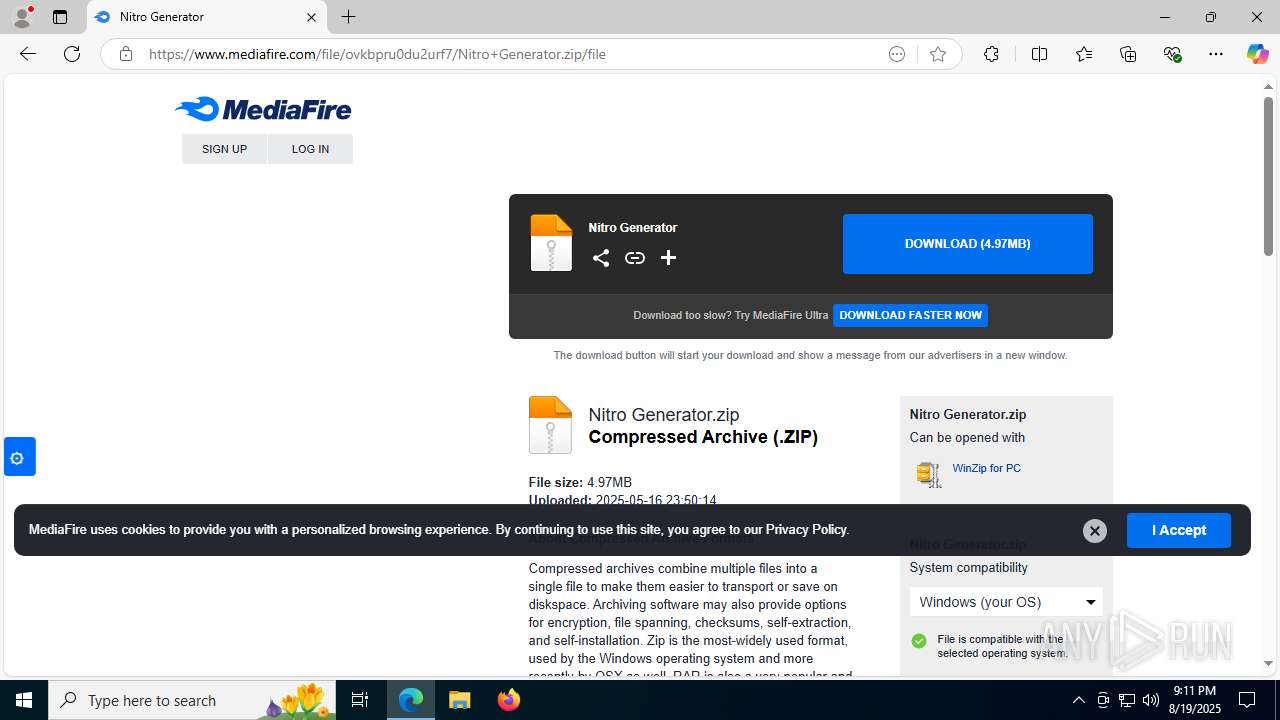
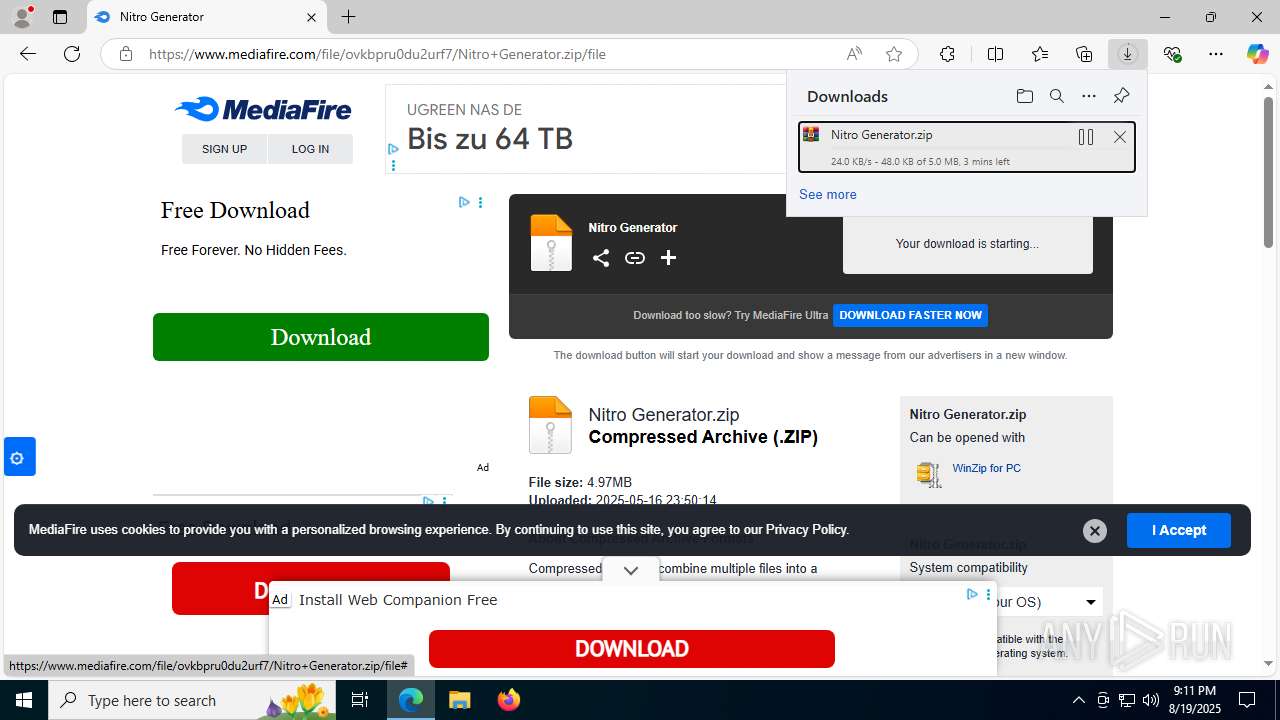
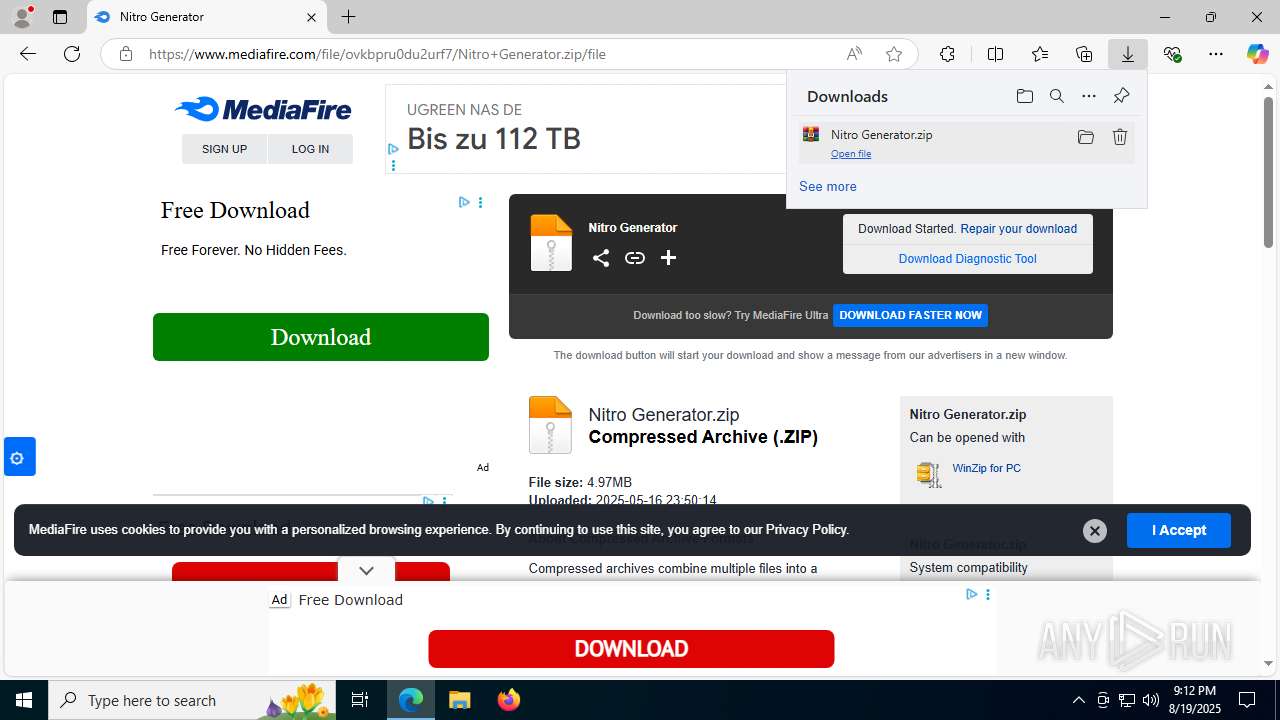
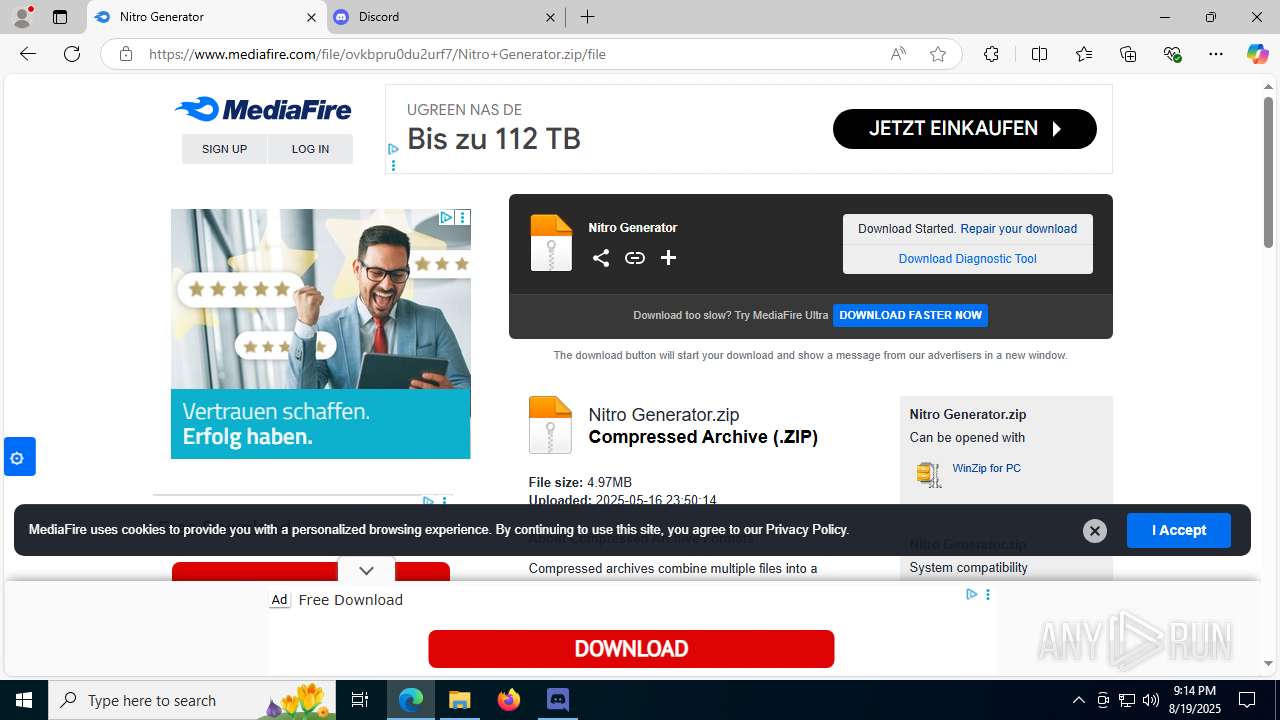
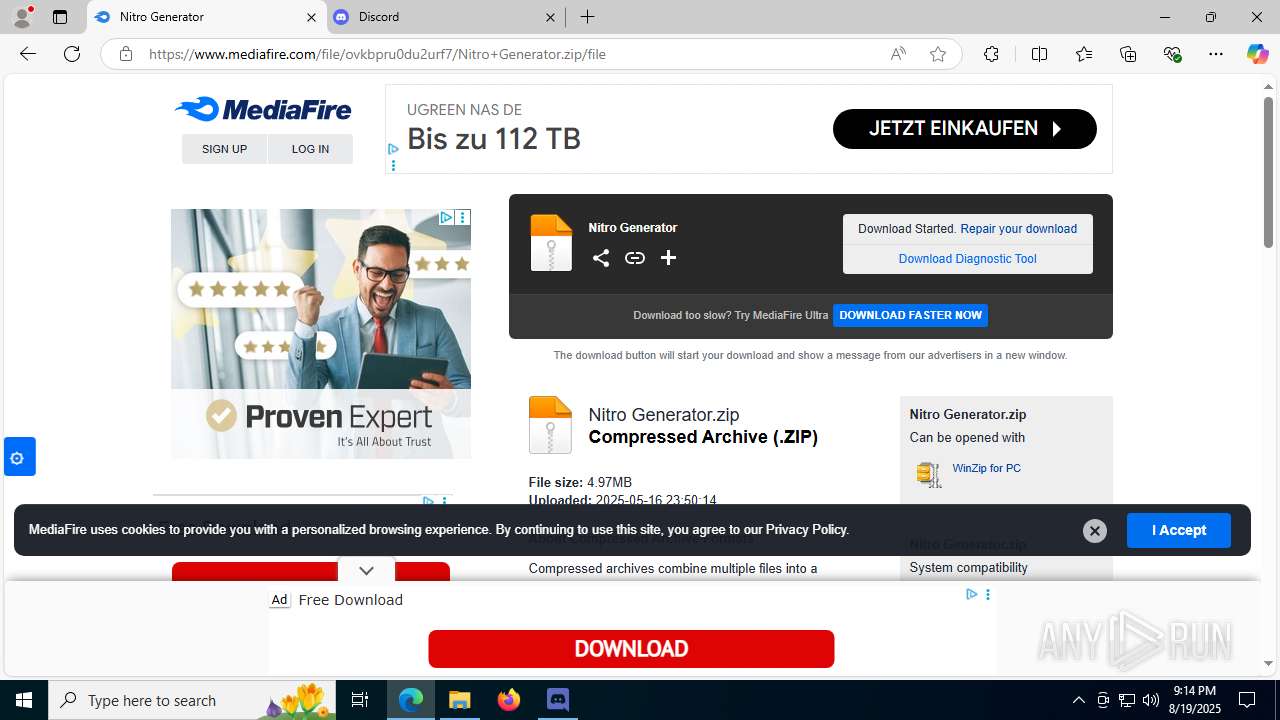
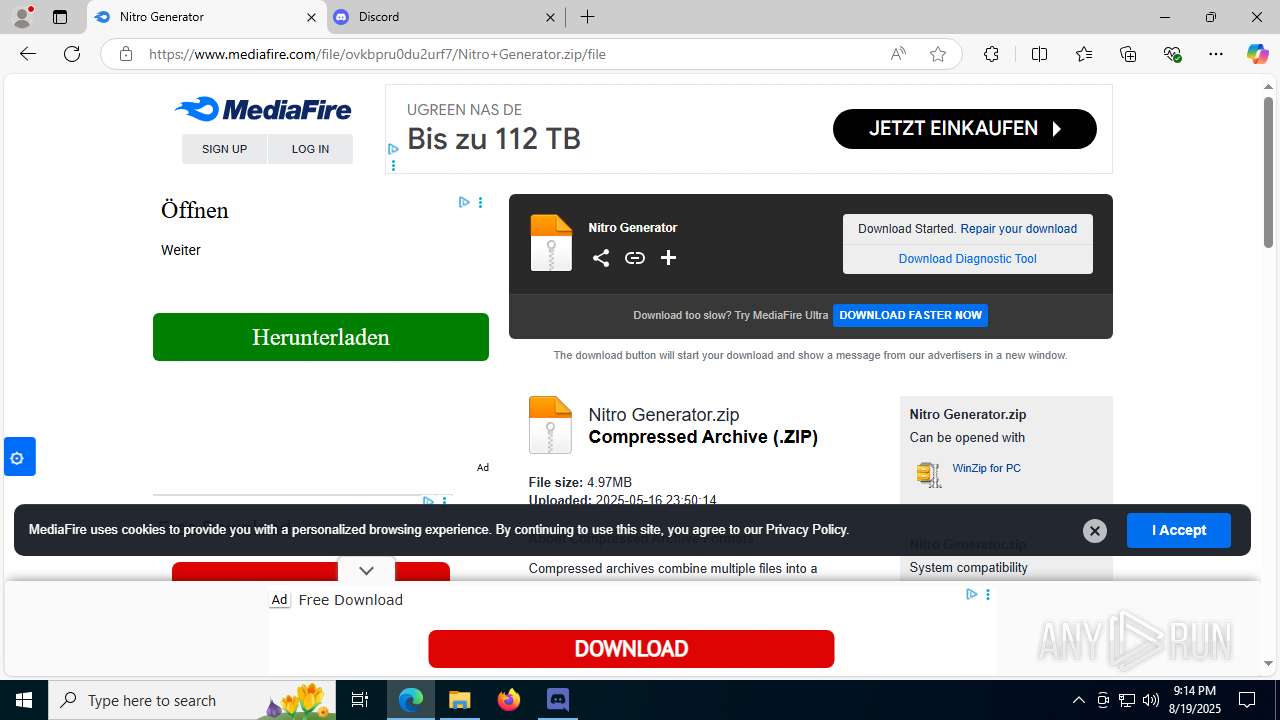
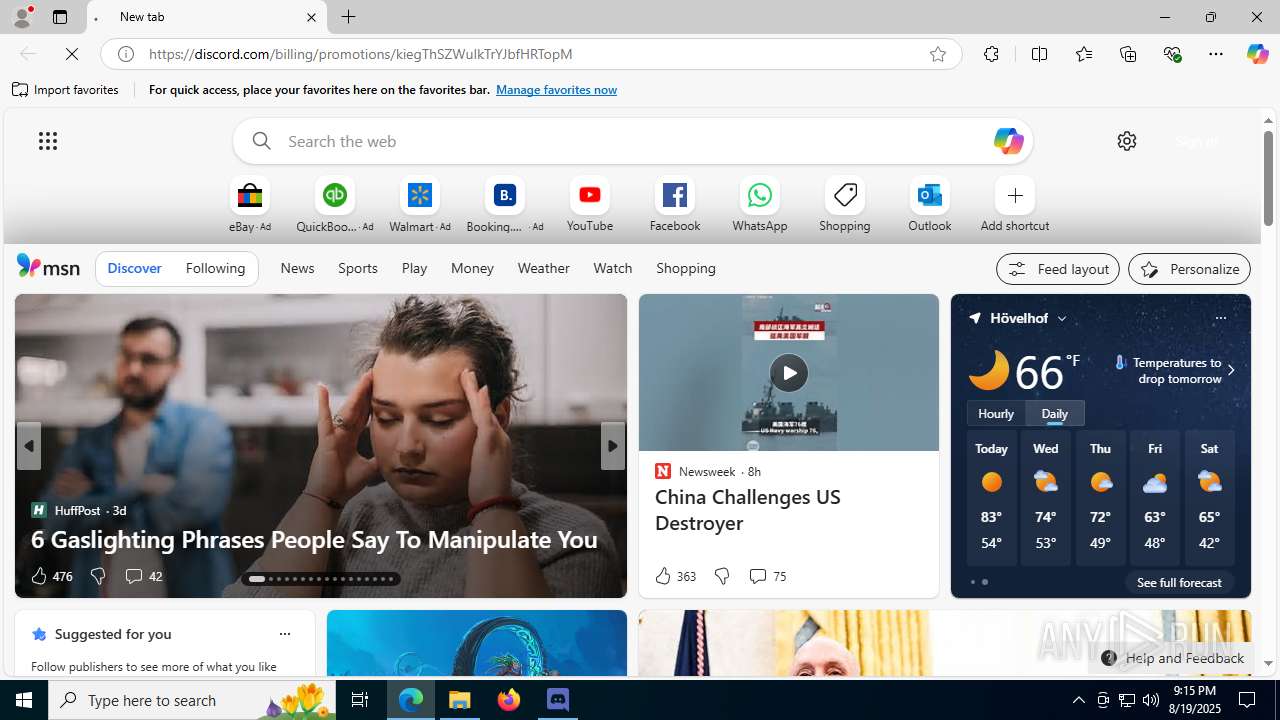
| URL: | https://l1nq.com/DjGyY |
| Full analysis: | https://app.any.run/tasks/d5f9ff79-f082-42ed-b8cc-2f116e3ba561 |
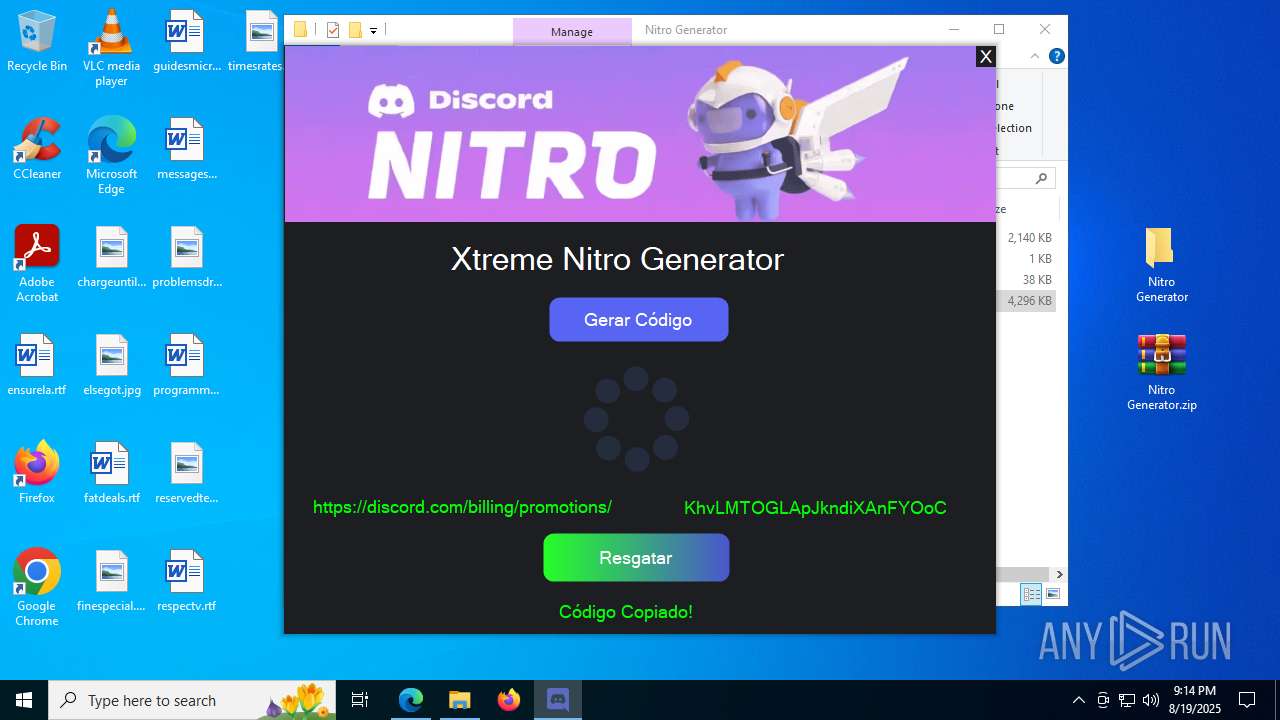
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2025, 21:11:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DEEB230E9387A4F66B10DC92D6E9232D |
| SHA1: | 3F1103ABCF7FB4ADEA102E3E04594EEACAFB1085 |
| SHA256: | AAFB69925A235AB70111F2BAB84E5DF28CA37EFB94584A58B99AD3030FE903FC |
| SSDEEP: | 3:N8ULUyK3On:2Upln |
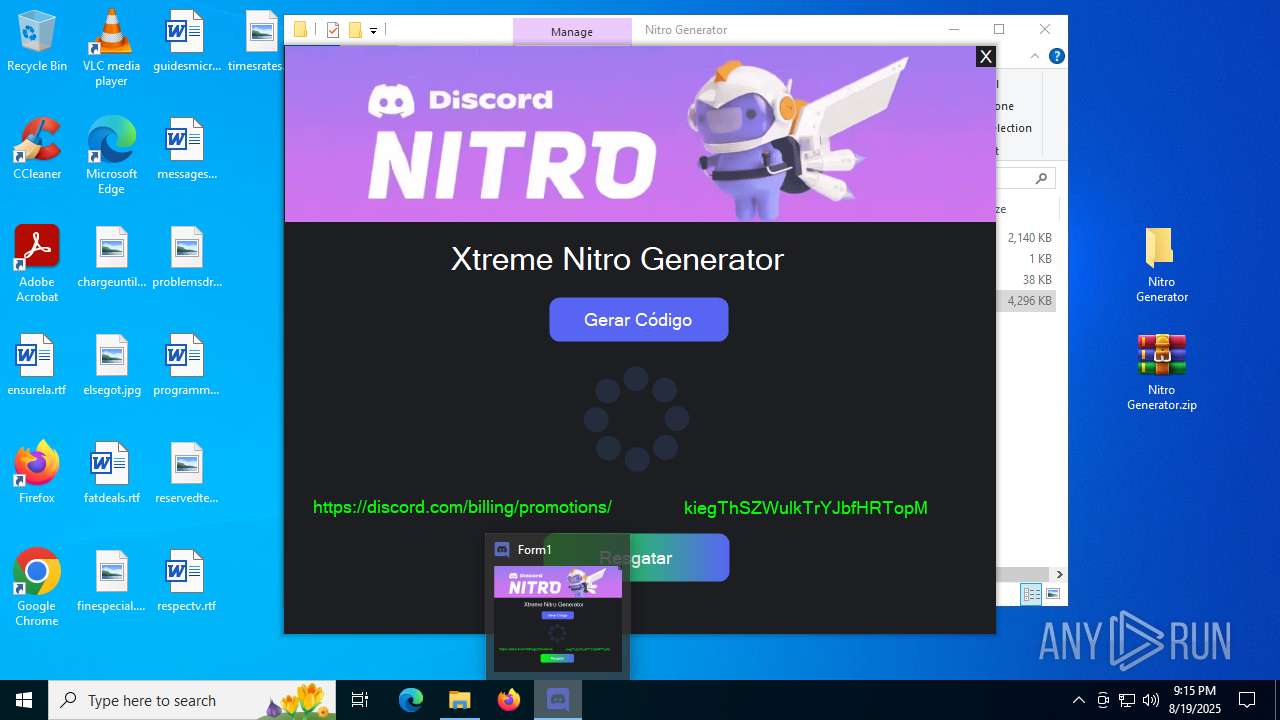
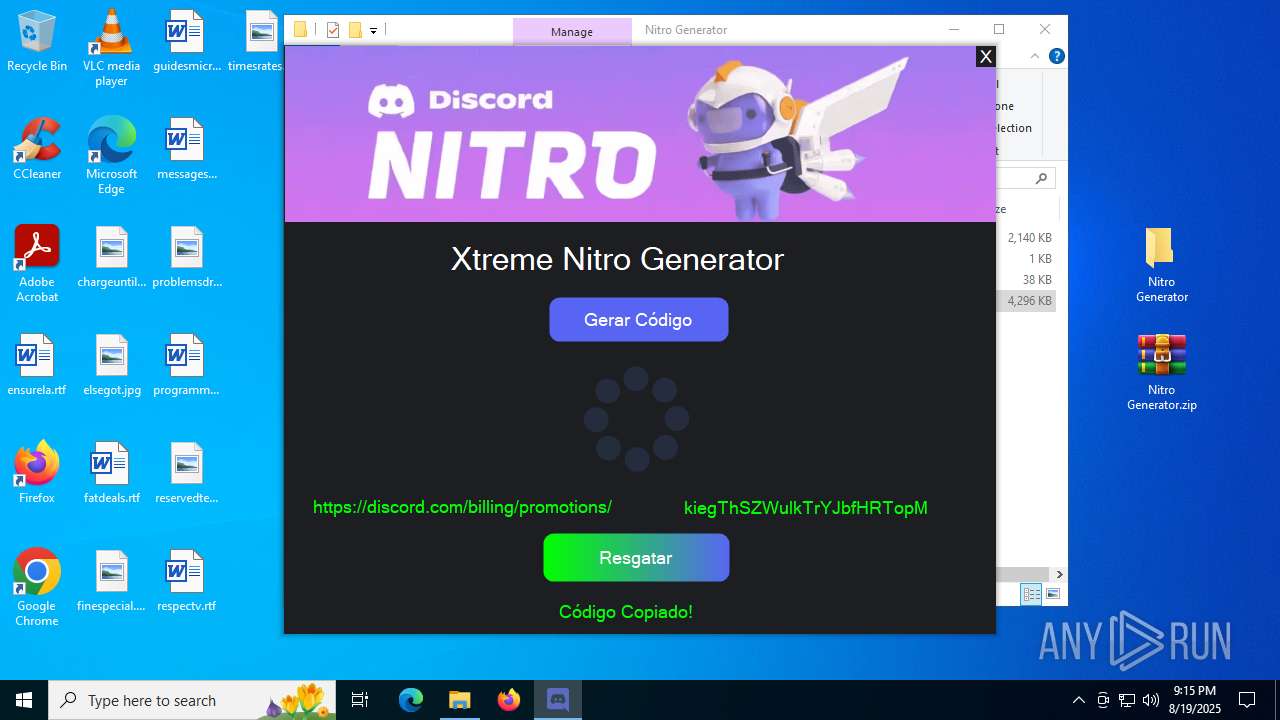
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Xtreme Nitro Gen.exe (PID: 7344)
- 0xc0312199.exe (PID: 3968)
- Xtreme Nitro Gen.exe (PID: 4412)
- 0xc0312199.exe (PID: 2400)
Reads the date of Windows installation
- Xtreme Nitro Gen.exe (PID: 7344)
- 0xc0312199.exe (PID: 3968)
- Xtreme Nitro Gen.exe (PID: 4412)
- 0xc0312199.exe (PID: 2400)
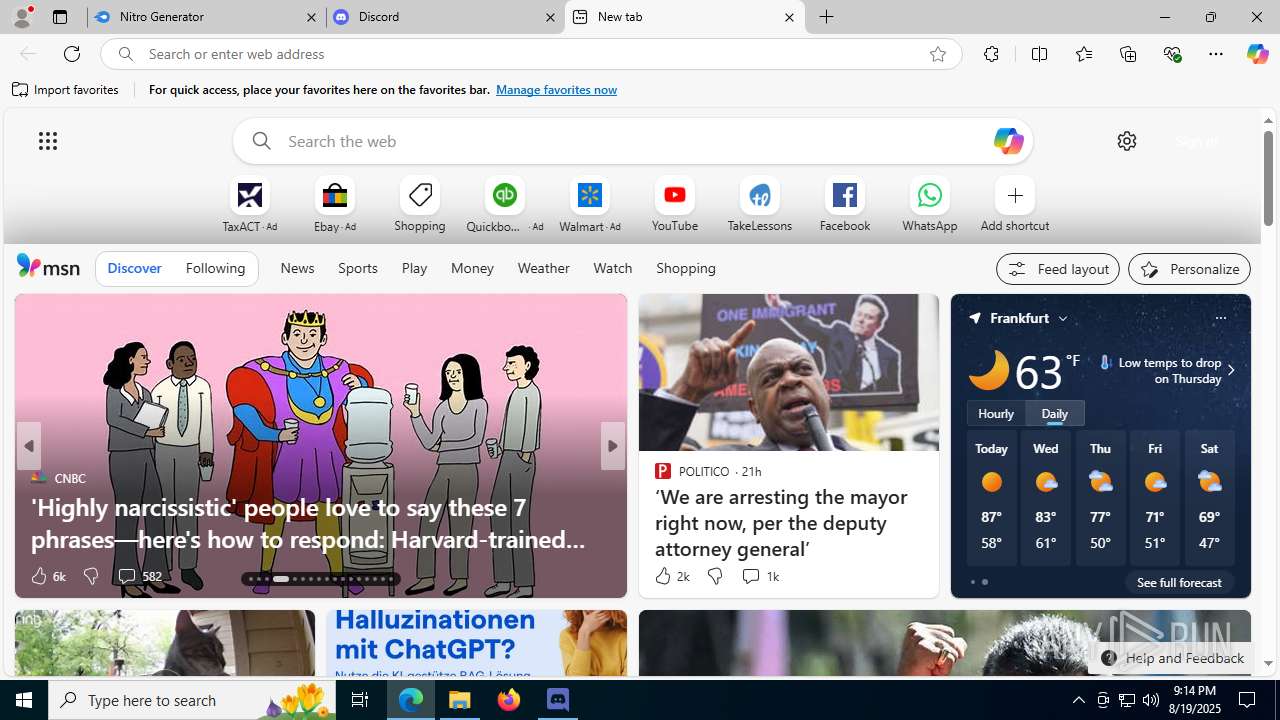
The process creates files with name similar to system file names
- 0xc0312199.exe (PID: 3968)
- 0xc0312199.exe (PID: 2400)
Starts itself from another location
- 0xc0312199.exe (PID: 3968)
- 0xc0312199.exe (PID: 2400)
Executes application which crashes
- Xtreme Nitro Gen.exe (PID: 7344)
- Xtreme Nitro Gen.exe (PID: 4412)
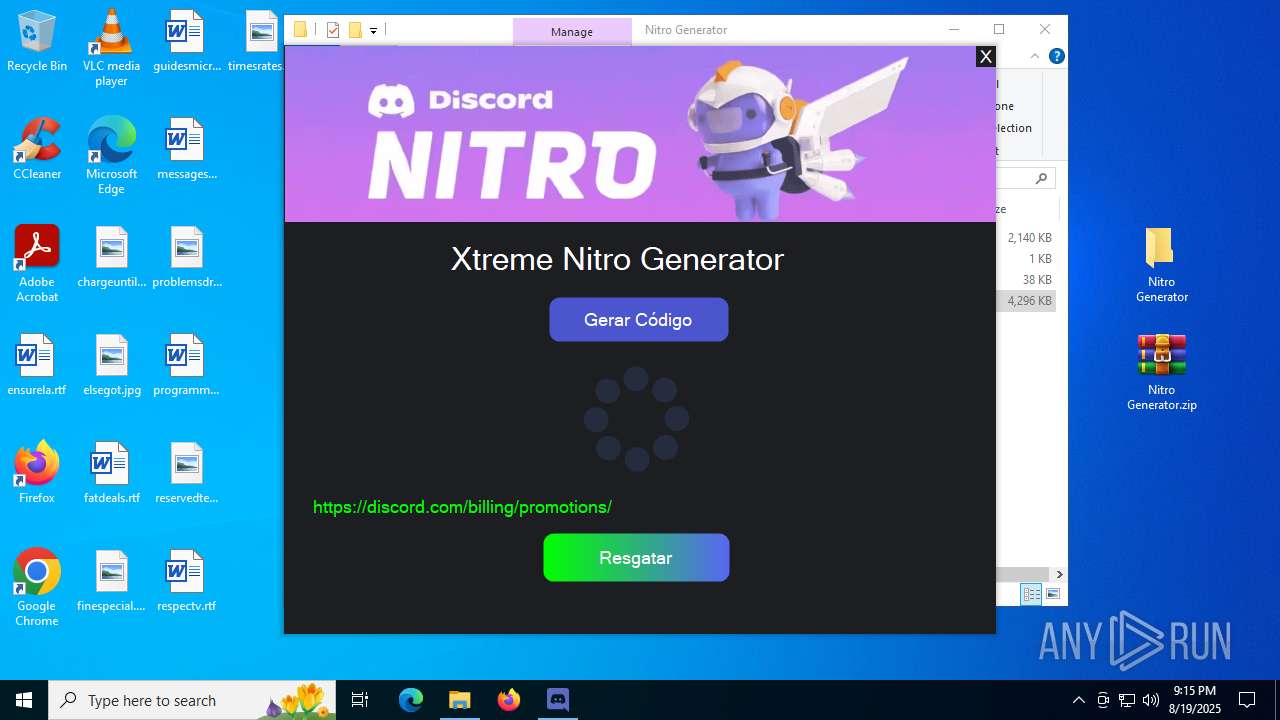
There is functionality for taking screenshot (YARA)
- Nitro.exe (PID: 7256)
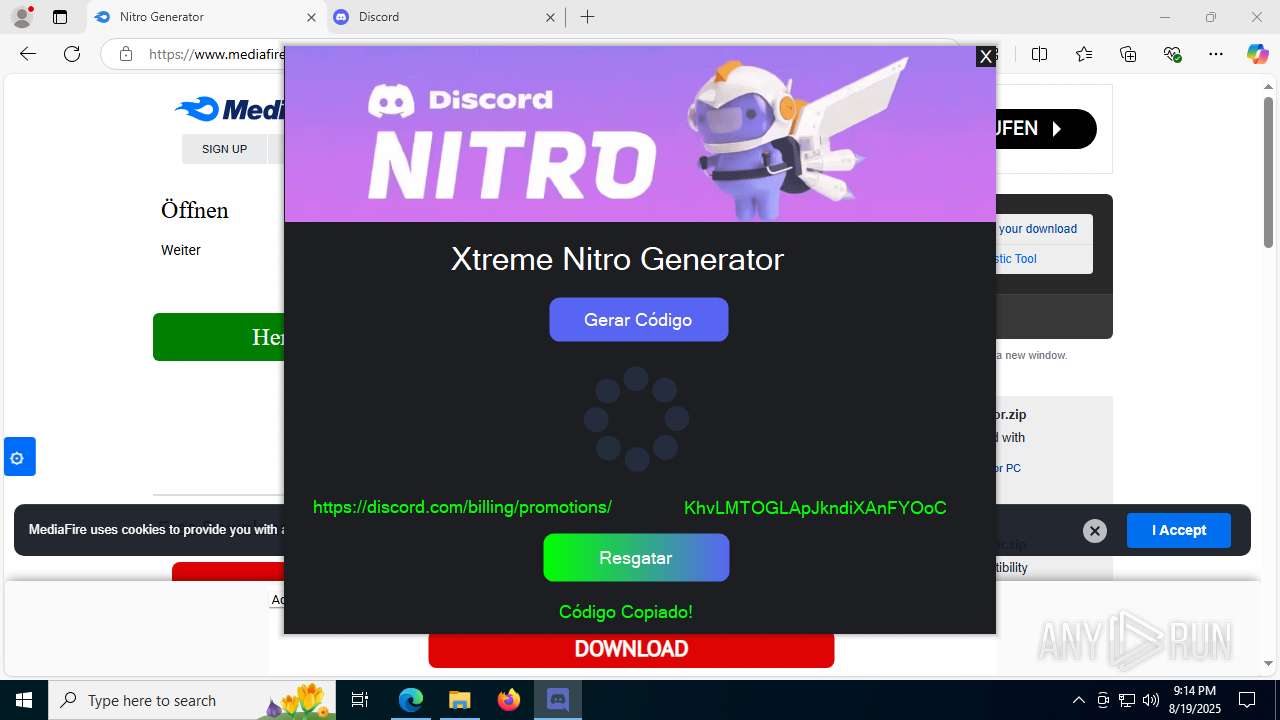
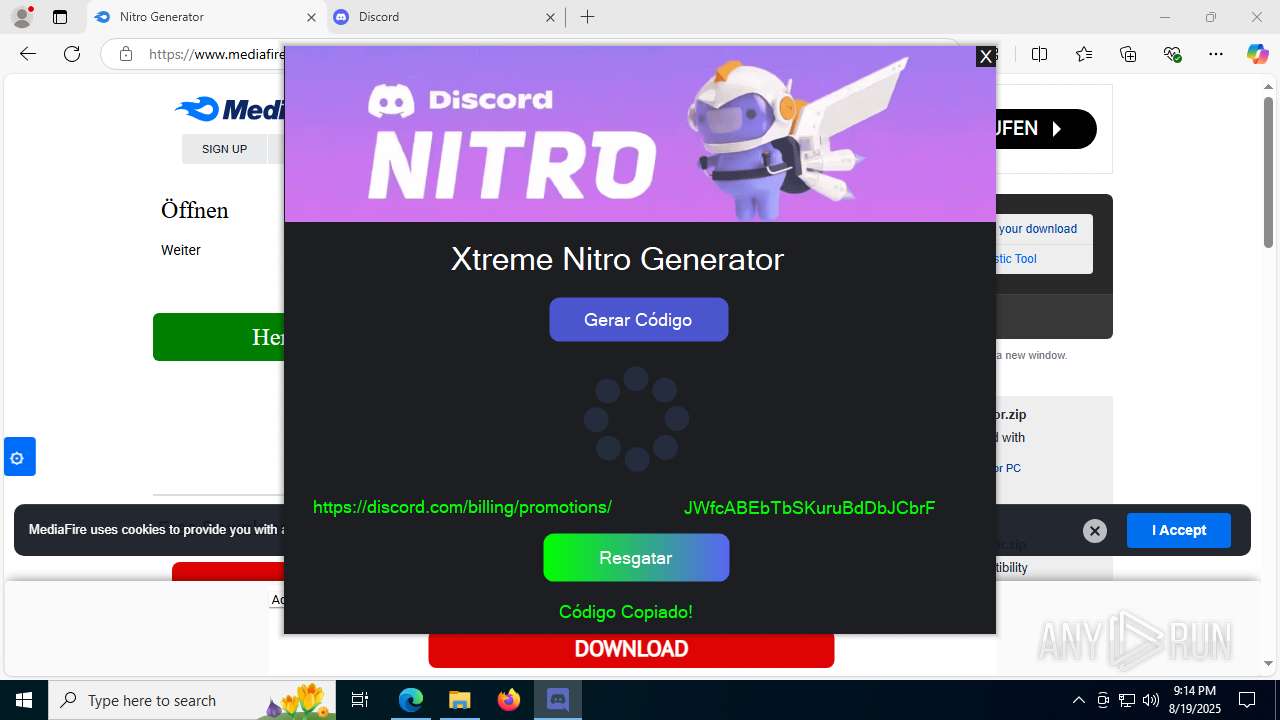
Possible usage of Discord/Telegram API has been detected (YARA)
- smlahost.exe (PID: 5928)
INFO
Application launched itself
- msedge.exe (PID: 1056)
- msedge.exe (PID: 3392)
Reads the computer name
- identity_helper.exe (PID: 7760)
- Xtreme Nitro Gen.exe (PID: 7344)
- 0xc0312199.exe (PID: 3968)
- Nitro.exe (PID: 7256)
- smlahost.exe (PID: 5928)
- identity_helper.exe (PID: 2108)
- Xtreme Nitro Gen.exe (PID: 4412)
- 0xc0312199.exe (PID: 2400)
- Nitro.exe (PID: 7636)
- smlahost.exe (PID: 1660)
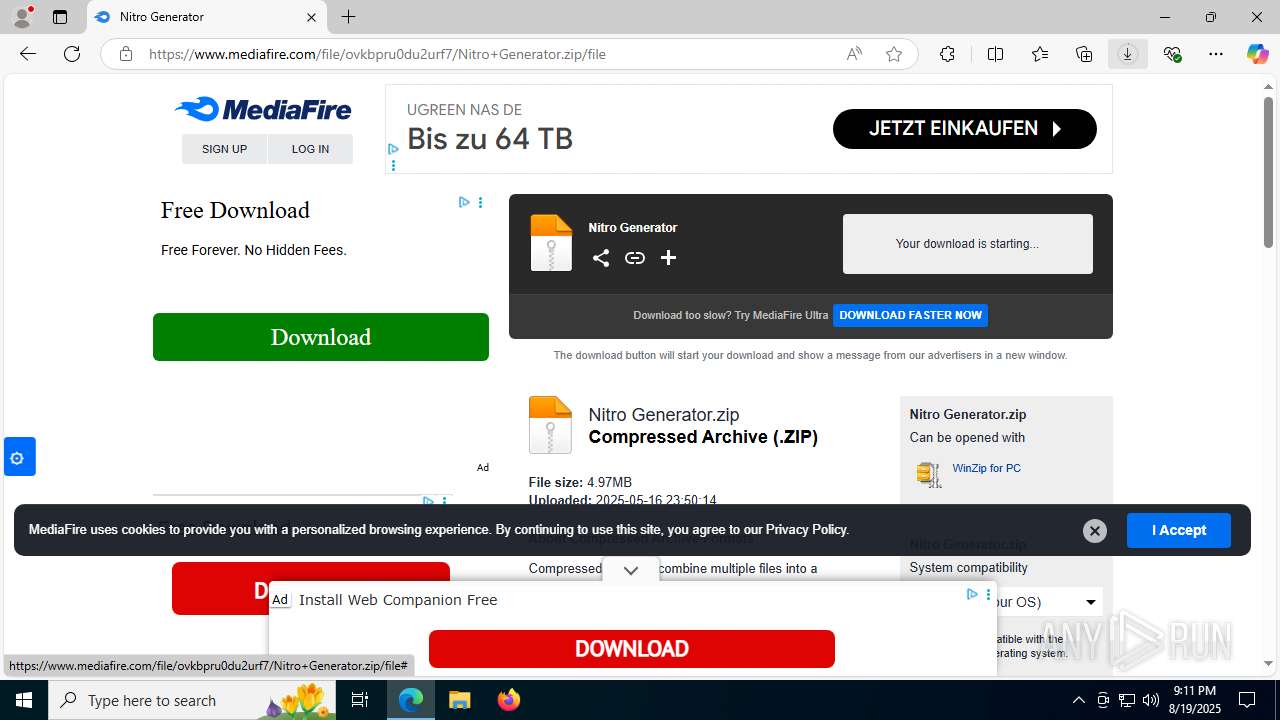
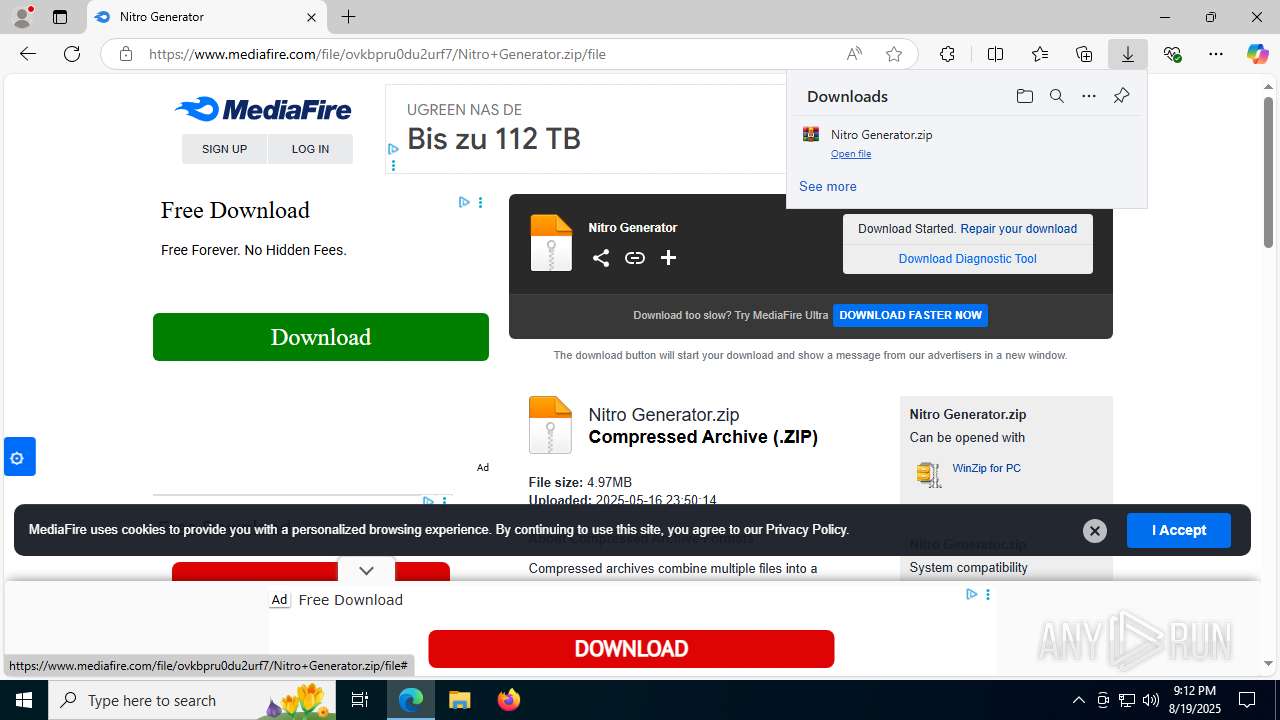
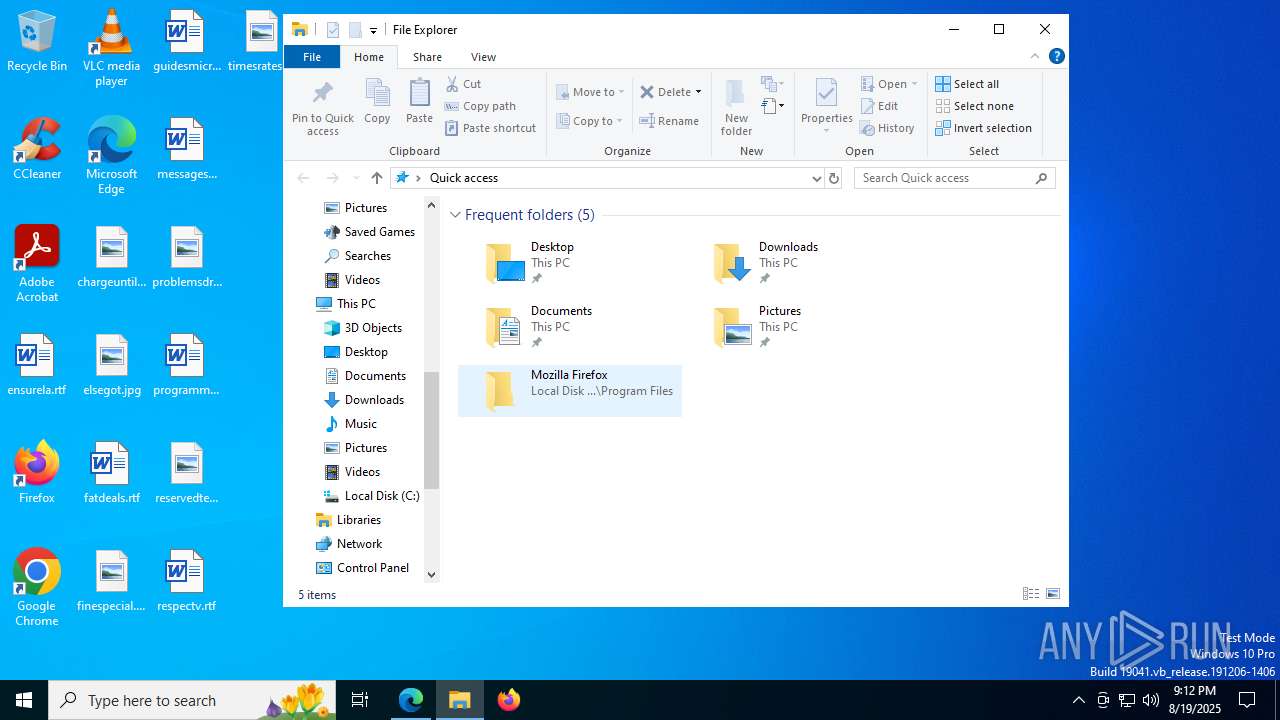
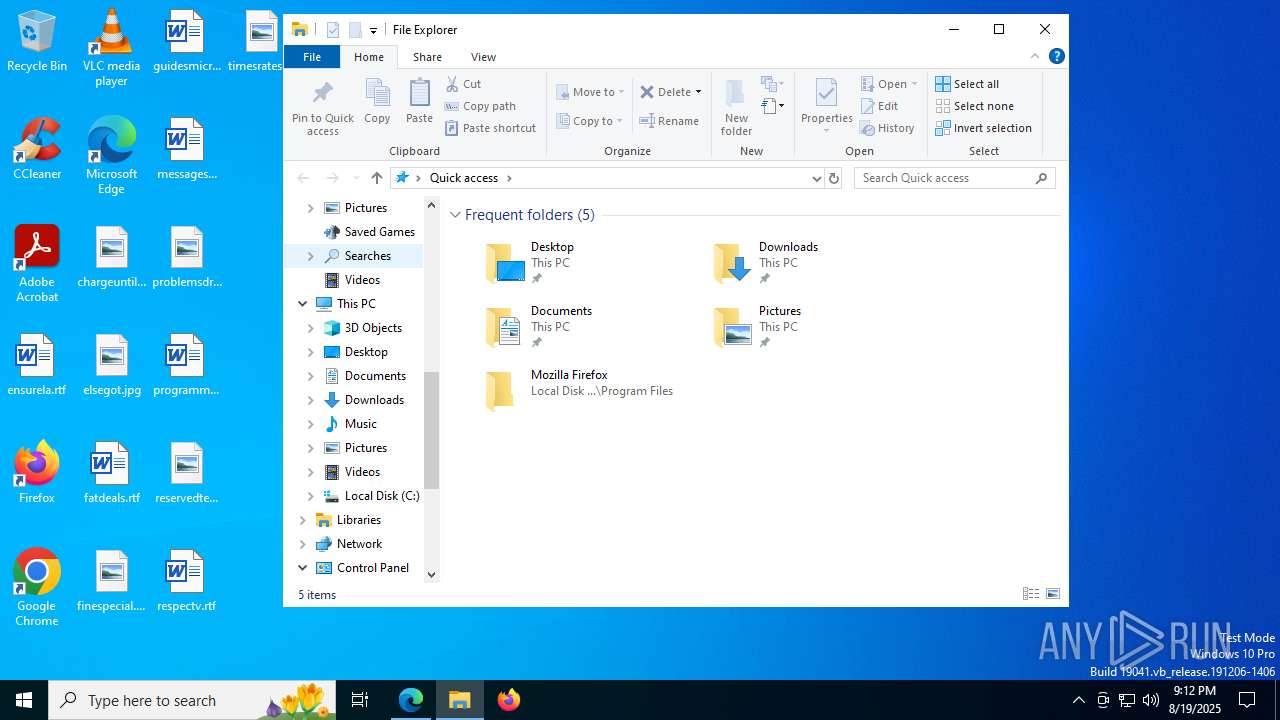
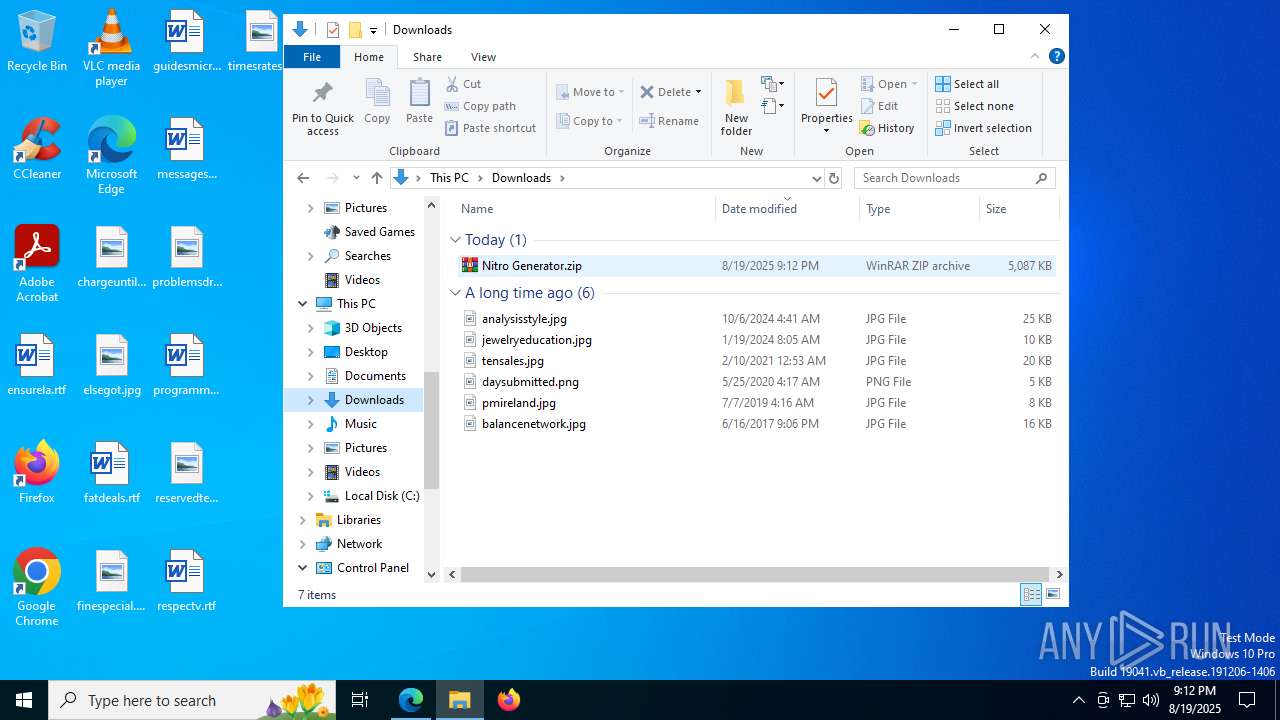
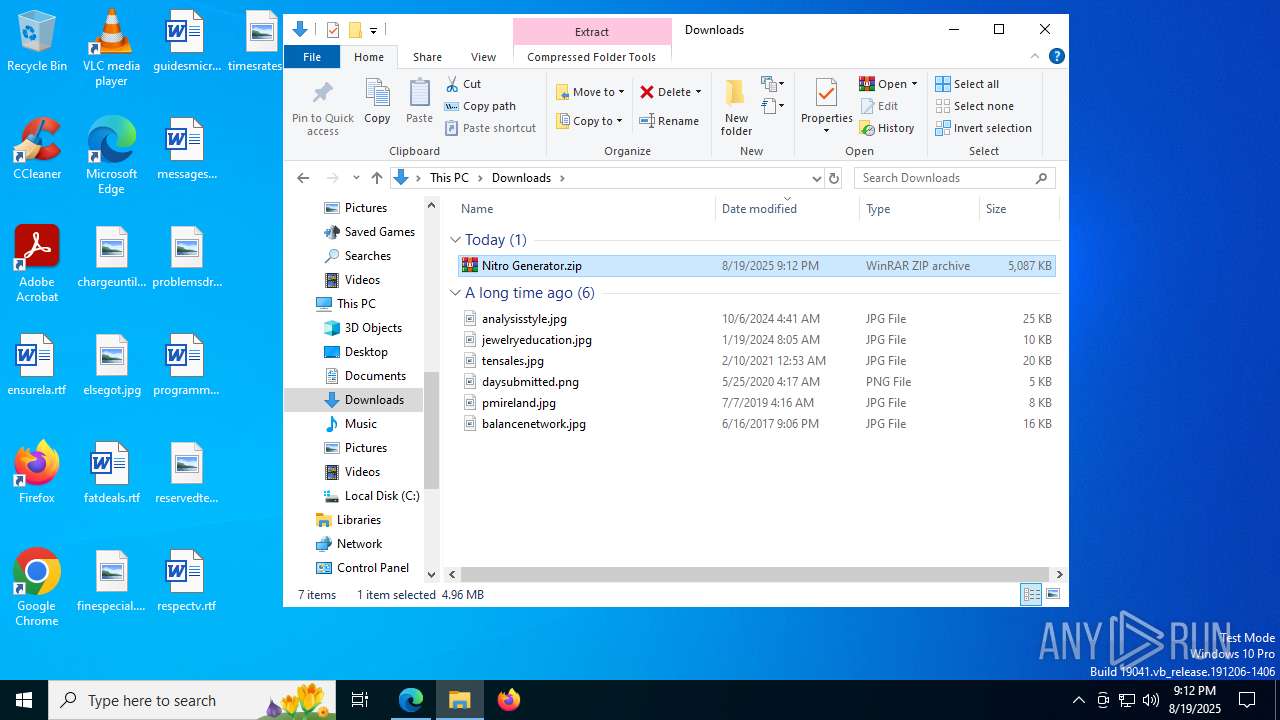
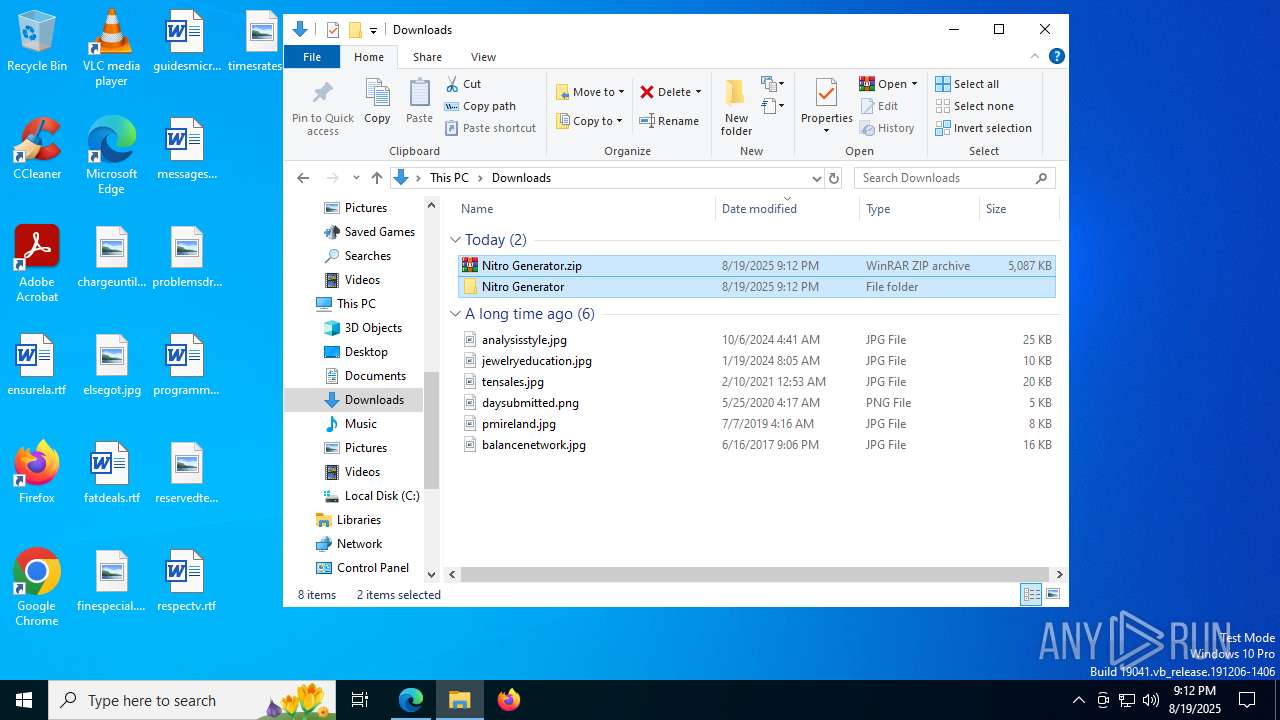
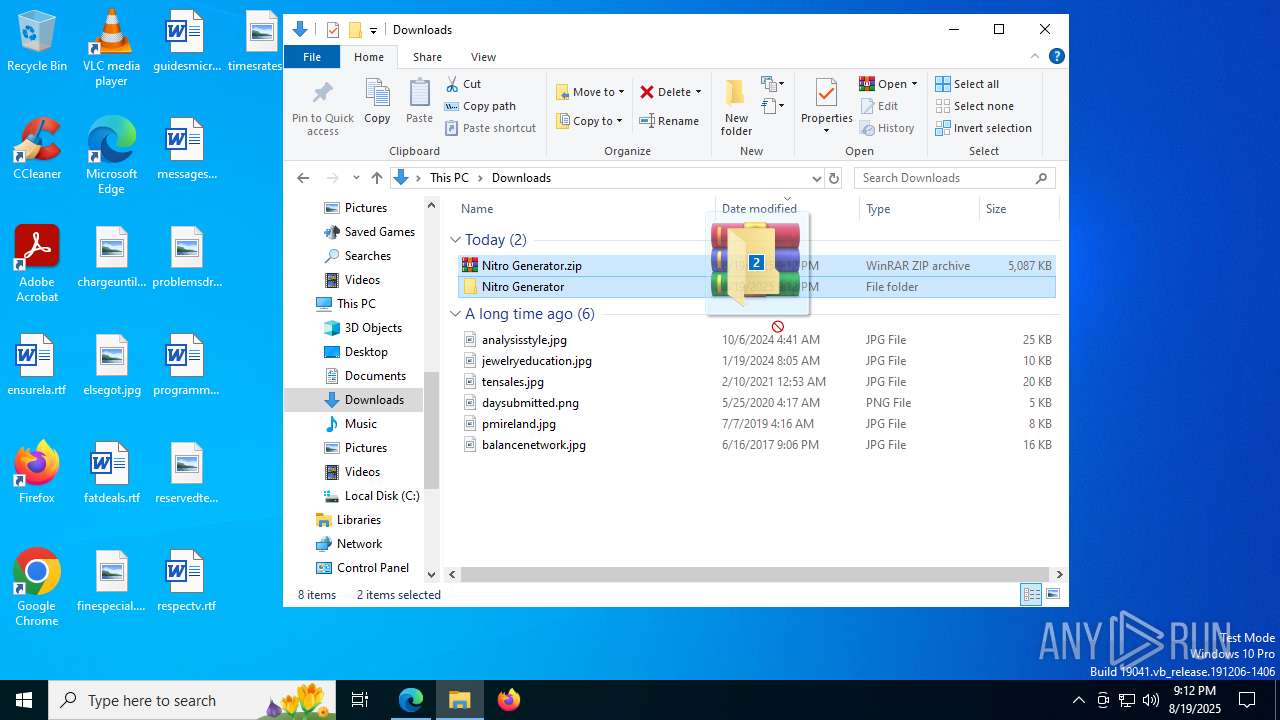
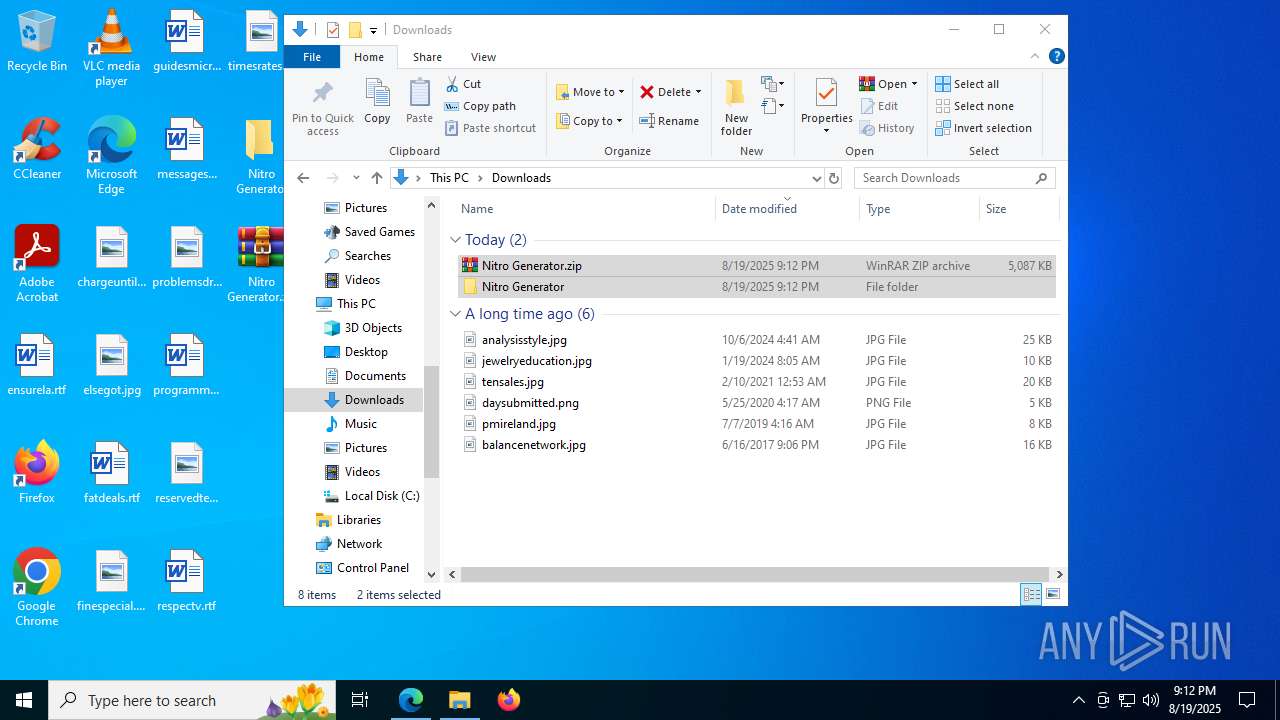
Launching a file from the Downloads directory
- msedge.exe (PID: 1056)
Reads Microsoft Office registry keys
- msedge.exe (PID: 1056)
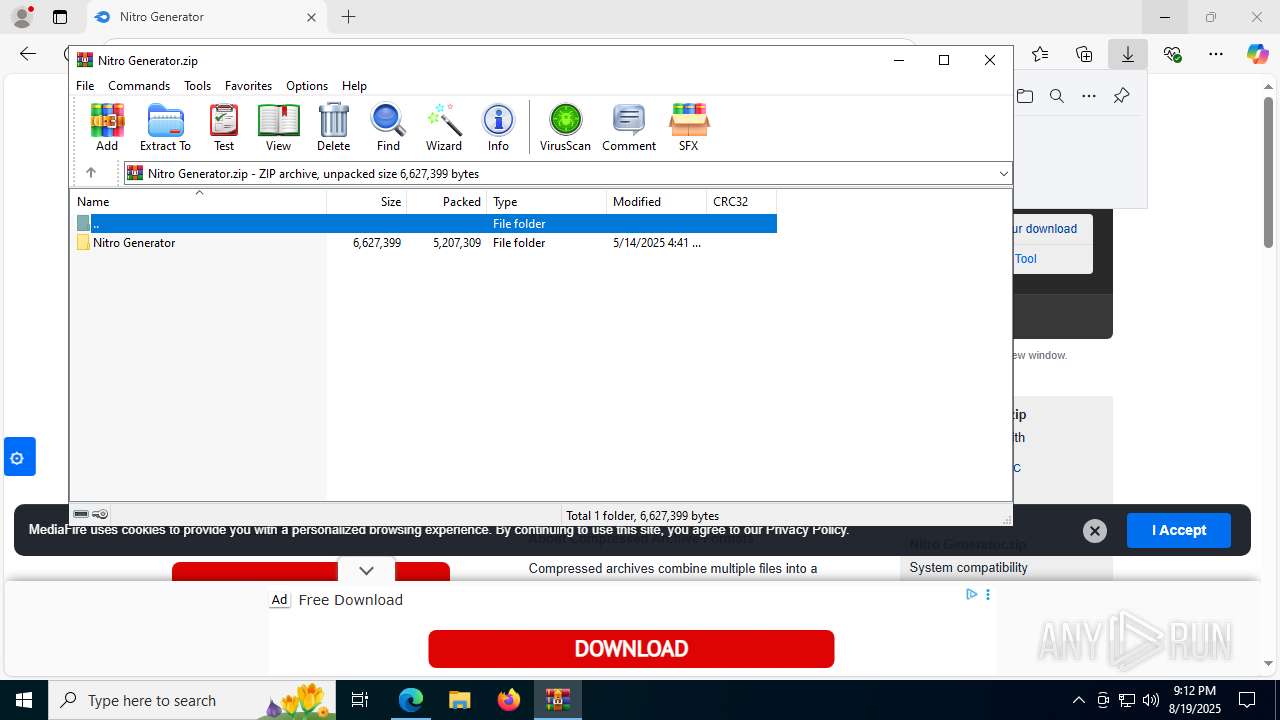
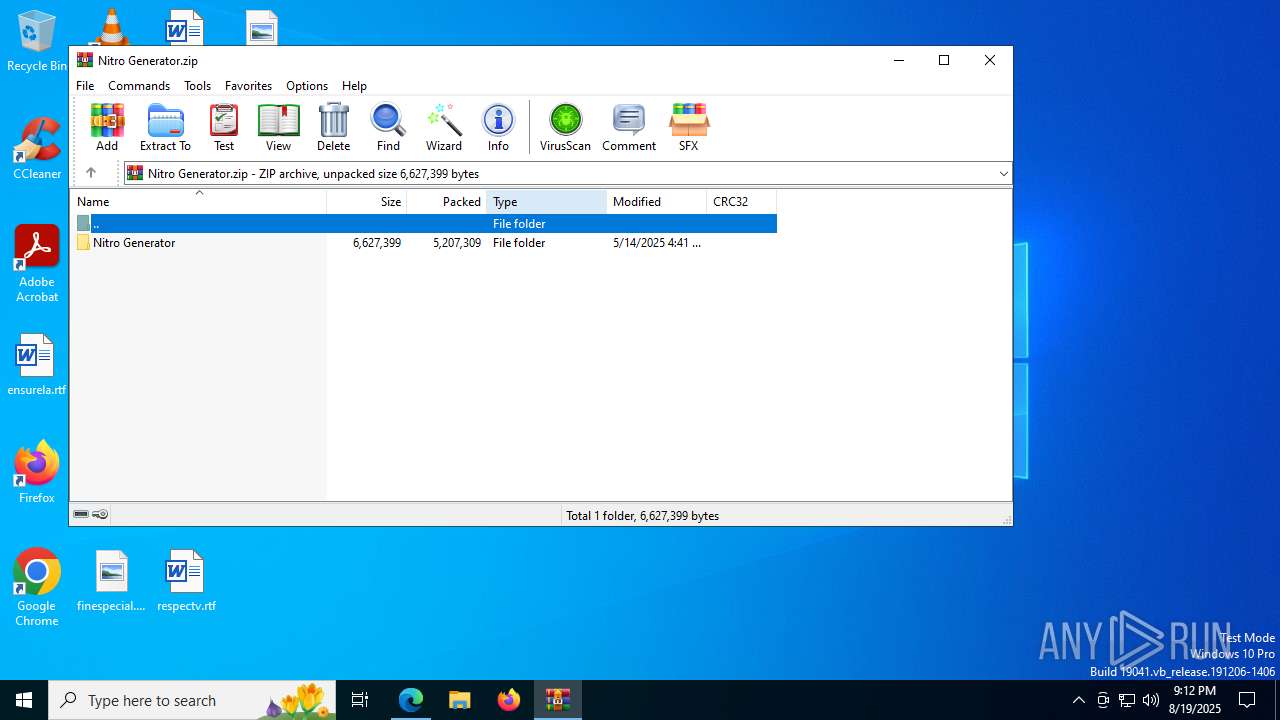
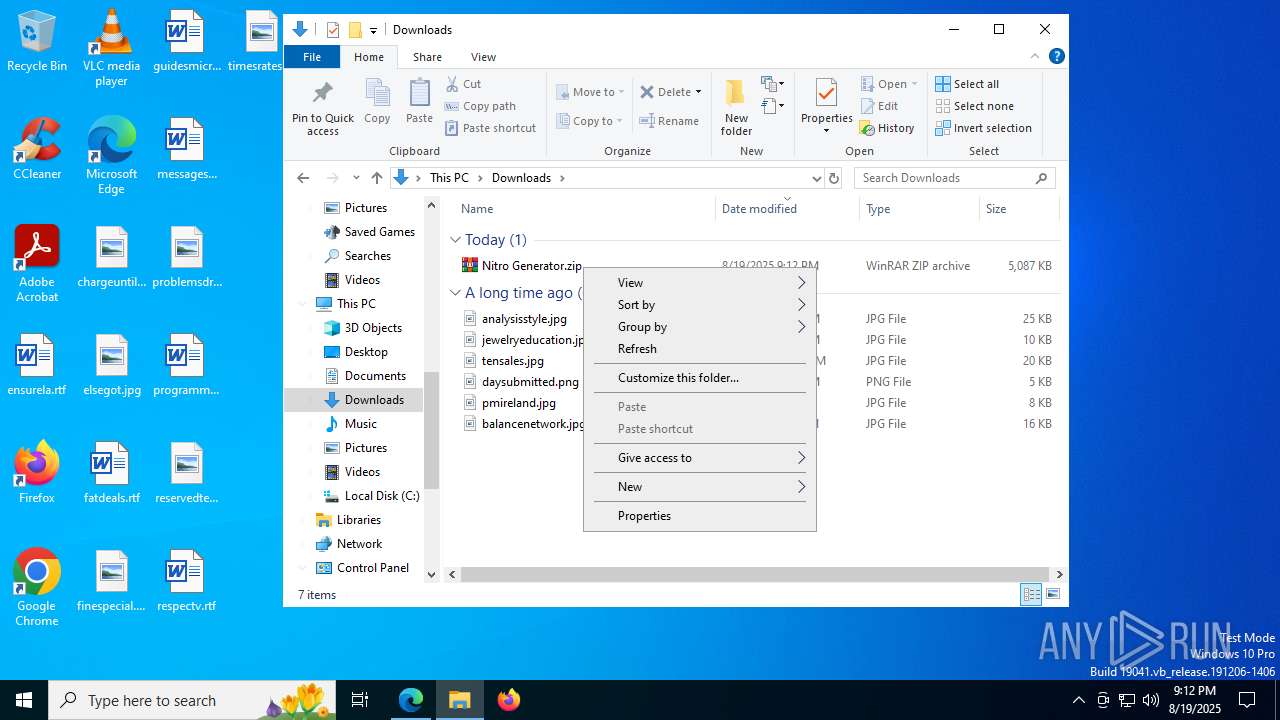
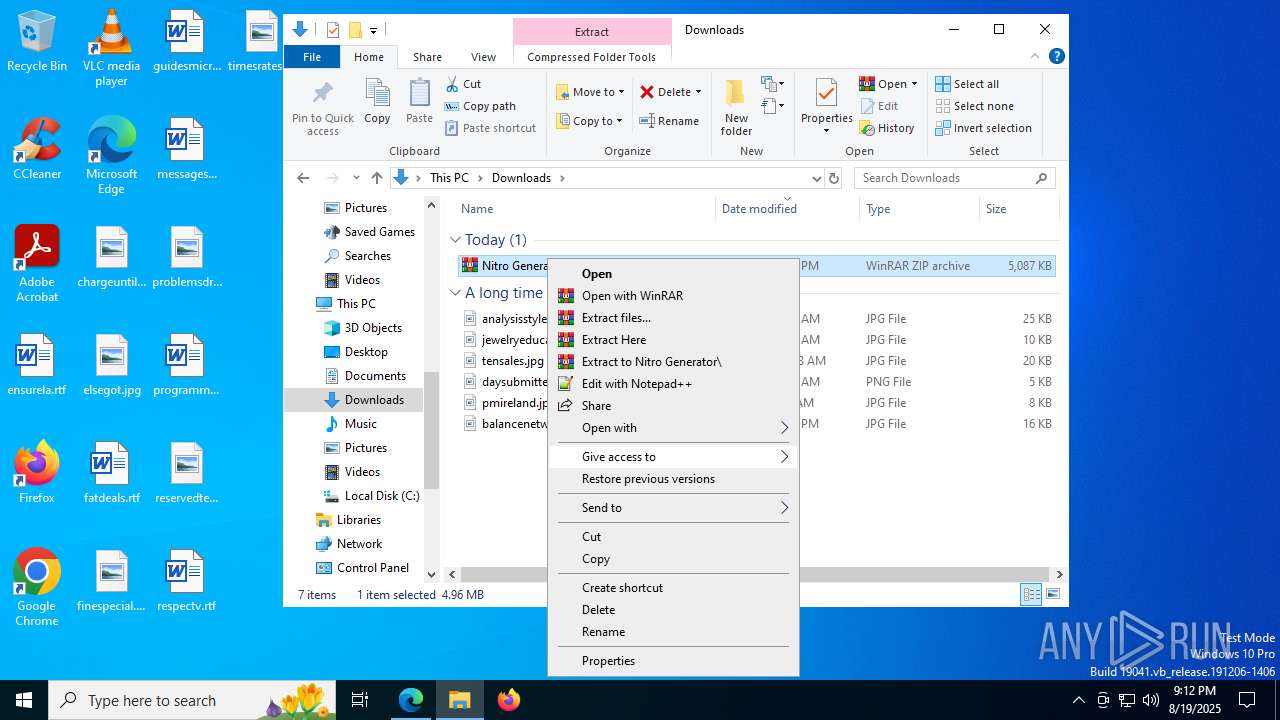
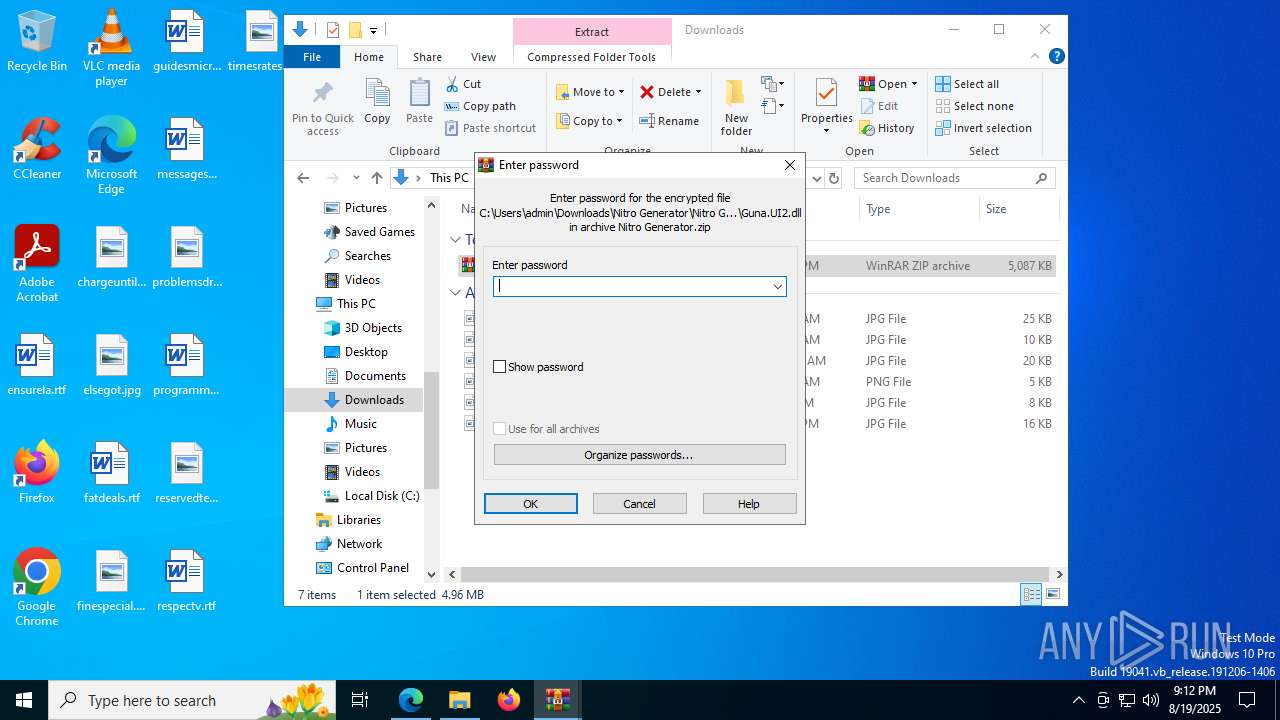
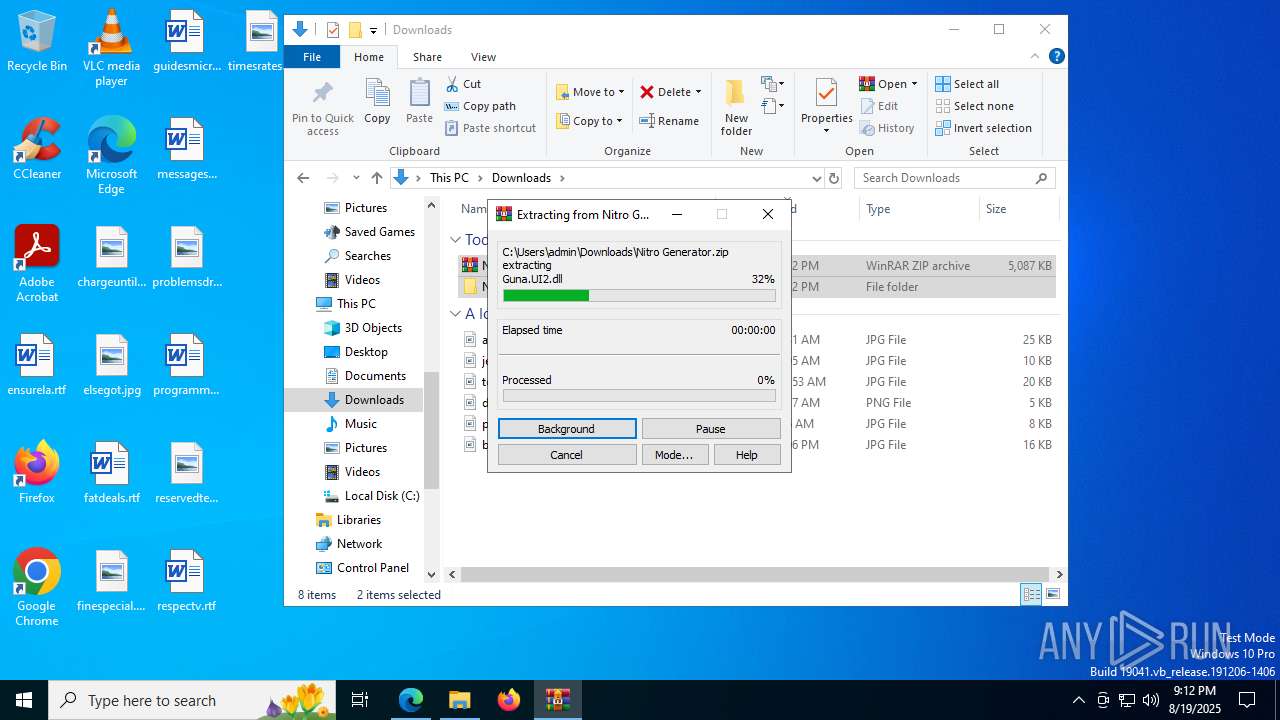
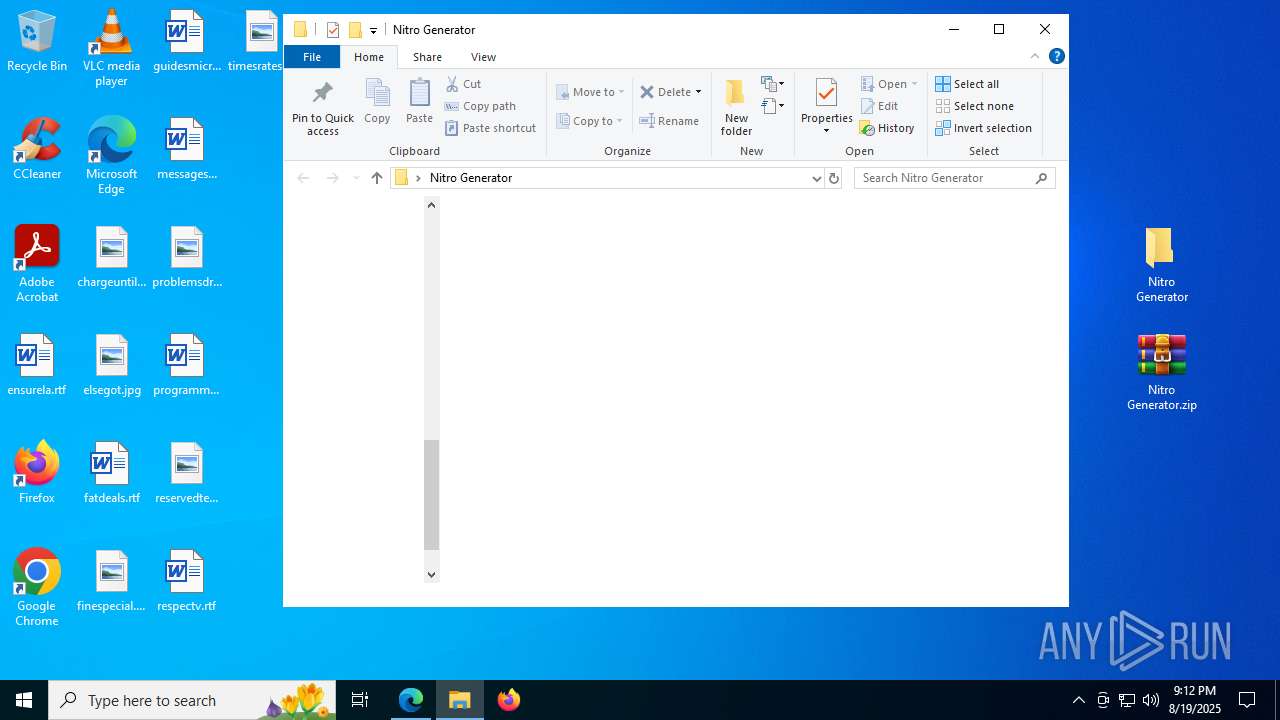
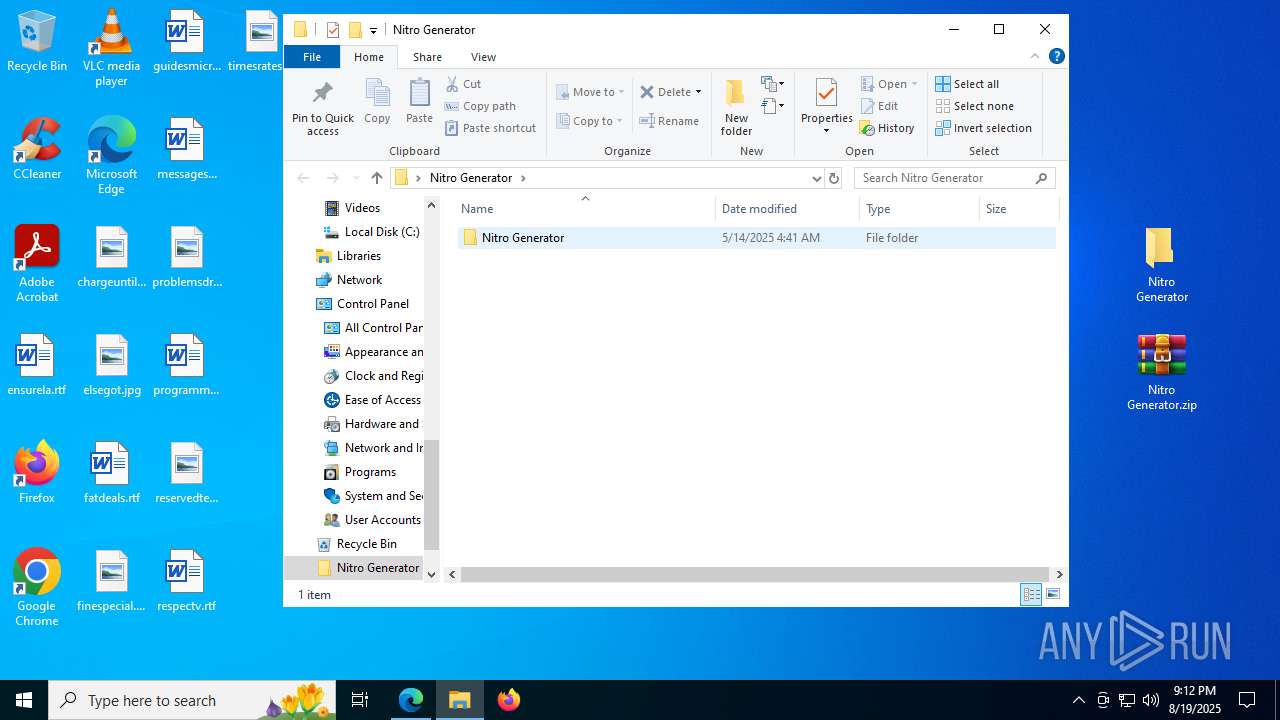
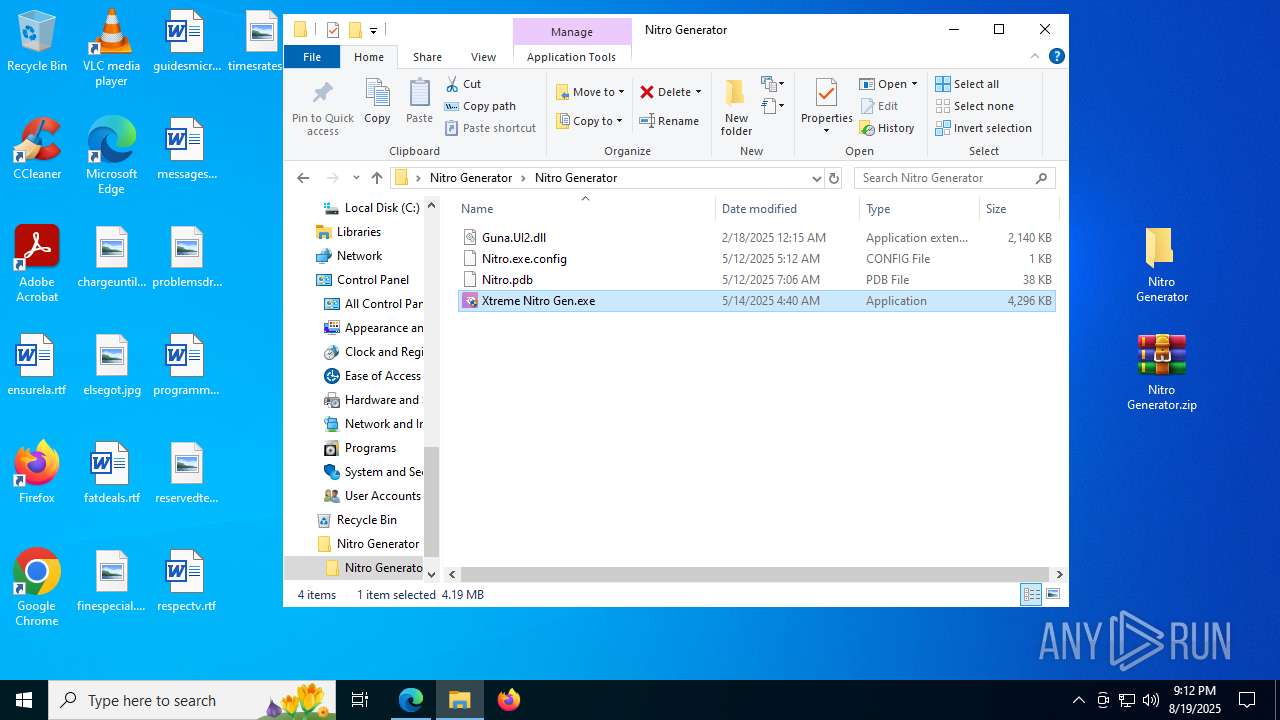
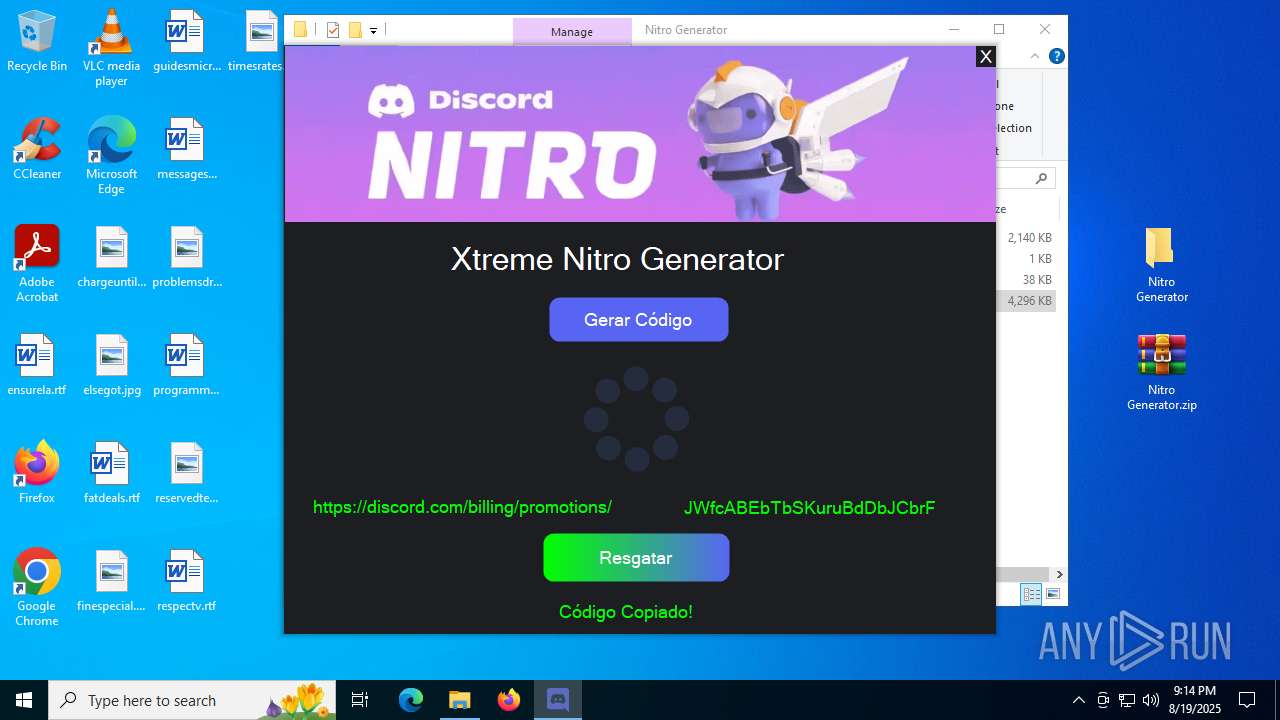
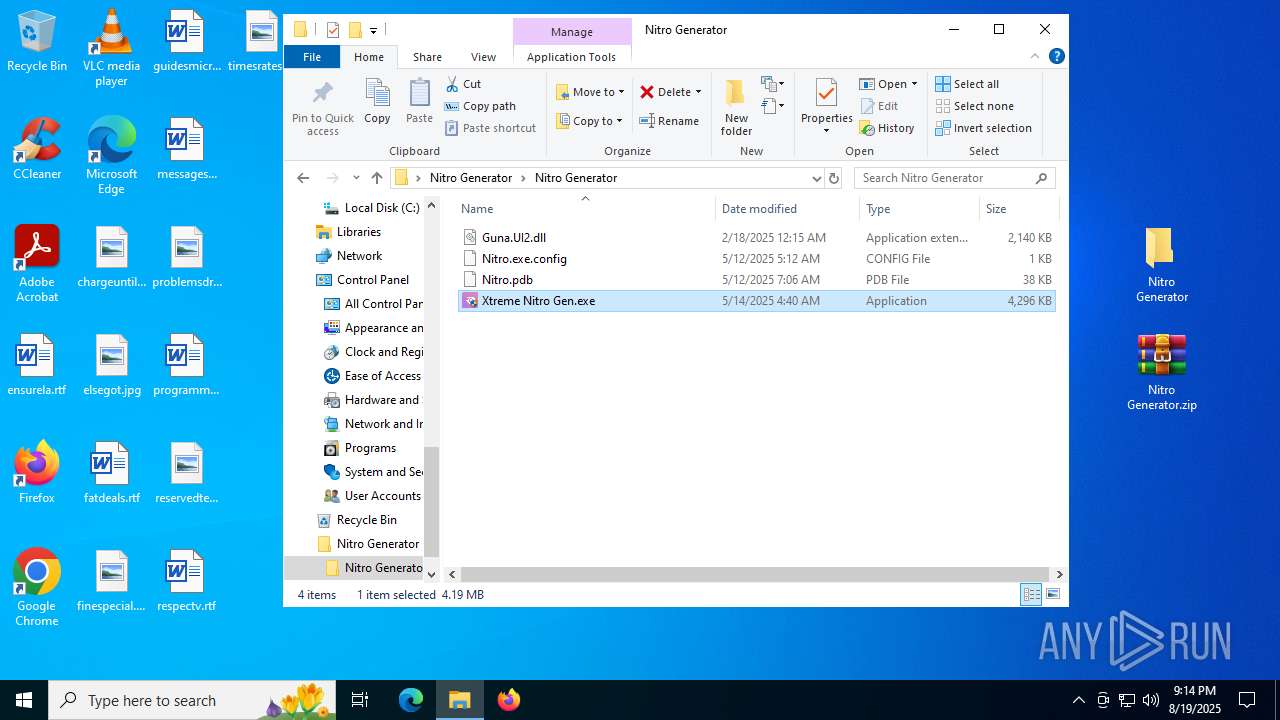
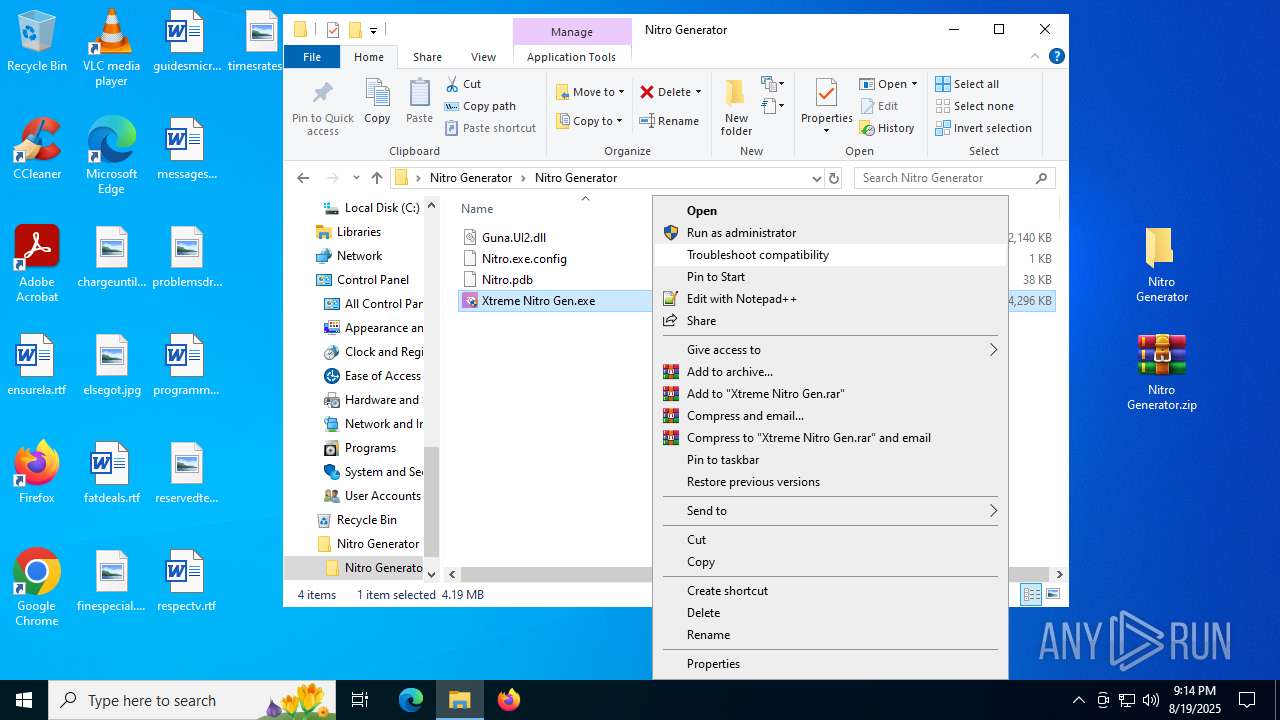
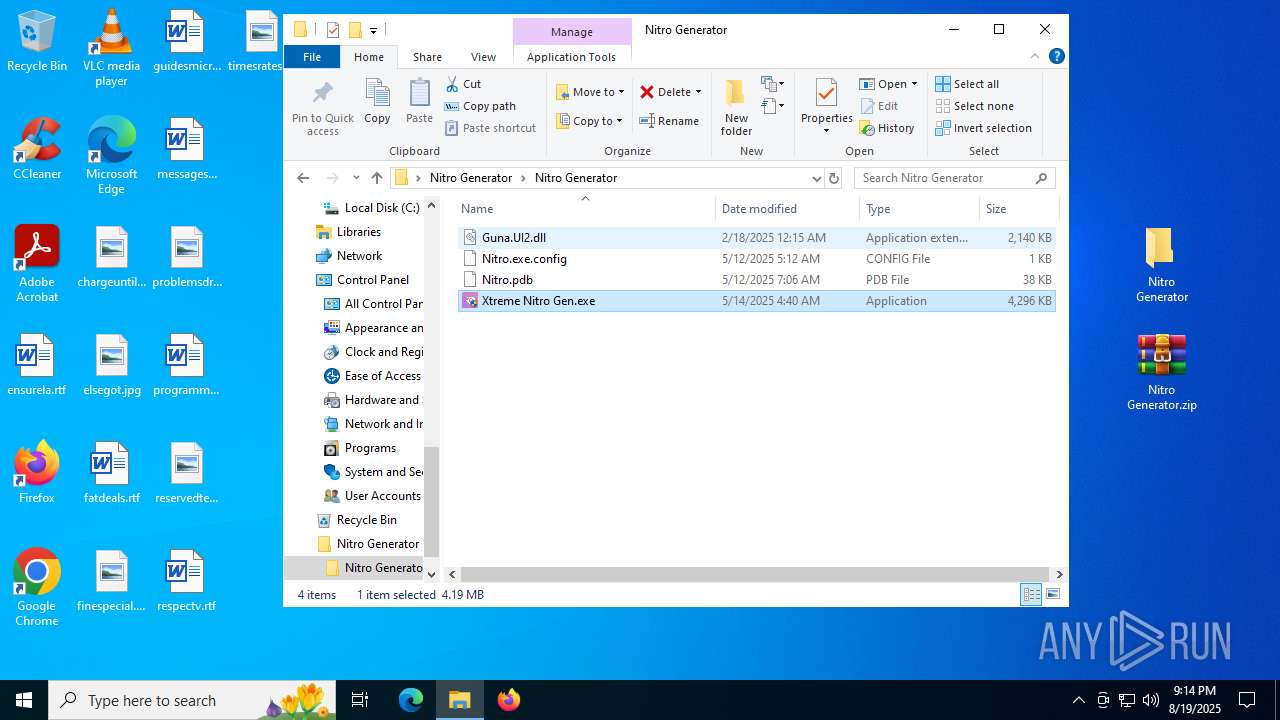
Manual execution by a user
- WinRAR.exe (PID: 8000)
- Xtreme Nitro Gen.exe (PID: 7336)
- Xtreme Nitro Gen.exe (PID: 7344)
- Xtreme Nitro Gen.exe (PID: 4412)
- msedge.exe (PID: 3644)
Checks supported languages
- identity_helper.exe (PID: 7760)
- Xtreme Nitro Gen.exe (PID: 7344)
- 0xc0312199.exe (PID: 3968)
- smlahost.exe (PID: 5928)
- Nitro.exe (PID: 7256)
- identity_helper.exe (PID: 2108)
- Xtreme Nitro Gen.exe (PID: 4412)
- 0xc0312199.exe (PID: 2400)
- Nitro.exe (PID: 7636)
- smlahost.exe (PID: 1660)
Reads Environment values
- identity_helper.exe (PID: 7760)
- smlahost.exe (PID: 5928)
- identity_helper.exe (PID: 2108)
- smlahost.exe (PID: 1660)
Process checks computer location settings
- Xtreme Nitro Gen.exe (PID: 7344)
- 0xc0312199.exe (PID: 3968)
- Xtreme Nitro Gen.exe (PID: 4412)
- 0xc0312199.exe (PID: 2400)
Create files in a temporary directory
- Xtreme Nitro Gen.exe (PID: 7344)
- Xtreme Nitro Gen.exe (PID: 4412)
Creates files in the program directory
- 0xc0312199.exe (PID: 3968)
- 0xc0312199.exe (PID: 2400)
Reads the machine GUID from the registry
- Xtreme Nitro Gen.exe (PID: 7344)
- smlahost.exe (PID: 5928)
- Nitro.exe (PID: 7256)
- Xtreme Nitro Gen.exe (PID: 4412)
- Nitro.exe (PID: 7636)
- smlahost.exe (PID: 1660)
Disables trace logs
- smlahost.exe (PID: 5928)
- smlahost.exe (PID: 1660)
Reads the software policy settings
- slui.exe (PID: 7876)
