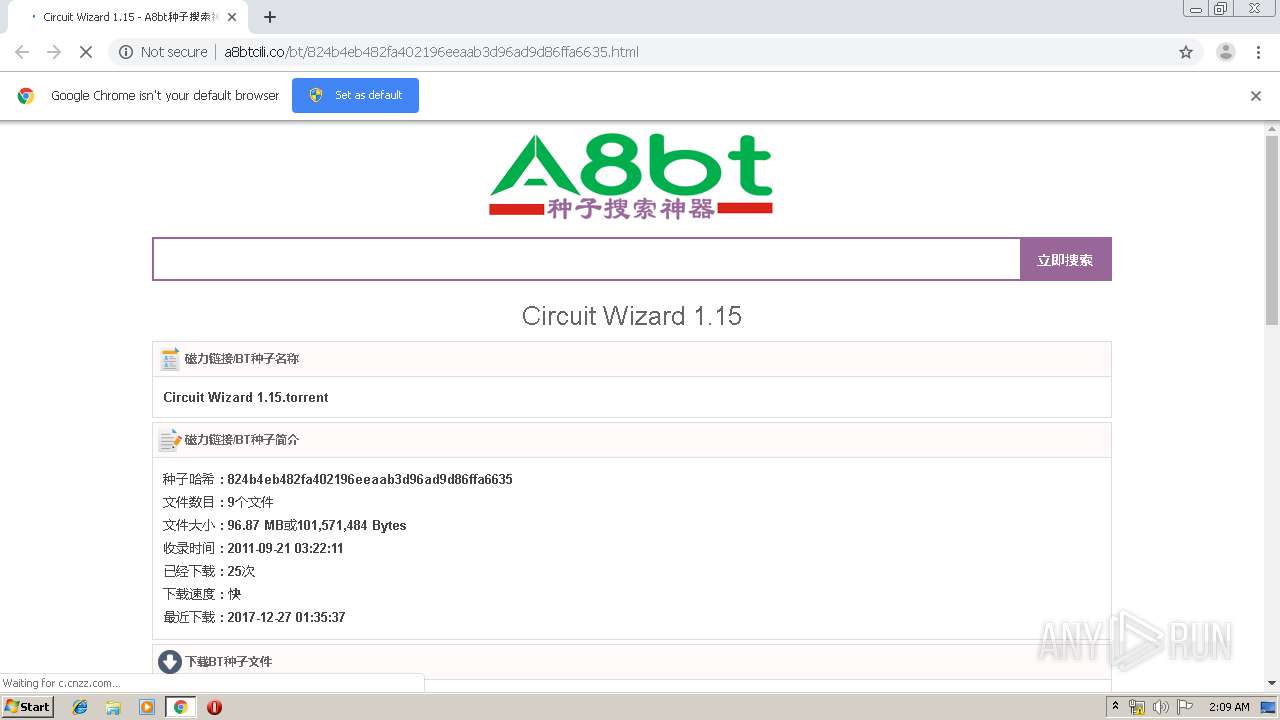
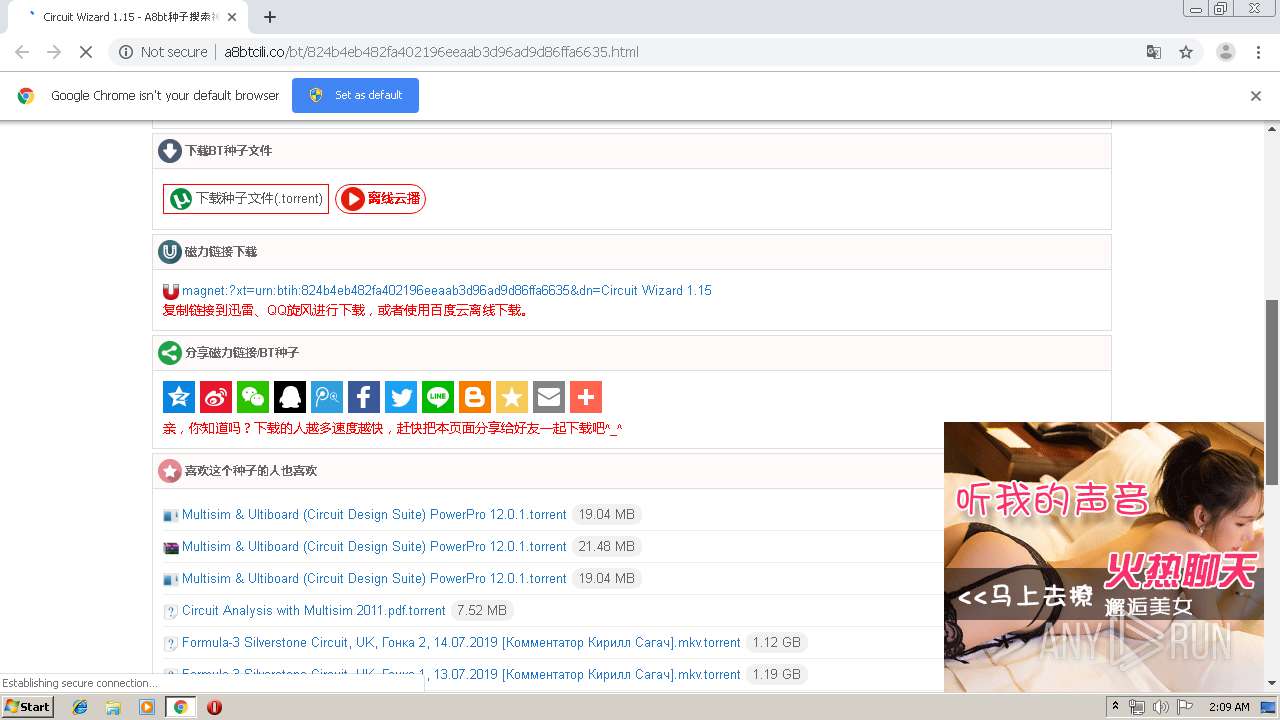
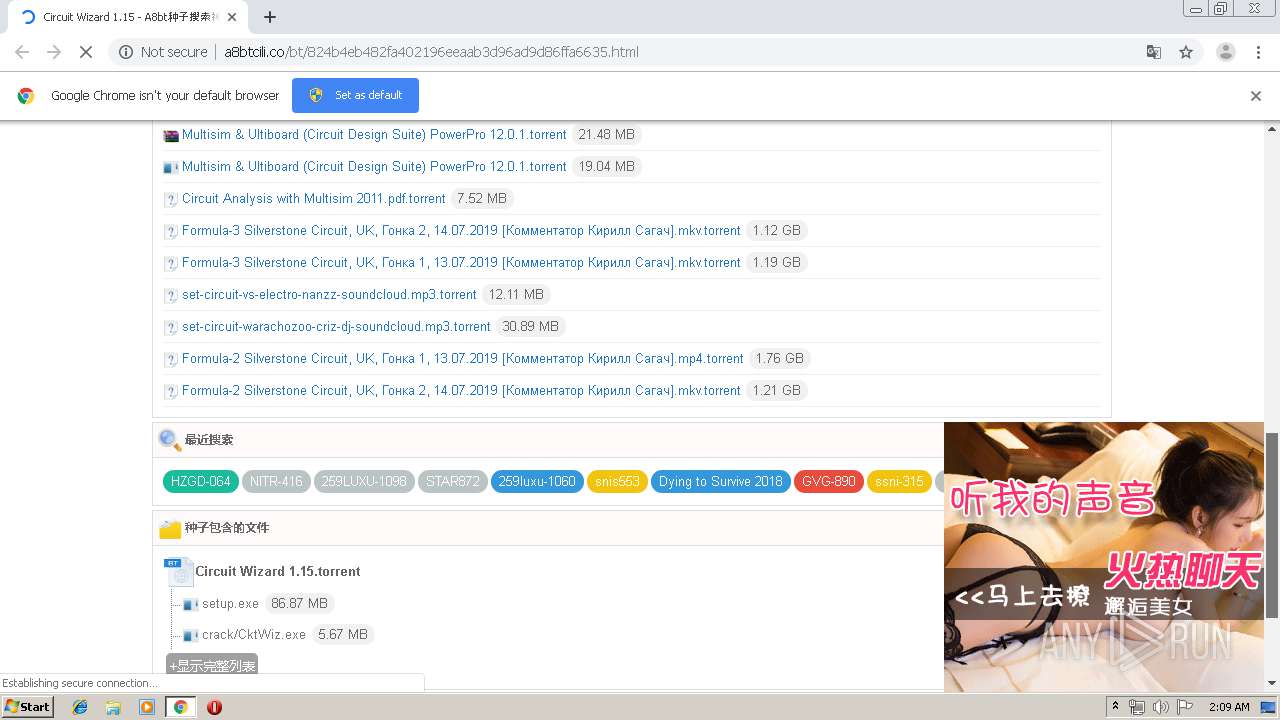
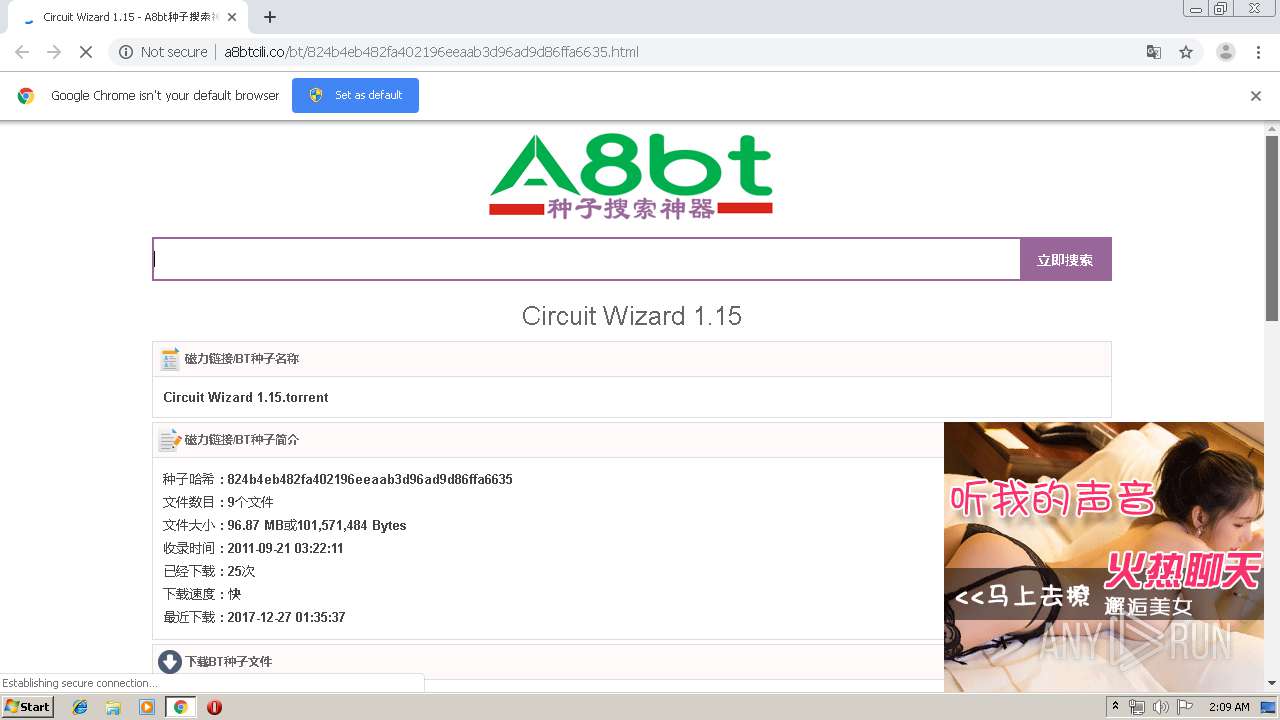
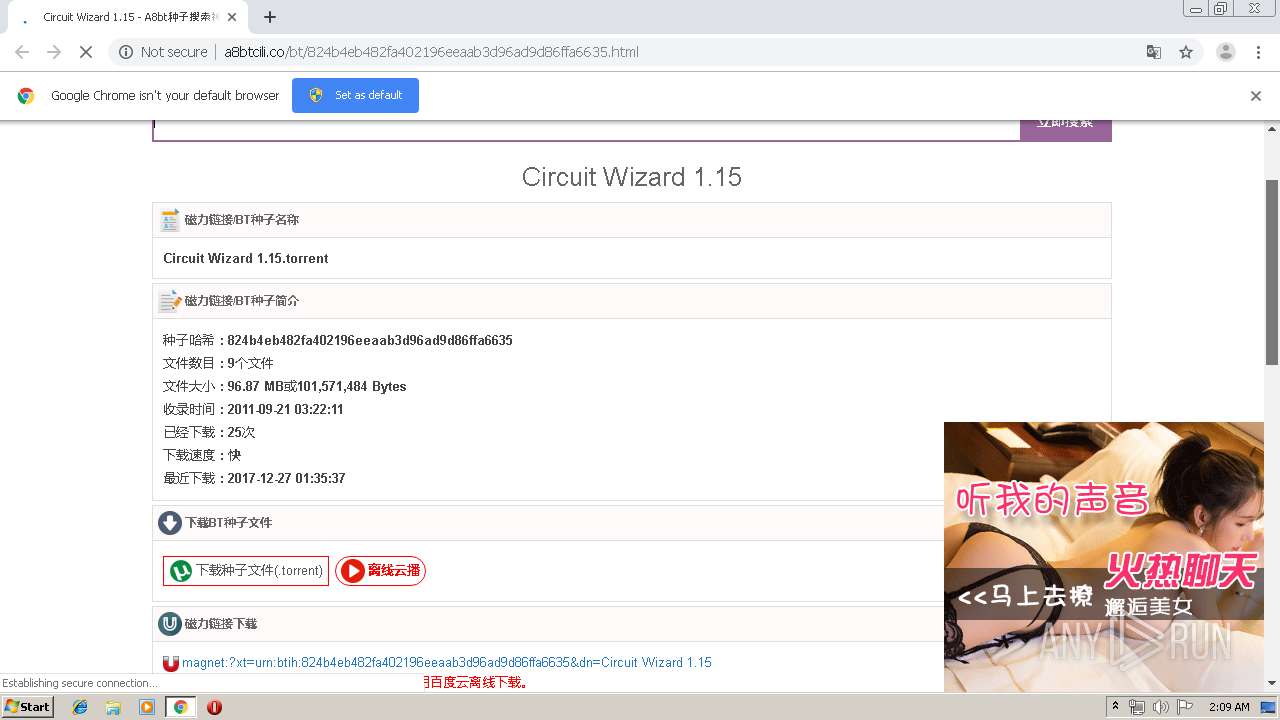
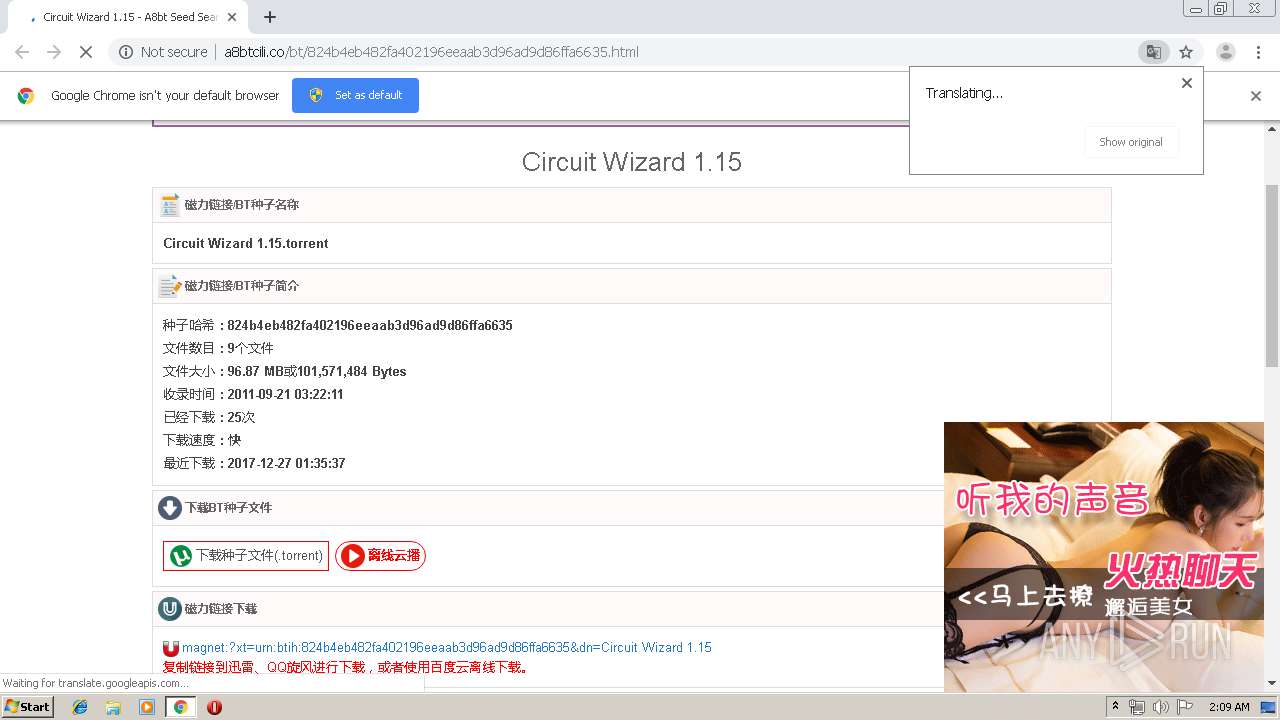
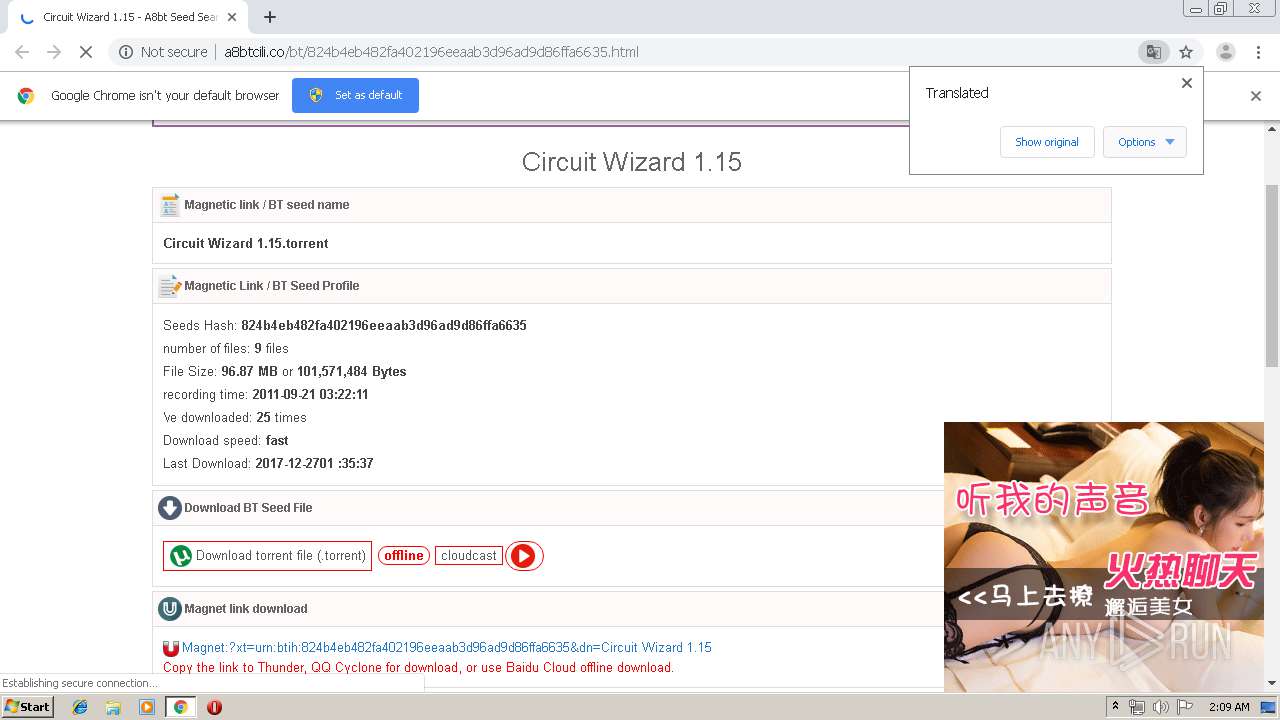
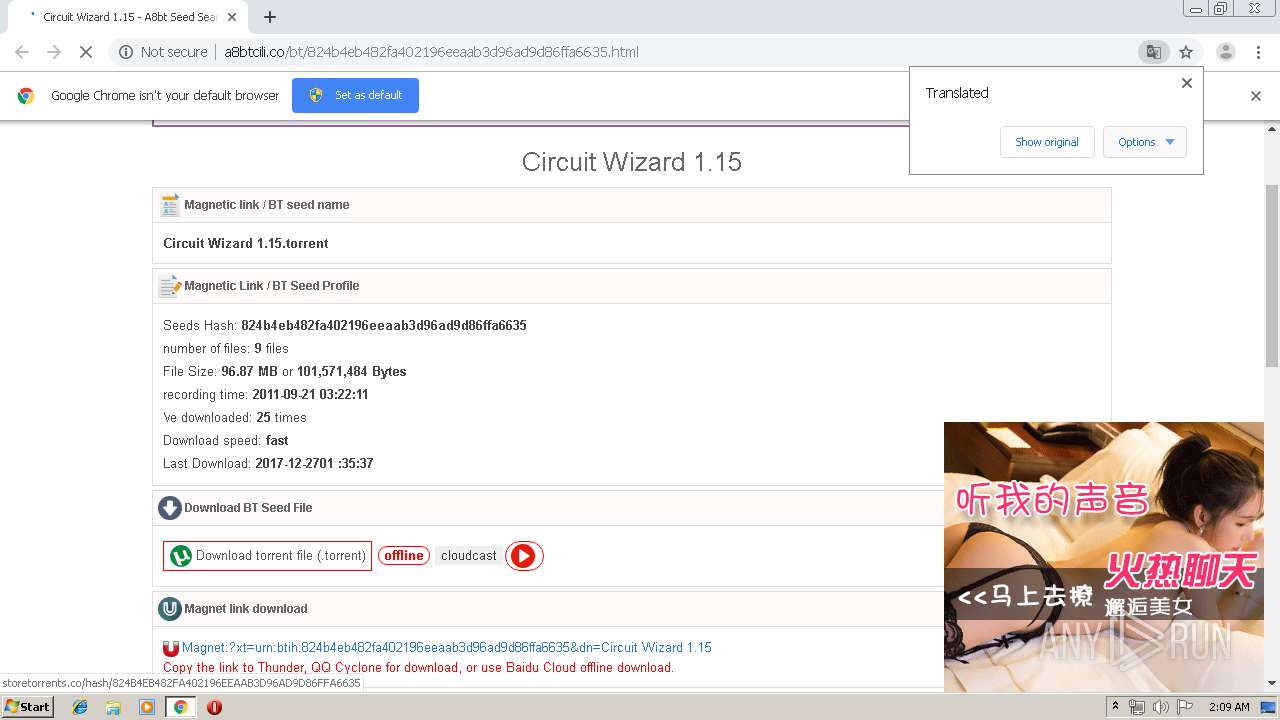
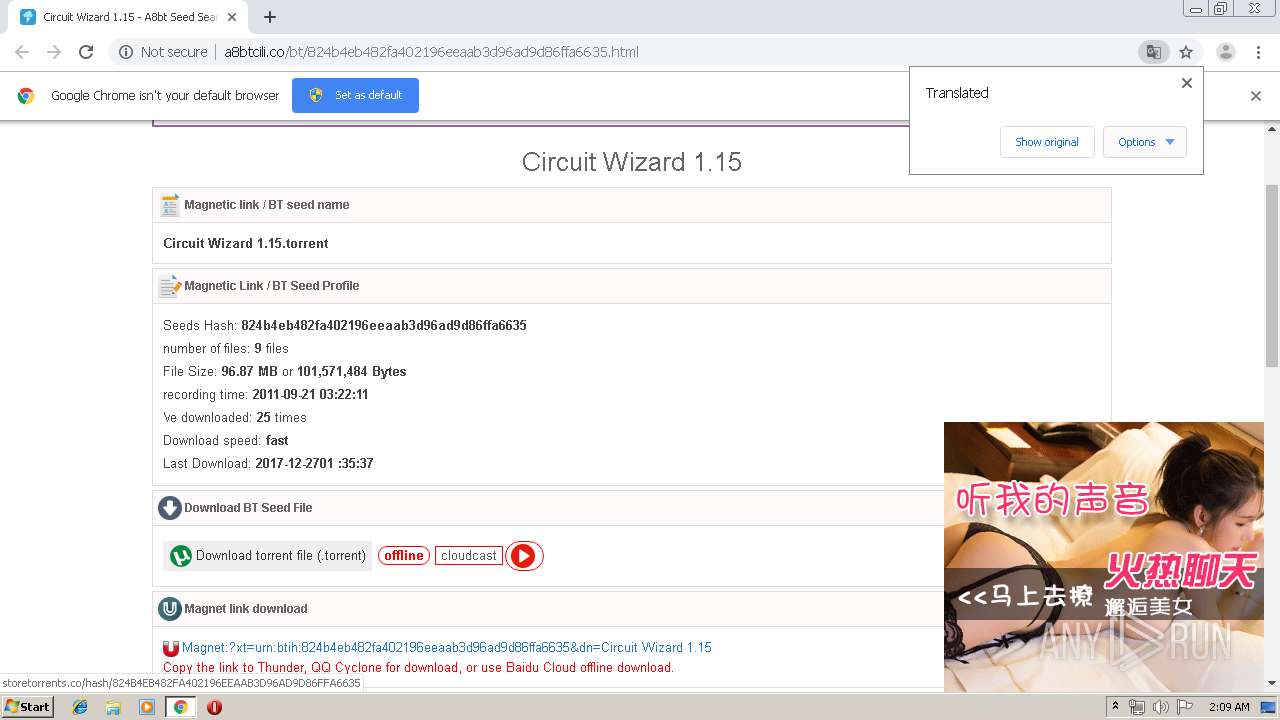
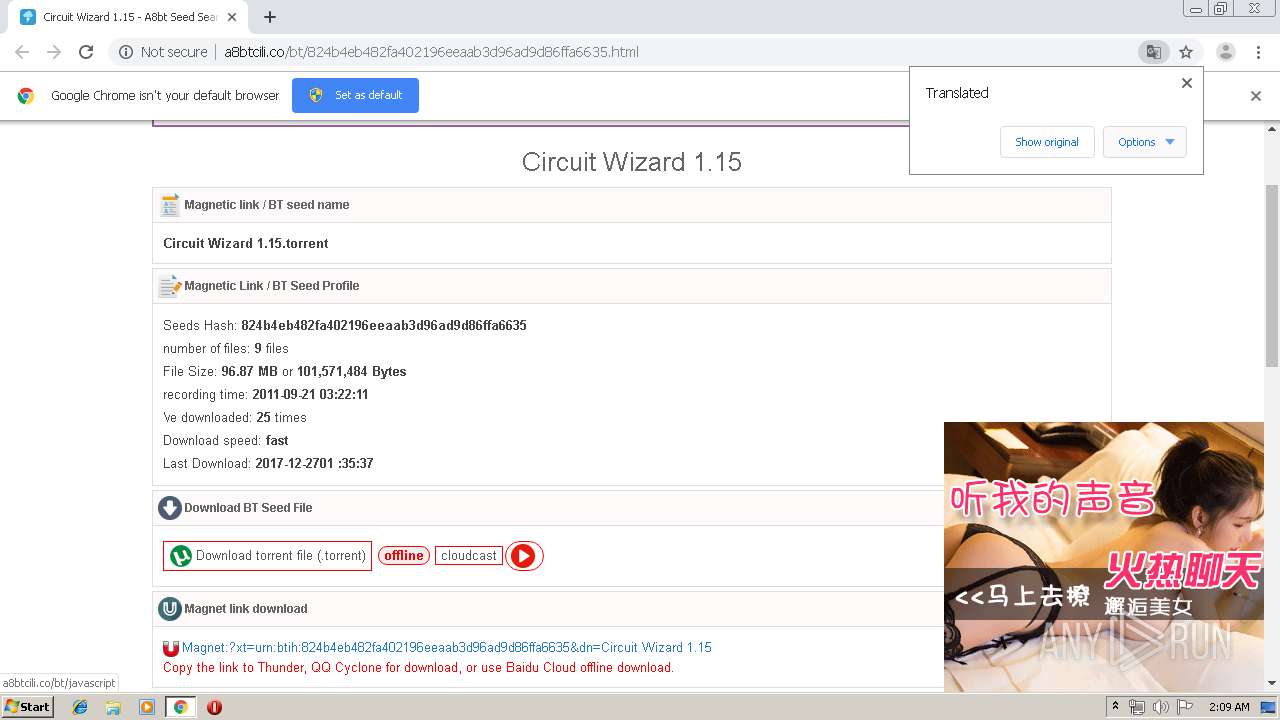
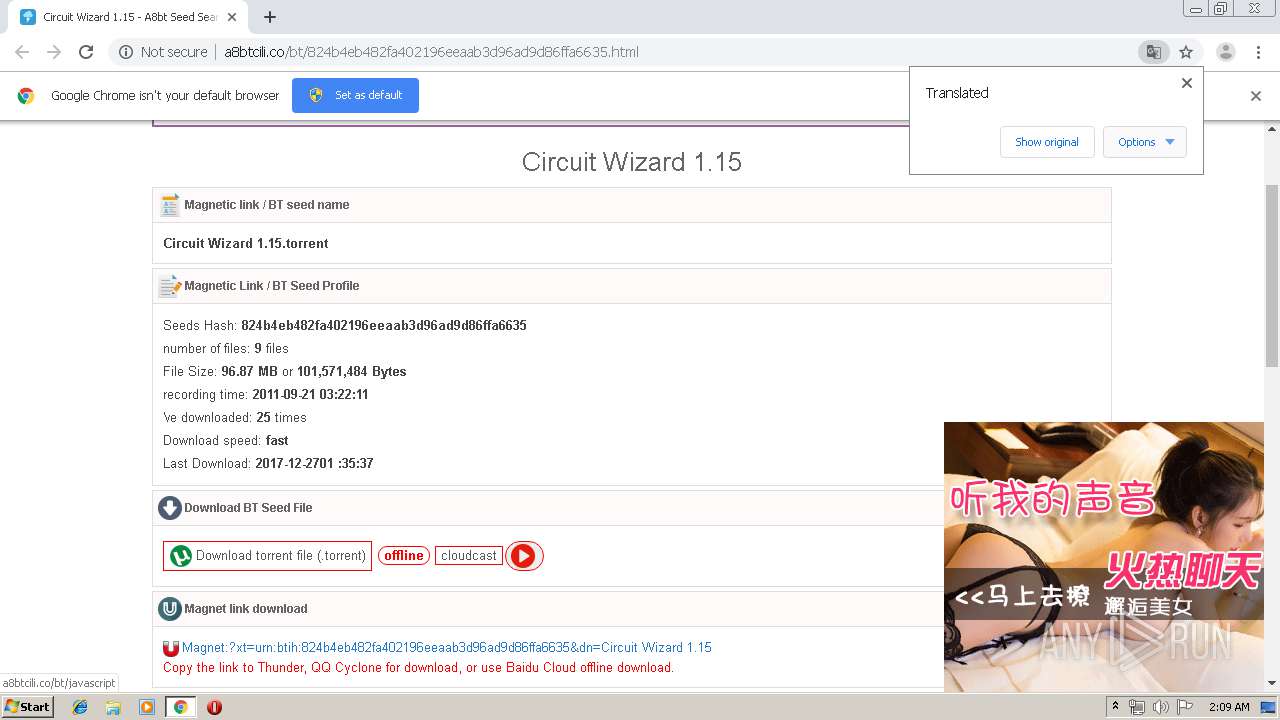
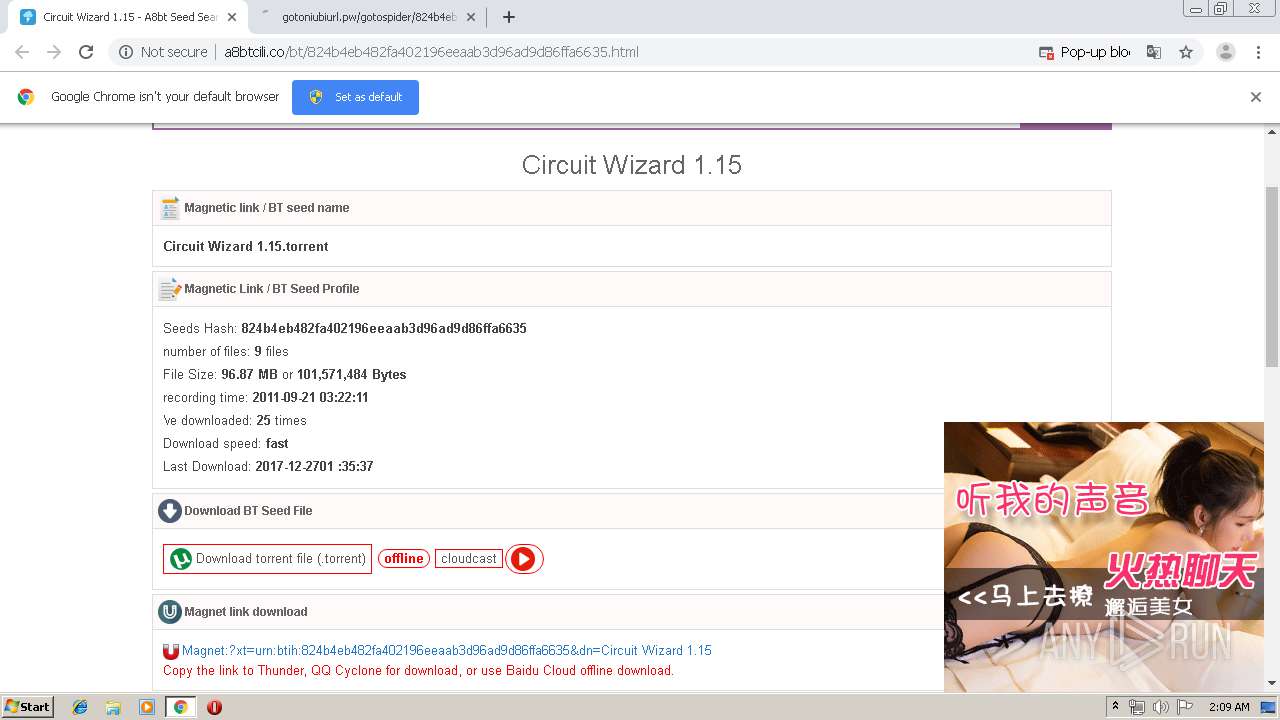
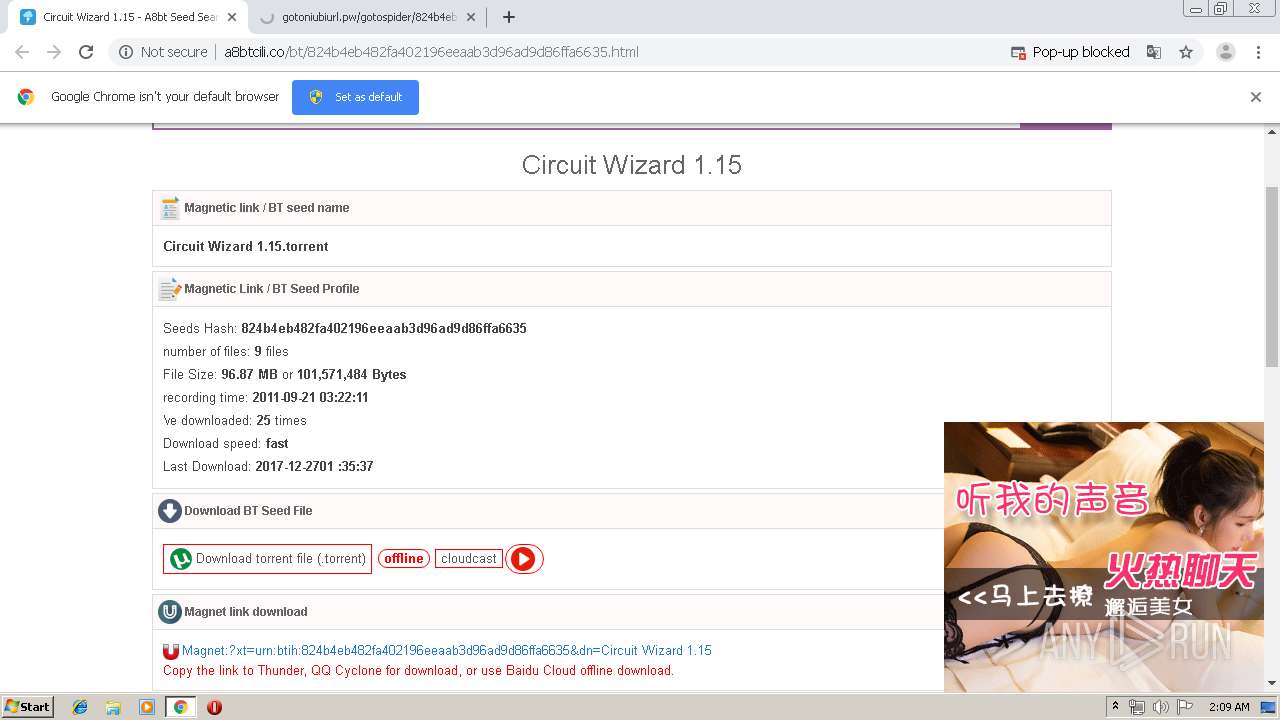
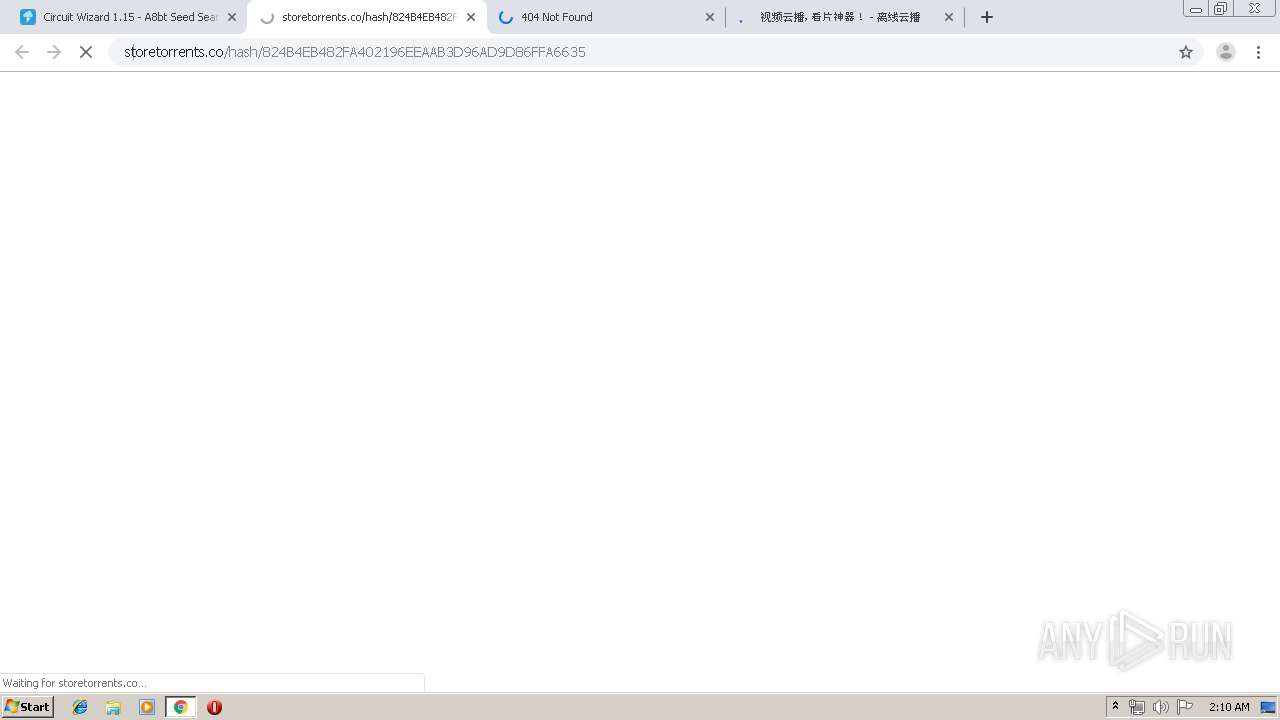
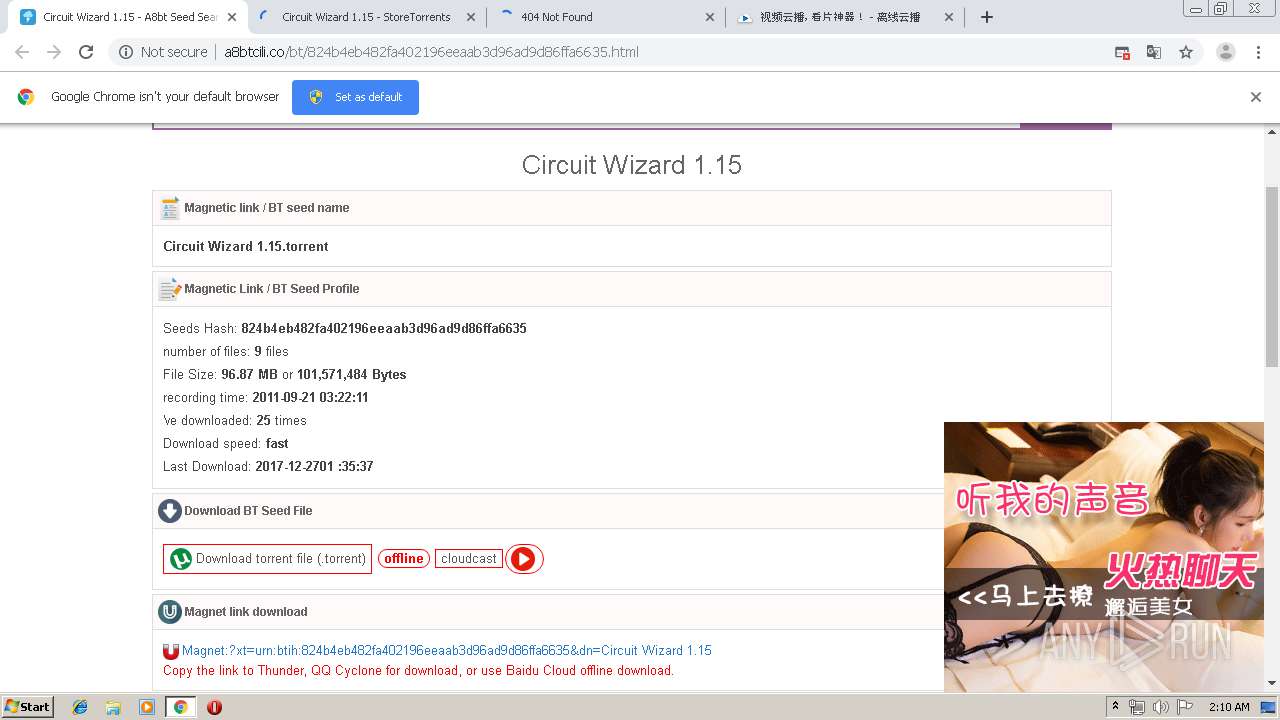
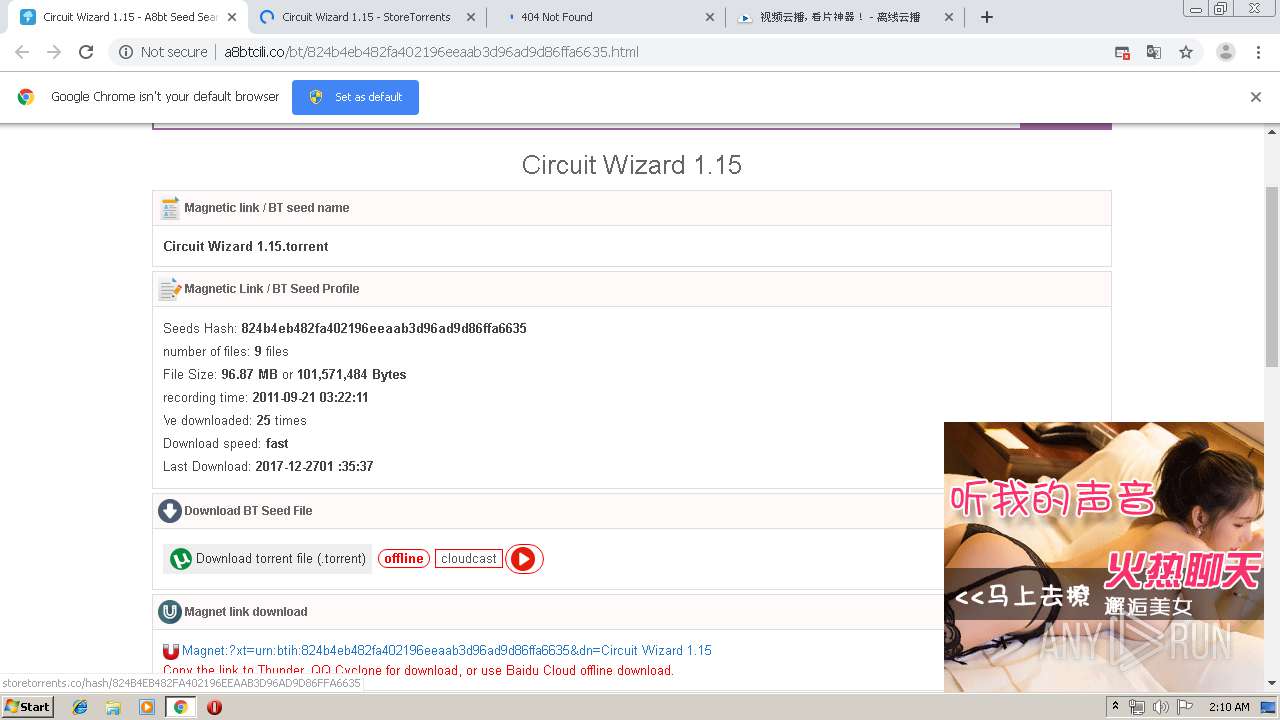
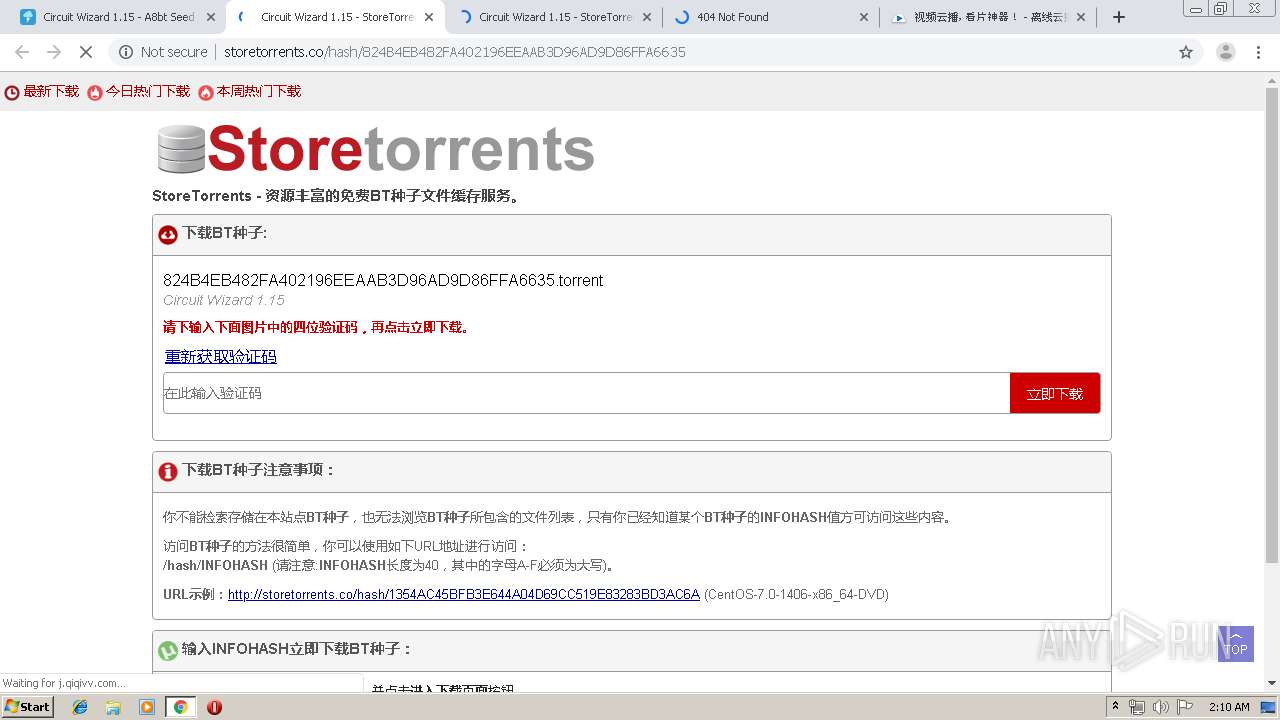
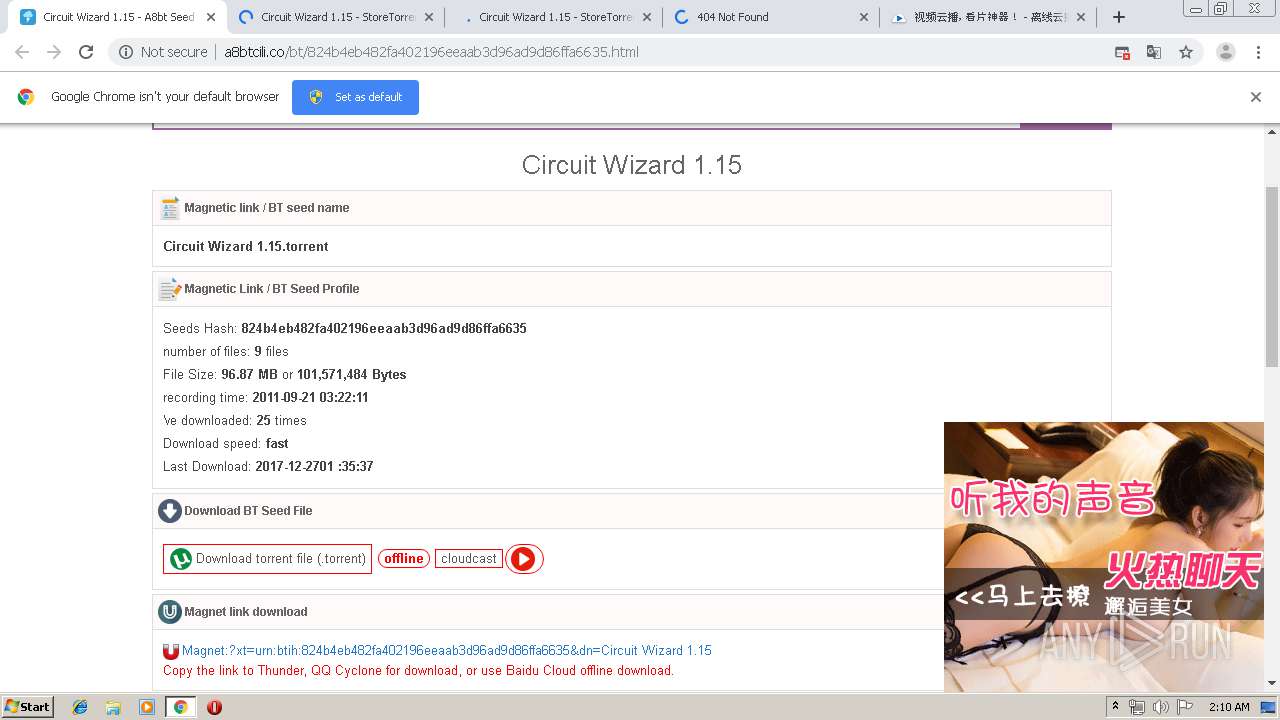
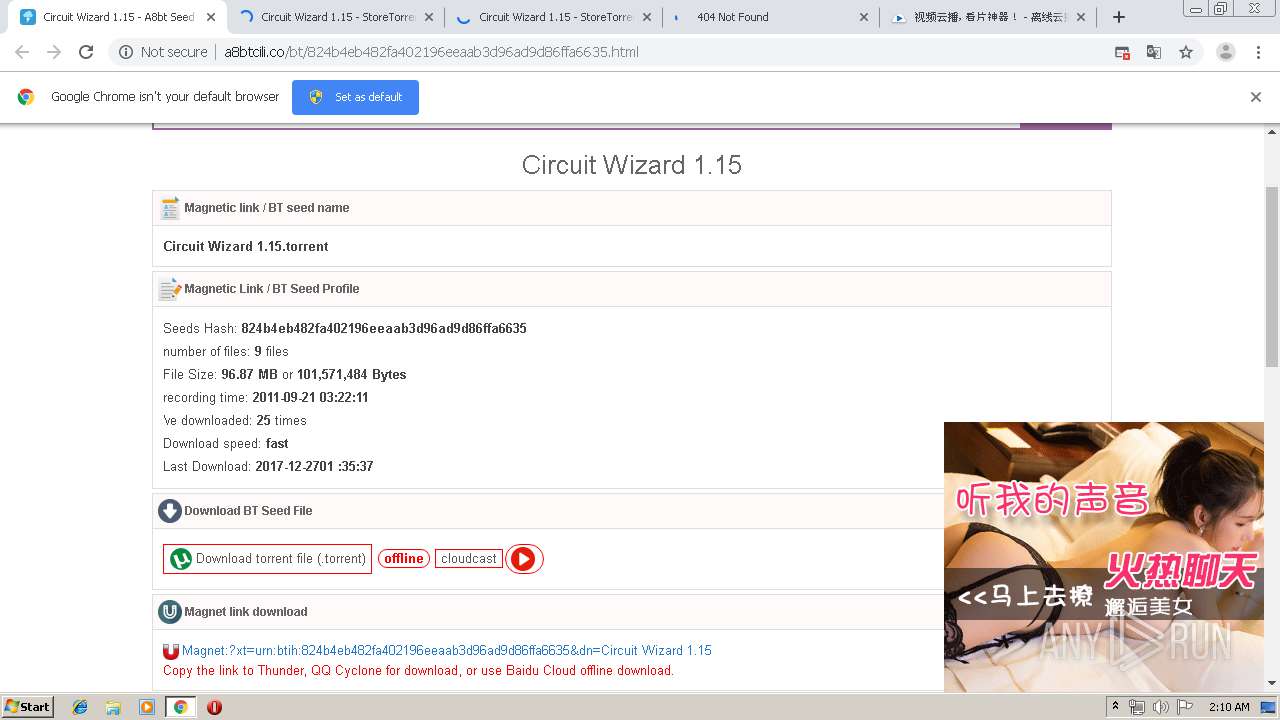
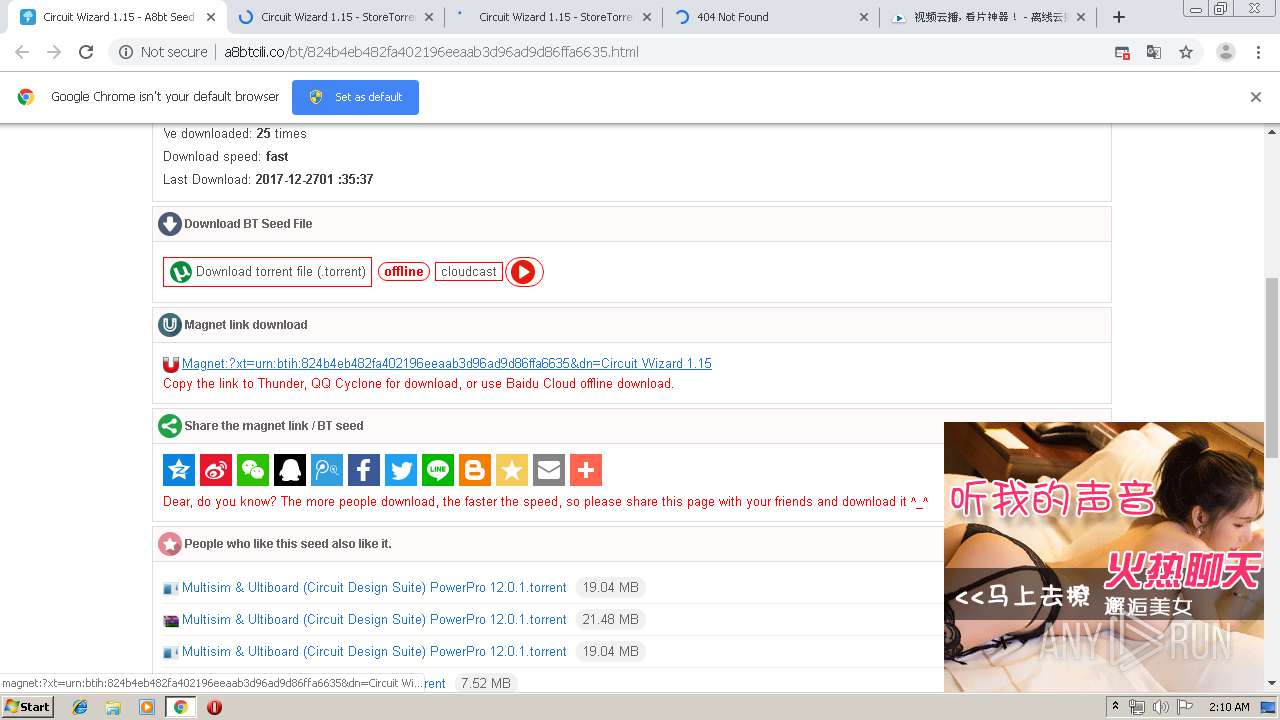
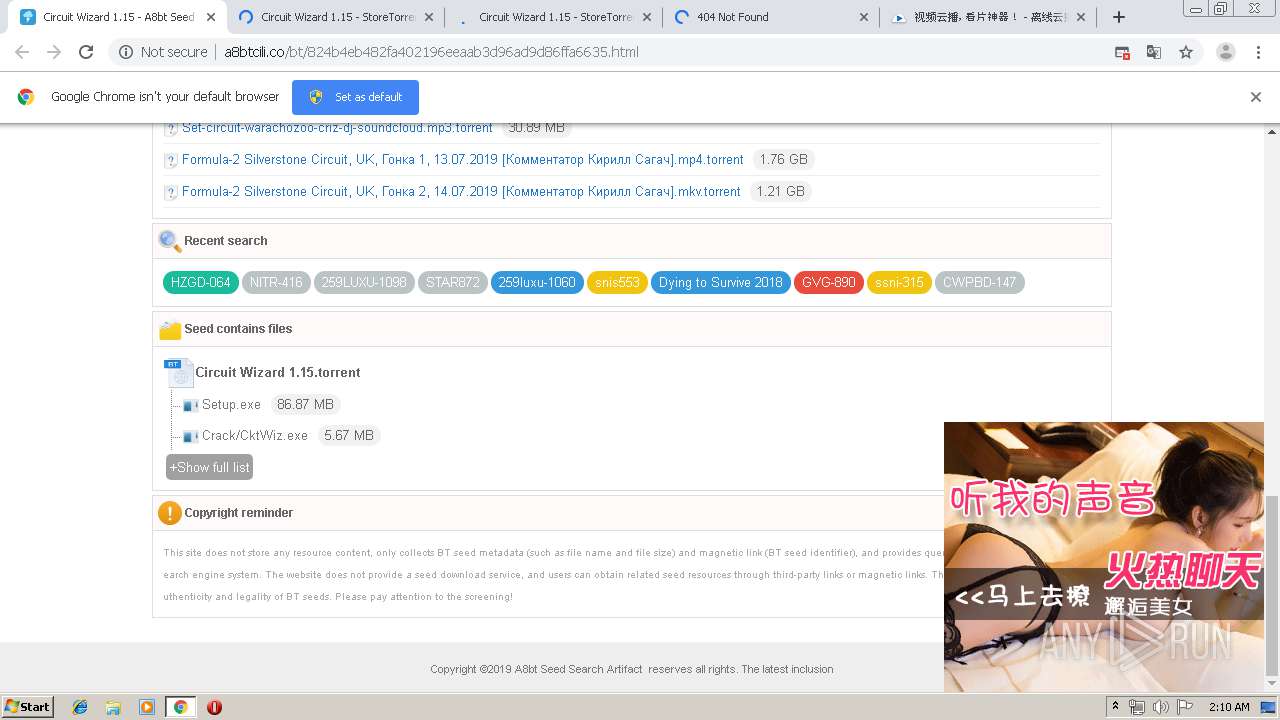
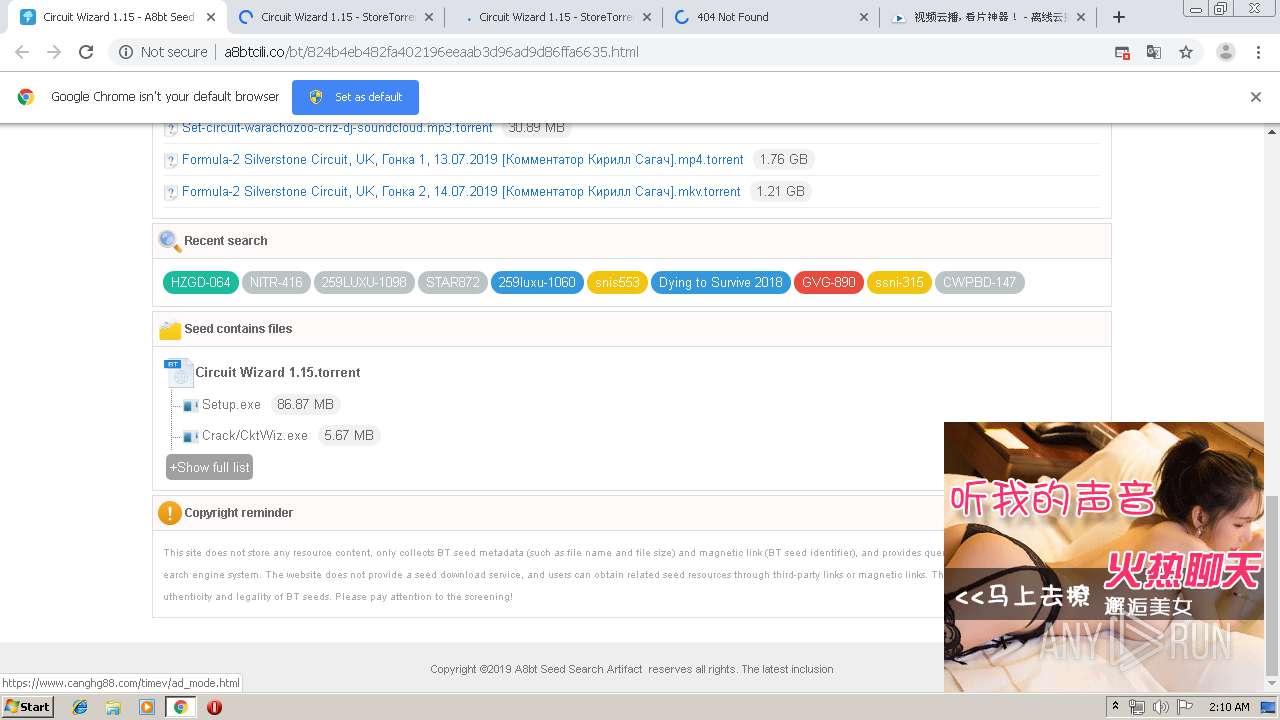
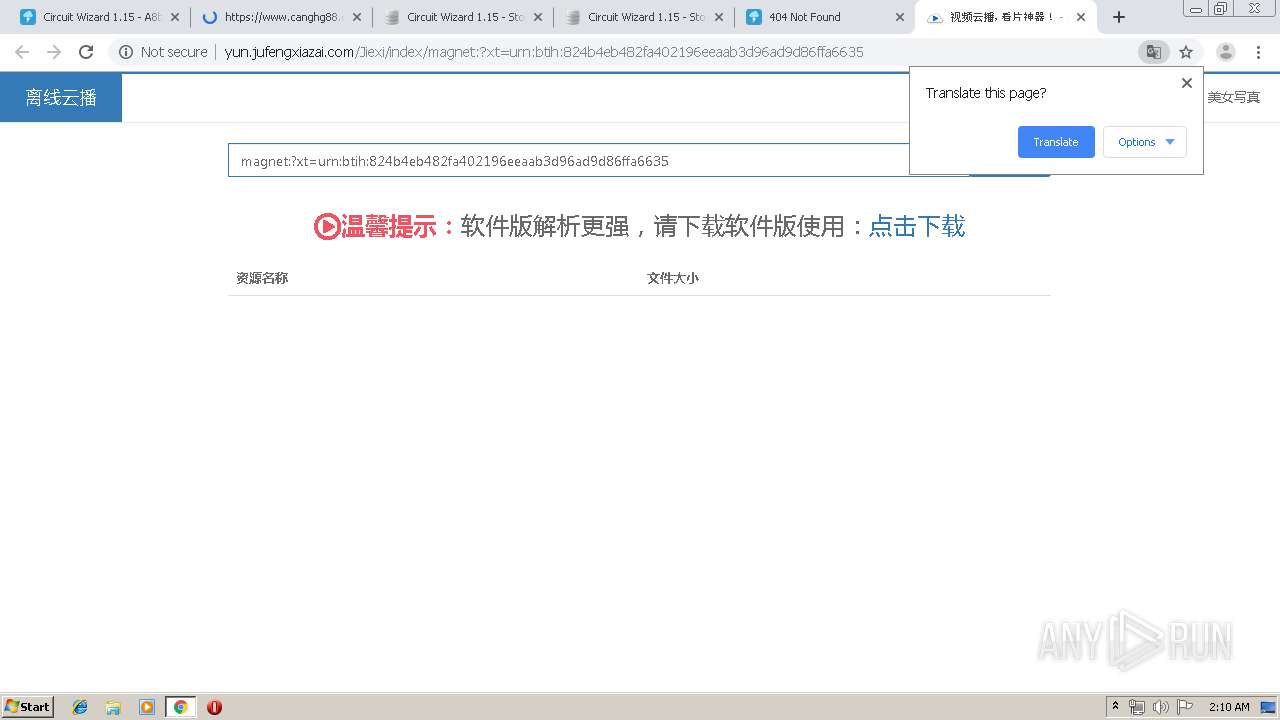
| URL: | http://a8btcili.co/bt/824b4eb482fa402196eeaab3d96ad9d86ffa6635.html |
| Full analysis: | https://app.any.run/tasks/dda3005b-1956-4d7f-92ef-85d6a990af1a |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 01:08:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2F35F481F7A43E7D5B02D4AF3B65E014 |
| SHA1: | 7F878CC01AFC94025037A71CA3638A7CBDB53E46 |
| SHA256: | AAEDF9A3009462568037E873EAE106C6B72AAA0F78B6FE83FF21BB7B46992C95 |
| SSDEEP: | 3:N1KfrbCXO4MhE2BnBoPDyQn:CHiO4yZBnBiJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
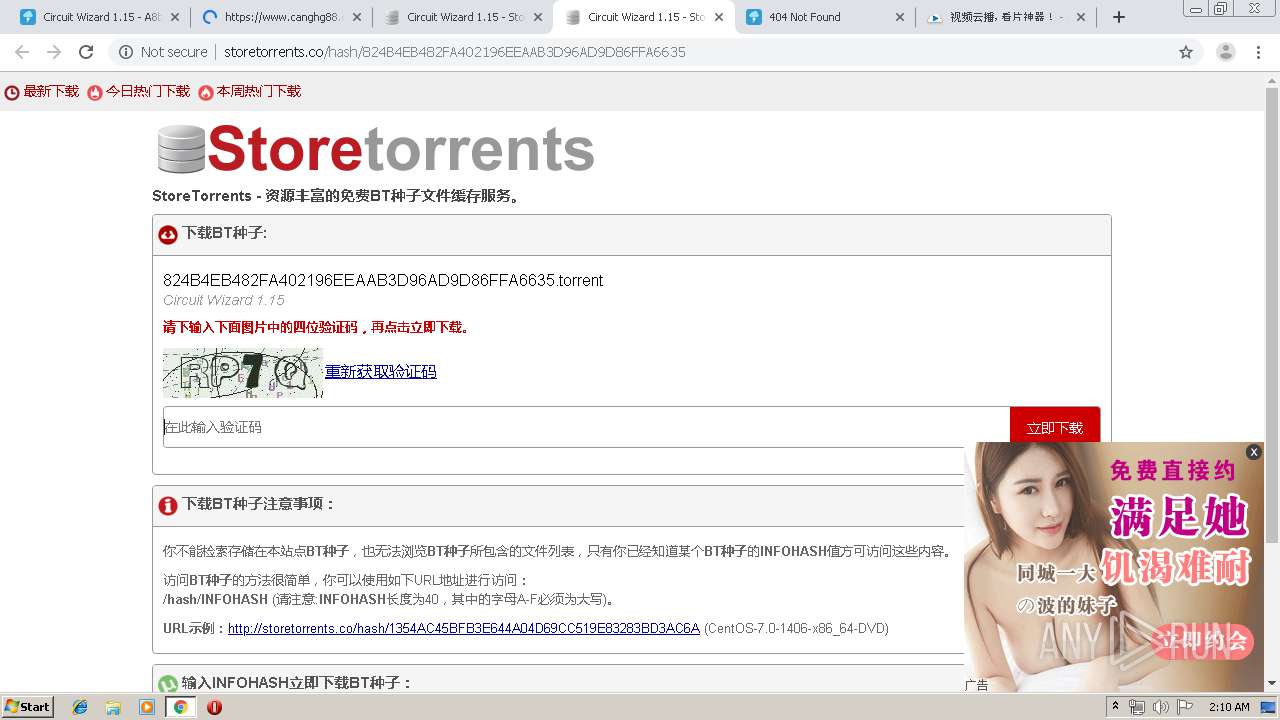
Modifies files in Chrome extension folder
- chrome.exe (PID: 2900)
INFO
Application launched itself
- chrome.exe (PID: 2900)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
32
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,18326130933547670040,8873278233659060796,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7523611305043086320 --mojo-platform-channel-handle=4308 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,18326130933547670040,8873278233659060796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6821205463379790423 --mojo-platform-channel-handle=1940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,18326130933547670040,8873278233659060796,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5209348977924402404 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,18326130933547670040,8873278233659060796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1865927247270415237 --mojo-platform-channel-handle=1500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,18326130933547670040,8873278233659060796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9163184882484179531 --mojo-platform-channel-handle=3752 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,18326130933547670040,8873278233659060796,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1018386285602572044 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=976,18326130933547670040,8873278233659060796,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=1397009306181394454 --mojo-platform-channel-handle=4304 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2904 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,18326130933547670040,8873278233659060796,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=173370488990928635 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,18326130933547670040,8873278233659060796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2480390531275281823 --mojo-platform-channel-handle=3956 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
636
Read events
552
Write events
80
Delete events
4
Modification events
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2900-13207885731219375 |
Value: 259 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
125
Text files
194
Unknown types
53
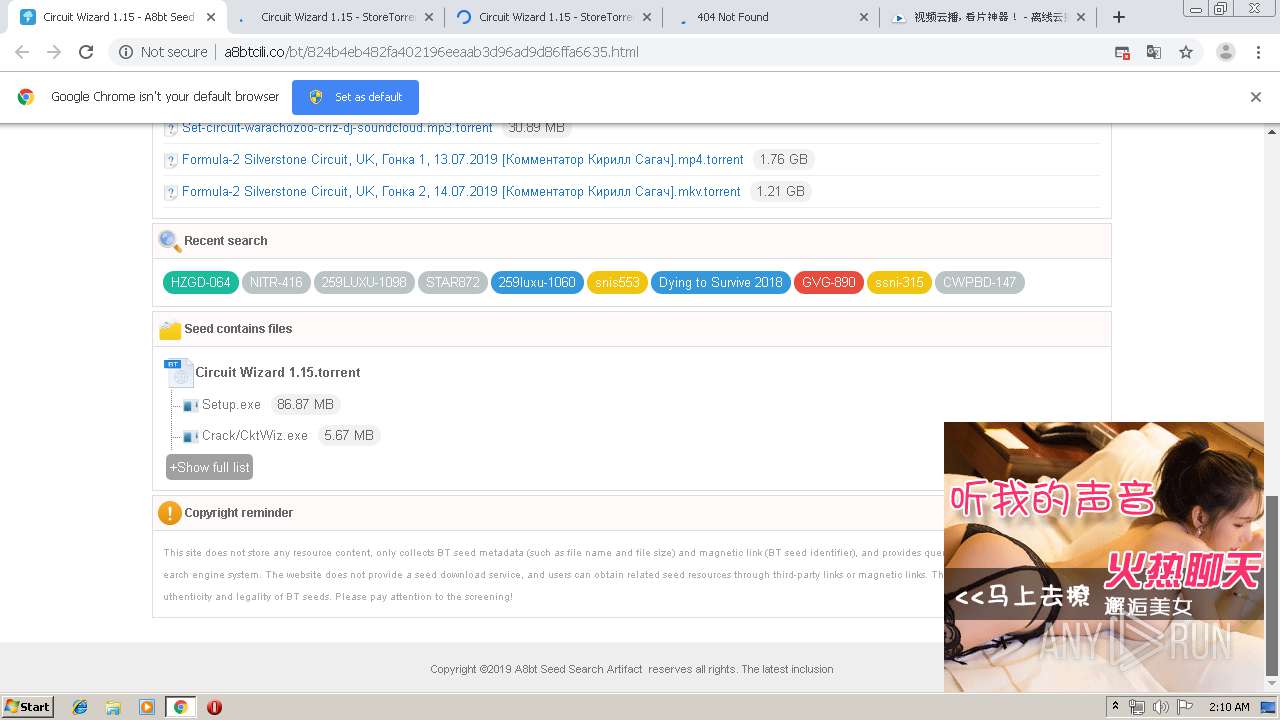
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8ba9f607-c28f-4597-b781-53ad5b50bda5.tmp | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF17ad09.TMP | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17abd0.TMP | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF17abe0.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
98
TCP/UDP connections
126
DNS requests
71
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
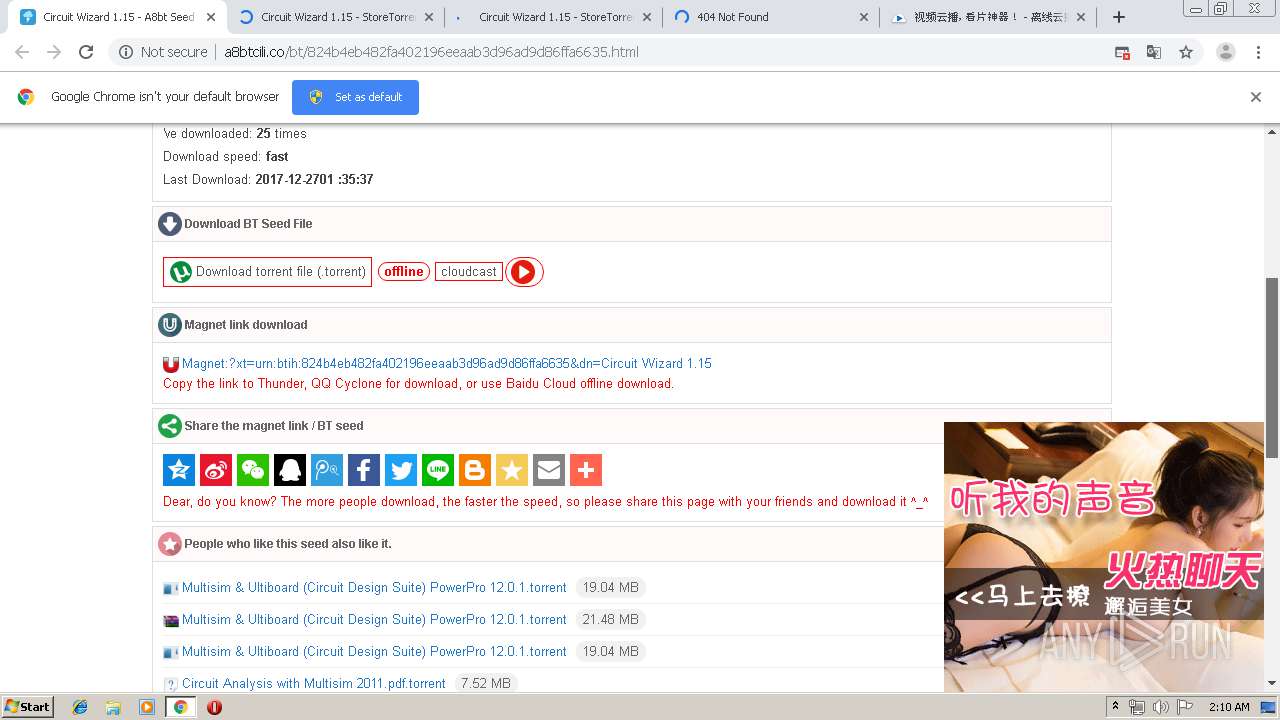
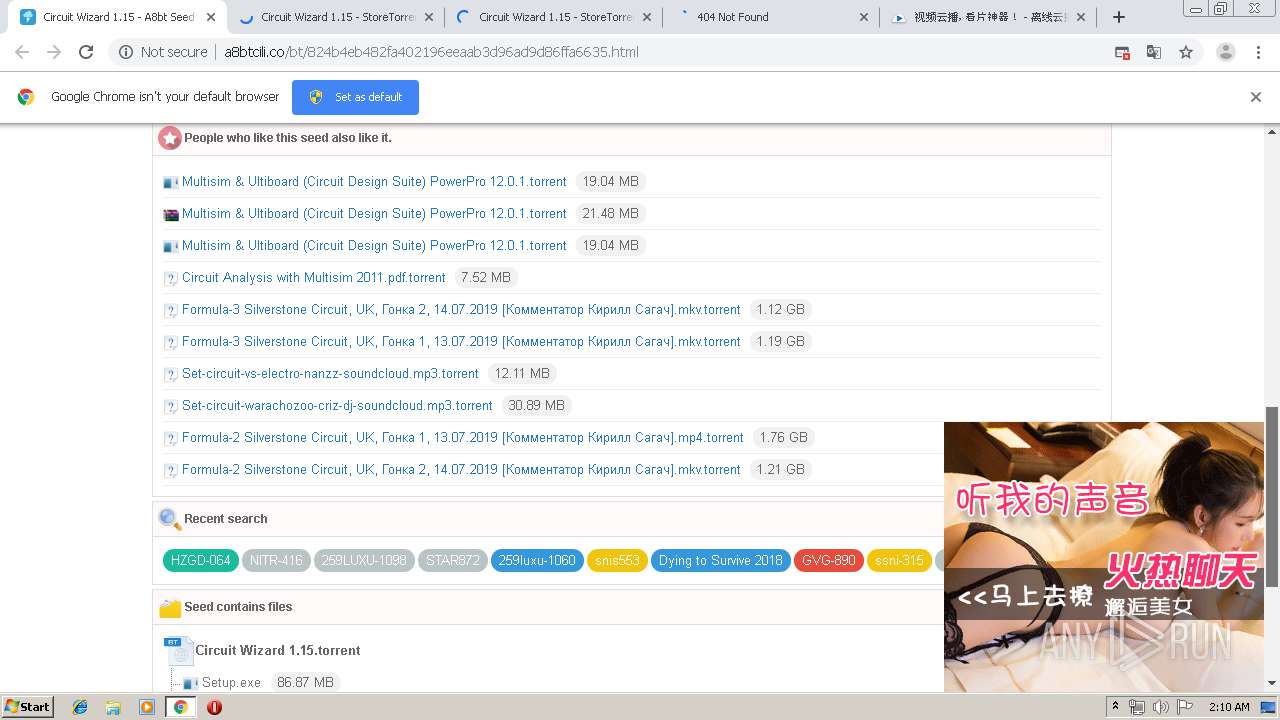
2284 | chrome.exe | GET | 200 | 104.31.64.111:80 | http://a8btcili.co/images/torrent_name.png | US | image | 2.17 Kb | shared |
2284 | chrome.exe | GET | 200 | 104.31.64.111:80 | http://a8btcili.co/images/share.png | US | image | 2.88 Kb | shared |
2284 | chrome.exe | GET | 200 | 104.31.64.111:80 | http://a8btcili.co/images/down.png | US | image | 1.56 Kb | shared |
2284 | chrome.exe | GET | 200 | 104.31.64.111:80 | http://a8btcili.co/images/ext/text.png | US | image | 2.53 Kb | shared |
2284 | chrome.exe | GET | 200 | 104.31.64.111:80 | http://a8btcili.co/images/torrent.png | US | image | 2.10 Kb | shared |
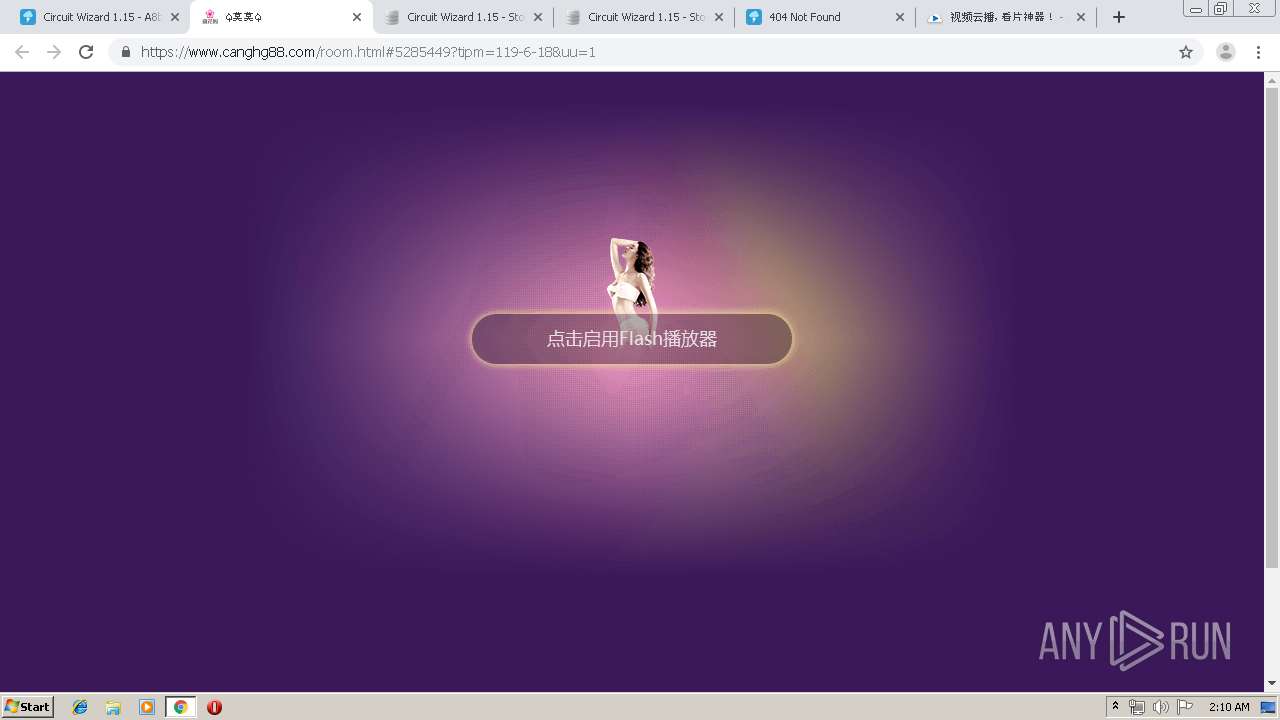
2284 | chrome.exe | GET | 200 | 104.27.161.240:80 | http://gotoniubiurl.pw/play.png | US | image | 2.31 Kb | suspicious |
2284 | chrome.exe | GET | 200 | 2.21.36.164:80 | http://s7.addthis.com/js/300/addthis_widget.js | FR | text | 109 Kb | whitelisted |
2284 | chrome.exe | GET | 200 | 104.31.64.111:80 | http://a8btcili.co/images/desc.png | US | image | 2.49 Kb | shared |
2284 | chrome.exe | GET | 200 | 104.31.64.111:80 | http://a8btcili.co/images/favorite.png | US | image | 2.50 Kb | shared |
2284 | chrome.exe | GET | 200 | 104.31.64.111:80 | http://a8btcili.co/images/magnet.png | US | image | 3.14 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2284 | chrome.exe | 104.27.161.240:80 | gotoniubiurl.pw | Cloudflare Inc | US | shared |
2284 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2284 | chrome.exe | 104.31.64.111:80 | a8btcili.co | Cloudflare Inc | US | shared |
2284 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2284 | chrome.exe | 59.80.39.94:80 | k.550tg.com | China Unicom IP network | CN | unknown |
2284 | chrome.exe | 195.27.31.226:443 | www.ailiyou1999.com | CW Vodafone Group PLC | DE | unknown |
2284 | chrome.exe | 61.174.50.143:80 | count.qiqilm.com | No.31,Jin-rong Street | CN | unknown |
2284 | chrome.exe | 1.189.213.64:443 | k.550tg.com | CHINA UNICOM China169 Backbone | CN | unknown |
2284 | chrome.exe | 203.119.206.97:443 | z4.cnzz.com | — | CN | unknown |
2284 | chrome.exe | 103.224.212.222:80 | s1.guanglijiudian.com | Trellian Pty. Limited | AU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
a8btcili.co |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
k.550tg.com |
| suspicious |
j.qiqivv.com |
| unknown |
www.ailiyou1999.com |
| suspicious |
cdn.jsdelivr.net |
| whitelisted |
s5.cnzz.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2284 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
2284 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2284 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2284 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
2284 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
2284 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
2284 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |