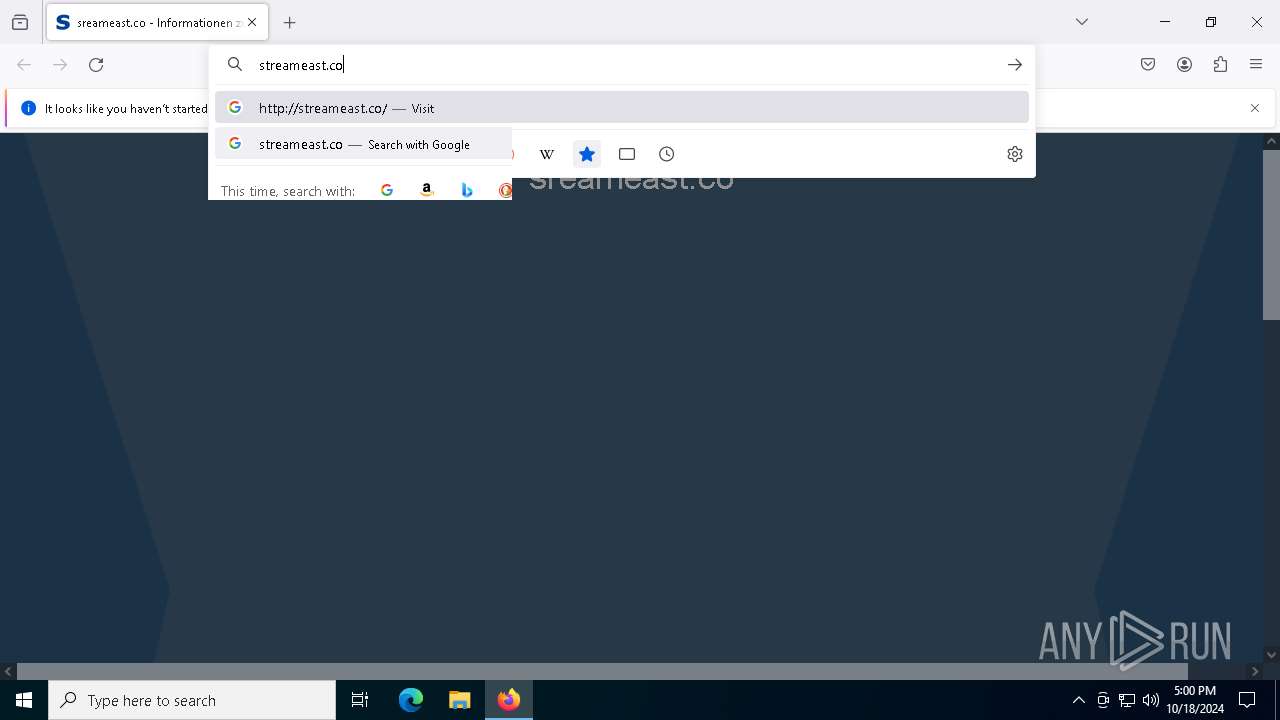
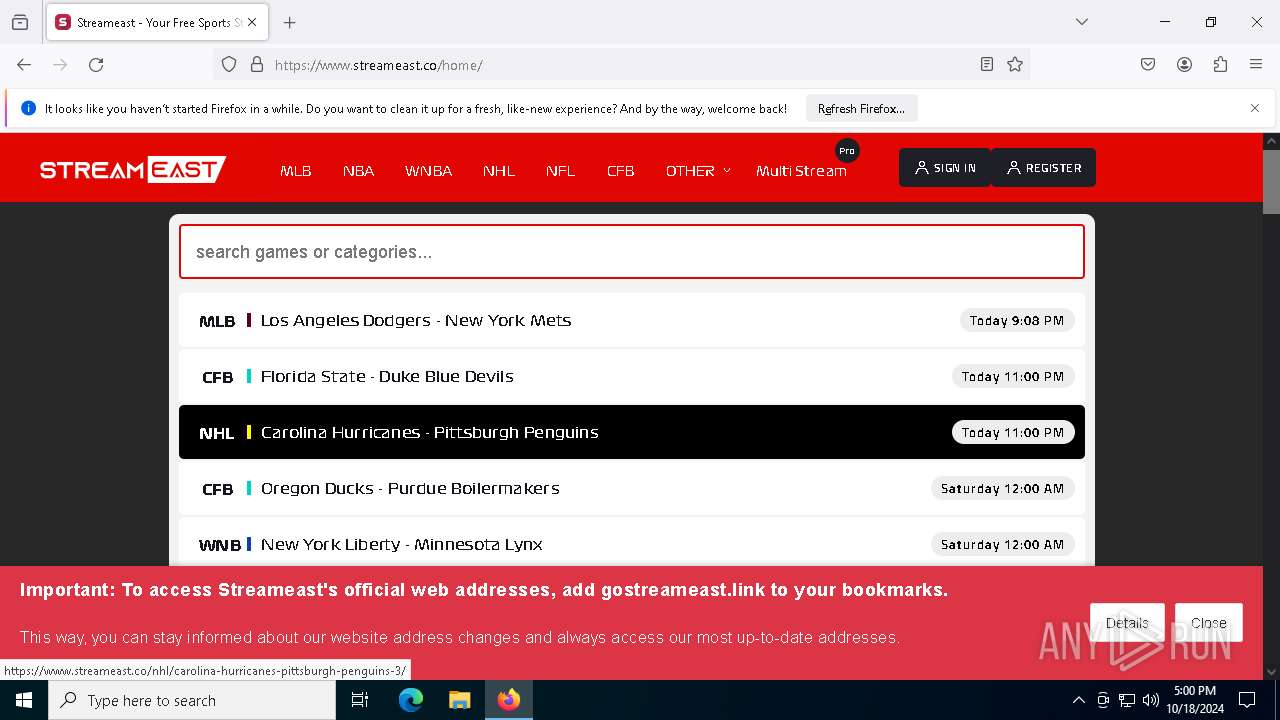
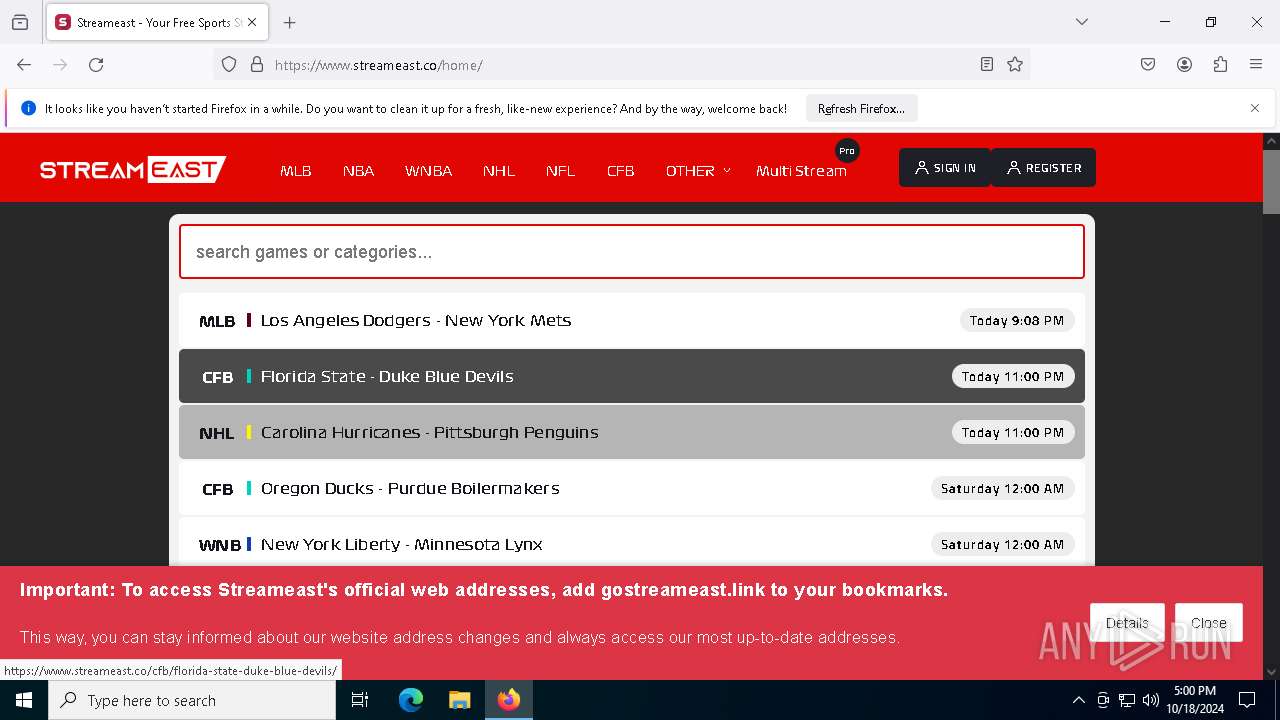
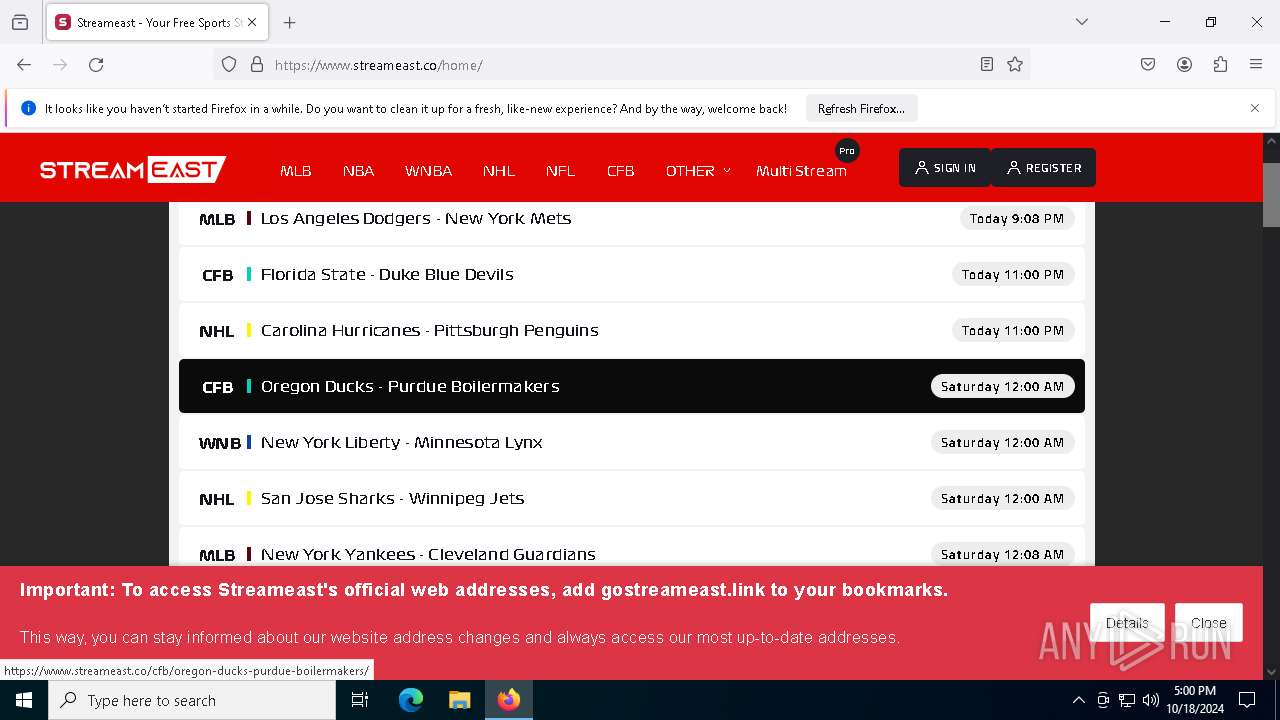
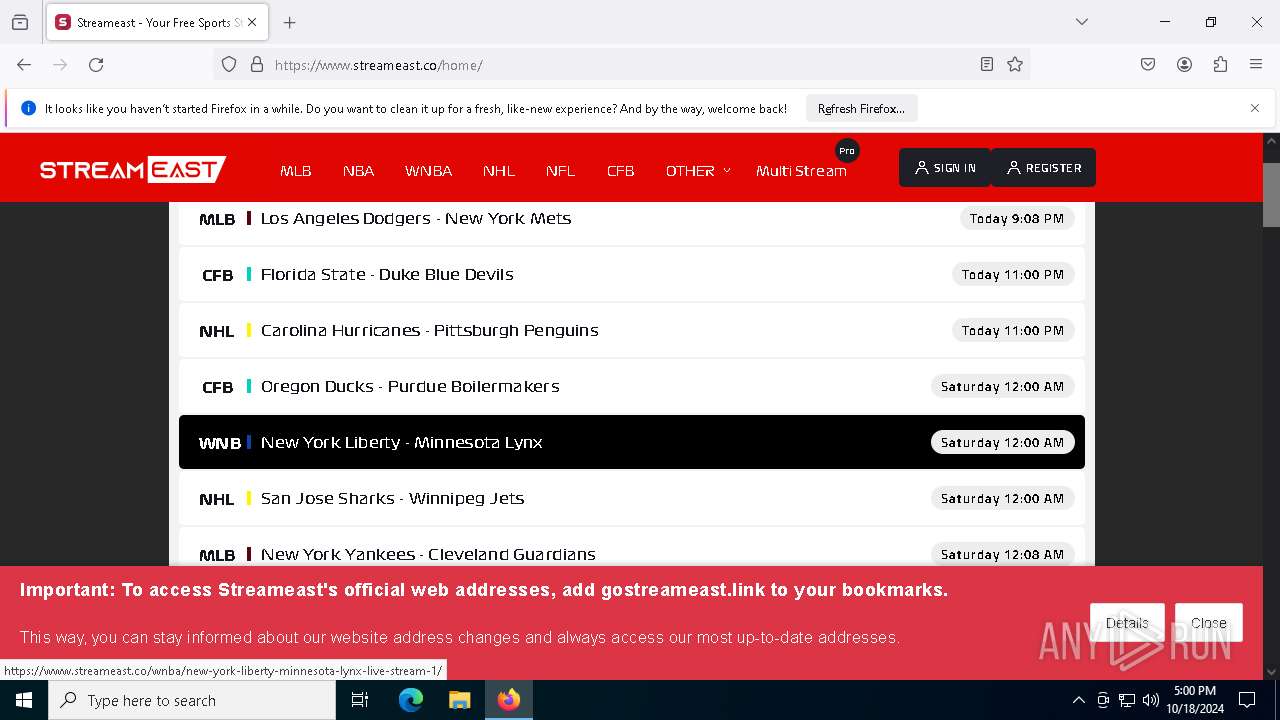
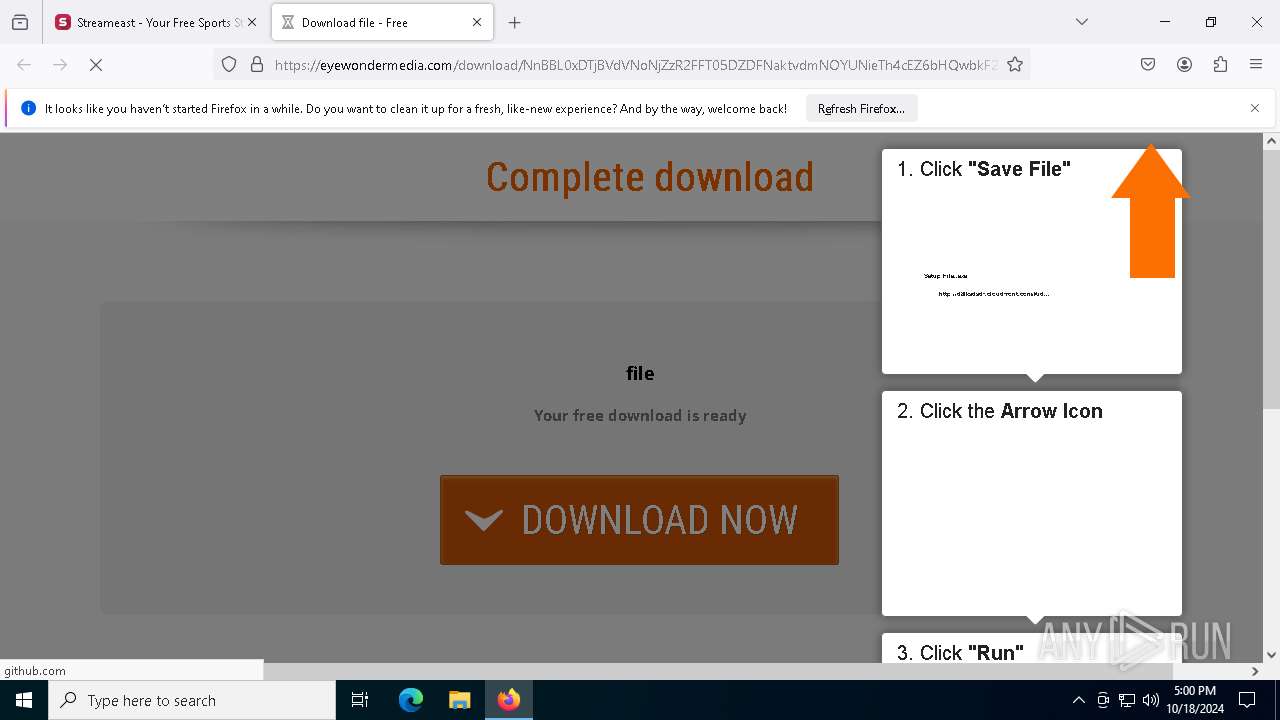
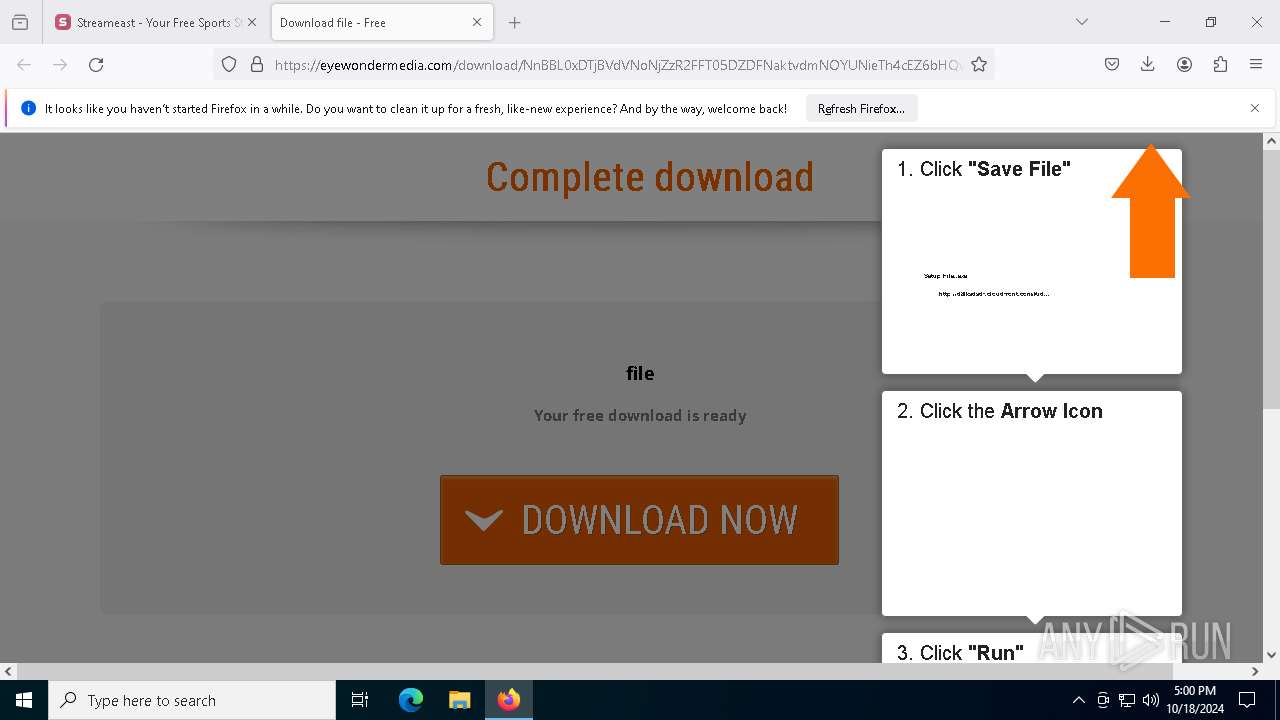
| URL: | sreameast.co |
| Full analysis: | https://app.any.run/tasks/7bfa880f-7941-4b26-884c-3b0f28cc1daa |
| Verdict: | Malicious activity |
| Analysis date: | October 18, 2024, 17:00:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A85A3F734D6359F63D35AA5552E996D2 |
| SHA1: | 10E4BCF4030133B031788995C471E5DE8139A3DE |
| SHA256: | AB1D387AD9AF0AF623E9719C5C7BB469D798169A715BF36E1A9B338A9F0122B1 |
| SSDEEP: | 3:VEIyGKn:VESKn |
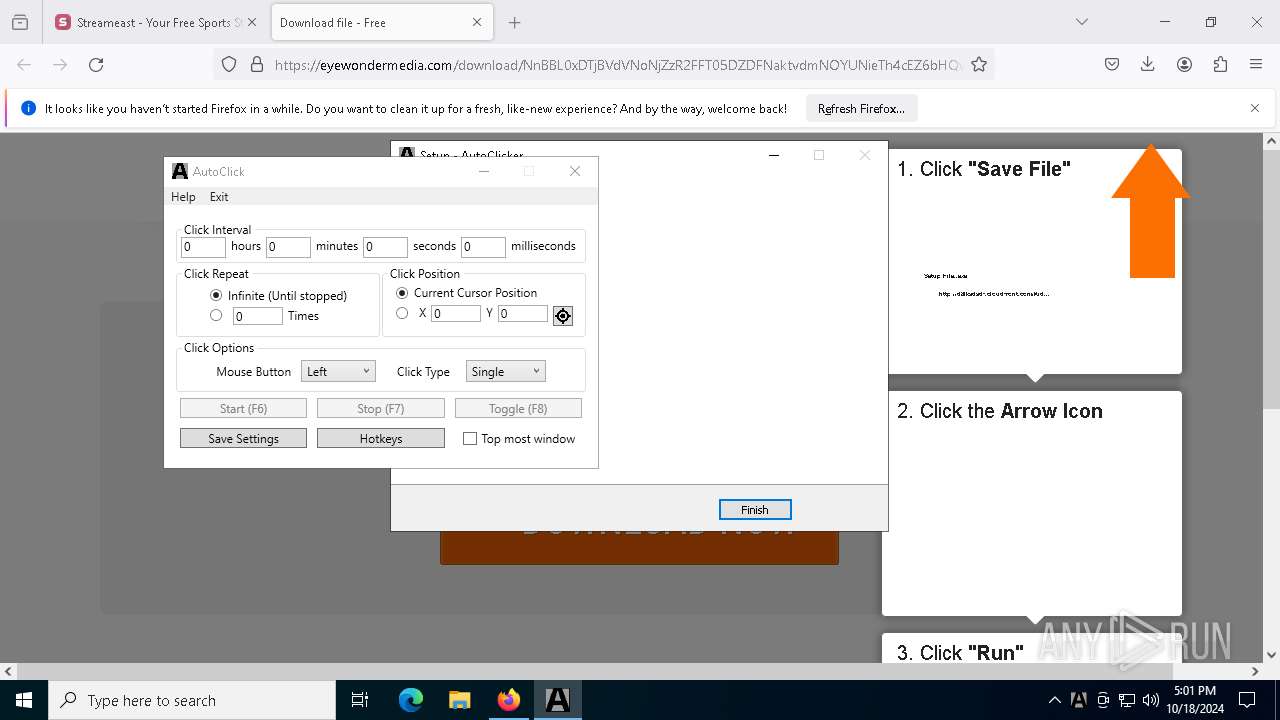
MALICIOUS
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2172)
SUSPICIOUS
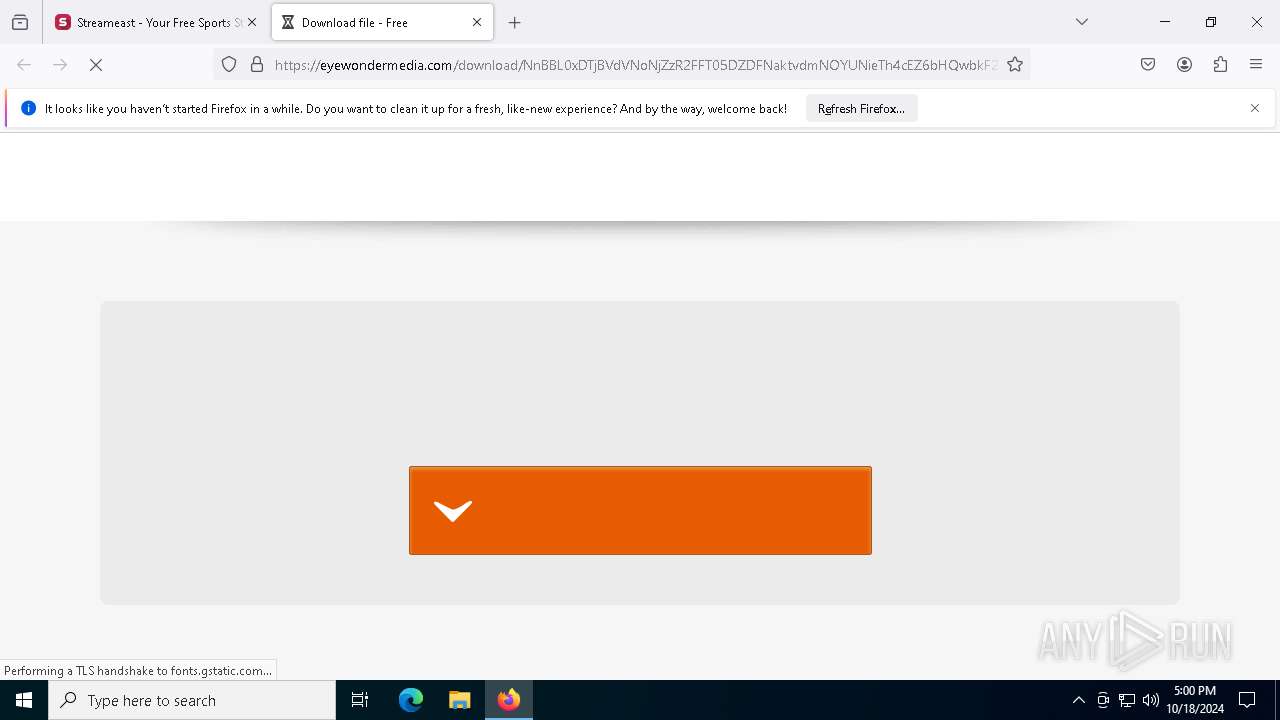
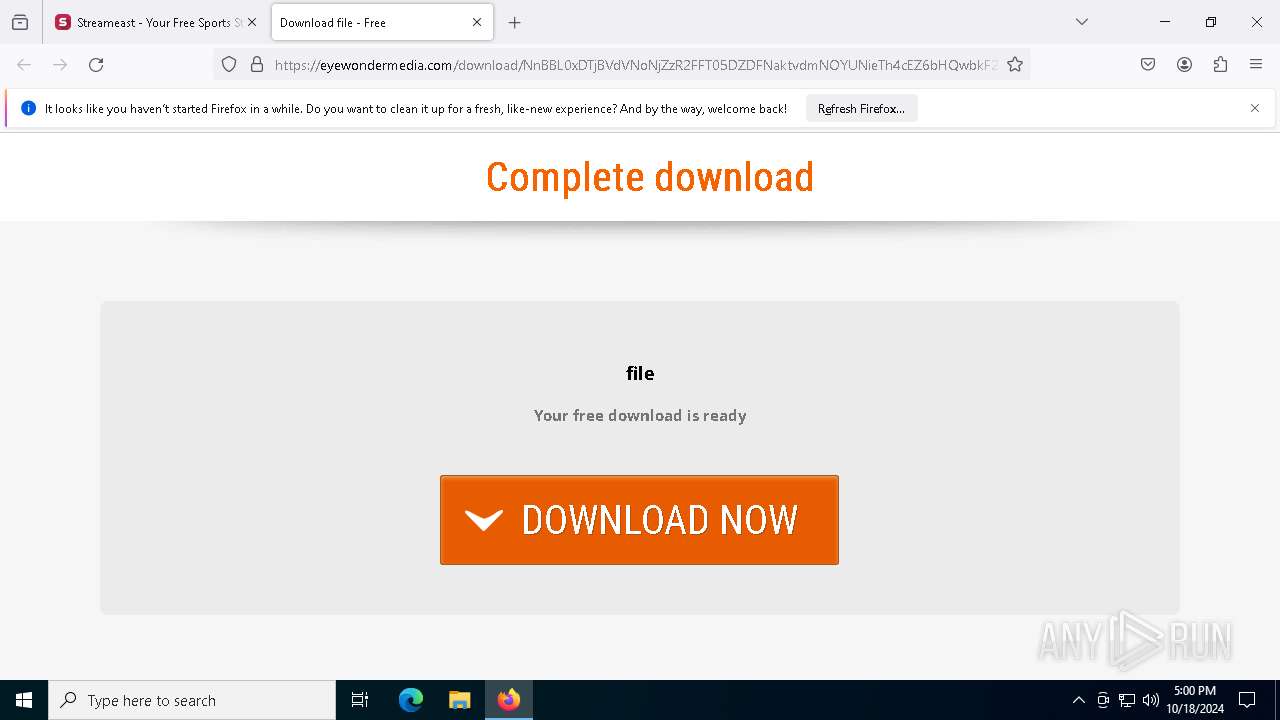
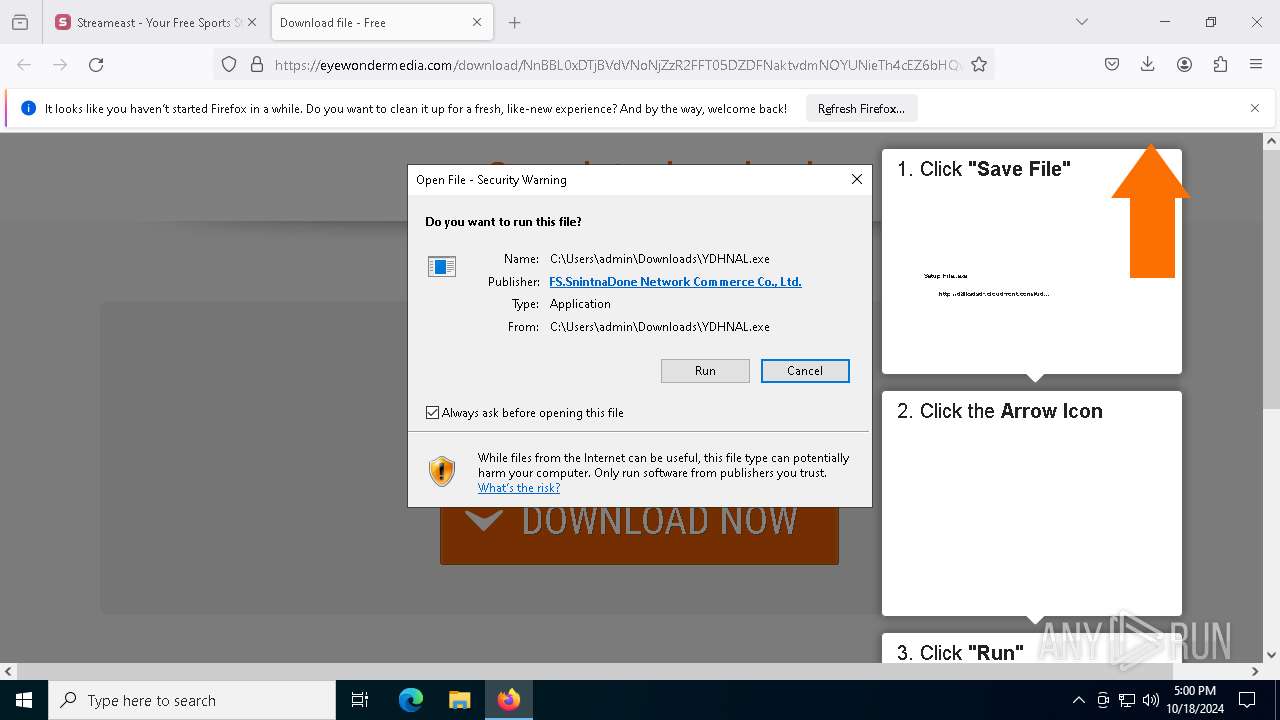
Executing commands from a ".bat" file
- YDHNAL.tmp (PID: 7248)
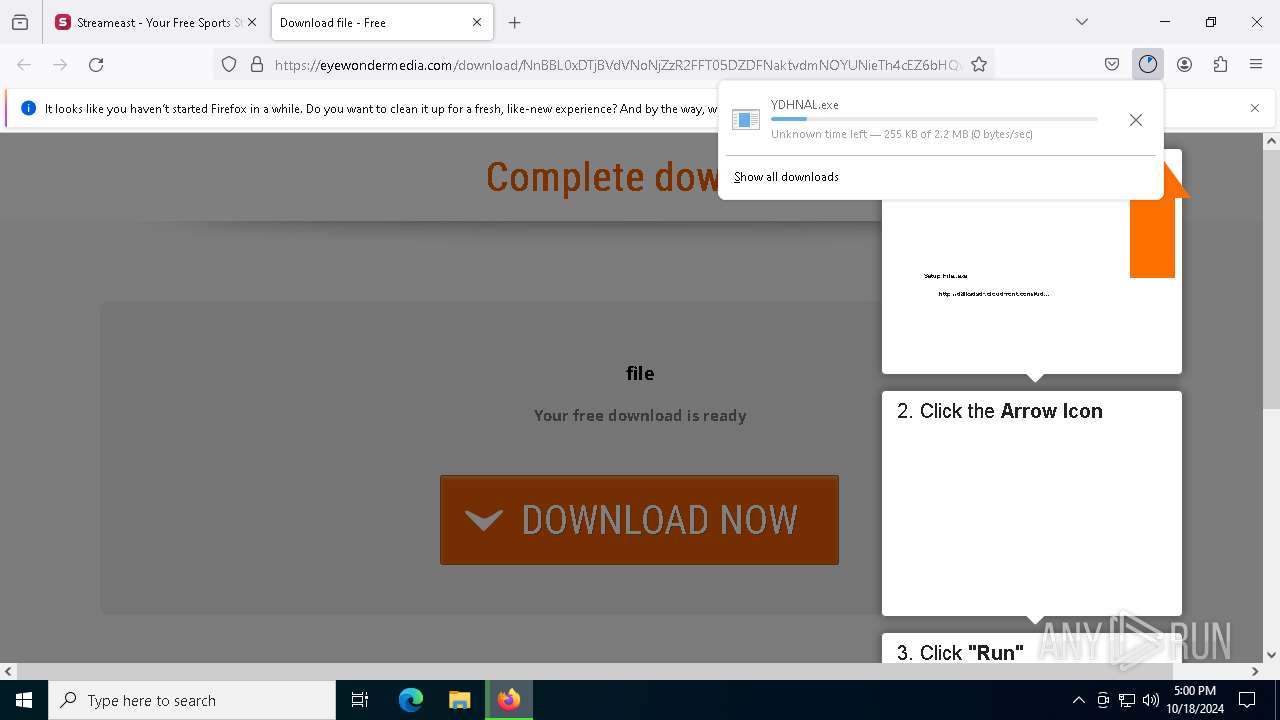
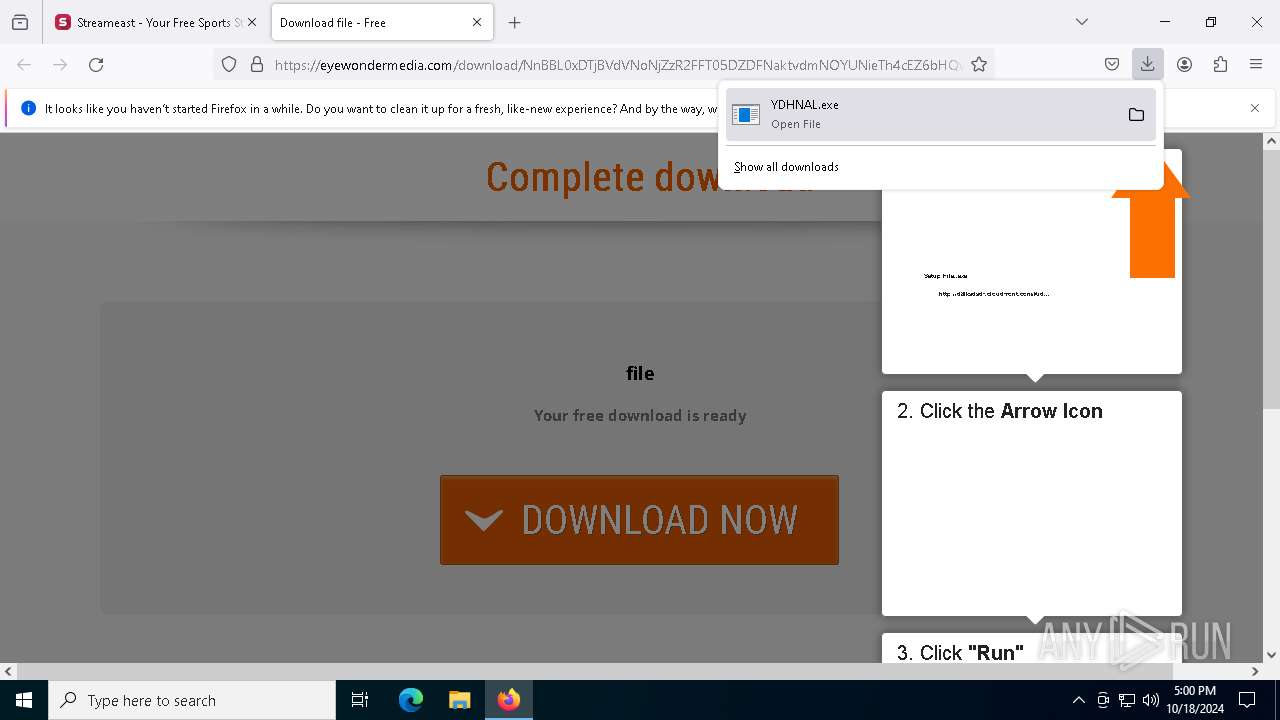
Executable content was dropped or overwritten
- YDHNAL.exe (PID: 7636)
- YDHNAL.exe (PID: 5564)
- YDHNAL.tmp (PID: 7248)
Process drops legitimate windows executable
- YDHNAL.tmp (PID: 7248)
Starts CMD.EXE for commands execution
- YDHNAL.tmp (PID: 7248)
INFO
Application launched itself
- firefox.exe (PID: 6560)
- firefox.exe (PID: 6684)
Executable content was dropped or overwritten
- firefox.exe (PID: 6684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
160
Monitored processes
29
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1068 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6600 -childID 8 -isForBrowser -prefsHandle 6624 -prefMapHandle 6620 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1136 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {579ab318-18c0-40e3-8a0f-8a45675f0e47} 6684 "\\.\pipe\gecko-crash-server-pipe.6684" 1ff473f3a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1792 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
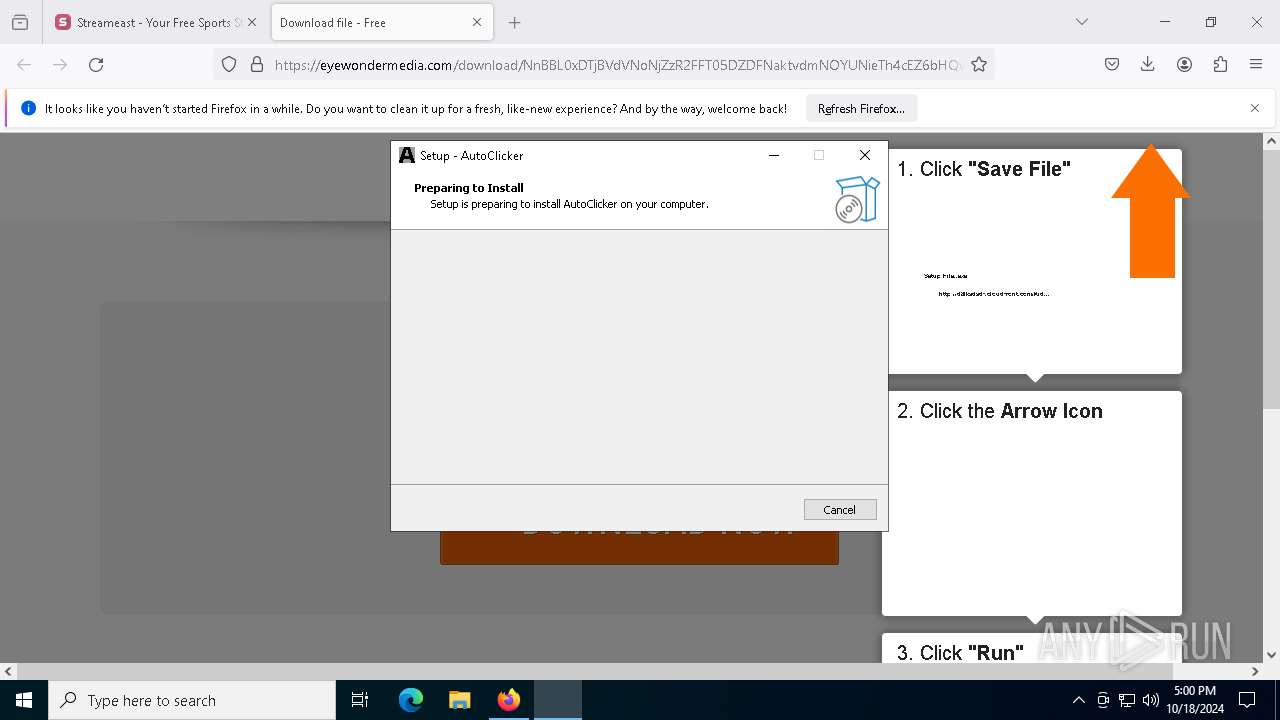
| 2652 | "C:\Program Files\AutoClicker\AutoClicker.exe" | C:\Program Files\AutoClicker\AutoClicker.exe | — | YDHNAL.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: AutoClick Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3604 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2184 -parentBuildID 20240213221259 -prefsHandle 2176 -prefMapHandle 2164 -prefsLen 30705 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c5457e09-b631-4e01-8402-dc9c2cfec17f} 6684 "\\.\pipe\gecko-crash-server-pipe.6684" 1ff31483f10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5160 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1800 -parentBuildID 20240213221259 -prefsHandle 1728 -prefMapHandle 1720 -prefsLen 30705 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {486afbae-88d7-4b21-8c93-7a5333534d1f} 6684 "\\.\pipe\gecko-crash-server-pipe.6684" 1ff3d1c4510 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5232 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6204 -childID 9 -isForBrowser -prefsHandle 6392 -prefMapHandle 6072 -prefsLen 31242 -prefMapSize 244343 -jsInitHandle 1136 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f04675cf-57cf-4937-811d-505df8b86ec1} 6684 "\\.\pipe\gecko-crash-server-pipe.6684" 1ff473f3f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5332 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files\AutoClicker\AutoClickerUpdate.bat" " | C:\Windows\SysWOW64\cmd.exe | — | YDHNAL.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5564 | "C:\Users\admin\Downloads\YDHNAL.exe" /SPAWNWND=$802F2 /NOTIFYWND=$C0222 | C:\Users\admin\Downloads\YDHNAL.exe | YDHNAL.tmp | ||||||||||||
User: admin Company: AutoClicker v6.8 Integrity Level: HIGH Description: AutoClicker Setup Version: 6.8.1 Modules
| |||||||||||||||
Total events
23 219
Read events
23 217
Write events
2
Delete events
0
Modification events
| (PID) Process: | (6684) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6684) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
Executable files
40
Suspicious files
163
Text files
69
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:8BD997F90ECBED0083C0F3B144B2F721 | SHA256:25EC68792A8D0944AEC3A5C97A589369B3CEF2F6F5F2721E09A1570C270E8255 | |||
| 6684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:1D537D871F04EE31D48BB7ED3240B90A | SHA256:D0C1C9278F056494A97736D38013F26016ED73C0EDE33FEF44123B3634F16BE6 | |||
| 6684 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:C09FF302D57C404B61E6A89B0B9F36E7 | SHA256:6A5B4F82595799346D0E501FE6CC8629E0FD6ED27B74D0E6CB5073DDB2E3C40B | |||
| 6684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | dbf | |
MD5:D30F5B10F3D4B3992E4D666F622163F4 | SHA256:2585819A7401A308DA879FA416278E473CEA5F6D0D24C59F514C5A698C61D03A | |||
| 6684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:EB6E766AB44C5216C6C15F601A6249EE | SHA256:9B516782270553A2AE298A8BF26A7256F4259A88C0755B9844036396BA5E1129 | |||
| 6684 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:8BD997F90ECBED0083C0F3B144B2F721 | SHA256:25EC68792A8D0944AEC3A5C97A589369B3CEF2F6F5F2721E09A1570C270E8255 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
182
DNS requests
209
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6684 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
6684 | firefox.exe | GET | 200 | 64.190.63.136:80 | http://ww16.sreameast.co/search/tsc.php?ses=ogc2bI6imj0-J04PHKAbMW8lsl9LGUJP760yURILW7c6SVRdqsBVfiBNicjksc4JNKntigaLTlbNxN_3zAegSwDYB9KAjMXJxNGgm9mcDVApK3yt7HFFlrEReN7RWXf0GtLFjYjPRCPskDYzWs2yeVgkrt84aD9E2j9_hE0b0ZSfPrxR1HQbUa1jWERnDDGSQBgXyn_XevX7ivz_Aw4fGIlecbKhtCLdChEvZ3ECQibhJVjsrFclUxQlT_TSrHXzHFC2KiqyZL1z4QjvNonSfWeoBdH8nPpxtIf9Bs2xyu0VhcTui95mxfgLz5q7gD93SHPL1JUADIXHTJdhjNpm97u0ffEAPQexPfS-ZOkWs3kt8was8FL28lYD-rbHw&cv=2 | DE | — | — | whitelisted |
6684 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | DE | binary | 504 b | whitelisted |
6684 | firefox.exe | GET | 200 | 172.217.16.132:80 | http://www.google.com/adsense/domains/caf.js?abp=1&YEr3CiF6AuQqLspNobyal3ji0SyqxBLn=true | US | text | 54.1 Kb | whitelisted |
6684 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
6684 | firefox.exe | GET | 302 | 103.224.182.244:80 | http://sreameast.co/ | AU | text | 2 b | unknown |
6684 | firefox.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/templates/logos/sedo_logo.png | US | image | 14.7 Kb | whitelisted |
6684 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2 | US | binary | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 92.123.104.47:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
864 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
6684 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6684 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
sreameast.co |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
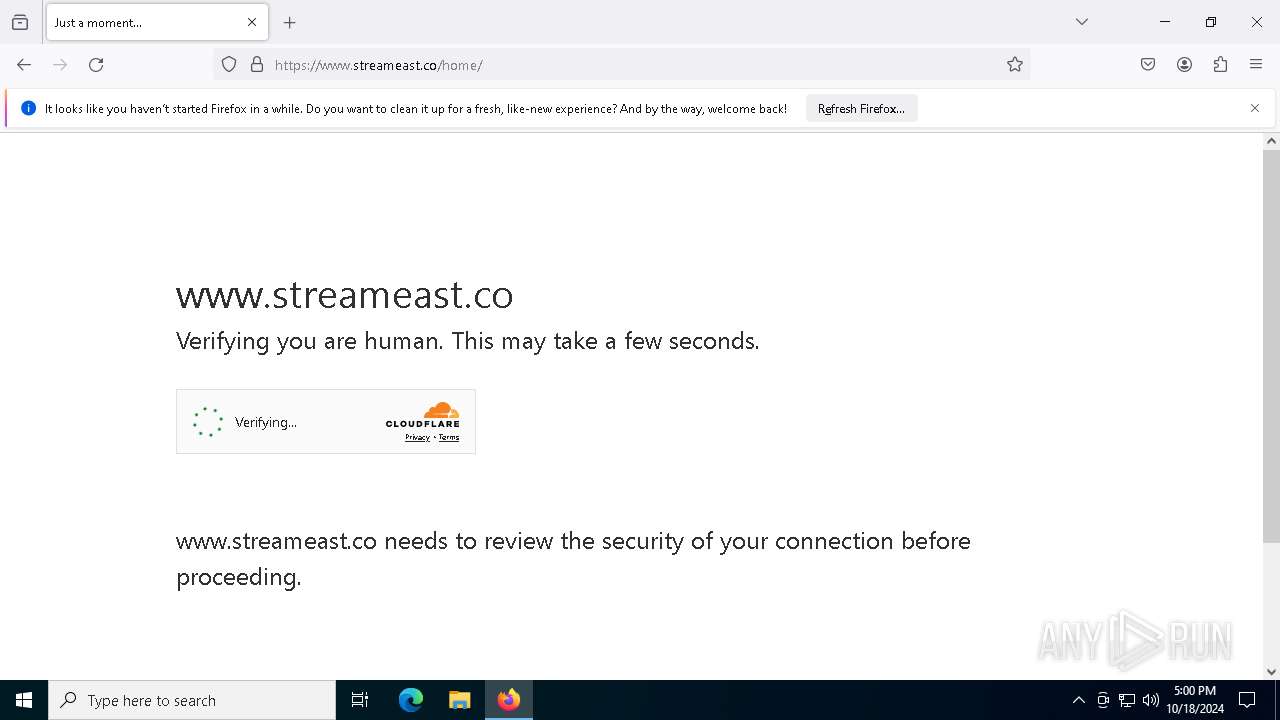
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
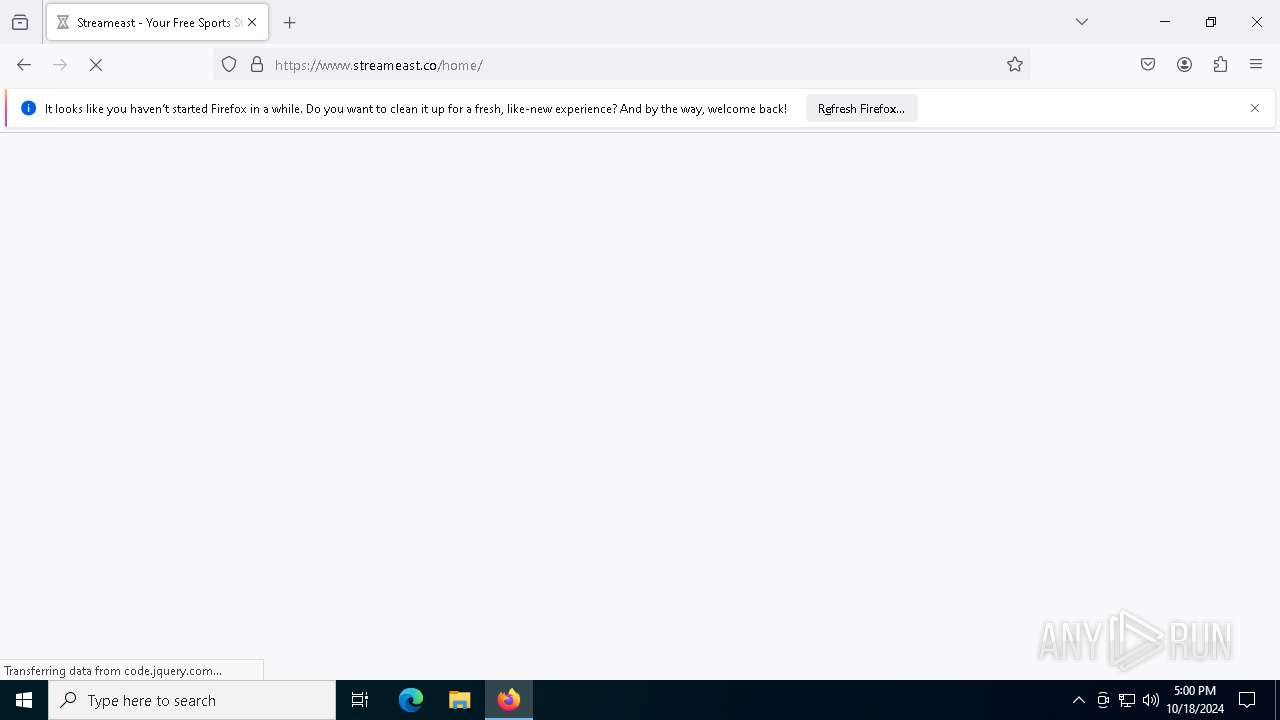
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2172 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (cdnchallengezone) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |