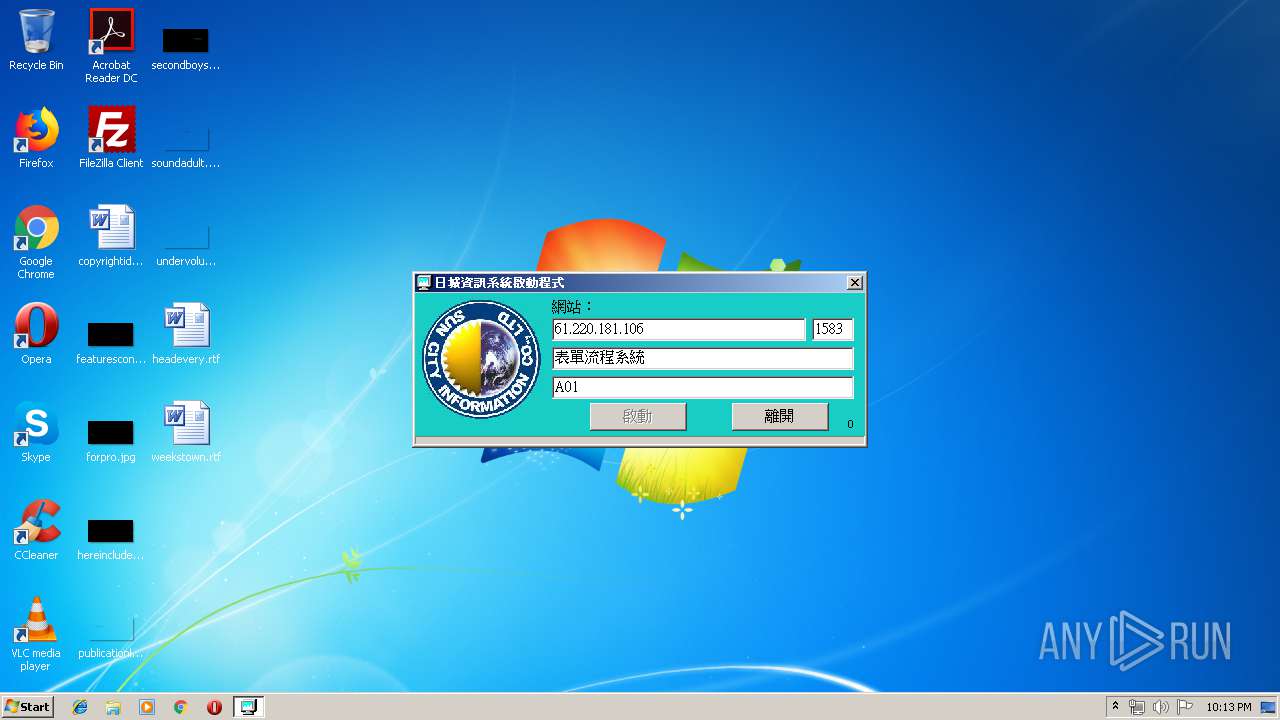
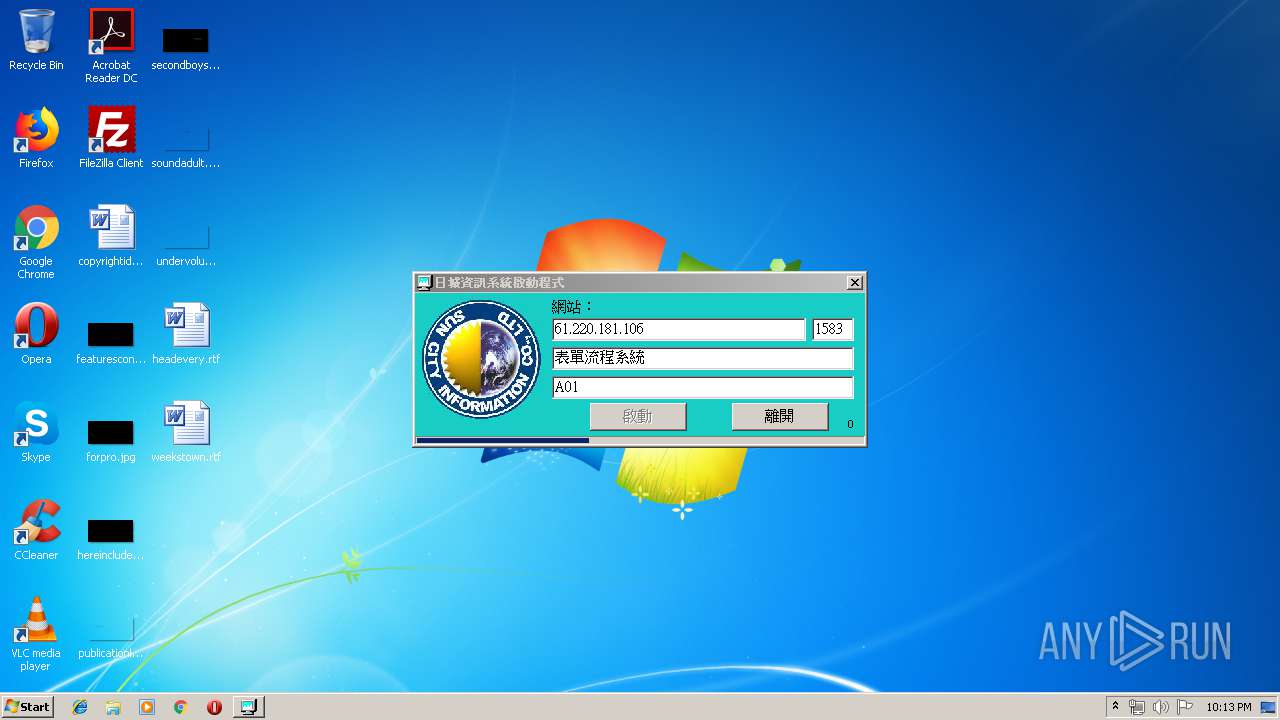
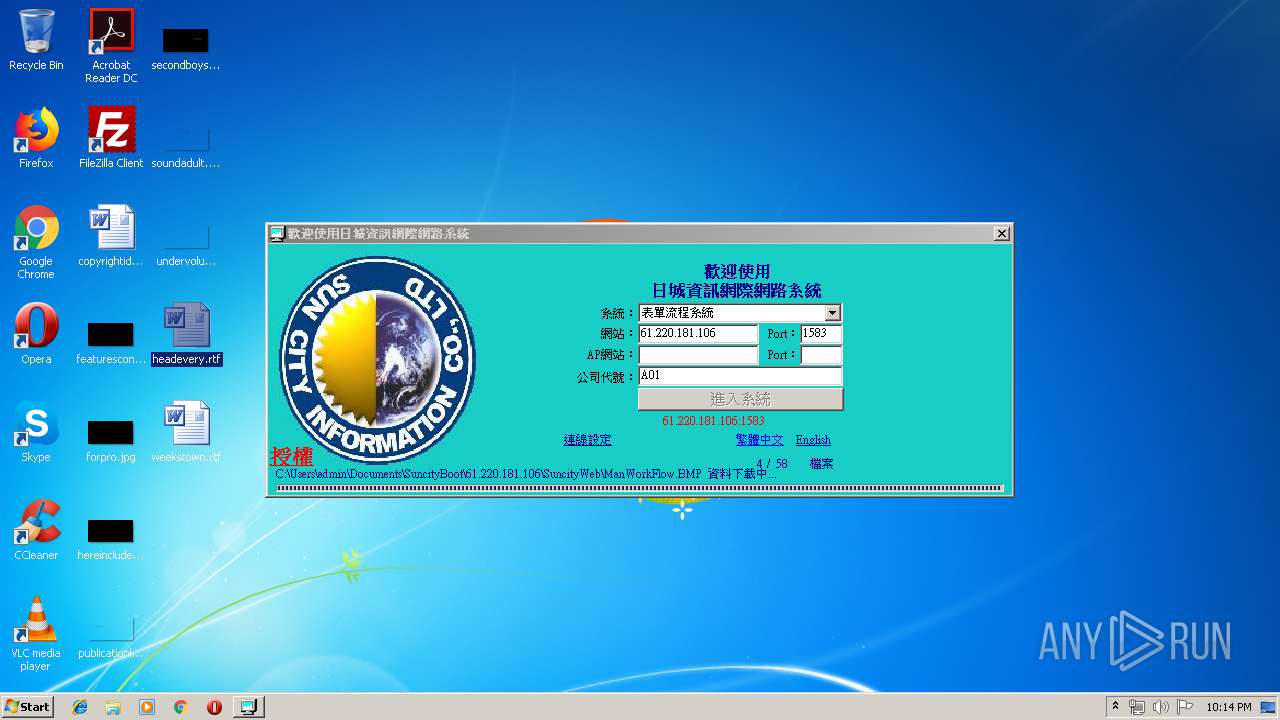
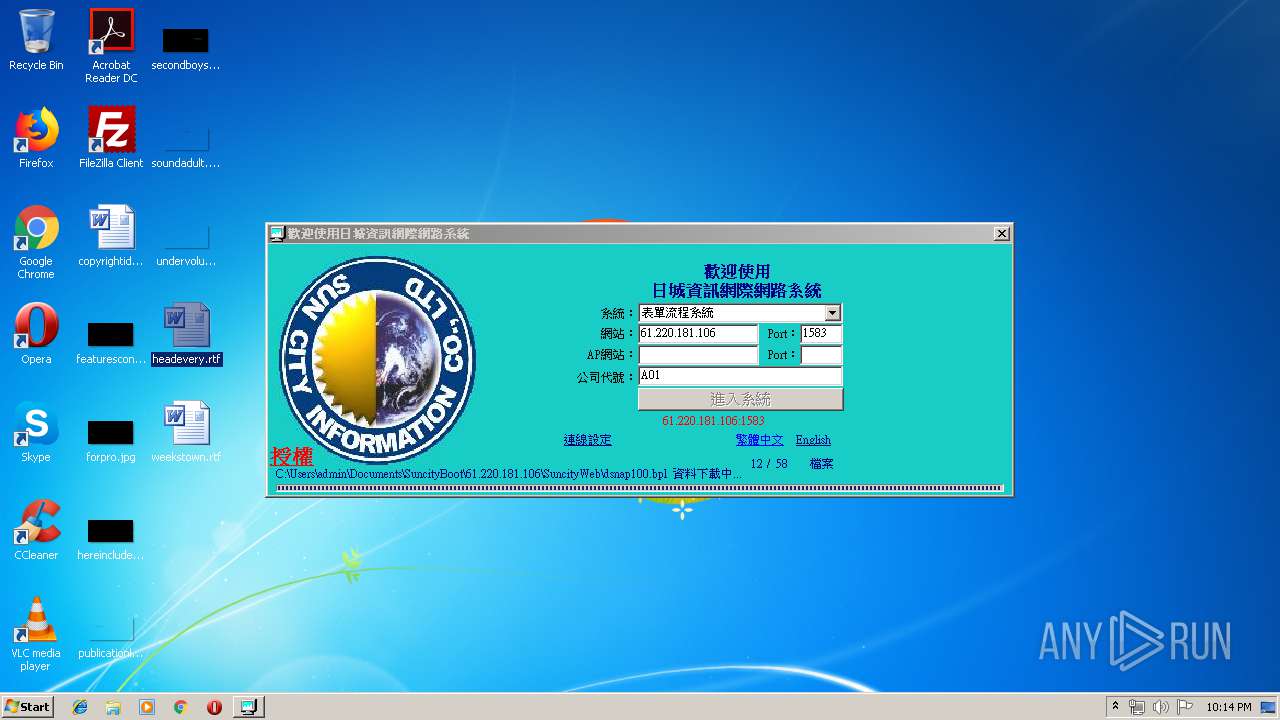
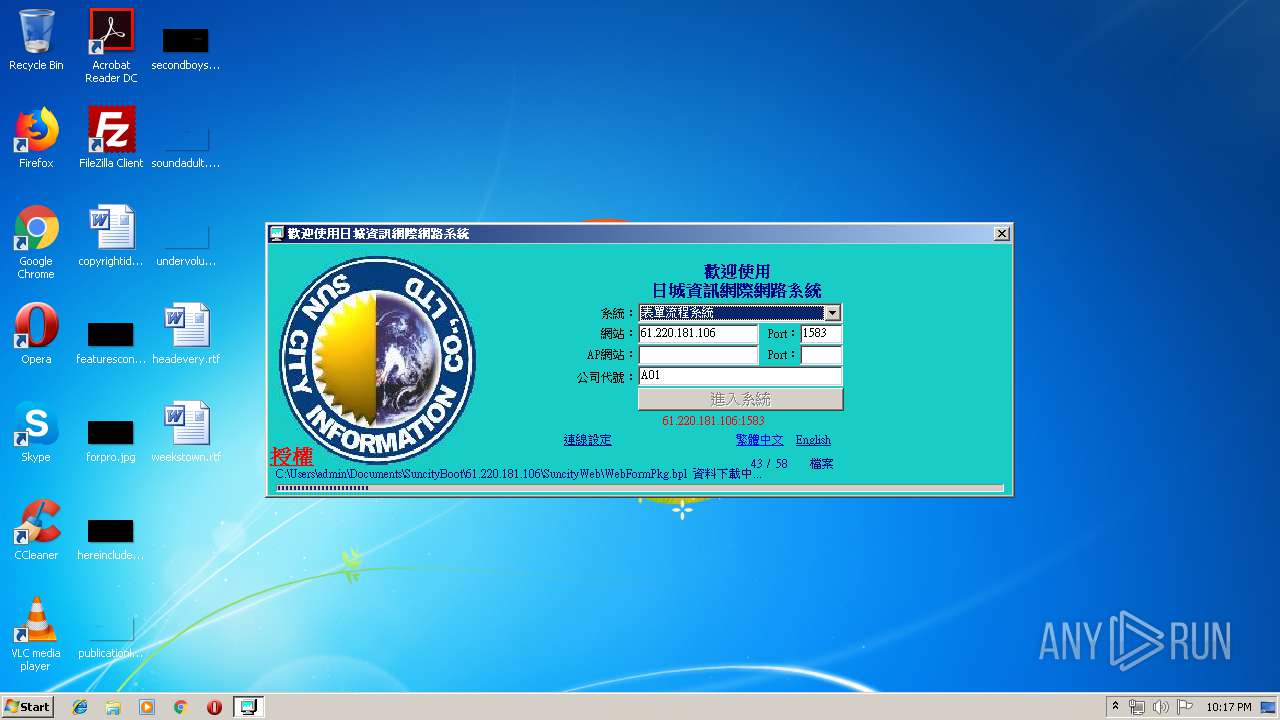
| File name: | 表單流程系統.exe |
| Full analysis: | https://app.any.run/tasks/0772d9cd-87f8-422a-ba9e-92fc201430a5 |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2019, 21:13:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D42B9403288F1AADCFA0A9C113165CCD |
| SHA1: | 5F26B23E95251EEA5F8BB8AD9E31E4EC041F7BAD |
| SHA256: | AAE6D47C6E527E9E1032B41C4A7DE61AA711DA54BE5A99D4AC6F3FADFE71411A |
| SSDEEP: | 24576:g5Bqw+FmMVt0k0zzDLP60iZp5ab9PcvH:SBAVp+hPqH |
MALICIOUS
Application was dropped or rewritten from another process
- BrowserBoot.exe (PID: 2140)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2920)
SUSPICIOUS
Executable content was dropped or overwritten
- 表單流程系統.exe (PID: 3388)
- BrowserBoot.exe (PID: 2140)
INFO
Dropped object may contain Bitcoin addresses
- BrowserBoot.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:17 08:36:58+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 821760 |
| InitializedDataSize: | 139264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc9e88 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.1.540 |
| ProductVersionNumber: | 1.0.1.540 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Traditional) |
| CharacterSet: | Windows, Taiwan (Big5) |
| CompanyName: | Suncity Information Co.,Ltd |
| FileDescription: | - |
| FileVersion: | 1.0.1.540 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | 日城瀏覽器啟動 |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jun-2019 06:36:58 |
| Detected languages: |
|
| CompanyName: | Suncity Information Co.,Ltd |
| FileDescription: | - |
| FileVersion: | 1.0.1.540 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | 日城瀏覽器啟動 |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 17-Jun-2019 06:36:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000C7378 | 0x000C7400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57555 |
.itext | 0x000C9000 | 0x0000141C | 0x00001600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.09797 |
.data | 0x000CB000 | 0x00004D94 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13431 |
.bss | 0x000D0000 | 0x00005668 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000D6000 | 0x00003492 | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.09468 |
.tls | 0x000DA000 | 0x0000004C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000DB000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.20692 |
.reloc | 0x000DC000 | 0x0000C778 | 0x0000C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.66645 |
.rsrc | 0x000E9000 | 0x0000D200 | 0x0000D200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.8794 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.9209 | 850 | UNKNOWN | Chinese - Taiwan | RT_MANIFEST |
2 | 2.80231 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4079 | 2.31395 | 92 | UNKNOWN | UNKNOWN | RT_STRING |
4080 | 3.242 | 872 | UNKNOWN | UNKNOWN | RT_STRING |
4081 | 3.47476 | 784 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
wininet.dll |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2140 | "C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\BrowserBoot.exe" SUNCITYBOOT=TRUE,BASE=NjEuMjIwLjE4MS4xMDY=,PORT=MTU4Mw==,LOGINTYPE=Mg==,CM_NO=QTAx,LOGINID=,LOGINPASW=,SUNCITYWEBDIR=QzpcVXNlcnNcYWRtaW5cRG9jdW1lbnRzXFN1bmNpdHlCb290XDYxLjIyMC4xODEuMTA2XFN1bmNpdHlXZWI=,PARENT_EXENAME=QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxUZW1wXOihqOWWrua1geeoi+ezu+e1sS5leGU=,PARENT_PARENT_EXENAME=QzpcV2luZG93c1xFeHBsb3Jlci5FWEU= | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\BrowserBoot.exe | 表單流程系統.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.1934 Modules
| |||||||||||||||
| 2920 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\AppData\Local\Temp\表單流程系統.exe" | C:\Users\admin\AppData\Local\Temp\表單流程系統.exe | explorer.exe | ||||||||||||
User: admin Company: Suncity Information Co.,Ltd Integrity Level: MEDIUM Exit code: 0 Version: 1.0.1.540 Modules
| |||||||||||||||
Total events
763
Read events
724
Write events
39
Delete events
0
Modification events
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3388) 表單流程系統.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\??????_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
43
Suspicious files
0
Text files
219
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | 表單流程系統.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\BrowserBoot.download | — | |
MD5:— | SHA256:— | |||
| 2140 | BrowserBoot.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\Browser.download | — | |
MD5:— | SHA256:— | |||
| 2140 | BrowserBoot.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\SActBrowserPaswInput.download | — | |
MD5:— | SHA256:— | |||
| 2140 | BrowserBoot.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\HumanFlow.download | — | |
MD5:— | SHA256:— | |||
| 2140 | BrowserBoot.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\SuncityBG.download | — | |
MD5:— | SHA256:— | |||
| 2140 | BrowserBoot.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\ManWorkFlow.download | — | |
MD5:— | SHA256:— | |||
| 2140 | BrowserBoot.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\WorkFlow.download | — | |
MD5:— | SHA256:— | |||
| 2140 | BrowserBoot.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\adortl100.download | — | |
MD5:— | SHA256:— | |||
| 2140 | BrowserBoot.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\bdertl100.download | — | |
MD5:— | SHA256:— | |||
| 2140 | BrowserBoot.exe | C:\Users\admin\Documents\SuncityBoot\61.220.181.106\SuncityWeb\dbrtl100.download | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
167
TCP/UDP connections
169
DNS requests
0
Threats
503
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2140 | BrowserBoot.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
3388 | 表單流程系統.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
3388 | 表單流程系統.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
2140 | BrowserBoot.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
2140 | BrowserBoot.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
2140 | BrowserBoot.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
3388 | 表單流程系統.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
3388 | 表單流程系統.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
3388 | 表單流程系統.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
3388 | 表單流程系統.exe | POST | — | 61.220.181.106:1583 | http://61.220.181.106:1583/A001 | TW | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | 表單流程系統.exe | 61.220.181.106:1583 | — | Data Communication Business Group | TW | suspicious |
2140 | BrowserBoot.exe | 61.220.181.106:1583 | — | Data Communication Business Group | TW | suspicious |
— | — | 61.220.181.106:1583 | — | Data Communication Business Group | TW | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3388 | 表單流程系統.exe | Generic Protocol Command Decode | SURICATA HTTP request header invalid |
3388 | 表單流程系統.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3388 | 表單流程系統.exe | Potentially Bad Traffic | ET INFO GENERIC SUSPICIOUS POST to Dotted Quad with Fake Browser 1 |
3388 | 表單流程系統.exe | Generic Protocol Command Decode | SURICATA HTTP request header invalid |
3388 | 表單流程系統.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3388 | 表單流程系統.exe | Potentially Bad Traffic | ET INFO GENERIC SUSPICIOUS POST to Dotted Quad with Fake Browser 1 |
3388 | 表單流程系統.exe | Generic Protocol Command Decode | SURICATA HTTP request header invalid |
3388 | 表單流程系統.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3388 | 表單流程系統.exe | Potentially Bad Traffic | ET INFO GENERIC SUSPICIOUS POST to Dotted Quad with Fake Browser 1 |
3388 | 表單流程系統.exe | Generic Protocol Command Decode | SURICATA HTTP request header invalid |