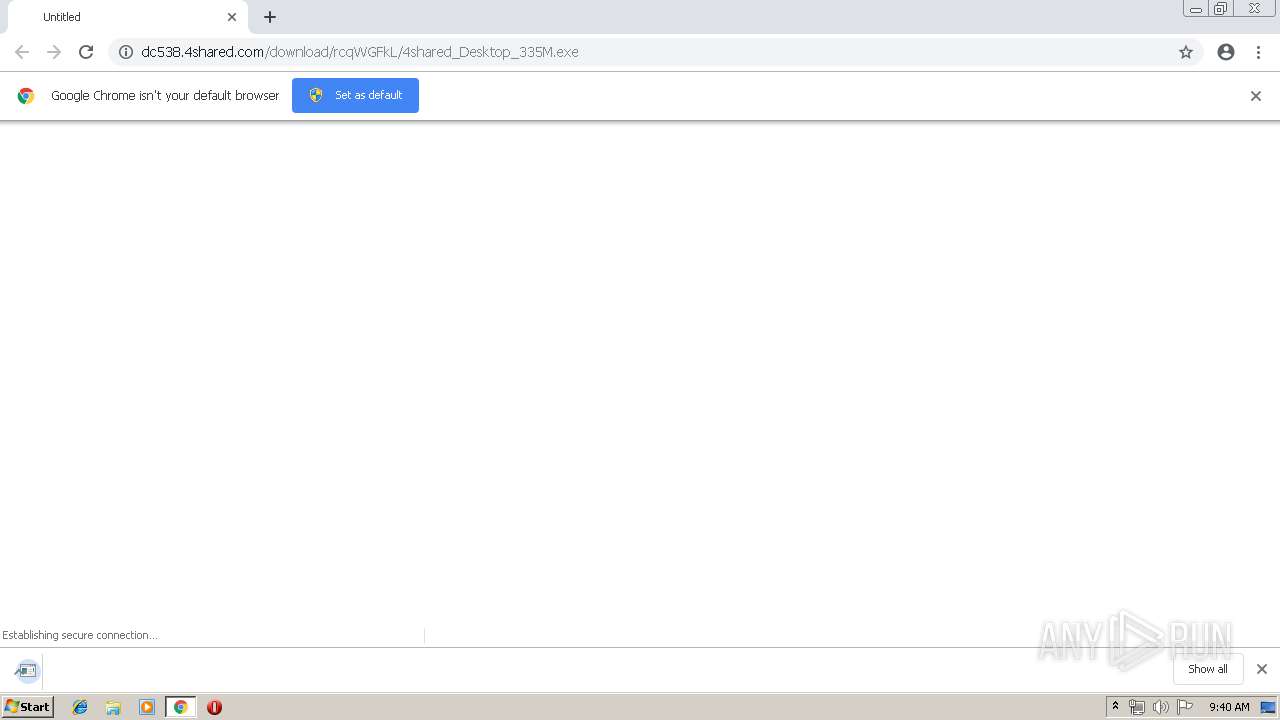
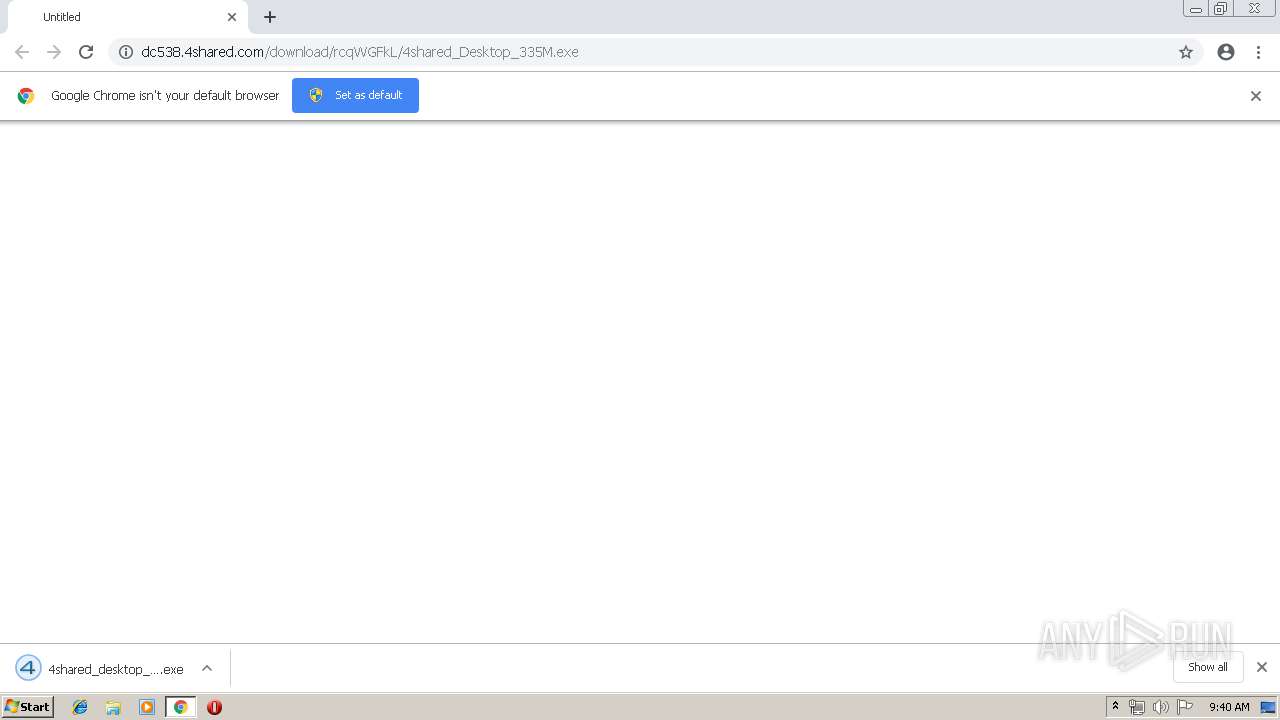
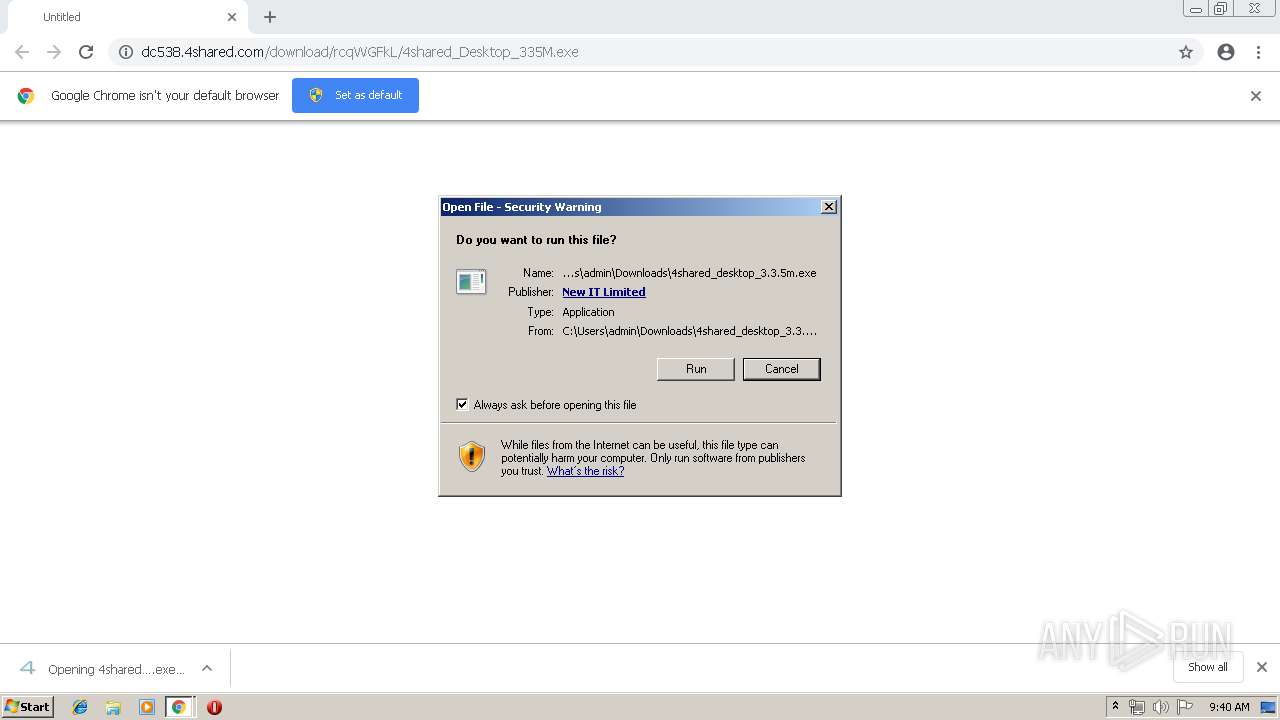
| URL: | http://dc538.4shared.com/download/rcqWGFkL/4shared_Desktop_335M.exe |
| Full analysis: | https://app.any.run/tasks/fb6f62be-d938-4ed3-8b26-722e3518c334 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2019, 08:40:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 99FE8F7F47F0F55FD798B4E408517C6B |
| SHA1: | 4375F2641F4DF1D3B576F168182F2468E73316D1 |
| SHA256: | AAD60894A82D024B622C12957570B34359F86C003FC13B0ABF34B231227C223A |
| SSDEEP: | 3:N1KaGQvNbIK8L+iyYIrRuC:CaHKK88YIQC |
MALICIOUS
Application was dropped or rewritten from another process
- 4shared_desktop_3.3.5m.exe (PID: 2752)
- 4shared_desktop_3.3.5m.exe (PID: 1424)
- desktop.exe (PID: 4072)
Loads dropped or rewritten executable
- 4shared_desktop_3.3.5m.exe (PID: 2752)
- 4shared_desktop_3.3.5m.exe (PID: 1424)
- desktop.exe (PID: 4072)
SUSPICIOUS
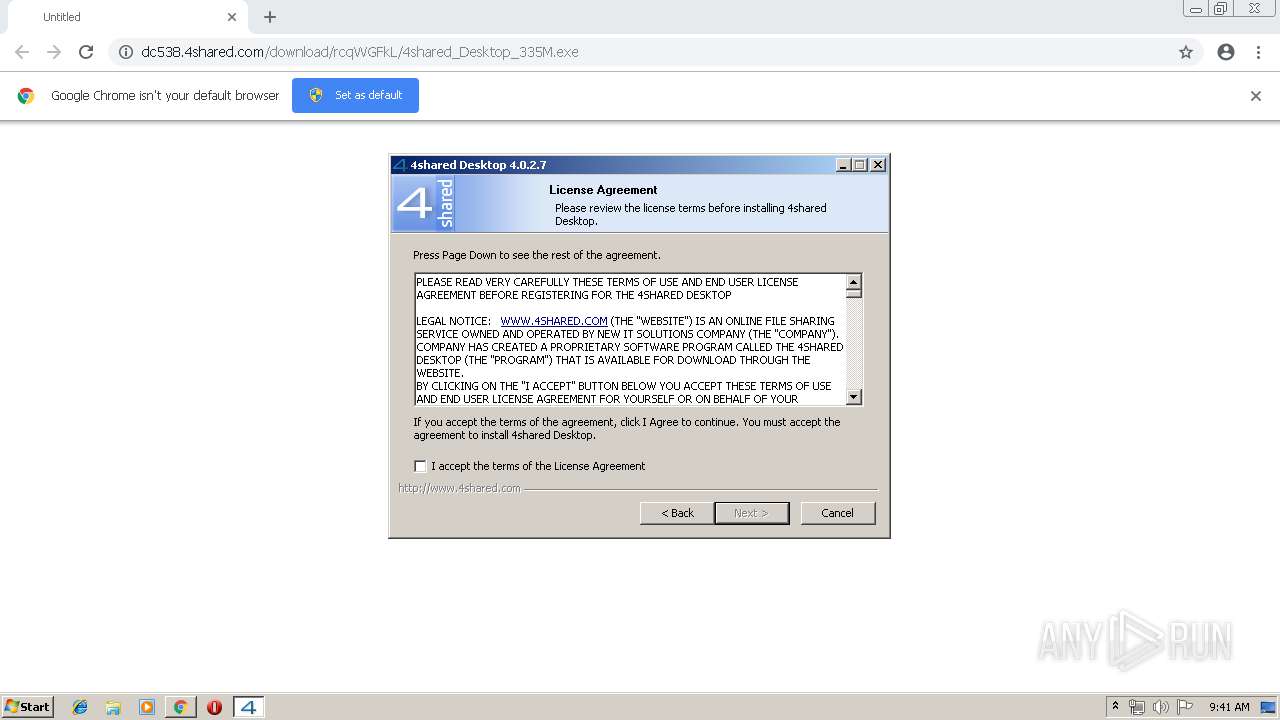
Creates files in the program directory
- 4shared_desktop_3.3.5m.exe (PID: 1424)
Executable content was dropped or overwritten
- 4shared_desktop_3.3.5m.exe (PID: 2752)
- chrome.exe (PID: 3948)
- 4shared_desktop_3.3.5m.exe (PID: 1424)
Application launched itself
- 4shared_desktop_3.3.5m.exe (PID: 2752)
Creates files in the user directory
- 4shared_desktop_3.3.5m.exe (PID: 1424)
- desktop.exe (PID: 4072)
Creates COM task schedule object
- 4shared_desktop_3.3.5m.exe (PID: 1424)
Creates a software uninstall entry
- 4shared_desktop_3.3.5m.exe (PID: 1424)
Starts Internet Explorer
- 4shared_desktop_3.3.5m.exe (PID: 1424)
Reads internet explorer settings
- desktop.exe (PID: 4072)
Reads Internet Cache Settings
- desktop.exe (PID: 4072)
INFO
Application launched itself
- chrome.exe (PID: 3948)
- iexplore.exe (PID: 2856)
Reads Internet Cache Settings
- chrome.exe (PID: 3948)
- iexplore.exe (PID: 2344)
Changes internet zones settings
- iexplore.exe (PID: 2856)
Creates files in the user directory
- iexplore.exe (PID: 2344)
Reads internet explorer settings
- iexplore.exe (PID: 2344)
Changes settings of System certificates
- iexplore.exe (PID: 2344)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2344)
Reads settings of System Certificates
- iexplore.exe (PID: 2344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
14
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=928,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9209648873079548662 --mojo-platform-channel-handle=3700 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3932 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
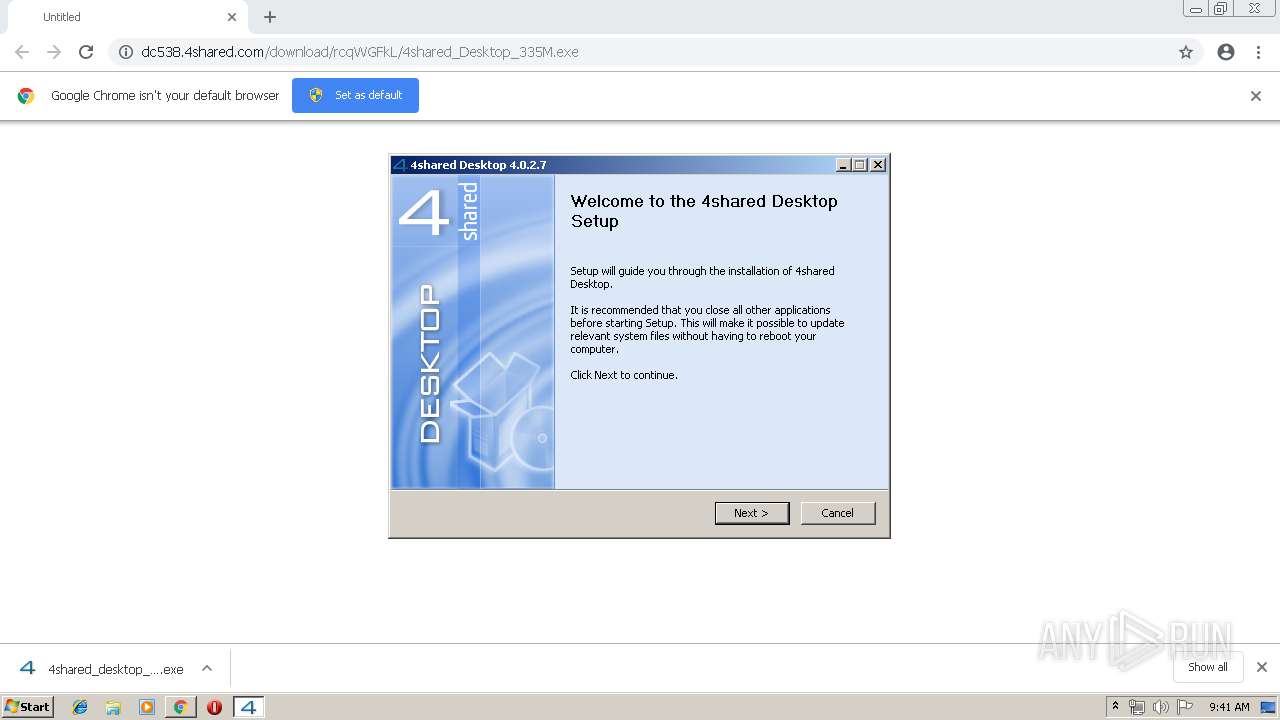
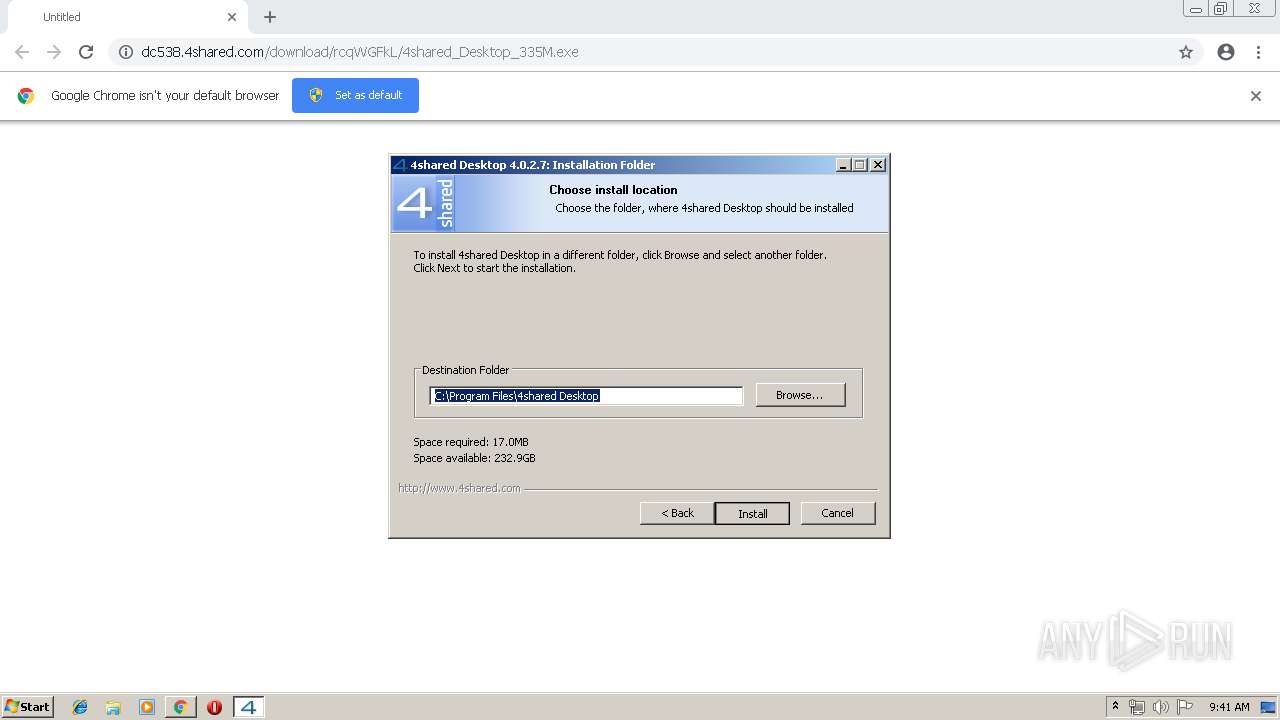
| 1424 | "C:\Users\admin\Downloads\4shared_desktop_3.3.5m.exe" /UAC:601FE /NCRC | C:\Users\admin\Downloads\4shared_desktop_3.3.5m.exe | 4shared_desktop_3.3.5m.exe | ||||||||||||
User: admin Company: New IT Solutions Integrity Level: HIGH Description: 4shared Desktop Setup Exit code: 1223 Version: 4.0.2.7 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=928,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=6540198023234917099 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6540198023234917099 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=928,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=66203899630775436 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2856 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=928,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=17667289432405912191 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17667289432405912191 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\Downloads\4shared_desktop_3.3.5m.exe" | C:\Users\admin\Downloads\4shared_desktop_3.3.5m.exe | chrome.exe | ||||||||||||
User: admin Company: New IT Solutions Integrity Level: MEDIUM Description: 4shared Desktop Setup Exit code: 1223 Version: 4.0.2.7 Modules
| |||||||||||||||
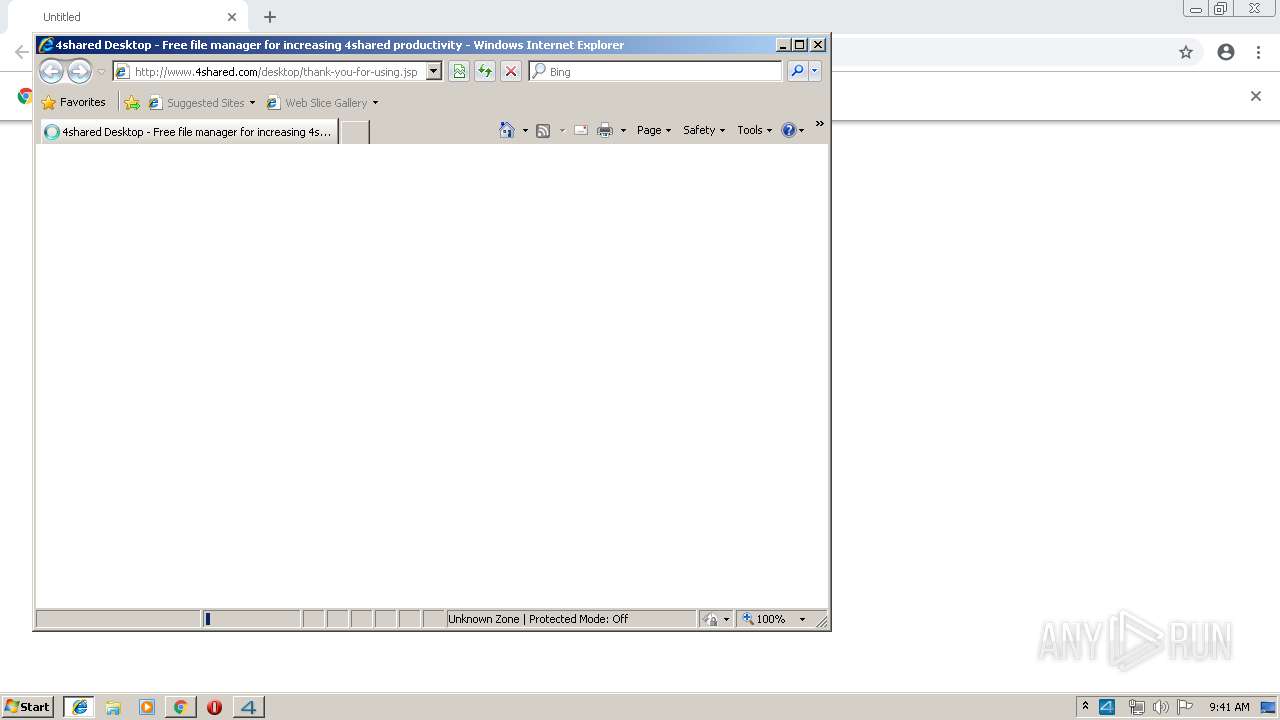
| 2856 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.4shared.com/desktop/thank-you-for-using.jsp | C:\Program Files\Internet Explorer\iexplore.exe | 4shared_desktop_3.3.5m.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=928,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=14846457759106036303 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14846457759106036303 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 146
Read events
1 949
Write events
192
Delete events
5
Modification events
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3948-13205234419578750 |
Value: 259 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3948-13205234419578750 |
Value: 259 | |||
Executable files
17
Suspicious files
13
Text files
107
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f83d95c4-d131-4416-aa73-a5e425c33f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
53
DNS requests
10
Threats
42
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3948 | chrome.exe | GET | 302 | 74.117.178.93:80 | http://dc538.4shared.com/download/rcqWGFkL/4shared_Desktop_335M.exe | VG | — | — | malicious |
4072 | desktop.exe | GET | 200 | 199.101.134.234:80 | http://www.4shared.com/uploader/signup.jsp | US | — | — | suspicious |
2344 | iexplore.exe | GET | 200 | 199.101.134.234:80 | http://www.4shared.com/desktop/thank-you-for-using.jsp | US | html | 68.1 Kb | suspicious |
1424 | 4shared_desktop_3.3.5m.exe | POST | 200 | 199.101.134.234:80 | http://www.4shared.com/desktop_stats.jsp | US | — | — | suspicious |
2856 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3948 | chrome.exe | 199.101.134.186:443 | dc730.4shared.com | WZ Communications Inc. | US | suspicious |
3948 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
2344 | iexplore.exe | 199.101.134.234:80 | dc538.4shared.com | WZ Communications Inc. | US | suspicious |
1424 | 4shared_desktop_3.3.5m.exe | 199.101.134.234:80 | dc538.4shared.com | WZ Communications Inc. | US | suspicious |
2856 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4072 | desktop.exe | 199.101.134.234:80 | dc538.4shared.com | WZ Communications Inc. | US | suspicious |
2344 | iexplore.exe | 204.155.149.42:443 | static.4shared.com | WZ Communications Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
dc538.4shared.com |
| malicious |
accounts.google.com |
| shared |
dc730.4shared.com |
| suspicious |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.4shared.com |
| suspicious |
static.4shared.com |
| suspicious |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1424 | 4shared_desktop_3.3.5m.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
41 ETPRO signatures available at the full report