- smlahost.exe (PID: 5928)
- WerFault.exe (PID: 7788)
- WerFault.exe (PID: 4224)
- smlahost.exe (PID: 1660)
Checks proxy server information
- slui.exe (PID: 7876)
- smlahost.exe (PID: 5928)
- WerFault.exe (PID: 7788)
- WerFault.exe (PID: 4224)
- smlahost.exe (PID: 1660)
Creates files or folders in the user directory
- WerFault.exe (PID: 7788)
- WerFault.exe (PID: 4224)
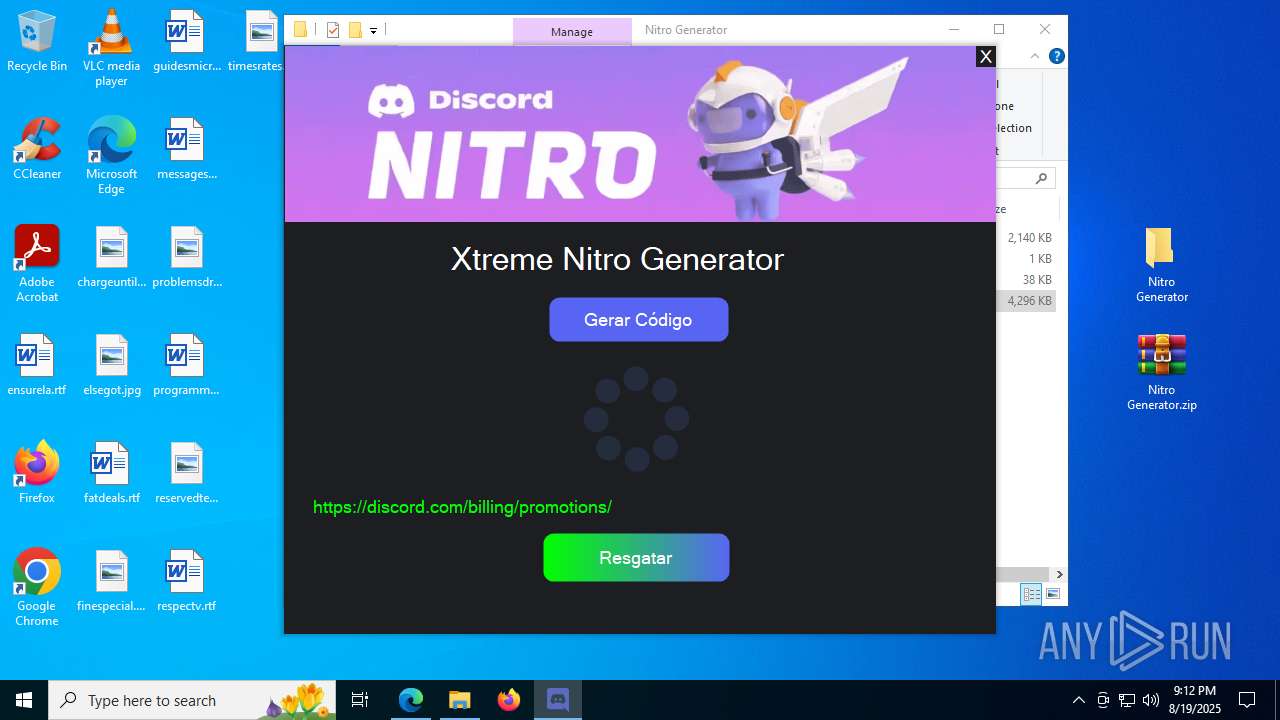
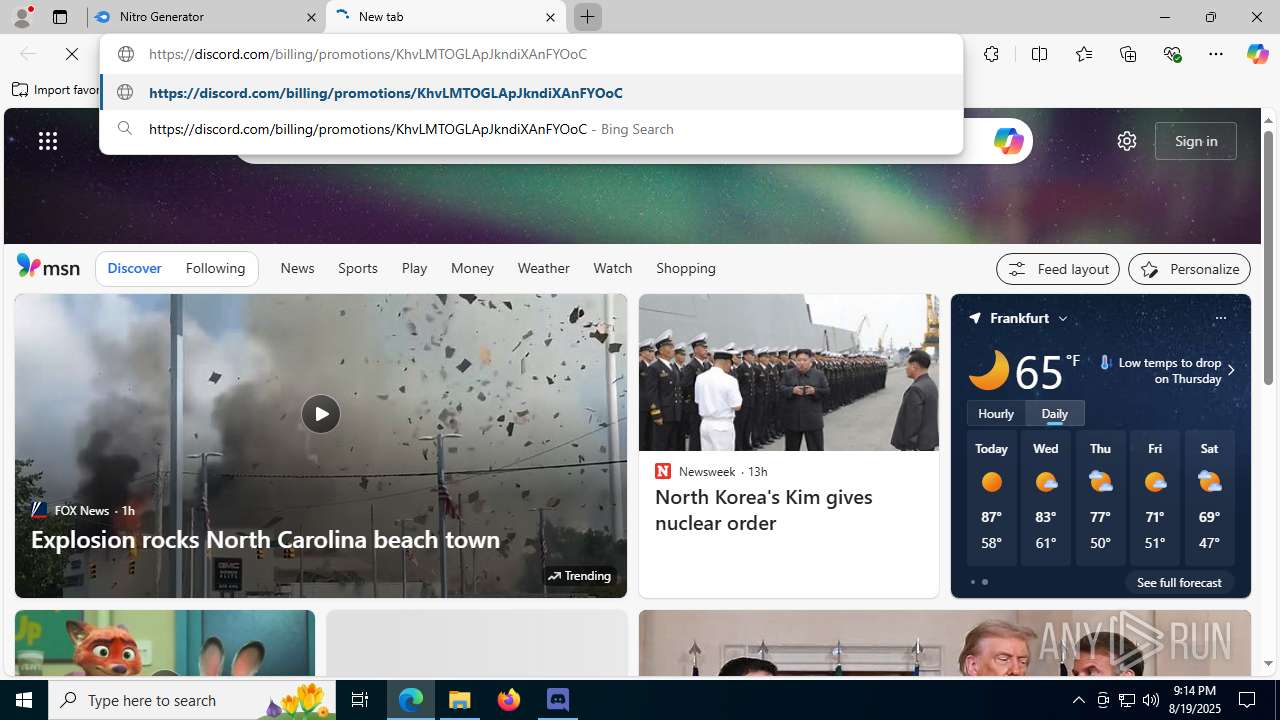
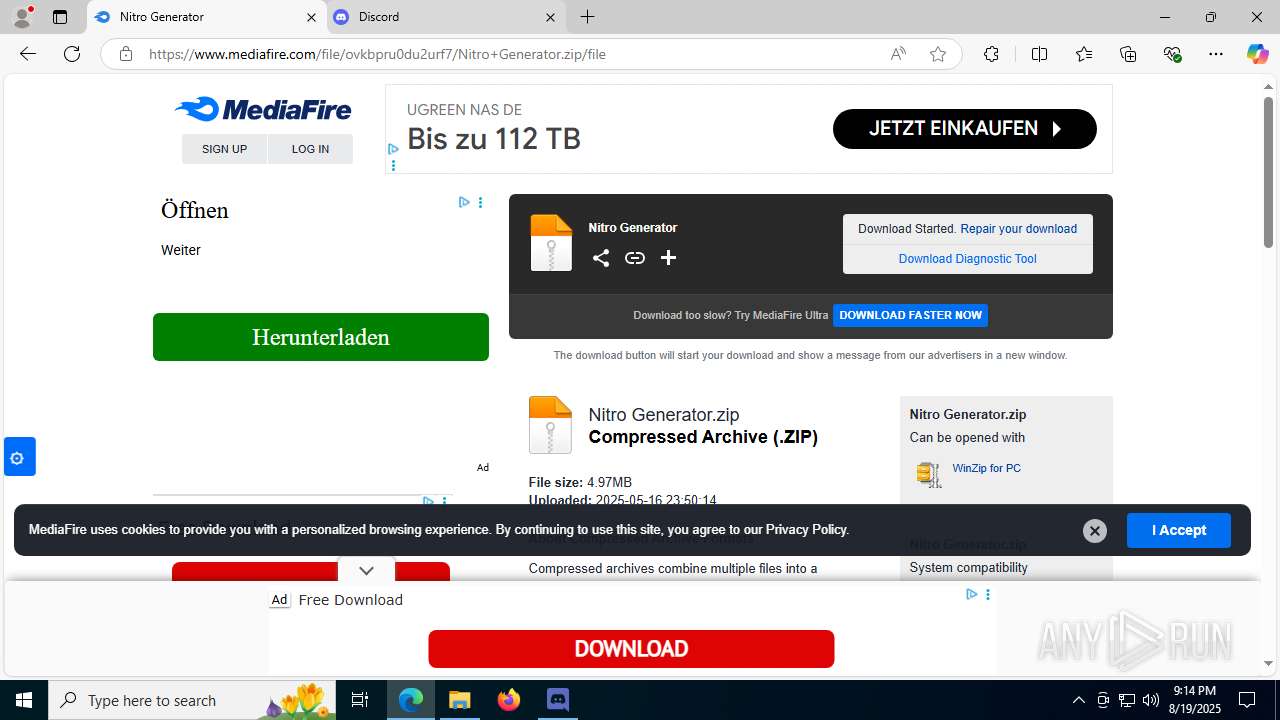
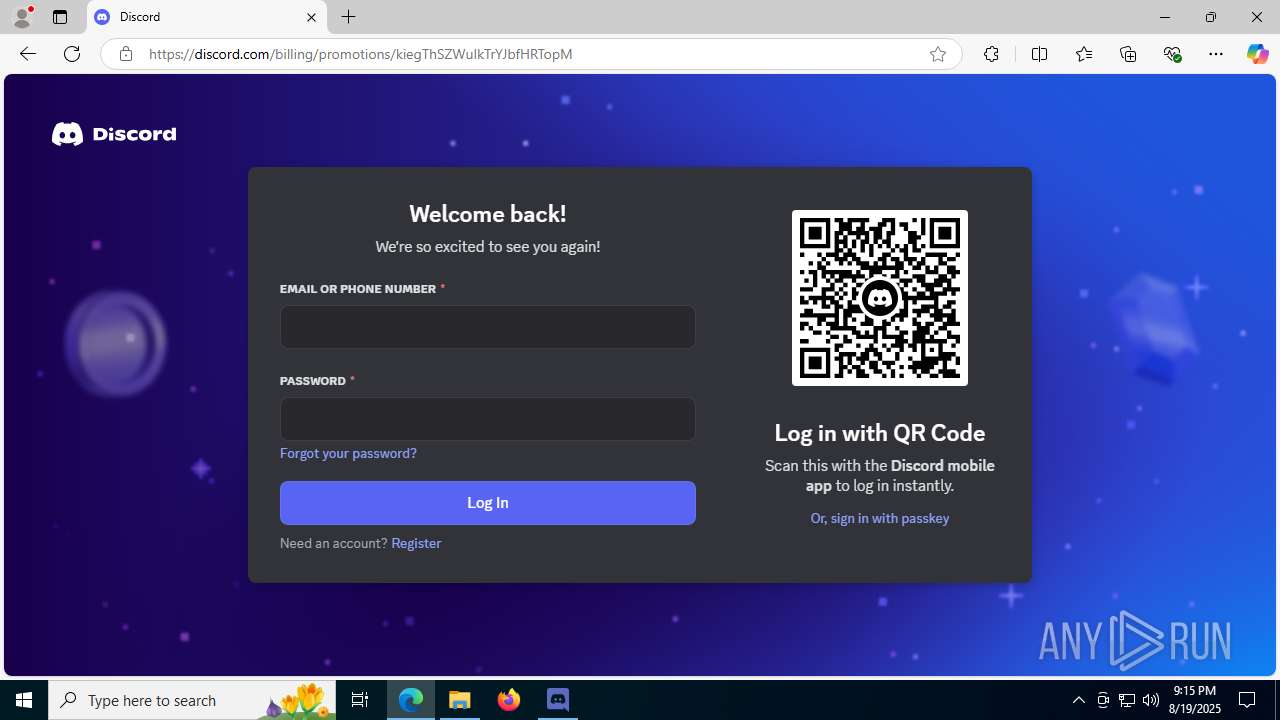
Attempting to use instant messaging service
- msedge.exe (PID: 4916)
- msedge.exe (PID: 6704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(5928) smlahost.exe
Discord-Webhook-Tokens (2)1375591644715421778/Jsmz3x0dfd0CafYMJEMSle9iQxo9M_nt2mf9W8bL49m_S4F5xyWwqFQQAKcfvI5imCUl
1375591089083252766/SSKLyirsu7hEQzS8ghv70WykqwCuZ21aw-oVUiGrsM7t2e6qoOtDBNtlGVakRLiDol6j
Discord-Info-Links
1375591644715421778/Jsmz3x0dfd0CafYMJEMSle9iQxo9M_nt2mf9W8bL49m_S4F5xyWwqFQQAKcfvI5imCUl
Get Webhook Infohttps://discord.com/api/webhooks/1375591644715421778/Jsmz3x0dfd0CafYMJEMSle9iQxo9M_nt2mf9W8bL49m_S4F5xyWwqFQQAKcfvI5imCUl
1375591089083252766/SSKLyirsu7hEQzS8ghv70WykqwCuZ21aw-oVUiGrsM7t2e6qoOtDBNtlGVakRLiDol6j
Get Webhook Infohttps://discord.com/api/webhooks/1375591089083252766/SSKLyirsu7hEQzS8ghv70WykqwCuZ21aw-oVUiGrsM7t2e6qoOtDBNtlGVakRLiDol6j
Total processes
248
Monitored processes
90
Malicious processes
0
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --always-read-main-dll --field-trial-handle=6324,i,12843740090424408218,15068313170238099141,262144 --variations-seed-version --mojo-platform-channel-handle=1604 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://l1nq.com/DjGyY" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=4620,i,12843740090424408218,15068313170238099141,262144 --variations-seed-version --mojo-platform-channel-handle=8672 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4632,i,12843740090424408218,15068313170238099141,262144 --variations-seed-version --mojo-platform-channel-handle=7380 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --always-read-main-dll --field-trial-handle=1480,i,12843740090424408218,15068313170238099141,262144 --variations-seed-version --mojo-platform-channel-handle=7024 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=1868,i,12843740090424408218,15068313170238099141,262144 --variations-seed-version --mojo-platform-channel-handle=1800 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1468 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5344,i,12843740090424408218,15068313170238099141,262144 --variations-seed-version --mojo-platform-channel-handle=6748 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\smlahost module\smlahost.exe" initialinstalling | C:\Program Files (x86)\smlahost module\smlahost.exe | 0xc0312199.exe | ||||||||||||
User: admin Company: smlahost service offset Integrity Level: HIGH Description: smlahost Version: 10.0.21718.22 Modules
| |||||||||||||||
| 1880 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2752,i,14653156202023407832,12721296771112678721,262144 --variations-seed-version --mojo-platform-channel-handle=2588 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1964 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --always-read-main-dll --field-trial-handle=6688,i,12843740090424408218,15068313170238099141,262144 --variations-seed-version --mojo-platform-channel-handle=4748 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
24 547
Read events
24 412
Write events
126
Delete events
9
Modification events
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590586 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E19BBA94-9206-45B8-A06D-C65404CFC77F} | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 633A1994549B2F00 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590586 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9B5ED8C1-171F-4E5E-845B-B5D56A6AFD54} | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590586 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D8A4D358-B93F-4D93-9525-C2323CF11028} | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590586 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DB73B9A8-63C3-4523-BBE9-A02AD731CF42} | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
47
Suspicious files
884
Text files
175
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d8f6.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d8e6.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d8e6.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d905.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d905.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
412
DNS requests
531
Threats
50
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8008 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/550117a4-8c0f-4d0d-8ff8-7c3caccb0e8a?P1=1756109235&P2=404&P3=2&P4=GUGmxj7gY0qM3J43p%2fVZ0OelSns2lFnE2DoGCE2DEG0l3rzP8f9qrPeEW6YlAJJqKBDRZQRWMoJkkVw6gefHWQ%3d%3d | DE | binary | 2.98 Kb | whitelisted |
8008 | svchost.exe | GET | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/550117a4-8c0f-4d0d-8ff8-7c3caccb0e8a?P1=1756109235&P2=404&P3=2&P4=GUGmxj7gY0qM3J43p%2fVZ0OelSns2lFnE2DoGCE2DEG0l3rzP8f9qrPeEW6YlAJJqKBDRZQRWMoJkkVw6gefHWQ%3d%3d | DE | binary | 6.24 Kb | whitelisted |
8008 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1756109224&P2=404&P3=2&P4=FzkqxR%2fu15EiABA8RFXl9Te2n9%2b3HteeQJLnWdUIMIX3wJ5y4GgjqNcgevAThYhniEjYl91fJsJj7rU7R3%2bUJQ%3d%3d | DE | binary | 6.24 Kb | whitelisted |
7788 | WerFault.exe | GET | 200 | 23.216.77.5:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
7788 | WerFault.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
8008 | svchost.exe | GET | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ad7d1123-5b48-4c00-8f9e-492599630d8d?P1=1756112826&P2=404&P3=2&P4=cdMVgHQx1rrnJpslGikvMXabqWDE81X27NZ0T4wVYGokU1dipTt0%2fW3hAsRvMJCnAuHKPMw3CnMXiXSHjo%2fh7Q%3d%3d | DE | binary | 18.4 Kb | whitelisted |
8008 | svchost.exe | GET | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1756109224&P2=404&P3=2&P4=FzkqxR%2fu15EiABA8RFXl9Te2n9%2b3HteeQJLnWdUIMIX3wJ5y4GgjqNcgevAThYhniEjYl91fJsJj7rU7R3%2bUJQ%3d%3d | DE | binary | 7.71 Kb | whitelisted |
8008 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ad7d1123-5b48-4c00-8f9e-492599630d8d?P1=1756112826&P2=404&P3=2&P4=cdMVgHQx1rrnJpslGikvMXabqWDE81X27NZ0T4wVYGokU1dipTt0%2fW3hAsRvMJCnAuHKPMw3CnMXiXSHjo%2fh7Q%3d%3d | DE | binary | 7.71 Kb | whitelisted |
4916 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:64LveXRkf4fuRr9XtJY_GvH5zVoUnKE04zxkFzkVpDo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 97 b | whitelisted |
592 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4460 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4916 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4916 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4916 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4916 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
4916 | msedge.exe | 198.49.23.145:443 | l1nq.com | SQUARESPACE | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
l1nq.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
encurtador.dev |
| unknown |
www.encurtador.dev |
| unknown |
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
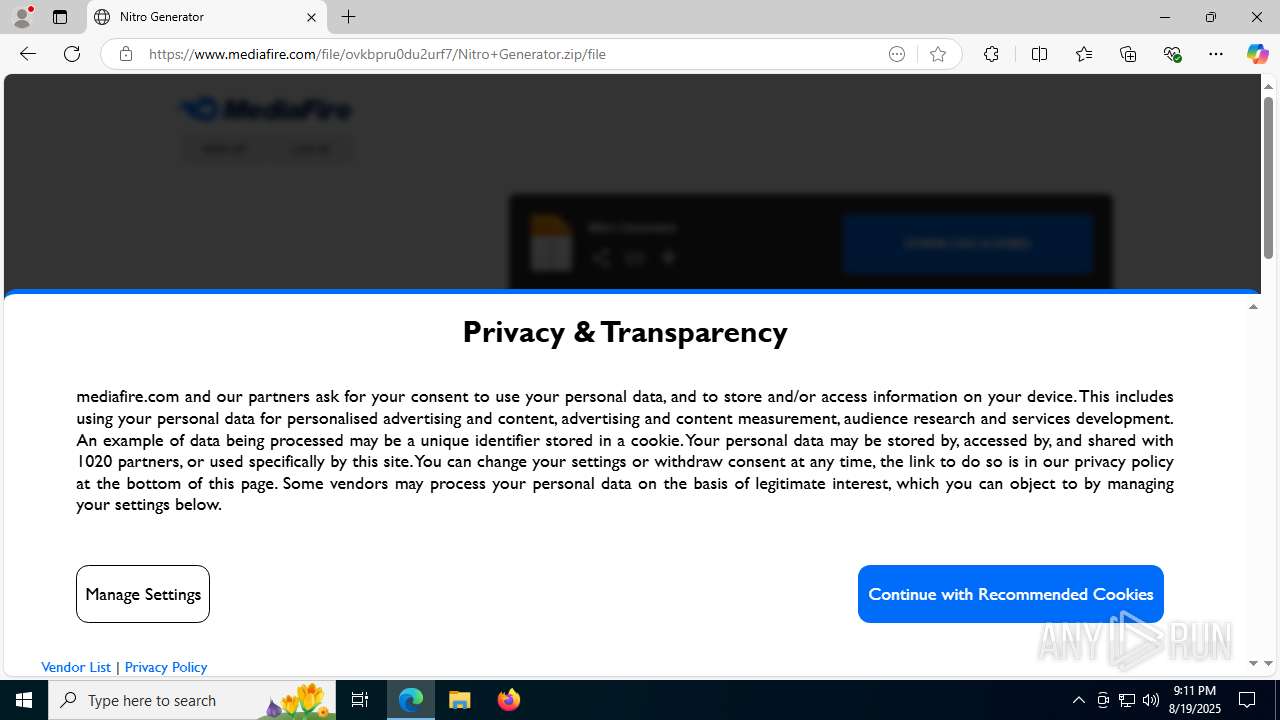
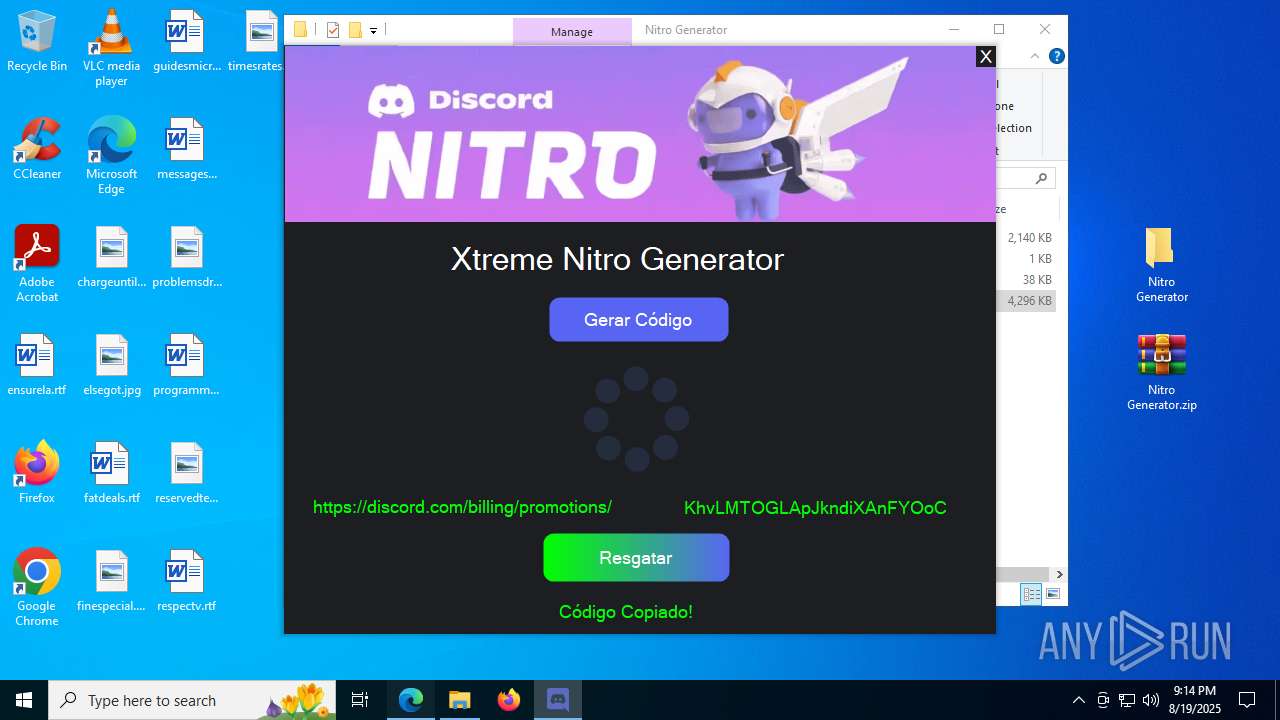
4916 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
4916 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
4916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
4916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
4916 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
4916 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |