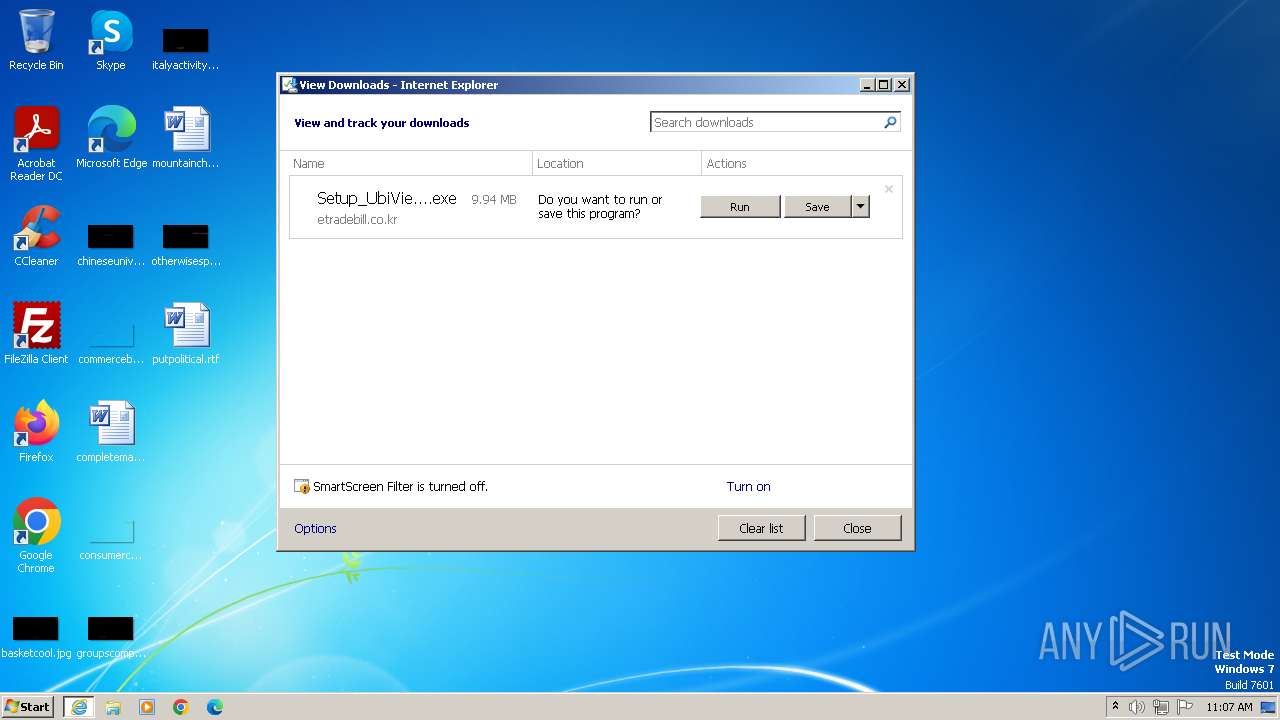
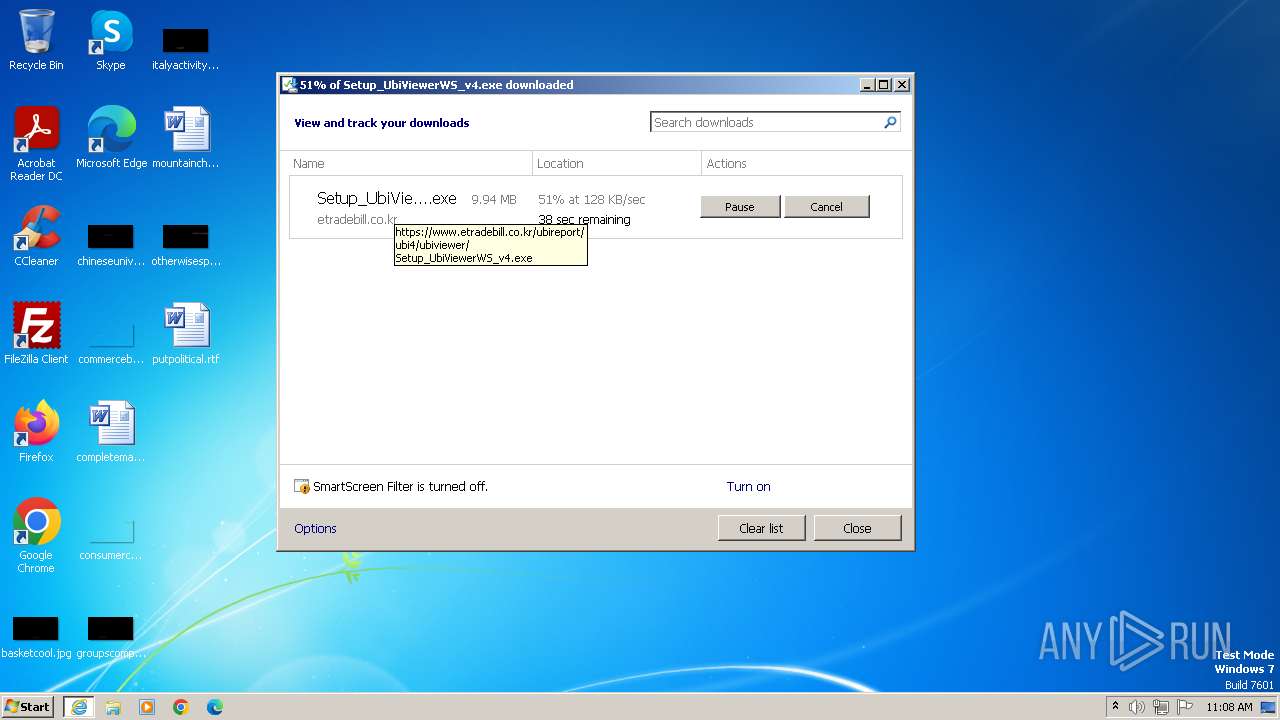
| URL: | https://www.etradebill.co.kr/ubireport/ubi4/ubiviewer/Setup_UbiViewerWS_v4.exe |
| Full analysis: | https://app.any.run/tasks/92036252-5a0d-4784-9a42-d7ea7785862f |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2023, 11:07:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 23CB86F031CA918E8C2615C6444DF5A0 |
| SHA1: | FA2C0359EB4338D3F1C0AEFCFD14765CC0689DEF |
| SHA256: | AACD74366DA548FF4B82B50F97049D74284A0544DE51629A2A0858AE48119070 |
| SSDEEP: | 3:N8DSLrQKQsPsQwOt0QOzMLRLAC:2OLrXPsV3MRJ |
MALICIOUS
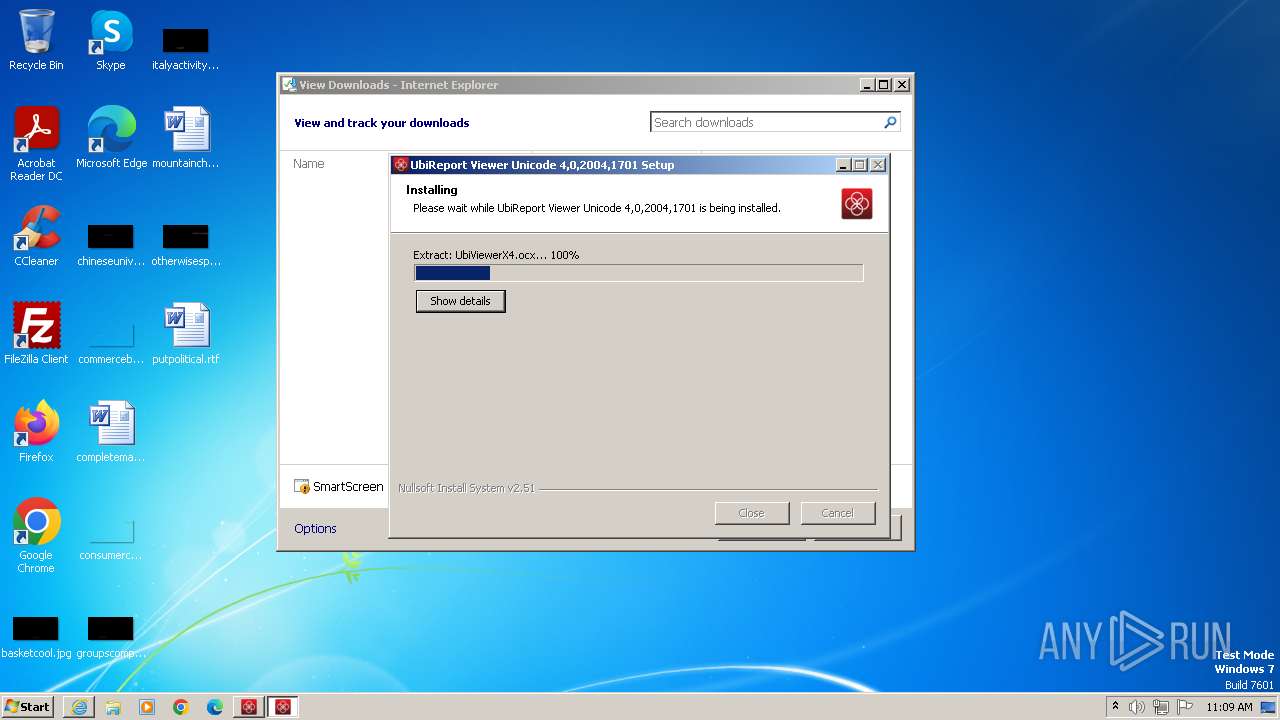
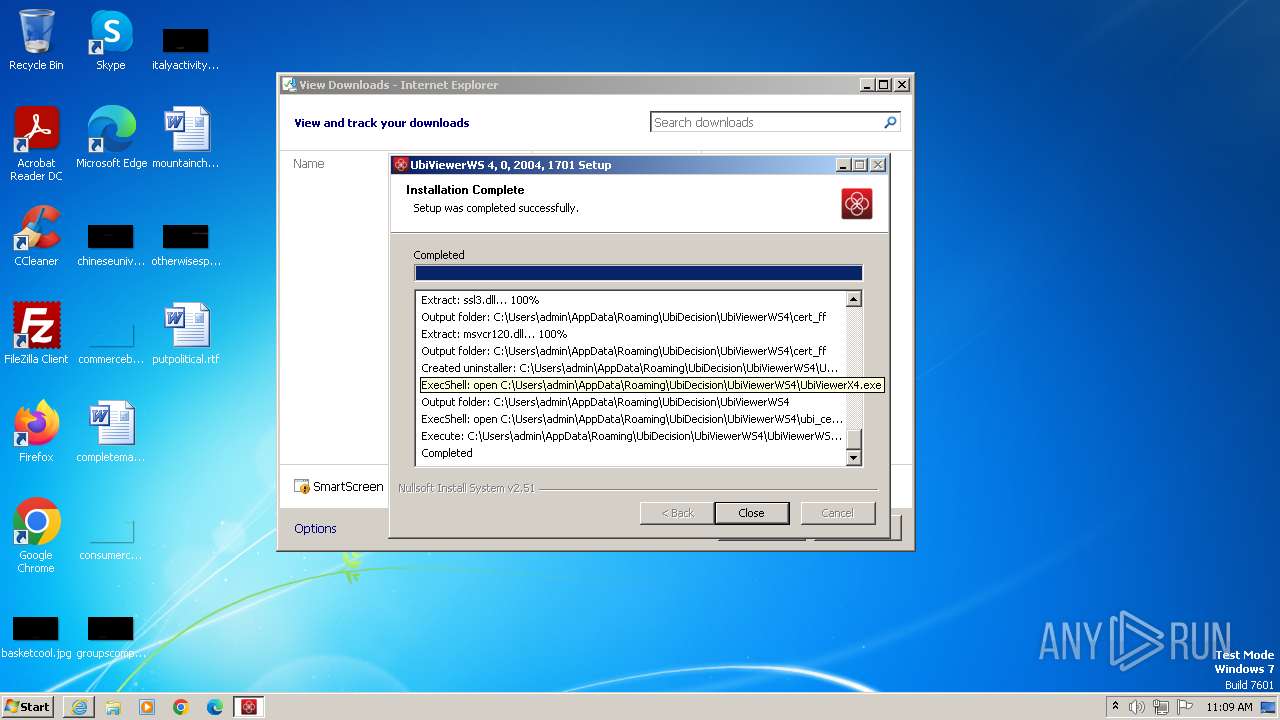
Drops the executable file immediately after the start
- Setup_UbiViewerWS_v4.exe (PID: 2520)
- UbiViewerX4.exe (PID: 1004)
Actions looks like stealing of personal data
- cmd.exe (PID: 3492)
- certutil.exe (PID: 3656)
Steals credentials from Web Browsers
- cmd.exe (PID: 3492)
SUSPICIOUS
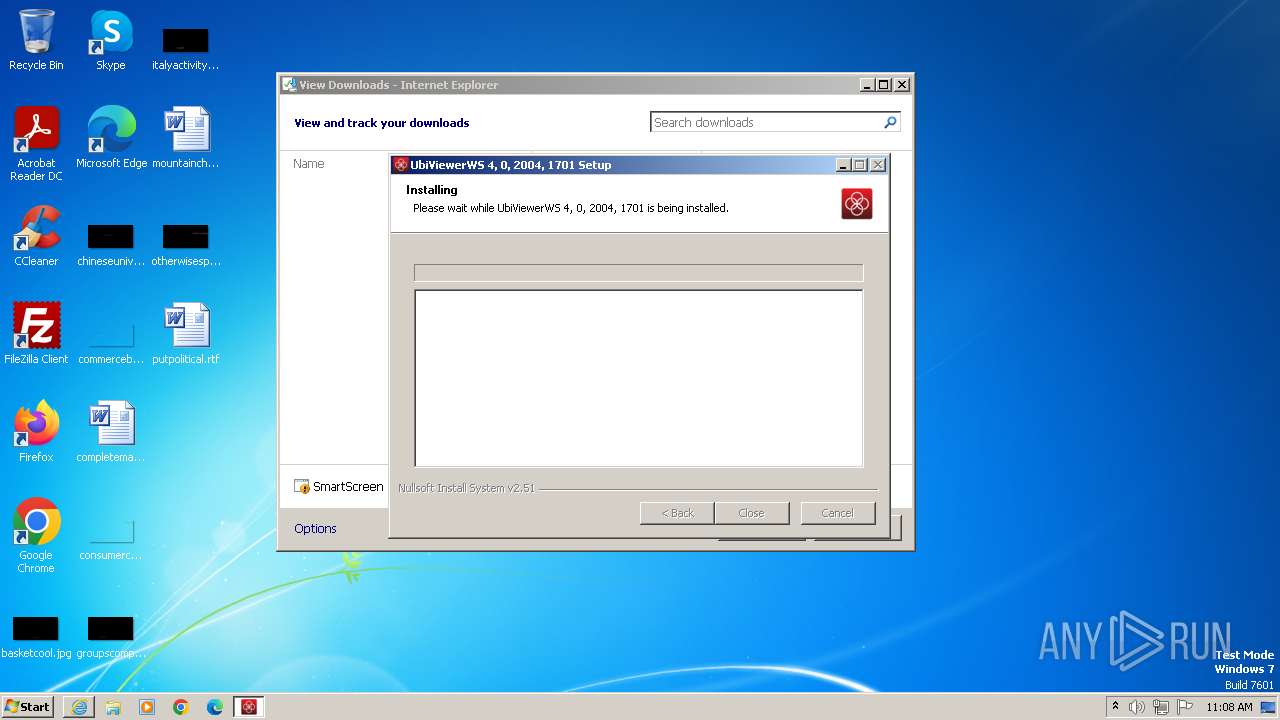
The process drops C-runtime libraries
- Setup_UbiViewerWS_v4.exe (PID: 2520)
The process creates files with name similar to system file names
- Setup_UbiViewerWS_v4.exe (PID: 2520)
Process drops legitimate windows executable (CertUtil.exe)
- Setup_UbiViewerWS_v4.exe (PID: 2520)
Reads the Internet Settings
- Setup_UbiViewerWS_v4.exe (PID: 2520)
- ubi_cert.exe (PID: 4064)
Application launched itself
- cmd.exe (PID: 3492)
Executing commands from a ".bat" file
- ubi_cert.exe (PID: 4064)
Process drops legitimate windows executable
- UbiViewerX4.exe (PID: 1004)
- Setup_UbiViewerWS_v4.exe (PID: 2520)
Starts CMD.EXE for commands execution
- ubi_cert.exe (PID: 4064)
- cmd.exe (PID: 3492)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 3940)
- Setup_UbiViewerWS_v4.exe (PID: 2520)
- UbiViewerX4.exe (PID: 1004)
- ubi_cert.exe (PID: 4064)
- certutil.exe (PID: 3656)
- UbiViewerWS4.exe (PID: 1064)
Manual execution by a user
- wmpnscfg.exe (PID: 3940)
Checks supported languages
- wmpnscfg.exe (PID: 3940)
- Setup_UbiViewerWS_v4.exe (PID: 2520)
- ubi_cert.exe (PID: 4064)
- UbiViewerWS4.exe (PID: 1064)
- certutil.exe (PID: 3656)
- UbiViewerX4.exe (PID: 1004)
Application launched itself
- iexplore.exe (PID: 1864)
The process uses the downloaded file
- iexplore.exe (PID: 1864)
Drops the executable file immediately after the start
- iexplore.exe (PID: 1864)
- iexplore.exe (PID: 2136)
Create files in a temporary directory
- Setup_UbiViewerWS_v4.exe (PID: 2520)
Creates files or folders in the user directory
- Setup_UbiViewerWS_v4.exe (PID: 2520)
- UbiViewerX4.exe (PID: 1004)
- certutil.exe (PID: 3656)
Reads Environment values
- Setup_UbiViewerWS_v4.exe (PID: 2520)
The executable file from the user directory is run by the CMD process
- certutil.exe (PID: 3656)
Checks operating system version
- cmd.exe (PID: 3492)
Reads the machine GUID from the registry
- UbiViewerWS4.exe (PID: 1064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
14
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
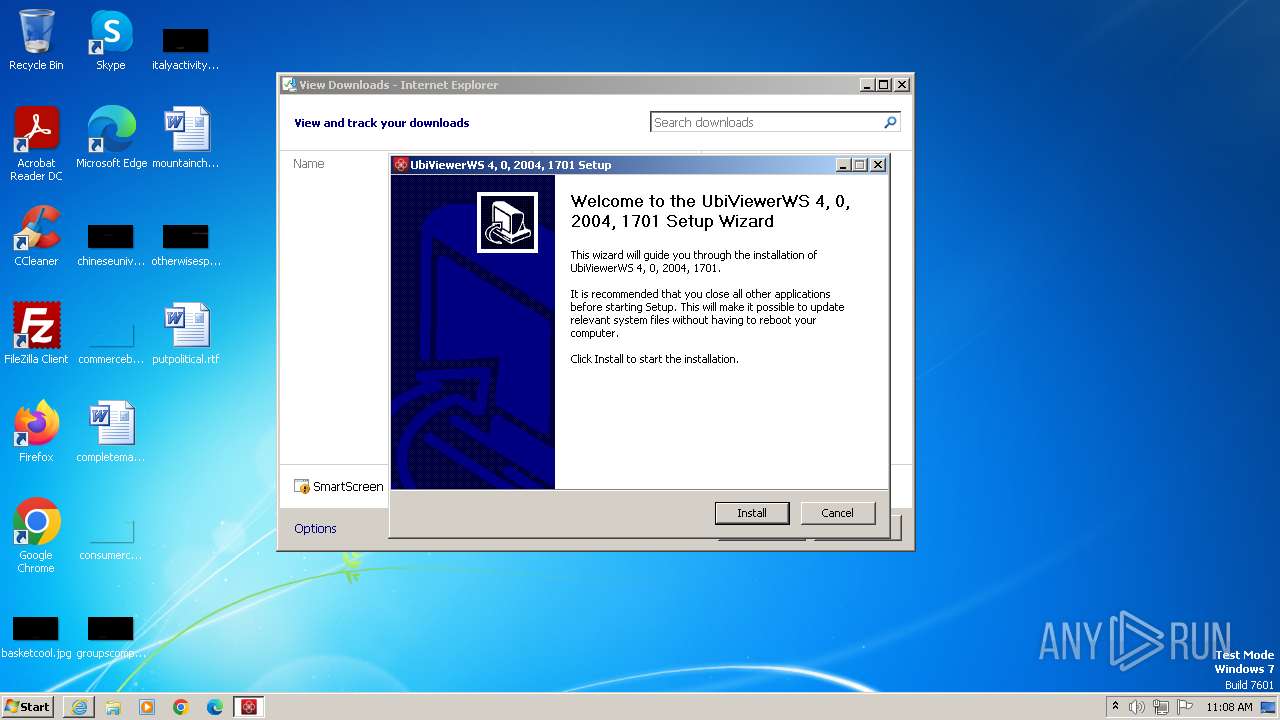
| 1004 | "C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\UbiViewerX4.exe" | C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\UbiViewerX4.exe | Setup_UbiViewerWS_v4.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: UbiViewer Exit code: 0 Version: 4,0,2004,1701 Modules
| |||||||||||||||
| 1064 | C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\UbiViewerWS4.exe | C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\UbiViewerWS4.exe | Setup_UbiViewerWS_v4.exe | ||||||||||||
User: admin Company: UbiDecision Integrity Level: MEDIUM Description: UbiViewerWS 4.0 Exit code: 0 Version: 4, 0, 2004, 1701 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.etradebill.co.kr/ubireport/ubi4/ubiviewer/Setup_UbiViewerWS_v4.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1864 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\ubi_cert.exe" | C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\ubi_cert.exe | — | Setup_UbiViewerWS_v4.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Setup_UbiViewerWS_v4.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Setup_UbiViewerWS_v4.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: UbiViewerWS 4.0 Installer Exit code: 0 Version: 4, 0, 2004, 1701 Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\UbiViewerX4.exe" | C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\UbiViewerX4.exe | — | Setup_UbiViewerWS_v4.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: UbiViewer Exit code: 3221226540 Version: 4,0,2004,1701 Modules
| |||||||||||||||
| 3492 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\ubi_cert_rootca.bat" " | C:\Windows\System32\cmd.exe | ubi_cert.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3608 | C:\Windows\system32\certutil.exe -enterprise -addstore root rootca.crt | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
| 3656 | "C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4"\cert_ff\certutil.exe -A -n "UbiViewerWS" -i "C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\rootca.crt" -t CT,C,C -d "C:\Users\admin\AppData\Roaming\Mozilla\Firefox\\Profiles/qldyz51w.default" | C:\Users\admin\AppData\Roaming\UbiDecision\UbiViewerWS4\cert_ff\certutil.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
18 977
Read events
18 886
Write events
89
Delete events
2
Modification events
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
33
Suspicious files
23
Text files
21
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:05BED65BF78A2C039DE304B52806CCA2 | SHA256:5575DEF28C6B38614C678250EC1C465FAEFF1ABDF23D01989617BF6835045196 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50EEA4485D851270C10F80BFBCC48ED3 | binary | |
MD5:5D511695C44DC221ECD71A609B511645 | SHA256:EA377E292A4CA06A77E569EECE5E458736CB7E9AE9553D53F1703420FAAA5719 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:CB401A975FABD1A9EAF5AAF57B362495 | SHA256:9E19272B8E2DFEA4C3BDA40F3AE9828A097DB22035638F1FE852B57DC55DA5D9 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Setup_UbiViewerWS_v4[1].exe | executable | |
MD5:1B0D51FE9B3436279B44FA7E944E3B45 | SHA256:5A5C8DC3A12640927DBD773EE54A62C9435B00D8283A7119128BE53DB2875D4A | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:03C7F2208B0FCA2AE5BA3709A30FC2E0 | SHA256:9A9C267478323D3B2ABB84EB66B5FA2B290785C08D7514C4F84CFACEC72F8B9E | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50EEA4485D851270C10F80BFBCC48ED3 | binary | |
MD5:49AA645B7DF36547548994622FEAD168 | SHA256:BA2F0E5B4A2F05E7B7FAC3E6E731763A20329EA8E098AF7AD8DAAF8D6828D2FC | |||
| 1864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 1864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:578F08D4BF860DE4B047955220AED6E7 | SHA256:D3AFDC14E5C2B7BACF9166049DCCB686B7C00C0877DD04483D87799B88CA5F95 | |||
| 1864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:1B0A195C9F74B54A7F21C1929D4C54E5 | SHA256:DFF3B61E66EF9E3E08CCA4274B95790FDFFC1104E185D43FEDEC612A90C4EBB9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
22
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2136 | iexplore.exe | GET | 200 | 23.53.40.40:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0b7725d384a0a9d4 | unknown | compressed | 4.66 Kb | unknown |
1864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
2136 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEG3Ae8bPNoMETZl7K4Pzqdk%3D | unknown | binary | 471 b | unknown |
1864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
1864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 23.53.40.19:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d04ae3e1fa2d6d38 | unknown | compressed | 65.2 Kb | unknown |
1864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
2136 | iexplore.exe | GET | 200 | 23.53.40.40:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7c0985578a653cb5 | unknown | compressed | 4.66 Kb | unknown |
2136 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | unknown |
2136 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | binary | 1.42 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2136 | iexplore.exe | 203.242.255.177:443 | www.etradebill.co.kr | Korea Trade Network | KR | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2136 | iexplore.exe | 23.53.40.40:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2136 | iexplore.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
2136 | iexplore.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | shared |
1864 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
1864 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.etradebill.co.kr |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
UbiViewerWS4.exe | FTH: (1064): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|