| File name: | aacc8432eda684b179dab3de142286625d9a7322e5d9b3501b9cc711af9b50dc |
| Full analysis: | https://app.any.run/tasks/f41dcb9a-0e1f-4e09-9678-d6838e3c378b |
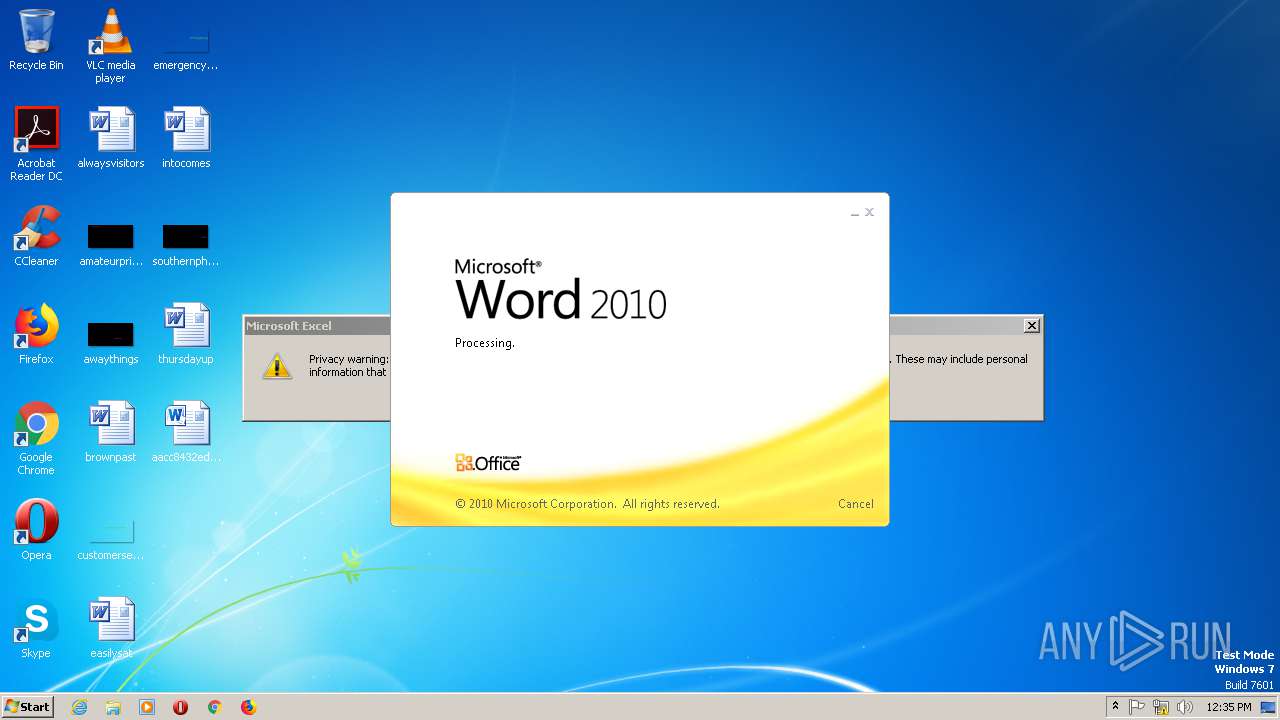
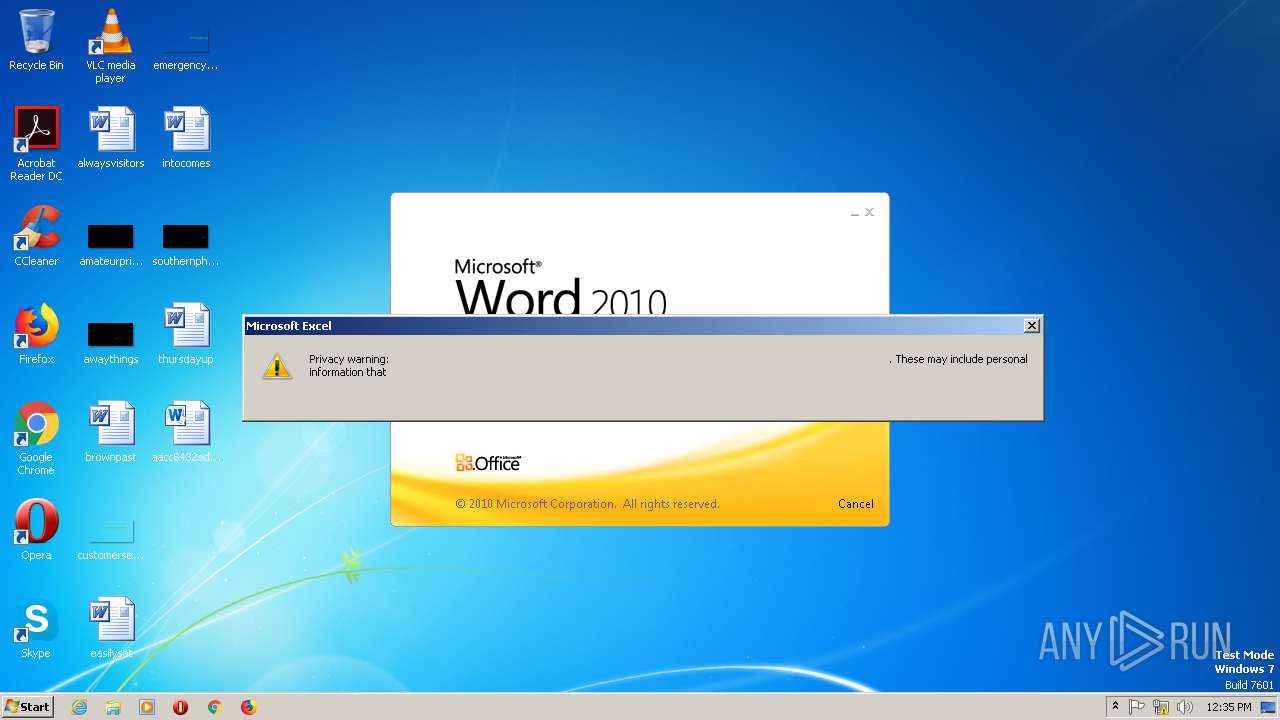
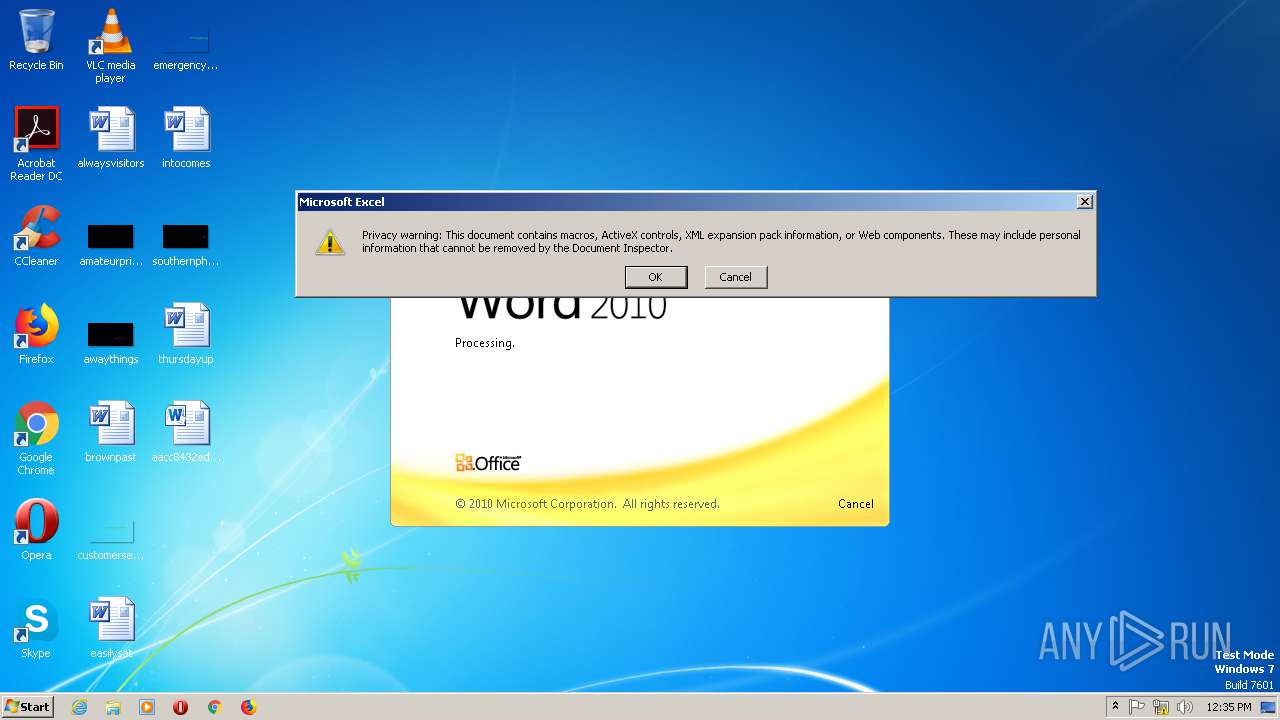
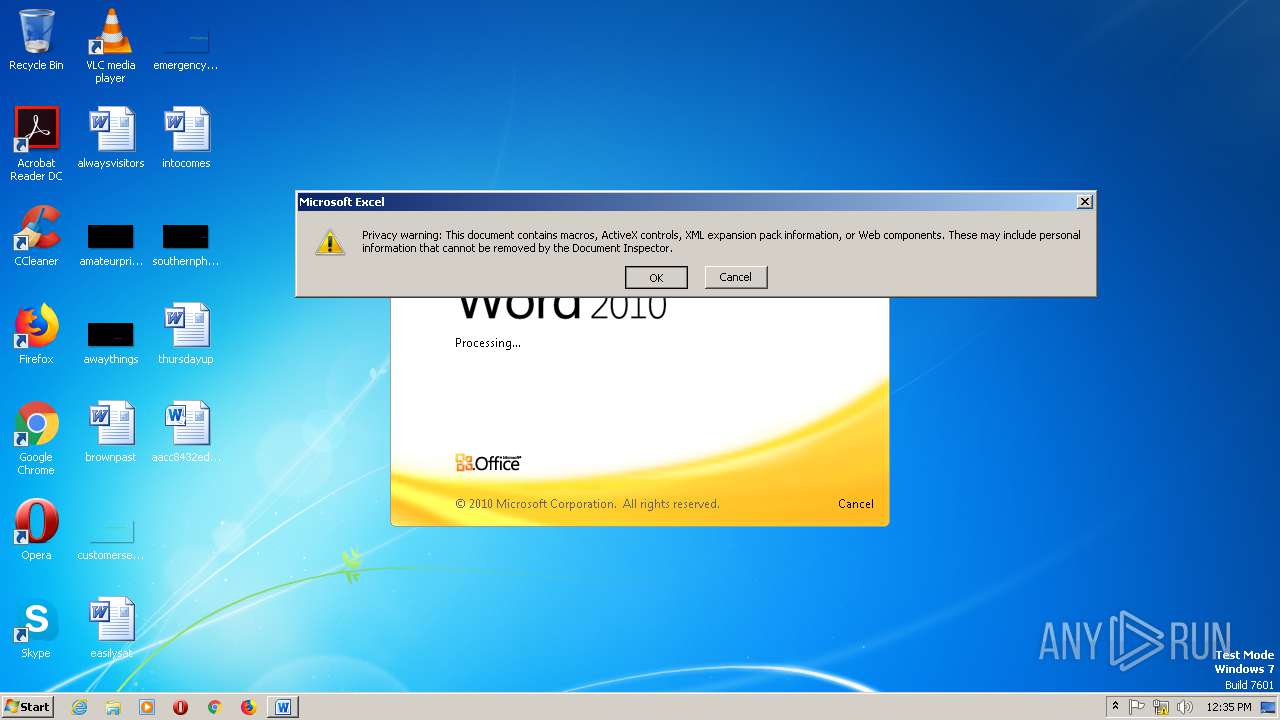
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 12:34:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
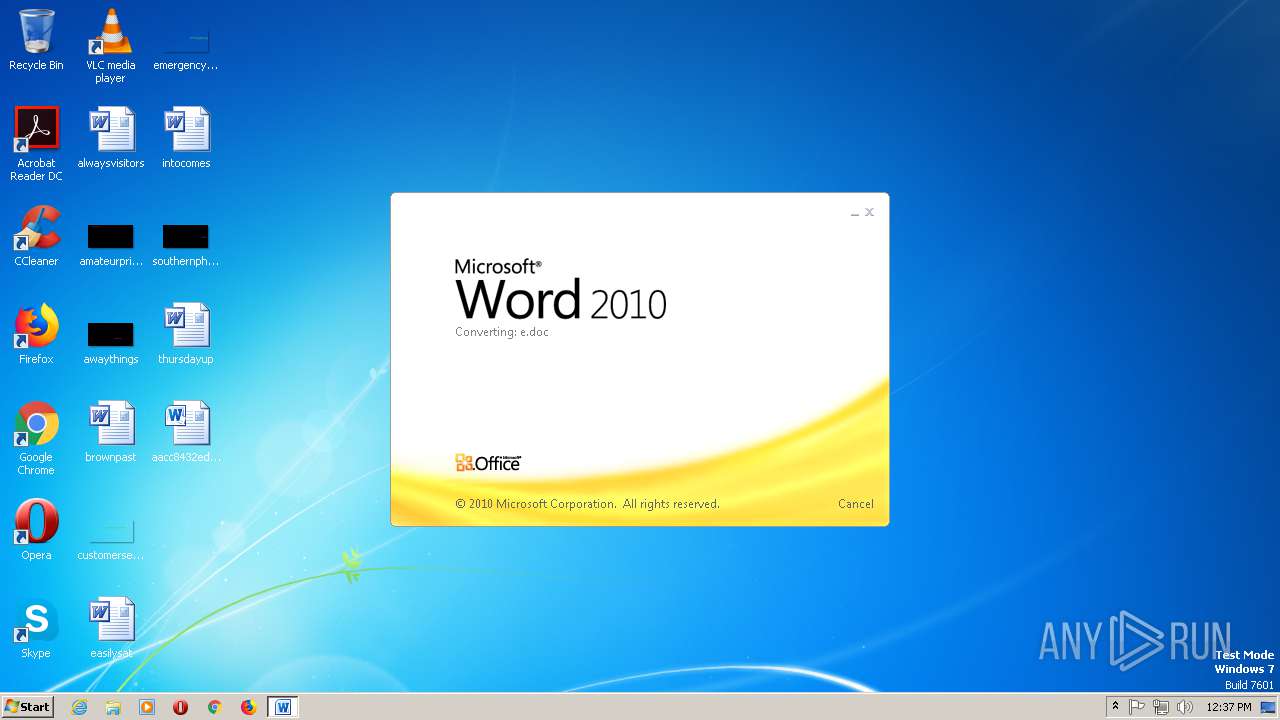
| File info: | Microsoft Word 2007+ |
| MD5: | 43B1FEE15096EDB5B3EB18999B84B838 |
| SHA1: | 2777ECB029E986AB2FC281724DF1EDF2C71B429A |
| SHA256: | AACC8432EDA684B179DAB3DE142286625D9A7322E5D9B3501B9CC711AF9B50DC |
| SSDEEP: | 1536:Jnz0vf4iGbX51pae9ziilMtQzRzn+FNWqnalO/Kp:Jz0X49L51MVipx+FNWCCp |
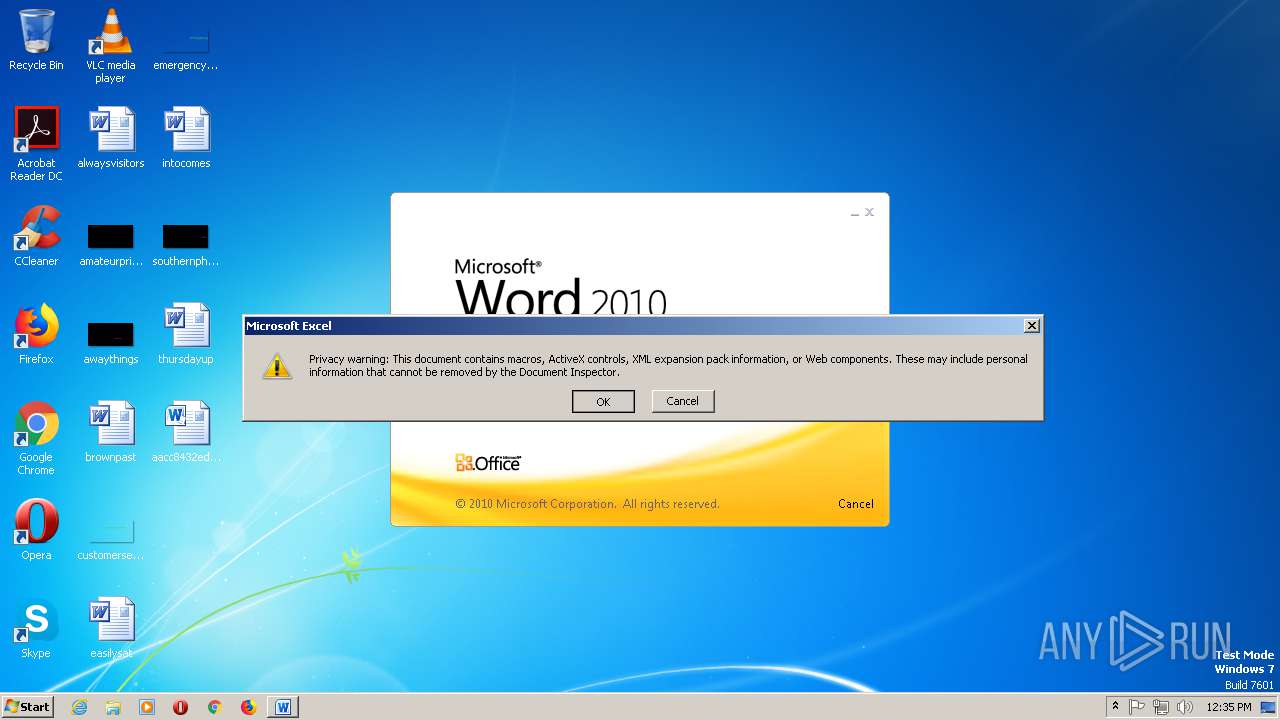
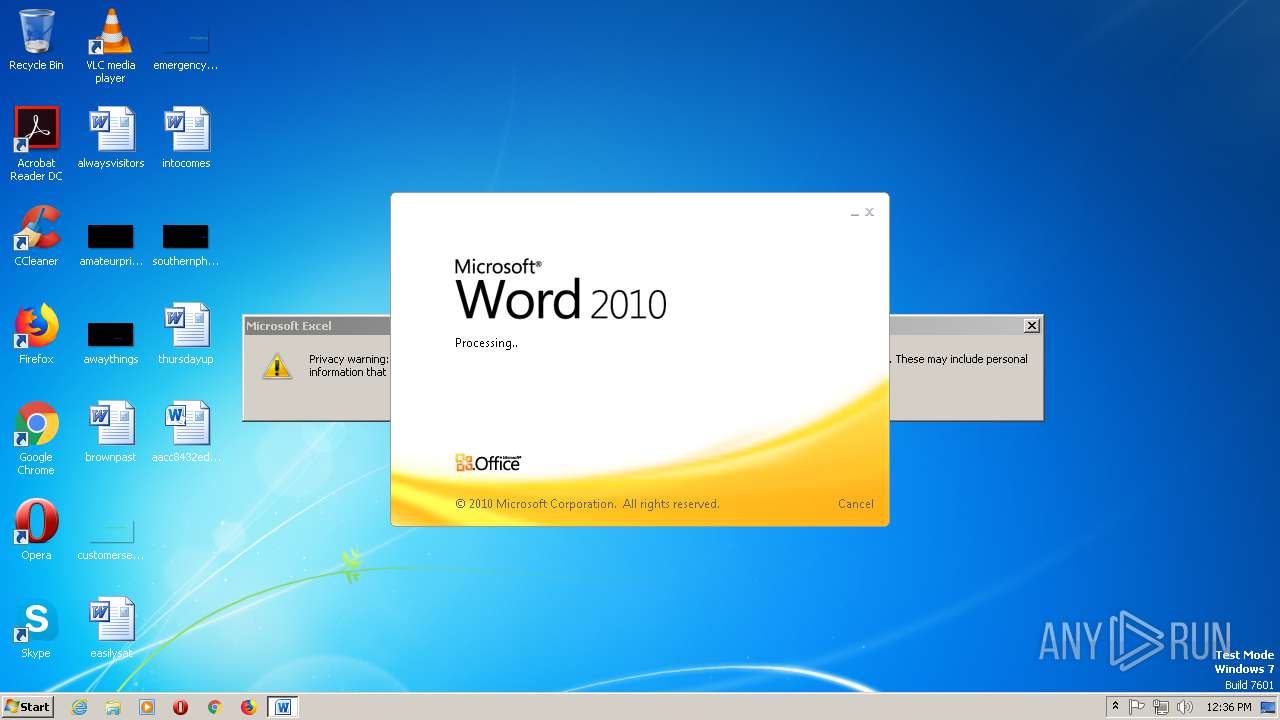
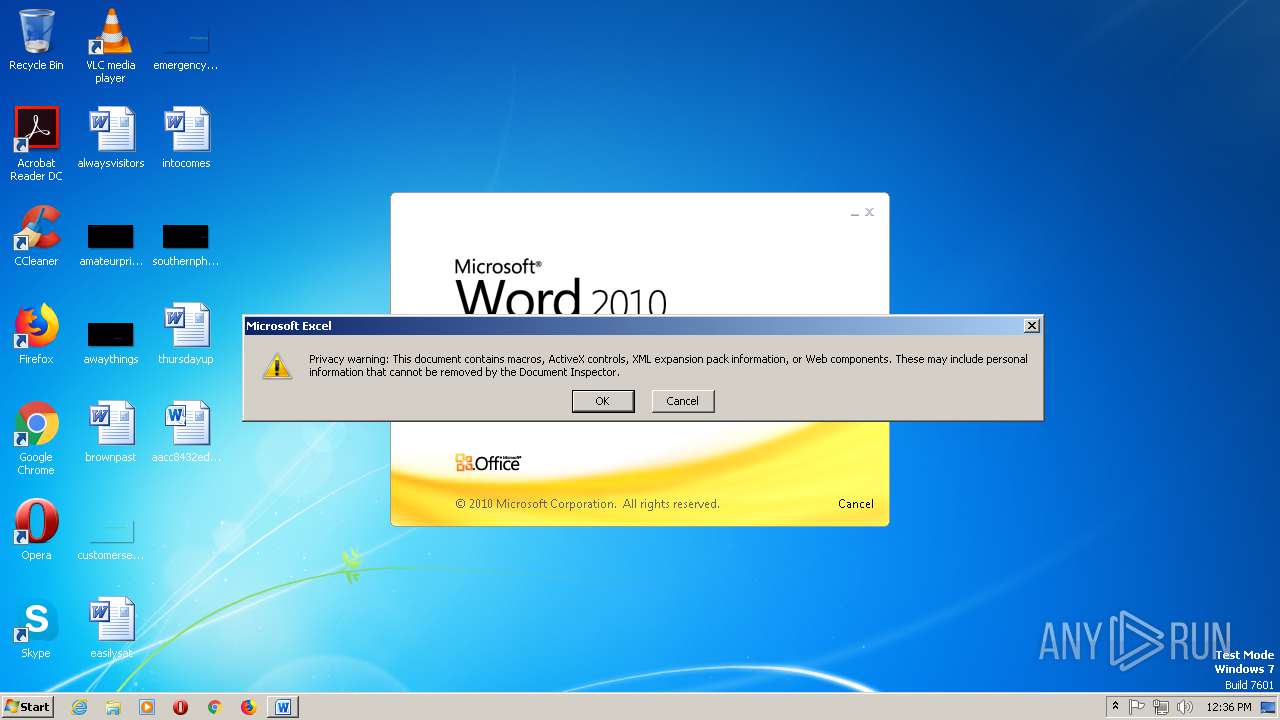
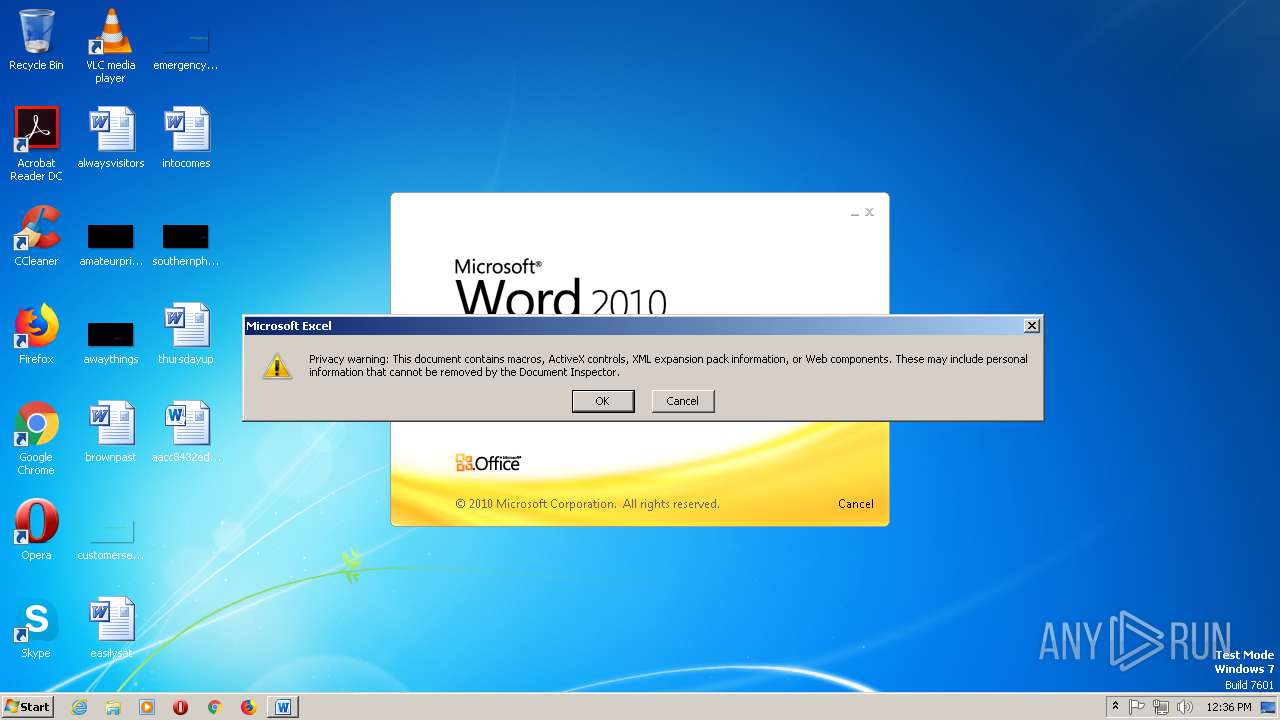
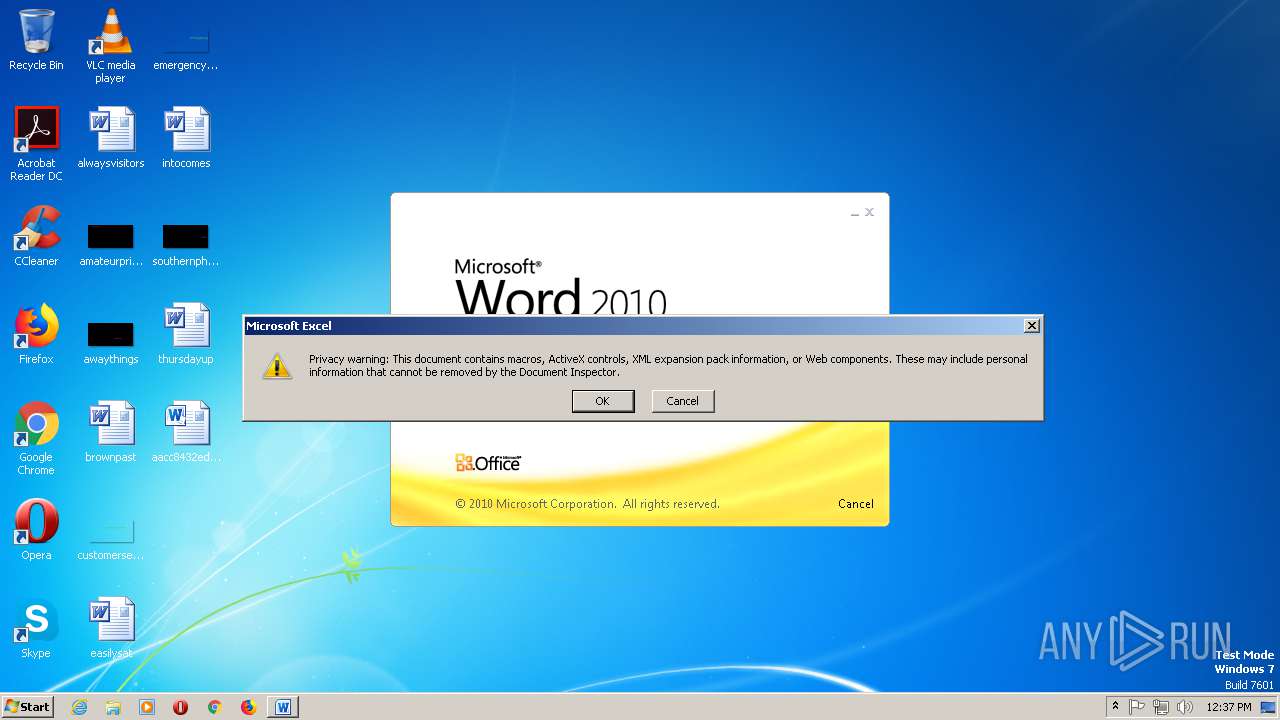
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2904)
- EXCEL.EXE (PID: 2712)
- EXCEL.EXE (PID: 2732)
- EXCEL.EXE (PID: 2964)
- EXCEL.EXE (PID: 968)
- EXCEL.EXE (PID: 2444)
- EXCEL.EXE (PID: 1400)
- EXCEL.EXE (PID: 2644)
- EXCEL.EXE (PID: 2112)
- EXCEL.EXE (PID: 2564)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2884)
- cmd.exe (PID: 2212)
- cmd.exe (PID: 1648)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 2104)
- cmd.exe (PID: 1284)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 2248)
- cmd.exe (PID: 668)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 992)
- cmd.exe (PID: 3068)
- cmd.exe (PID: 1360)
- cmd.exe (PID: 1476)
- cmd.exe (PID: 2072)
- cmd.exe (PID: 1448)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2904)
- EXCEL.EXE (PID: 2712)
- EXCEL.EXE (PID: 2732)
- EXCEL.EXE (PID: 2964)
- EXCEL.EXE (PID: 968)
- EXCEL.EXE (PID: 2444)
- EXCEL.EXE (PID: 1400)
- EXCEL.EXE (PID: 2644)
- EXCEL.EXE (PID: 2112)
- EXCEL.EXE (PID: 2564)
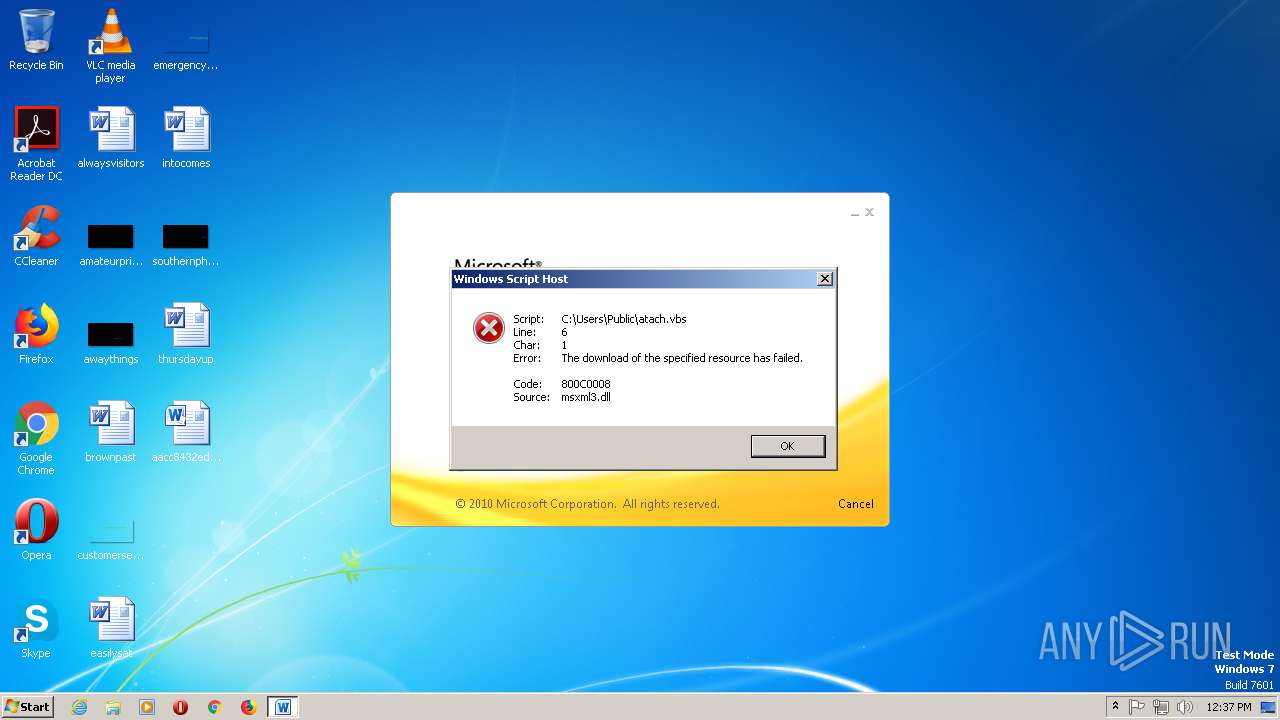
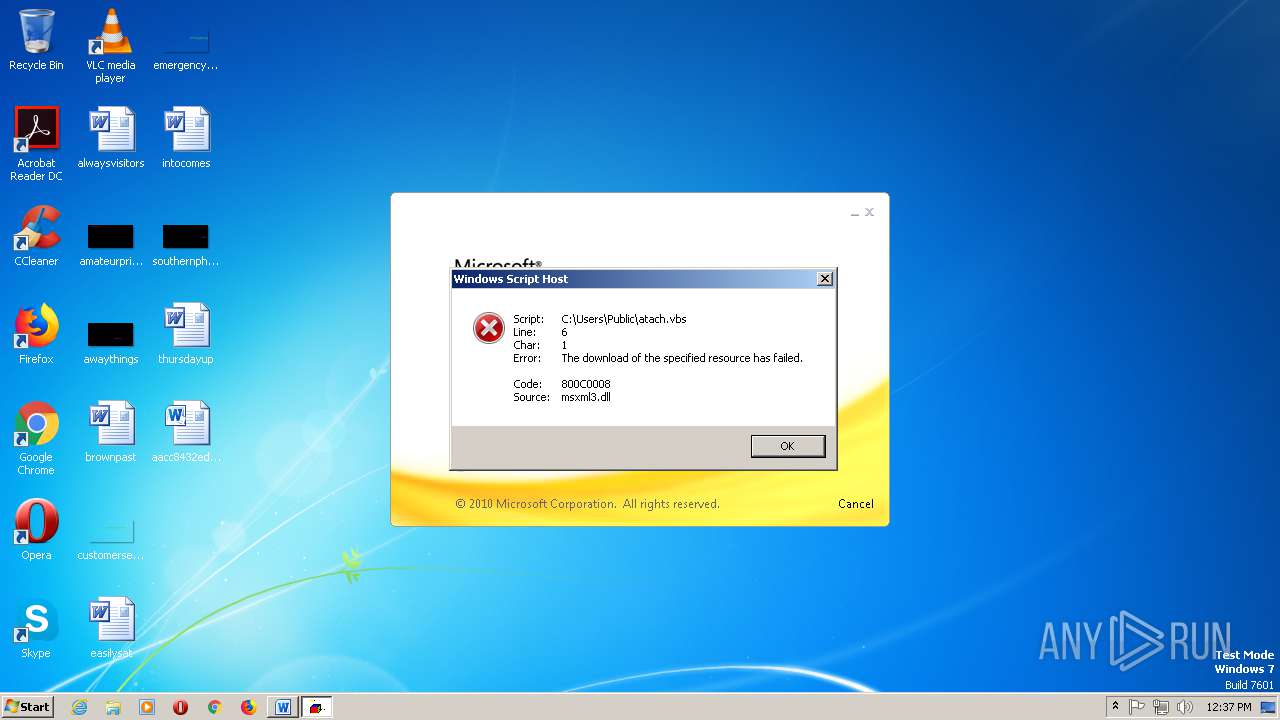
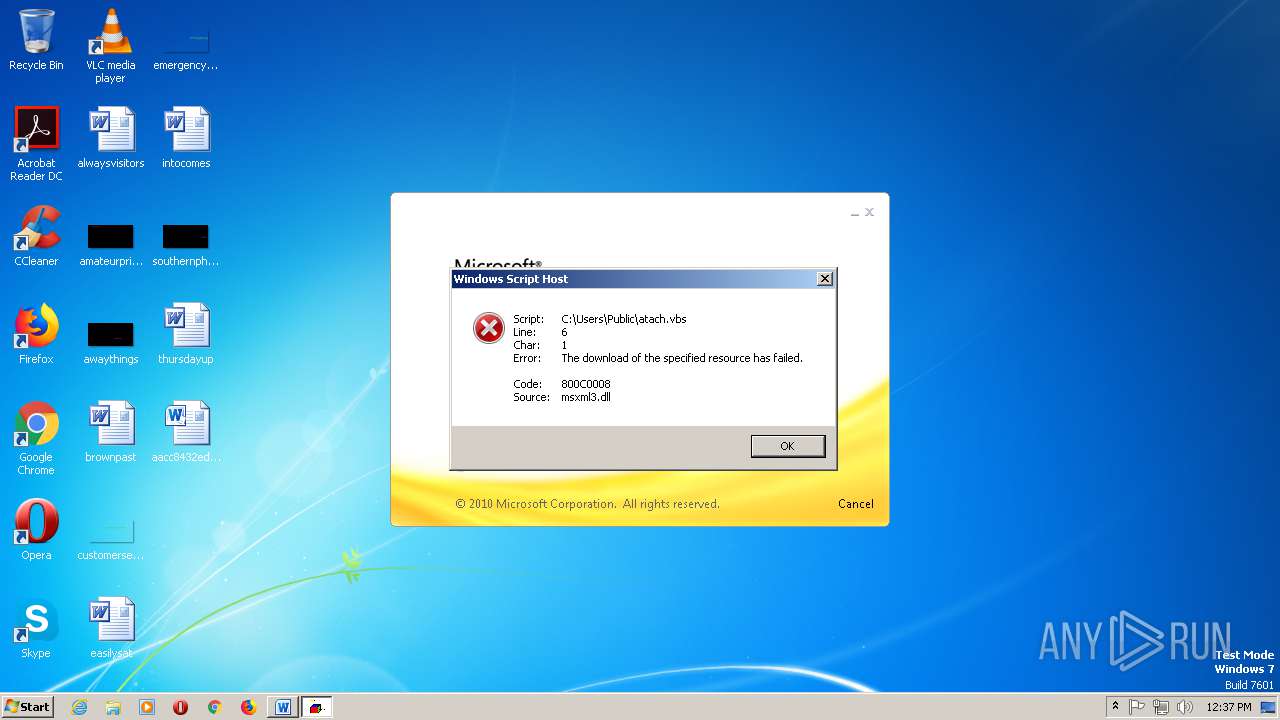
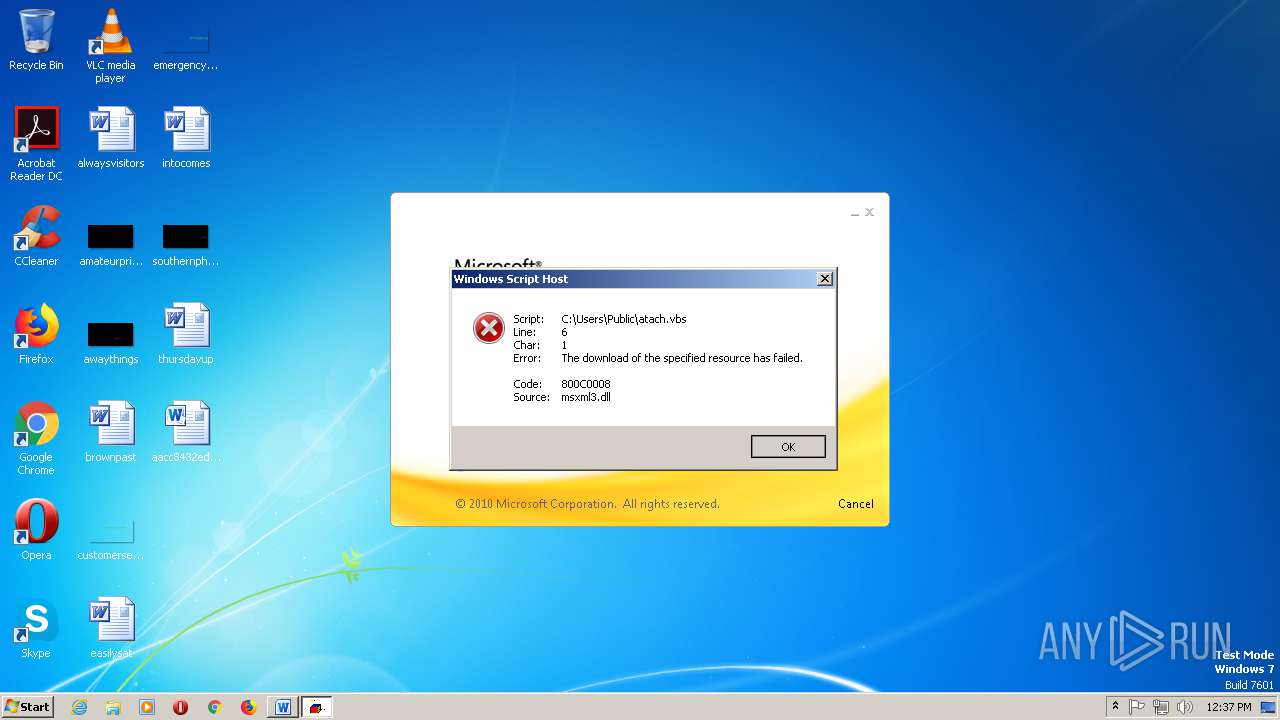
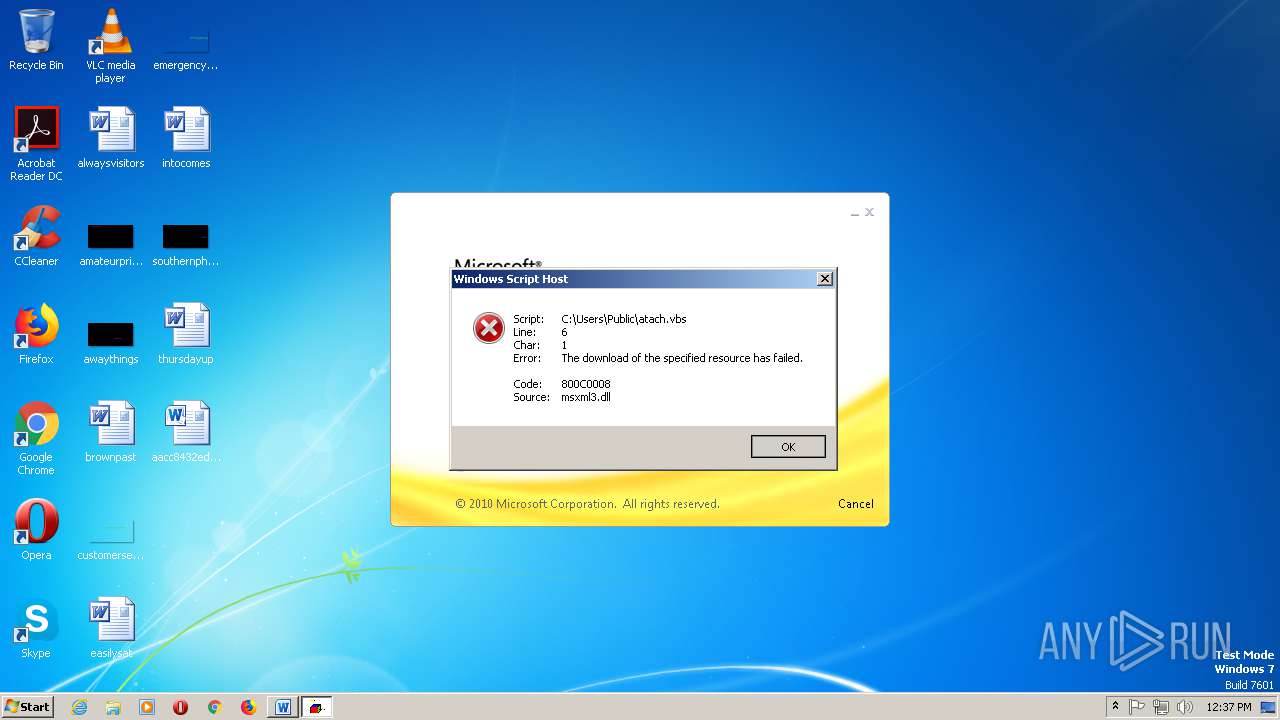
Application was dropped or rewritten from another process
- WScript.exe (PID: 2576)
- amsi.dll (PID: 2260)
- wscript.exe (PID: 2276)
- WScript.exe (PID: 2548)
- amsi.dll (PID: 2556)
- WScript.exe (PID: 2740)
- WScript.exe (PID: 2208)
- wscript.exe (PID: 3012)
- WScript.exe (PID: 2152)
- WScript.exe (PID: 2668)
- wscript.exe (PID: 2280)
- WScript.exe (PID: 2080)
- WScript.exe (PID: 392)
- wscript.exe (PID: 2564)
- WScript.exe (PID: 600)
- WScript.exe (PID: 1748)
- WScript.exe (PID: 1368)
- WScript.exe (PID: 2080)
- wscript.exe (PID: 1816)
- WScript.exe (PID: 1916)
- WScript.exe (PID: 1404)
- wscript.exe (PID: 2328)
- WScript.exe (PID: 1152)
- WScript.exe (PID: 2176)
- wscript.exe (PID: 1668)
- WScript.exe (PID: 608)
- WScript.exe (PID: 2432)
- WScript.exe (PID: 2608)
- wscript.exe (PID: 2280)
- WScript.exe (PID: 3036)
- wscript.exe (PID: 2416)
Loads dropped or rewritten executable
- cmd.exe (PID: 2884)
- cmd.exe (PID: 2212)
- WScript.exe (PID: 2548)
- amsi.dll (PID: 2260)
- wscript.exe (PID: 2276)
- cmd.exe (PID: 1648)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 2104)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 1284)
- cmd.exe (PID: 2248)
- cmd.exe (PID: 668)
- explorer.exe (PID: 1896)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 992)
- cmd.exe (PID: 3068)
- cmd.exe (PID: 1360)
- cmd.exe (PID: 1476)
- cmd.exe (PID: 2072)
- cmd.exe (PID: 1448)
Writes to a start menu file
- amsi.dll (PID: 2260)
- amsi.dll (PID: 2556)
- WScript.exe (PID: 2208)
- WScript.exe (PID: 2668)
- WScript.exe (PID: 392)
- WScript.exe (PID: 2080)
- WScript.exe (PID: 1404)
- WScript.exe (PID: 1152)
- WScript.exe (PID: 2432)
- WScript.exe (PID: 3036)
Changes the autorun value in the registry
- amsi.dll (PID: 2260)
- WScript.exe (PID: 2208)
- amsi.dll (PID: 2556)
- WScript.exe (PID: 2668)
- WScript.exe (PID: 392)
- WScript.exe (PID: 2080)
- WScript.exe (PID: 1404)
- WScript.exe (PID: 1152)
- WScript.exe (PID: 2432)
- WScript.exe (PID: 3036)
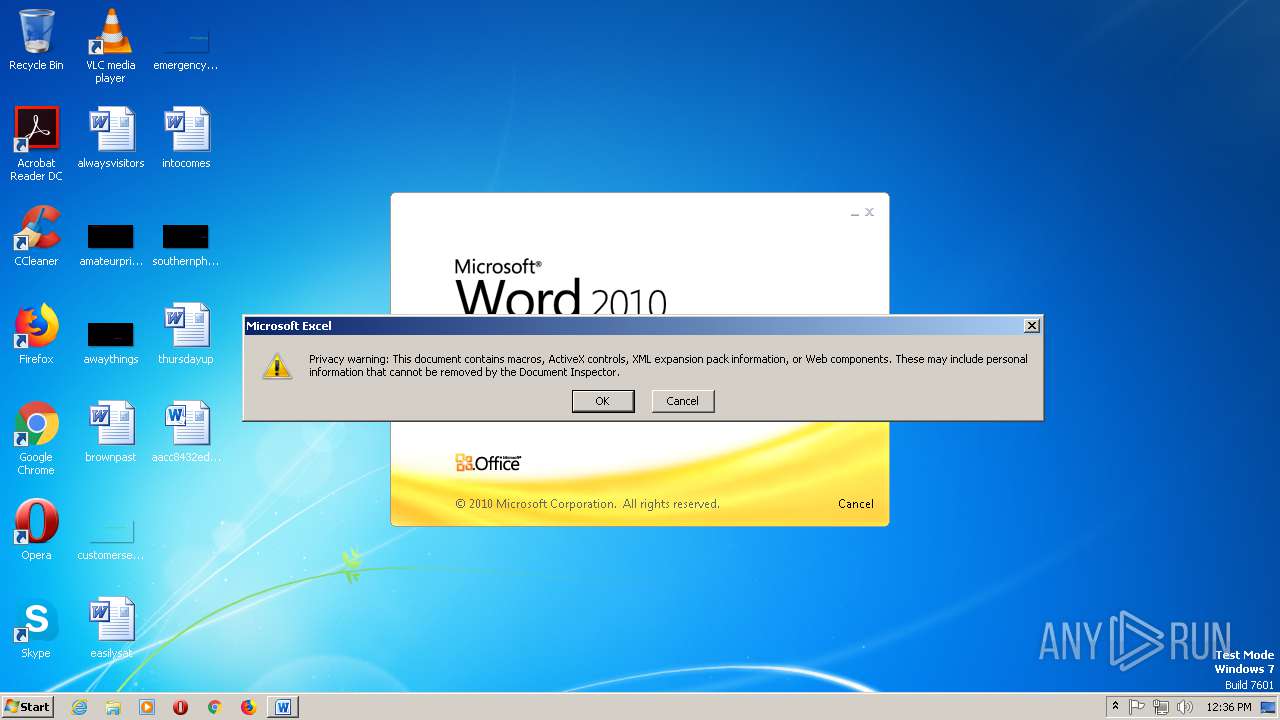
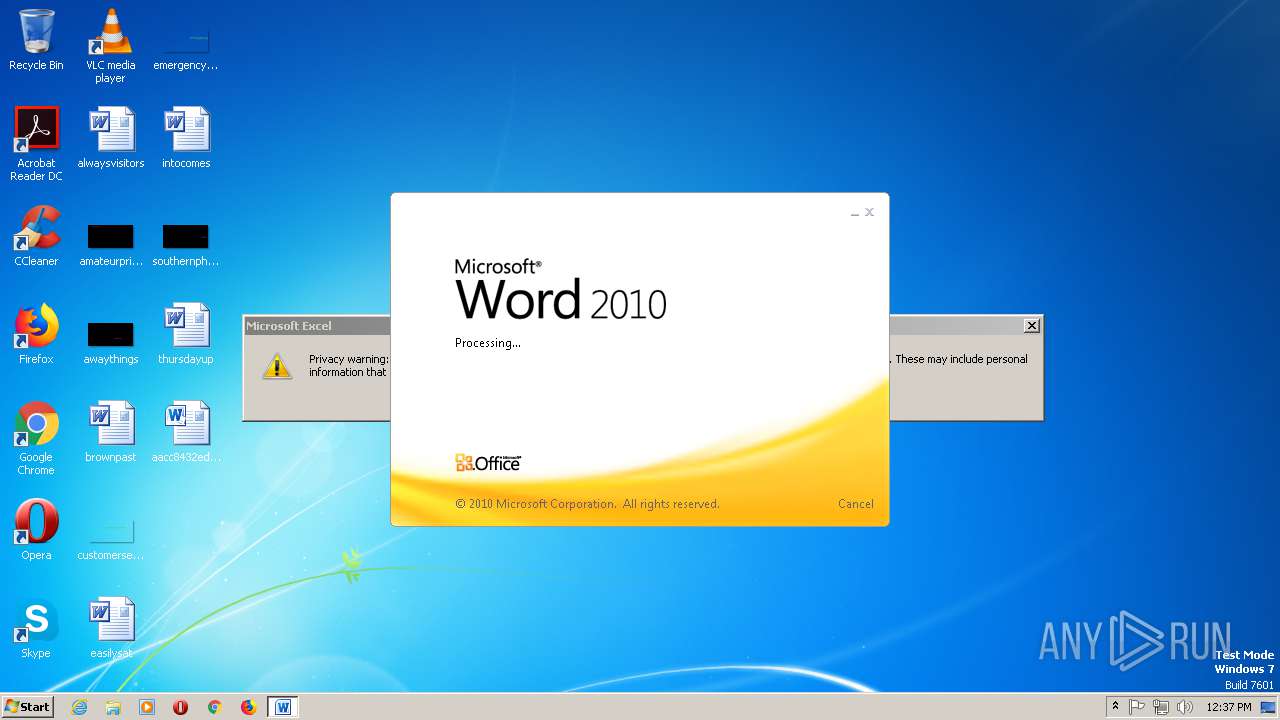
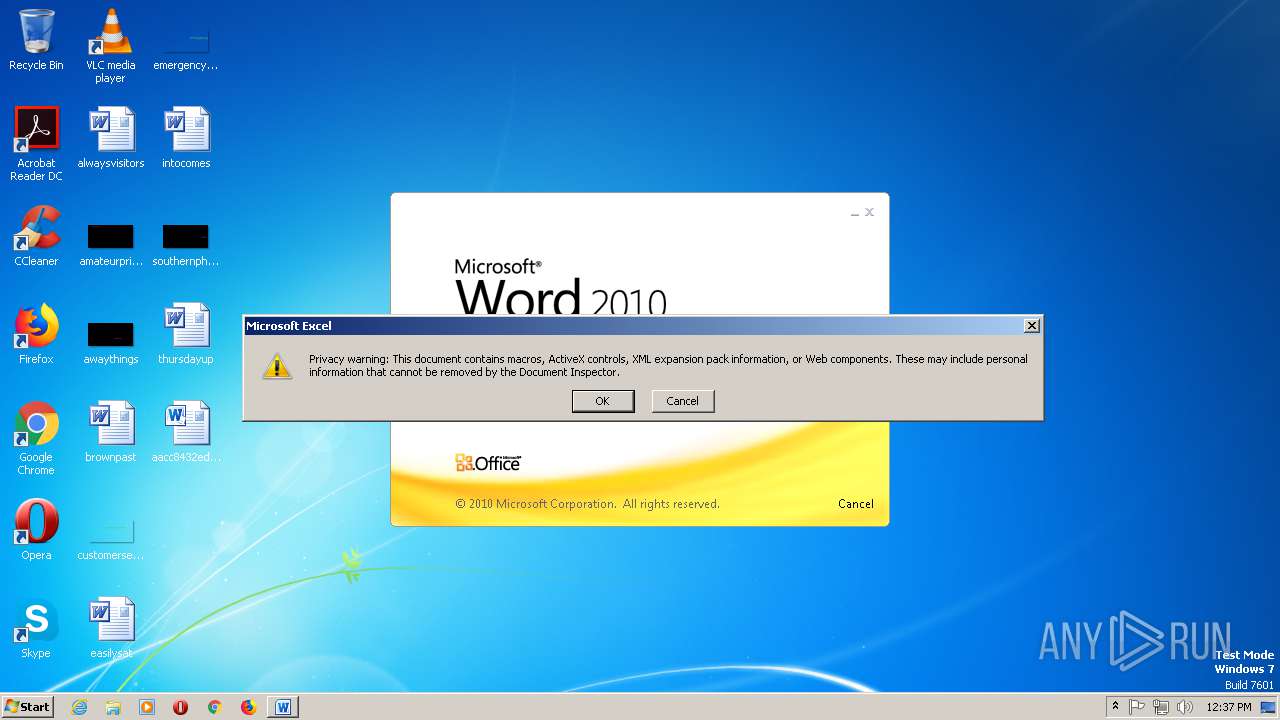
SUSPICIOUS
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2904)
- WINWORD.EXE (PID: 2992)
- amsi.dll (PID: 2260)
- EXCEL.EXE (PID: 2712)
- WScript.exe (PID: 2208)
- EXCEL.EXE (PID: 2732)
- WScript.exe (PID: 2668)
- amsi.dll (PID: 2556)
- EXCEL.EXE (PID: 2964)
- WScript.exe (PID: 392)
- EXCEL.EXE (PID: 968)
- WScript.exe (PID: 1748)
- EXCEL.EXE (PID: 2444)
- WScript.exe (PID: 2080)
- EXCEL.EXE (PID: 1400)
- WScript.exe (PID: 1404)
- EXCEL.EXE (PID: 2644)
- WScript.exe (PID: 1152)
- EXCEL.EXE (PID: 2112)
- WScript.exe (PID: 2432)
- EXCEL.EXE (PID: 2564)
- WScript.exe (PID: 3036)
Executed via COM
- EXCEL.EXE (PID: 2904)
- EXCEL.EXE (PID: 2712)
- excelcnv.exe (PID: 2320)
- EXCEL.EXE (PID: 2732)
- excelcnv.exe (PID: 2988)
- EXCEL.EXE (PID: 2964)
- excelcnv.exe (PID: 2696)
- excelcnv.exe (PID: 2772)
- EXCEL.EXE (PID: 968)
- excelcnv.exe (PID: 2440)
- EXCEL.EXE (PID: 2444)
- excelcnv.exe (PID: 2760)
- EXCEL.EXE (PID: 1400)
- excelcnv.exe (PID: 1344)
- excelcnv.exe (PID: 2824)
- EXCEL.EXE (PID: 2644)
- EXCEL.EXE (PID: 2112)
- excelcnv.exe (PID: 1232)
- EXCEL.EXE (PID: 2564)
- excelcnv.exe (PID: 2336)
Executes scripts
- cmd.exe (PID: 2884)
- cmd.exe (PID: 2212)
- amsi.dll (PID: 2260)
- cmd.exe (PID: 1648)
- cmd.exe (PID: 2100)
- WScript.exe (PID: 2208)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 2104)
- WScript.exe (PID: 2668)
- cmd.exe (PID: 1284)
- cmd.exe (PID: 2376)
- WScript.exe (PID: 392)
- cmd.exe (PID: 2248)
- cmd.exe (PID: 668)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 3024)
- WScript.exe (PID: 2080)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2064)
- WScript.exe (PID: 1404)
- cmd.exe (PID: 992)
- cmd.exe (PID: 3068)
- WScript.exe (PID: 1152)
- cmd.exe (PID: 1360)
- cmd.exe (PID: 1476)
- cmd.exe (PID: 2072)
- WScript.exe (PID: 2432)
- cmd.exe (PID: 1448)
- WScript.exe (PID: 3036)
Executable content was dropped or overwritten
- WScript.exe (PID: 2548)
Starts itself from another location
- WScript.exe (PID: 2548)
- amsi.dll (PID: 2260)
Reads the machine GUID from the registry
- WScript.exe (PID: 2576)
- WScript.exe (PID: 2548)
- amsi.dll (PID: 2260)
- wscript.exe (PID: 2276)
- amsi.dll (PID: 2556)
- WScript.exe (PID: 2740)
- WScript.exe (PID: 2208)
- WScript.exe (PID: 2152)
- WScript.exe (PID: 2668)
- WScript.exe (PID: 2080)
- WScript.exe (PID: 392)
- WScript.exe (PID: 600)
- WScript.exe (PID: 1748)
- WScript.exe (PID: 1368)
- WScript.exe (PID: 2080)
- WScript.exe (PID: 1916)
- WScript.exe (PID: 1404)
- WScript.exe (PID: 2176)
- WScript.exe (PID: 1152)
- WScript.exe (PID: 2432)
- WScript.exe (PID: 608)
- WScript.exe (PID: 2608)
- WScript.exe (PID: 3036)
Starts application with an unusual extension
- WScript.exe (PID: 2548)
- wscript.exe (PID: 2276)
Creates files in the user directory
- amsi.dll (PID: 2260)
- explorer.exe (PID: 1896)
Application launched itself
- WScript.exe (PID: 2208)
- WScript.exe (PID: 2668)
- WScript.exe (PID: 392)
- WScript.exe (PID: 2080)
- WScript.exe (PID: 1404)
- WScript.exe (PID: 1152)
- WScript.exe (PID: 2432)
- WScript.exe (PID: 3036)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 1896)
Reads settings of System Certificates
- EXCEL.EXE (PID: 2904)
- amsi.dll (PID: 2260)
- amsi.dll (PID: 2556)
- EXCEL.EXE (PID: 2712)
- WScript.exe (PID: 2208)
- EXCEL.EXE (PID: 2732)
- WScript.exe (PID: 2668)
- EXCEL.EXE (PID: 2964)
- WScript.exe (PID: 392)
- EXCEL.EXE (PID: 968)
- EXCEL.EXE (PID: 2444)
- WScript.exe (PID: 2080)
- EXCEL.EXE (PID: 1400)
- WScript.exe (PID: 1404)
- EXCEL.EXE (PID: 2644)
- WScript.exe (PID: 1152)
- EXCEL.EXE (PID: 2112)
- WScript.exe (PID: 2432)
- EXCEL.EXE (PID: 2564)
- WScript.exe (PID: 3036)
Creates files in the user directory
- EXCEL.EXE (PID: 2904)
- WINWORD.EXE (PID: 2992)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2992)
- EXCEL.EXE (PID: 2904)
- excelcnv.exe (PID: 2696)
- EXCEL.EXE (PID: 2712)
- excelcnv.exe (PID: 2320)
- EXCEL.EXE (PID: 2732)
- excelcnv.exe (PID: 2988)
- EXCEL.EXE (PID: 2964)
- excelcnv.exe (PID: 2772)
- EXCEL.EXE (PID: 968)
- excelcnv.exe (PID: 2440)
- EXCEL.EXE (PID: 2444)
- excelcnv.exe (PID: 2760)
- EXCEL.EXE (PID: 1400)
- excelcnv.exe (PID: 1344)
- EXCEL.EXE (PID: 2644)
- EXCEL.EXE (PID: 2112)
- excelcnv.exe (PID: 2824)
- excelcnv.exe (PID: 1232)
- EXCEL.EXE (PID: 2564)
- excelcnv.exe (PID: 2336)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2904)
- WINWORD.EXE (PID: 2992)
- EXCEL.EXE (PID: 2712)
- EXCEL.EXE (PID: 2732)
- excelcnv.exe (PID: 2320)
- excelcnv.exe (PID: 2988)
- EXCEL.EXE (PID: 2964)
- excelcnv.exe (PID: 2696)
- excelcnv.exe (PID: 2772)
- EXCEL.EXE (PID: 968)
- excelcnv.exe (PID: 2440)
- EXCEL.EXE (PID: 2444)
- excelcnv.exe (PID: 2760)
- EXCEL.EXE (PID: 1400)
- excelcnv.exe (PID: 1344)
- EXCEL.EXE (PID: 2644)
- excelcnv.exe (PID: 2824)
- excelcnv.exe (PID: 1232)
- EXCEL.EXE (PID: 2112)
- excelcnv.exe (PID: 2336)
- EXCEL.EXE (PID: 2564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xf2459e1f |
| ZipCompressedSize: | 392 |
| ZipUncompressedSize: | 1806 |
| ZipFileName: | [Content_Types].xml |
XMP
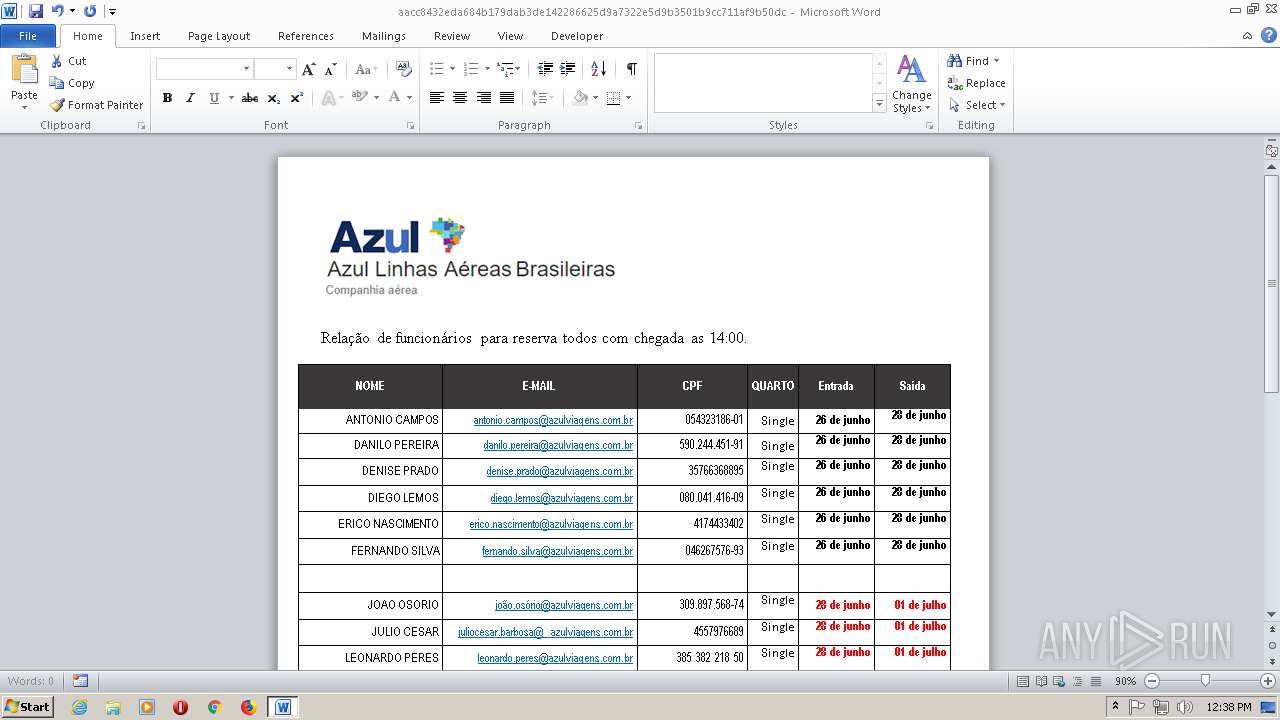
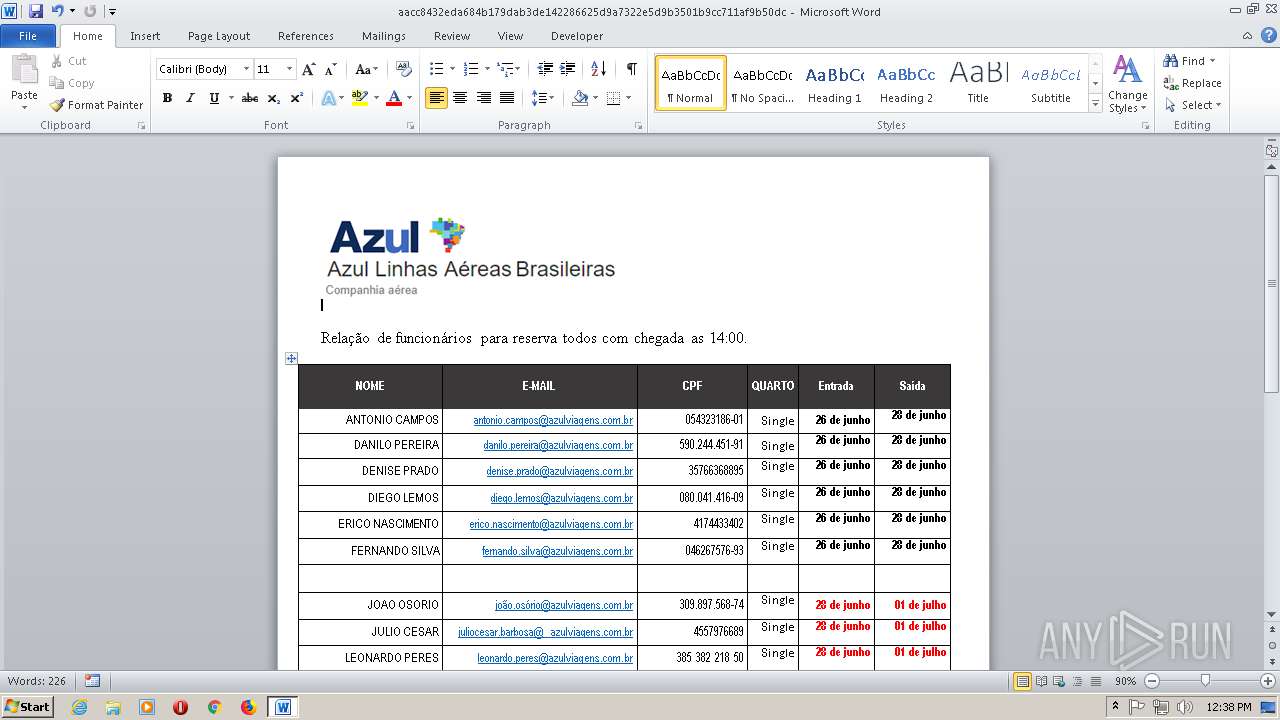
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Joselio Bonin |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | Joselio Bonin |
| RevisionNumber: | 5 |
| CreateDate: | 2019:06:16 00:44:00Z |
| ModifyDate: | 2019:06:17 01:53:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 17.4 hours |
| Pages: | 1 |
| Words: | 411 |
| Characters: | 2221 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 18 |
| Paragraphs: | 5 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 2627 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
155
Monitored processes
93
Malicious processes
39
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\atach.vbs" | C:\Windows\System32\WScript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 600 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\WindowsDefender.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 608 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\WindowsDefender.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 668 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 5 > nul & start C:\Users\Public\atach.vbs | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 764 | ping 127.0.0.1 -n 3 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.4756.1000 Modules
| |||||||||||||||
| 992 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 3 > nul & start C:\Users\Public\WindowsDefender.vbs | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 996 | ping 127.0.0.1 -n 3 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | ping 127.0.0.1 -n 5 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1152 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\atach.vbs" | C:\Windows\System32\WScript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
229 619
Read events
226 906
Write events
2 455
Delete events
258
Modification events
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;.' |
Value: 3B2E2700B00B0000010000000000000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1896) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {C41662BB-1FA0-4CE0-8DC5-9B7F8279FF97} {BB2E617C-0920-11D1-9A0B-00C04FC2D6C1} 0xFFFF |
Value: 01000000000000009854CF559B26D501 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1322450986 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451070 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451071 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B00B0000C60A64559B26D50100000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /2' |
Value: 2F322700B00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | /2' |
Value: 2F322700B00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
1
Suspicious files
27
Text files
117
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFA3B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{9A5D553E-AE7A-4A0A-8DA2-2750AB7D0CB5} | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{684D3160-23A5-4D38-8404-DD21D40E0D25} | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F25EF064.doc | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C67B94EB.doc | — | |
MD5:— | SHA256:— | |||
| 2904 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9FE1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSF-{0E1EEE64-E8C6-4E2A-9759-63CF07FD8988}.FSF | binary | |
MD5:— | SHA256:— | |||
| 2904 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\P9VIFZZ5.txt | text | |
MD5:— | SHA256:— | |||
| 2904 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF43CEF5CF0C4D3892.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
320
DNS requests
7
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
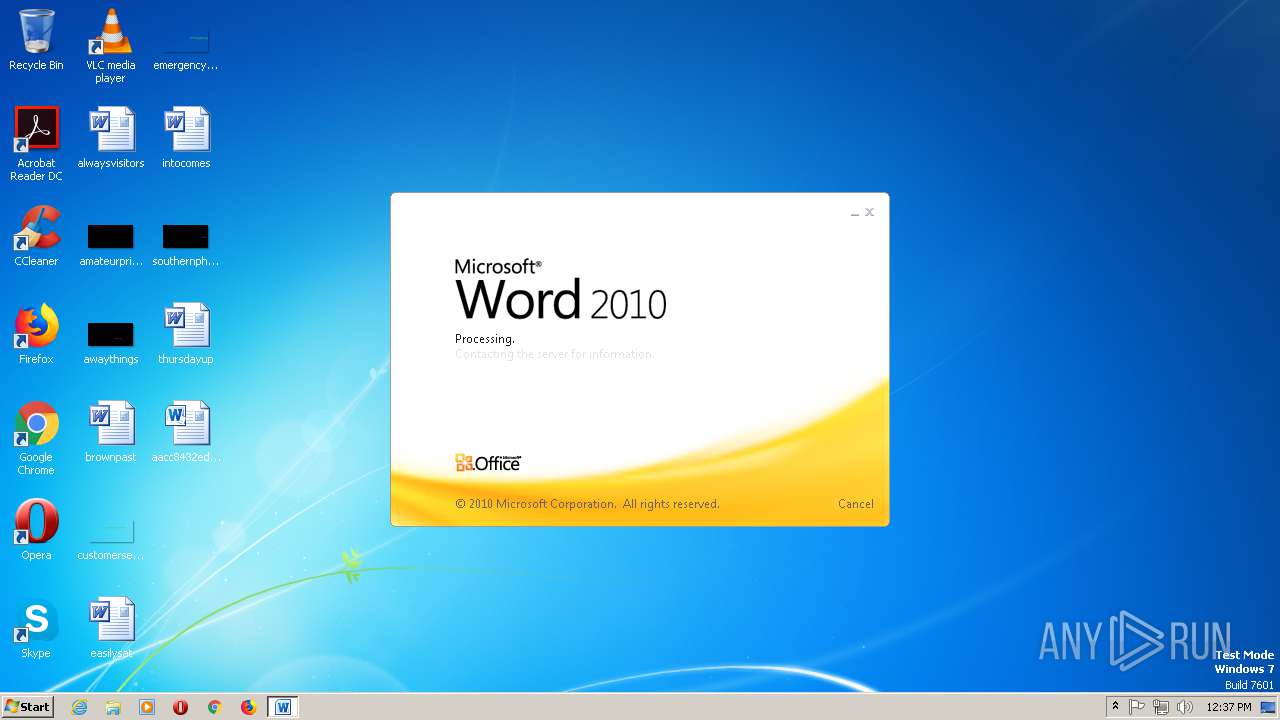
2992 | WINWORD.EXE | OPTIONS | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/ | BR | — | — | malicious |
2992 | WINWORD.EXE | GET | 304 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/a.doc | BR | — | — | malicious |
2992 | WINWORD.EXE | GET | 304 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/a.doc | BR | — | — | malicious |
2992 | WINWORD.EXE | GET | 304 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/b.doc | BR | — | — | malicious |
2992 | WINWORD.EXE | HEAD | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/c.doc | BR | — | — | malicious |
2992 | WINWORD.EXE | GET | 304 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/b.doc | BR | — | — | malicious |
2992 | WINWORD.EXE | HEAD | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/b.doc | BR | — | — | malicious |
844 | svchost.exe | OPTIONS | — | 191.252.51.35:80 | http://hotelpremier.com.br/ | BR | — | — | malicious |
2992 | WINWORD.EXE | GET | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/a.doc | BR | text | 104 Kb | malicious |
844 | svchost.exe | PROPFIND | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/ | BR | html | 31.3 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2260 | amsi.dll | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
2904 | EXCEL.EXE | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
2556 | amsi.dll | 168.197.229.117:70 | bylgay.hopto.org | GIGASAT SERVIÇOS DE PROCESSAMENTOS DE DADOS LTDA | BR | malicious |
2556 | amsi.dll | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
844 | svchost.exe | 191.252.51.35:80 | hotelpremier.com.br | Locaweb Serviços de Internet S/A | BR | malicious |
2556 | amsi.dll | 79.134.225.20:70 | microsoftoutlook.duckdns.org | Andreas Fink trading as Fink Telecom Services | CH | malicious |
2208 | WScript.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
2992 | WINWORD.EXE | 191.252.51.35:80 | hotelpremier.com.br | Locaweb Serviços de Internet S/A | BR | malicious |
392 | WScript.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
2444 | EXCEL.EXE | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hotelpremier.com.br |
| malicious |
dns.msftncsi.com |
| shared |
pastebin.com |
| malicious |
bylgay.hopto.org |
| malicious |
soucdtevoceumcuzao.duckdns.org |
| malicious |
microsoftoutlook.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2992 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
2992 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
372 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2992 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
2992 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
372 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2992 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
2992 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
2992 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
2992 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |